Business Continuity and Information Security Camillo Toselli Tuesday
Business Continuity and Information Security Camillo Toselli Tuesday 24 th May 2016
Topics • Information Security • Business Continuity • Escalation Process • Case Study: multiple phases email box attack • Portable devices and security Tuesday 24 th May 2016 pag. 2
What is Information Security? - 1 The aim of Information Security is to • ensure that information systems achieve accurately the assigned tasks, error free and tampering free • ensure that information systems and data can be used or modified only by authorized people • check if and when infringments to the two previous points take place and, possibly, • restore original data (before tampering has taken place) and stop the recognized source of tampering/unauthorized access Tuesday 24 th May 2016 pag. 3
How to do Information Security? - 1 For example, consider the application design process. The application • must be designed to avoid security issues since the early stages. The key point is to produce test-friendly software: check points and logging features should be deeply embedded in the software structure • must be implemented thinking to what kind of interactions with other applications, servers, network, storage, etc. . will take place • must handle correctly authentication, authorization and accounting process and should be able to manage multiple administration and users access profiles Tuesday 24 th May 2016 pag. 4
How to do Information Security? – 2 Hence, it follows that if the application • has bugs or poorly designed procedures which can result in unpredictable behaviour, application crash or more severe system crash (input validation) • has no logging/accounting tools for tracing application/user behaviour • wastes infrastructure resources such as network, servers and storage • does not handle correctly authentication/authorization process • has unknown interactions with other parts of the infrastructure will be unsafe. Tuesday 24 th May 2016 pag. 5
Where to do Information Security? – Infrastructure • The most common way to gain access to information systems is through the network. Hence, Information Security is deeply related to network infrastructure which should embed specific tools to monitor (IDS) and block (IPS) behaviour-oriented security attacks. Protocol-oriented security threats are handled by stateful firewalls. However, information security does not involve only network infrastructure protection: • System infrastructure protection has a central role in information security and it is usually concerned to hostoriented tools. • Application infrastructure has strict interactions with the previous infrastructures and must contribute to the monitoring and prevention of attacks through behaviororiented analysis of components interactions. Tuesday 24 th May 2016 pag. 6
Where to do Information Security? – Application • The most common targets of security attacks and threats are application vulnerabilities which arise from any weakness manifested in design/development phases. • There are specific methodologies and tools for both design and development phases which give support to prevention of security issues. (for example, OWASP) Tuesday 24 th May 2016 pag. 7
Where to do Information Security? – Client-side Observing that • using client devices in a safe and aware manner reduces consistenly the probability of being exploited • exploited intra-organization client devices are the preferred assets for hackers to gain access to internal information systems it can be deduced that • using client devices in a safe and aware manner protects user’s personal data and organization’s data as well Hence, it is extremely important to promote such behaviours. Tuesday 24 th May 2016 pag. 8
Business Continuity – What is and why is important Business Continuity is a meta process which aims to ensure that services are working correctly and respect SLA even if • infrastructure/application/process changes are needed in order to § introduce new features § optimize/strengthen existing features • routine or extra maintenance activities are required • adverse events occour (e. g. security attacks, failures) B. C. relies on Risk Assessment and Risk Management processes Tuesday 24 th May 2016 pag. 9
Business Continuity – How to do - 1 Coherent actions on infrastructures/applications/processes require: • Asset and Configuration management: § the CMDB is a tool for managing assets and relations among them § the DMS is a tool for documentation purposes (e. g. Wiki) § backup tools for configurations, servers, data, etc… • Asset monitoring: § automated monitoring tools (e. g. Nagios) § manual (checklists to do routinely) • Roles and procedures definition: § Incident, Problem, Change, Request Management These are the basic daily tools required for doing Business Continuity Tuesday 24 th May 2016 pag. 10
Business Continuity – How to do - 2 Data collected by mean of descripted tools and procedures • allow to semplify daily management tasks • permit to effectively perform service recovery when adverse events occur To be useful, collected data must be • up-to-date: to recover the most recent service state • tested: administrators should be able to trust them • well organized: administrators should be able to easily understand them • centralized: stored in a single repository which can be replicated in a disaster recovery site Tuesday 24 th May 2016 pag. 11
