Building Secure Microservices Design Patterns Adib Saikali asaikali

Building Secure Microservices Design Patterns Adib Saikali – @asaikali Advisory Platform Architect © 2016 Pivotal Software, Inc. All rights reserved. 1

The Goal Secure Microservices © 2016 Pivotal Software, Inc. All rights reserved. 2
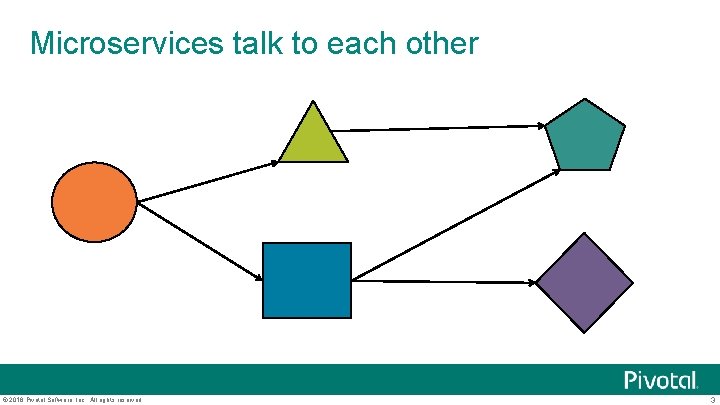
Microservices talk to each other © 2016 Pivotal Software, Inc. All rights reserved. 3
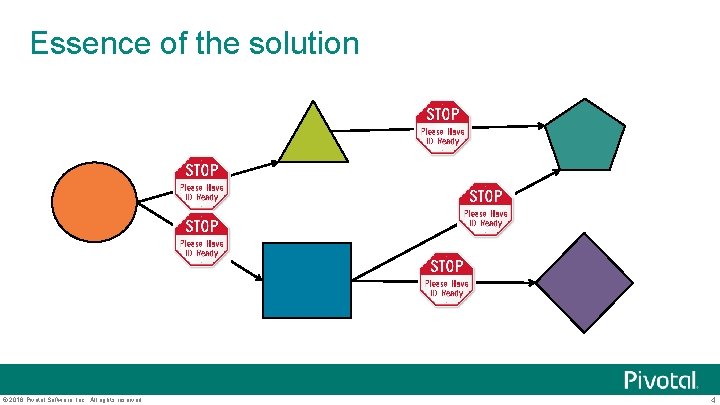
Essence of the solution © 2016 Pivotal Software, Inc. All rights reserved. 4
Solution Every request to a microservice must include a security token that the microservice can easily authenticate and use for making authorization decisions. © 2016 Pivotal Software, Inc. All rights reserved. 5
What protocol does your microservice speak? HTTP (REST, SOAP) AMQP (Messaging) Apache Thrift (Remote Procedure Call Framework) g. RPC (Remote Procedure Call Framework) § A high performance, open source, general RPC framework that puts mobile and HTTP/2 first from Google. Custom TCP protocol © 2016 Pivotal Software, Inc. All rights reserved. 6
Key Idea: There is no one “best” protocol! There is no one best protocol to use Protocols will evolve over time so it’s best to make sure that any security solution can work with current and future protocols © 2016 Pivotal Software, Inc. All rights reserved. 7
Problems to solve What format should security token use? How are tokens supposed to be obtained? What libraries should be used for authentication and authorization when implementing microservices? What information should be in the token? © 2016 Pivotal Software, Inc. All rights reserved. 8

