Bytecode Verification on Java Smart cards Xavier Leroy
Bytecode Verification on Java Smart cards Xavier Leroy Presentation(Day 2) - Nithya
JSR n Subroutines -> mostly used for compiling the try-finally construct n n n Subroutines and Sun’s Verfn algorithm Subroutines and our Verfn Algorithm JSR instruction Ret instruction Role of local variable
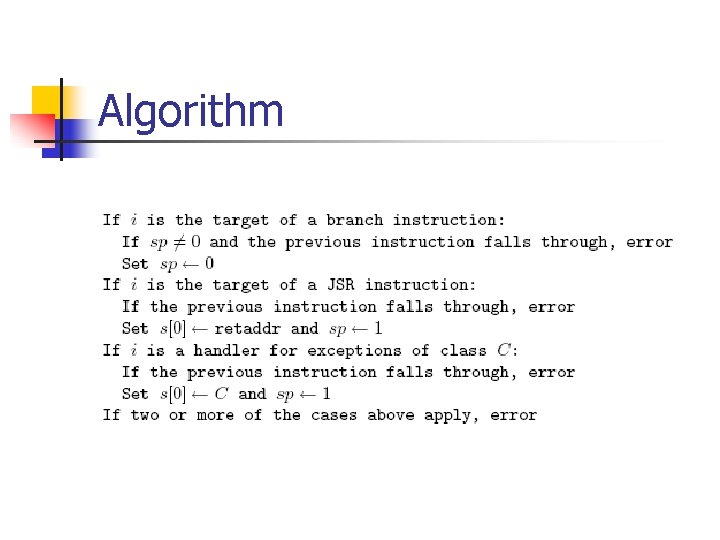
Algorithm
JSR vs invoke n n Methods : invokevirtual, invokenonvirtual, return, areturn, Ireturn JSR instruction and ret instruction
Off. Card code Transformations n 1. 2. Two methods to ensure that all correct applets pass verification: Using special Java compiler Using a std Java Compiler and Java Card Converter (for Off-card code Transformation) and pass it to on card verifier