Escalation Process – What is The key point of Business Continuity is to optimize fault management meta process to achieve the service recovery as responsive and efficient as possible. The fault management meta process relies on several subprocess which are categorized on the actual severity of the event occured: • Level 1 Incident Management: low severity • Level 2 Problem Management: medium/high severity • Level 3 Emergency Management: high/very high severity • Level 4 Disaster Management: disaster event – DRP The Escalation Process defines the correct escalation (forward and backward) path among levels 1, 2 and 3. Tuesday 24 th May 2016 pag. 12
Escalation Process – Definitions - 1 Severity depends on priority and it is categorized as follows: • Incident: a single service failure seems to be delimited to few users. Monitoring parameters for that service are under the warning threshold. Specifically, symptoms could be: § reduced service quality for a few users § monitoring tools show the failure of a component in a redudant system that has no significant impact on services • Problem: one or more services fail. Each service failure seems to be generalized to almost all users. Monitoring parameters for those services are above warning threshold. However, most services still work correctly. Usually, a problem is the root cause of several simultaneous incidents. (Correlation) • Emergency: one or more services fail but almost all services show monitoring parameters significantly beyond threshold. It is possible to foresee when the services will be up again. • Disaster: no service is available and it is not possible to tell precisely when they will be recovered. Tuesday 24 th May 2016 pag. 13
Escalation Process – Definitions - 2 Priority is calculated as a product of impact and urgency factors: The impact factor depends on how much the failures are widespread: • which and how many departments are affected? • which and how many services are affected? • which and how many business process are affected? The urgency factor depends on • how long the services has been unavailable • deadlines (e. g. enrollment taxes) • affected stakeholders Tuesday 24 th May 2016 pag. 14
Escalation Process – Critical elements - 1 The responsive phase of the process should take into account the following elements: • Subjectiveness can not be avoided when severity is evaluated: • local and global point of view • background and contextual information • integration of monitoring/troubleshooting tools • Organization of the response activities is the key factor: • coherent analysis • communications between actors • schedule of the analysis/recovery actions Tuesday 24 th May 2016 pag. 15
Escalation Process – Critical elements - 2 • A Communication plan to the users is needed. Information must be delivered • quickly • accurately • transparently • Checking every remediation/resolution activity is important to avoid errors: • A follow-up process to verify that every change gives the expected result • A review process to understand why the failure has taken place and to determine how to avoid new occurences of the same issue Tuesday 24 th May 2016 pag. 16
Escalation Process – Critical elements - 3 The proactive phase of the process should take into account the following elements: • Risk Analysis of architectures and services during design phase • Planning of routine maintenance activities • Information sharing: § a bulletin board which displays key events, deploys, planned maintenance activities, deadlines, etc… • Risk Management Team to give support for key events Tuesday 24 th May 2016 pag. 17
Escalation Process – Critical elements - 4 Finally, more general elements to be considered should be: • Roles defined in the Escalation Process have to be specific to improve skills • Escalation Process must be exposed to constant revision: it is important to make only few changes at a time to correctly evaluate the effect • The Escalation Process overhead on daily tasks must avoid Tuesday 24 th May 2016 pag. 18 any unnecessary
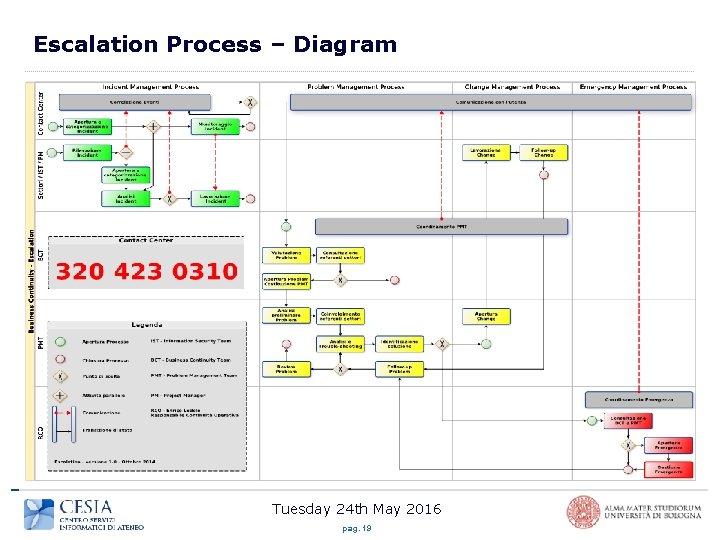
Escalation Process – Diagram Tuesday 24 th May 2016 pag. 19
Case study: Email – Security Tools Email server infrastructure is protected by active and passive security tools: • Antispam: • Reputation System - Behavioural Analizer – Content Analizer • Antivirus – Attachment Cleaner • Spamtraps – Sandboxing • Behavioural Firewall Email clients are protected by active security tools: • Antivirus • Webfilter • personal and network Firewalls Tuesday 24 th May 2016 pag. 20
Case study: Email – « 0 -Days Attacks» Malware distributed through emails can be spread • either as attachments analyzed by Antivirus, Sandboxes • or as hyperlinks analyzed by Web-Filters, Reputation systems Security tools can be bypassed by • obfuscating the code with not yet known algorithms • applying dynamic polymorphism to code/urls to make signature-analyzers useless More generally, security systems can be bypassed by • using exploits based on undisclosed software vulnerabilities Tuesday 24 th May 2016 pag. 21