What Format Should Security Tokens Use? Answer is to use a “standard” token format © 2016 Pivotal Software, Inc. All rights reserved. 9
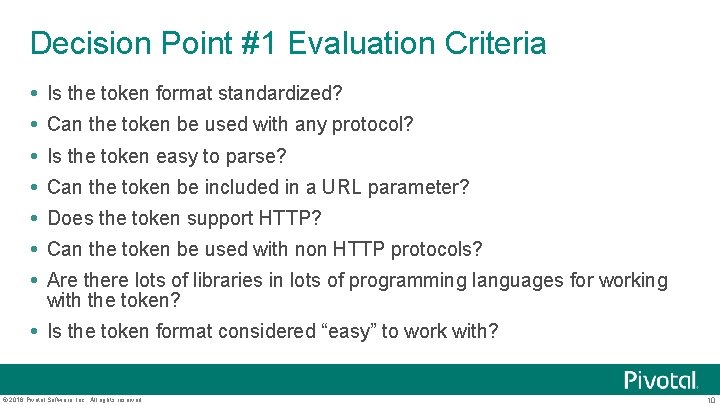
Decision Point #1 Evaluation Criteria Is the token format standardized? Can the token be used with any protocol? Is the token easy to parse? Can the token be included in a URL parameter? Does the token support HTTP? Can the token be used with non HTTP protocols? Are there lots of libraries in lots of programming languages for working with the token? Is the token format considered “easy” to work with? © 2016 Pivotal Software, Inc. All rights reserved. 10
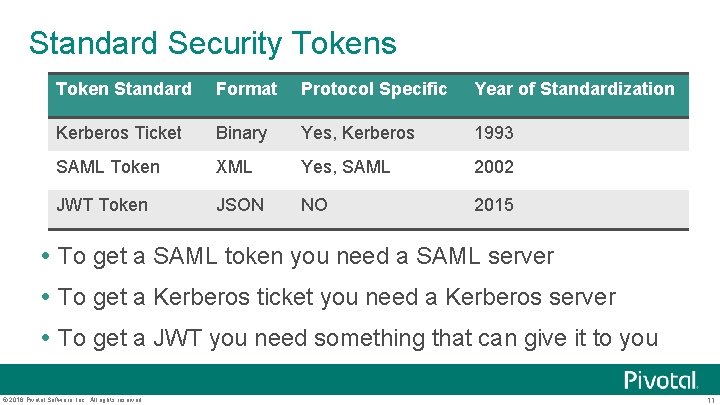
Standard Security Tokens Token Standard Format Protocol Specific Year of Standardization Kerberos Ticket Binary Yes, Kerberos 1993 SAML Token XML Yes, SAML 2002 JWT Token JSON NO 2015 To get a SAML token you need a SAML server To get a Kerberos ticket you need a Kerberos server To get a JWT you need something that can give it to you © 2016 Pivotal Software, Inc. All rights reserved. 11

A Toolbox of Standards RFC Name Title 5849 OAuth 1 The OAuth 1. 0 Protocol Apr 2010 https: //tools. ietf. org/html/rfc 5849 6749 OAuth 2 The OAuth 2. 0 Authorization Framework Oct 2012 https: //tools. ietf. org/html/rfc 6749 6750 Bearer Token The OAuth 2. 