BYOD and Beyond Leong See Kay 2012 Ciscoandorits
BYOD and Beyond Leong See Kay ©© 2012 Ciscoand/orits itsaffiliates. All Allrightsreserved. Cisco Confidential 1
• Why BYOD? An introduction • BYOD Challenges • The Cisco BYOD Solution • BYOD Use Cases • Summary © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 2
© 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 3
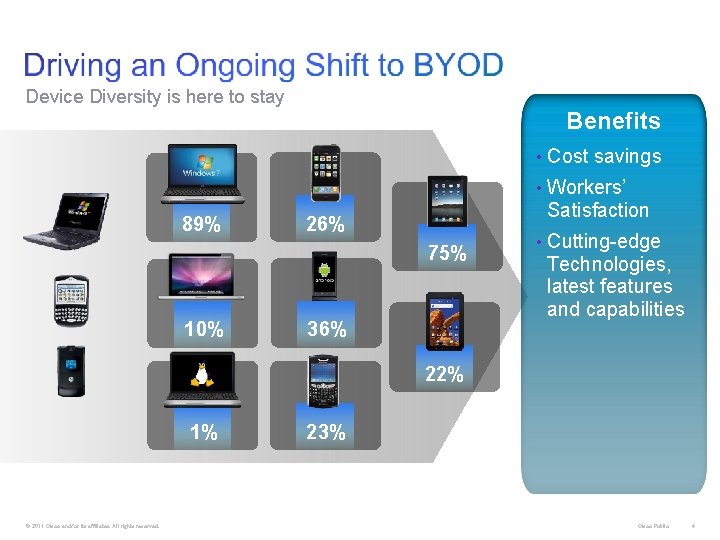
Device Diversity is here to stay Benefits • Cost savings • Workers’ 89% Satisfaction 26% 75% 10% 36% • Cutting-edge Technologies, latest features and capabilities 22% 1% © 2011 Cisco and/or its affiliates. All rights reserved. 23% Cisco Public 4
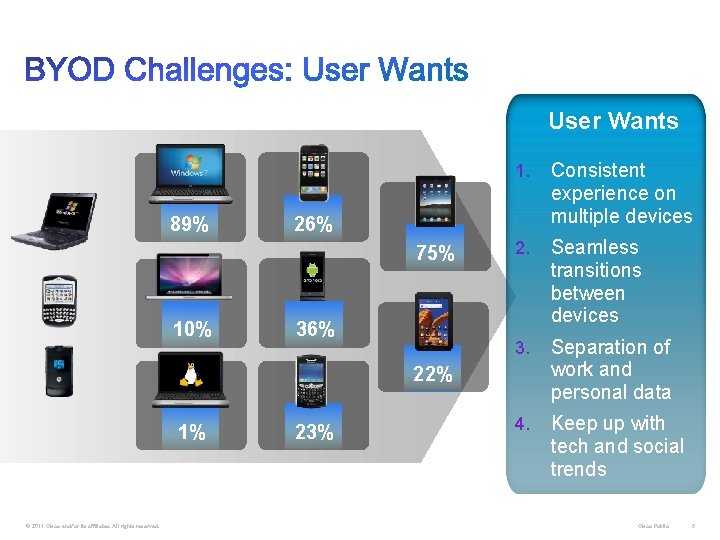
User Wants 89% Consistent experience on multiple devices 2. Seamless transitions between devices 3. Separation of work and personal data 4. Keep up with tech and social trends 26% 75% 10% 1. 36% 22% 1% © 2011 Cisco and/or its affiliates. All rights reserved. 23% Cisco Public 5
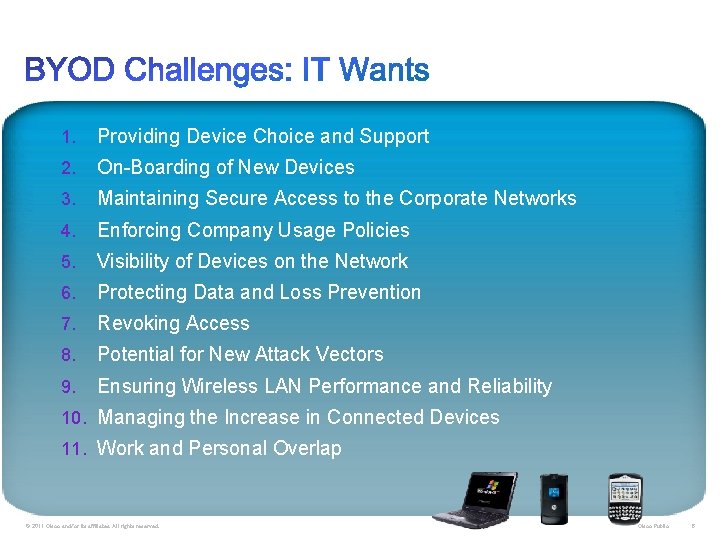
1. Providing Device Choice and Support 2. On-Boarding of New Devices 3. Maintaining Secure Access to the Corporate Networks 4. Enforcing Company Usage Policies 5. Visibility of Devices on the Network 6. Protecting Data and Loss Prevention 7. Revoking Access 8. Potential for New Attack Vectors 9. Ensuring Wireless LAN Performance and Reliability 10. Managing the Increase in Connected Devices 11. Work and Personal Overlap © 2011 Cisco and/or its affiliates. All rights reserved. Cisco Public 6
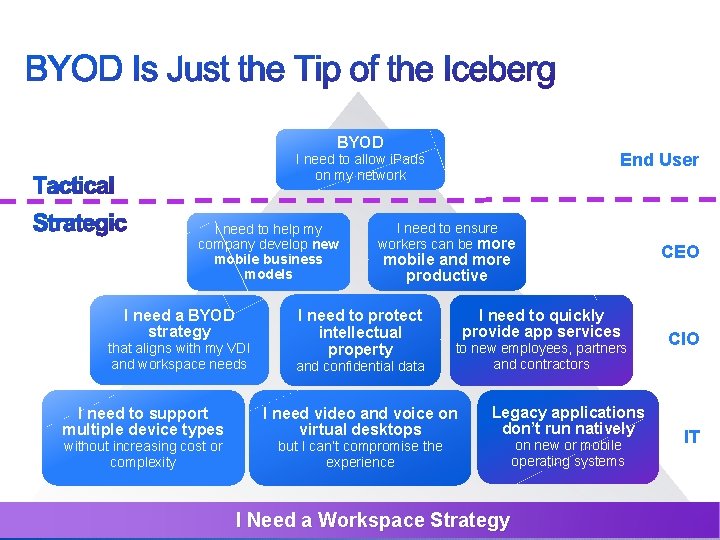
BYOD End User I need to allow i. Pads on my network I need to help my company develop new mobile business models I need a BYOD strategy that aligns with my VDI and workspace needs I need to support multiple device types without increasing cost or complexity © 2012 Cisco and/or its affiliates. All rights reserved. I need to ensure workers can be more CEO mobile and more productive I need to protect intellectual property and confidential data I need to quickly provide app services to new employees, partners and contractors I need video and voice on virtual desktops CIO Legacy applications don’t run natively but I can’t compromise the experience I Need a Workspace Strategy on new or mobile operating systems Cisco Confidential IT 7
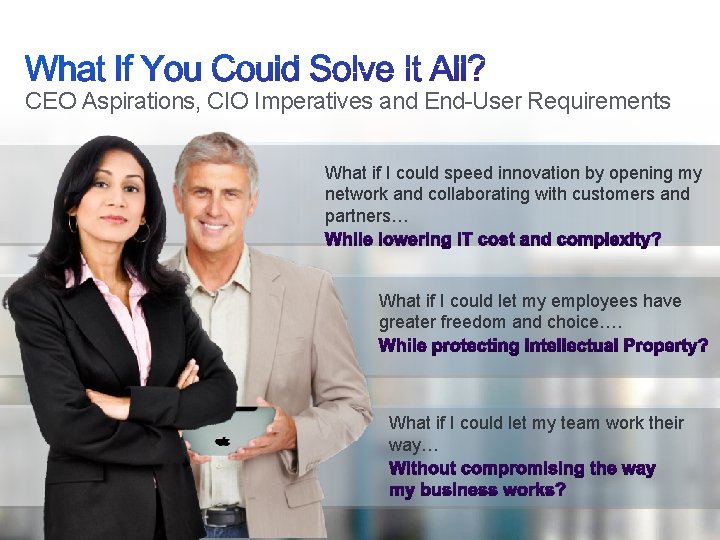
CEO Aspirations, CIO Imperatives and End-User Requirements What if I could speed innovation by opening my network and collaborating with customers and partners… What if I could let my employees have greater freedom and choice…. What if I could let my team work their way… © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 8
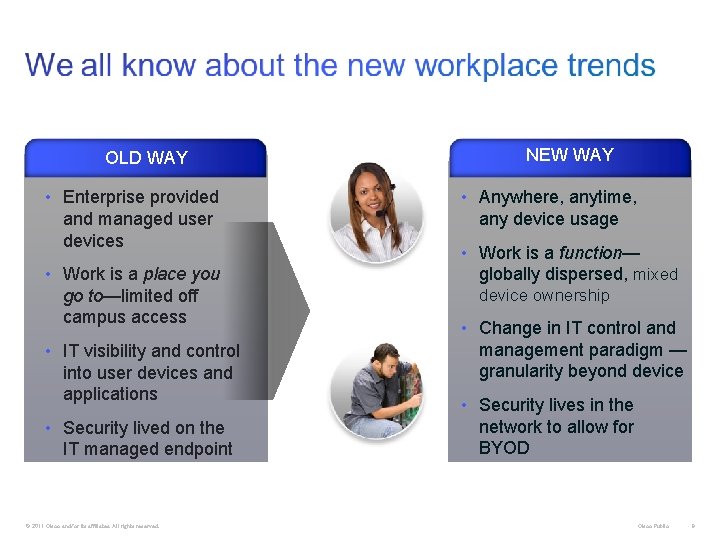
NEW WAY OLD WAY • Enterprise provided and managed user devices EXECUTIVE • Work is a place you go to—limited off campus access • IT visibility and control into user devices and applications • Anywhere, anytime, any device usage • Work is a function— globally dispersed, mixed device ownership EMPLOYEE • Change in IT control and management paradigm — granularity beyond device • Security lives in the network to allow for BYOD • Security lived on the IT managed endpoint IT © 2011 Cisco and/or its affiliates. All rights reserved. Cisco Public 9

