CCNA Configuration Lab Hands on Natthapong Wannurat CCNA
CCNA Configuration Lab Hands on Natthapong Wannurat CCNA, CCDA, CSE, SMBAM, SMBSE Channel Account Manager South Region Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 1
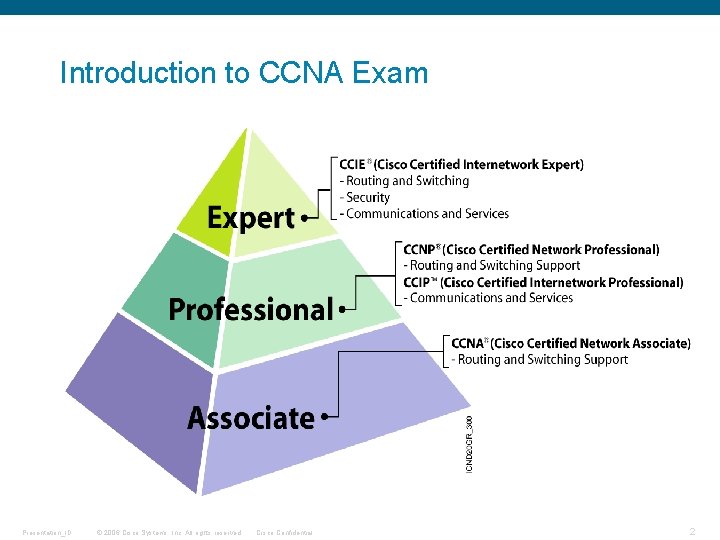
Introduction to CCNA Exam Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 2
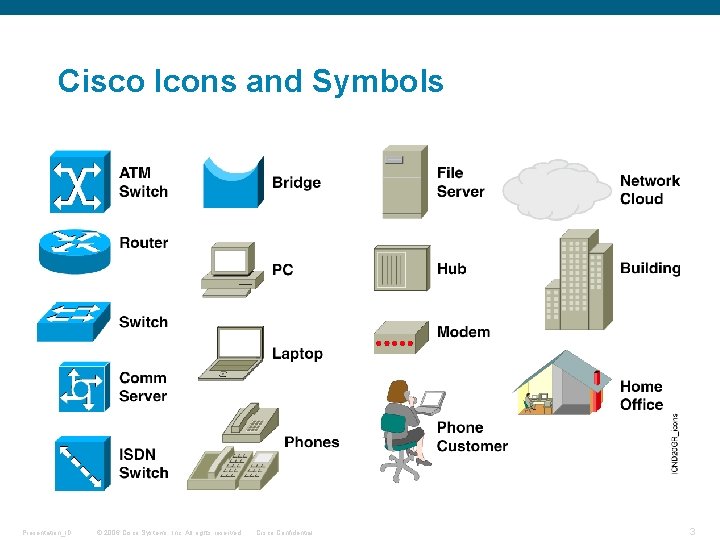
Cisco Icons and Symbols Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 3
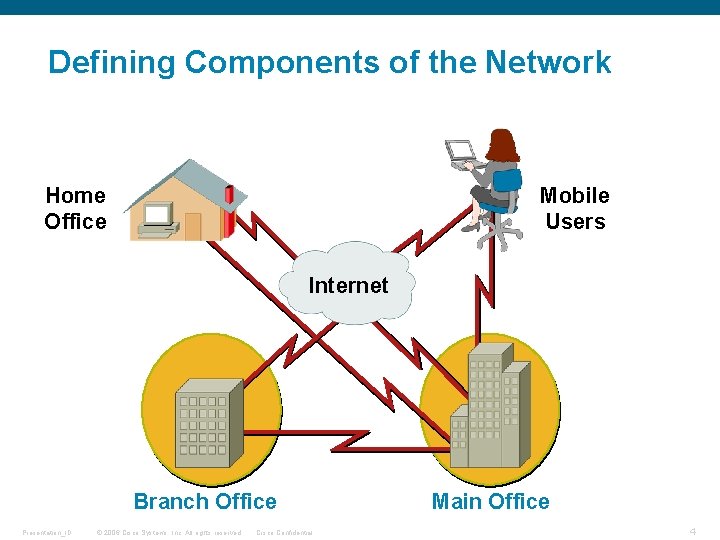
Defining Components of the Network Home Office Mobile Users Internet Branch Office Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential Main Office 4
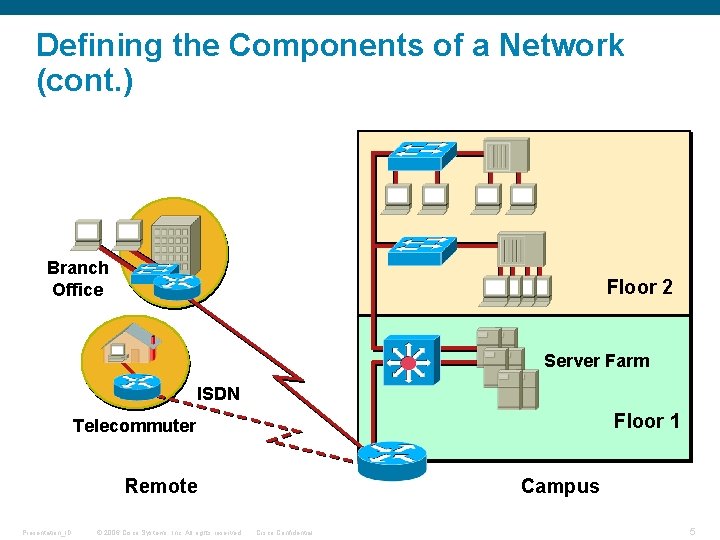
Defining the Components of a Network (cont. ) Branch Office Floor 2 Server Farm ISDN Floor 1 Telecommuter Remote Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Campus Cisco Confidential 5
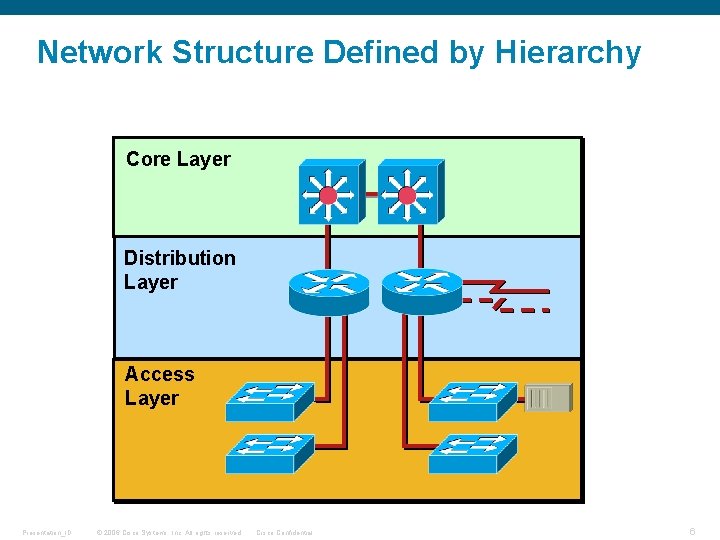
Network Structure Defined by Hierarchy Core Layer Distribution Layer Access Layer Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 6
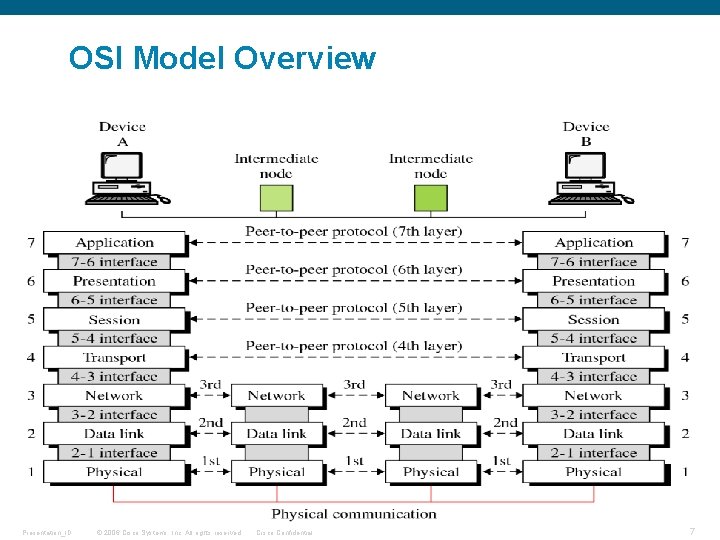
OSI Model Overview Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 7
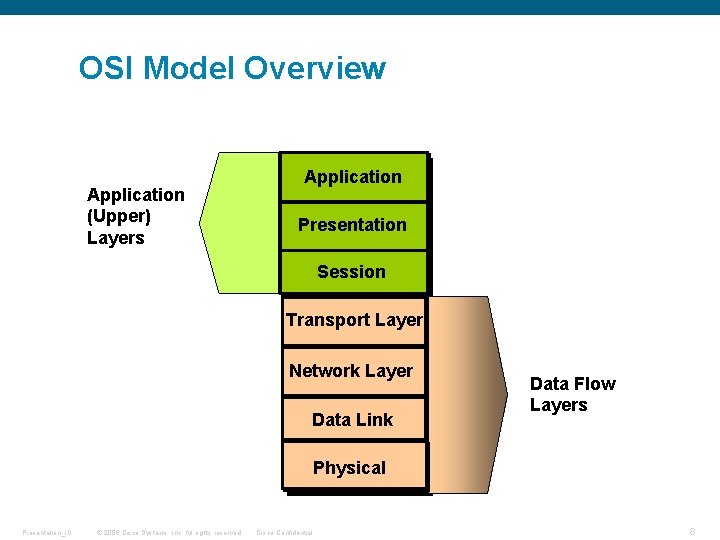
OSI Model Overview Application (Upper) Layers Application Presentation Session Transport Layer Network Layer Data Link Data Flow Layers Physical Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 8
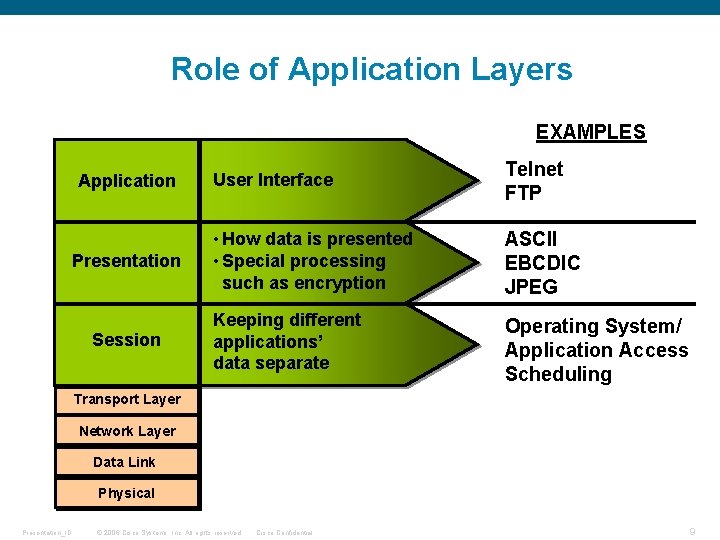
Role of Application Layers EXAMPLES Application Presentation Session User Interface Telnet FTP • How data is presented • Special processing such as encryption ASCII EBCDIC JPEG Keeping different applications’ data separate Operating System/ Application Access Scheduling Transport Layer Network Layer Data Link Physical Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 9
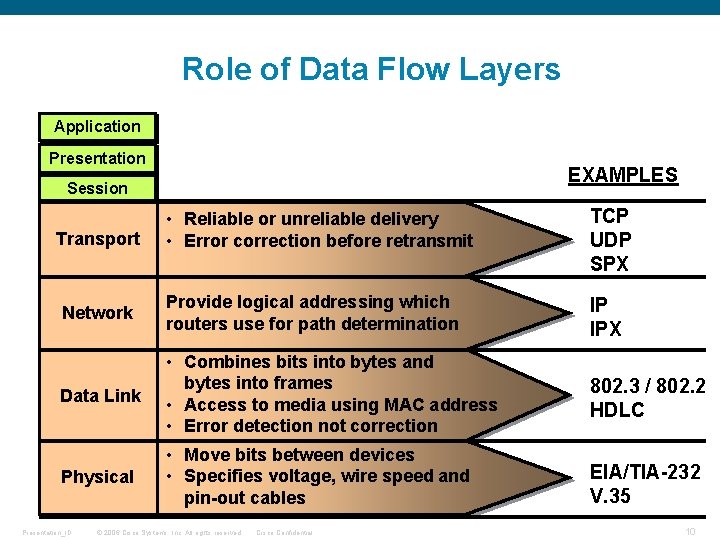
Role of Data Flow Layers Application Presentation EXAMPLES Session • Reliable or unreliable delivery • Error correction before retransmit TCP UDP SPX Network Provide logical addressing which routers use for path determination IP IPX Data Link • Combines bits into bytes and bytes into frames • Access to media using MAC address • Error detection not correction 802. 3 / 802. 2 HDLC Physical • Move bits between devices • Specifies voltage, wire speed and pin-out cables EIA/TIA-232 V. 35 Transport Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 10
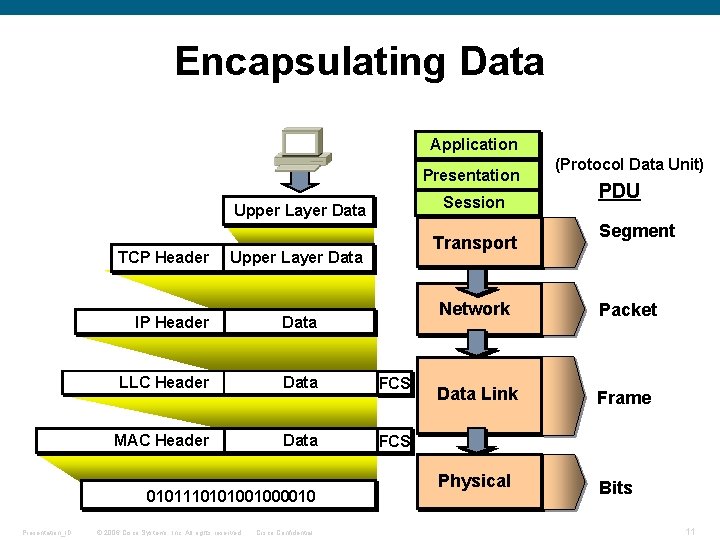
Encapsulating Data Application Presentation Session Upper Layer Data TCP Header Upper Layer Data IP Header Data LLC Header Data FCS MAC Header Data FCS 0101110101001000010 Presentation_ID Transport © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential (Protocol Data Unit) PDU Segment Network Packet Data Link Frame Physical Bits 11
Introduction to TCP/IP Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 12
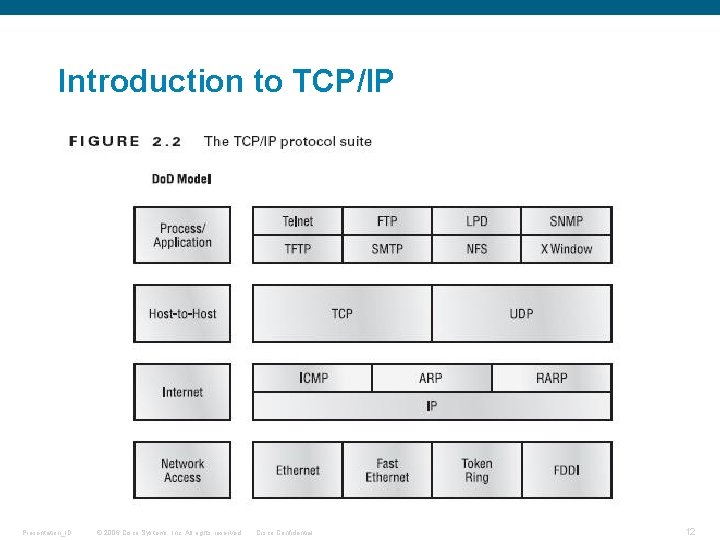
Introduction to TCP/IP TCP )Transmission Control Protocol) is a set of rules (protocol) used along with the Internet Protocol (IP) to send data in the form of message units between computers over the Internet. While IP takes care of handling the actual delivery of the data, TCP takes care of keeping track of the individual units of data (called packets) that a message is divided into for efficient routing through the Internet. User Datagram Protocol) UDP (is one of the core protocols of the Internet protocol suite. Using UDP, programs on networked computers can send short messages sometimes known as datagrams) using Datagram Sockets) to one another. UDP is sometimes called the Universal Datagram Protocol or Unreliable Datagram Protocol. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 13
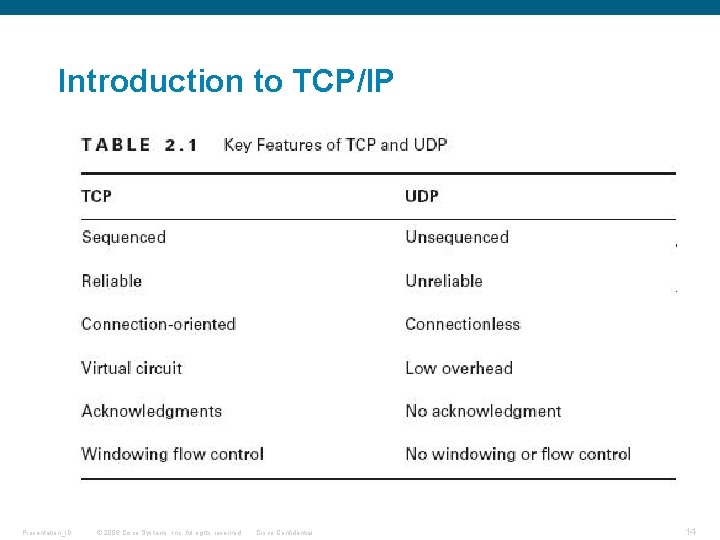
Introduction to TCP/IP Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 14
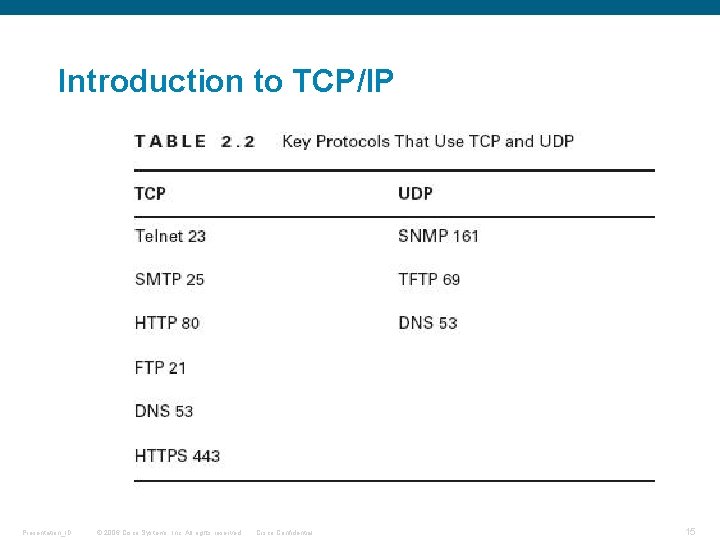
Introduction to TCP/IP Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 15
IP Addressing, Subnetting and Variable-Length Subnet Masks (VLSM) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 16
1. Agenda § Explain basic IP Addressing § Review Subnetting concepts § How to Calculate Subnets, host Addresses and broadcast id's § Explain VLSM concepts and Route Summarization Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 17
Why IP Addresses? Uniquely identifies each device on an IP network so that data can be sent correctly to those locations. Real life analogies: Address on a letter Telephone number Every host (computer, networking device, peripheral) must have a unique address. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 18
Parts of the IP Address § Each IP address consists of: Network ID Identifies the network to which the host belongs Assigned by registry authority and cannot be changed Host ID Identifies the individual host Assigned by organizations to individual devices Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 19
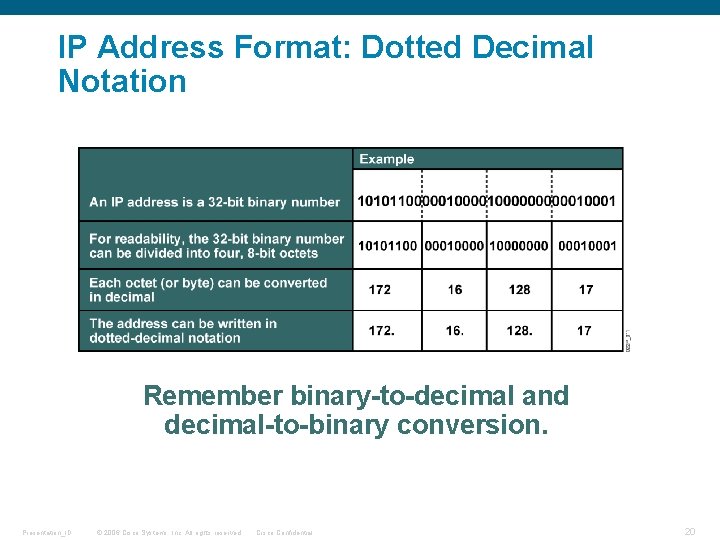
IP Address Format: Dotted Decimal Notation Remember binary-to-decimal and decimal-to-binary conversion. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 20
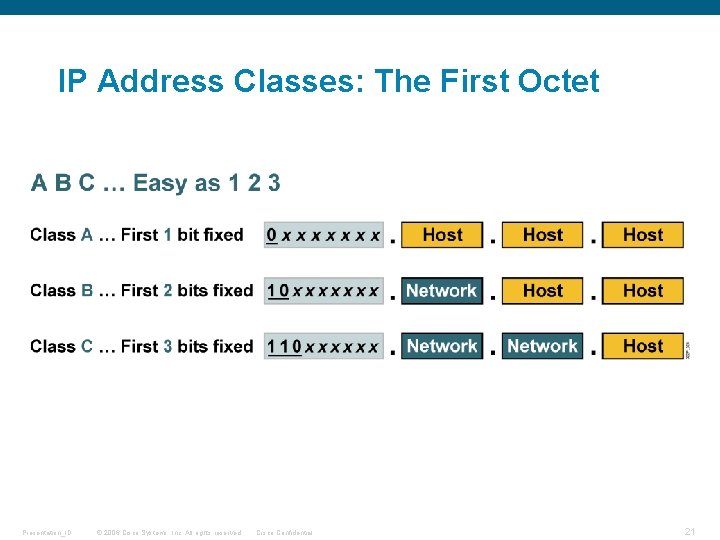
IP Address Classes: The First Octet Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 21
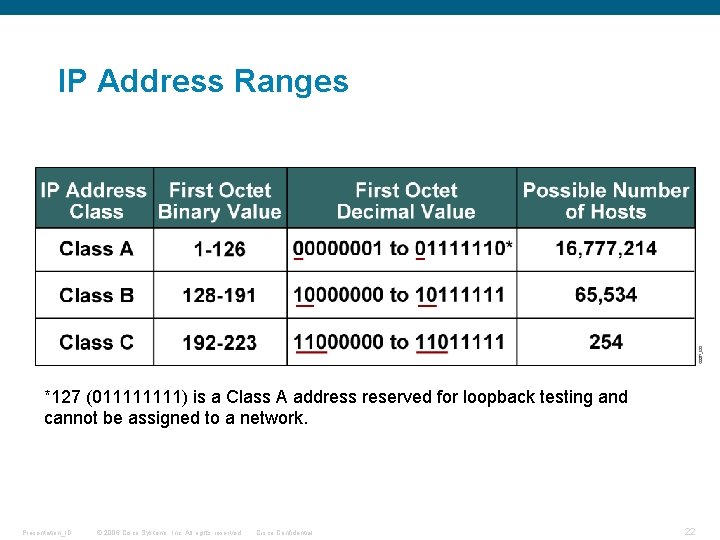
IP Address Ranges *127 (01111) is a Class A address reserved for loopback testing and cannot be assigned to a network. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 22
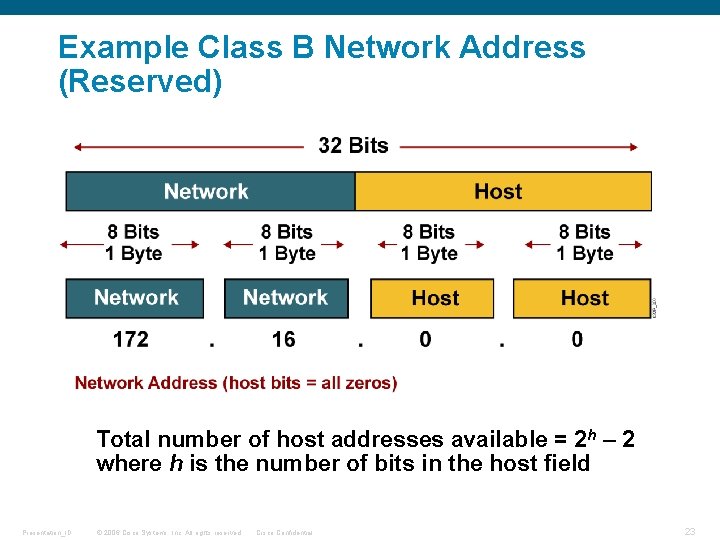
Example Class B Network Address (Reserved) Total number of host addresses available = 2 h – 2 where h is the number of bits in the host field Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 23
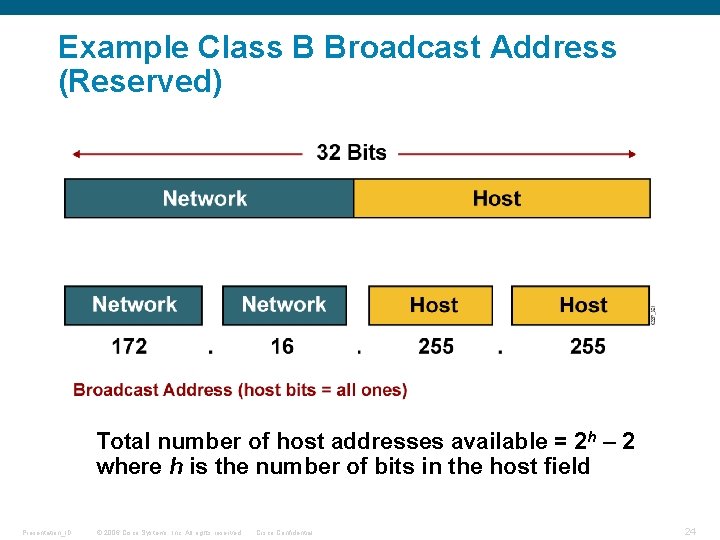
Example Class B Broadcast Address (Reserved) Total number of host addresses available = 2 h – 2 where h is the number of bits in the host field Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 24
