BUSINESS DATA COMMUNICATIONS NETWORKING Chapter 2 Application Layerpg
BUSINESS DATA COMMUNICATIONS & NETWORKING Chapter 2 Application Layer(pg. 26 -35)a Speshock #3 Josh Speshock Fitz. Gerald ● Dennis ● Durcikova Prepared by Taylor M. Wells: College of Business Administration, California State University, Sacramento Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
Chapter 2 Topics: Pages 26 -35 • • • Intro to Architectures Application Architectures Host-Based Architectures Client-Based Client-Server Tiered-Architectures Thin and Thick Clients Cloud Architectures Peer-to-Peer Architectures Choosing the Best Architecture Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2 Intro Application Architectures • Work Done By An Application Program Divided Into Four General Functions 1. 2. Data Storage • Application Programs Require Data to Be Stored or Received • For example : – A Small File Such as a Memo Produced By A Word Processor – Large Database such as an Organization’s Accounting Records Data Access Logic – Processing Required To Access Data, – Database Queries In SQL 3. Application Logic(Sometimes Called Business Logic) 4. Presentation Logic – Presentation of Information To The User And The Acceptance Of The User’s Commands Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
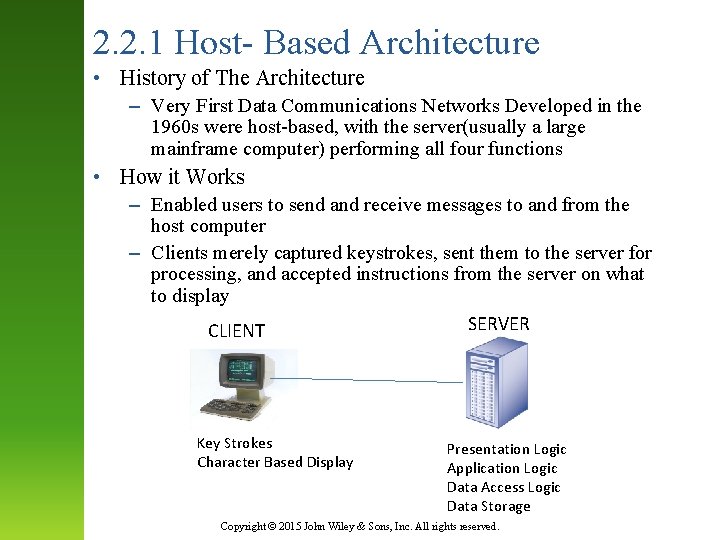
2. 2. 1 Host- Based Architecture • History of The Architecture – Very First Data Communications Networks Developed in the 1960 s were host-based, with the server(usually a large mainframe computer) performing all four functions • How it Works – Enabled users to send and receive messages to and from the host computer – Clients merely captured keystrokes, sent them to the server for processing, and accepted instructions from the server on what to display SERVER CLIENT Key Strokes Character Based Display Presentation Logic Application Logic Data Access Logic Data Storage Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2. 1 Cons of the Host-Based Architecture • Cons of The Architecture – Two Fundamental Problems With The Network • 1. Servers must process all messages • Why is that bad? – As the demands for more and more network applications grew, many servers become overloaded and unable to quickly process all the users’ demands • 2. Upgrades to the mainframes that usually are the servers in this architecture are “lumpy”. – That is, upgrades come in large increments and are expensive( e. g. , $ 500, 000); it is difficult to upgrade “a little”. Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