0 Authorization Framework: Bearer Token Usage Oct 2012 https: //tools. ietf. org/html/rfc 6750 7516 JWE JSON Web Encryption May 2015 https: //tools. ietf. org/html/rfc 7516 7517 JWK JSON Web Key May 2015 https: //tools. ietf. org/html/rfc 7517 7518 JWA JSON Web Algorithms May 2015 https: //tools. ietf. org/html/rfc 7518 7519 JWT JSON Web Token May 2015 https: //tools. ietf. org/html/rfc 7519 7520 JOSE Examples of Protecting Content Using JSON Object Signing and Encryption May 2015 https: //tools. ietf. org/html/rfc 7520 JSON Web Signature (JWS) Unencoded Payload Option Feb 2016 https: //tools. ietf. org/html/rfc 7797 © 2016 Pivotal Software, Inc. All rights reserved. Date Spec 12
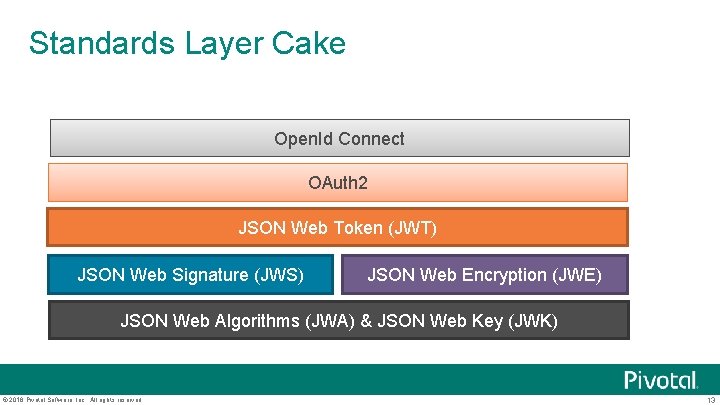
Standards Layer Cake Open. Id Connect OAuth 2 JSON Web Token (JWT) JSON Web Signature (JWS) JSON Web Encryption (JWE) JSON Web Algorithms (JWA) & JSON Web Key (JWK) © 2016 Pivotal Software, Inc. All rights reserved. 13
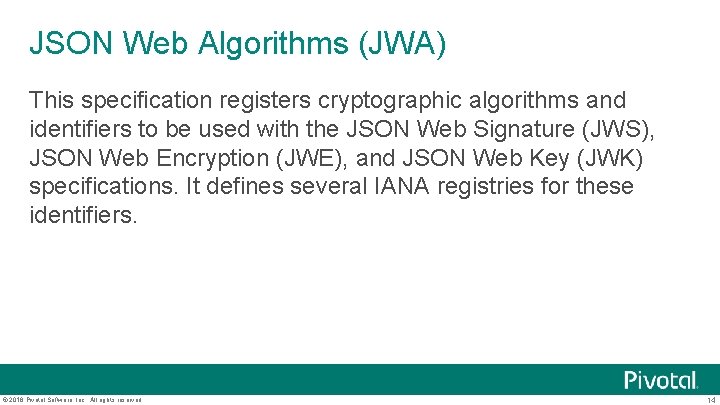
JSON Web Algorithms (JWA) This specification registers cryptographic algorithms and identifiers to be used with the JSON Web Signature (JWS), JSON Web Encryption (JWE), and JSON Web Key (JWK) specifications. It defines several IANA registries for these identifiers. © 2016 Pivotal Software, Inc. All rights reserved. 14
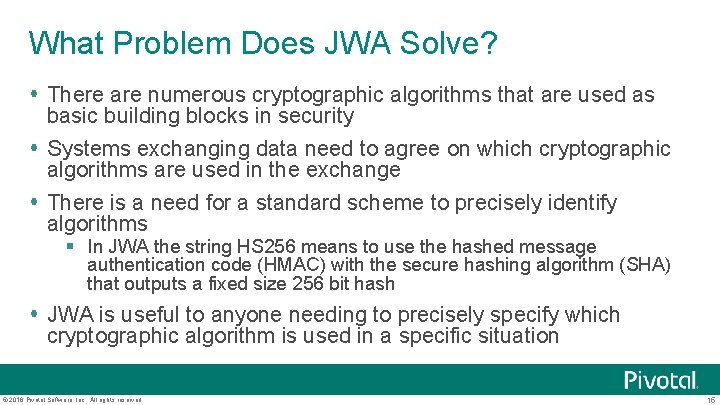
What Problem Does JWA Solve? There are numerous cryptographic algorithms that are used as basic building blocks in security Systems exchanging data need to agree on which cryptographic algorithms are used in the exchange There is a need for a standard scheme to precisely identify algorithms § In JWA the string HS 256 means to use