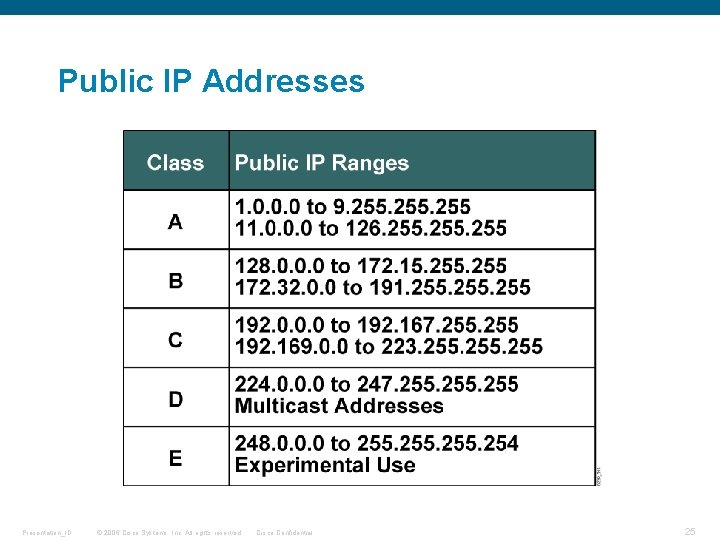
Public IP Addresses Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 25
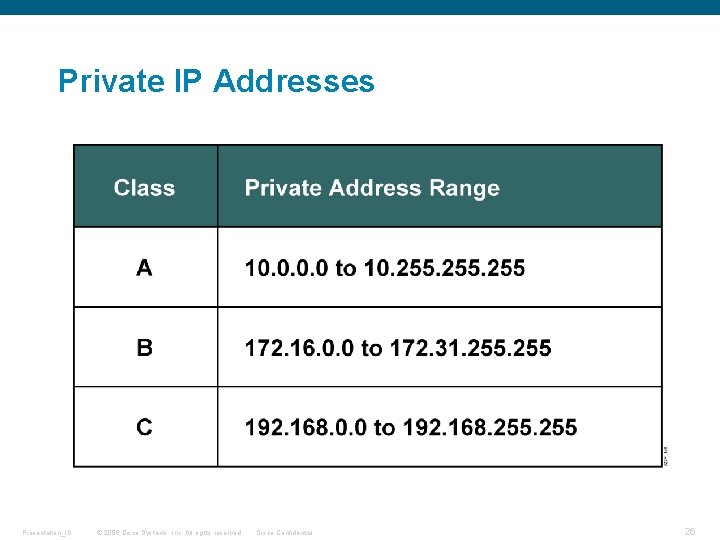
Private IP Addresses Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 26
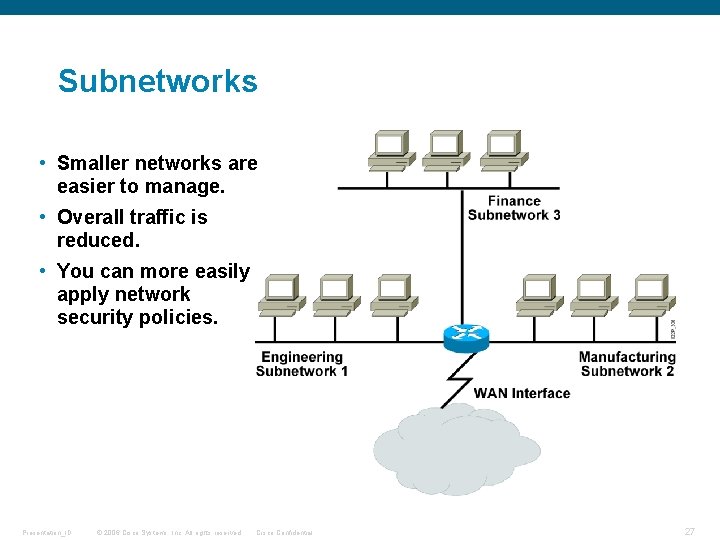
Subnetworks • Smaller networks are easier to manage. • Overall traffic is reduced. • You can more easily apply network security policies. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 27
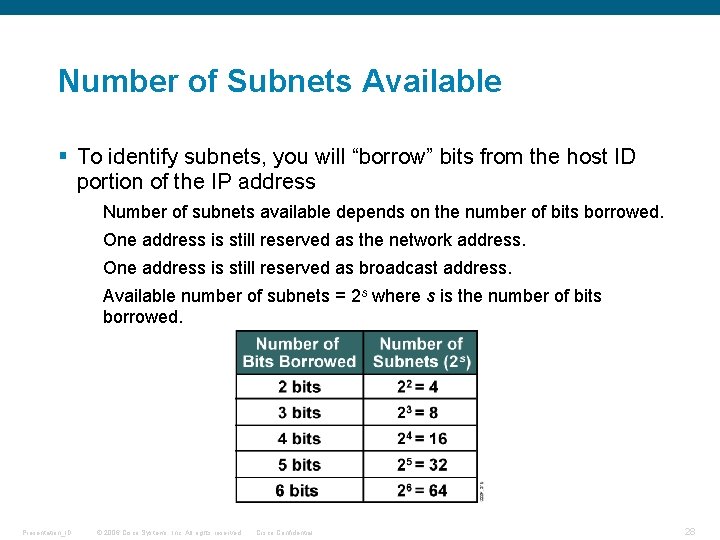
Number of Subnets Available § To identify subnets, you will “borrow” bits from the host ID portion of the IP address Number of subnets available depends on the number of bits borrowed. One address is still reserved as the network address. One address is still reserved as broadcast address. Available number of subnets = 2 s where s is the number of bits borrowed. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 28
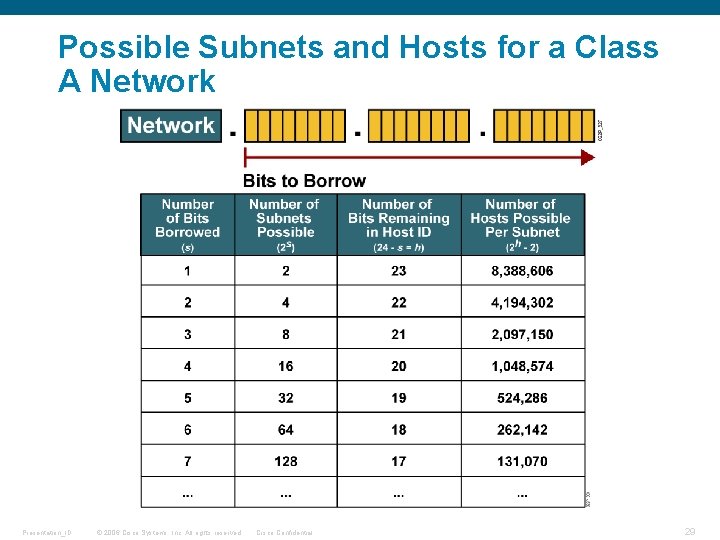
Possible Subnets and Hosts for a Class A Network Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 29
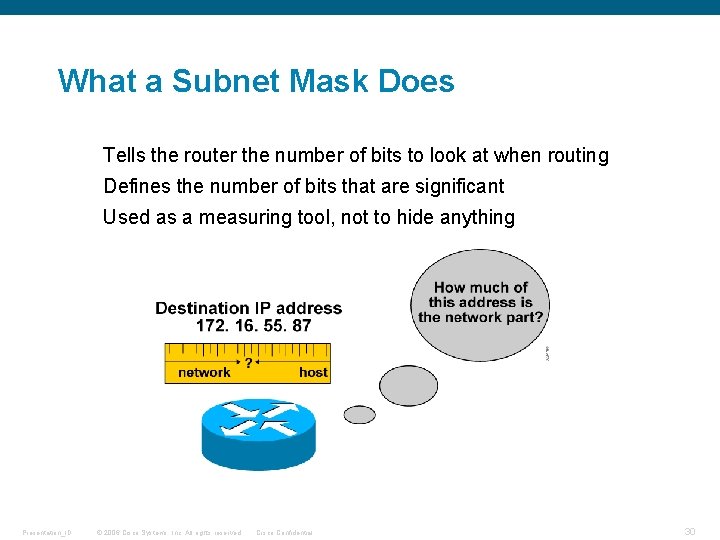
What a Subnet Mask Does Tells the router the number of bits to look at when routing Defines the number of bits that are significant Used as a measuring tool, not to hide anything Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 30
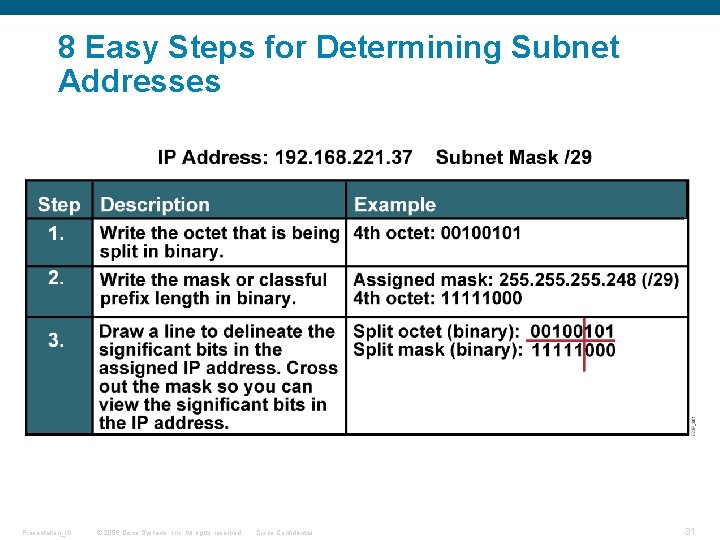
8 Easy Steps for Determining Subnet Addresses Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 31
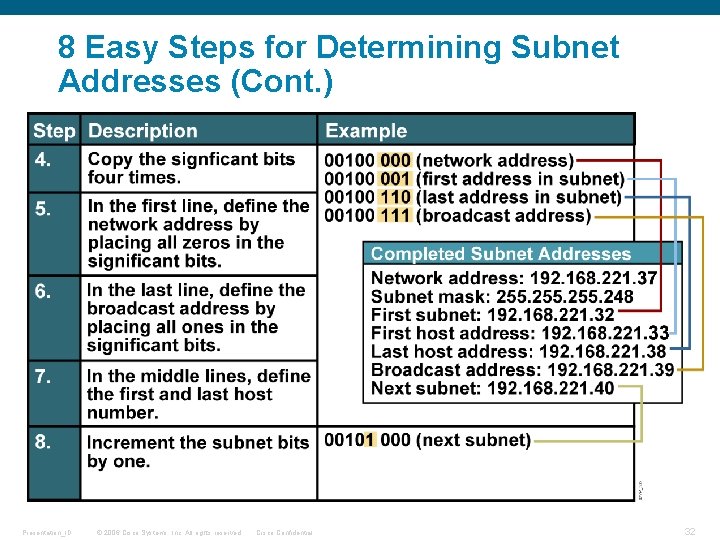
8 Easy Steps for Determining Subnet Addresses (Cont. ) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 32
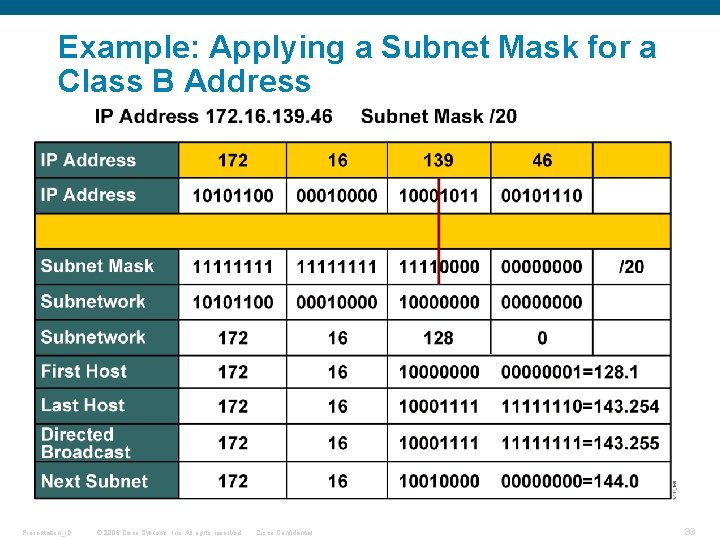
Example: Applying a Subnet Mask for a Class B Address Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 33
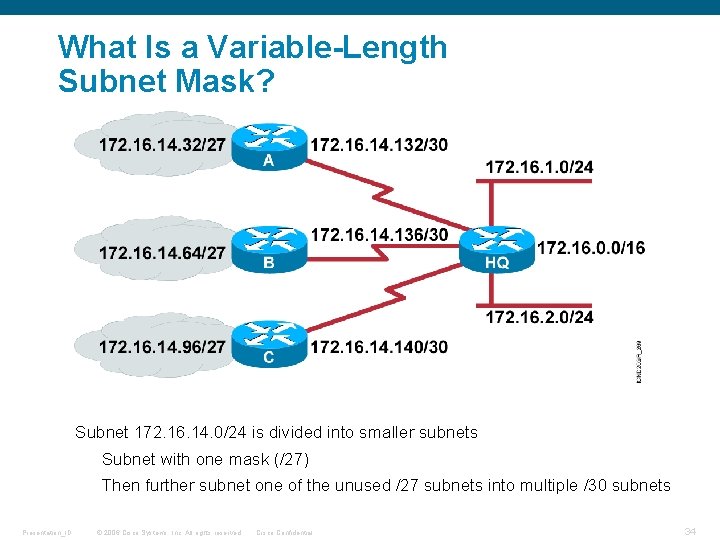
What Is a Variable-Length Subnet Mask? Subnet 172. 16. 14. 0/24 is divided into smaller subnets Subnet with one mask (/27) Then further subnet one of the unused /27 subnets into multiple /30 subnets Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 34
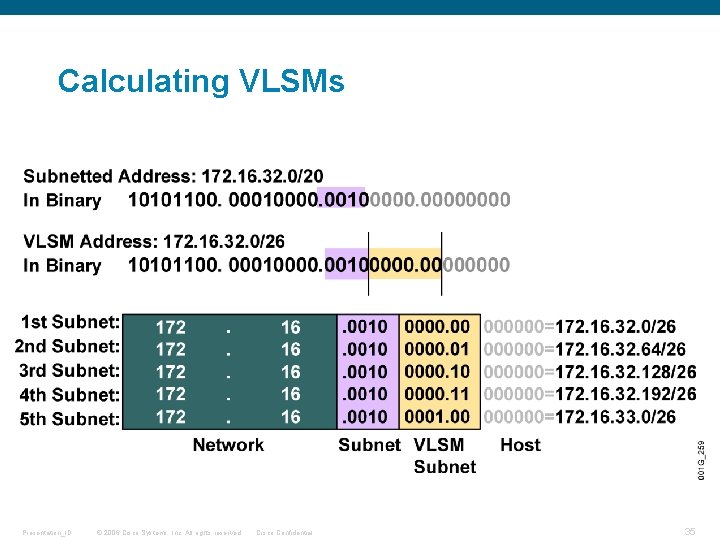
Calculating VLSMs Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 35
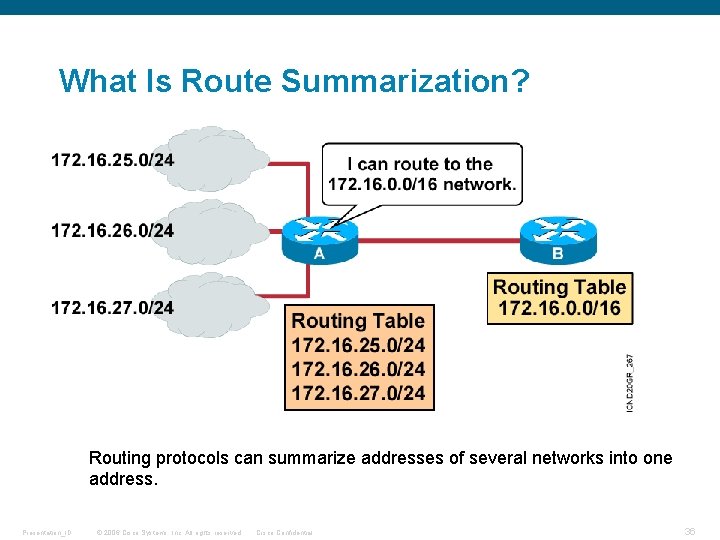
What Is Route Summarization? Routing protocols can summarize addresses of several networks into one address. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 36
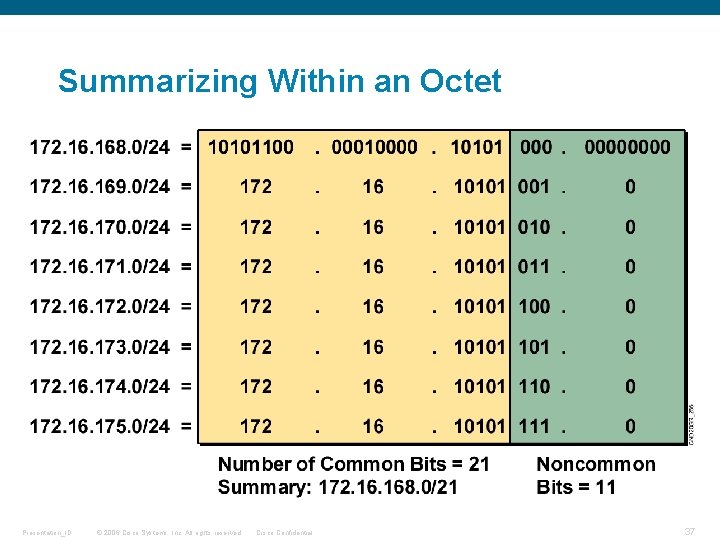
Summarizing Within an Octet Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 37
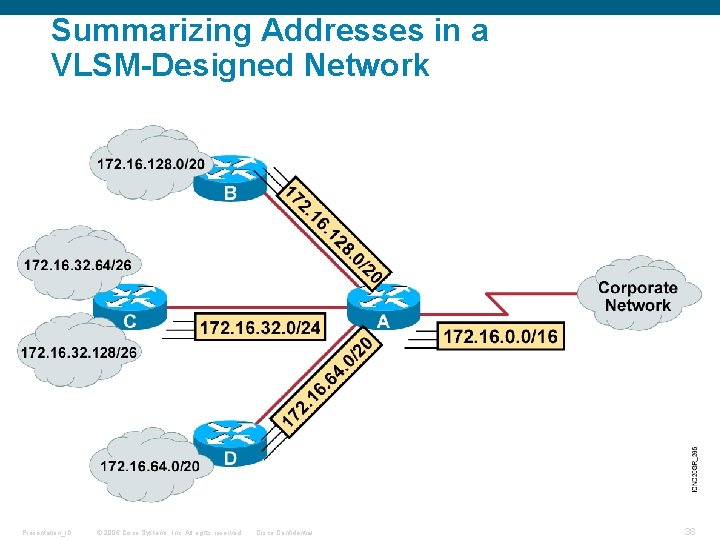
Summarizing Addresses in a VLSM-Designed Network Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 38
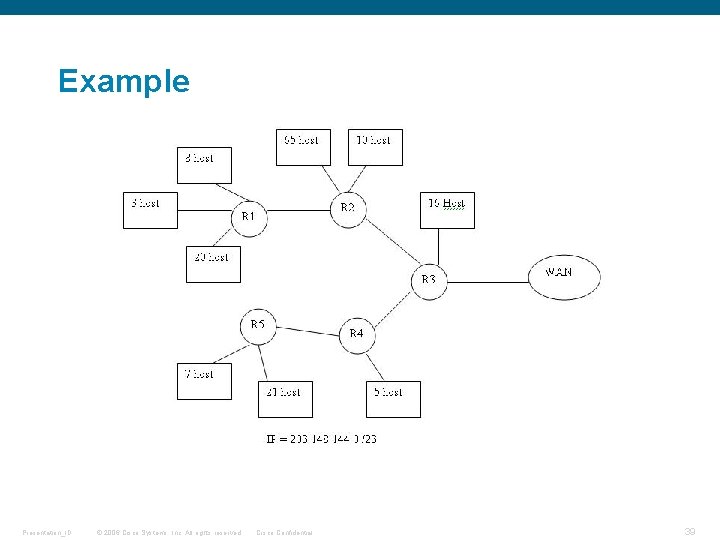
Example Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 39
Summary § Basic IP Addressing § Subnetting concepts § Calculate Subnets, host Addresses and broadcast id's § VLSM concepts and Route Summarization Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 40
Using Cisco IOS Command Line Interface (CLI) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 41
Agenda • Overview • Cisco IOS Software Features and Functions • Starting up Cisco Network Routers and Switches • Cisco IOS Command-Line Interface Functions • Entering the EXEC Modes • Entering Configuration Mode • Using the CLI to configure and test Routers and Switches • Summary Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 42
Cisco IOS Software CLI A common interface for managing Cisco devices. • Features to carry the chosen network protocols and functions • Connectivity for high-speed traffic between devices • Security to control access and prohibit unauthorized network use • Scalability to add interfaces and capability as needed for network growth • Reliability to ensure dependable access to networked resources Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 43
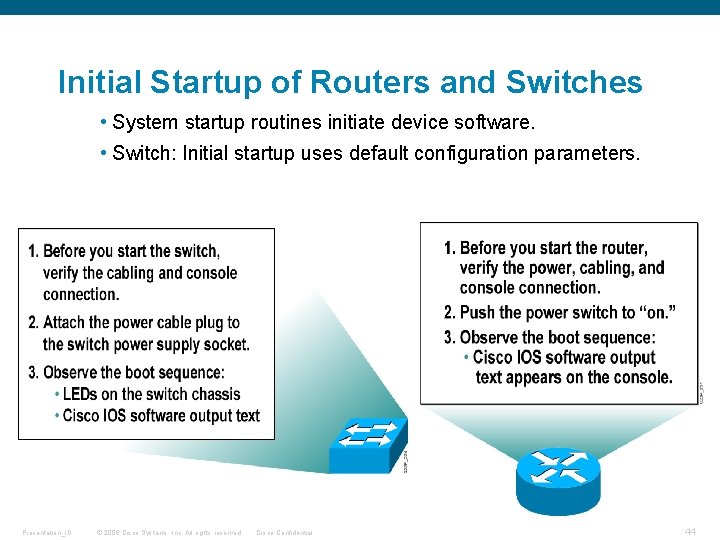
Initial Startup of Routers and Switches • System startup routines initiate device software. • Switch: Initial startup uses default configuration parameters. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 44
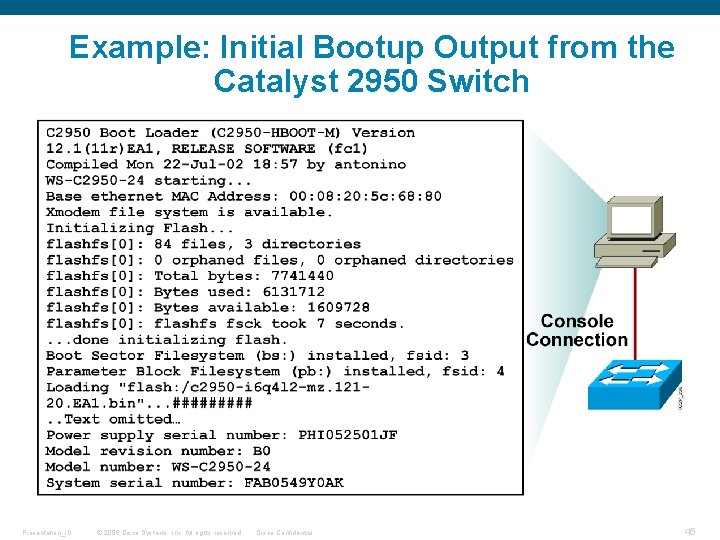
Example: Initial Bootup Output from the Catalyst 2950 Switch Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 45
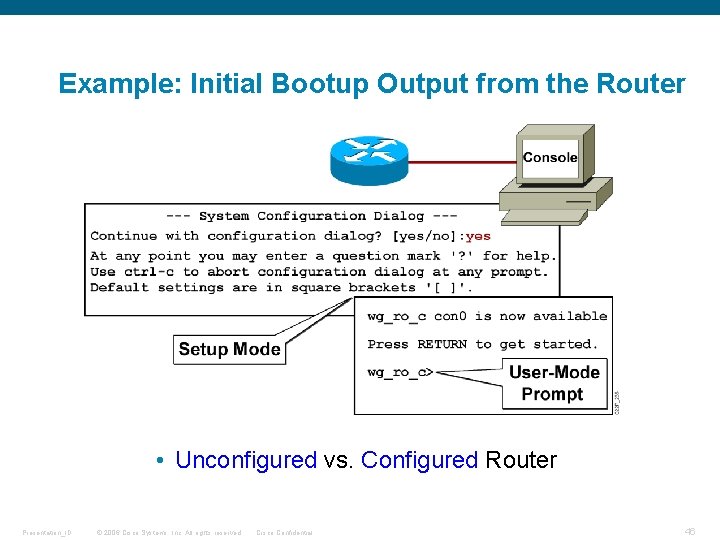
Example: Initial Bootup Output from the Router • Unconfigured vs. Configured Router Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 46
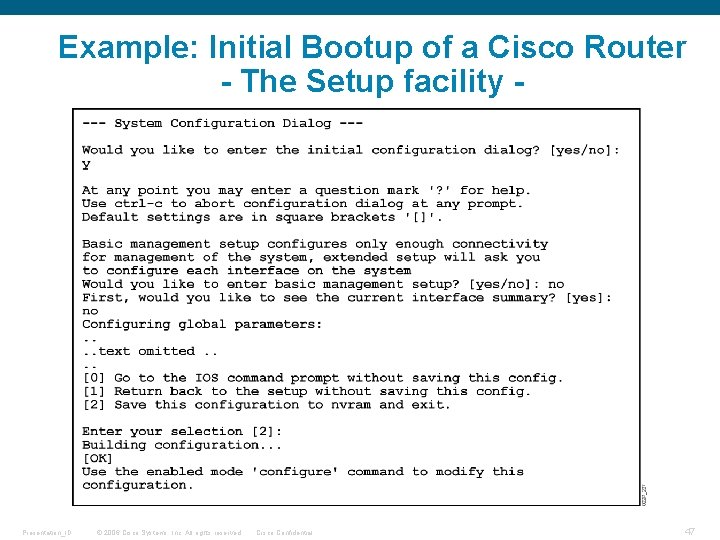
Example: Initial Bootup of a Cisco Router - The Setup facility - Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 47
Configuring Network Devices • Configuration sets up the device with the following: • Network policy of the functions required • Protocol addressing and parameter settings • Options for administration and management • A Catalyst switch memory has initial configuration with default settings. • A Cisco router will prompt for initial configuration if there is no configuration previously saved in memory. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 48
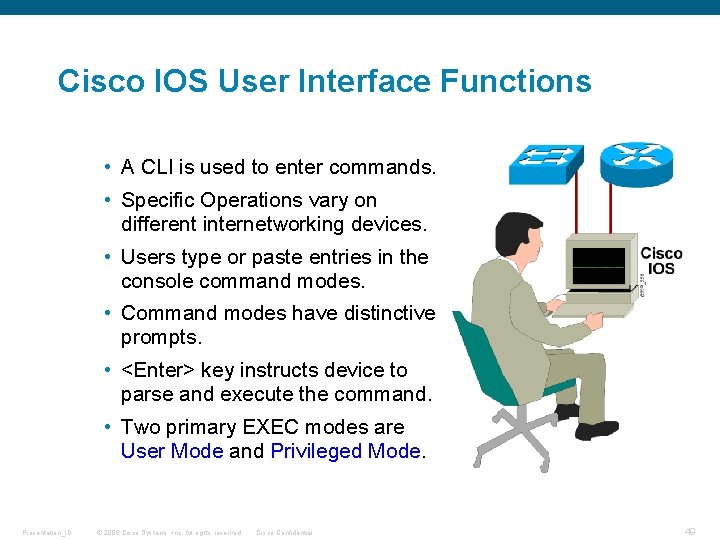
Cisco IOS User Interface Functions • A CLI is used to enter commands. • Specific Operations vary on different internetworking devices. • Users type or paste entries in the console command modes. • Command modes have distinctive prompts. • <Enter> key instructs device to parse and execute the command. • Two primary EXEC modes are User Mode and Privileged Mode. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 49
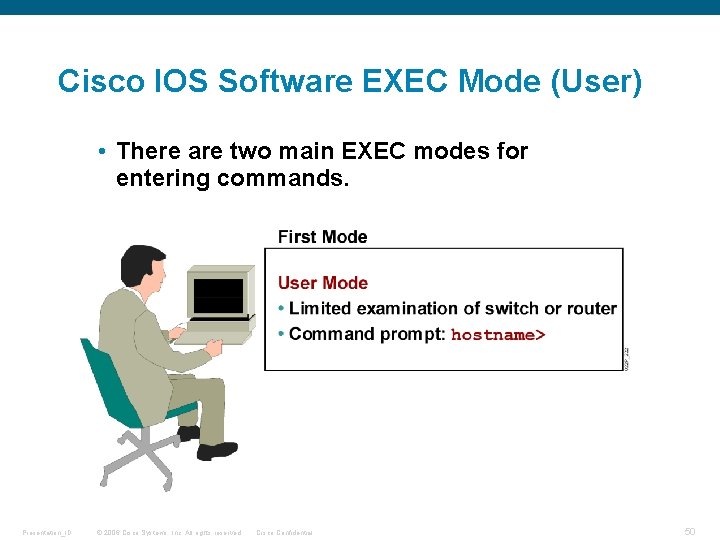
Cisco IOS Software EXEC Mode (User) • There are two main EXEC modes for entering commands. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 50
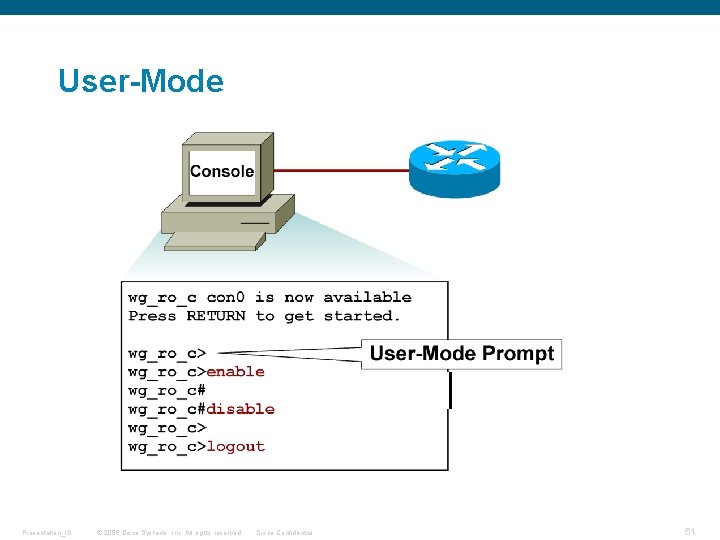
User-Mode Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 51
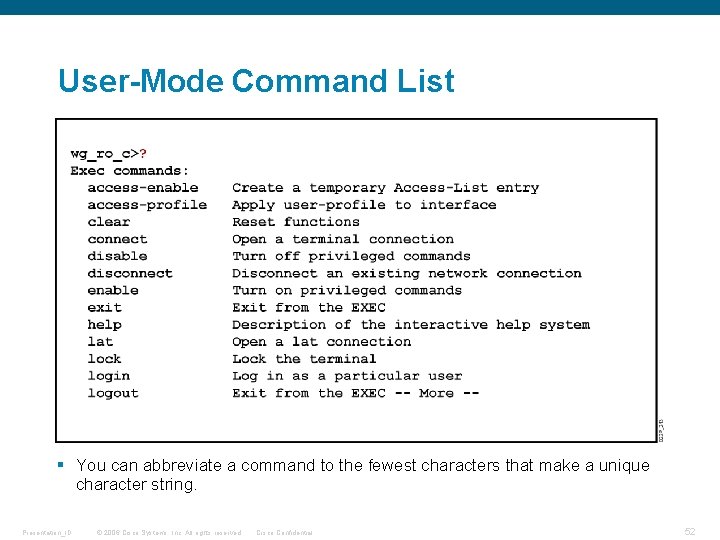
User-Mode Command List § You can abbreviate a command to the fewest characters that make a unique character string. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 52