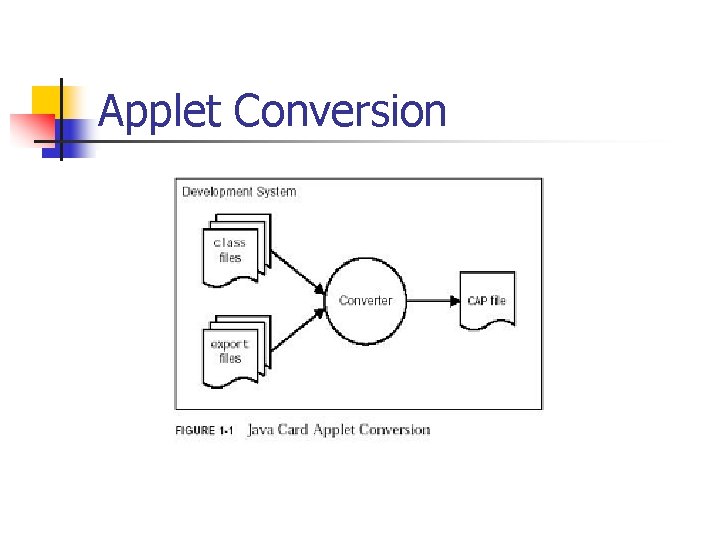
Applet Conversion
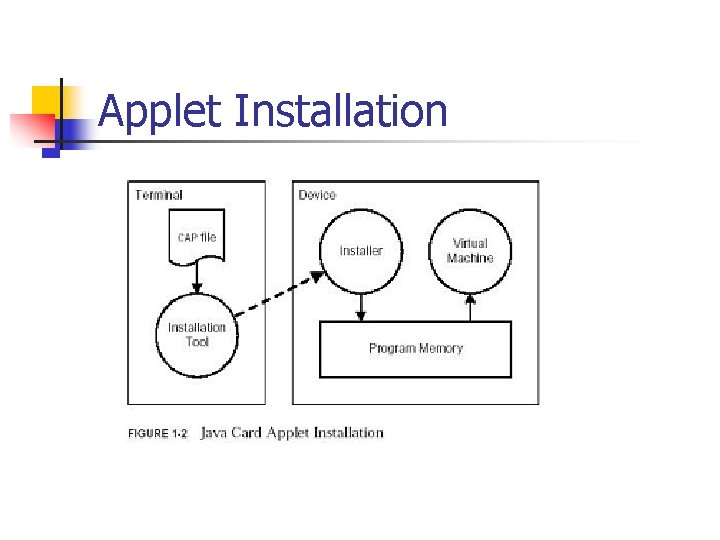
Applet Installation
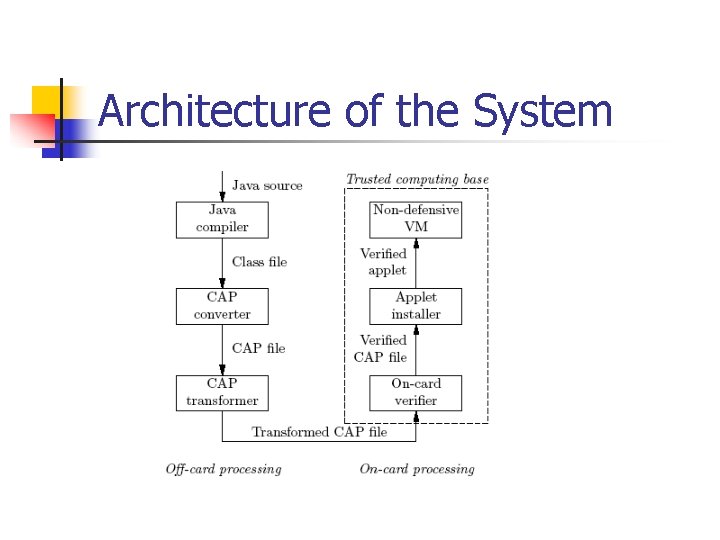
Architecture of the System
Transformations n n Stack Normalisation Register Reallocation
Stack Normalisation For a branch with non-empty stack: n Insert stores to fresh registers before the branch n Loads from the same registers at the branch target
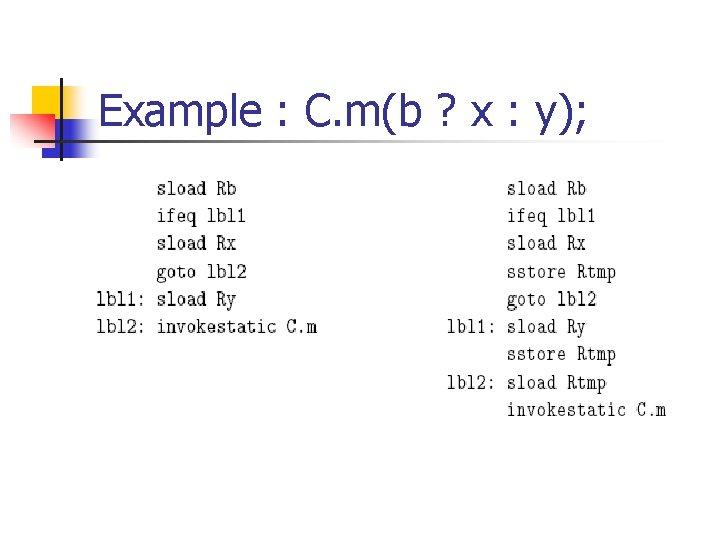
Example : C. m(b ? x : y);
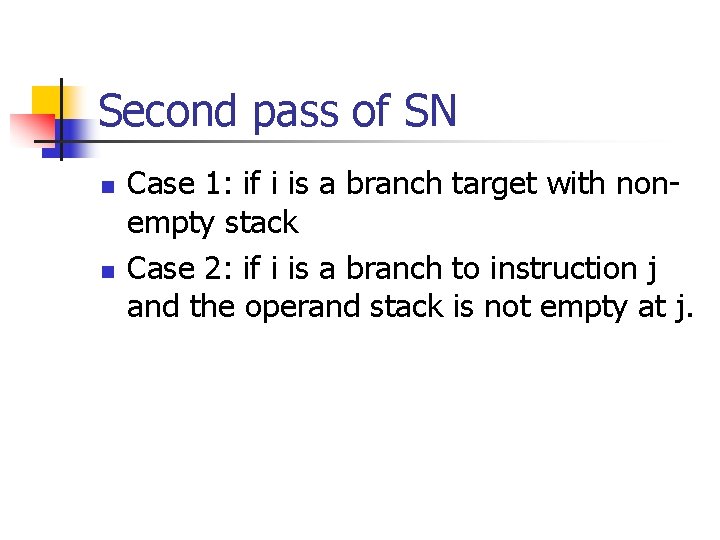
Second pass of SN n n Case 1: if i is a branch target with nonempty stack Case 2: if i is a branch to instruction j and the operand stack is not empty at j.
