Caesar Cipher Cybersecurity Concept Lesson This document is
Caesar Cipher Cybersecurity Concept Lesson This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Caesar Cipher Learning Objectives Upon completion of this lesson, students will be able to: • investigate how Caesar Ciphers work to achieve the goal of confidentiality of information, their historical context, and strengths and weaknesses, • encrypt and decrypt text using Caesar Ciphers, • implement a Caesar Cipher in a programming language, and • ascertain the correctness of their program as a functional program to protect information assets and computing resources. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Who Needs Secret Communication • Rulers need to communicate plans to exactly whom they want without those plans being compromised by an adversary. • Generals need to direct their armies without enemies responding to that direction before it has been communicated. • Internet shoppers need to buy shoes without hackers stealing the personal information required to make the purchase. • Companies need to share data without rival companies stealing and benefiting from it. • Law enforcement needs to plan operations without awareness of the criminals who have been targeted. • Romeo needs to communicate with Juliet without arousing the suspicions of Juliet’s parents. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Basics of Cryptography Definition: The process of creating a secure message which can be read by the intended recipient but cannot be read by unauthorized third parties. Vocabulary: • Plaintext: ordinary, readable information (like the first line of a book) • Ciphertext: information which has been made unintelligible (e. g. , PU AOL ILNPUUPUN NVK JYLHALK AOL OLHCLU HUK AOL LHYAO) • Key: a shared secret which allows the recipient to convert ciphertext into plaintext This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
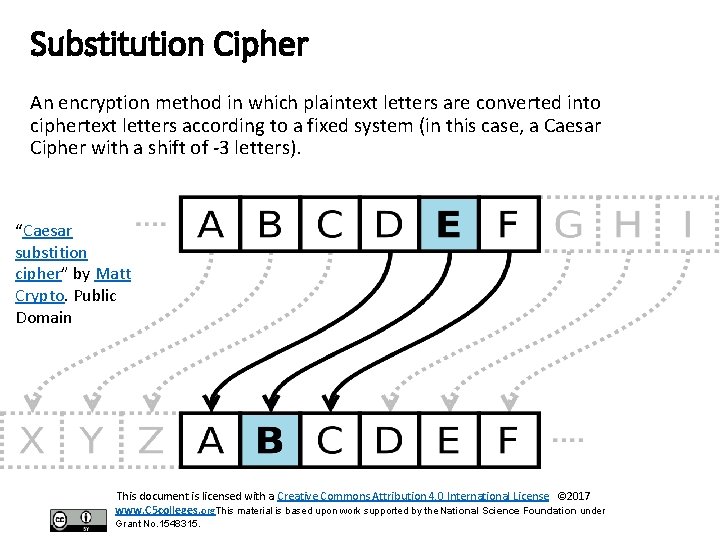
Substitution Cipher An encryption method in which plaintext letters are converted into ciphertext letters according to a fixed system (in this case, a Caesar Cipher with a shift of -3 letters). “Caesar substition cipher” by Matt Crypto. Public Domain This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
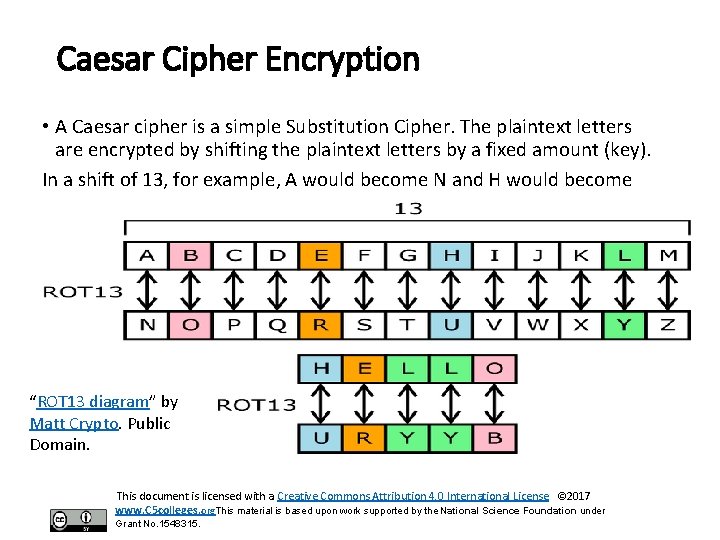
Caesar Cipher Encryption • A Caesar cipher is a simple Substitution Cipher. The plaintext letters are encrypted by shifting the plaintext letters by a fixed amount (key). In a shift of 13, for example, A would become N and H would become U. “ROT 13 diagram” by Matt Crypto. Public Domain. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
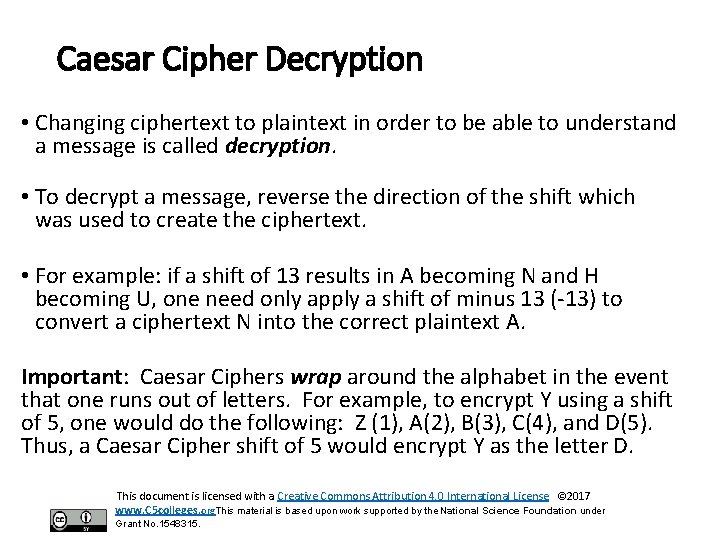