Compliance Operations Network Team Security Operations Endpoint Team Application Team © 2012 Cisco and/or its affiliates. All rights reserved. Human Resources Cisco Confidential 10
© 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 11
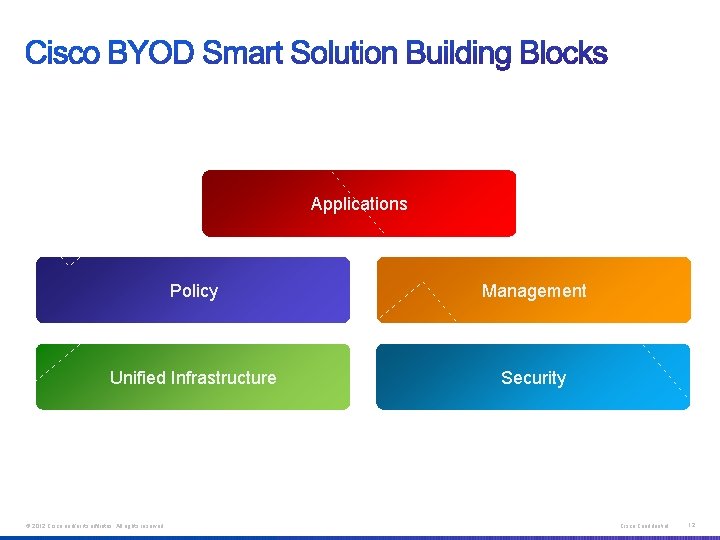
Applications Policy Management Unified Infrastructure Security © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 12
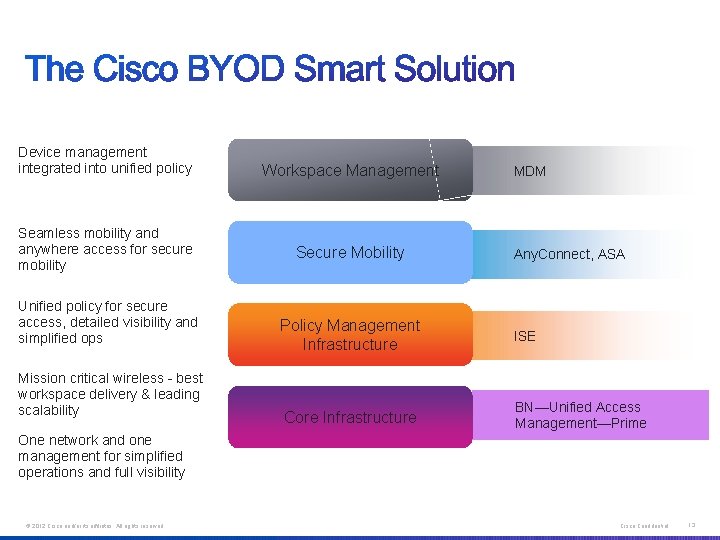
Device management integrated into unified policy Seamless mobility and anywhere access for secure mobility Unified policy for secure access, detailed visibility and simplified ops Mission critical wireless - best workspace delivery & leading scalability Workspace Management Secure Mobility MDM Any. Connect, ASA Policy Management Infrastructure ISE Core Infrastructure BN—Unified Access Management—Prime One network and one management for simplified operations and full visibility © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 13

