Carnegie Mellon Worcester Polytechnic Institute Project 2 Linux
- Slides: 35
Carnegie Mellon Worcester Polytechnic Institute Project 2 Linux Kernel Hacking Professor Hugh C. Lauer CS-3013, Operating Systems (Slides include copyright materials Modern Operating Systems, 3 rd ed. , by Andrew Tanenbaum and from Operating System Concepts, 7 th and 8 th ed. , by Silbershatz, Galvin, & Gagne) CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 1
Carnegie Mellon Worcester Polytechnic Institute Objective ¢ ¢ To learn how to work inside an operating system kernel To understand some of the constraints and techniques of programming in a kernel (versus user space) CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 2
Carnegie Mellon Worcester Polytechnic Institute This Assignment ¢ ¢ Using an LKM, intercept two existing system calls in order to record information in syslog Add a new system call to get useful information from the data structures of a Linux kernel CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 3
Carnegie Mellon Worcester Polytechnic Institute Reminder – System Call ¢ ¢ A structured function call across a protection boundary between less privileged applications and more privileged operating system functions Also, across privilege layers of the operating system itself CS-3013, C-Term 2013 System Calls 4
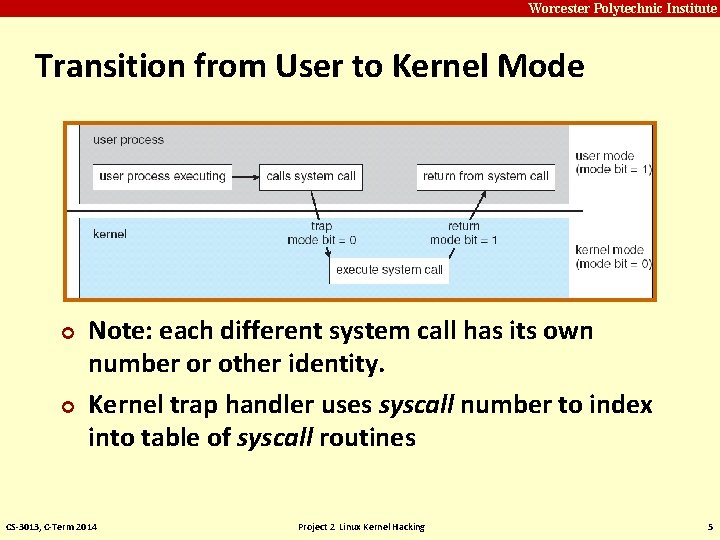
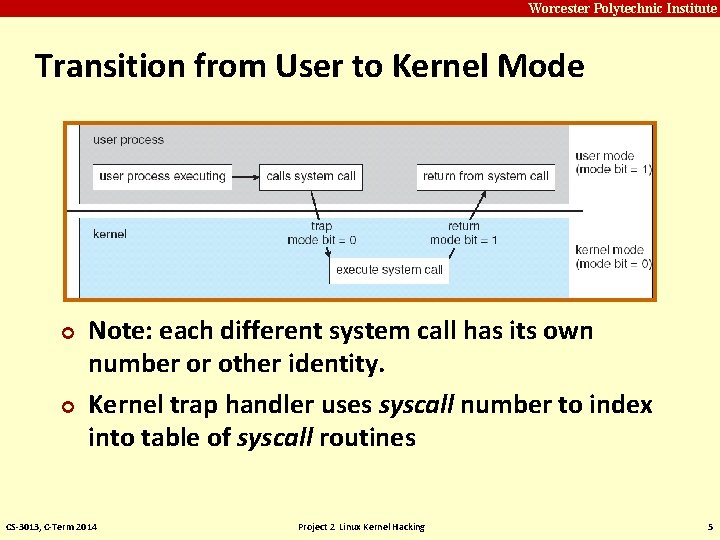
Carnegie Mellon Worcester Polytechnic Institute Transition from User to Kernel Mode ¢ ¢ Note: each different system call has its own number or other identity. Kernel trap handler uses syscall number to index into table of syscall routines CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 5