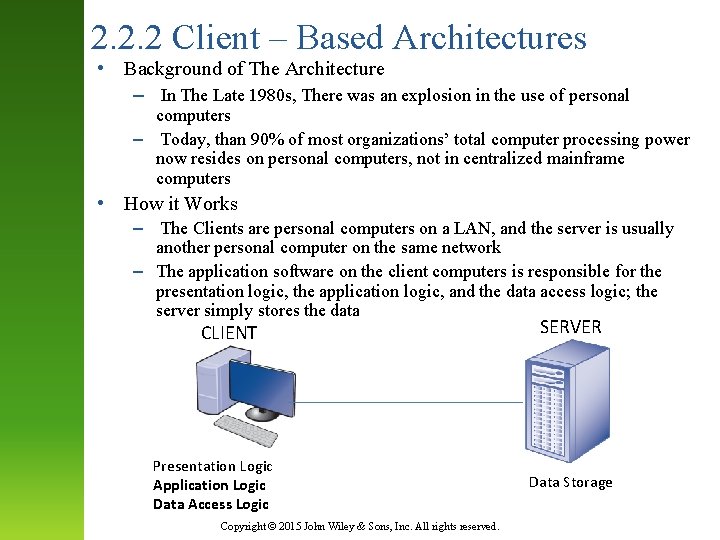
2. 2. 2 Client – Based Architectures • Background of The Architecture – In The Late 1980 s, There was an explosion in the use of personal computers – Today, than 90% of most organizations’ total computer processing power now resides on personal computers, not in centralized mainframe computers • How it Works – The Clients are personal computers on a LAN, and the server is usually another personal computer on the same network – The application software on the client computers is responsible for the presentation logic, the application logic, and the data access logic; the server simply stores the data CLIENT Presentation Logic Application Logic Data Access Logic Copyright © 2015 John Wiley & Sons, Inc. All rights reserved. SERVER Data Storage
2. 2. 2 Cons of Client-Based Architectures • Fundamental Problem In Client – Based Networks – All data on the server must travel to the client for processing – For example, • Suppose the user wishes to display a list of all employees with company life insurance – All the data in the database( or all the indices) must travel from the server where the database is stored over the network circuit to the client, which then examines each record to see if it matches the data requested by the user – This can overload the network circuits because far more data are transmitted from the server to the client than the client actually needs Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
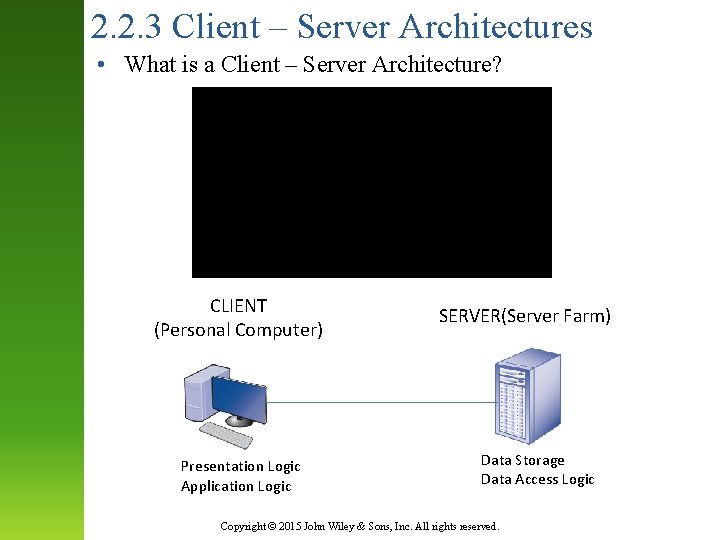
2. 2. 3 Client – Server Architectures • What is a Client – Server Architecture? CLIENT (Personal Computer) Presentation Logic Application Logic SERVER(Server Farm) Data Storage Data Access Logic Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2. 3 The Middleware Solution • The Middleware Solution? – One of the strengths of client-server networks is that they enable software and hardware from different vendors to be used together • How is this a disadvantage or a bad thing? – Well, it can be difficult to get software from different vendors to work together • First, What is Middleware? – It is software that sits between the application software on the client and the application software on the server Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2. 