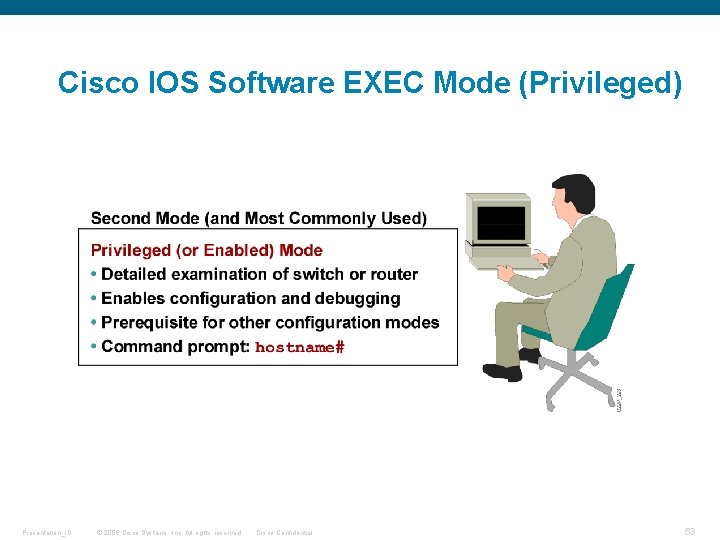
Cisco IOS Software EXEC Mode (Privileged) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 53
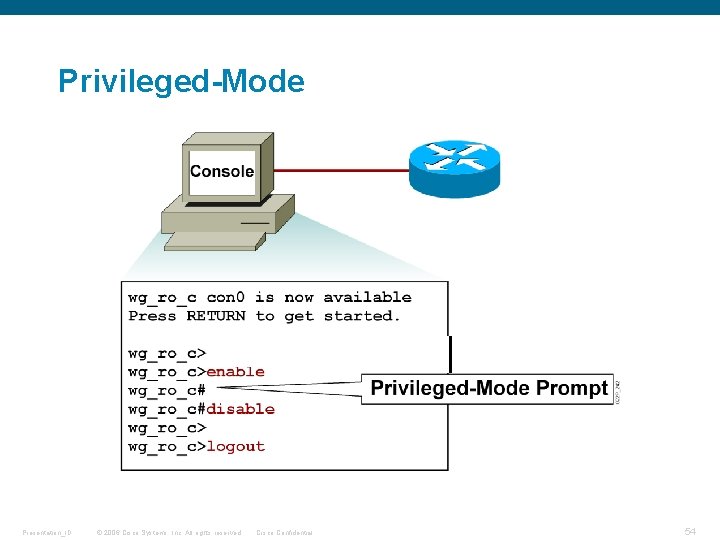
Privileged-Mode Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 54
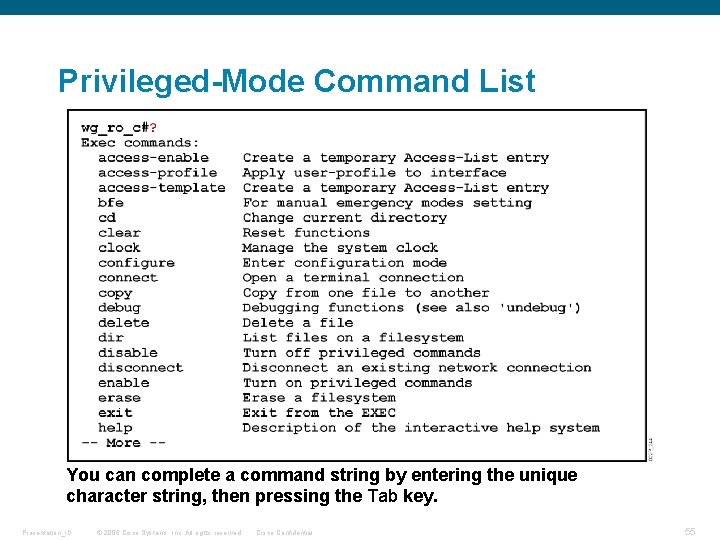
Privileged-Mode Command List You can complete a command string by entering the unique character string, then pressing the Tab key. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 55
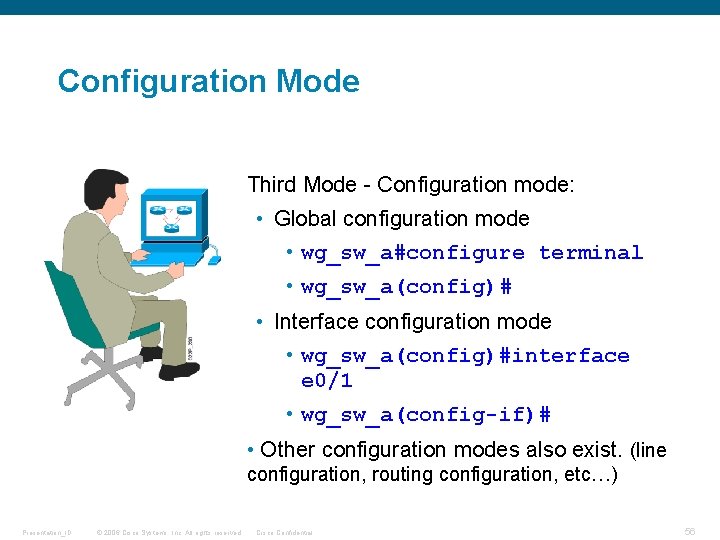
Configuration Mode Third Mode - Configuration mode: • Global configuration mode • wg_sw_a#configure terminal • wg_sw_a(config)# • Interface configuration mode • wg_sw_a(config)#interface e 0/1 • wg_sw_a(config-if)# • Other configuration modes also exist. (line configuration, routing configuration, etc…) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 56
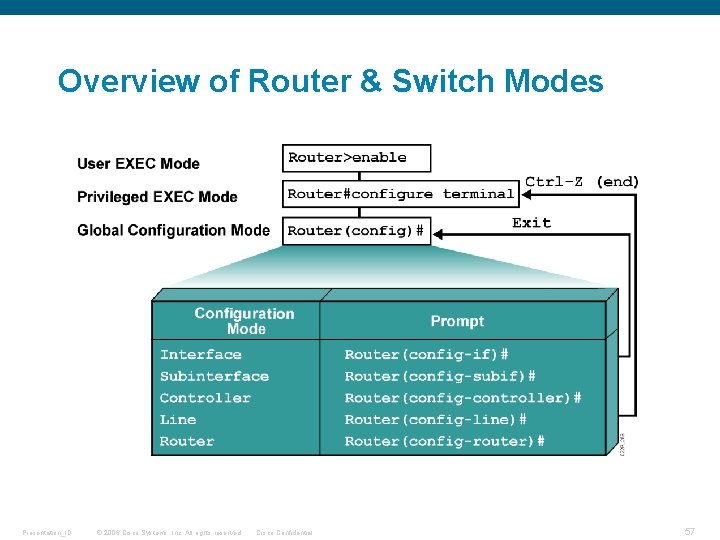
Overview of Router & Switch Modes Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 57
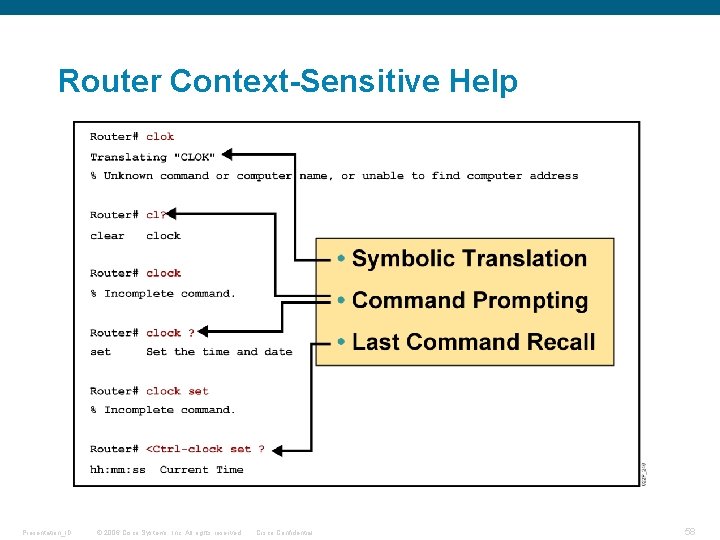
Router Context-Sensitive Help Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 58
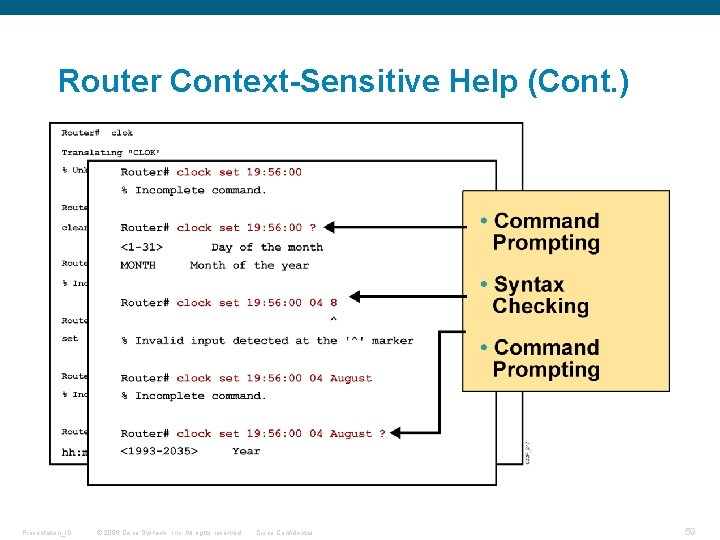
Router Context-Sensitive Help (Cont. ) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 59
Enhanced Editing Commands Router>Shape the future of internetworking by creating unpreced • Shape the future of internetworking by creating unprecedented value for customers, employees, and partners. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 60
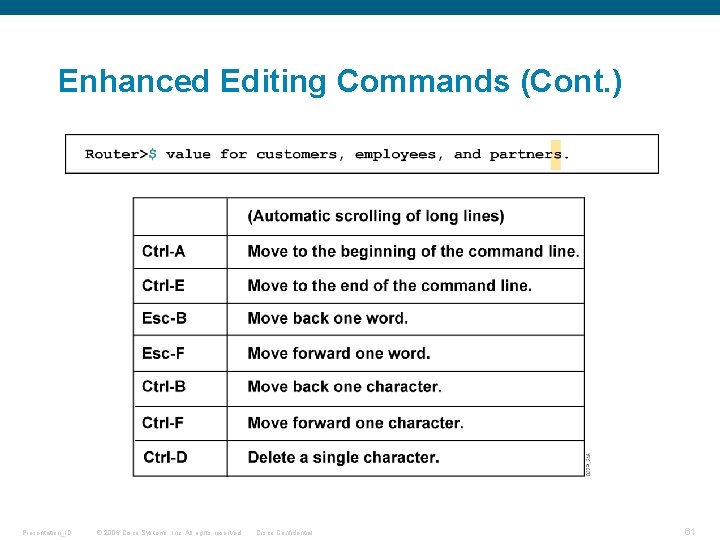
Enhanced Editing Commands (Cont. ) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 61
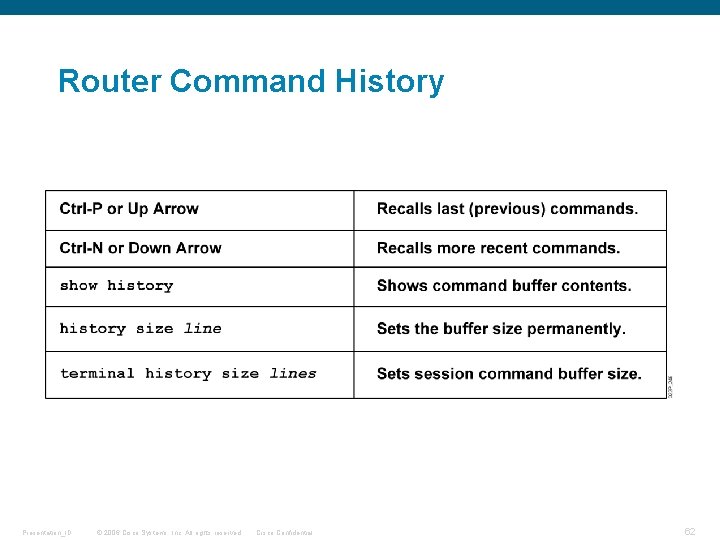
Router Command History Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 62
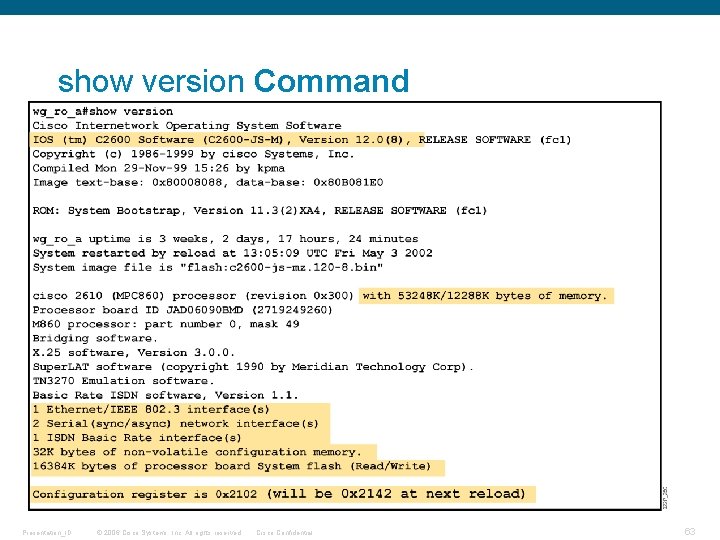
show version Command Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 63
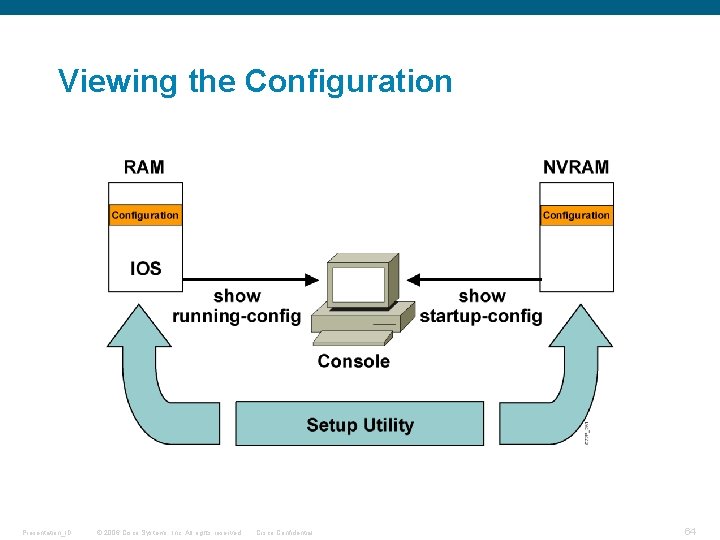
Viewing the Configuration Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 64
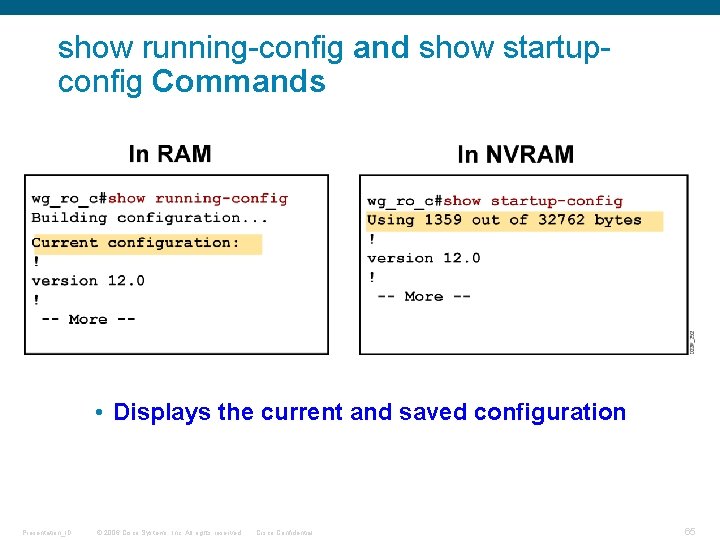
show running-config and show startupconfig Commands • Displays the current and saved configuration Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 65
Summary • The Cisco switch or router has considerable configuration and testing capabilities and can be configured using the Command Line Interface (CLI). • A switch or router can be configured from a local terminal connected to the console port or from a remote terminal connected via a modem connection to the auxiliary port. • The CLI is used by network administrators to monitor and to configure various Cisco IOS devices. CLI also offers a help facility to aid network administrators with the verification and configuration commands. • The CLI supports two EXEC modes: user and privileged. The privileged EXEC mode provides more functionality than the user EXEC mode. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 66
Summary (Cont. ) • From the privileged EXEC mode, the global configuration mode can be entered, providing access to other configuration modes such as the interface configuration mode or line configuration mode. • The CLI will be used to configure the router name, password, and other console commands. • Interface characteristics such as the IP address and bandwidth are configured using the interface configuration mode. • When the router configuration has been completed, it can be verified by using show commands. • Always remember to save your configuration! Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 67
Part 1 – Routing Protocols Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 68
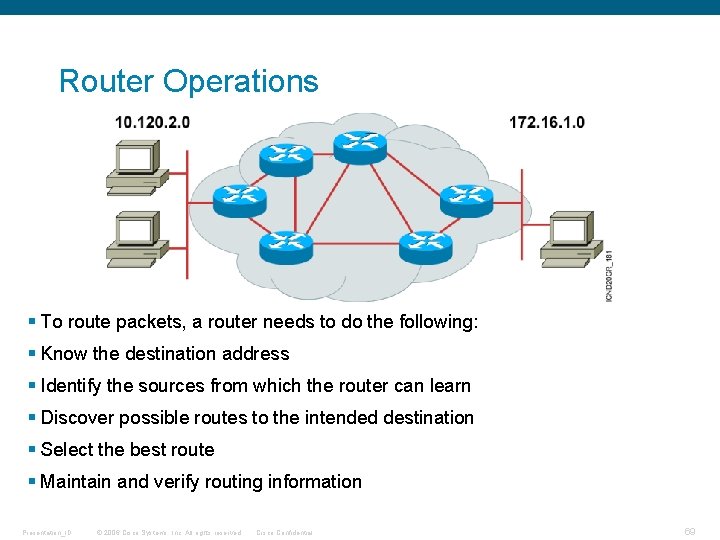
Router Operations § To route packets, a router needs to do the following: § Know the destination address § Identify the sources from which the router can learn § Discover possible routes to the intended destination § Select the best route § Maintain and verify routing information Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 69
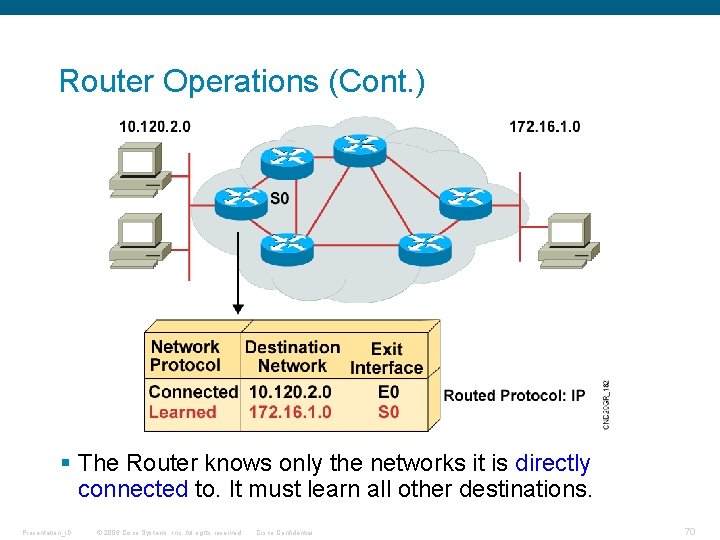
Router Operations (Cont. ) § The Router knows only the networks it is directly connected to. It must learn all other destinations. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 70
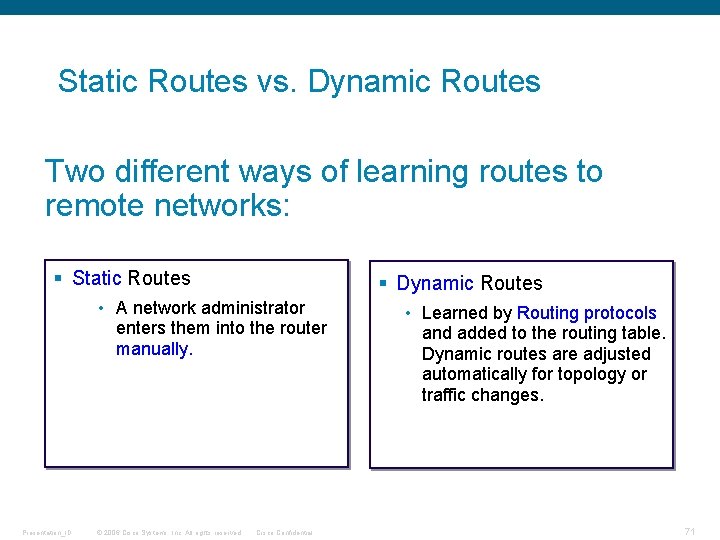
Static Routes vs. Dynamic Routes Two different ways of learning routes to remote networks: § Static Routes § Dynamic Routes • A network administrator enters them into the router manually. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential • Learned by Routing protocols and added to the routing table. Dynamic routes are adjusted automatically for topology or traffic changes. 71
![Static Route Configuration Router(config)#ip route network [mask] {address | interface}[distance] [permanent] § Defines a Static Route Configuration Router(config)#ip route network [mask] {address | interface}[distance] [permanent] § Defines a](http://slidetodoc.com/presentation_image_h2/f03a40dbd7f3b6823317d8d60e437535/image-72.jpg)
Static Route Configuration Router(config)#ip route network [mask] {address | interface}[distance] [permanent] § Defines a path to an IP destination network or subnet or host by specifying the next hop router interface IP address. § Address = IP address of the next hop router § Interface = outbound interface of the local router Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 72
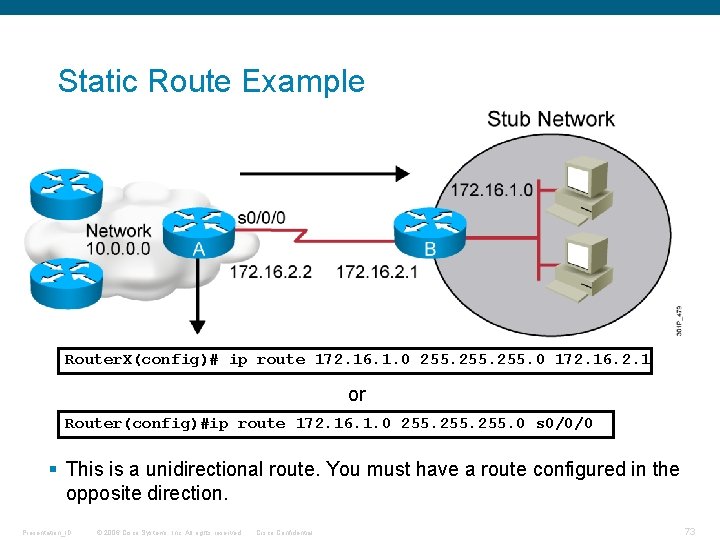
Static Route Example Router. X(config)# ip route 172. 16. 1. 0 255. 0 172. 16. 2. 1 or Router(config)#ip route 172. 16. 1. 0 255. 0 s 0/0/0 § This is a unidirectional route. You must have a route configured in the opposite direction. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 73
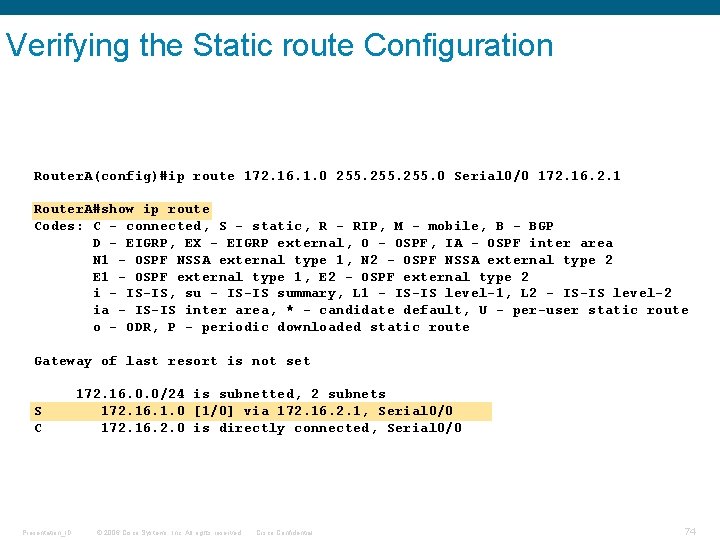