Carnegie Mellon Worcester Polytechnic Institute Inside Kernel, the OS can … ¢ ¢ Read and modify data structures not in user address space Control devices and hardware settings forbidden to user processes Invoke operating system functions not available to user processes Access address of space of invoking process CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 6
Carnegie Mellon Worcester Polytechnic Institute Accessing the Kernel via System Call ¢ Normally embedded within a library routine § ¢ System call mechanism is machine specific § ¢ User APIs generally don’t make system calls directly Different CPU architectures make system calls in different ways System call numbers different for various architectures Even for same operating system & version! § E. g. , poll system call is #167 on Power. PC but #168 on Intel 386 platforms (in SUSE Linux 9. 3) § CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 7
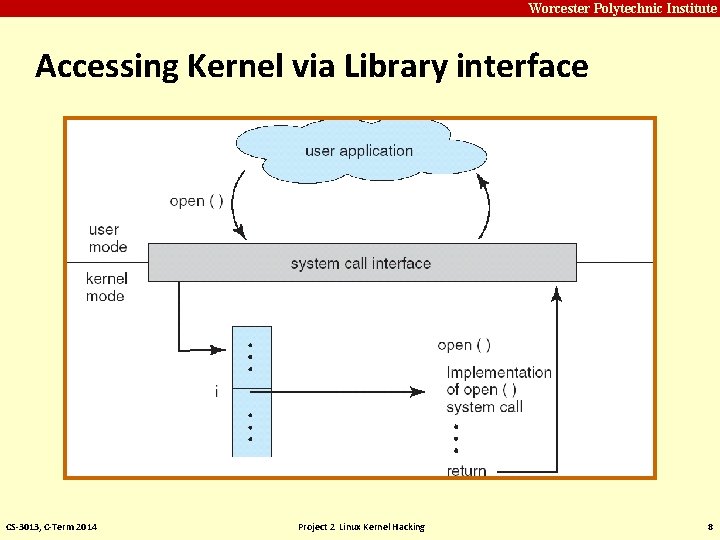
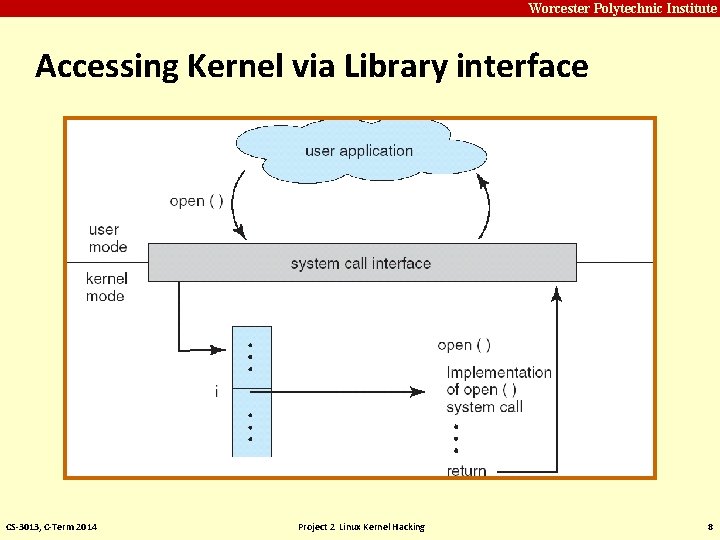
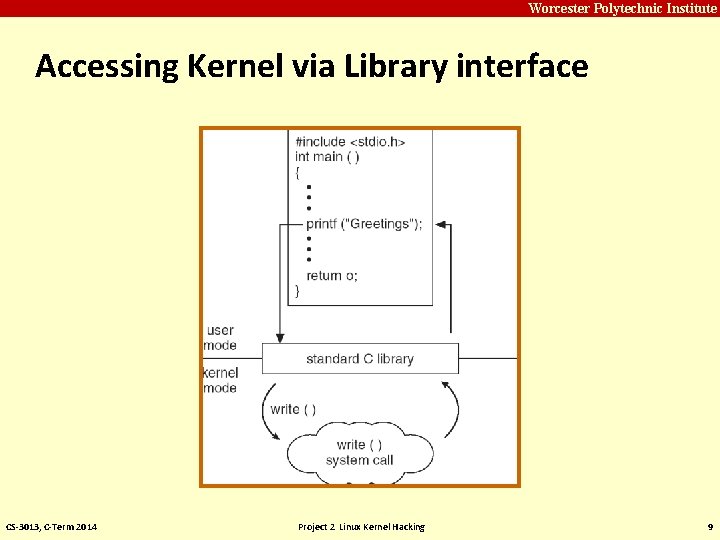
Carnegie Mellon Worcester Polytechnic Institute Accessing Kernel via Library interface CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 8
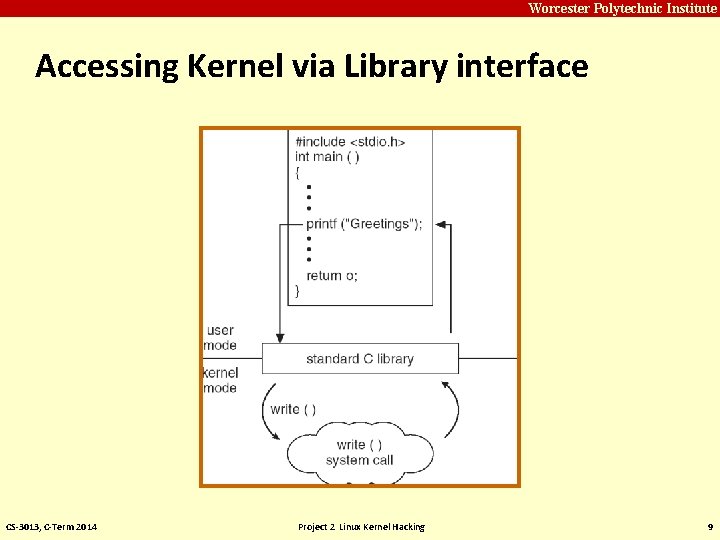
Carnegie Mellon Worcester Polytechnic Institute Accessing Kernel via Library interface CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 9
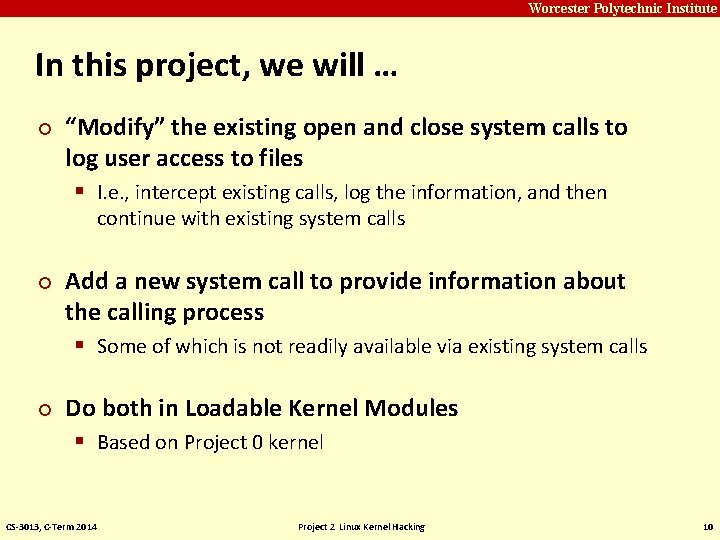
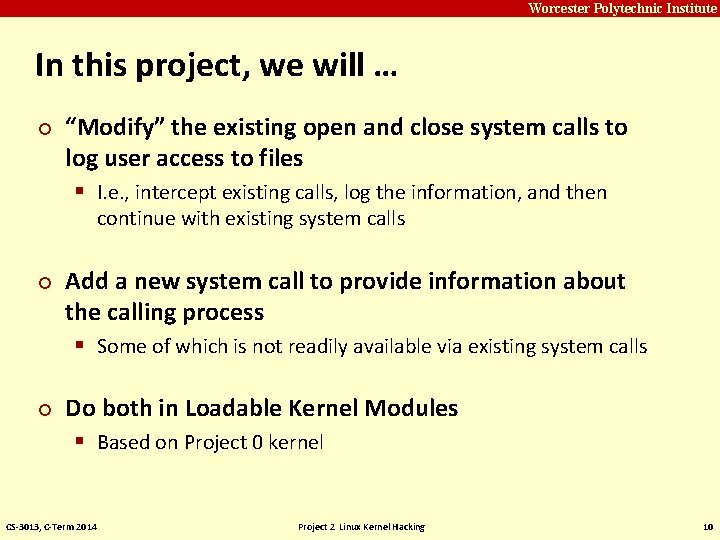