LIMIT BASIC ENHANCED ADVANCED Environment Requires Tight Controls Focus on Basic Services, Easy Access Enable Differentiated Services, On-Boarding with Security— Onsite/Offsite Corp Native Applications, New Services, Full Control Corp Only Device Manufacturing Environment Trading Floor Classified Government Networks Traditional Enterprise Broader Device Types but Internet Only Educational Environments Public Institutions Simple Guest Multiple Device Types + Access Methods Early BYOD Enterprise Adopters Any Device, Any Ownership Innovative Enterprises Retail on Demand Mobile Sales Services (Video, Collaboration, etc. ) © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 14
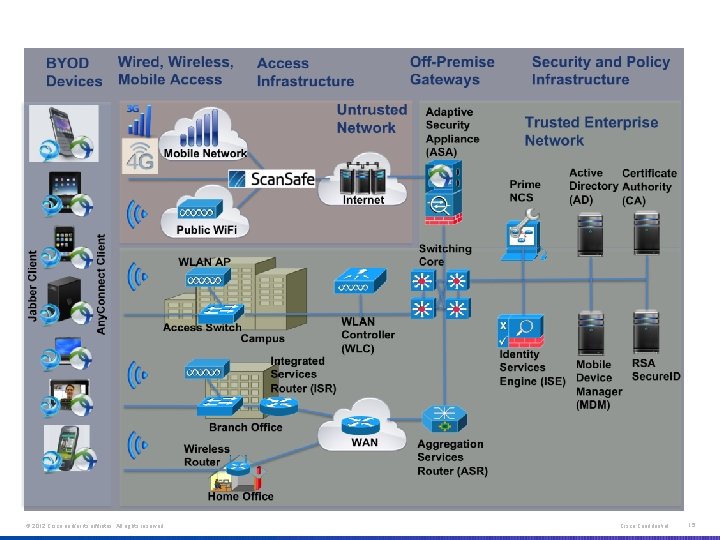
BYOD 2. 1 Solution Components © 2012 Cisco and/or its affiliates. All rights reserved. * Note: Scan. Safe validated in a future phase Cisco Confidential 15
© 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 16
Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 17 17