Verifying the Static route Configuration Router. A(config)#ip route 172. 16. 1. 0 255. 0 Serial 0/0 172. 16. 2. 1 Router. A#show ip route Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N 1 - OSPF NSSA external type 1, N 2 - OSPF NSSA external type 2 E 1 - OSPF external type 1, E 2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L 1 - IS-IS level-1, L 2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route Gateway of last resort is not set S C Presentation_ID 172. 16. 0. 0/24 is subnetted, 2 subnets 172. 16. 1. 0 [1/0] via 172. 16. 2. 1, Serial 0/0 172. 16. 2. 0 is directly connected, Serial 0/0 © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 74
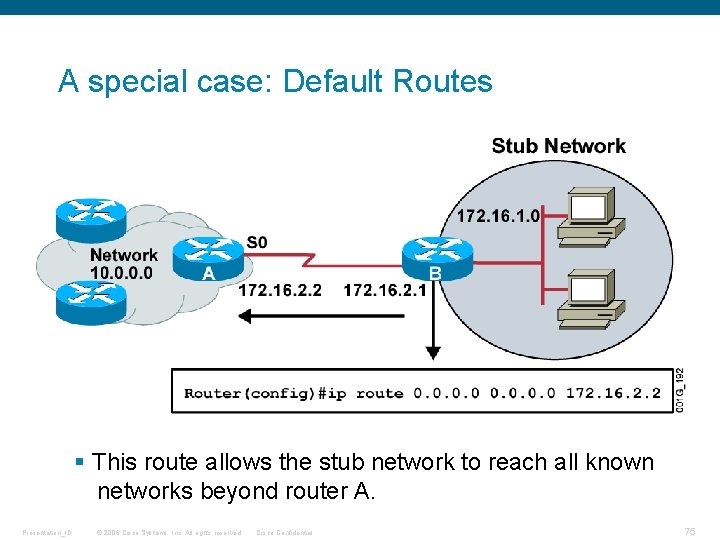
A special case: Default Routes § This route allows the stub network to reach all known networks beyond router A. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 75
Static Routes: Benefits and Disadvantages Benefits: - No overhead on the router CPU - No bandwidth usage between routers - Security and control Disadvantages: - Administrative burden. - Not practical in large networks. - By default it is not conveyed to other routers as part of an update process. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 76
![Dynamic Routing Configuration Router(config)#router protocol [keyword] Defines an IP routing protocol Router(config-router)#network-number • Mandatory Dynamic Routing Configuration Router(config)#router protocol [keyword] Defines an IP routing protocol Router(config-router)#network-number • Mandatory](http://slidetodoc.com/presentation_image_h2/f03a40dbd7f3b6823317d8d60e437535/image-77.jpg)
Dynamic Routing Configuration Router(config)#router protocol [keyword] Defines an IP routing protocol Router(config-router)#network-number • Mandatory configuration command for each IP routing process • Identifies the physically connected network to which routing updates are forwarded Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 77
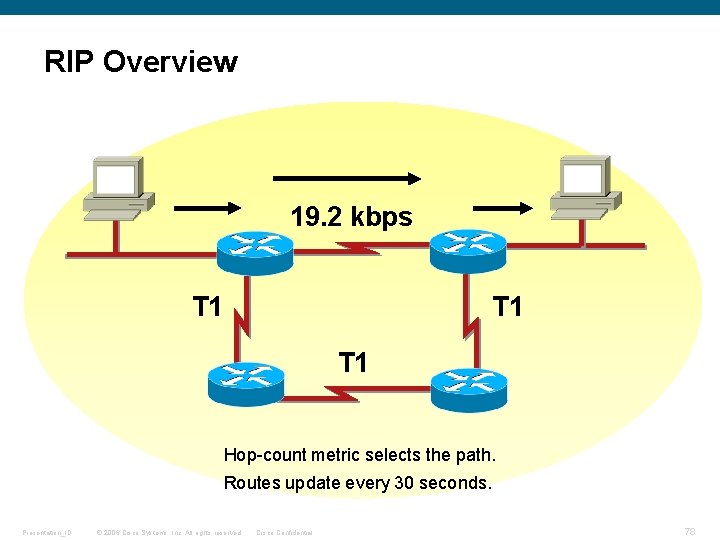
RIP Overview 19. 2 kbps T 1 T 1 Hop-count metric selects the path. Routes update every 30 seconds. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 78
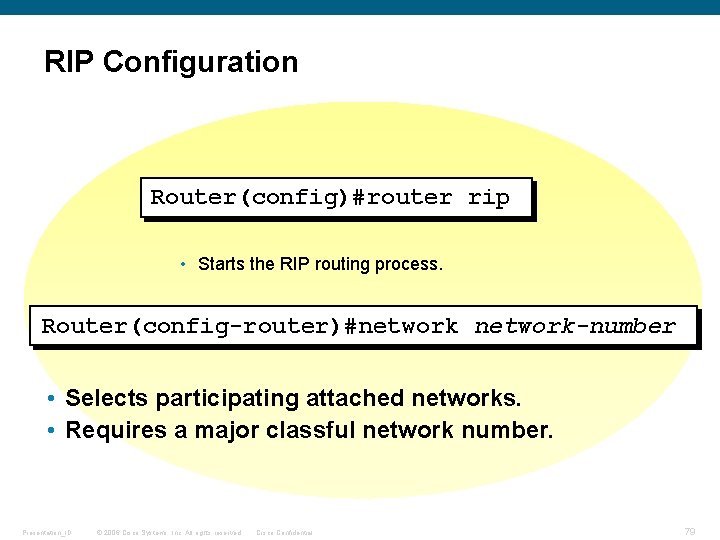
RIP Configuration Router(config)#router rip • Starts the RIP routing process. Router(config-router)#network-number • Selects participating attached networks. • Requires a major classful network number. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 79
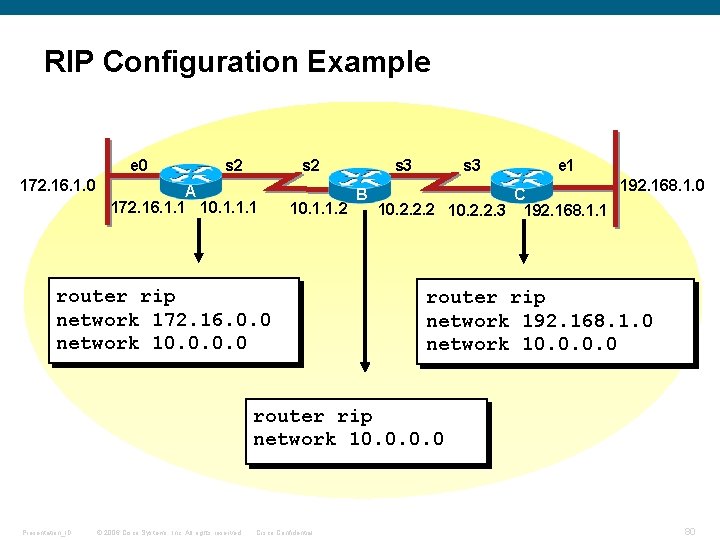
RIP Configuration Example e 0 172. 16. 1. 0 s 2 A 172. 16. 1. 1 10. 1. 1. 2 2. 3. 0. 0 router rip network 172. 16. 0. 0 network 10. 0 s 3 B s 3 e 1 C 10. 2. 2. 2 10. 2. 2. 3 192. 168. 1. 1 192. 168. 1. 0 2. 3. 0. 0 router rip network 192. 168. 1. 0 network 10. 0 router rip network 10. 0 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 80
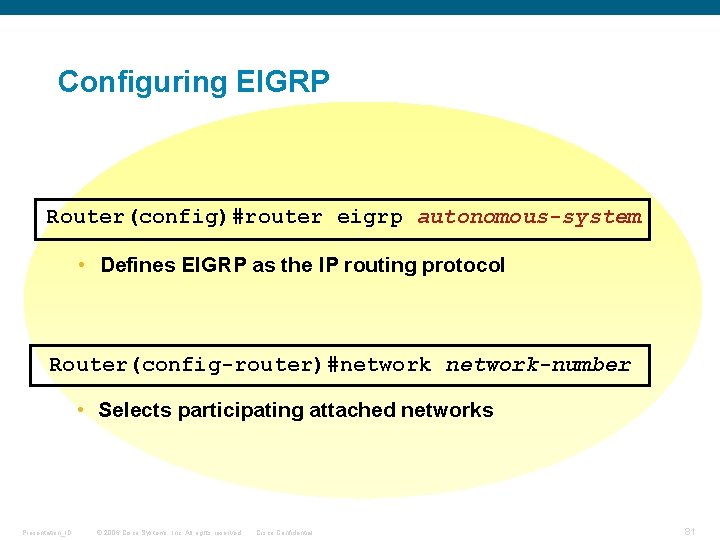
Configuring EIGRP Router(config)#router eigrp autonomous-system • Defines EIGRP as the IP routing protocol Router(config-router)#network-number • Selects participating attached networks Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 81
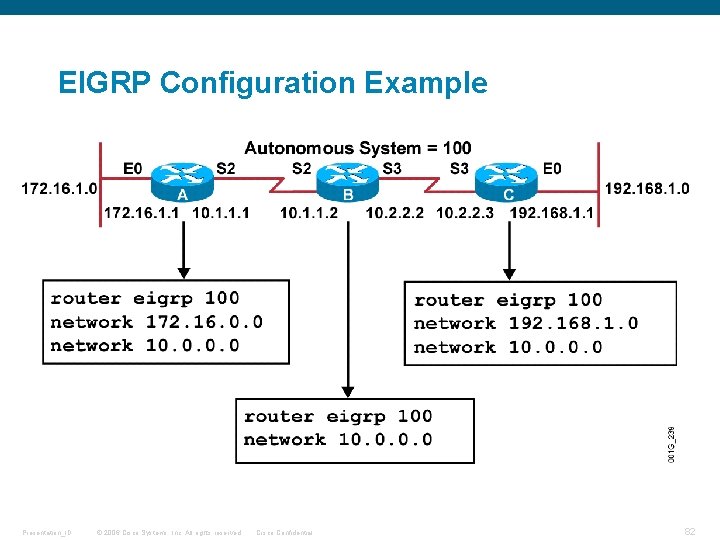
EIGRP Configuration Example Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 82
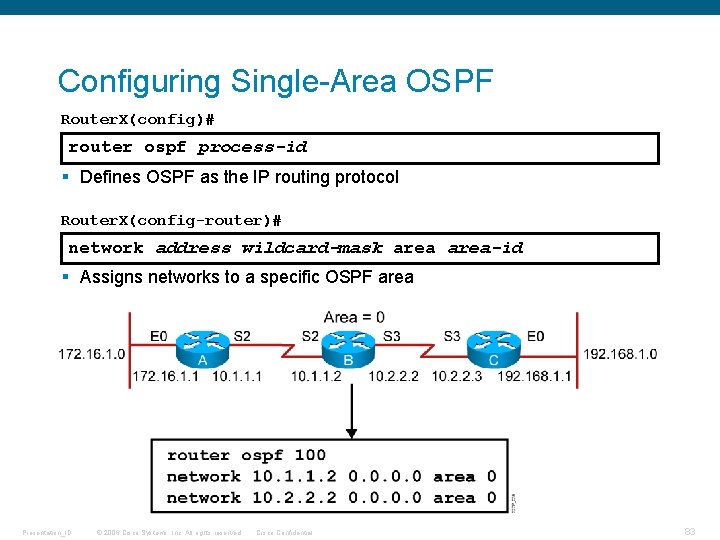
Configuring Single-Area OSPF Router. X(config)# router ospf process-id § Defines OSPF as the IP routing protocol Router. X(config-router)# network address wildcard-mask area-id § Assigns networks to a specific OSPF area Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 83
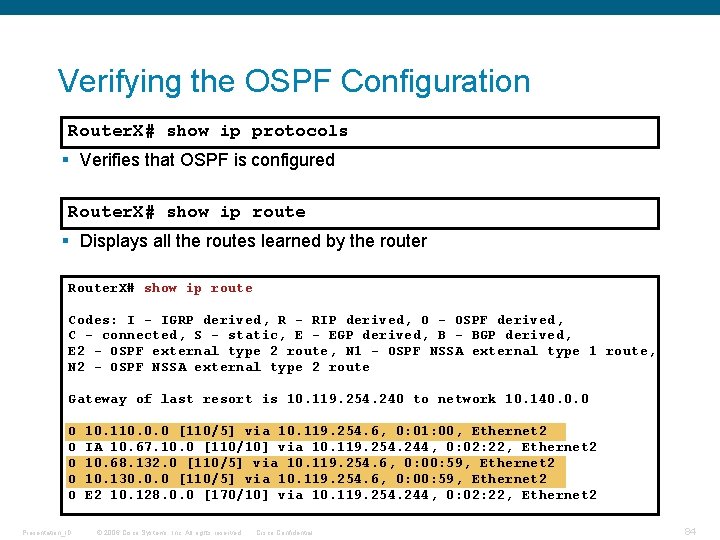
Verifying the OSPF Configuration Router. X# show ip protocols § Verifies that OSPF is configured Router. X# show ip route § Displays all the routes learned by the router Router. X# show ip route Codes: I - IGRP derived, R - RIP derived, O - OSPF derived, C - connected, S - static, E - EGP derived, B - BGP derived, E 2 - OSPF external type 2 route, N 1 - OSPF NSSA external type 1 route, N 2 - OSPF NSSA external type 2 route Gateway of last resort is 10. 119. 254. 240 to network 10. 140. 0. 0 O O O. Presentation_ID 10. 110. 0. 0 [110/5] via 10. 119. 254. 6, 0: 01: 00, Ethernet 2 IA 10. 67. 10. 0 [110/10] via 10. 119. 254. 244, 0: 02: 22, Ethernet 2 10. 68. 132. 0 [110/5] via 10. 119. 254. 6, 0: 00: 59, Ethernet 2 10. 130. 0. 0 [110/5] via 10. 119. 254. 6, 0: 00: 59, Ethernet 2 E 2 10. 128. 0. 0 [170/10] via 10. 119. 254. 244, 0: 02: 22, Ethernet 2. . © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 84
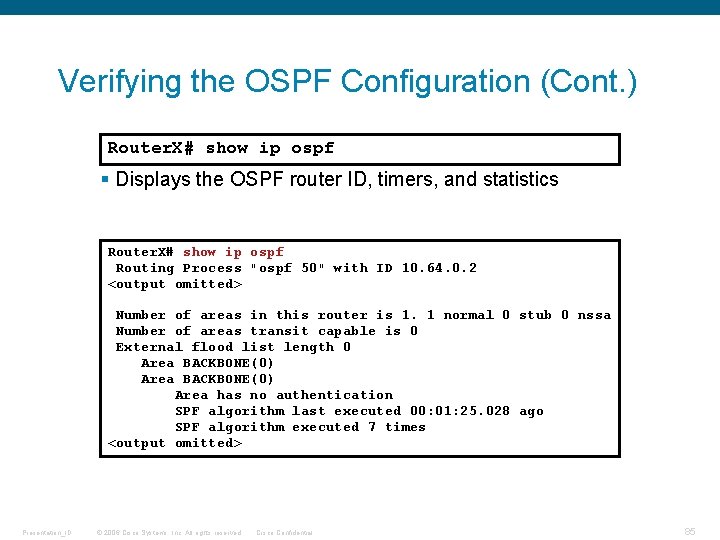
Verifying the OSPF Configuration (Cont. ) Router. X# show ip ospf § Displays the OSPF router ID, timers, and statistics Router. X# show ip ospf Routing Process "ospf 50" with ID 10. 64. 0. 2 <output omitted> Number of areas in this router is 1. 1 normal 0 stub 0 nssa Number of areas transit capable is 0 External flood list length 0 Area BACKBONE(0) Area has no authentication SPF algorithm last executed 00: 01: 25. 028 ago SPF algorithm executed 7 times <output omitted> Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 85
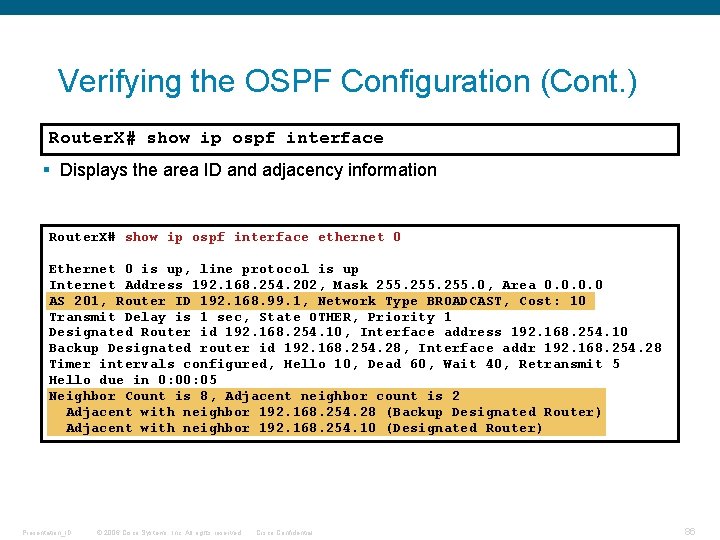
Verifying the OSPF Configuration (Cont. ) Router. X# show ip ospf interface § Displays the area ID and adjacency information Router. X# show ip ospf interface ethernet 0 Ethernet 0 is up, line protocol is up Internet Address 192. 168. 254. 202, Mask 255. 0, Area 0. 0 AS 201, Router ID 192. 168. 99. 1, Network Type BROADCAST, Cost: 10 Transmit Delay is 1 sec, State OTHER, Priority 1 Designated Router id 192. 168. 254. 10, Interface address 192. 168. 254. 10 Backup Designated router id 192. 168. 254. 28, Interface addr 192. 168. 254. 28 Timer intervals configured, Hello 10, Dead 60, Wait 40, Retransmit 5 Hello due in 0: 05 Neighbor Count is 8, Adjacent neighbor count is 2 Adjacent with neighbor 192. 168. 254. 28 (Backup Designated Router) Adjacent with neighbor 192. 168. 254. 10 (Designated Router) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 86
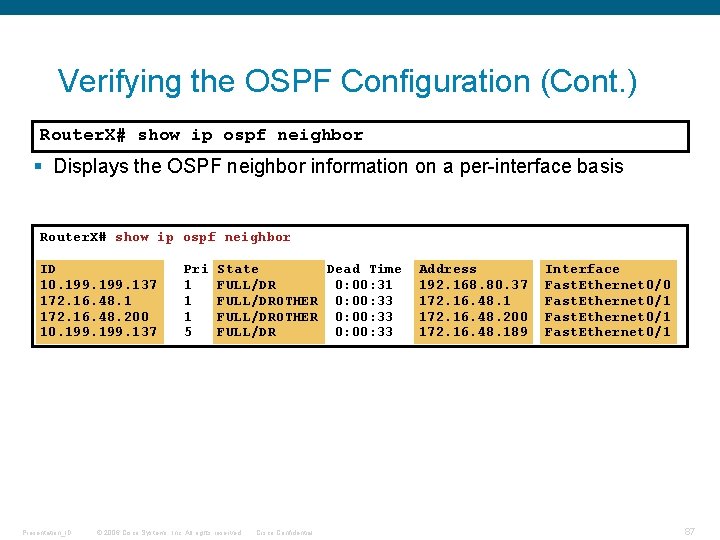