Carnegie Mellon Worcester Polytechnic Institute In this project, we will … ¢ “Modify” the existing open and close system calls to log user access to files § I. e. , intercept existing calls, log the information, and then continue with existing system calls ¢ ¢ Add a new system call to provide information about the calling process § Some of which is not readily available via existing system calls Do both in Loadable Kernel Modules § Based on Project 0 kernel CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 10
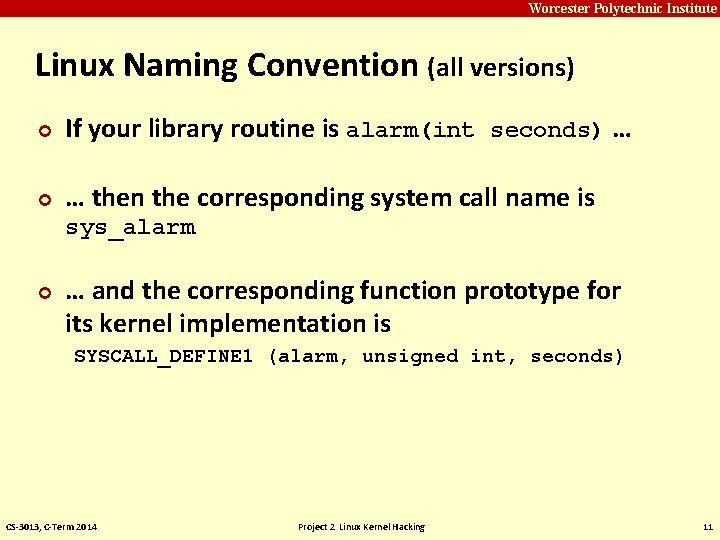
Carnegie Mellon Worcester Polytechnic Institute Linux Naming Convention (all versions) ¢ If your library routine is alarm(int seconds) … ¢ … then the corresponding system call name is sys_alarm ¢ … and the corresponding function prototype for its kernel implementation is SYSCALL_DEFINE 1 (alarm, unsigned int, seconds) CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 11
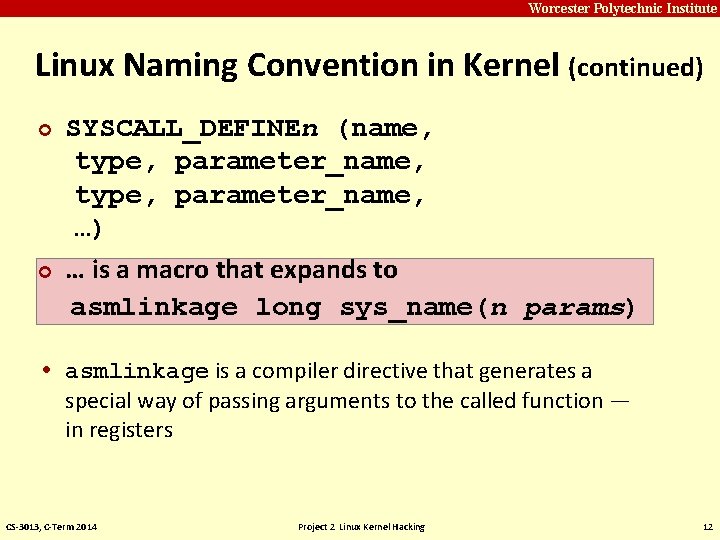
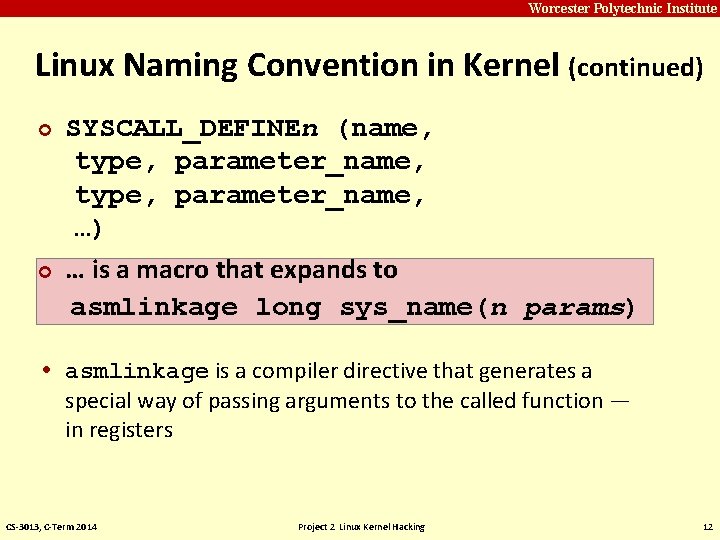
Carnegie Mellon Worcester Polytechnic Institute Linux Naming Convention in Kernel (continued) ¢ ¢ SYSCALL_DEFINEn (name, type, parameter_name, …) … is a macro that expands to asmlinkage long sys_name(n params) • asmlinkage is a compiler directive that generates a special way of passing arguments to the called function — in registers CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 12
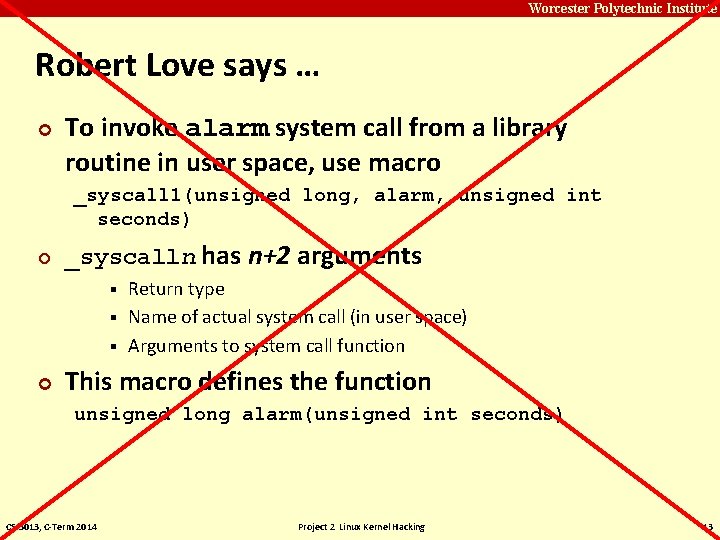
Carnegie Mellon Worcester Polytechnic Institute Robert Love says … ¢ To invoke alarm system call from a library routine in user space, use macro _syscall 1(unsigned long, alarm, unsigned int seconds) ¢ _syscalln has n+2 arguments Return type § Name of actual system call (in user space) § Arguments to system call function § ¢ This macro defines the function unsigned long alarm(unsigned int seconds) CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 13
