Cascaded Authorization with Anonymous Signer Aggregate Signatures Danfeng
![Aggregate signature scheme q Aggregate signature scheme [Boneh Gentry Shacham Lynn 03] l q Aggregate signature scheme q Aggregate signature scheme [Boneh Gentry Shacham Lynn 03] l q](https://slidetodoc.com/presentation_image_h2/ff60546f918ce9716ae28e714598d70b/image-9.jpg)
- Slides: 19
Cascaded Authorization with Anonymous. Signer Aggregate Signatures Danfeng Yao Department of Computer Science Brown University Joint work with Roberto Tamassia NSF grants CCF– 0311510, CNS– 0303577 and IIS– 0324846 IAW 2006
Outline q Motivation for anonymity and aggregation q Construction of Anonymous-Signer Aggregate Signature Scheme q Security properties of the scheme q Applications 2
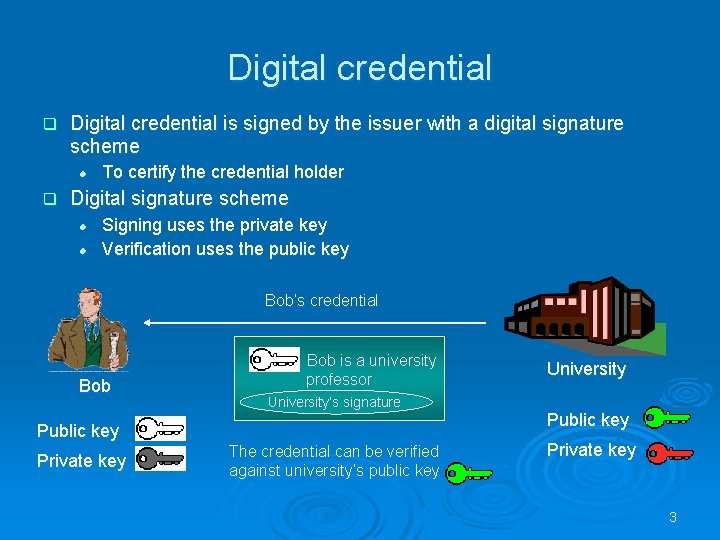
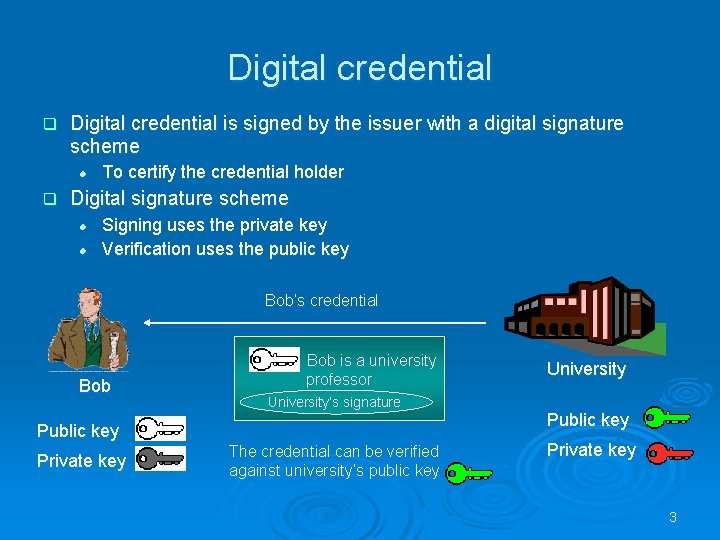
