BYOD Security Policy Governance Jawahar Sivasankaran Cisco Distinguished
BYOD: Security, Policy & Governance Jawahar Sivasankaran Cisco Distinguished Engineer & Senior Technical Director © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Public 1
BYOD: Opportunities Improved Employee Satisfaction Cost savings Increased Productivity © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Public 2

Device Proliferation Entitlement Strategy Security Support Policy Management and Communication Enterprise Apps, Collaboration, Productivity Services etc. *2 year comparison © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Public 3
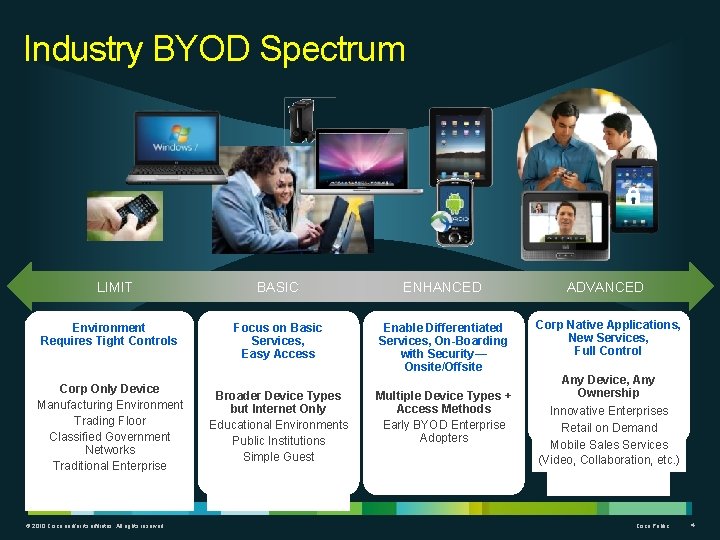
Industry BYOD Spectrum LIMIT Environment Requires Tight Controls Corp Only Device Manufacturing Environment Trading Floor Classified Government Networks Traditional Enterprise © 2010 Cisco and/or its affiliates. All rights reserved. BASIC ENHANCED ADVANCED Focus on Basic Services, Easy Access Enable Differentiated Services, On-Boarding with Security— Onsite/Offsite Corp Native Applications, New Services, Full Control Broader Device Types but Internet Only Educational Environments Public Institutions Simple Guest Multiple Device Types + Access Methods Early BYOD Enterprise Adopters Any Device, Any Ownership Innovative Enterprises Retail on Demand Mobile Sales Services (Video, Collaboration, etc. ) Cisco Public 4
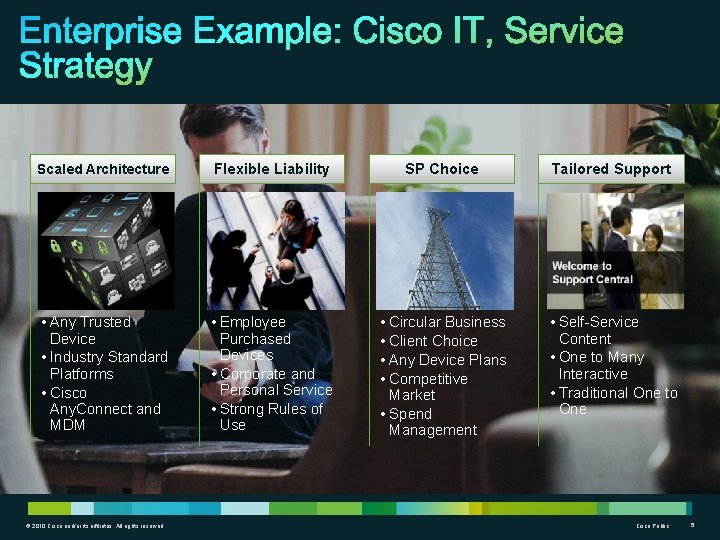
Enterprise Example: Cisco IT, Service Strategy Scaled Architecture Flexible Liability SP Choice Tailored Support • Any Trusted Device • Industry Standard Platforms • Cisco Any. Connect and MDM • Employee Purchased Devices • Corporate and Personal Service • Strong Rules of Use • Circular Business • Client Choice • Any Device Plans • Competitive Market • Spend Management • Self-Service Content • One to Many Interactive • Traditional One to One © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Public 5