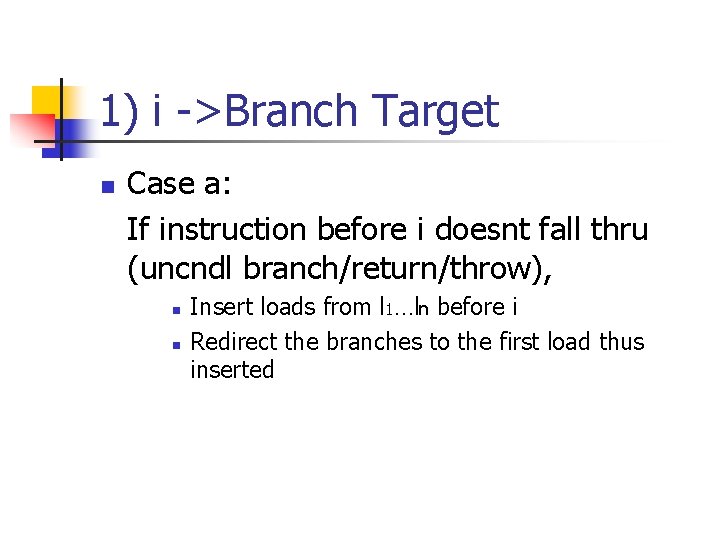
1) i ->Branch Target n Case a: If instruction before i doesnt fall thru (uncndl branch/return/throw), n n Insert loads from l 1…ln before i Redirect the branches to the first load thus inserted
Case a
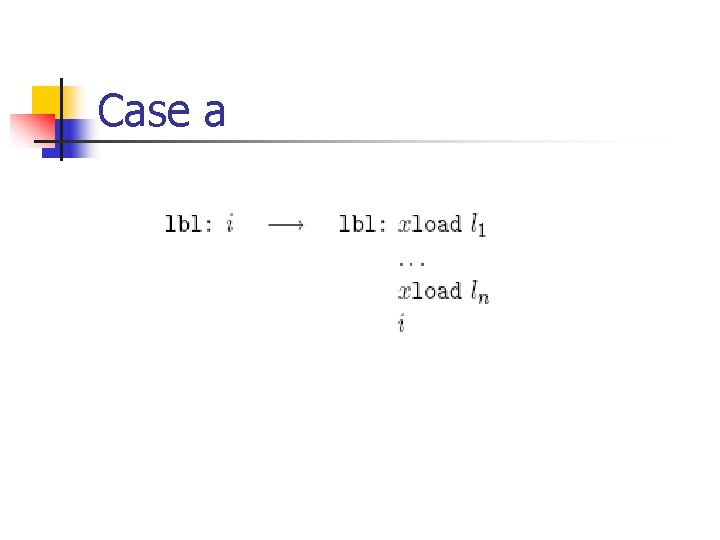
1)i ->Branch Target n Case b: If the instruction before i falls thru: n n Insert stores to ln. . l 1 Load from l 1. . ln, before i
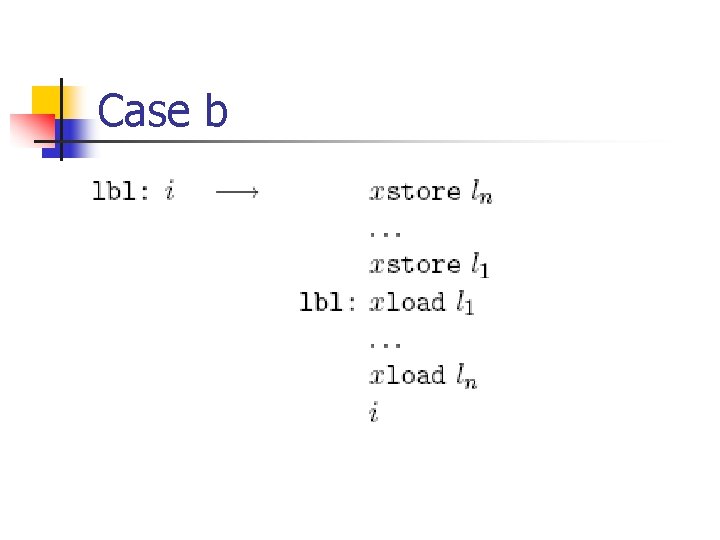