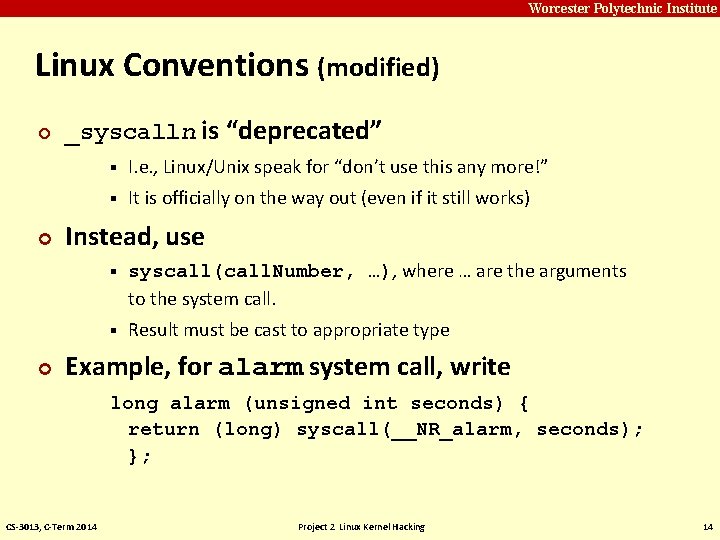
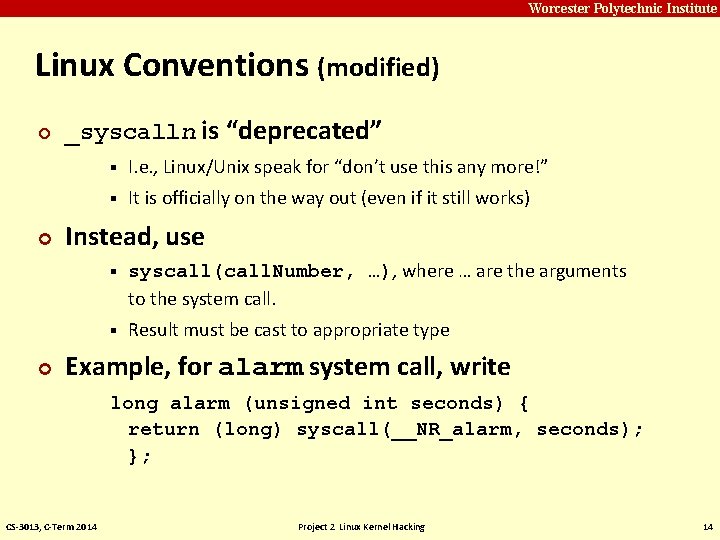
Carnegie Mellon Worcester Polytechnic Institute Linux Conventions (modified) ¢ ¢ ¢ _syscalln is “deprecated” § I. e. , Linux/Unix speak for “don’t use this any more!” § It is officially on the way out (even if it still works) Instead, use § syscall(call. Number, …), where … are the arguments to the system call. § Result must be cast to appropriate type Example, for alarm system call, write long alarm (unsigned int seconds) { return (long) syscall(__NR_alarm, seconds); }; CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 14
Carnegie Mellon Worcester Polytechnic Institute Questions? CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 15
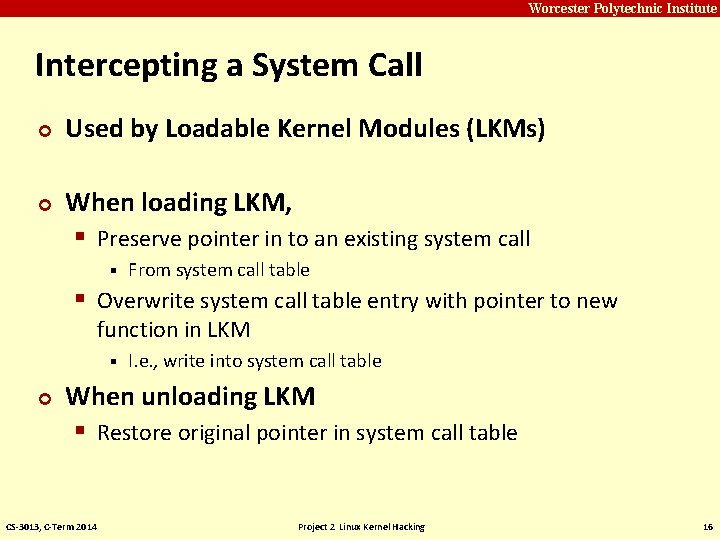
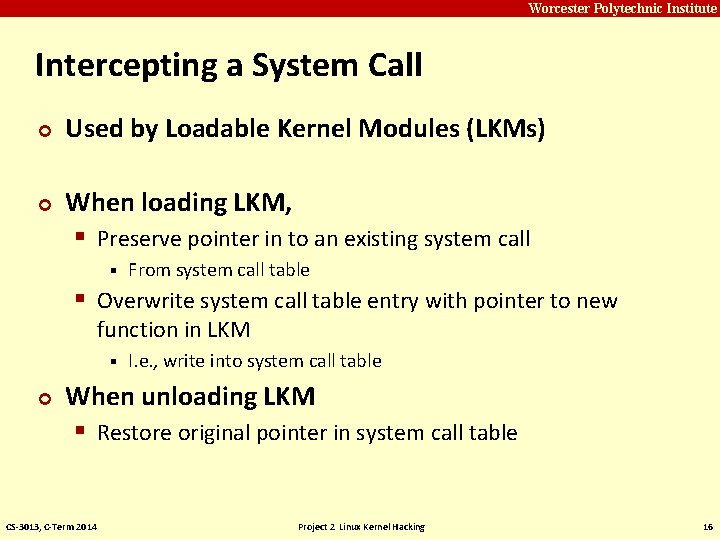
Carnegie Mellon Worcester Polytechnic Institute Intercepting a System Call ¢ ¢ Used by Loadable Kernel Modules (LKMs) When loading LKM, § Preserve pointer in to an existing system call § From system call table § Overwrite system call table entry with pointer to new function in LKM § ¢ I. e. , write into system call table When unloading LKM § Restore original pointer in system call table CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 16
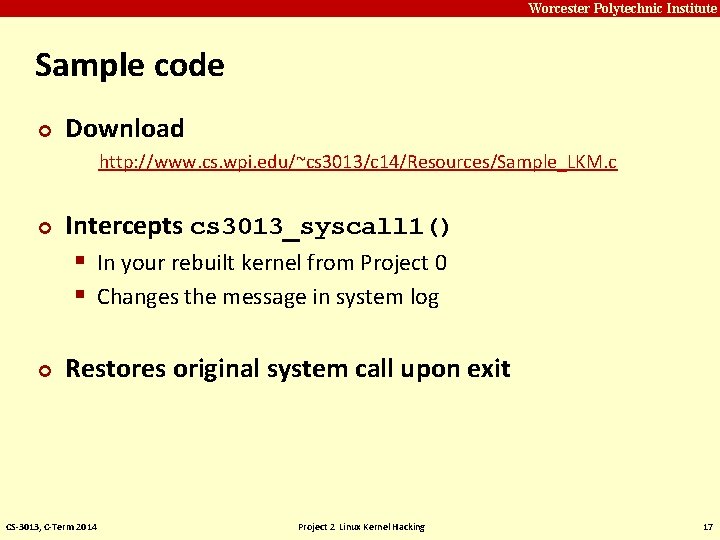
Carnegie Mellon Worcester Polytechnic Institute Sample code ¢ Download http: //www. cs. wpi. edu/~cs 3013/c 14/Resources/Sample_LKM. c ¢ ¢ Intercepts cs 3013_syscall 1() § In your rebuilt kernel from Project 0 § Changes the message in system log Restores original system call upon exit CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 17