Digital credential q Digital credential is signed by the issuer with a digital signature scheme l q To certify the credential holder Digital signature scheme l l Signing uses the private key Verification uses the public key Bob’s credential Bob is a university professor University’s signature Public key Private key The credential can be verified against university’s public key University Public key Private key 3
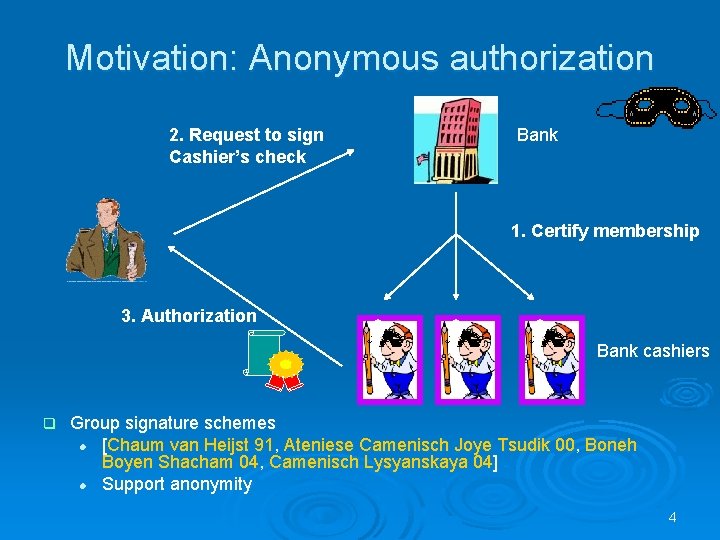
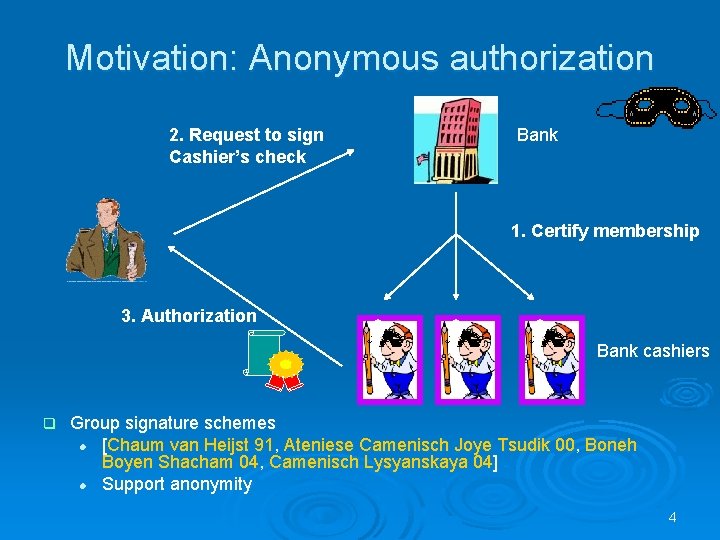
Motivation: Anonymous authorization 2. Request to sign Cashier’s check Bank 1. Certify membership 3. Authorization Bank cashiers q Group signature schemes l [Chaum van Heijst 91, Ateniese Camenisch Joye Tsudik 00, Boneh Boyen Shacham 04, Camenisch Lysyanskaya 04] l Support anonymity 4
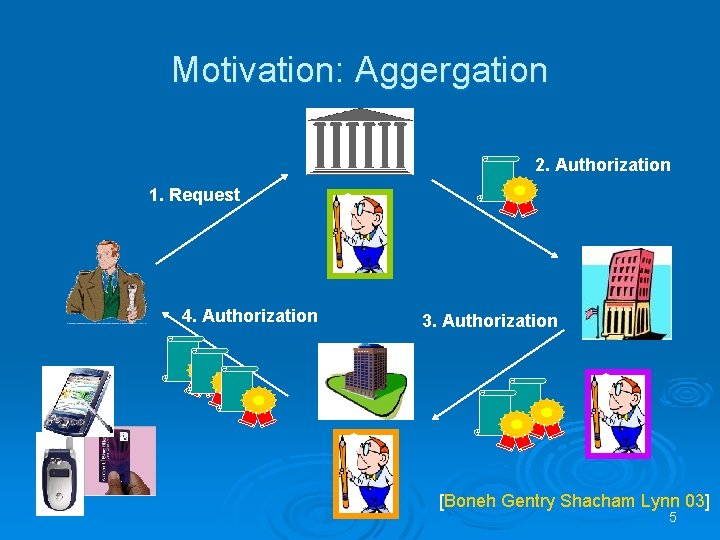
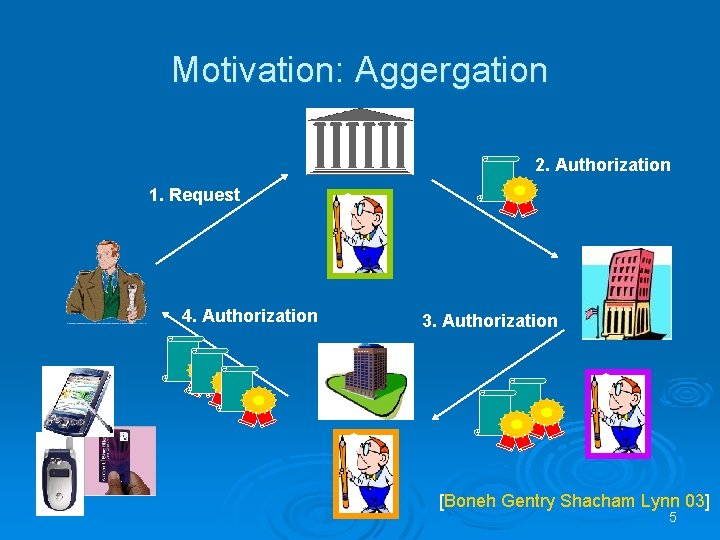
Motivation: Aggergation 2. Authorization 1. Request 4. Authorization 3. Authorization [Boneh Gentry Shacham Lynn 03] 5
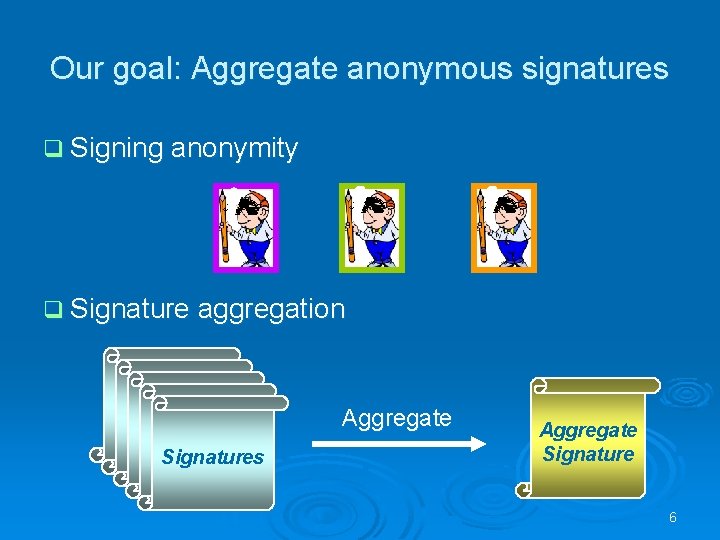
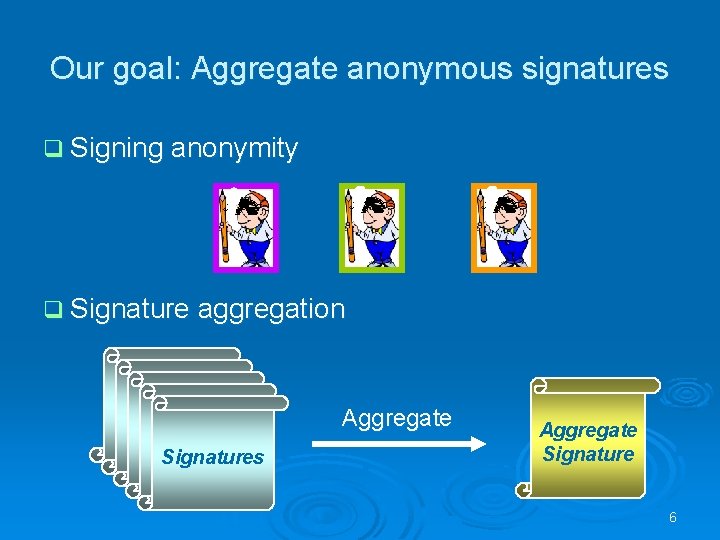