3 Client – Server Architectures Cont. • Middleware does two things to solve the problem – First • It provides a standard way of communicating that can translate between software from different vendors – Second • It manages the message transfer from clients to servers( and vice versa) so that clients need not know the specific server that contains the application’s data. • The application software on the client sends all messages to the middleware, which forwards them to the correct server • Furthermore, the application software on the client is therefore protected from any changes in the physical network. Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2. 3 Client – Server Architectures Cont. • Two- Tier, Three – Tier, and n – Tier Architectures – Video Explaining the Different Architectures Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
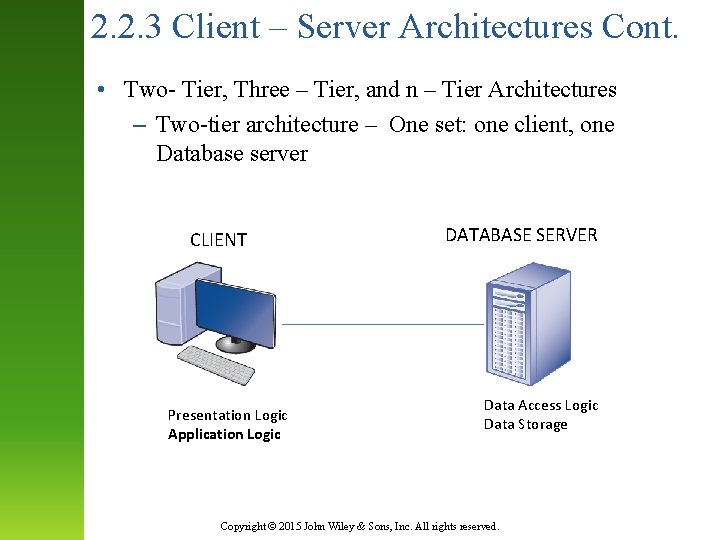
2. 2. 3 Client – Server Architectures Cont. • Two- Tier, Three – Tier, and n – Tier Architectures – Two-tier architecture – One set: one client, one Database server CLIENT Presentation Logic Application Logic DATABASE SERVER Data Access Logic Data Storage Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
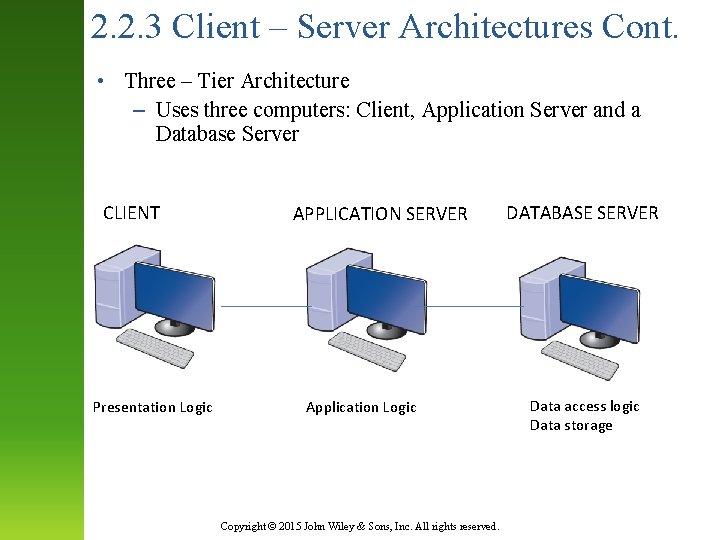
2. 2. 3 Client – Server Architectures Cont. • Three – Tier Architecture – Uses three computers: Client, Application Server and a Database Server CLIENT Presentation Logic APPLICATION SERVER Application Logic Copyright © 2015 John Wiley & Sons, Inc. All rights reserved. DATABASE SERVER Data access logic Data storage
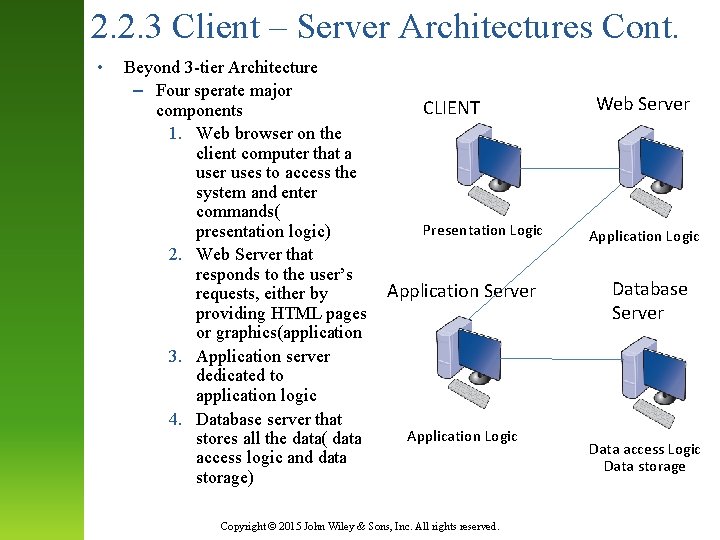
2. 2. 3 Client – Server Architectures Cont. • Beyond 3 -tier Architecture – Four sperate major components 1. Web browser on the client computer that a user uses to access the system and enter commands( presentation logic) 2. Web Server that responds to the user’s requests, either by providing HTML pages or graphics(application 3. Application server dedicated to application logic 4. Database server that stores all the data( data access logic and data storage) CLIENT Presentation Logic Application Server Application Logic Copyright © 2015 John Wiley & Sons, Inc. All rights reserved. Web Server Application Logic Database Server Data access Logic Data storage