Carnegie Mellon Worcester Polytechnic Institute Your task — Part 1 ¢ ¢ Intercept sys_open, sys_close If file/stream being opened or closed by ordinary user process, write entry in system log § And then open normally! If being opened or closed by system process, don’t write anything in system log § And then close normally! Restore original behavior when unloading LKM CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 18
Carnegie Mellon Worcester Polytechnic Institute printk() — Kernel Debug Print Tool ¢ Very robust May be called from (almost) anywhere in kernel § Same calling convention as printf() § ¢ § Writes to system log § Output survives crashes (almost all of the time) To read output, see /var/log/messages: – Circular log, newest messages at end § Read with /bin/dmesg or tail /var/log/syslog § ¢ See Linux Kernel Development, 3 rd ed. , Chapter 18 CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 19
Carnegie Mellon Worcester Polytechnic Institute Part 1 submission ¢ Your LKM ¢ Makefile to build it ¢ ¢ Test program or evidence that it works § I. e. , writes to log for ordinary users § Does not write to log for system processes § Properly unloads and restores original behavior Part 1 due Sunday, February 2 @ 11: 59 PM CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 20
Carnegie Mellon Worcester Polytechnic Institute Questions on Part 1? CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 21
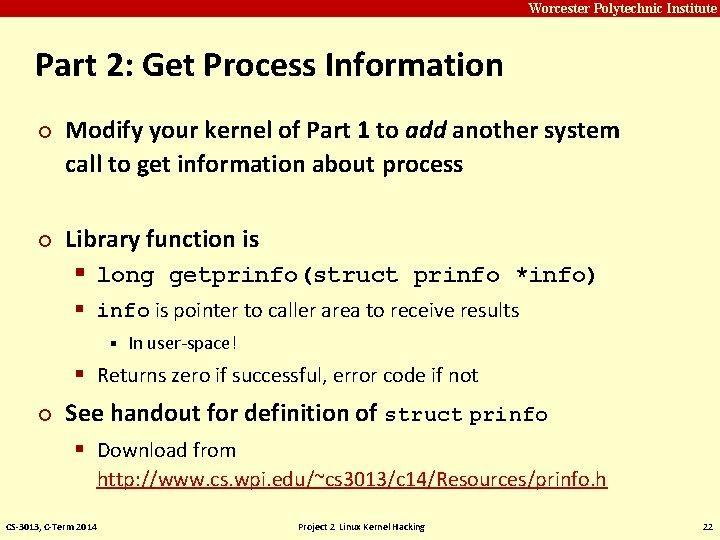