Verifying the OSPF Configuration (Cont. ) Router. X# show ip ospf neighbor § Displays the OSPF neighbor information on a per-interface basis Router. X# show ip ospf neighbor ID 10. 199. 137 172. 16. 48. 1 172. 16. 48. 200 10. 199. 137 Presentation_ID Pri 1 1 1 5 State Dead Time FULL/DR 0: 00: 31 FULL/DROTHER 0: 00: 33 FULL/DR 0: 00: 33 © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential Address 192. 168. 80. 37 172. 16. 48. 1 172. 16. 48. 200 172. 16. 48. 189 Interface Fast. Ethernet 0/0 Fast. Ethernet 0/1 87
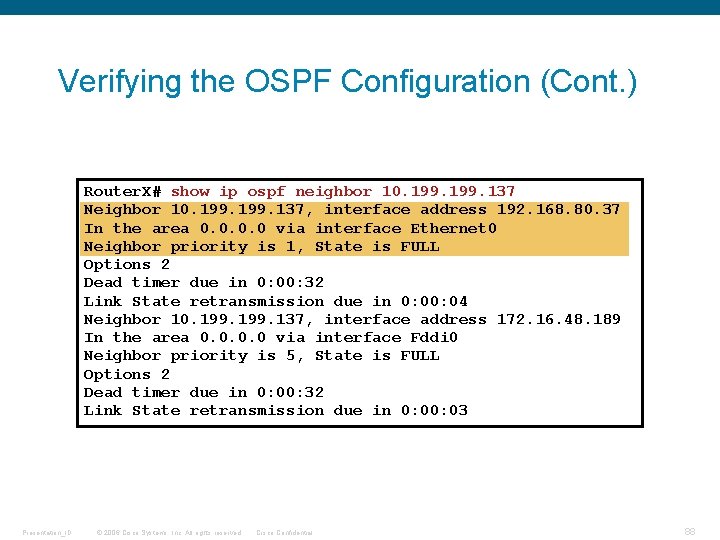
Verifying the OSPF Configuration (Cont. ) Router. X# show ip ospf neighbor 10. 199. 137 Neighbor 10. 199. 137, interface address 192. 168. 80. 37 In the area 0. 0 via interface Ethernet 0 Neighbor priority is 1, State is FULL Options 2 Dead timer due in 0: 00: 32 Link State retransmission due in 0: 04 Neighbor 10. 199. 137, interface address 172. 16. 48. 189 In the area 0. 0 via interface Fddi 0 Neighbor priority is 5, State is FULL Options 2 Dead timer due in 0: 00: 32 Link State retransmission due in 0: 03 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 88
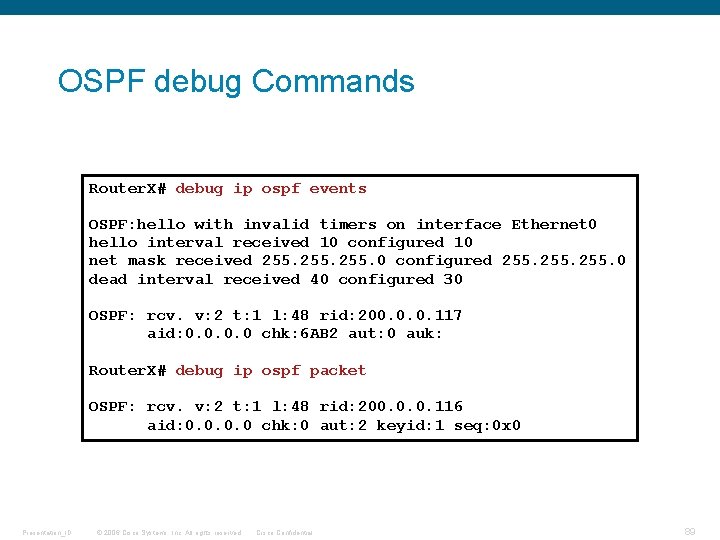
OSPF debug Commands Router. X# debug ip ospf events OSPF: hello with invalid timers on interface Ethernet 0 hello interval received 10 configured 10 net mask received 255. 0 configured 255. 0 dead interval received 40 configured 30 OSPF: rcv. v: 2 t: 1 l: 48 rid: 200. 0. 0. 117 aid: 0. 0 chk: 6 AB 2 aut: 0 auk: Router. X# debug ip ospf packet OSPF: rcv. v: 2 t: 1 l: 48 rid: 200. 0. 0. 116 aid: 0. 0 chk: 0 aut: 2 keyid: 1 seq: 0 x 0 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 89
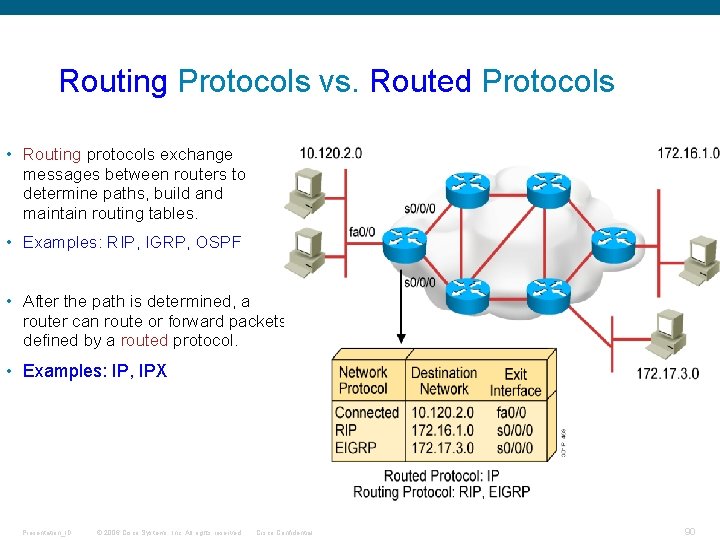
Routing Protocols vs. Routed Protocols • Routing protocols exchange messages between routers to determine paths, build and maintain routing tables. • Examples: RIP, IGRP, OSPF • After the path is determined, a router can route or forward packets defined by a routed protocol. • Examples: IP, IPX Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 90
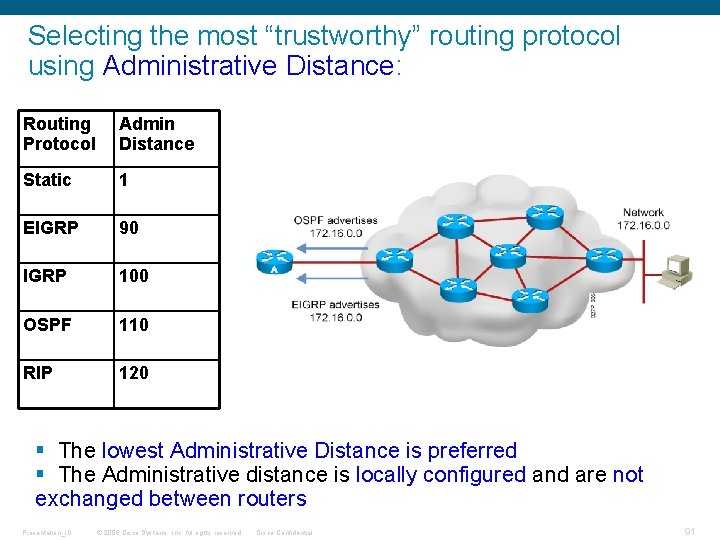
Selecting the most “trustworthy” routing protocol using Administrative Distance: Routing Protocol Admin Distance Static 1 EIGRP 90 IGRP 100 OSPF 110 RIP 120 § The lowest Administrative Distance is preferred § The Administrative distance is locally configured and are not exchanged between routers Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 91
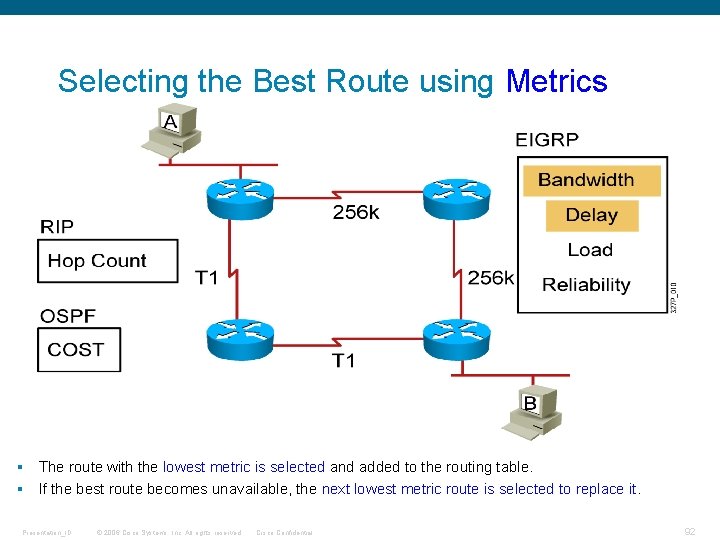
Selecting the Best Route using Metrics § The route with the lowest metric is selected and added to the routing table. § If the best route becomes unavailable, the next lowest metric route is selected to replace it. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 92
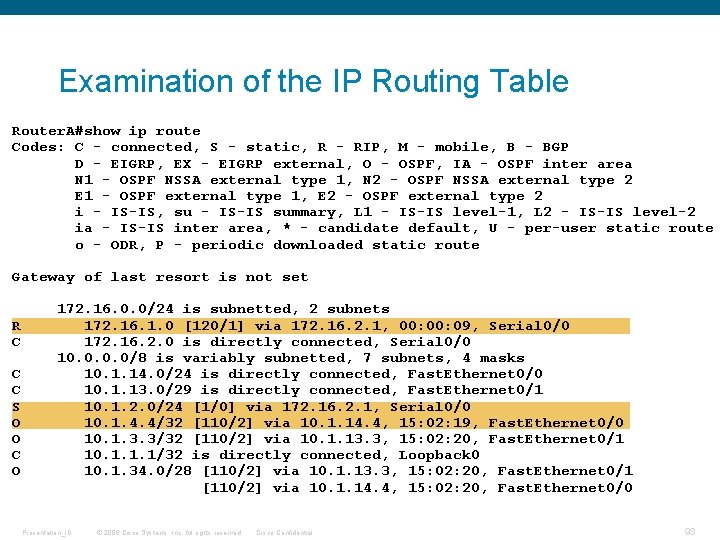
Examination of the IP Routing Table Router. A#show ip route Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N 1 - OSPF NSSA external type 1, N 2 - OSPF NSSA external type 2 E 1 - OSPF external type 1, E 2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L 1 - IS-IS level-1, L 2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route Gateway of last resort is not set R C C C S O O C O 172. 16. 0. 0/24 is subnetted, 2 subnets 172. 16. 1. 0 [120/1] via 172. 16. 2. 1, 00: 09, Serial 0/0 172. 16. 2. 0 is directly connected, Serial 0/0 10. 0/8 is variably subnetted, 7 subnets, 4 masks 10. 1. 14. 0/24 is directly connected, Fast. Ethernet 0/0 10. 1. 13. 0/29 is directly connected, Fast. Ethernet 0/1 10. 1. 2. 0/24 [1/0] via 172. 16. 2. 1, Serial 0/0 10. 1. 4. 4/32 [110/2] via 10. 1. 14. 4, 15: 02: 19, Fast. Ethernet 0/0 10. 1. 3. 3/32 [110/2] via 10. 1. 13. 3, 15: 02: 20, Fast. Ethernet 0/1 10. 1. 1. 1/32 is directly connected, Loopback 0 10. 1. 34. 0/28 [110/2] via 10. 1. 13. 3, 15: 02: 20, Fast. Ethernet 0/1 [110/2] via 10. 1. 14. 4, 15: 02: 20, Fast. Ethernet 0/0 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 93
Classful Routing Overview § Classful routing protocols do not include the subnet mask with the route advertisement. § Within the same network, consistency of the subnet masks is assumed (all subnet masks must be off the same length). § Summary routes are exchanged between foreign networks. § Examples of classful routing protocols: § RIP version 1 (RIPv 1) § IGRP Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 94
Classless Routing Overview § Classless routing protocols include the subnet mask with the route advertisement. § Classless routing protocols support variable-length subnet mask (VLSM). § Summary routes can be manually controlled within the network. § These are examples of classless routing protocols: § RIP version 2 (RIPv 2) § EIGRP § OSPF § IS-IS Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 95
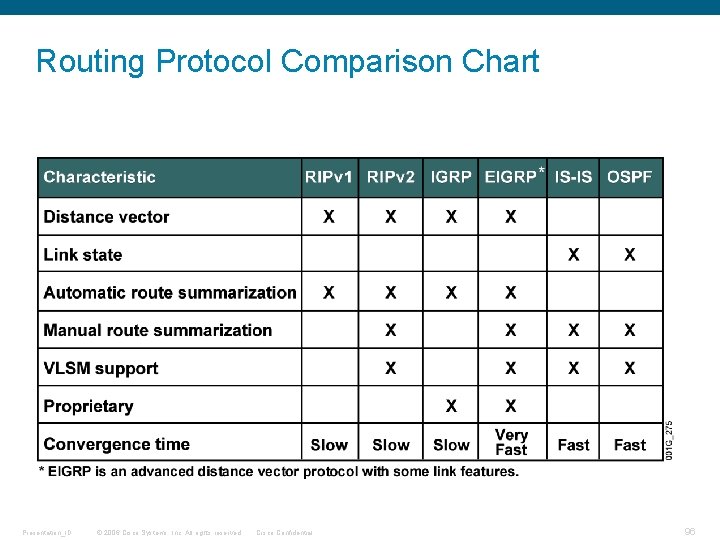
Routing Protocol Comparison Chart Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 96
Cisco LAN Switching Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 97
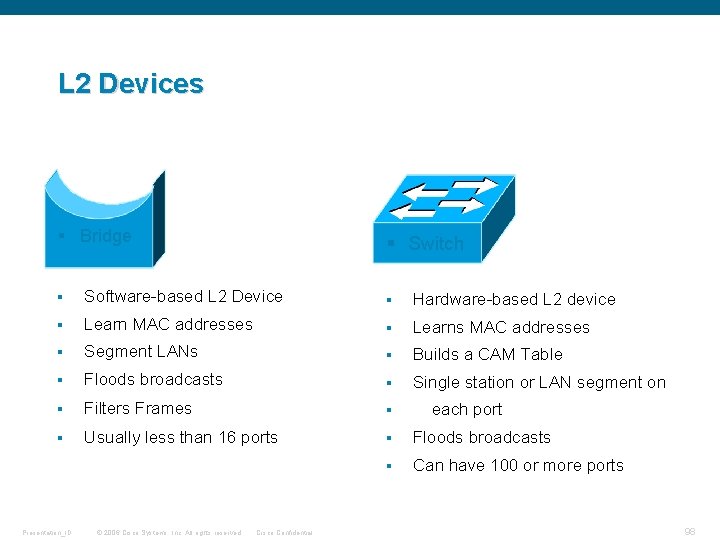
L 2 Devices § Bridge § Switch § Software-based L 2 Device § Hardware-based L 2 device § Learn MAC addresses § Learns MAC addresses § Segment LANs § Builds a CAM Table § Floods broadcasts § Single station or LAN segment on § Filters Frames § § Usually less than 16 ports § Floods broadcasts § Can have 100 or more ports Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential each port 98
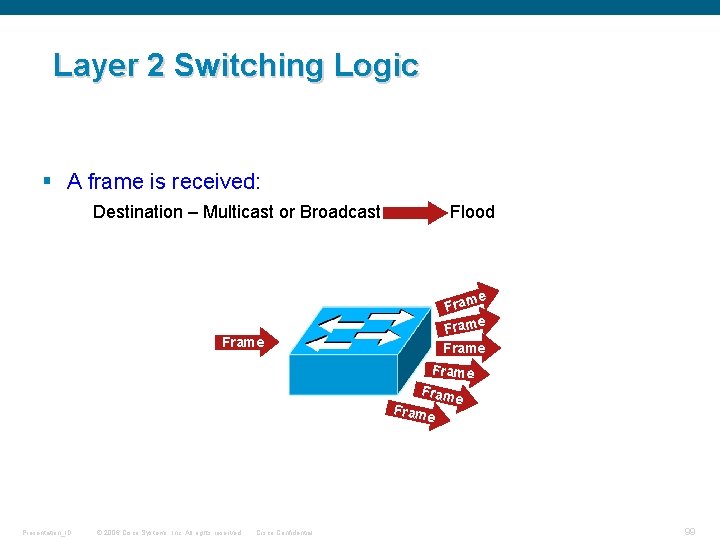
Layer 2 Switching Logic § A frame is received: Destination – Multicast or Broadcast Flood e Frame Fram e Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential e 99
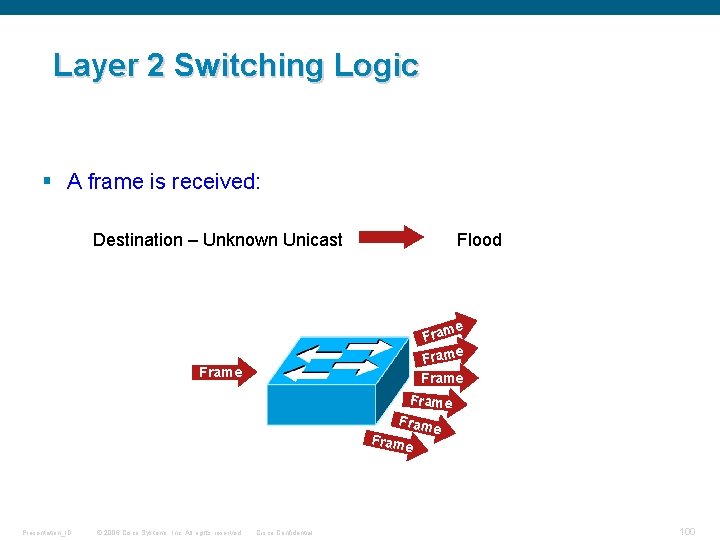
Layer 2 Switching Logic § A frame is received: Destination – Unknown Unicast Flood e Frame Fram e Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 100
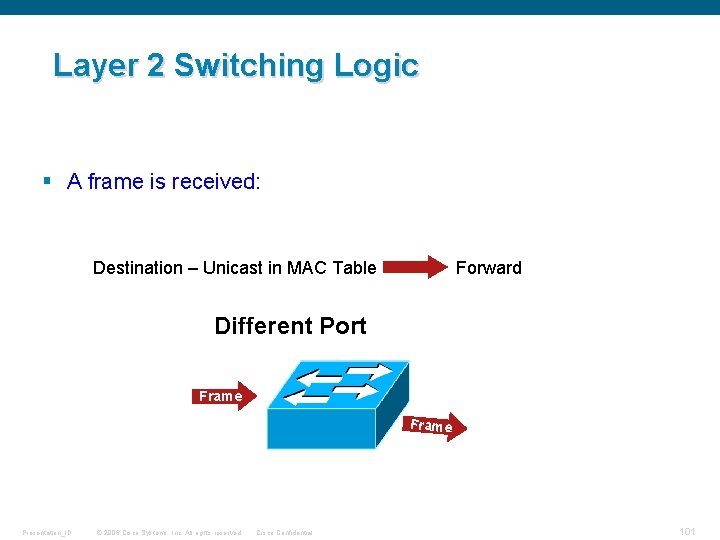
Layer 2 Switching Logic § A frame is received: Destination – Unicast in MAC Table Forward Different Port Frame Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 101
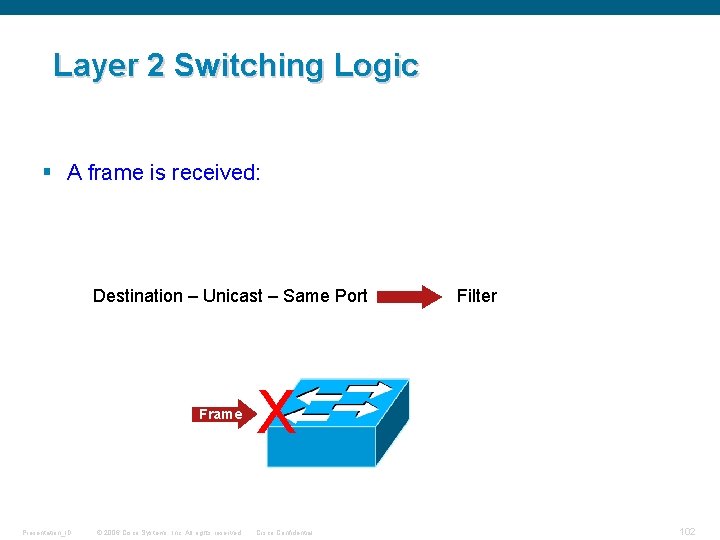