Trusted Wi F i ü Authenticate User ü Fingerprint Device ü Apply Corporate Config ü Enterprise Apps ü Automatic Policies Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 18 18
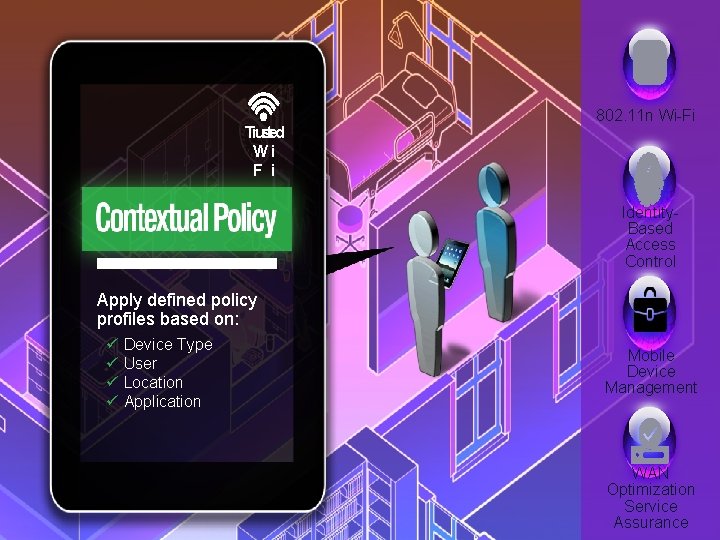
Trusted Wi F i 802. 11 n Wi-Fi Identity. Based Access Control Apply defined policy profiles based on: ü ü Device Type User Location Application Mobile Device Management Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. WAN Optimization Service Assurance 19 Cisco Confidential 19