Carnegie Mellon Worcester Polytechnic Institute Part 2: Get Process Information ¢ ¢ Modify your kernel of Part 1 to add another system call to get information about process Library function is § long getprinfo(struct prinfo *info) § info is pointer to caller area to receive results § In user-space! § Returns zero if successful, error code if not ¢ See handout for definition of struct prinfo § Download from http: //www. cs. wpi. edu/~cs 3013/c 14/Resources/prinfo. h CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 22
Carnegie Mellon Worcester Polytechnic Institute Two-person Teams (optional) ¢ You may do Part 2 in two-person teams. ¢ Please register your team with instructor Submit only once for the team § Both members share the same grade for Part 2 § ¢ Academic honesty with respect to teams — all members must carry roughly equal shares of the effort CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 23
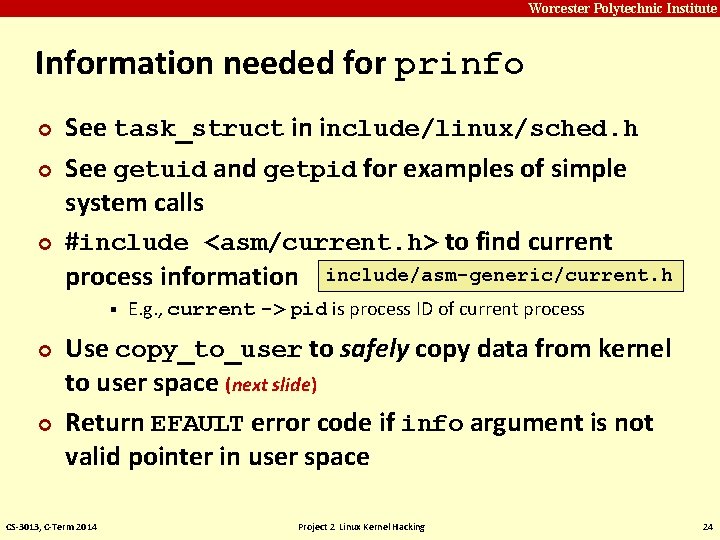
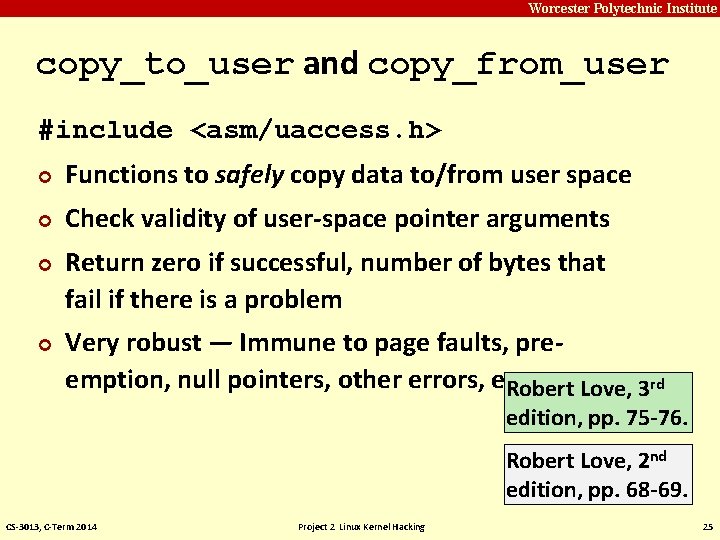
Carnegie Mellon Worcester Polytechnic Institute Information needed for prinfo ¢ ¢ ¢ See task_struct in include/linux/sched. h See getuid and getpid for examples of simple system calls #include <asm/current. h> to find current process information include/asm-generic/current. h § ¢ ¢ E. g. , current -> pid is process ID of current process Use copy_to_user to safely copy data from kernel to user space (next slide) Return EFAULT error code if info argument is not valid pointer in user space CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 24
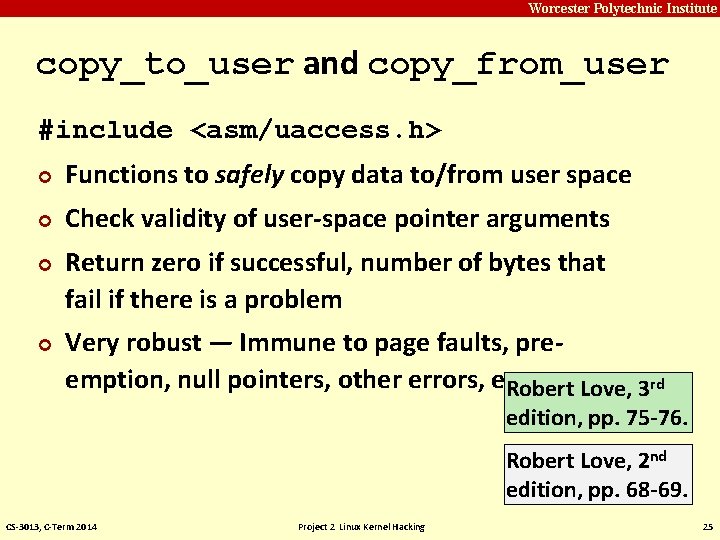
Carnegie Mellon Worcester Polytechnic Institute copy_to_user and copy_from_user #include <asm/uaccess. h> ¢ Functions to safely copy data to/from user space ¢ Check validity of user-space pointer arguments ¢ ¢ Return zero if successful, number of bytes that fail if there is a problem Very robust — Immune to page faults, preemption, null pointers, other errors, etc. Robert Love, 3 rd edition, pp. 75 -76. Robert Love, 2 nd edition, pp. 68 -69. CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 25