Case b
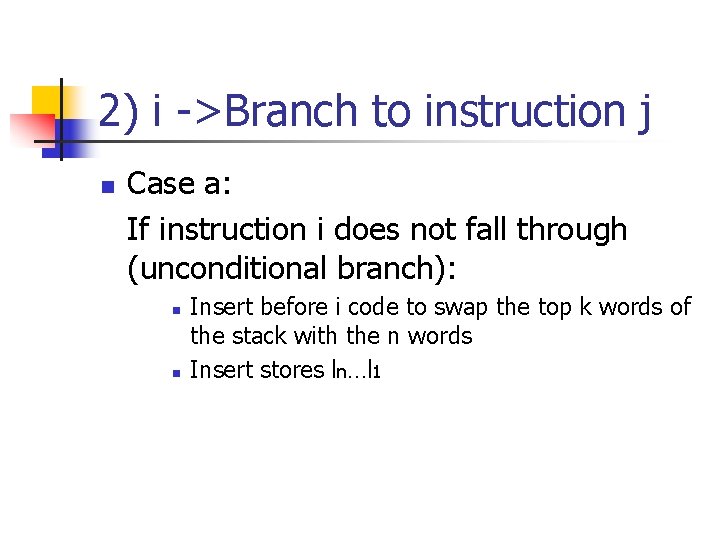
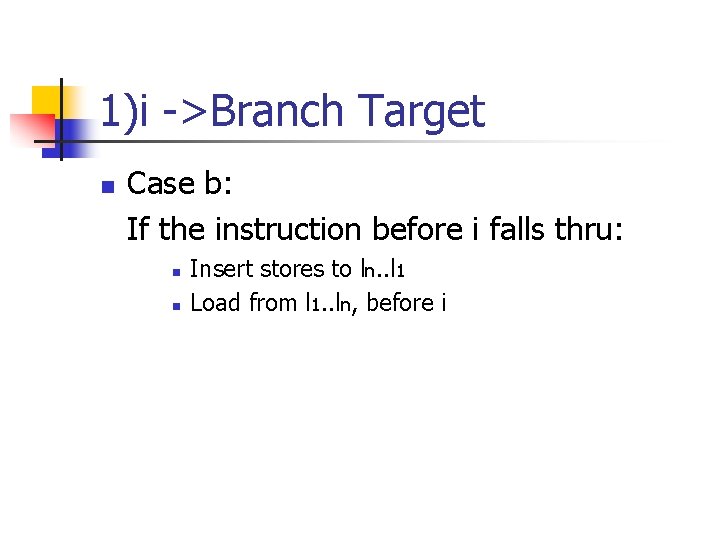
2) i ->Branch to instruction j n Case a: If instruction i does not fall through (unconditional branch): n n Insert before i code to swap the top k words of the stack with the n words Insert stores ln…l 1
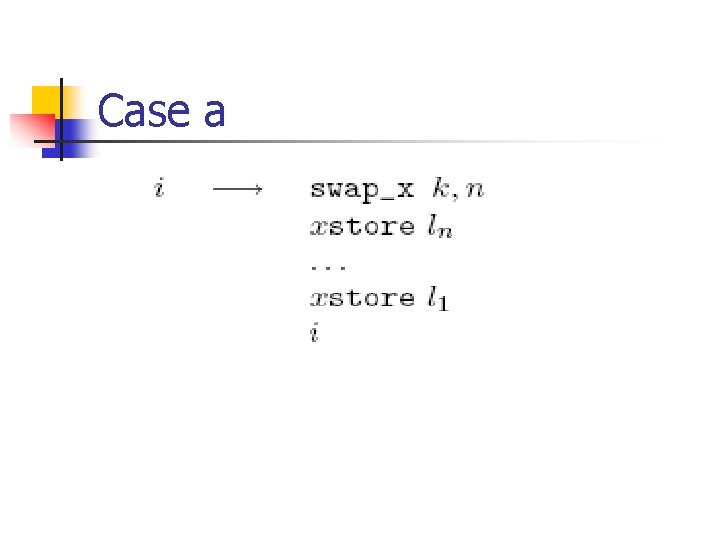
Case a
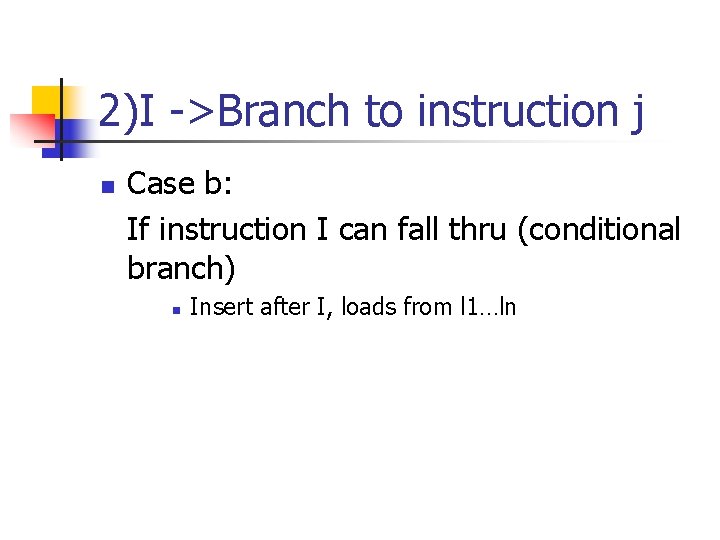