the hashed message authentication code (HMAC) with the secure hashing algorithm (SHA) that outputs a fixed size 256 bit hash JWA is useful to anyone needing to precisely specify which cryptographic algorithm is used in a specific situation © 2016 Pivotal Software, Inc. All rights reserved. 15
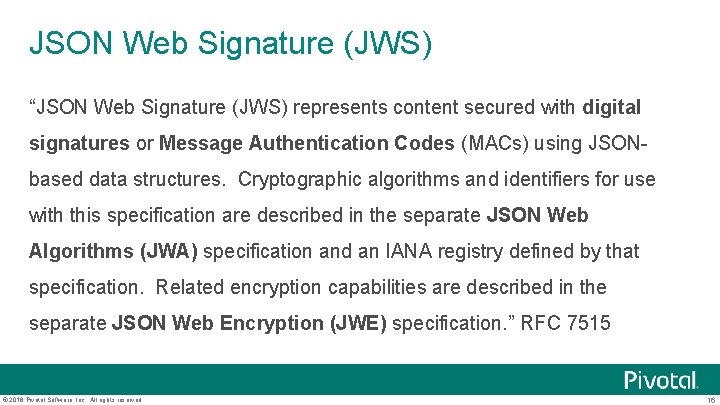
JSON Web Signature (JWS) “JSON Web Signature (JWS) represents content secured with digital signatures or Message Authentication Codes (MACs) using JSONbased data structures. Cryptographic algorithms and identifiers for use with this specification are described in the separate JSON Web Algorithms (JWA) specification and an IANA registry defined by that specification. Related encryption capabilities are described in the separate JSON Web Encryption (JWE) specification. ” RFC 7515 © 2016 Pivotal Software, Inc. All rights reserved. 16
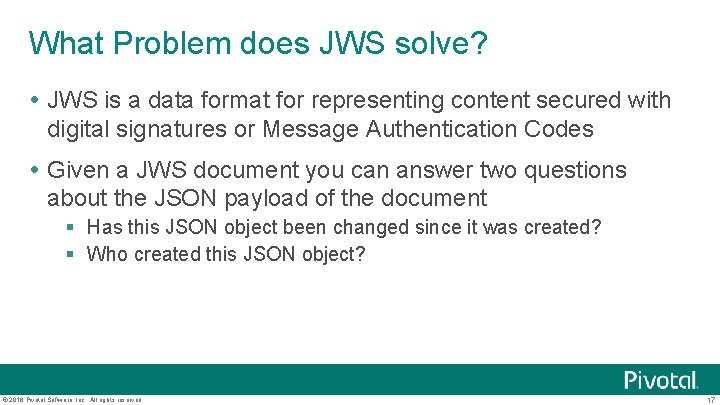
What Problem does JWS solve? JWS is a data format for representing content secured with digital signatures or Message Authentication Codes Given a JWS document you can answer two questions about the JSON payload of the document § Has this JSON object been changed since it was created? § Who created this JSON object? © 2016 Pivotal Software, Inc. All rights reserved. 17
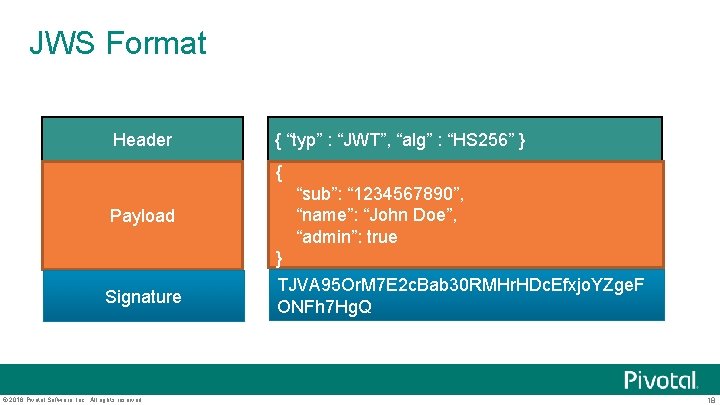
JWS Format Header { “typ” : “JWT”, “alg” : “HS 256” } { Payload Signature © 2016 Pivotal Software, Inc. All rights reserved. “sub”: “ 1234567890”, “name”: “John Doe”, “admin”: true } TJVA 95 Or. M 7 E 2 c. Bab 30 RMHr. HDc. Efxjo. YZge. F ONFh 7 Hg. Q 18