Trusted Wi F i Access: FULL No Yes Electronic Medical Records Mobile Tele. Presence Email Instant Messenger Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 20 20

Trusted Wi F i 802. 11 n Wi-Fi § Location § Video Optimization § Spectrum Intelligence § Client Acceleration Identity. Based Access Control Is Mr. Allen’s lab work ready yet? Not yet but i will let you know the moment it arrives Mobile Device Management Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 21 21

Untrusted. Wi. Fi Access: Limited Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 22 22

Hotspot 2. 0 802. 11 n Wi-Fi Web/Email Security Identity. Based Access Control VPN Collaboration /UC Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 23 23

Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 24 24
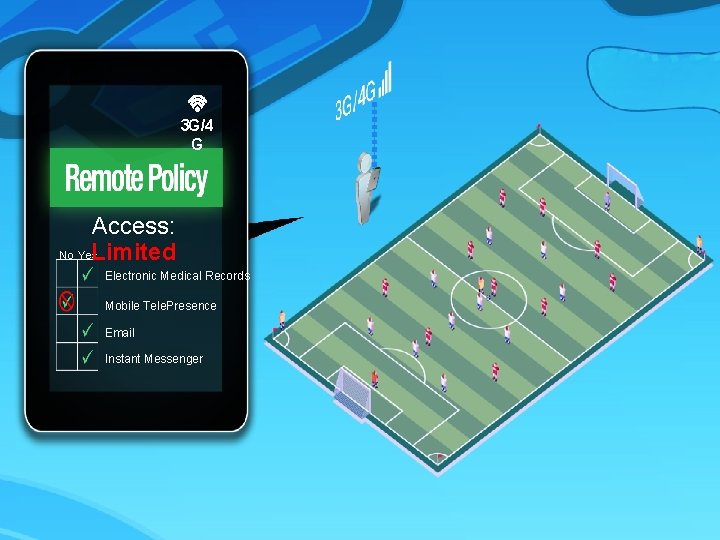
3 G/4 G Access: No Yes Limited Electronic Medical Records Mobile Tele. Presence Email Instant Messenger Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 25 25

