CASE STUDY ANN Section 3 1 Network Forensics
- Slides: 27
CASE STUDY : ANN Section 3. 1 Network Forensics TRACKING HACKERS THROUGH CYBERSPACE
SCENARIO: ANN’S BAD AIM Anarchy-R-Us, Inc. suspects that one of their employees, Ann Dercover, is really a secret agent working for their competitor. Ann has access to the company’s prize asset, the secret recipe. Security staff are worried that Ann may try to leak the company’s secret recipe. Security staff have been monitoring Ann’s activity for some time, but haven’t found anything suspicious– until now. Today an unexpected laptop briefly appeared on the company wireless network. Staff hypothesize it may have been someone in the parking lot, because no strangers were seen in the building. Ann’s computer, (192. 168. 1. 158) sent IMs over the wireless network to this computer. The rogue laptop disappeared shortly thereafter. “We have a packet capture of the activity, ” said security staff, “but we can’t figure out what’s going on. Can you help? ” http: //forensicscontest. com/2009/09/25/puzzle-1 -anns-bad-aim
MISSION You are the forensic investigator. Your mission is to figure out who Ann was IM-ing, what she sent, and recover evidence including: 1. What is the name of Ann’s IM buddy? 2. What was the first comment in the captured IM conversation? 3. What is the name of the file Ann transferred? 4. What is the magic number of the file you want to extract (first four bytes)? 5. What was the MD 5 sum of the file? 6. What is the secret recipe?
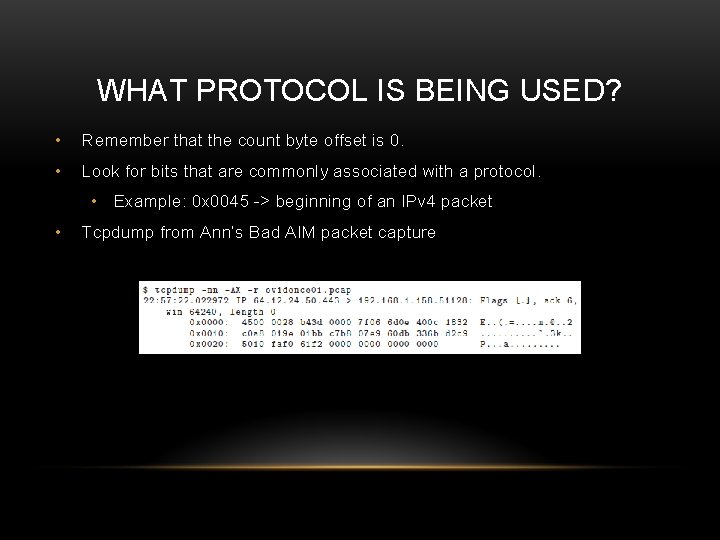
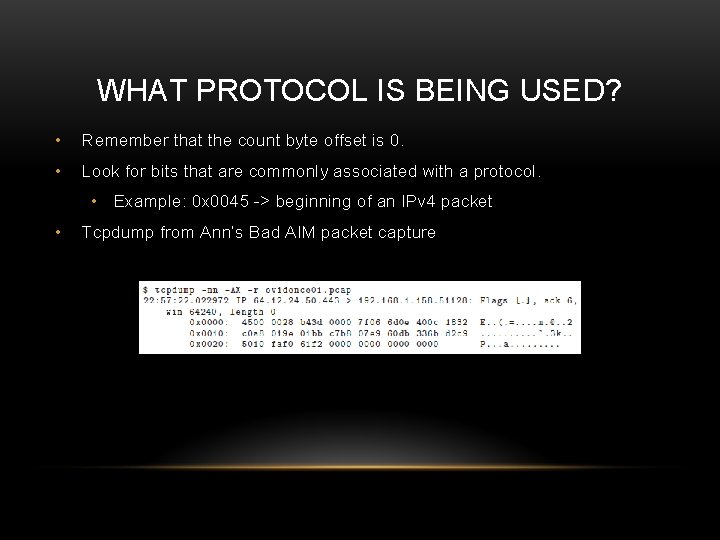
WHAT PROTOCOL IS BEING USED? • Remember that the count byte offset is 0. • Look for bits that are commonly associated with a protocol. • Example: 0 x 0045 -> beginning of an IPv 4 packet • Tcpdump from Ann’s Bad AIM packet capture
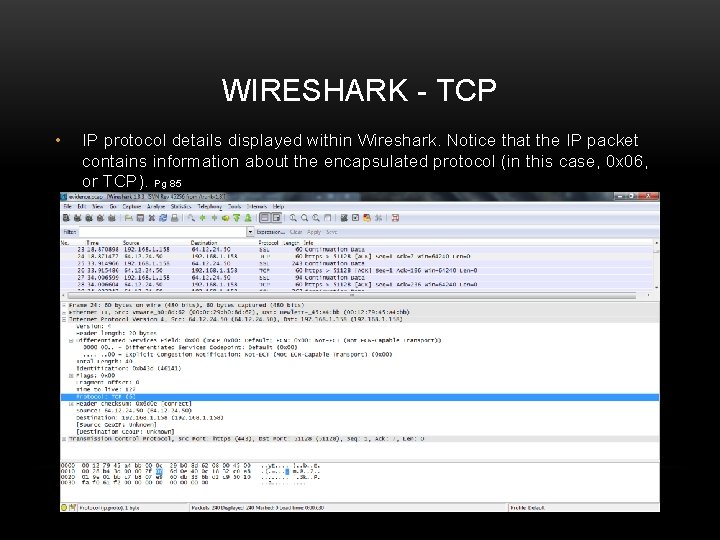
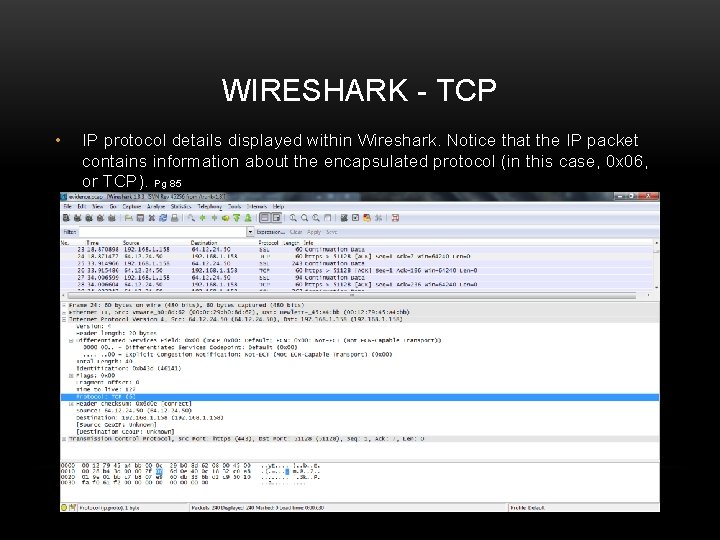
WIRESHARK - TCP • IP protocol details displayed within Wireshark. Notice that the IP packet contains information about the encapsulated protocol (in this case, 0 x 06, or TCP). Pg 85