2)I ->Branch to instruction j n Case b: If instruction I can fall thru (conditional branch) n Insert after I, loads from l 1…ln
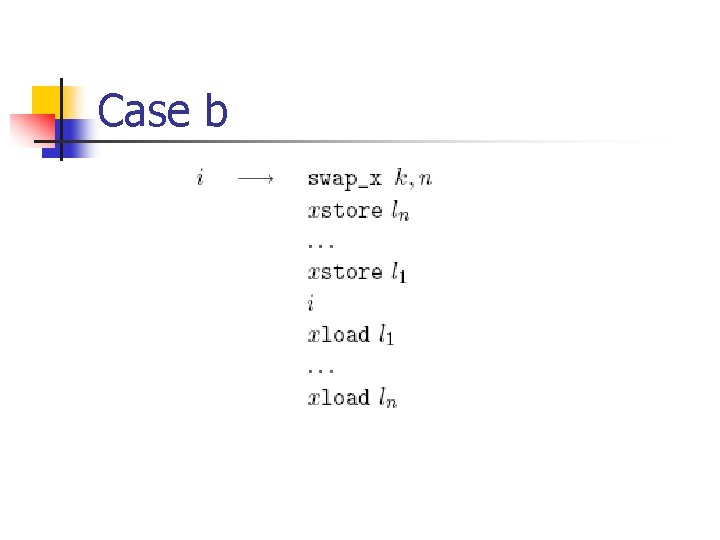
Case b
Worst case n Example of combination of two transformations: n n The instruction before i falls through i itself falls through
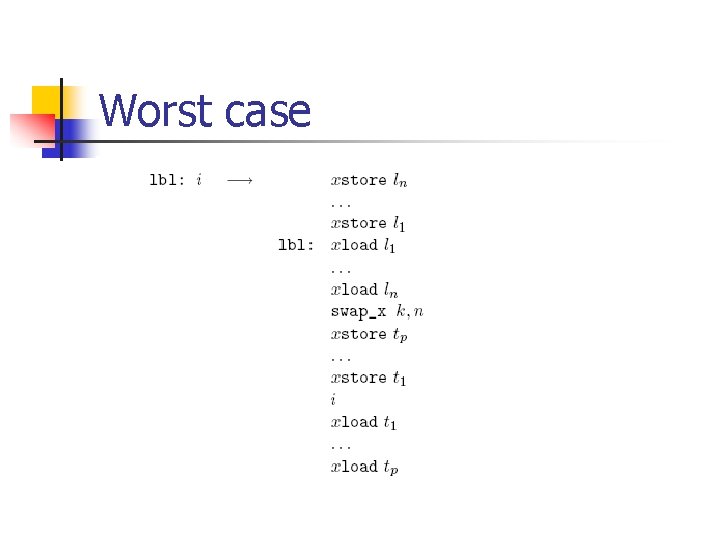
Worst case
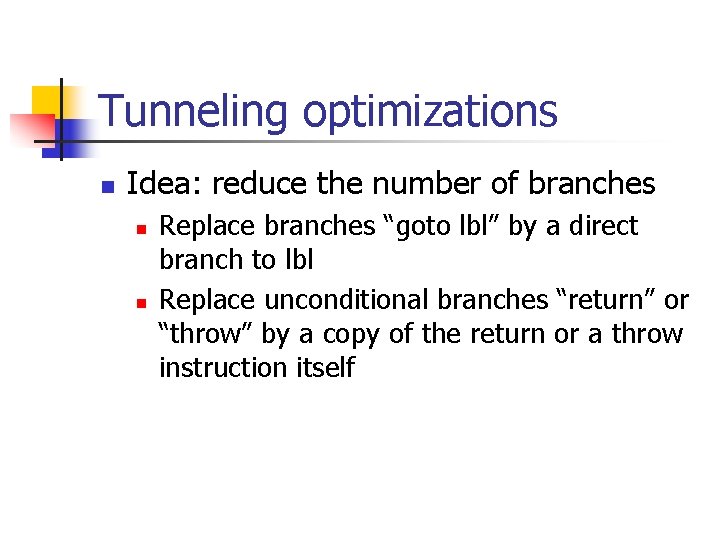
Tunneling optimizations n Idea: reduce the number of branches n n Replace branches “goto