3 G/4 G Identity. Based Access Control VPN Intelligent Packet Core Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 26 26
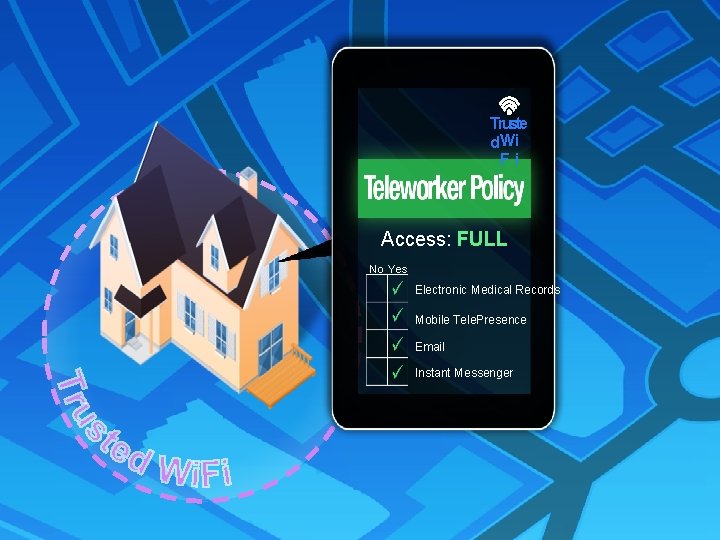
Truste d. Wi Fi Access: FULL No Yes Electronic Medical Records Mobile Tele. Presence Email Instant Messenger Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 27 27
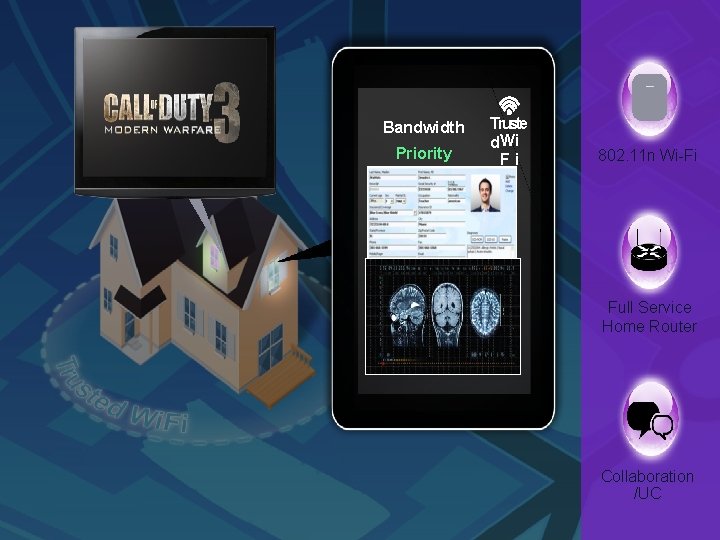
Bandwidth Priority Truste d. Wi Fi 802. 11 n Wi-Fi Full Service Home Router Collaboration /UC Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 28 28

Cisco Confidential © 2012 Cisco and/or its affiliates. All rights reserved. Presentation_ID © 2008 Cisco Systems, Inc. All rights reserved. Cisco Confidential 29 29
© 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 30
• BYOD impacts all areas of IT • Workspace delivery to any device can be native, virtual, or hybrid • BYOD implementation must address the entire “spectrum” of use cases in an organization Cisco BYOD Solution Any. Connect Scan. Safe © 2012 Cisco and/or its affiliates. All rights reserved. ASA ESA/WSA ISE Wireless Wired Sec Group Access Cisco Prime Cisco Confidential 31
Reduced Burden on IT Staff Device On-Boarding, Self Registration, Supplicant Provisioning Reduced Burden on Help Desk Staff Seamless Intuitive End-User Experience Self Service Model My Device Registration Portal, Guest Sponsorship Portal © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 32

Thank you. © 2012 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 33
- Slides: 33