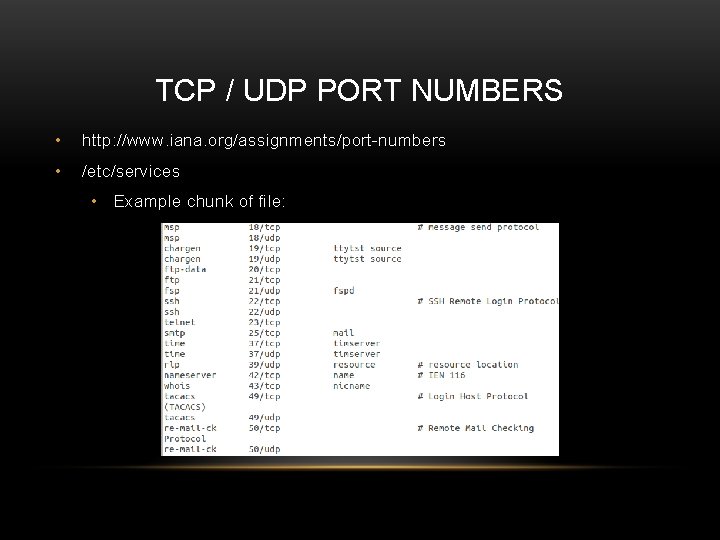
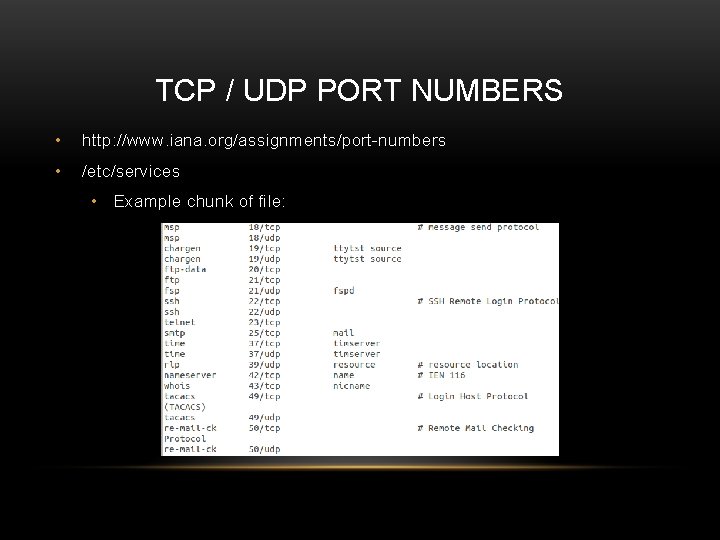
TCP / UDP PORT NUMBERS • http: //www. iana. org/assignments/port-numbers • /etc/services • Example chunk of file:
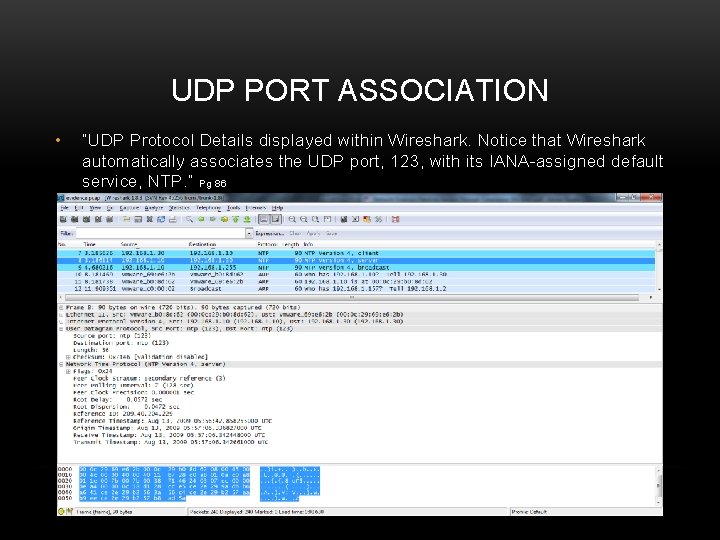
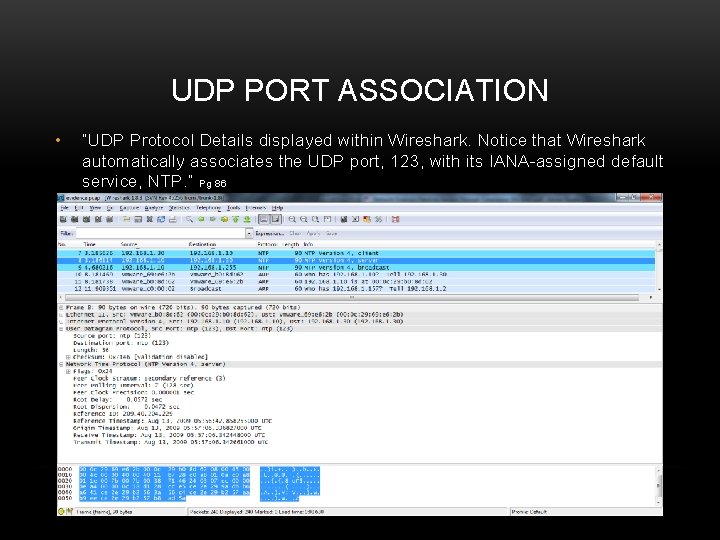
UDP PORT ASSOCIATION • “UDP Protocol Details displayed within Wireshark. Notice that Wireshark automatically associates the UDP port, 123, with its IANA-assigned default service, NTP. ” Pg 86
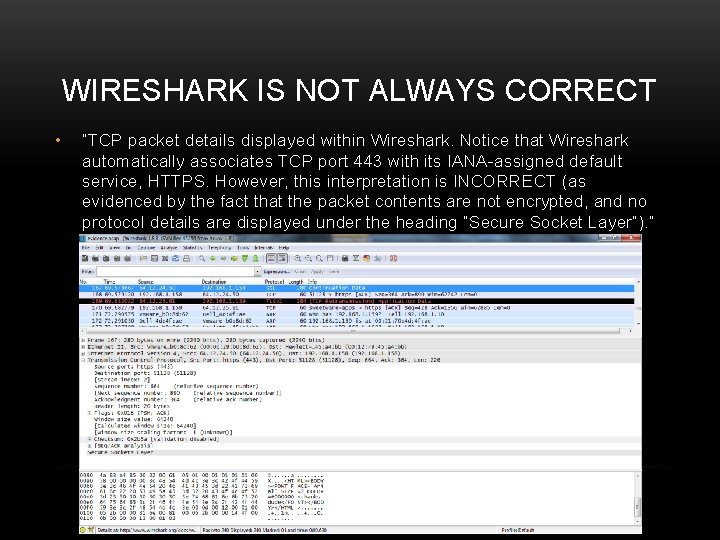
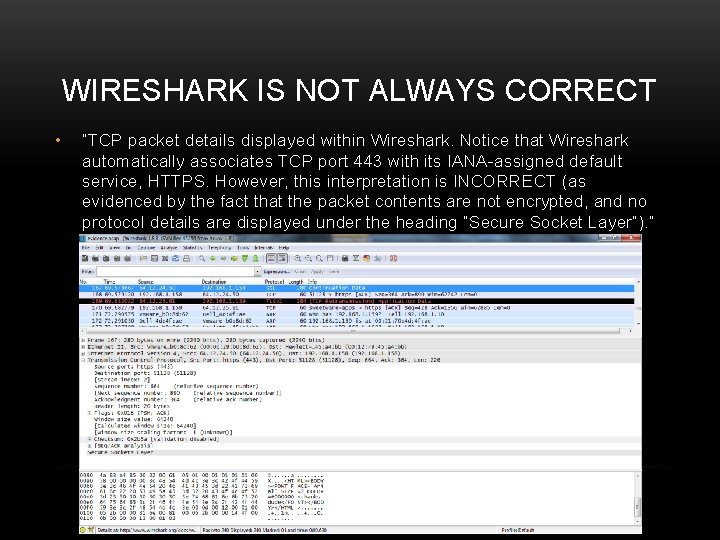
WIRESHARK IS NOT ALWAYS CORRECT • “TCP packet details displayed within Wireshark. Notice that Wireshark automatically associates TCP port 443 with its IANA-assigned default service, HTTPS. However, this interpretation is INCORRECT (as evidenced by the fact that the packet contents are not encrypted, and no protocol details are displayed under the heading “Secure Socket Layer”). ” Pg. 87