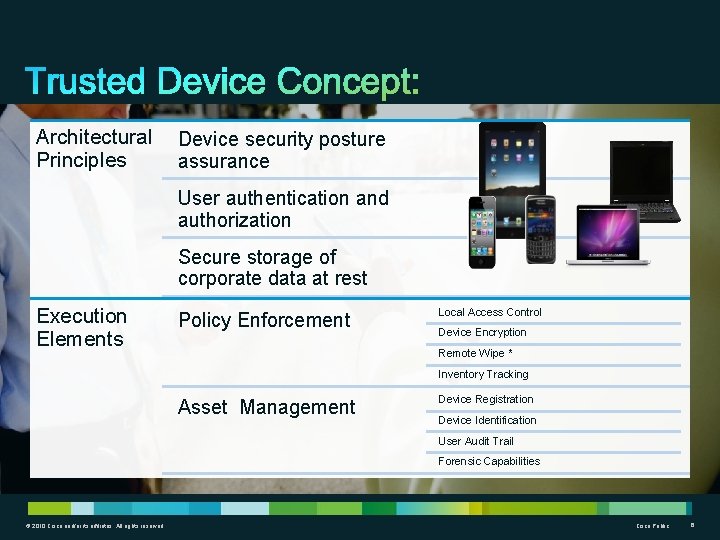
Trusted Device Concept: Architectural Principles Device security posture assurance User authentication and authorization Secure storage of corporate data at rest Execution Elements Policy Enforcement Local Access Control Device Encryption Remote Wipe * Inventory Tracking Asset Management Device Registration Device Identification User Audit Trail Forensic Capabilities © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Public 6
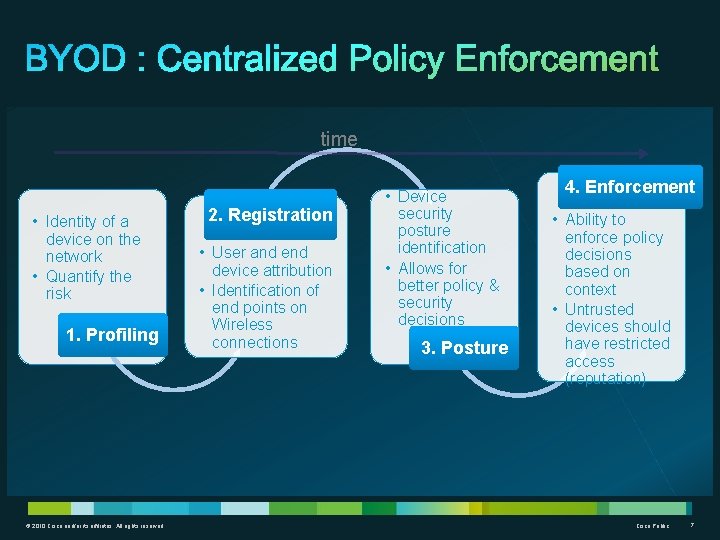
time • Identity of a device on the network • Quantify the risk 1. Profiling © 2010 Cisco and/or its affiliates. All rights reserved. 2. Registration • User and end device attribution • Identification of end points on Wireless connections • Device security posture identification • Allows for better policy & security decisions 3. Posture 4. Enforcement • Ability to enforce policy decisions based on context • Untrusted devices should have restricted access (reputation) Cisco Public 7
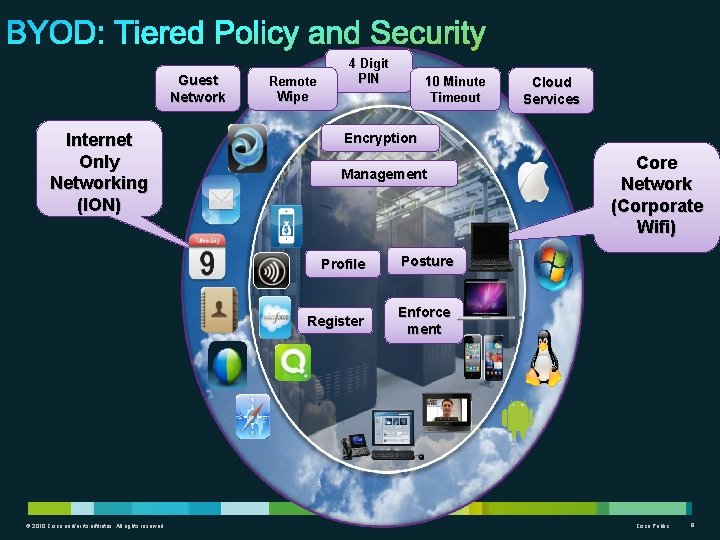
BYOD: Tiered Policy and Security Guest Network Internet Only Networking (ION) © 2010 Cisco and/or its affiliates. All rights reserved. Remote Wipe 4 Digit PIN 10 Minute Timeout Cloud Services Encryption Management Profile Posture Register Enforce ment Core Network (Corporate Wifi) Cisco Public 8
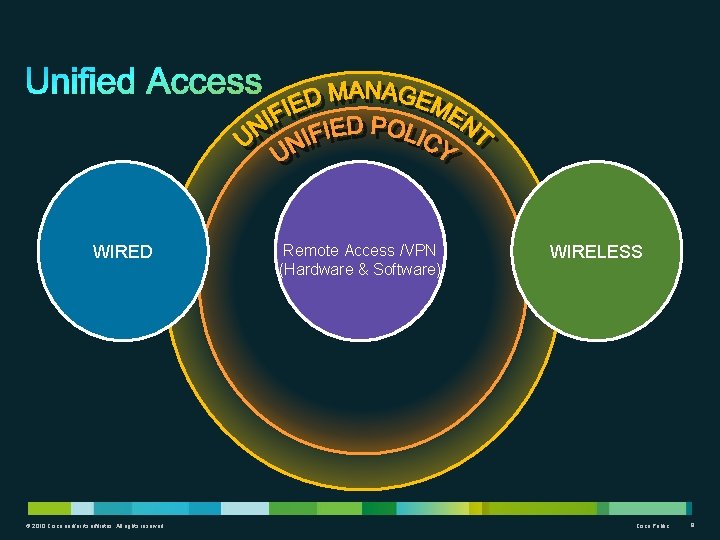
WIRED © 2010 Cisco and/or its affiliates. All rights reserved. Remote Access /VPN (Hardware & Software) WIRELESS Cisco Public 9

Thank you. © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Public 10
- Slides: 10