Our goal: Aggregate anonymous signatures q Signing anonymity q Signature aggregation Delegation Signatures Aggregate Signature 6
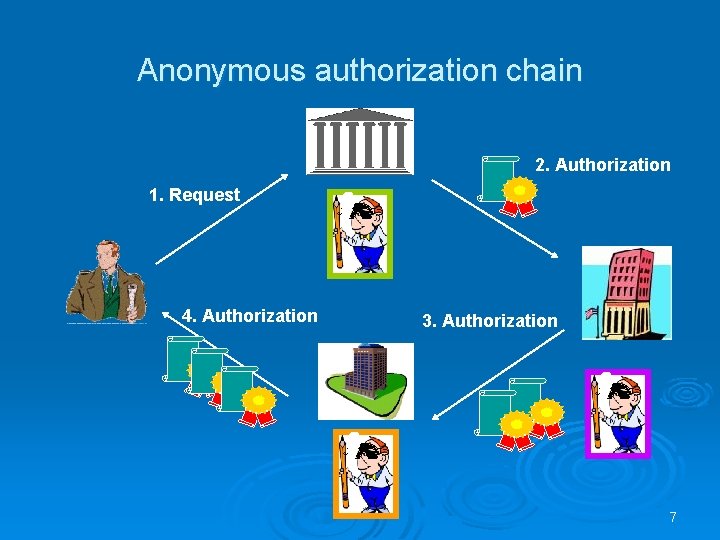
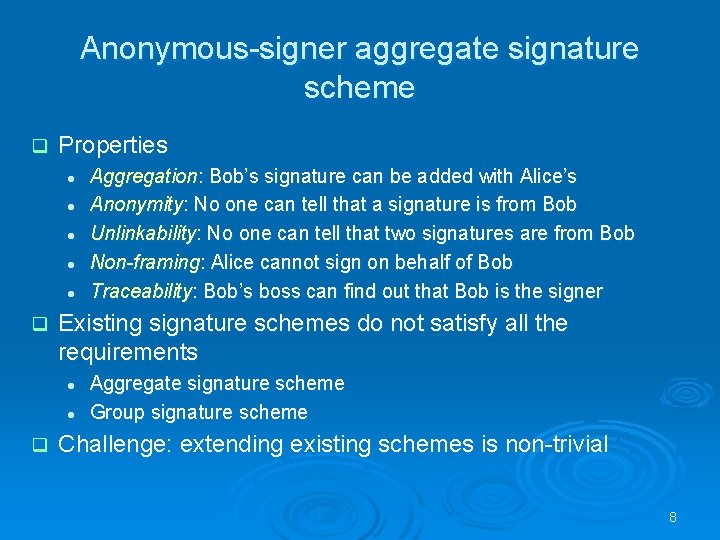
Anonymous authorization chain 2. Authorization 1. Request 4. Authorization 3. Authorization 7
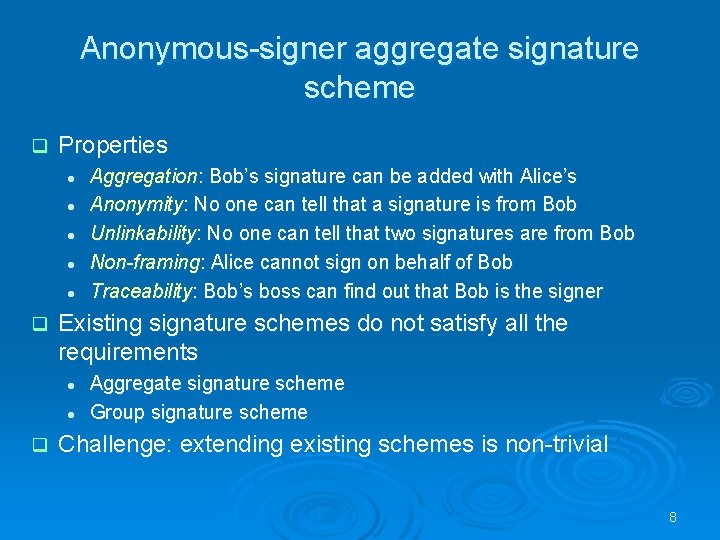
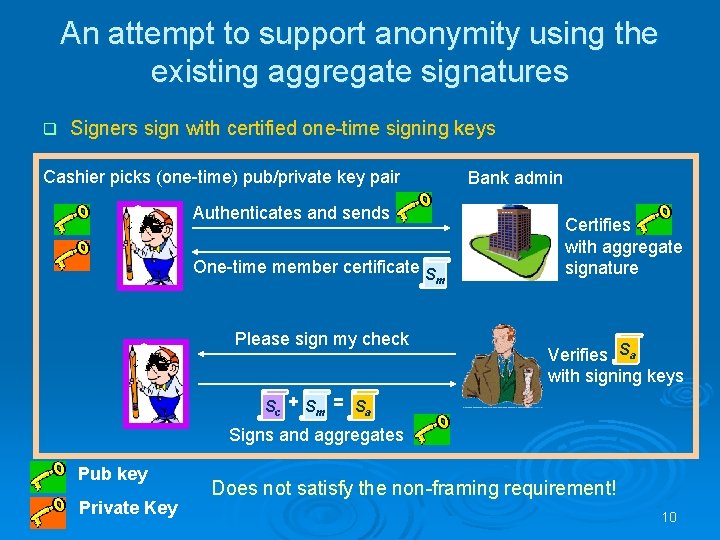
Anonymous-signer aggregate signature scheme q Properties l l l q Existing signature schemes do not satisfy all the requirements l l q Aggregation: Bob’s signature can be added with Alice’s Anonymity: No one can tell that a signature is from Bob Unlinkability: No one can tell that two signatures are from Bob Non-framing: Alice cannot sign on behalf of Bob Traceability: Bob’s boss can find out that Bob is the signer Aggregate signature scheme Group signature scheme Challenge: extending existing schemes is non-trivial 8