Layer 2 Switching Logic § A frame is received: Destination – Unicast – Same Port Frame Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Filter X Cisco Confidential 102
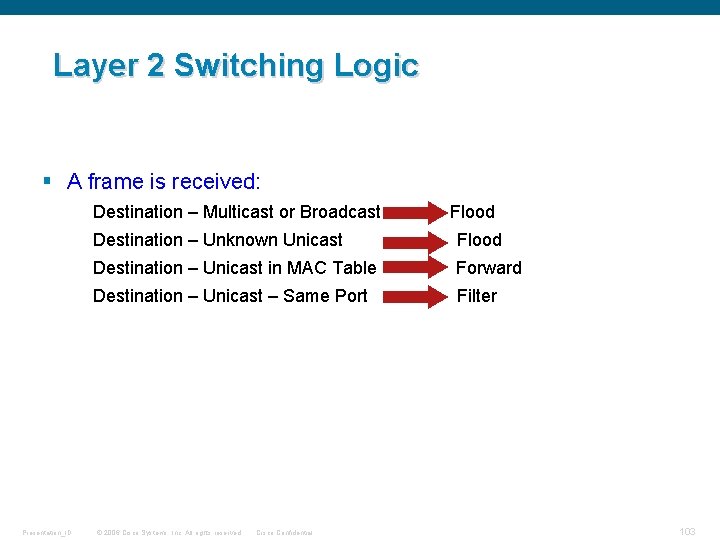
Layer 2 Switching Logic § A frame is received: Destination – Multicast or Broadcast Presentation_ID Flood Destination – Unknown Unicast Flood Destination – Unicast in MAC Table Forward Destination – Unicast – Same Port Filter © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 103
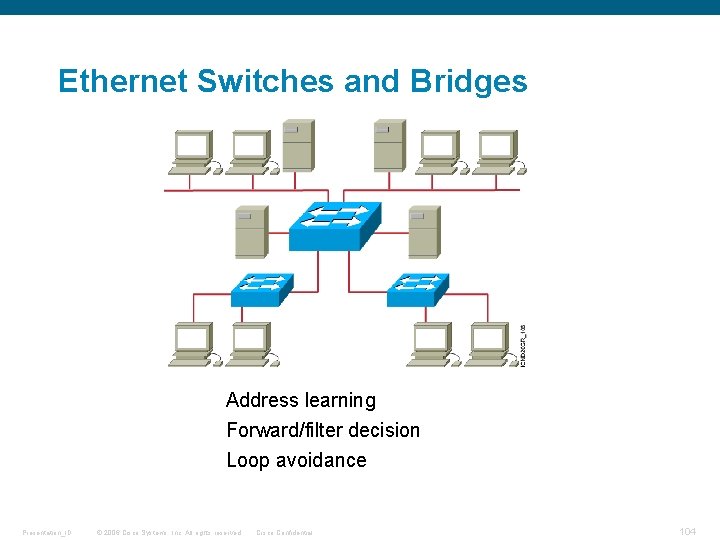
Ethernet Switches and Bridges Address learning Forward/filter decision Loop avoidance Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 104
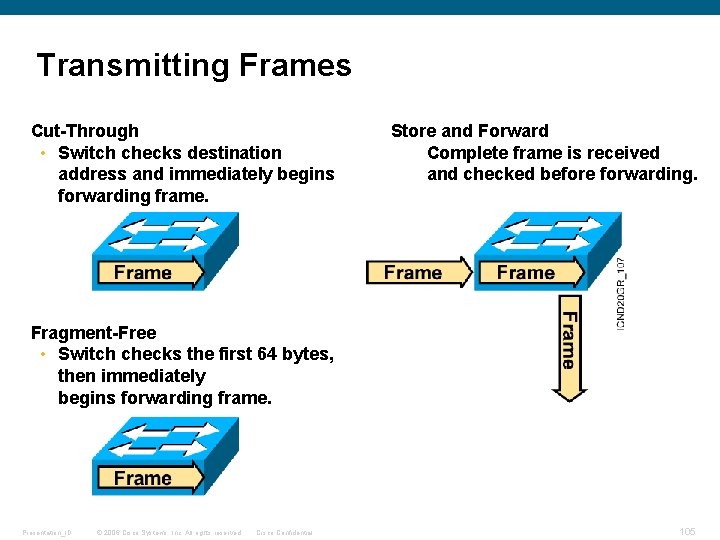
Transmitting Frames Cut-Through • Switch checks destination address and immediately begins forwarding frame. Store and Forward Complete frame is received and checked before forwarding. Fragment-Free • Switch checks the first 64 bytes, then immediately begins forwarding frame. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 105
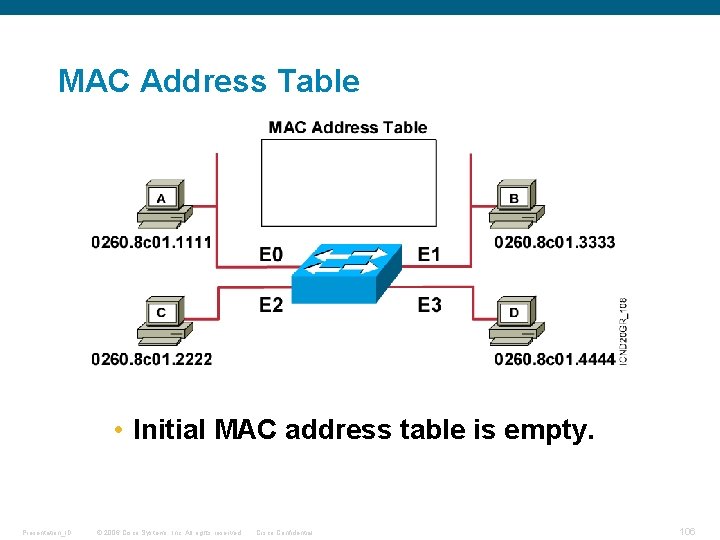
MAC Address Table • Initial MAC address table is empty. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 106
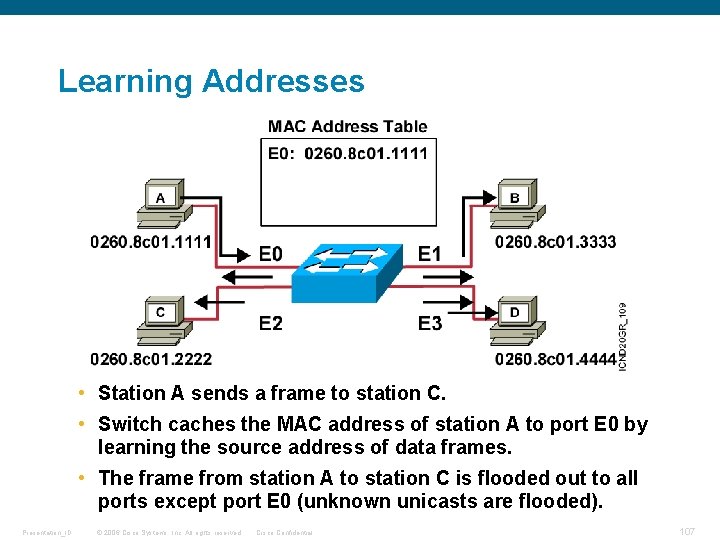
Learning Addresses • Station A sends a frame to station C. • Switch caches the MAC address of station A to port E 0 by learning the source address of data frames. • The frame from station A to station C is flooded out to all ports except port E 0 (unknown unicasts are flooded). Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 107
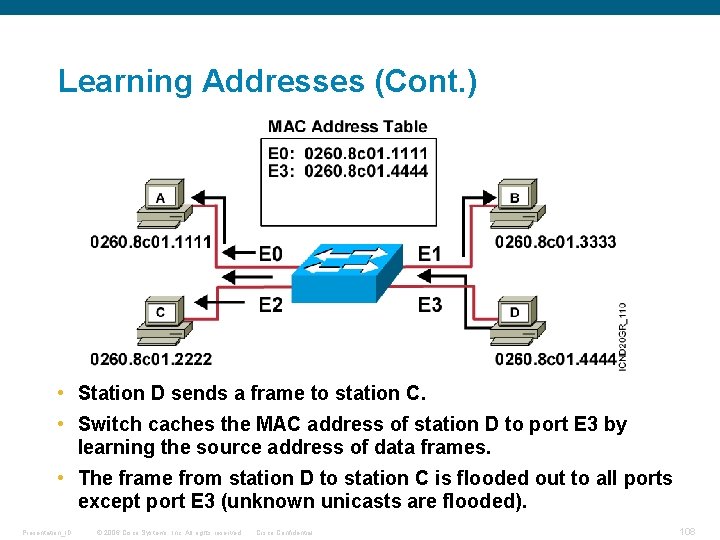
Learning Addresses (Cont. ) • Station D sends a frame to station C. • Switch caches the MAC address of station D to port E 3 by learning the source address of data frames. • The frame from station D to station C is flooded out to all ports except port E 3 (unknown unicasts are flooded). Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 108
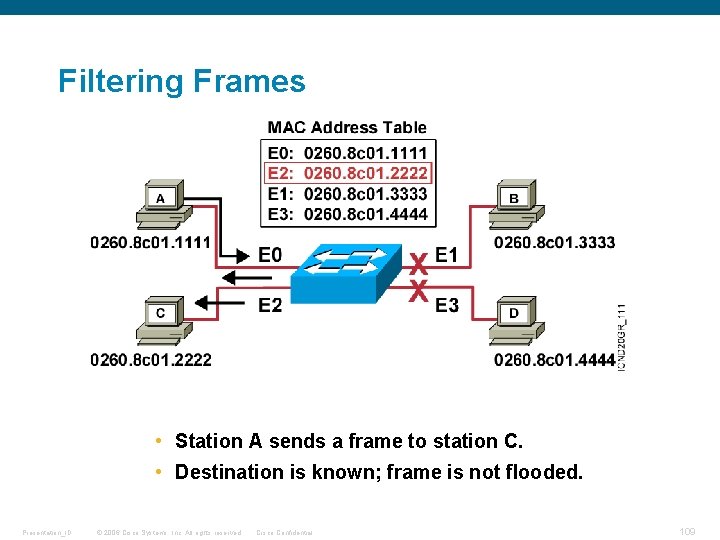
Filtering Frames • Station A sends a frame to station C. • Destination is known; frame is not flooded. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 109
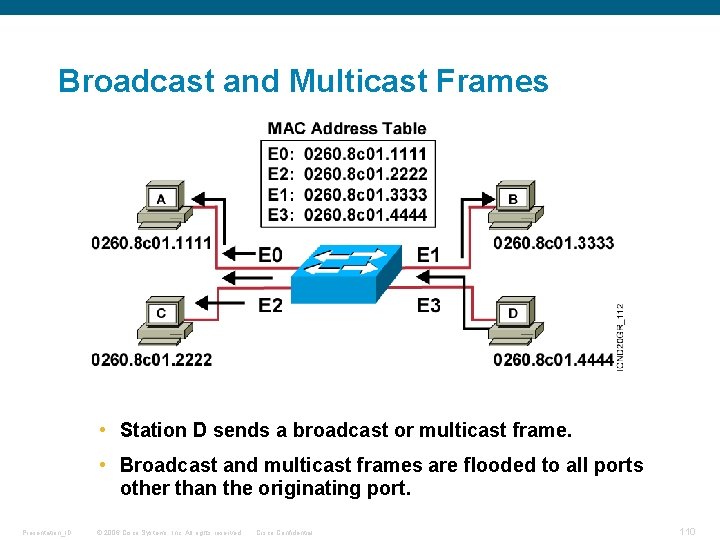
Broadcast and Multicast Frames • Station D sends a broadcast or multicast frame. • Broadcast and multicast frames are flooded to all ports other than the originating port. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 110
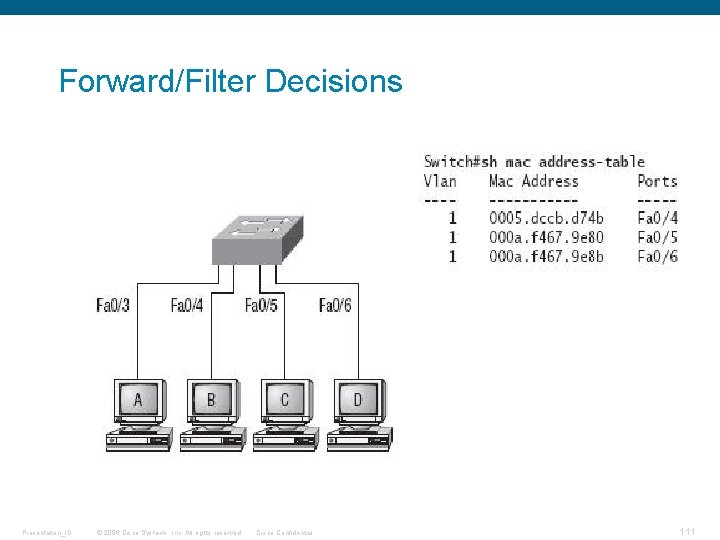
Forward/Filter Decisions Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 111
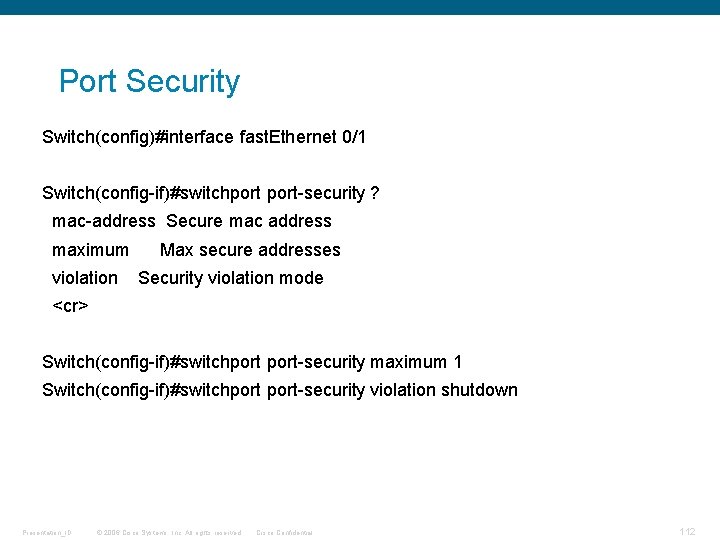
Port Security Switch(config)#interface fast. Ethernet 0/1 Switch(config-if)#switchport-security ? mac-address Secure mac address maximum violation Max secure addresses Security violation mode <cr> Switch(config-if)#switchport-security maximum 1 Switch(config-if)#switchport-security violation shutdown Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 112
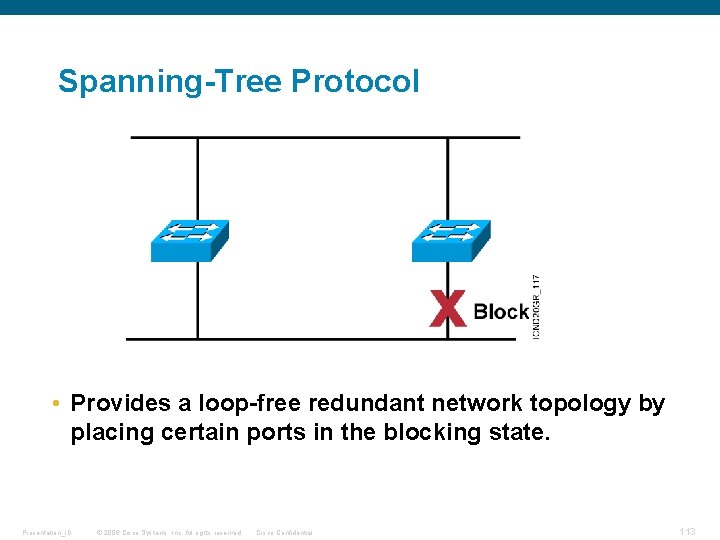
Spanning-Tree Protocol • Provides a loop-free redundant network topology by placing certain ports in the blocking state. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 113
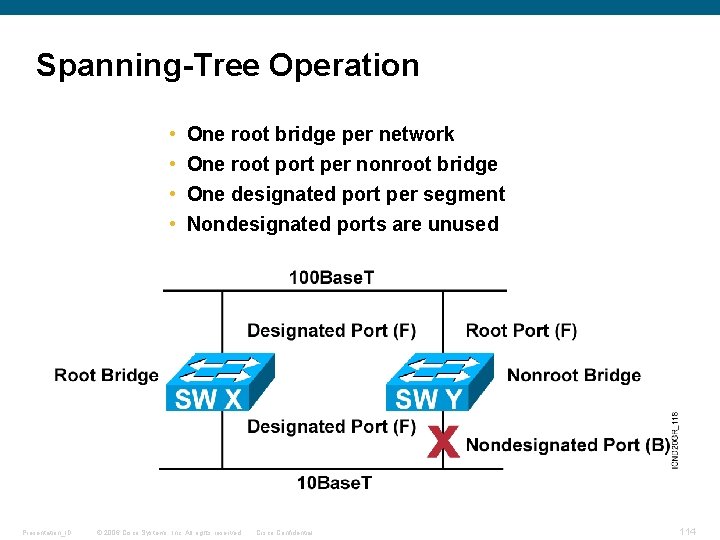
Spanning-Tree Operation • • Presentation_ID One root bridge per network One root port per nonroot bridge One designated port per segment Nondesignated ports are unused © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 114
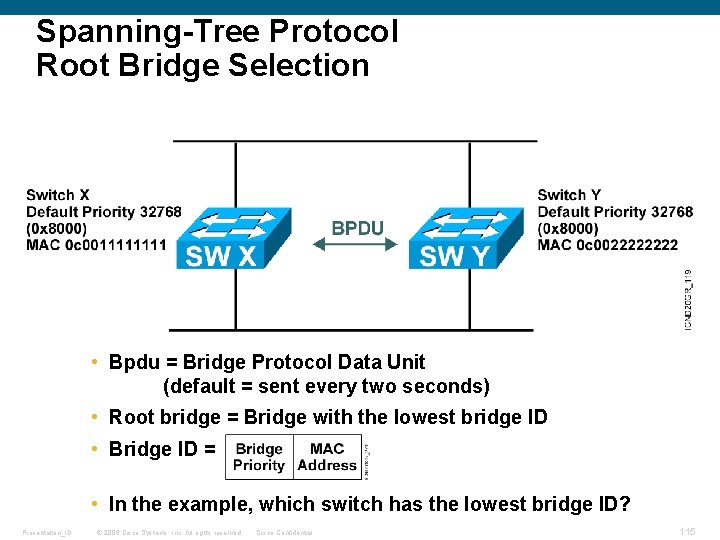
Spanning-Tree Protocol Root Bridge Selection • Bpdu = Bridge Protocol Data Unit (default = sent every two seconds) • Root bridge = Bridge with the lowest bridge ID • Bridge ID = • In the example, which switch has the lowest bridge ID? Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 115
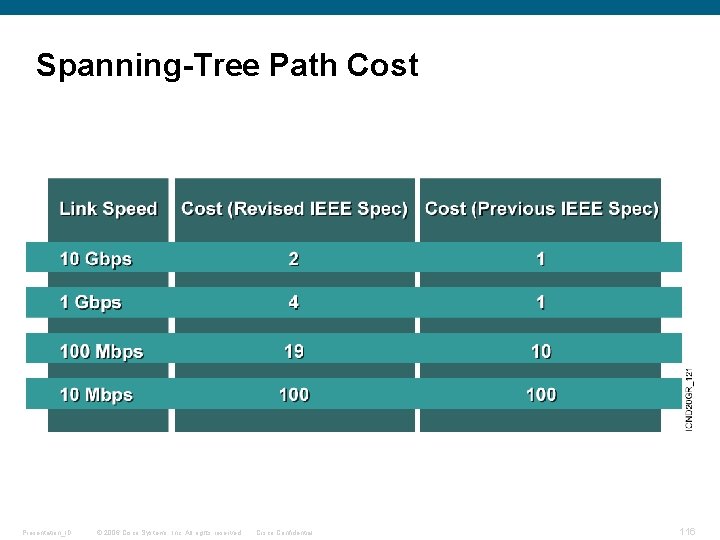
Spanning-Tree Path Cost Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 116
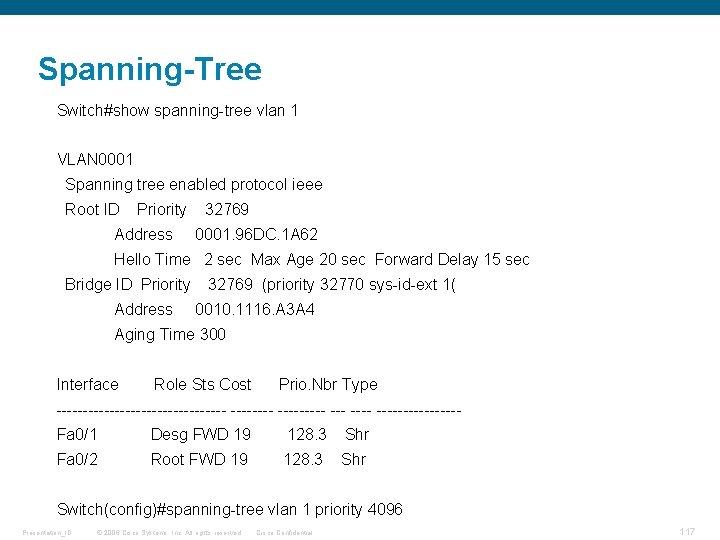
Spanning-Tree Switch#show spanning-tree vlan 1 VLAN 0001 Spanning tree enabled protocol ieee Root ID Priority Address 32769 0001. 96 DC. 1 A 62 Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec Bridge ID Priority Address 32769 (priority 32770 sys-id-ext 1( 0010. 1116. A 3 A 4 Aging Time 300 Interface Role Sts Cost Prio. Nbr Type ---------------- --------Fa 0/1 Desg FWD 19 128. 3 Shr Fa 0/2 Root FWD 19 128. 3 Shr Switch(config)#spanning-tree vlan 1 priority 4096 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 117
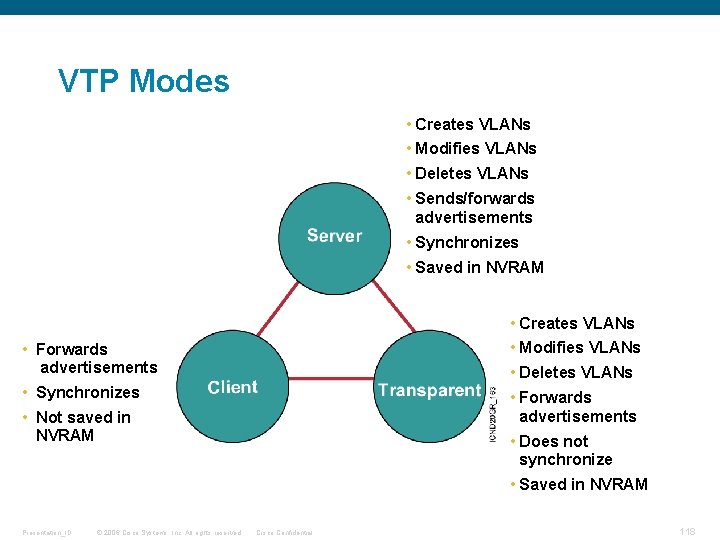
VTP Modes • Creates VLANs • Modifies VLANs • Deletes VLANs • Sends/forwards advertisements • Synchronizes • Saved in NVRAM • Creates VLANs • Forwards advertisements • Modifies VLANs • Synchronizes • Forwards advertisements • Deletes VLANs • Not saved in NVRAM • Does not synchronize • Saved in NVRAM Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 118
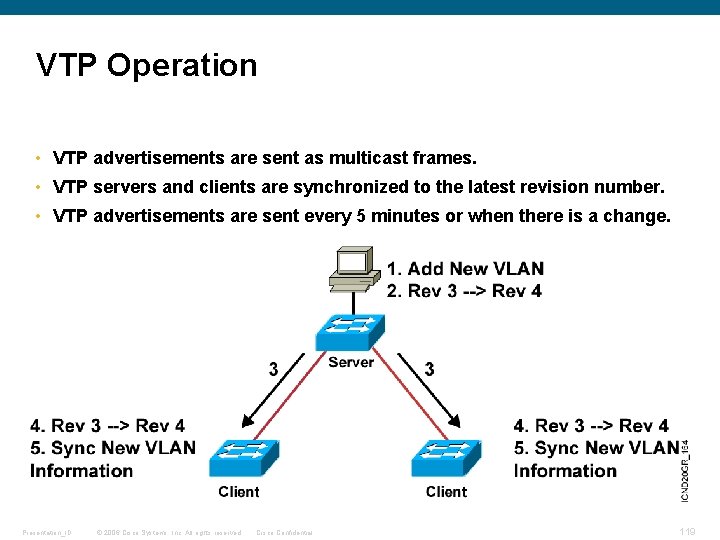
VTP Operation • VTP advertisements are sent as multicast frames. • VTP servers and clients are synchronized to the latest revision number. • VTP advertisements are sent every 5 minutes or when there is a change. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 119
Scaling the Network with NAT and PAT Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 120
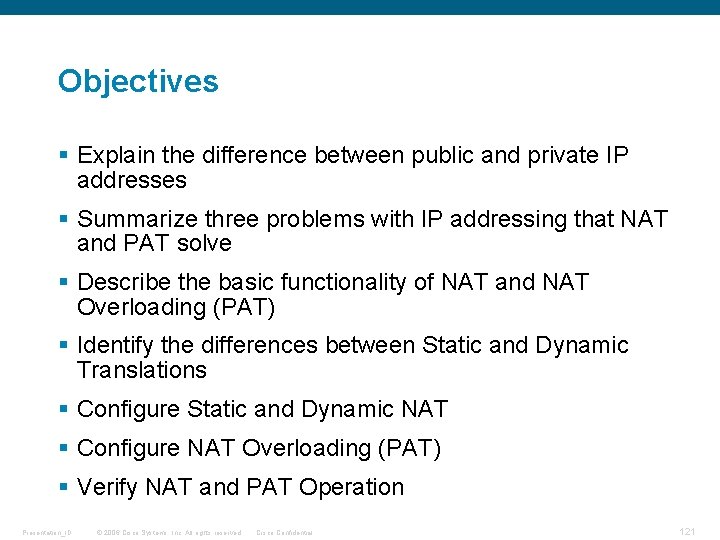
Objectives § Explain the difference between public and private IP addresses § Summarize three problems with IP addressing that NAT and PAT solve § Describe the basic functionality of NAT and NAT Overloading (PAT) § Identify the differences between Static and Dynamic Translations § Configure Static and Dynamic NAT § Configure NAT Overloading (PAT) § Verify NAT and PAT Operation Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 121
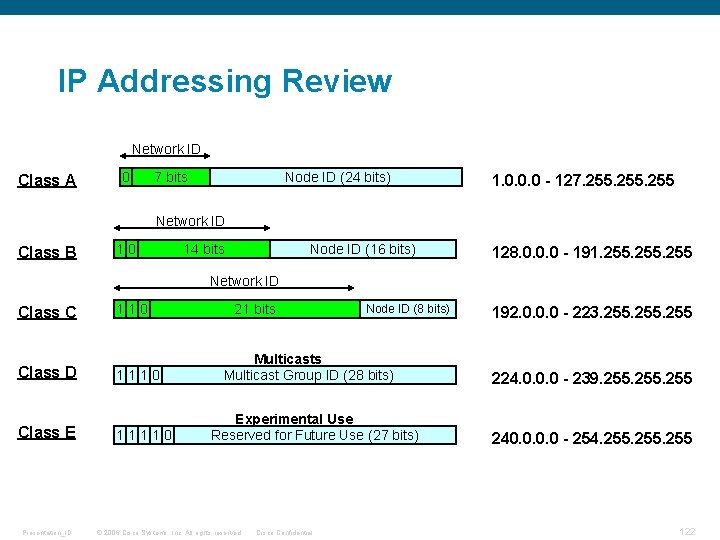
IP Addressing Review Network ID Class A 0 7 bits Node ID (24 bits) 1. 0. 0. 0 - 127. 255 Network ID Class B 10 14 bits Node ID (16 bits) 128. 0. 0. 0 - 191. 255 Network ID Class C Class D Class E Presentation_ID 110 11110 21 bits Node ID (8 bits) Multicasts Multicast Group ID (28 bits) Experimental Use Reserved for Future Use (27 bits) © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 192. 0. 0. 0 - 223. 255 224. 0. 0. 0 - 239. 255 240. 0 - 254. 255 122