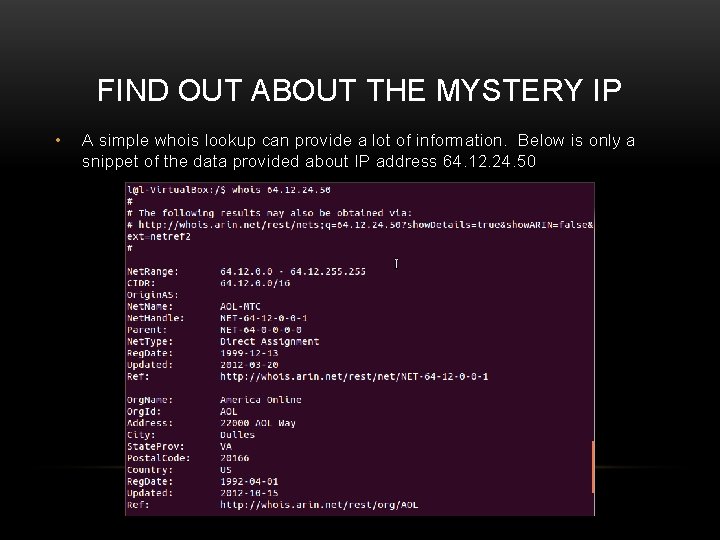
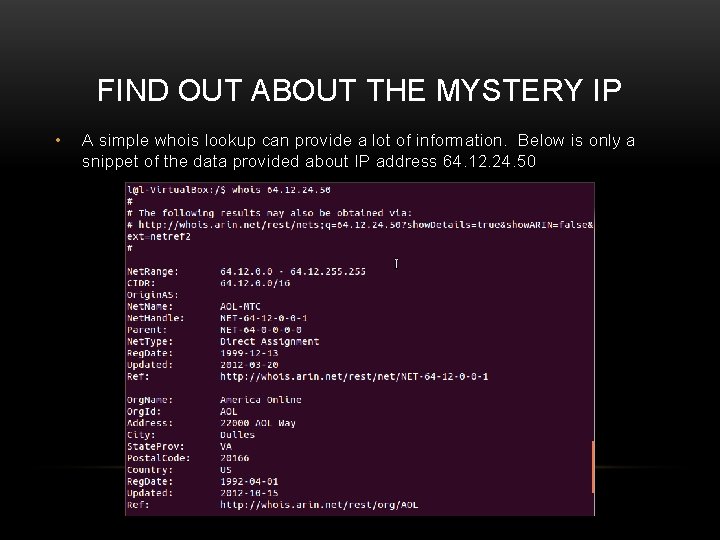
FIND OUT ABOUT THE MYSTERY IP • A simple whois lookup can provide a lot of information. Below is only a snippet of the data provided about IP address 64. 12. 24. 50
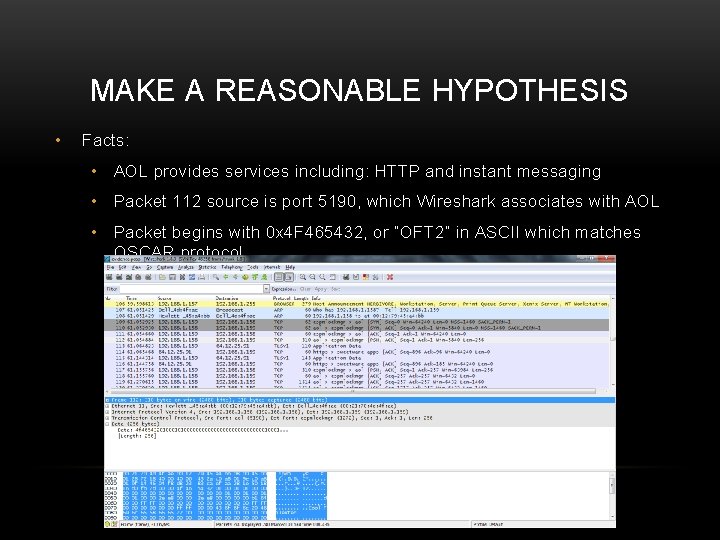
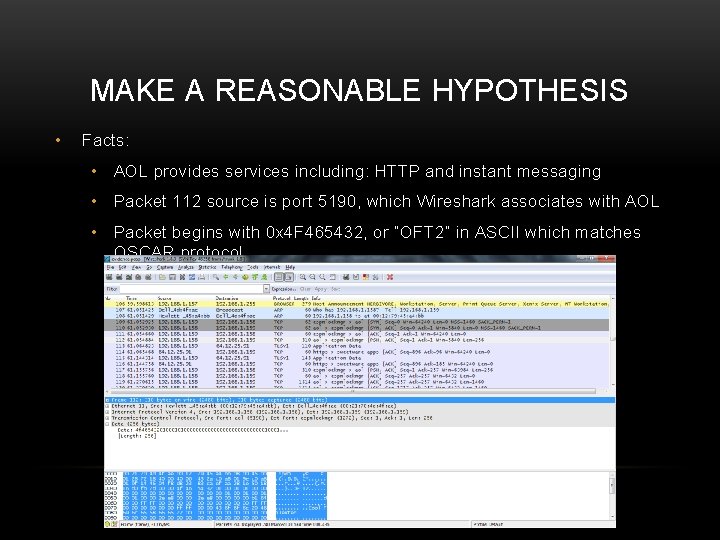
MAKE A REASONABLE HYPOTHESIS • Facts: • AOL provides services including: HTTP and instant messaging • Packet 112 source is port 5190, which Wireshark associates with AOL • Packet begins with 0 x 4 F 465432, or “OFT 2” in ASCII which matches OSCAR protocol
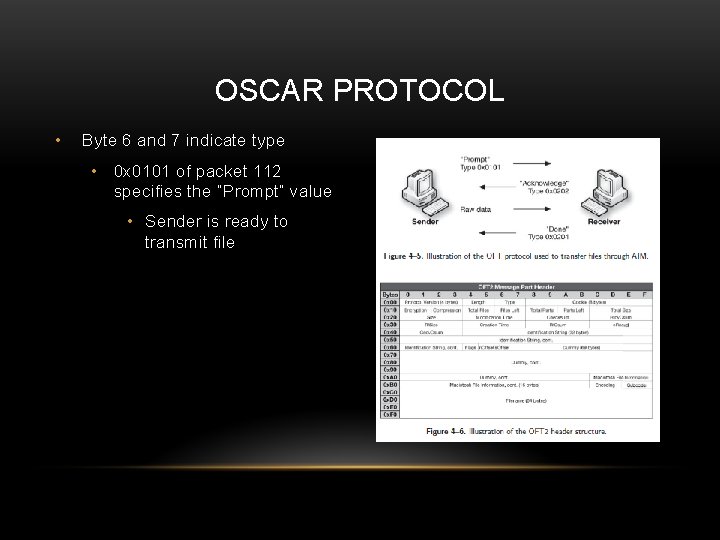
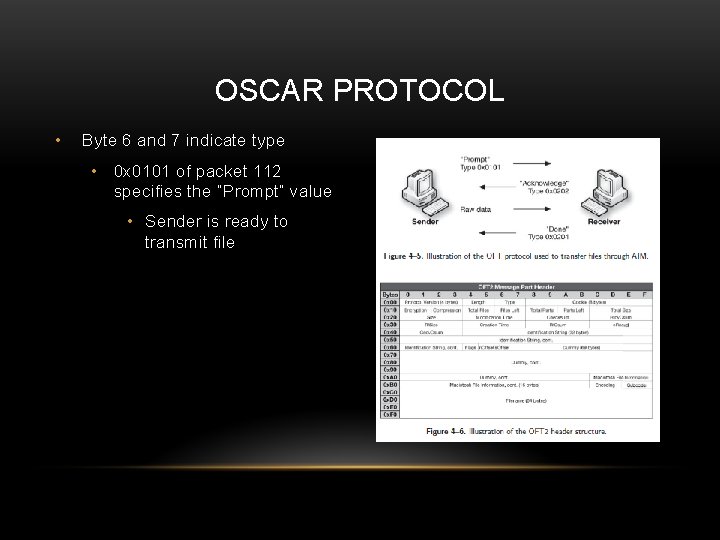
OSCAR PROTOCOL • Byte 6 and 7 indicate type • 0 x 0101 of packet 112 specifies the “Prompt” value • Sender is ready to transmit file
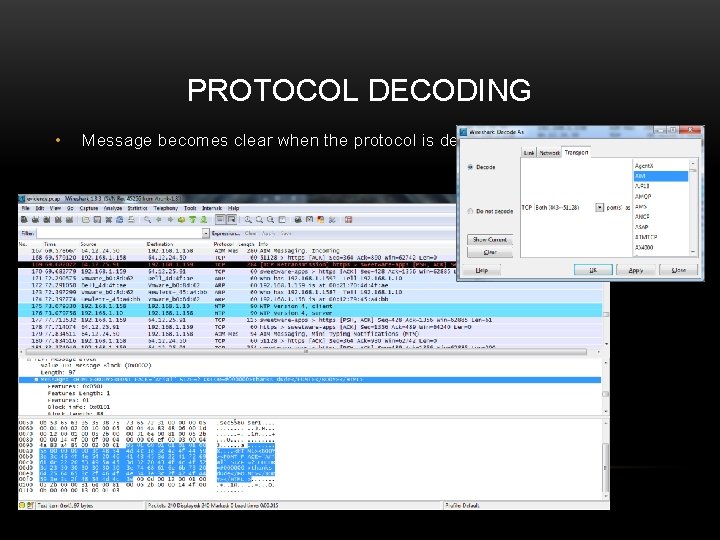
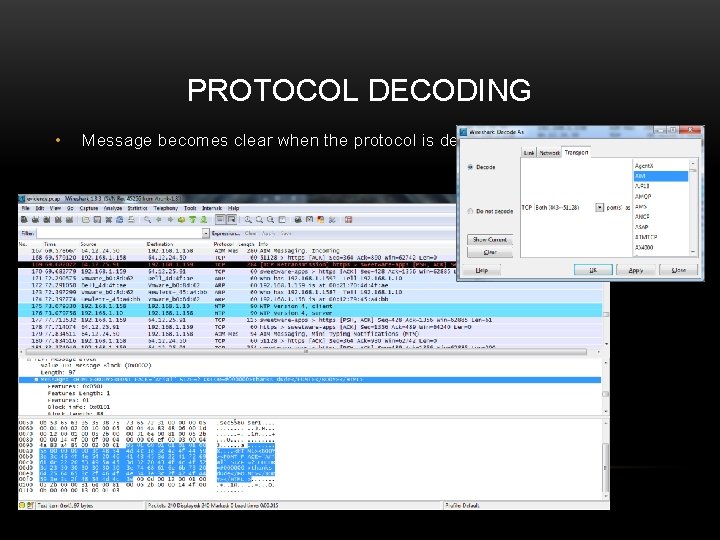
PROTOCOL DECODING • Message becomes clear when the protocol is decoded