lbl” by a direct branch to lbl Replace unconditional branches “return” or “throw” by a copy of the return or a throw instruction itself
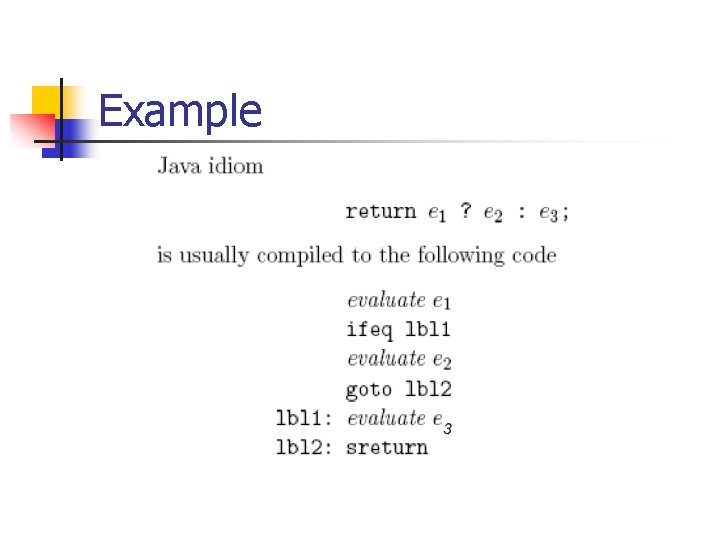
Example
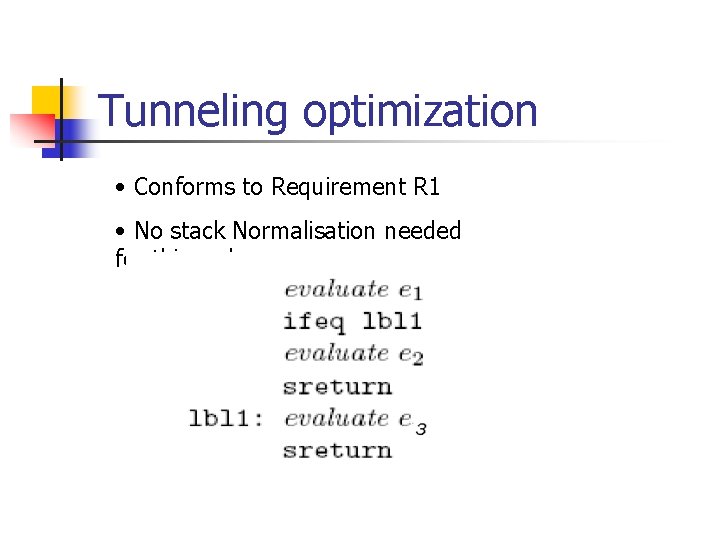
Tunneling optimization • Conforms to Requirement R 1 • No stack Normalisation needed for this code
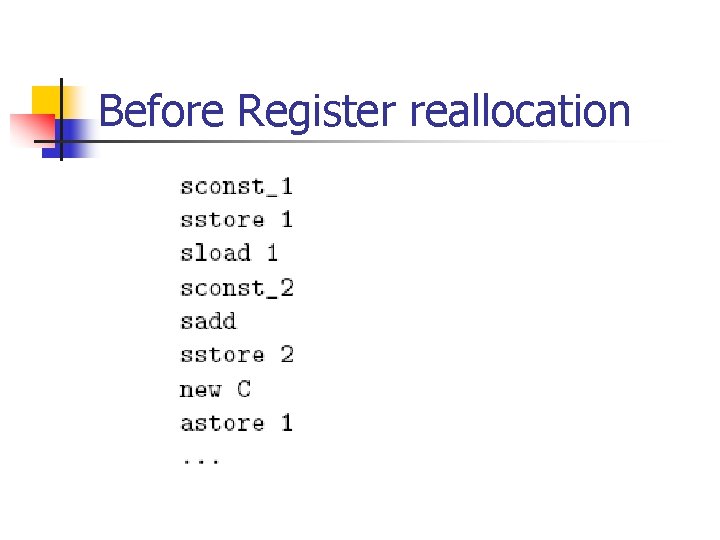
Before Register reallocation
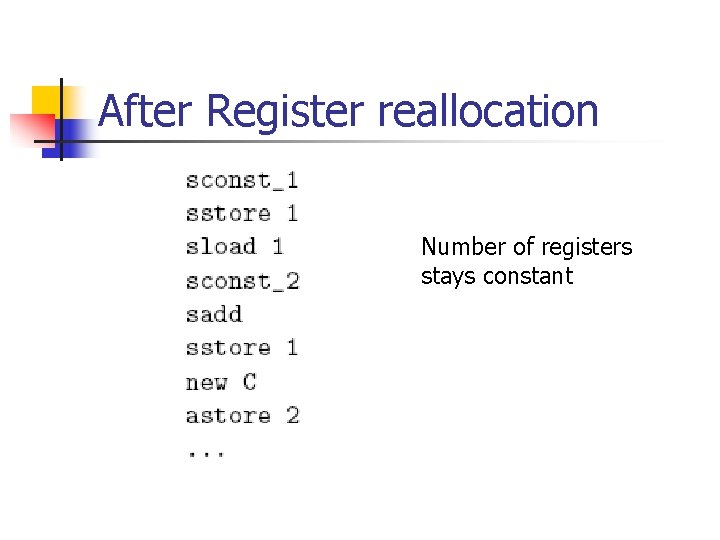