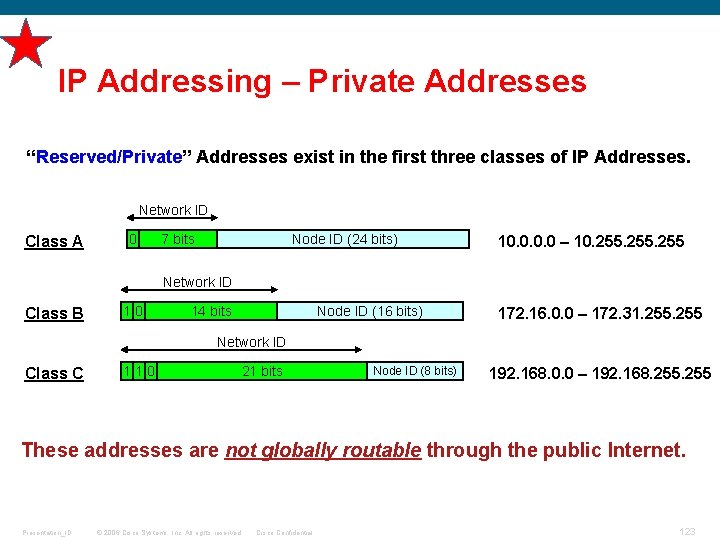
IP Addressing – Private Addresses “Reserved/Private” Addresses exist in the first three classes of IP Addresses. Network ID Class A 0 7 bits Node ID (24 bits) 10. 0 – 10. 255 Network ID Class B 10 14 bits Node ID (16 bits) 172. 16. 0. 0 – 172. 31. 255 Network ID Class C 110 21 bits Node ID (8 bits) 192. 168. 0. 0 – 192. 168. 255 These addresses are not globally routable through the public Internet. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 123
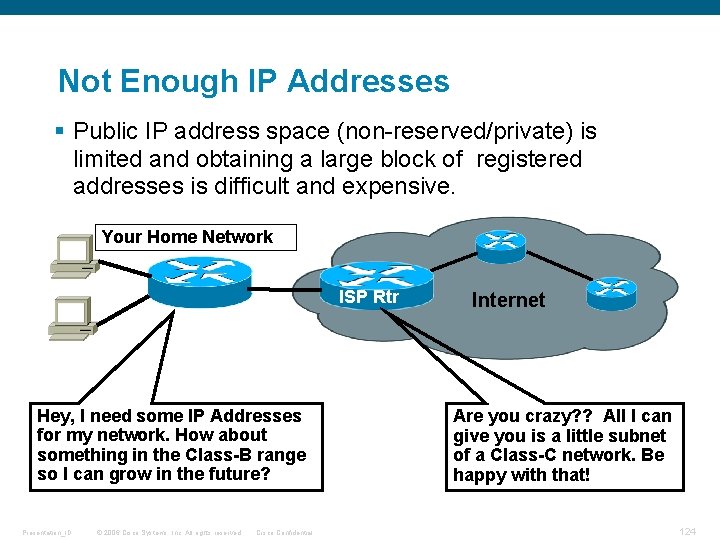
Not Enough IP Addresses § Public IP address space (non-reserved/private) is limited and obtaining a large block of registered addresses is difficult and expensive. Your Home Network ISP Rtr Hey, I need some IP Addresses for my network. How about something in the Class-B range so I can grow in the future? Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential Internet Are you crazy? ? All I can give you is a little subnet of a Class-C network. Be happy with that! 124
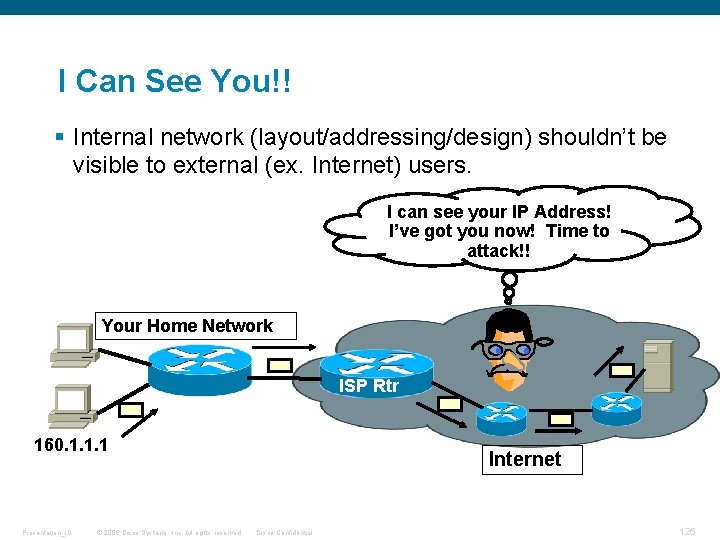
I Can See You!! § Internal network (layout/addressing/design) shouldn’t be visible to external (ex. Internet) users. I can see your IP Address! I’ve got you now! Time to attack!! Your Home Network ISP Rtr 160. 1. 1. 1 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Internet Cisco Confidential 125
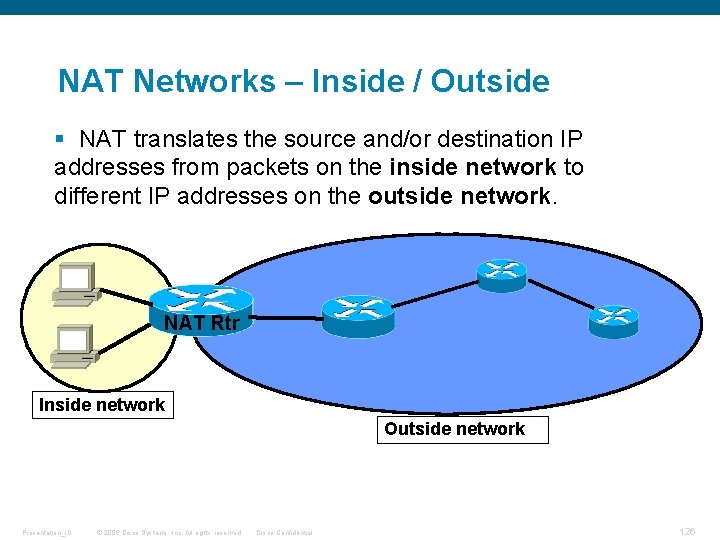
NAT Networks – Inside / Outside § NAT translates the source and/or destination IP addresses from packets on the inside network to different IP addresses on the outside network. NAT Rtr Inside network Outside network Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 126
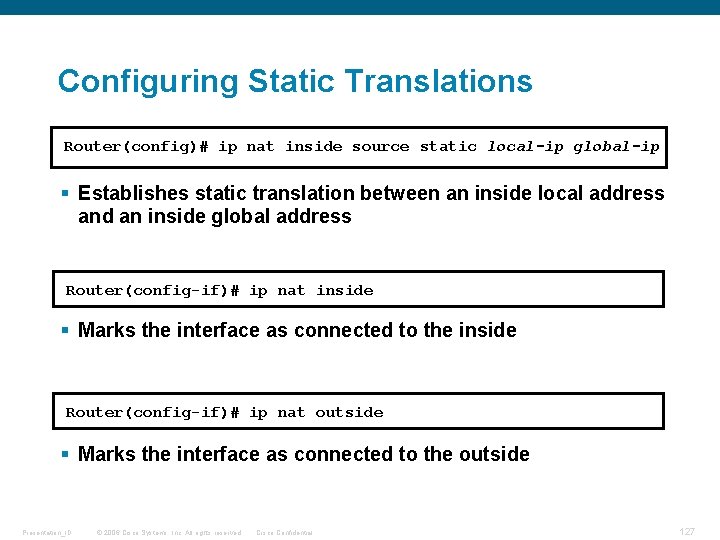
Configuring Static Translations Router(config)# ip nat inside source static local-ip global-ip § Establishes static translation between an inside local address and an inside global address Router(config-if)# ip nat inside § Marks the interface as connected to the inside Router(config-if)# ip nat outside § Marks the interface as connected to the outside Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 127
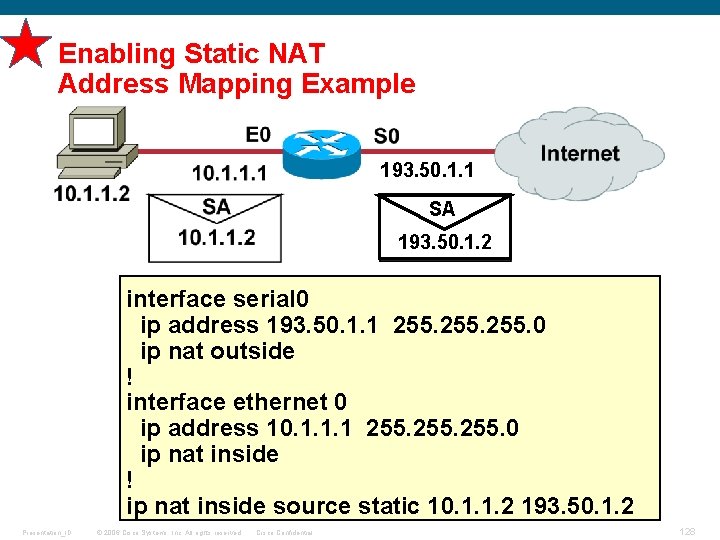
Enabling Static NAT Address Mapping Example 193. 50. 1. 1 SA 193. 50. 1. 2 interface serial 0 ip address 193. 50. 1. 1 255. 0 ip nat outside ! interface ethernet 0 ip address 10. 1. 1. 1 255. 0 ip nat inside ! 193. 50. 1. 2 ip nat inside source static 10. 1. 1. 2 193. 50. 1. 2 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 128
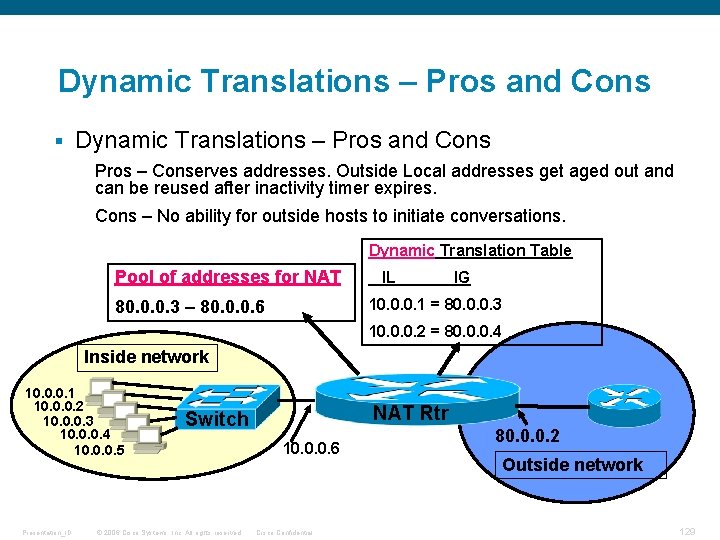
Dynamic Translations – Pros and Cons § Dynamic Translations – Pros and Cons Pros – Conserves addresses. Outside Local addresses get aged out and can be reused after inactivity timer expires. Cons – No ability for outside hosts to initiate conversations. Dynamic Translation Table Pool of addresses for NAT IL IG 10. 0. 0. 1 = 80. 0. 0. 3 – 80. 0. 0. 6 10. 0. 0. 2 = 80. 0. 0. 4 Inside network 10. 0. 0. 1 10. 0. 0. 2 10. 0. 0. 3 10. 0. 0. 4 10. 0. 0. 5 Presentation_ID NAT Rtr Switch © 2006 Cisco Systems, Inc. All rights reserved. 10. 0. 0. 6 Cisco Confidential 80. 0. 0. 2 Outside network 129
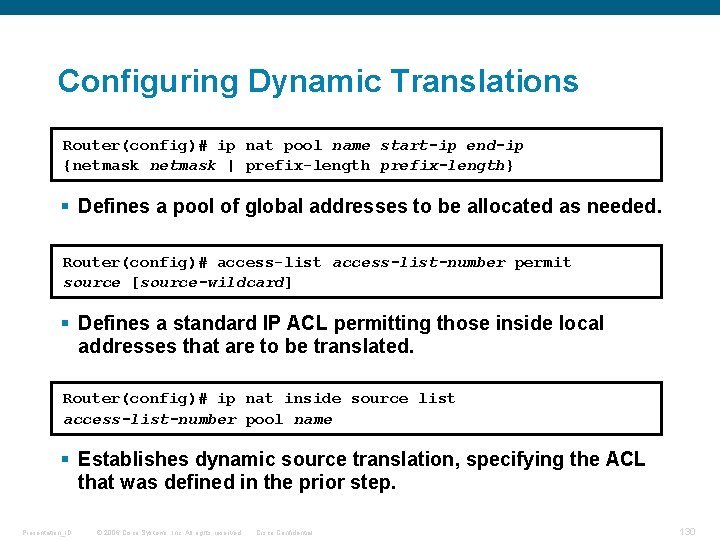
Configuring Dynamic Translations Router(config)# ip nat pool name start-ip end-ip {netmask | prefix-length} § Defines a pool of global addresses to be allocated as needed. Router(config)# access-list-number permit source [source-wildcard] § Defines a standard IP ACL permitting those inside local addresses that are to be translated. Router(config)# ip nat inside source list access-list-number pool name § Establishes dynamic source translation, specifying the ACL that was defined in the prior step. Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 130
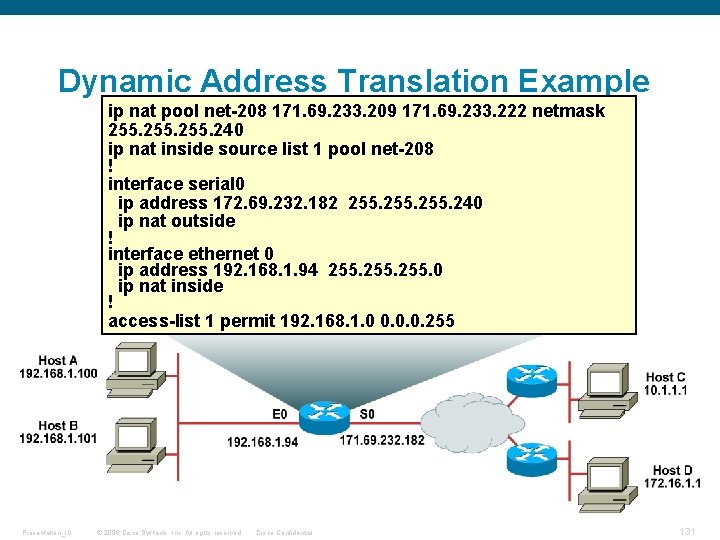
Dynamic Address Translation Example ip nat pool net-208 171. 69. 233. 209 171. 69. 233. 222 netmask 255. 240 ip nat inside source list 1 pool net-208 ! interface serial 0 ip address 172. 69. 232. 182 255. 240 ip nat outside ! interface ethernet 0 ip address 192. 168. 1. 94 255. 0 ip nat inside ! access-list 1 permit 192. 168. 1. 0 0. 0. 0. 255 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 131
How Does PAT (NAT Overloading) Change All This? Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 132
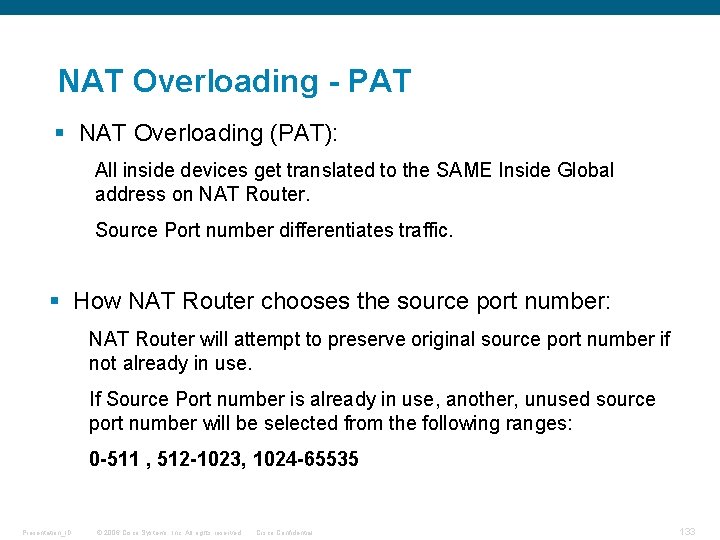
NAT Overloading - PAT § NAT Overloading (PAT): All inside devices get translated to the SAME Inside Global address on NAT Router. Source Port number differentiates traffic. § How NAT Router chooses the source port number: NAT Router will attempt to preserve original source port number if not already in use. If Source Port number is already in use, another, unused source port number will be selected from the following ranges: 0 -511 , 512 -1023, 1024 -65535 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 133
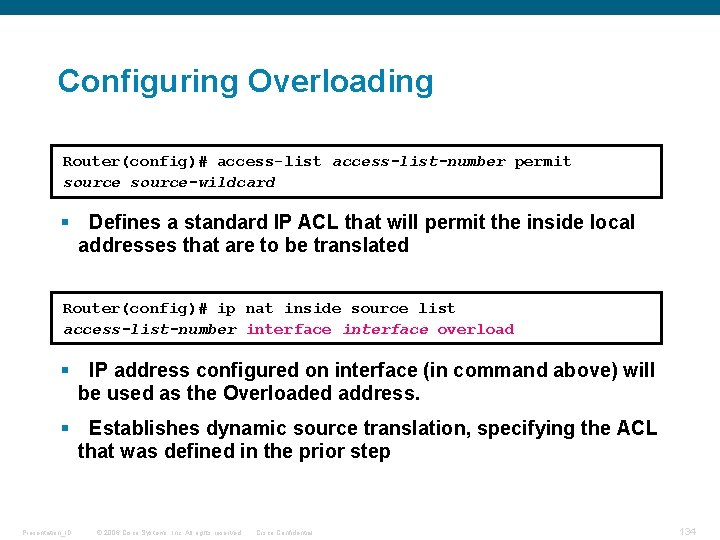
Configuring Overloading Router(config)# access-list-number permit source-wildcard § Defines a standard IP ACL that will permit the inside local addresses that are to be translated Router(config)# ip nat inside source list access-list-number interface overload § IP address configured on interface (in command above) will be used as the Overloaded address. § Establishes dynamic source translation, specifying the ACL that was defined in the prior step Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 134
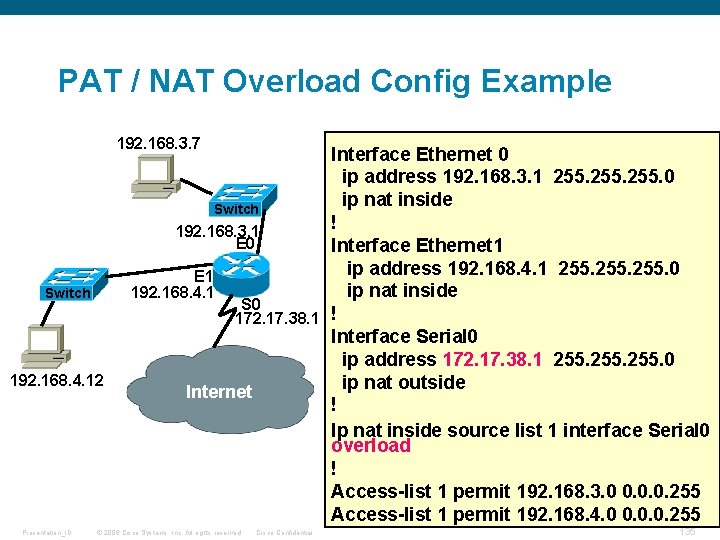
PAT / NAT Overload Config Example 192. 168. 3. 7 Switch 192. 168. 4. 12 Presentation_ID Interface Ethernet 0 ip address 192. 168. 3. 1 255. 0 ip nat inside Switch ! 192. 168. 3. 1 E 0 Interface Ethernet 1 ip address 192. 168. 4. 1 255. 0 E 1 ip nat inside 192. 168. 4. 1 S 0 172. 17. 38. 1 ! Interface Serial 0 ip address 172. 17. 38. 1 255. 0 ip nat outside Internet ! Ip nat inside source list 1 interface Serial 0 overload ! Access-list 1 permit 192. 168. 3. 0 0. 0. 0. 255 Access-list 1 permit 192. 168. 4. 0 0. 0. 0. 255 © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 135