![Aggregate signature scheme q Aggregate signature scheme Boneh Gentry Shacham Lynn 03 l q Aggregate signature scheme q Aggregate signature scheme [Boneh Gentry Shacham Lynn 03] l q](https://slidetodoc.com/presentation_image_h2/ff60546f918ce9716ae28e714598d70b/image-9.jpg)
Aggregate signature scheme q Aggregate signature scheme [Boneh Gentry Shacham Lynn 03] l q The size of signatures and public keys 170 bits with security comparable to 1024 bit RSA and 320 bit DSA schemes Verification is linear in the number of individual signatures PK 1, SK 1 Bob PK 2, SK 2 Sign m 1 S 1 Bob aggregates Alice PK 3, SK 3 Sign m 2 S 2 Eve Sign m 3 S 1 + S 2 + S 3 = SA How to make the aggregate signature scheme support anonymity? 9
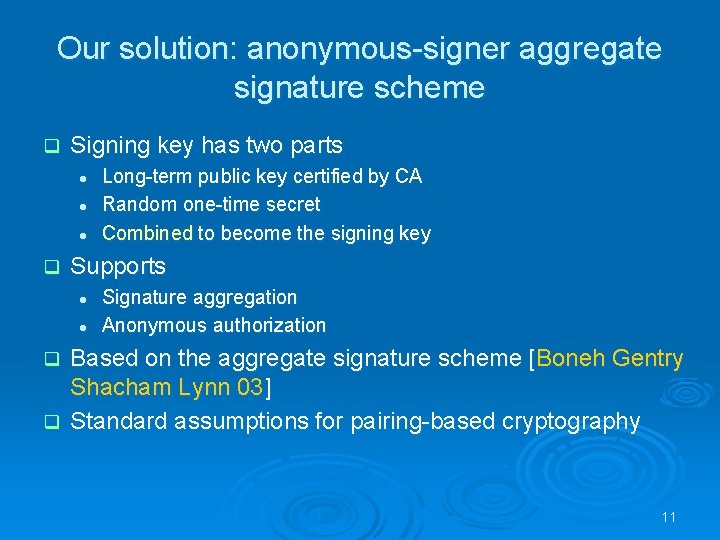
An attempt to support anonymity using the existing aggregate signatures q Signers sign with certified one-time signing keys Cashier picks (one-time) pub/private key pair Bank admin Authenticates and sends One-time member certificate S Please sign my check m