2. 2. 3 Thin Clients vs Thick Clients Intro. • Another way of classifying client-server architectures is by examining how much of the application logic is placed on the client computer • Thin – Client – Places little or no application logic on the client, i. e. Web application in Web Browser – Web Mail browser • Thick – Client – Places all or almost all of the application logic on the client – Office 2016, i. e. Power. Point, Outlook, etc. are installed on hard drive of client Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2. 3 Thin Clients vs Thick Clients Differences • Thin Clients are much easier to manage – For example, • If an application changes, only the server with the application logic needs to be updated • Whereas with a thick client, the software on all of clients must be updated, i. e. Office 2016 updates • Thin Clients are becoming more popular: – More and more application systems are being written to use a Web browser as the interface, • For instance : Javascriptor AJAX • Also called the distributed computing model Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
2. 2. 4 – Cloud Computing Architectures • Video Explaining What is Cloud Computing, Software as a Service(Saa. S), Platform as a Service(Paa. S), and Infrastructure as a Service(Iaa. S) • Conclusion of Cloud Computing, – Technology that fundamentally changed the way we think about applications in that they are rented and paid for as a service – Idea Similar to Using Utilities such as Water, Gas, Cable, and Phone Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
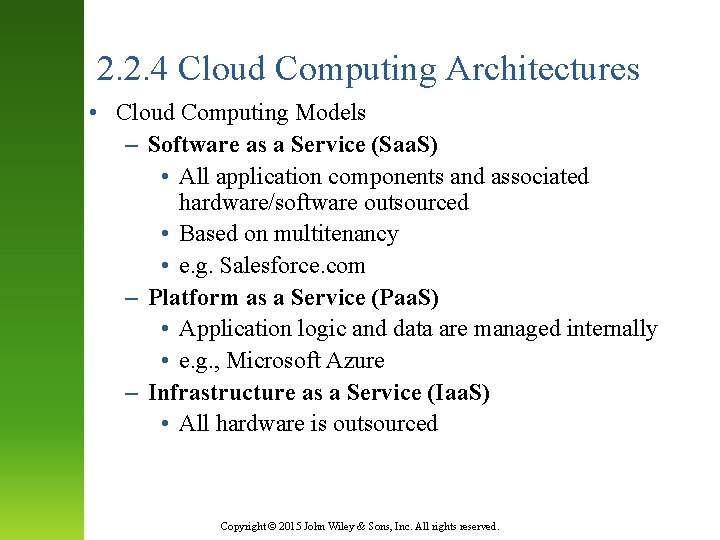
2. 2. 4 Cloud Computing Architectures • Cloud Computing Models – Software as a Service (Saa. S) • All application components and associated hardware/software outsourced • Based on multitenancy • e. g. Salesforce. com – Platform as a Service (Paa. S) • Application logic and data are managed internally • e. g. , Microsoft Azure – Infrastructure as a Service (Iaa. S) • All hardware is outsourced Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
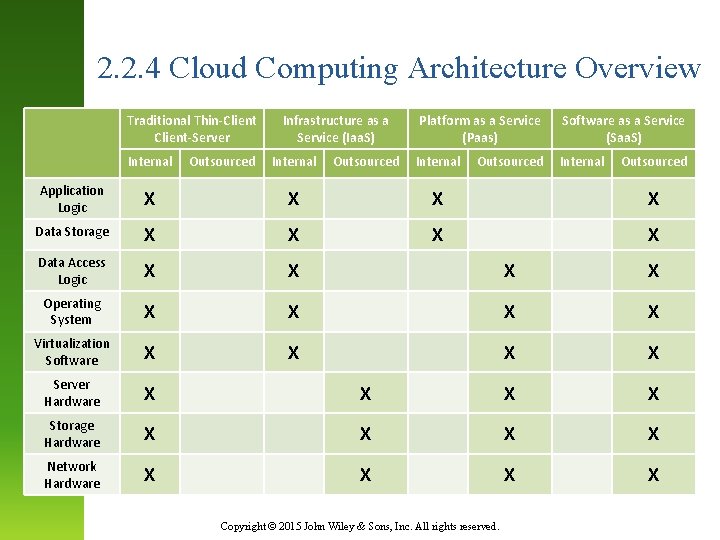
2. 2. 4 Cloud Computing Architecture Overview Traditional Thin-Client-Server Internal Outsourced Infrastructure as a Service (Iaa. S) Internal Outsourced Platform as a Service (Paas) Software as a Service (Saa. S) Internal Outsourced Application Logic X X Data Storage X X Data Access Logic X X Operating System X X Virtualization Software X X Server Hardware X X Storage Hardware X X Network Hardware X X Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.