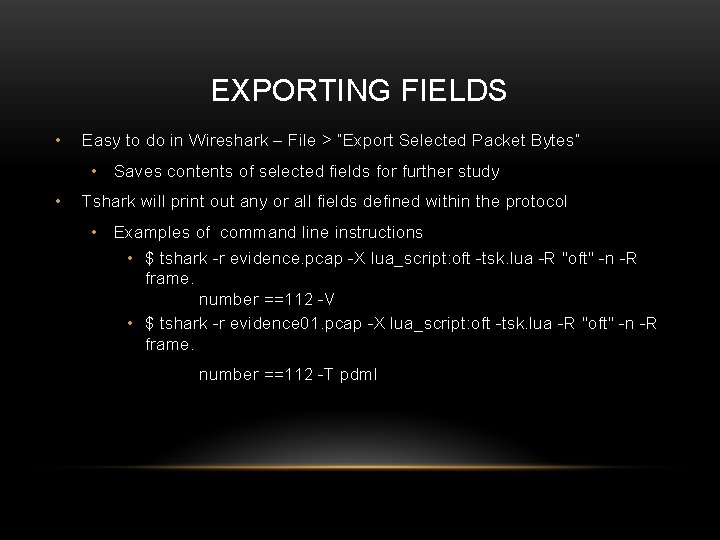
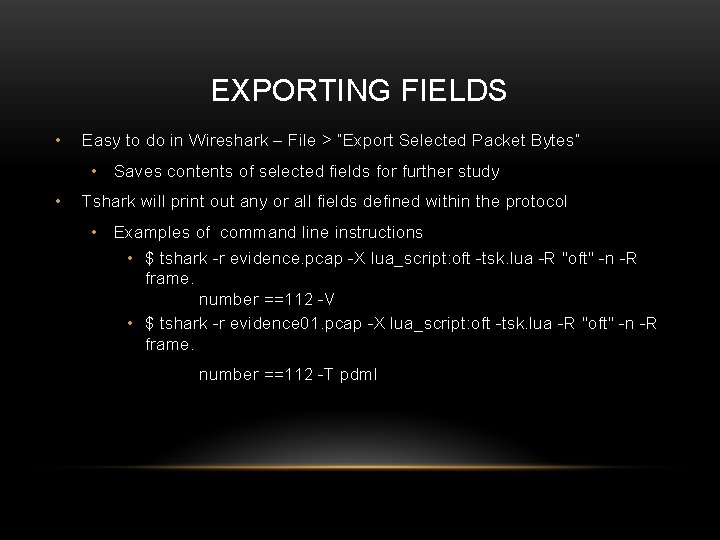
EXPORTING FIELDS • Easy to do in Wireshark – File > “Export Selected Packet Bytes” • Saves contents of selected fields for further study • Tshark will print out any or all fields defined within the protocol • Examples of command line instructions • $ tshark -r evidence. pcap -X lua_script: oft -tsk. lua -R "oft" -n -R frame. number ==112 -V • $ tshark -r evidence 01. pcap -X lua_script: oft -tsk. lua -R "oft" -n -R frame. number ==112 -T pdml
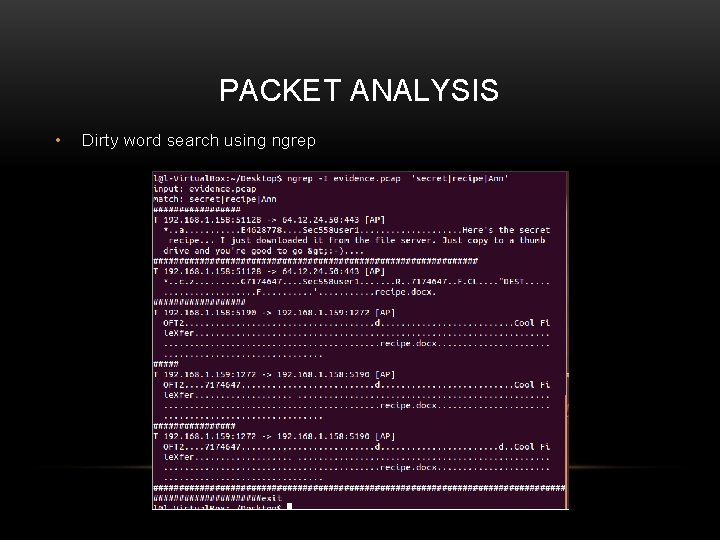
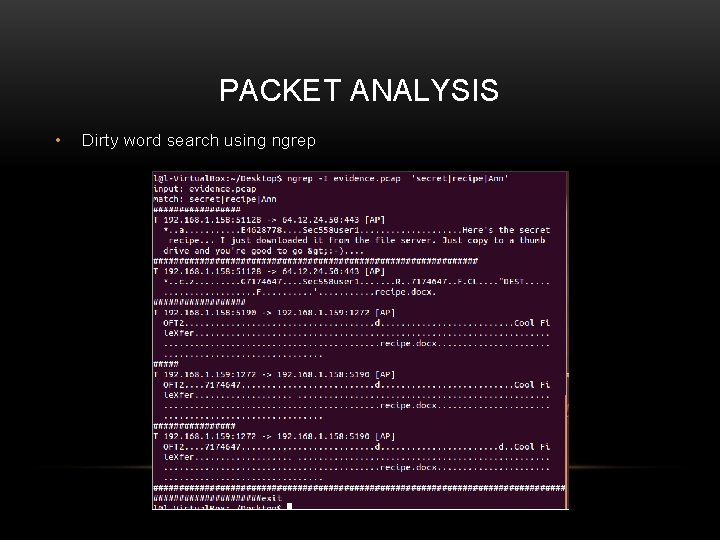
PACKET ANALYSIS • Dirty word search using ngrep
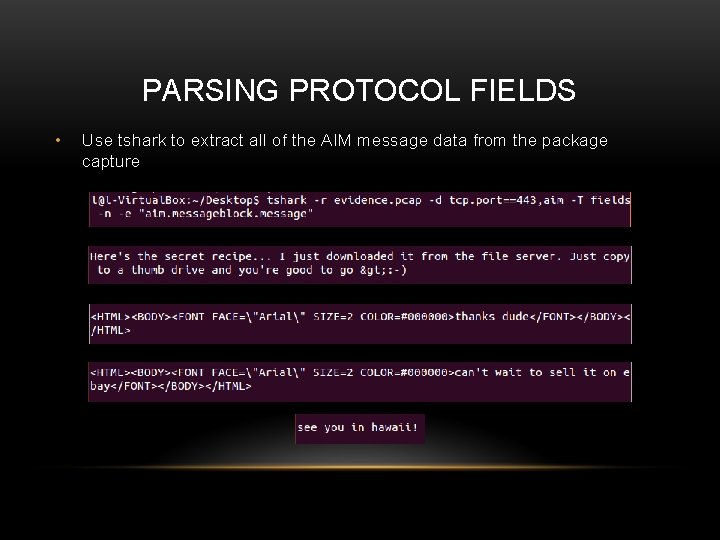
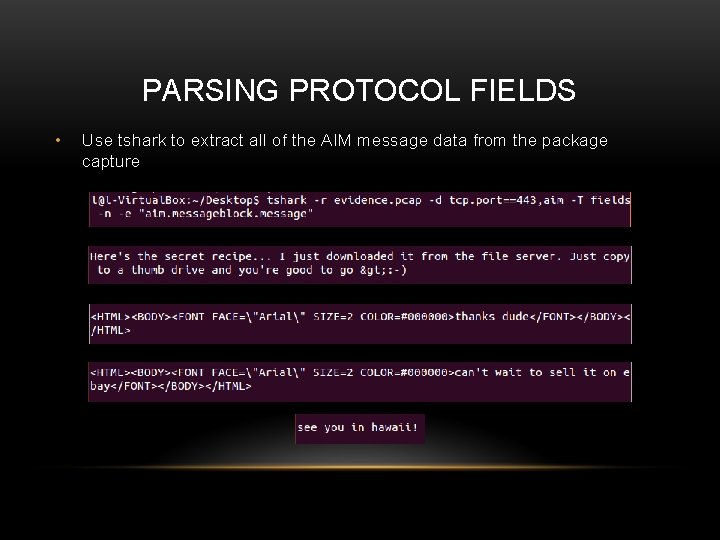
PARSING PROTOCOL FIELDS • Use tshark to extract all of the AIM message data from the package capture
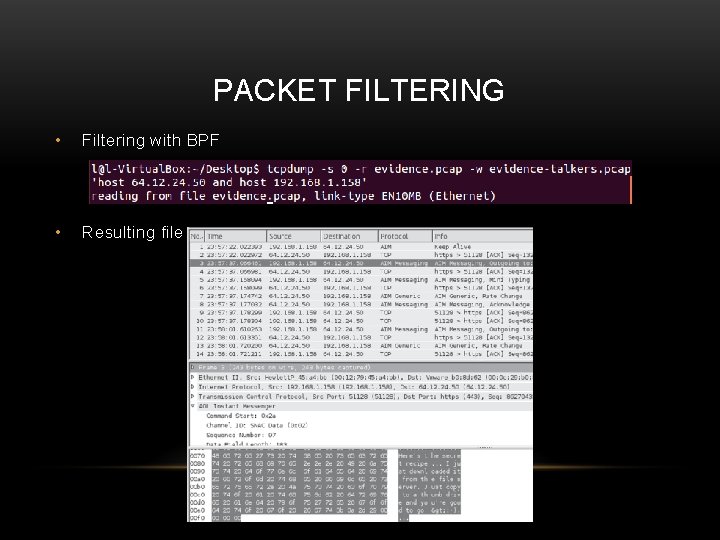
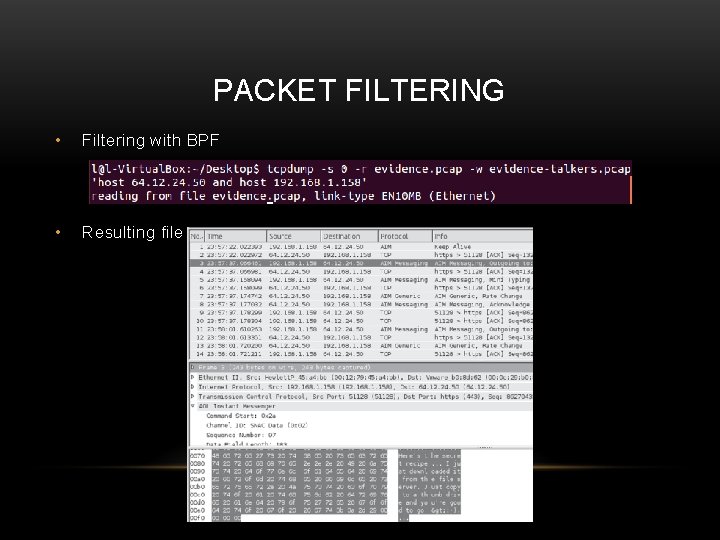
PACKET FILTERING • Filtering with BPF • Resulting file
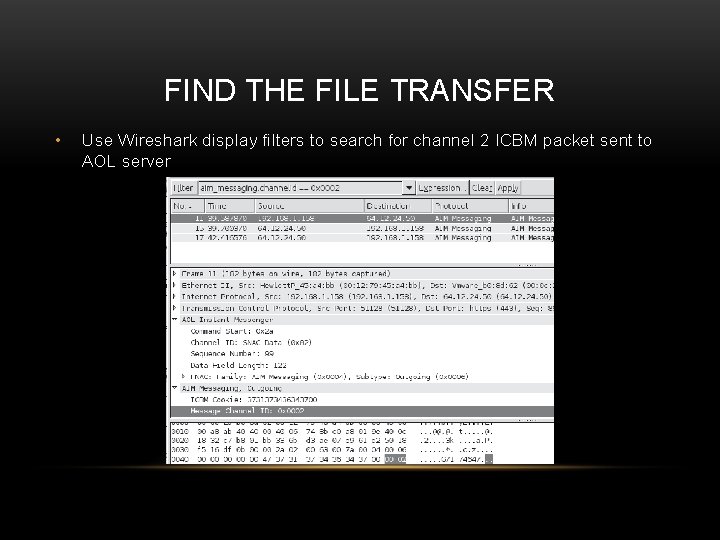