Certifies with aggregate signature Verifies Sa with signing keys Sc + Sm = Sa Signs and aggregates Pub key Private Key Does not satisfy the non-framing requirement! 10
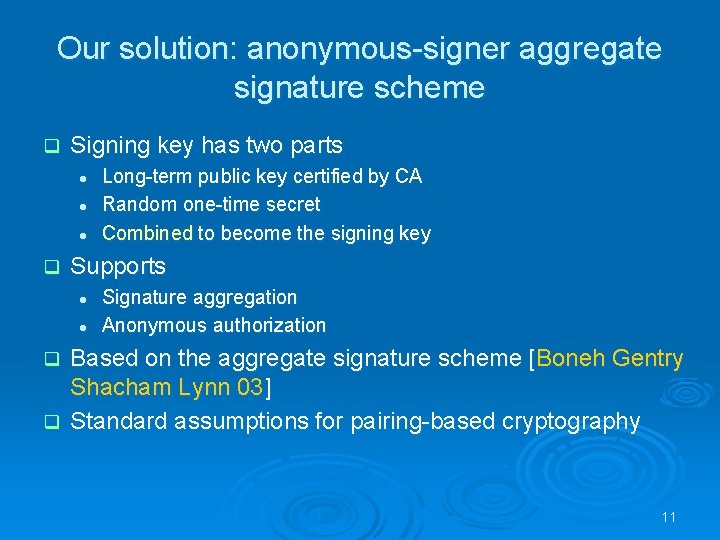
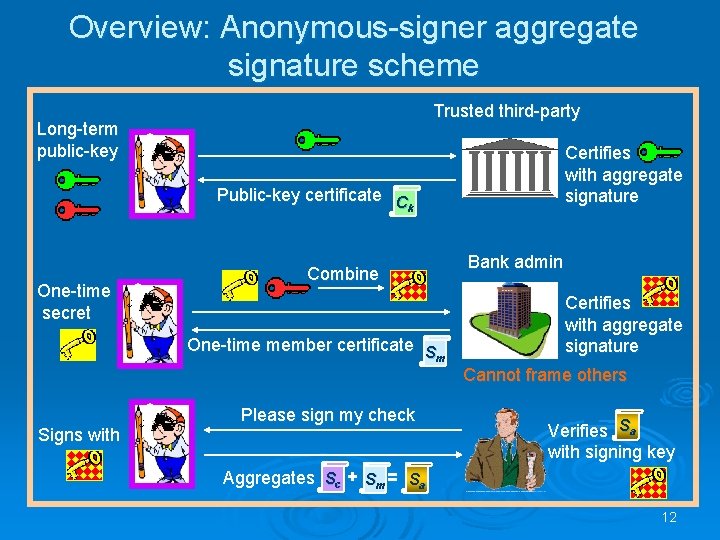
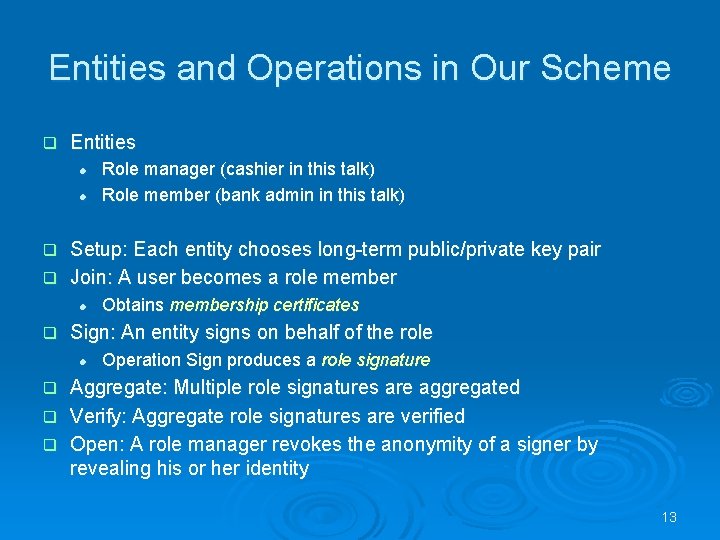
Our solution: anonymous-signer aggregate signature scheme q Signing key has two parts l l l q Long-term public key certified by CA Random one-time secret Combined to become the signing key Supports l l Signature aggregation Anonymous authorization Based on the aggregate signature scheme [Boneh Gentry Shacham Lynn 03] q Standard assumptions for pairing-based cryptography q 11
Overview: Anonymous-signer aggregate signature scheme Trusted third-party Long-term public-key Certifies with aggregate signature Public-key certificate C k One-time secret Combine One-time member certificate S m Bank admin Certifies with aggregate signature Cannot frame others Signs with Please sign my check Verifies Sa with signing key Aggregates Sc + Sm = Sa 12