Caesar Cipher Decryption • Changing ciphertext to plaintext in order to be able to understand a message is called decryption. • To decrypt a message, reverse the direction of the shift which was used to create the ciphertext. • For example: if a shift of 13 results in A becoming N and H becoming U, one need only apply a shift of minus 13 (-13) to convert a ciphertext N into the correct plaintext A. Important: Caesar Ciphers wrap around the alphabet in the event that one runs out of letters. For example, to encrypt Y using a shift of 5, one would do the following: Z (1), A(2), B(3), C(4), and D(5). Thus, a Caesar Cipher shift of 5 would encrypt Y as the letter D. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Strengths & Weaknesses of Caesar Ciphers Strengths: • Simplicity • Speed • Useful for simple problems (like passing notes in class) Weaknesses: • Easily broken-there are only 26 possible alphabetic shifts • Susceptible to Frequency Analysis This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Encryption and Ethics Activity: Students will read the article, “The Case of Bill Barr vs. Apple” concerning government access to encrypted phones. Discussion Questions: • Who are the stakeholders? • Is Privacy being attacked? • Where is accountability assigned? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
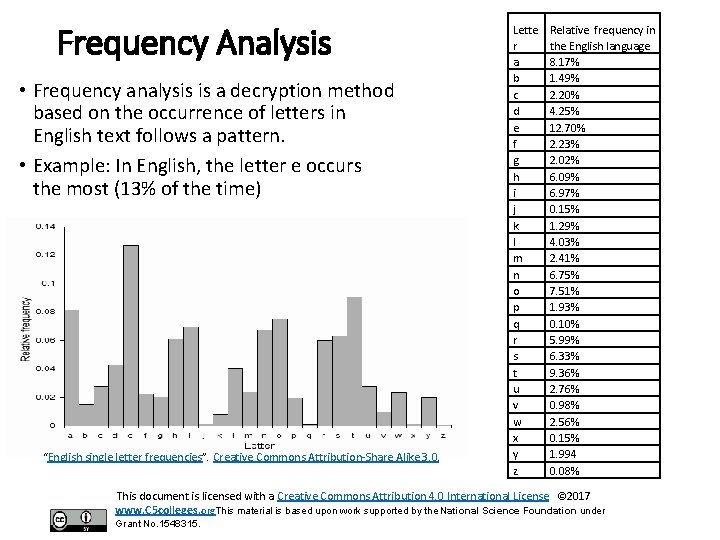
Frequency Analysis • Frequency analysis is a decryption method based on the occurrence of letters in English text follows a pattern. • Example: In English, the letter e occurs the most (13% of the time) “English single letter frequencies”. Creative Commons Attribution-Share Alike 3. 0. Lette r a b c d e f g h i j k l m n o p q r s t u v w x y z Relative frequency in the English language 8. 17% 1. 49% 2. 20% 4. 25% 12. 70% 2. 23% 2. 02% 6. 09% 6. 97% 0. 15% 1. 29% 4. 03% 2. 41% 6. 75% 7. 51% 1. 93% 0. 10% 5. 99% 6. 33% 9. 36% 2. 76% 0. 98% 2. 56% 0. 15% 1. 994 0. 08% This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Frequency Analysis: Steps • Make a frequency analysis chart of the ciphertext • Compare the ciphertext frequency analysis chart to the English frequency analysis chart • How many letters would it take to shift the ciphertext frequency analysis chart so that it looks like the English frequency analysis chart • That shift could be the Caesar Cipher key used to create the ciphertext. • Decipher and check. Repeat steps as necessary. Note: This method will work provided that the ciphertext is in English and is long enough to provide a good sample This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Programming Assignment: Necessary Skills • Loop Statements • Conditional Statements • Arrays or Lists • Array or List Processing • Strings • String Processing • Modulus Math This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org. This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Catalyzing Computing and Cybersecurity in Community Colleges www. ncyte. net This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
- Slides: 13