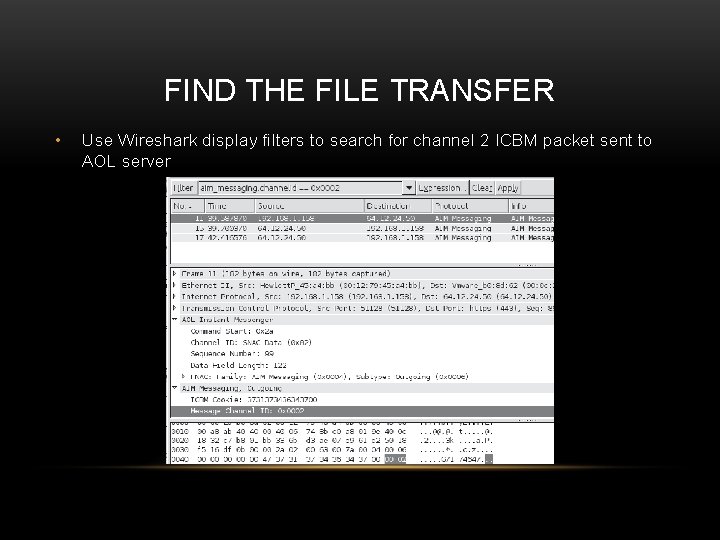
FIND THE FILE TRANSFER • Use Wireshark display filters to search for channel 2 ICBM packet sent to AOL server
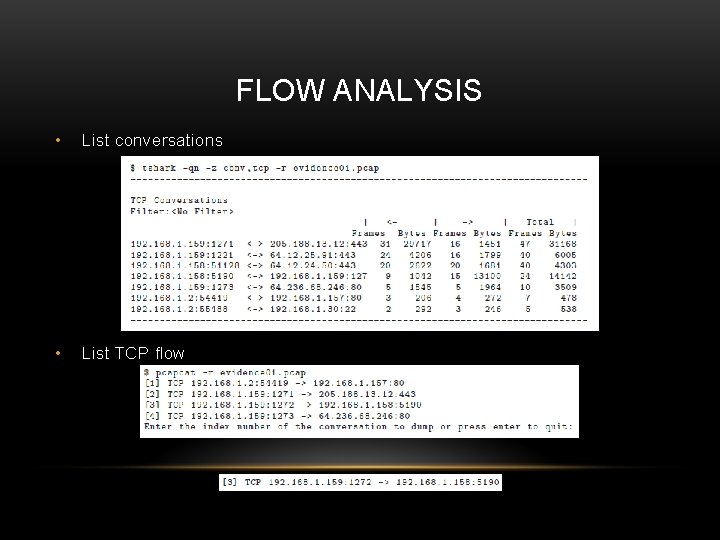
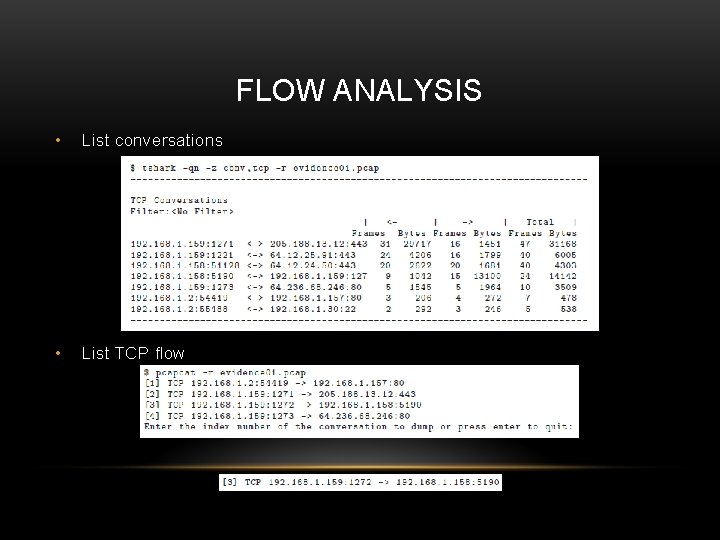
FLOW ANALYSIS • List conversations • List TCP flow
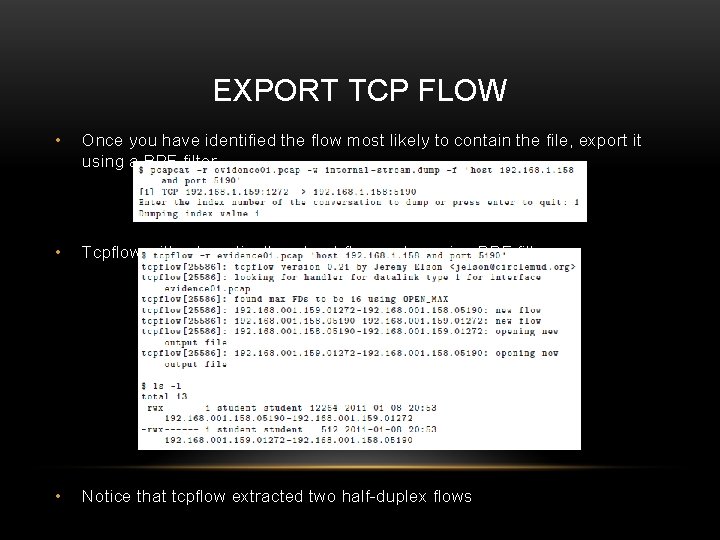
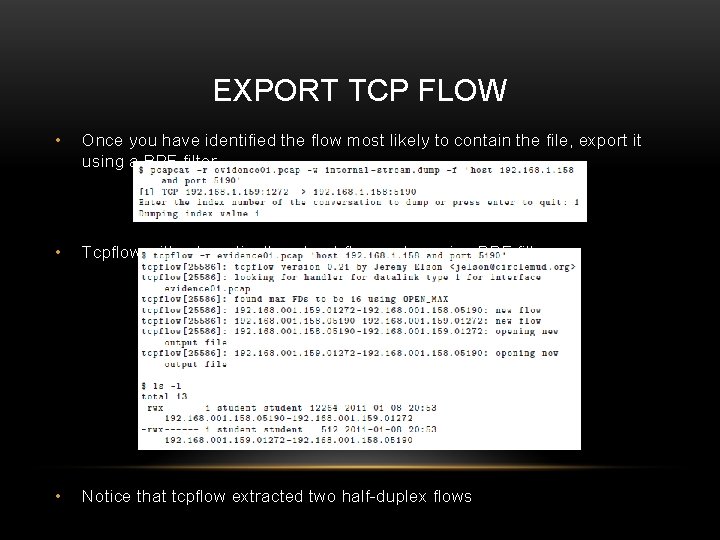
EXPORT TCP FLOW • Once you have identified the flow most likely to contain the file, export it using a BPF filter • Tcpflow will automatically extract flows, also using BPF filter • Notice that tcpflow extracted two half-duplex flows
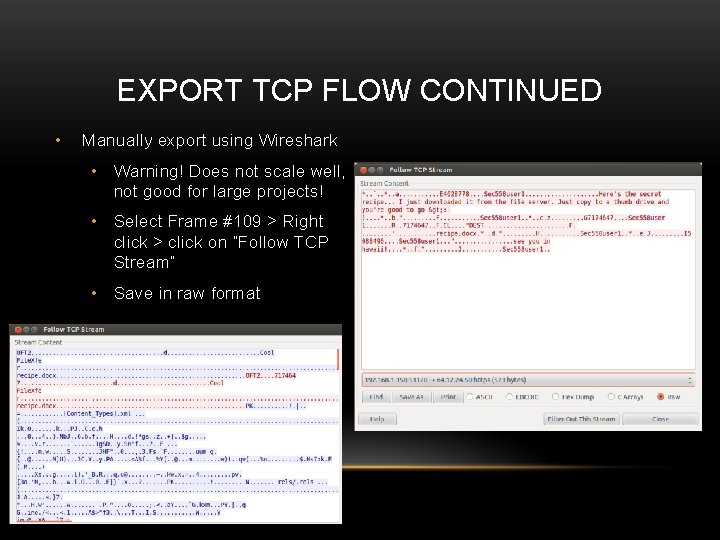
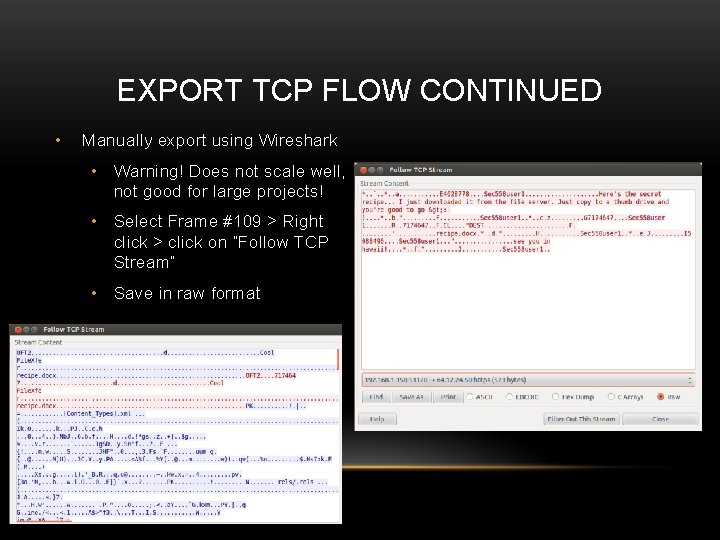
EXPORT TCP FLOW CONTINUED • Manually export using Wireshark • Warning! Does not scale well, not good for large projects! • Select Frame #109 > Right click > click on “Follow TCP Stream” • Save in raw format
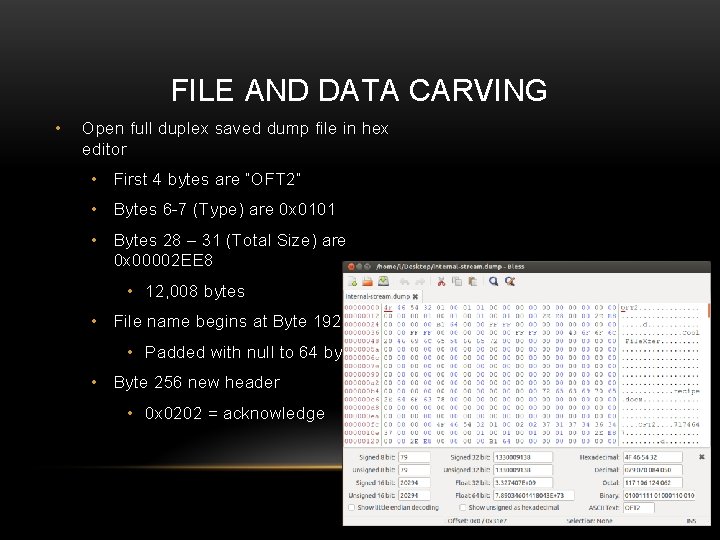
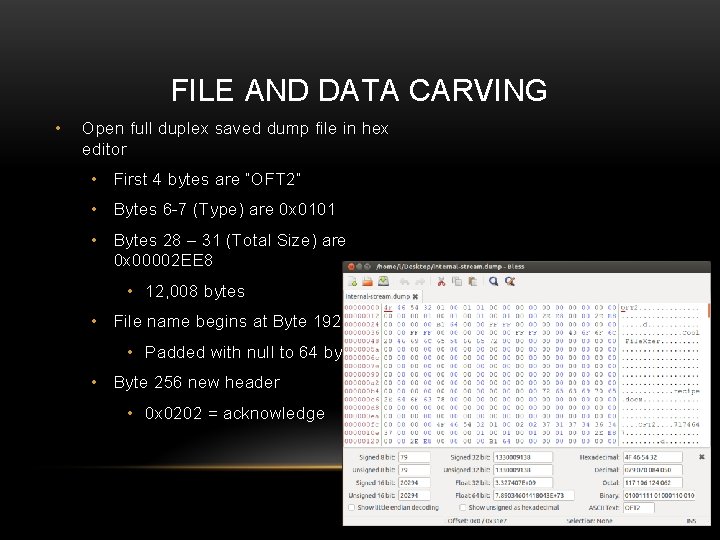