Case study: Email – The war begins - 1 Alert state has been raised by • a few users who noticed that they can not access some of their files stored on a shared file server • spamtraps received emails with suspicious attachments • email service administrators observe a massive flow of emails However, • attachments were not recognized as potential malware by several antivirus yet • reputation filters had not categorized email sources as dangerous yet Tuesday 24 th May 2016 pag. 22
Case study: Email – The war begins - 2 Escalation Process starts and Computer System Incident Response Team (CSIRT) discovers that • sandboxed execution of the attached code displays anomalous behaviour which can be related to a Crypto. Locker malware • inaccessible files on the shared file server were already crypted • a few antiviruses recognize threat (2/98) Tuesday 24 th May 2016 pag. 23
Case study: Email – Fight! - 1 First step countermeasures: • writing to the file server was temporarily forbidden • suspicious attachments were removed from emails: infection vector was a. cab compressed archive • users were informed of the running attack and were told how to behave with respect to email attachments • malware samples were sent to Sophos to generate the required antivirus signatures • when the antivirus has been updated with the new signatures, writing to the file server was allowed again Tuesday 24 th May 2016 pag. 24
Case study: Email – Fight! - 2 After that, attackers started developing new strategies: • crafting emails with more trustworthy content • continuosly changing the attachment type • developing delayed activation malware Hence, more efficient defensive strategies were needed: • users were suddendly informed of an incoming attack when the first symptoms revealed • execution of email attachments was forbidden • potential dangerous attachments were removed if directed to mail boxes of people who have permission to access to critical shared file servers Tuesday 24 th May 2016 pag. 25
Yuor smartphone is a PC… • a rough comparison between smartphone’s and PC’s computation performance shows 1 Notebook @ 2004 ≈ 1 Smartphone @ 2010 1 Notebook @ 2006 ≈ 1 Smartphone @ 2012 • however, if integrated peripherals and sensors are compared, there is no match: Smartphone @ 2012 vs. Notebook @ 2006 5, 6, …, 10 – 0: • Network/Communications Interfaces • Sensors/Position Gathering • Multimedia Capabilities • talking about usability, the revolution is going on and was started by Apple with i. Phone and closely followed by all other competitors, notably by Google Android Tuesday 24 th May 2016 pag. 26
…with a incredibly easier interface • nevertheless, such an easy interaction model hides a true operative system under the hood • GNU Linux @ Android • BSD Unix @ i. OS • Win 32 @ Windows Phone • which require a lot of carefulness and awareness to avoid security pitfalls: OS and Apps can be exploited Tuesday 24 th May 2016 pag. 27
Your smartphone knows everything of you… • it knows your digital identities (accounts) you use • for institutional purposes: workplace, government, educational… • for services: Email, on-line shopping, bank account… • for social networks: Facebook, Google+, Twitter… • it knows your debit/credit card number • it knows what you are doing: • calendars, events, Siri, Google Now… • Position: GPS, GSM/3 G, Wi. Fi… • it knows what you are talking about: • SMS, Email, Instant Messaging, phone calls… • It knows who you are talking to: • Contact lists: phone numbers, Email addresses, social newtork contacts… Tuesday 24 th May 2016 pag. 28
…and it can tell to everyone! • your smartphone is exploitable and if exploited it can tell your personal information to someone who owns its control • it tells where you are • it tells who your talking/messaging to • it tells what you are talking/chatting about • it tells your habits • it tells which services you use and how you use them • it can take pictures, listen your phone calls or do environmental monitoring • your smartphone can be used to attribute to you crimes actually committed by someone else • rooting (jailbreaking) your smartphone exponentially rise the risk of exploitation Tuesday 24 th May 2016 pag. 29
Malware starts spreading… • to root your smartphone you need to apply an exploit which relies on software vulnerabilities: • no (or default) root password • apps execute with excessive privilege • hacked software from untrusted or illegal sources is full of malware and backdoors • an exploited smartphone is a vehicle for further exploitation: • remote control consoles • rogue AP through portable Wi. Fi Hotspot Wi. Fi • scanning/bruteforcing • Do. S attacks to network infrastructure Tuesday 24 th May 2016 pag. 30
How to defend? • risk awareness and careful usage: • change frequently the passwords, choose secure passwords • keep system and apps as updated as possible • avoid hackered apps and illegal or bordeline behaviour • install antimalware and monitoring tools • you have to know what your apps are doing: • rooting (jailbreak), p 2 p, instant-messagging, networkscan/hacking, darknet are risky apps Tuesday 24 th May 2016 pag. 31
- Slides: 31