2. 2. 5 Peer- to – Peer Architectures • • Background of the Architecture • Very old • Popular in the early 2000 s: rise of P 2 P file sharing applications ( e. g. , Napster) How it Works • All computers act as both a client and a server • All computers perform all four functions : presentation logic, application logic, data access logic, and data storage • With a P 2 P file sharing application, a user uses a presentation application, and data access logic installed on his or her computer to access the data stored on another computer in the network • Advantage of The Network • Data can be installed anywhere on the network • They spread the storage throughout the network, even globally, so they can be very resilient to the failure of any one computer • Challenge of the Architecture • The challenge is finding the data • Need central server that enables you to find the data you need, so P 2 P architectures often are combined with a client – server architecture • Security in the Peer – To – Peer Networks • Security Is a major concern in most P 2 P networks, so P 2 P architectures are not commonly used in organizations, except for specialized computing needs( e. g. , grid computing) Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
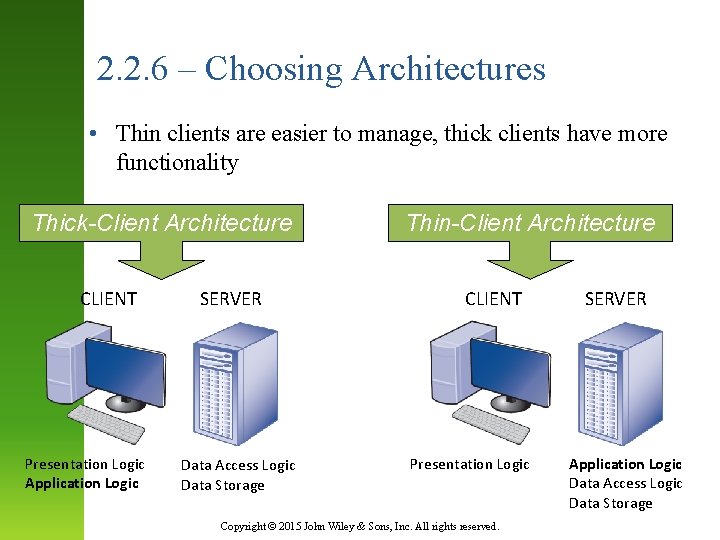
2. 2. 6 – Choosing Architectures • Thin clients are easier to manage, thick clients have more functionality Thick-Client Architecture CLIENT Presentation Logic Application Logic SERVER Data Access Logic Data Storage Thin-Client Architecture CLIENT Presentation Logic Copyright © 2015 John Wiley & Sons, Inc. All rights reserved. SERVER Application Logic Data Access Logic Data Storage
Criteria for Choosing Architecture • Infrastructure – Cost of servers, clients, and circuits – Reliability • Development Costs – Software; cheaper on host-based architectures • Scalability – Ability to increase (or decrease) in computing capacity as network demand changes – Easier in client-server architectures Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
THE END! Copyright © 2015 John Wiley & Sons, Inc. All rights reserved.
- Slides: 23