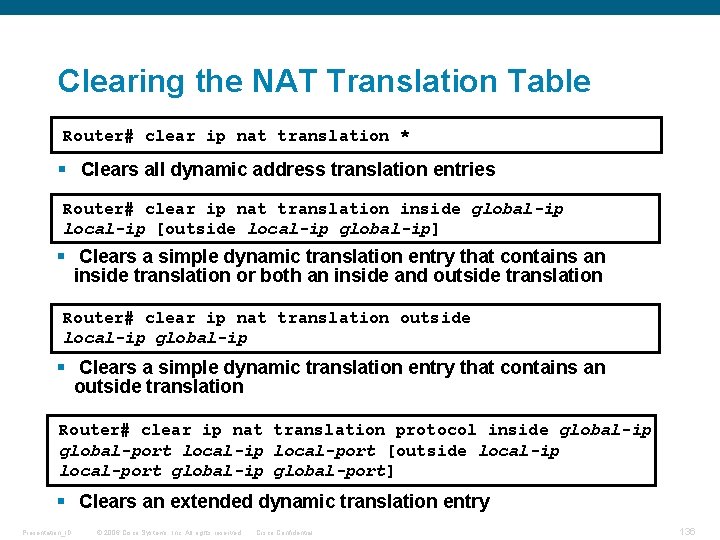
Clearing the NAT Translation Table Router# clear ip nat translation * § Clears all dynamic address translation entries Router# clear ip nat translation inside global-ip local-ip [outside local-ip global-ip] § Clears a simple dynamic translation entry that contains an inside translation or both an inside and outside translation Router# clear ip nat translation outside local-ip global-ip § Clears a simple dynamic translation entry that contains an outside translation Router# clear ip nat translation protocol inside global-ip global-port local-ip local-port [outside local-ip local-port global-ip global-port] § Clears an extended dynamic translation entry Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 136
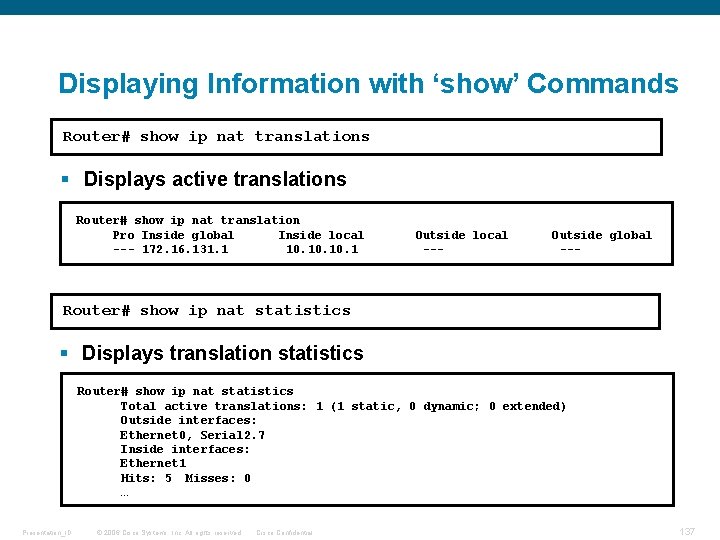
Displaying Information with ‘show’ Commands Router# show ip nat translations § Displays active translations Router# show ip nat translation Pro Inside global Inside local --- 172. 16. 131. 1 10. 10. 1 Outside local --- Outside global --- Router# show ip nat statistics § Displays translation statistics Router# show ip nat statistics Total active translations: 1 (1 static, 0 dynamic; 0 extended) Outside interfaces: Ethernet 0, Serial 2. 7 Inside interfaces: Ethernet 1 Hits: 5 Misses: 0 … Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 137
Access Control Lists Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 138
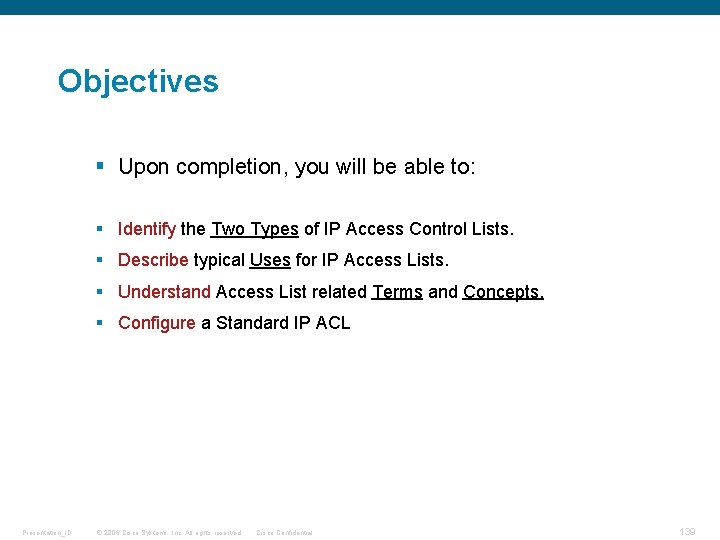
Objectives § Upon completion, you will be able to: § Identify the Two Types of IP Access Control Lists. § Describe typical Uses for IP Access Lists. § Understand Access List related Terms and Concepts. § Configure a Standard IP ACL Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 139
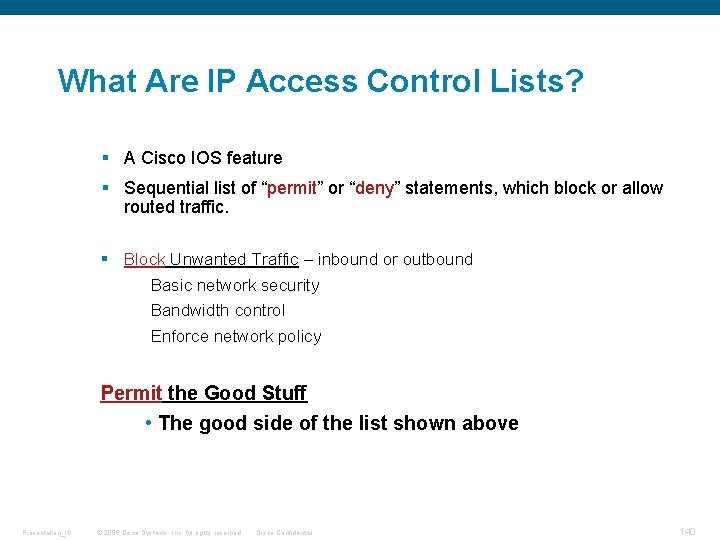
What Are IP Access Control Lists? § A Cisco IOS feature § Sequential list of “permit” or “deny” statements, which block or allow routed traffic. § Block Unwanted Traffic – inbound or outbound Basic network security Bandwidth control Enforce network policy Permit the Good Stuff • The good side of the list shown above Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 140
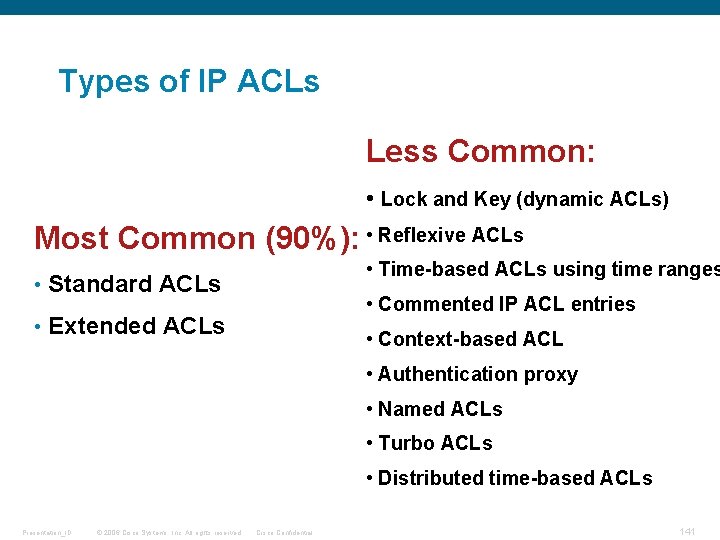
Types of IP ACLs Less Common: • Lock and Key (dynamic ACLs) Most Common (90%): • Reflexive ACLs • Time-based ACLs using time ranges • Standard ACLs • Commented IP ACL entries • Extended ACLs • Context-based ACL • Authentication proxy • Named ACLs • Turbo ACLs • Distributed time-based ACLs Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 141
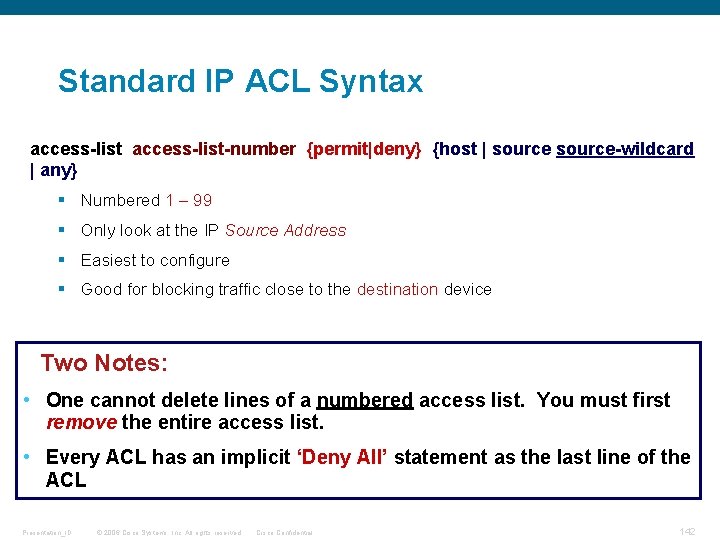
Standard IP ACL Syntax access-list-number {permit|deny} {host | source-wildcard | any} § Numbered 1 – 99 § Only look at the IP Source Address § Easiest to configure § Good for blocking traffic close to the destination device Two Notes: • One cannot delete lines of a numbered access list. You must first remove the entire access list. • Every ACL has an implicit ‘Deny All’ statement as the last line of the ACL Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 142
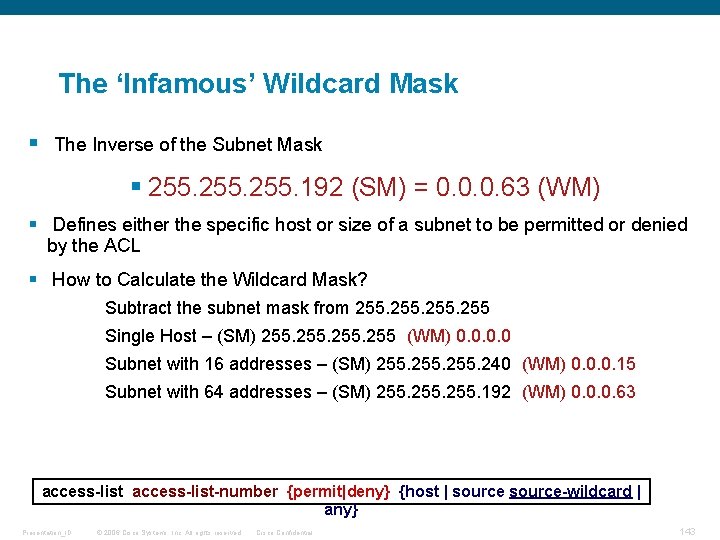
The ‘Infamous’ Wildcard Mask § The Inverse of the Subnet Mask § 255. 192 (SM) = 0. 0. 0. 63 (WM) § Defines either the specific host or size of a subnet to be permitted or denied by the ACL § How to Calculate the Wildcard Mask? Subtract the subnet mask from 255 Single Host – (SM) 255 (WM) 0. 0 Subnet with 16 addresses – (SM) 255. 240 (WM) 0. 0. 0. 15 Subnet with 64 addresses – (SM) 255. 192 (WM) 0. 0. 0. 63 access-list-number {permit|deny} {host | source-wildcard | any} Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 143
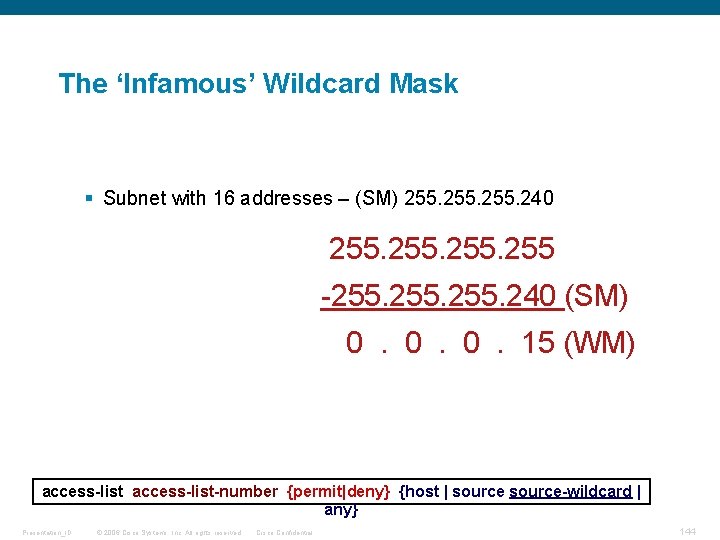
The ‘Infamous’ Wildcard Mask § Subnet with 16 addresses – (SM) 255. 240 255 -255. 240 (SM) 0. 0. 0. 15 (WM) access-list-number {permit|deny} {host | source-wildcard | any} Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 144
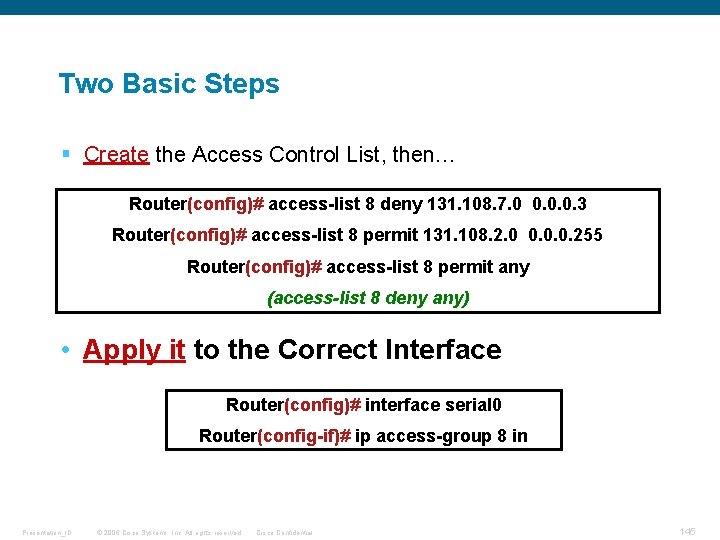
Two Basic Steps § Create the Access Control List, then… Router(config)# access-list 8 deny 131. 108. 7. 0 0. 0. 0. 3 Router(config)# access-list 8 permit 131. 108. 2. 0 0. 0. 0. 255 Router(config)# access-list 8 permit any (access-list 8 deny any) • Apply it to the Correct Interface Router(config)# interface serial 0 Router(config-if)# ip access-group 8 in Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 145
Configuring an Extended IP ACL Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 146
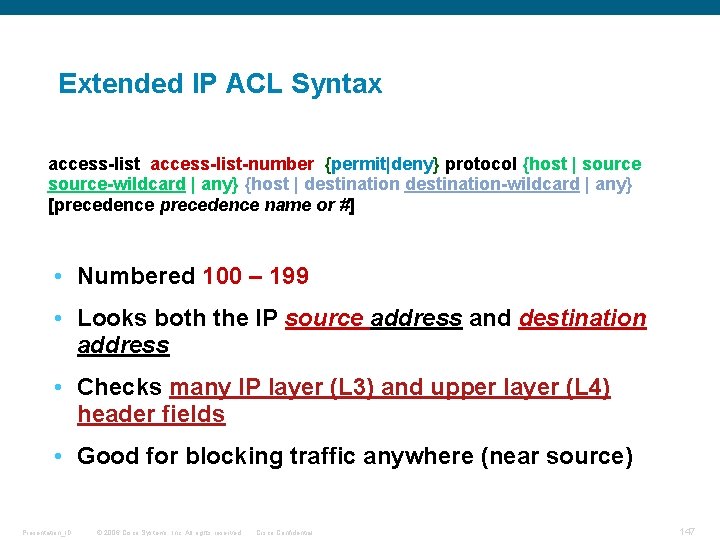
Extended IP ACL Syntax access-list-number {permit|deny} protocol {host | source-wildcard | any} {host | destination-wildcard | any} [precedence name or #] • Numbered 100 – 199 • Looks both the IP source address and destination address • Checks many IP layer (L 3) and upper layer (L 4) header fields • Good for blocking traffic anywhere (near source) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 147
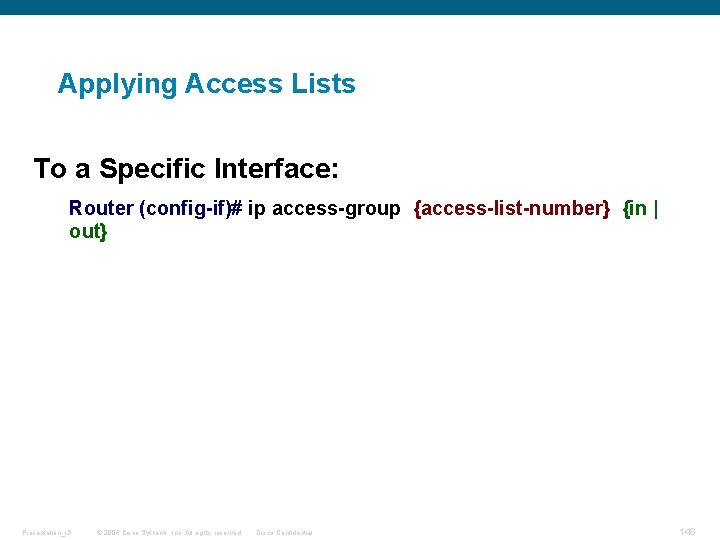
Applying Access Lists To a Specific Interface: Router (config-if)# ip access-group {access-list-number} {in | out} Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 148
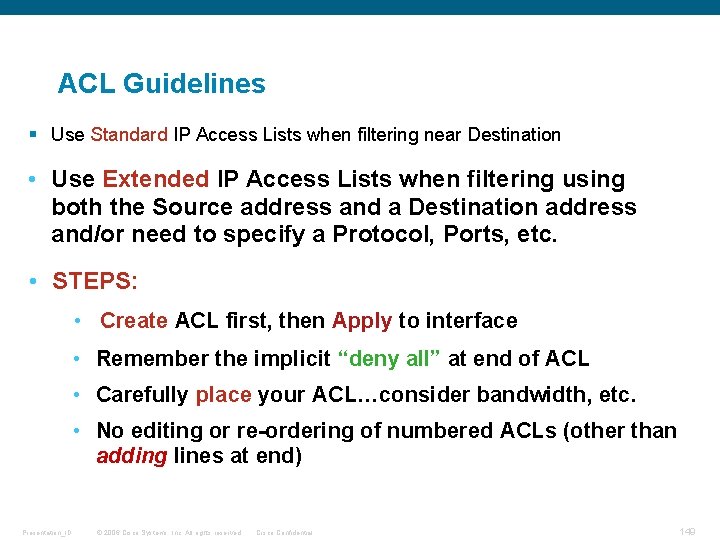
ACL Guidelines § Use Standard IP Access Lists when filtering near Destination • Use Extended IP Access Lists when filtering using both the Source address and a Destination address and/or need to specify a Protocol, Ports, etc. • STEPS: • Create ACL first, then Apply to interface • Remember the implicit “deny all” at end of ACL • Carefully place your ACL…consider bandwidth, etc. • No editing or re-ordering of numbered ACLs (other than adding lines at end) Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 149
Q and A Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 150

Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 151
- Slides: 151