FILE AND DATA CARVING • Open full duplex saved dump file in hex editor • First 4 bytes are “OFT 2” • Bytes 6 -7 (Type) are 0 x 0101 • Bytes 28 – 31 (Total Size) are 0 x 00002 EE 8 • 12, 008 bytes • File name begins at Byte 192 0 xc 0 • Padded with null to 64 bytes • Byte 256 new header • 0 x 0202 = acknowledge
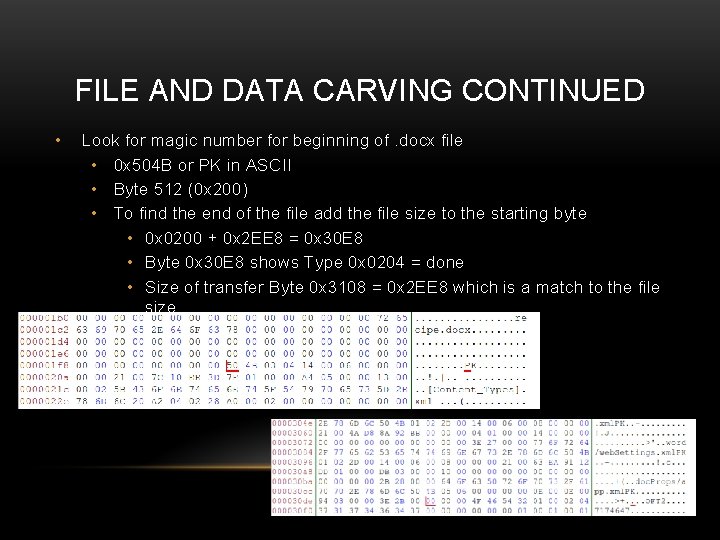
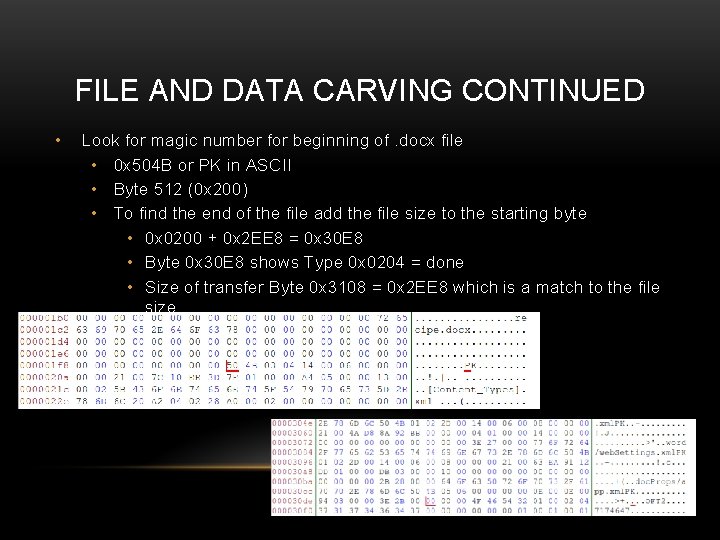
FILE AND DATA CARVING CONTINUED • Look for magic number for beginning of. docx file • 0 x 504 B or PK in ASCII • Byte 512 (0 x 200) • To find the end of the file add the file size to the starting byte • 0 x 0200 + 0 x 2 EE 8 = 0 x 30 E 8 • Byte 0 x 30 E 8 shows Type 0 x 0204 = done • Size of transfer Byte 0 x 3108 = 0 x 2 EE 8 which is a match to the file size
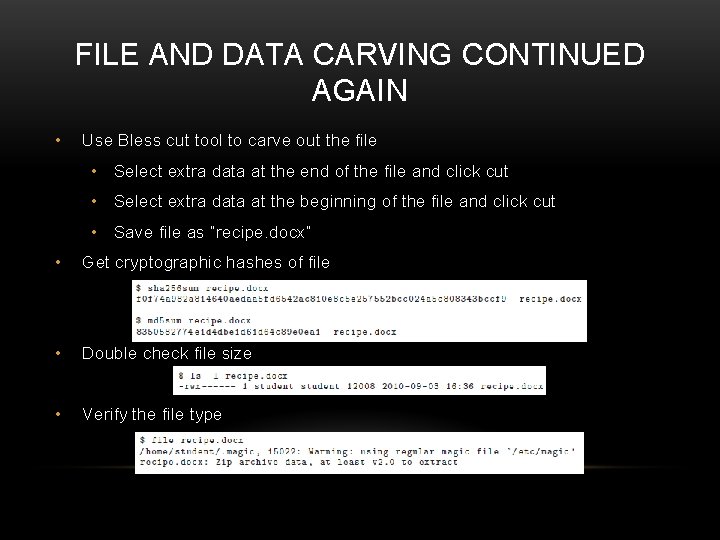
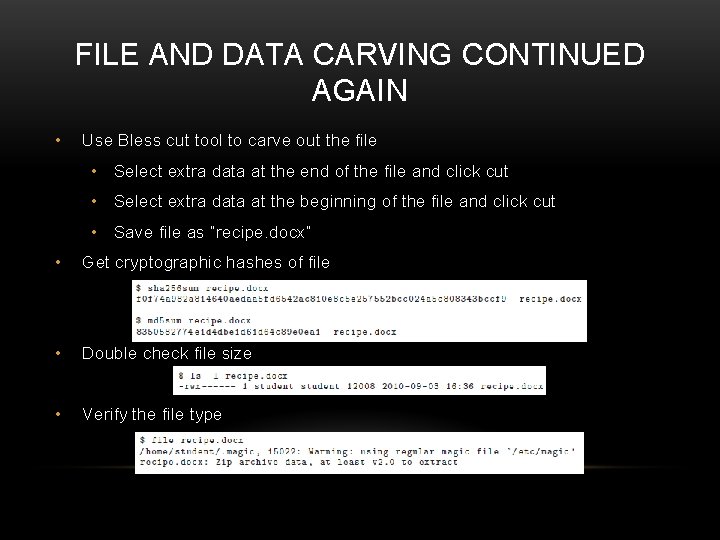
FILE AND DATA CARVING CONTINUED AGAIN • Use Bless cut tool to carve out the file • Select extra data at the end of the file and click cut • Select extra data at the beginning of the file and click cut • Save file as “recipe. docx” • Get cryptographic hashes of file • Double check file size • Verify the file type