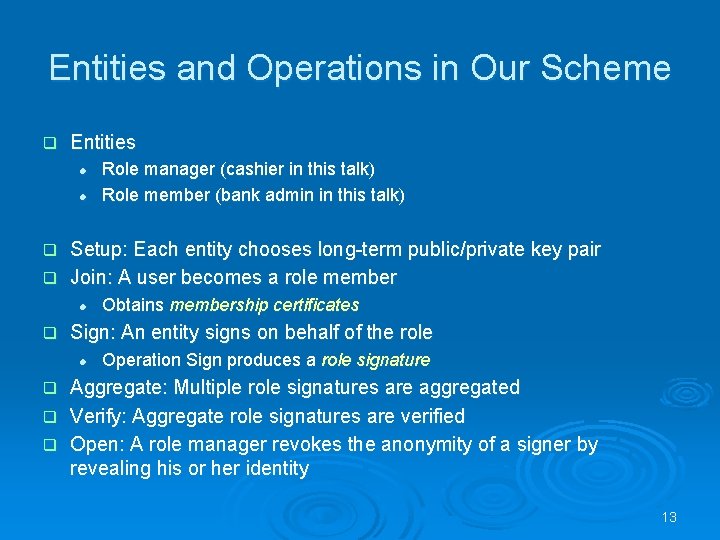
Entities and Operations in Our Scheme q Entities l l Role manager (cashier in this talk) Role member (bank admin in this talk) Setup: Each entity chooses long-term public/private key pair q Join: A user becomes a role member q l q Obtains membership certificates Sign: An entity signs on behalf of the role l Operation Sign produces a role signature Aggregate: Multiple role signatures are aggregated q Verify: Aggregate role signatures are verified q Open: A role manager revokes the anonymity of a signer by revealing his or her identity q 13
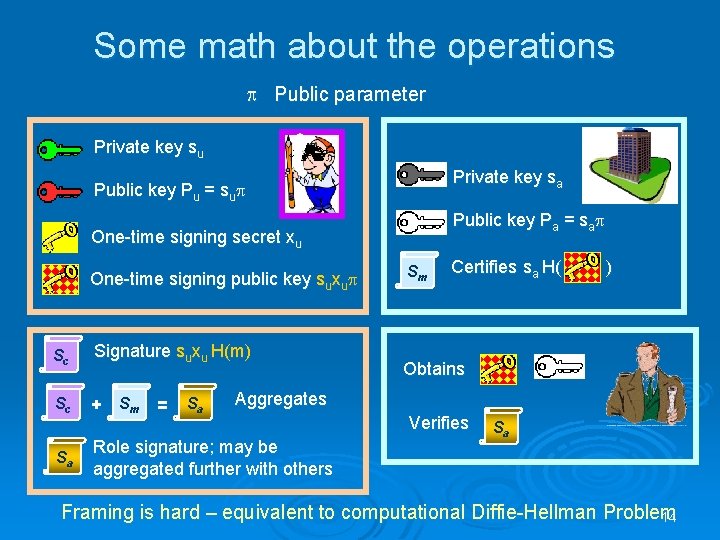
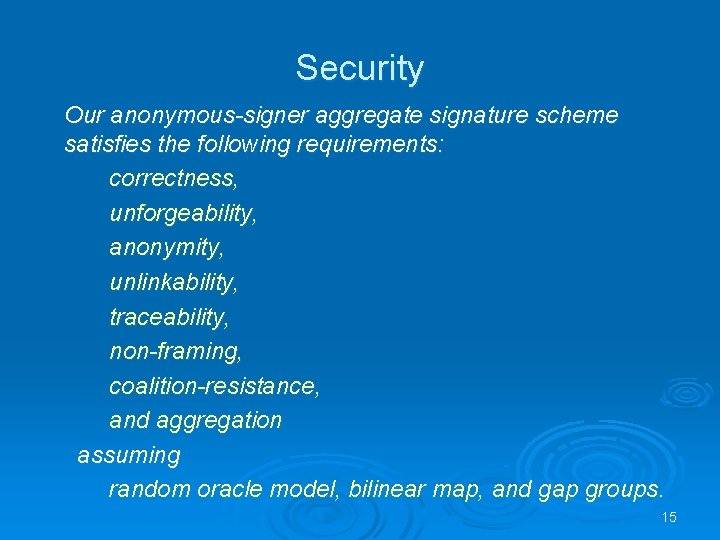
Some math about the operations Public parameter Private key su Private key sa Public key Pu = su Public key Pa = sa One-time signing secret xu One-time signing public key suxu Sc Signature suxu H(m) Sc + Sm = Sa Sa