After Register reallocation Number of registers stays constant
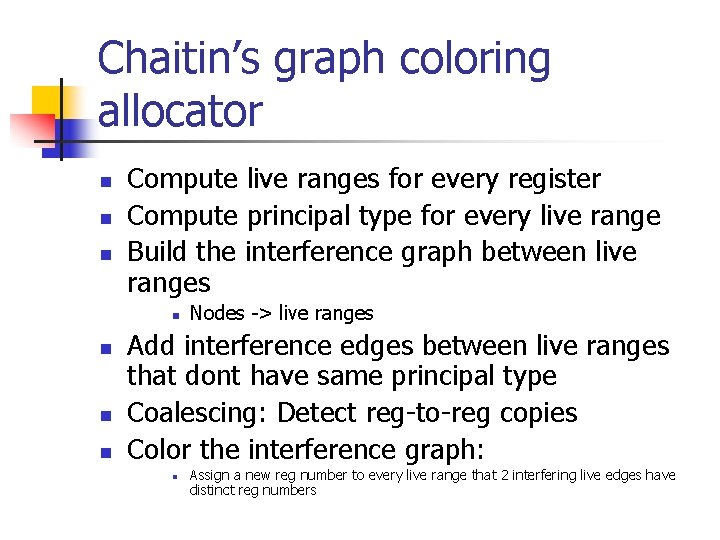
Chaitin’s graph coloring allocator n n n Compute live ranges for every register Compute principal type for every live range Build the interference graph between live ranges n n Nodes -> live ranges Add interference edges between live ranges that dont have same principal type Coalescing: Detect reg-to-reg copies Color the interference graph: n