Carnegie Mellon Worcester Polytechnic Institute Implementing getprinfo System Call ¢ ¢ ¢ Intercept cs 3013_syscall 1 system call from Project 0 Implement LKM sys_getprinfo. c Use printk() to print debugging statements to system log § For your debugging convenience CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 26
Carnegie Mellon Worcester Polytechnic Institute More on getprinfo ¢ Most of the information is easy ¢ Can be obtained from task_struct of process ¢ Siblings and children are harder — ¢ § Involve Linux kernel list traversal macros § See handout; also Ch 6 of Linux Kernel Development Suggestion: – get everything else working before attempting to master these CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 27
Carnegie Mellon Worcester Polytechnic Institute Still more on getprinfo ¢ ¢ Times are maintained in an internal representation called jiffies Convert to microseconds using cputime_to_usecs() § CS-3013, C-Term 2014 #include <asm/cputime. h> Project 2 Linux Kernel Hacking 28
Carnegie Mellon Worcester Polytechnic Institute Process start time (nanoseconds) ¢ ¢ Start time is measured in nanoseconds since boot is stored as a struct timespec § i. e. , seconds plus nanoseconds You need to convert this to nanoseconds to store in prinfo CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 29
Carnegie Mellon Worcester Polytechnic Institute Testing getprinfo() ¢ Write test program in user space § Note: – distributed version of prinfo. h can be used in user-space or kernel-space (including LKMs) ¢ ¢ ¢ Run multiple times from same shell, different processes Note differences in results Compare with what you can find about processes from ps command from Project 1 program. CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 30
Carnegie Mellon Worcester Polytechnic Institute Testing getprinfo() (continued) ¢ Design test program to § fork multiple processes, § show a hierarchy of children and grandchildren, and § have multiple siblings CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 31
Carnegie Mellon Worcester Polytechnic Institute Submission – Part 2 ¢ Zip file named Project 2_part 2. zip containing two folders § LKM § User space code and test program ¢ ¢ Output from system logs and/or other evidence that it works README §. txt, . doc, or. pdf format CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 32
Carnegie Mellon Worcester Polytechnic Institute Submission — Part 2 (continued) ¢ LKM folder § Your Loadable Kernel Module § Makefile § Copy of prinfo. h … § … so that graders can type make to build ¢ User-space folder § Comprehensive test program(s) § Copy of prinfo. h § getprinfo. c — library routine to access system call § Makefile CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 33
Carnegie Mellon Worcester Polytechnic Institute Discussion Board ¢ ¢ ¢ Use class e-mail list as a discussion board Ask lots of questions if you get into trouble Offer lots of answers if you can! CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 34
Carnegie Mellon Worcester Polytechnic Institute Questions? CS-3013, C-Term 2014 Project 2 Linux Kernel Hacking 35