Sm Certifies sa H( ) Obtains Aggregates Role signature; may be aggregated further with others Verifies Sa Framing is hard – equivalent to computational Diffie-Hellman Problem 14 14
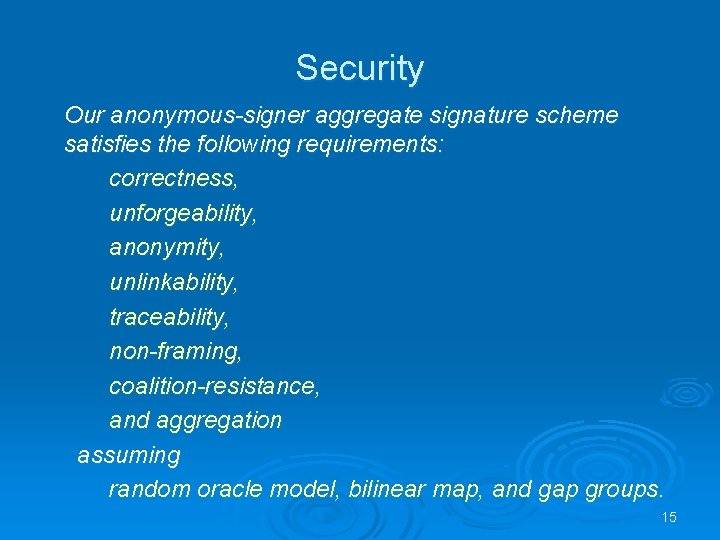
Security Our anonymous-signer aggregate signature scheme satisfies the following requirements: correctness, unforgeability, anonymity, unlinkability, traceability, non-framing, coalition-resistance, and aggregation assuming random oracle model, bilinear map, and gap groups. 15
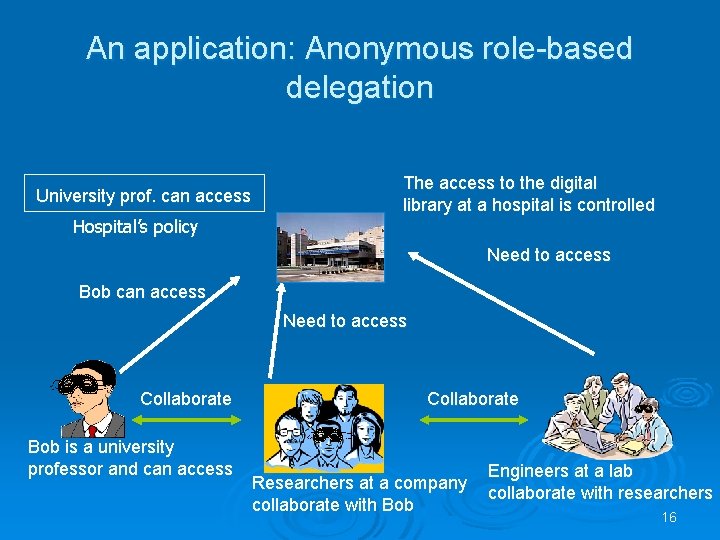
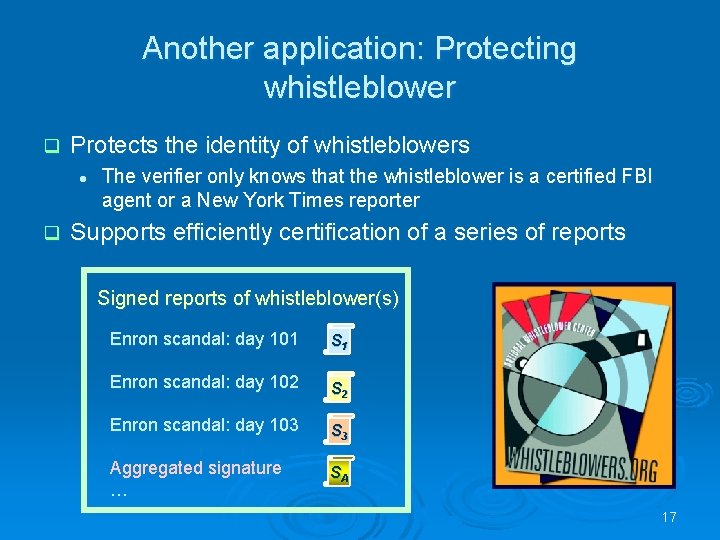
An application: Anonymous role-based delegation University prof. can access Hospital’s policy The access to the digital library at a hospital is controlled Need to access Bob can access Need to access Collaborate Bob is a university professor and can access Collaborate Researchers at a company collaborate with Bob Engineers at a lab collaborate with researchers 16