Assign a new reg number to every live range that 2 interfering live edges have distinct reg numbers
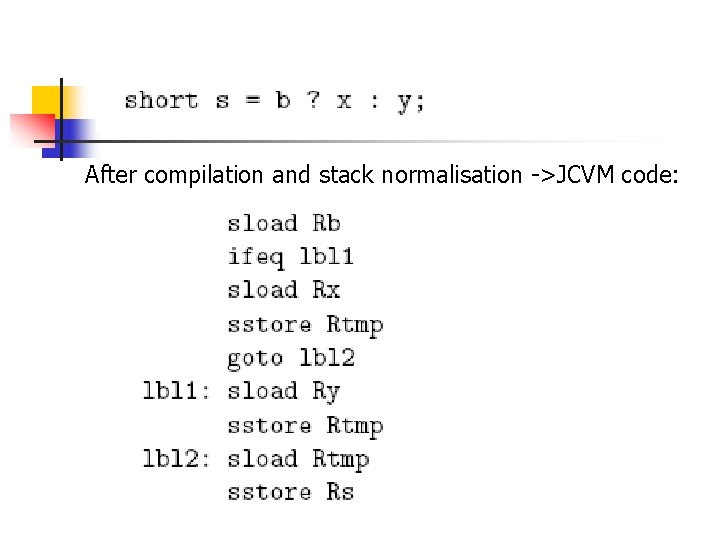
After compilation and stack normalisation ->JCVM code:
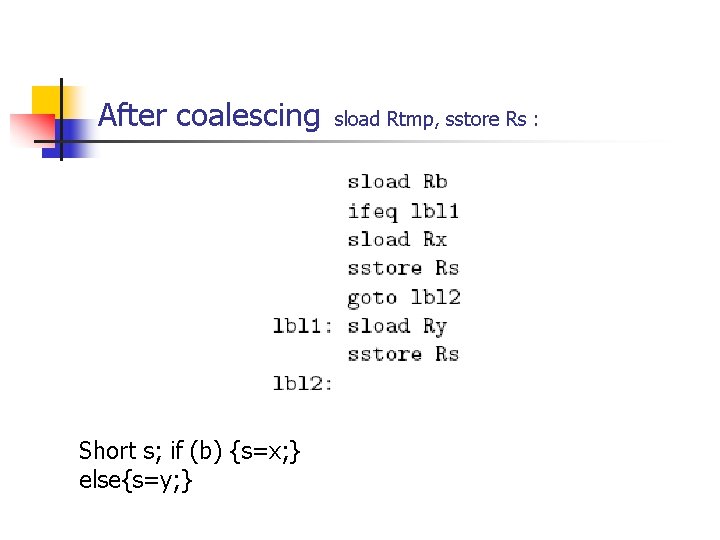
After coalescing Short s; if (b) {s=x; } else{s=y; } sload Rtmp, sstore Rs :
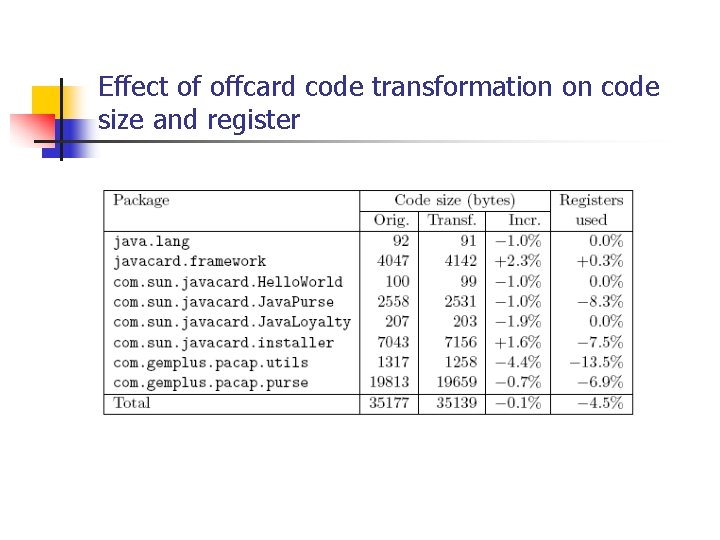
Effect of offcard code transformation on code size and register
Comments?
- Slides: 32