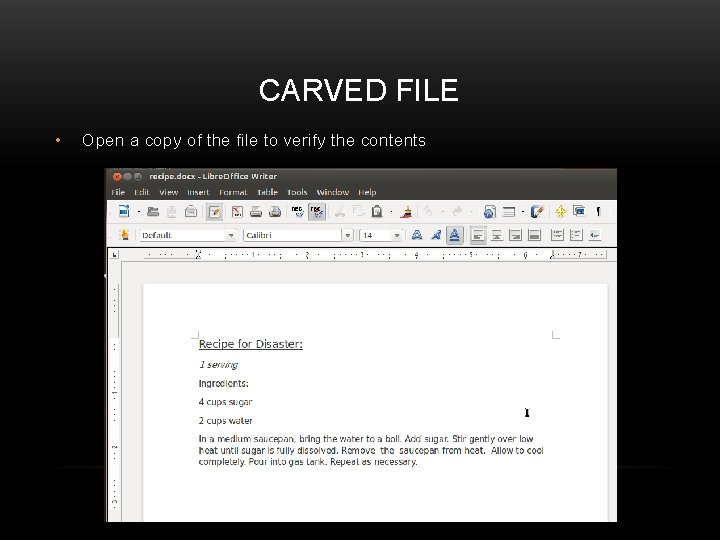
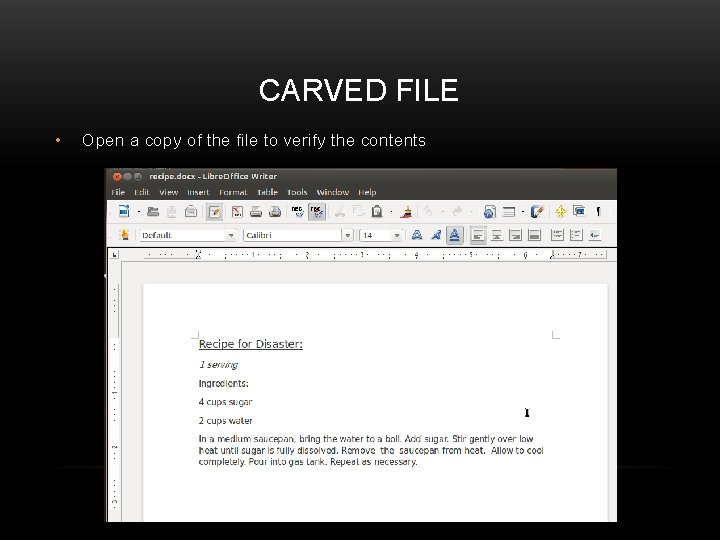
CARVED FILE • Open a copy of the file to verify the contents
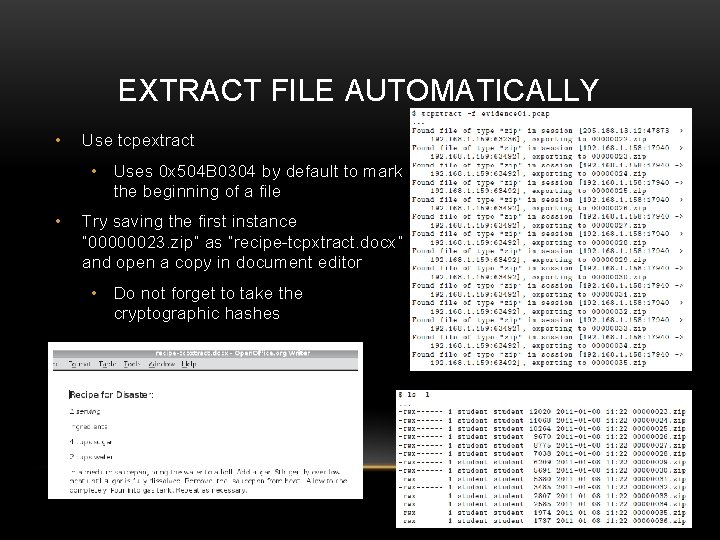
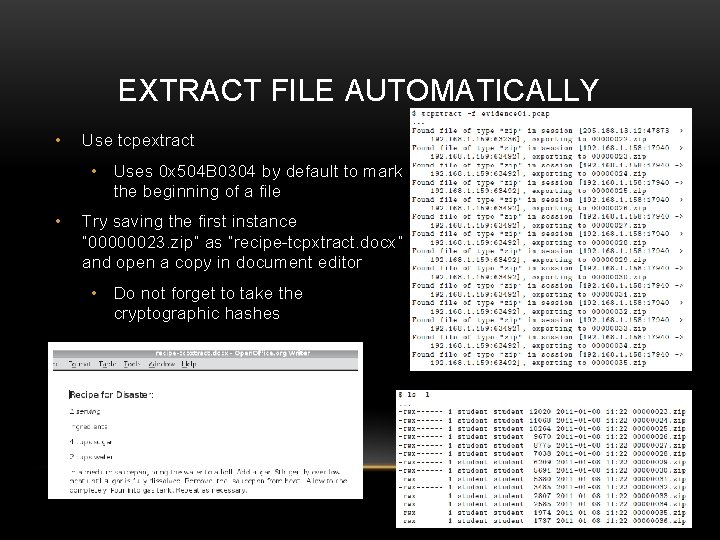
EXTRACT FILE AUTOMATICALLY • Use tcpextract • Uses 0 x 504 B 0304 by default to mark the beginning of a file • Try saving the first instance “ 00000023. zip” as “recipe-tcpxtract. docx” and open a copy in document editor • Do not forget to take the cryptographic hashes
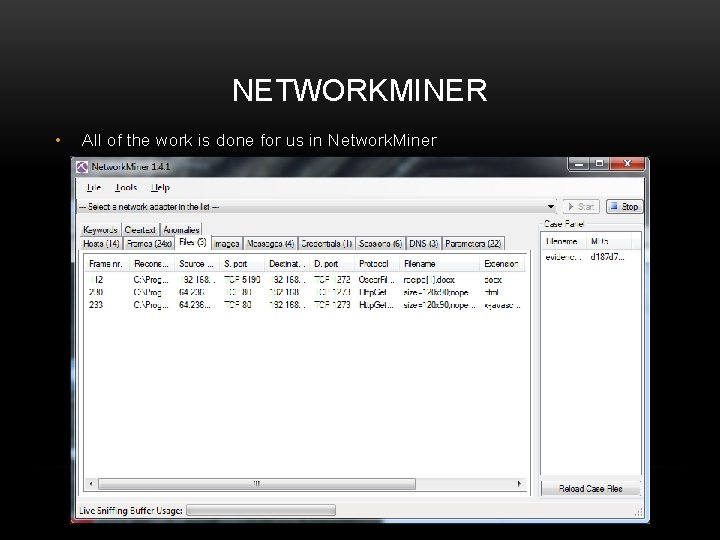
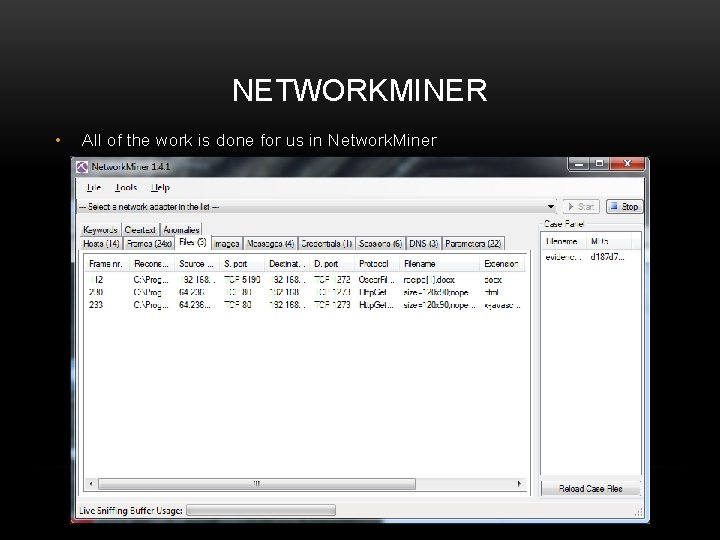
NETWORKMINER • All of the work is done for us in Network. Miner
Disclaimer: All information and data pulled directly from this book. Pages 88 - 134 Works Cited Davidoff, S. , & Ham, J. (2012). Network Forensics Tracking Hackers Through Cyberspace. Boston: Prentice Hall.