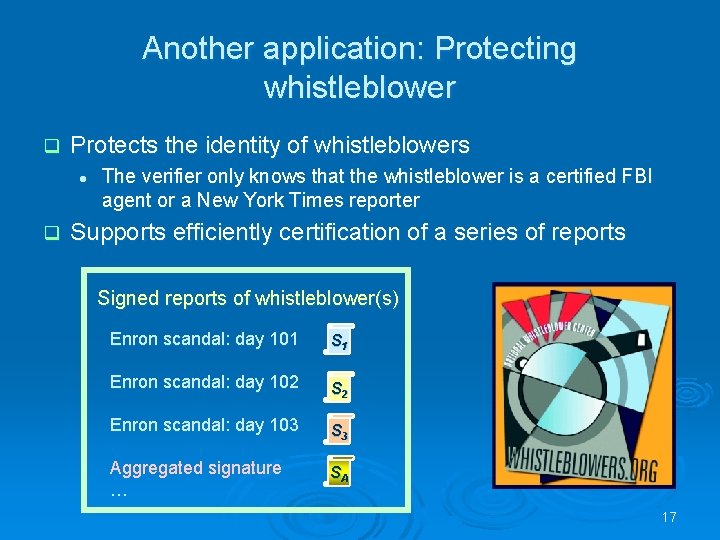
Another application: Protecting whistleblower q Protects the identity of whistleblowers l q The verifier only knows that the whistleblower is a certified FBI agent or a New York Times reporter Supports efficiently certification of a series of reports Signed reports of whistleblower(s) Enron scandal: day 101 S 1 Enron scandal: day 102 S 2 Enron scandal: day 103 S 3 Aggregated signature … SA 17
18
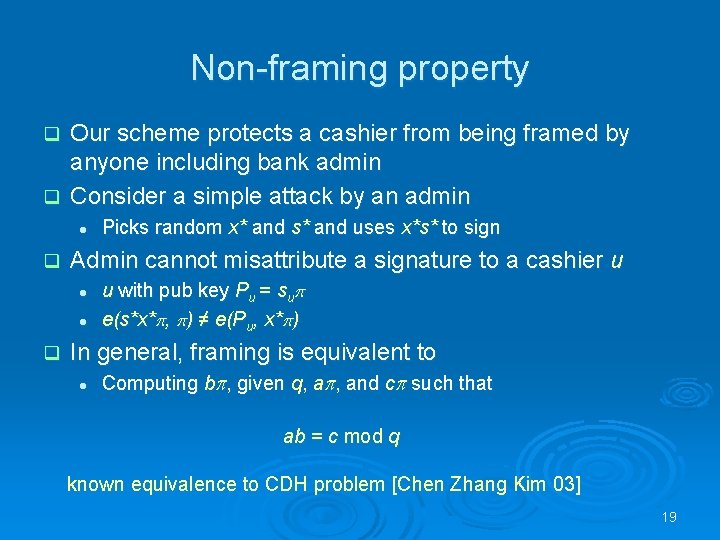
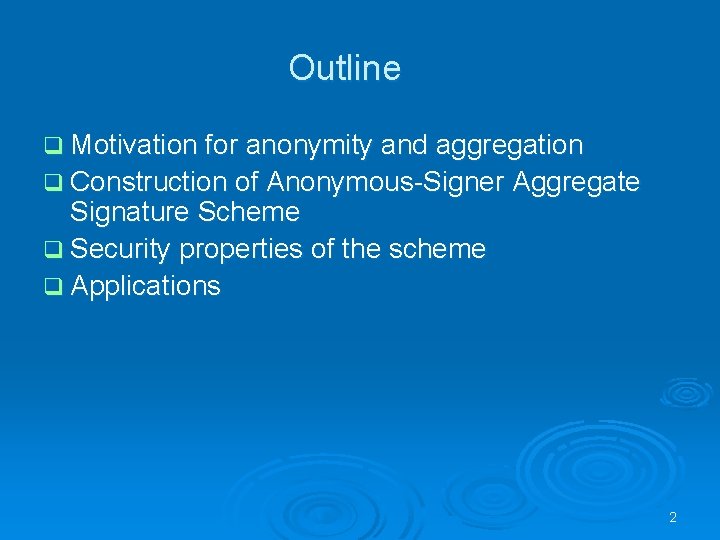
Non-framing property Our scheme protects a cashier from being framed by anyone including bank admin q Consider a simple attack by an admin q l q Admin cannot misattribute a signature to a cashier u l l q Picks random x* and s* and uses x*s* to sign u with pub key Pu = su e(s*x* , ) ≠ e(Pu, x* ) In general, framing is equivalent to l Computing b , given q, a , and c such that ab = c mod q known equivalence to CDH problem [Chen Zhang Kim 03] 19