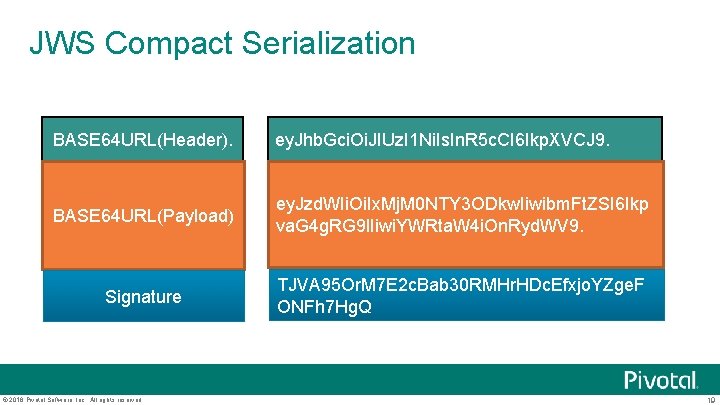
JWS Compact Serialization BASE 64 URL(Header). ey. Jhb. Gci. Oi. JIUz. I 1 Ni. Is. In. R 5 c. CI 6 Ikp. XVCJ 9. BASE 64 URL(Payload) ey. Jzd. WIi. Oi. Ix. Mj. M 0 NTY 3 ODkw. Iiwibm. Ft. ZSI 6 Ikp va. G 4 g. RG 9 l. Iiwi. YWRta. W 4 i. On. Ryd. WV 9. Signature TJVA 95 Or. M 7 E 2 c. Bab 30 RMHr. HDc. Efxjo. YZge. F ONFh 7 Hg. Q © 2016 Pivotal Software, Inc. All rights reserved. 19
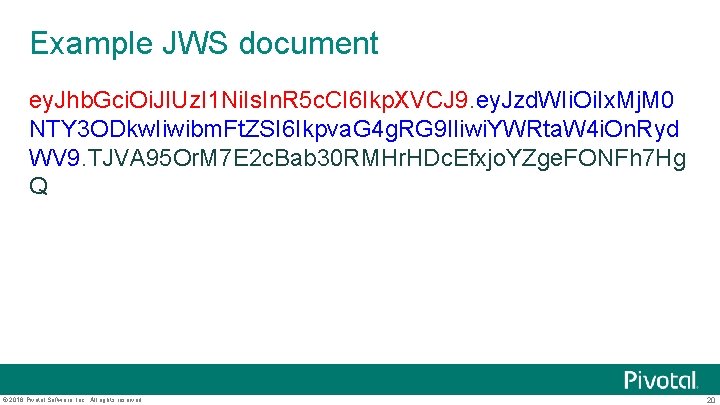
Example JWS document ey. Jhb. Gci. Oi. JIUz. I 1 Ni. Is. In. R 5 c. CI 6 Ikp. XVCJ 9. ey. Jzd. WIi. Oi. Ix. Mj. M 0 NTY 3 ODkw. Iiwibm. Ft. ZSI 6 Ikpva. G 4 g. RG 9 l. Iiwi. YWRta. W 4 i. On. Ryd WV 9. TJVA 95 Or. M 7 E 2 c. Bab 30 RMHr. HDc. Efxjo. YZge. FONFh 7 Hg Q © 2016 Pivotal Software, Inc. All rights reserved. 20
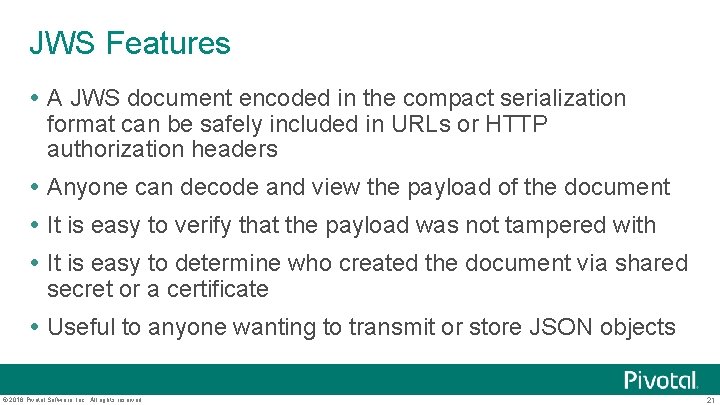
JWS Features A JWS document encoded in the compact serialization format can be safely included in URLs or HTTP authorization headers Anyone can decode and view the payload of the document It is easy to verify that the payload was not tampered with It is easy to determine who created the document via shared secret or a certificate Useful to anyone wanting to transmit or store JSON objects © 2016 Pivotal Software, Inc. All rights reserved. 21
What Problem does JWE solve? JWE is a data format for representing content that has been encrypted using JSON data structures Given a JSON you can encrypt it and represent the result as a JWE document © 2016 Pivotal Software, Inc. All rights reserved. 22
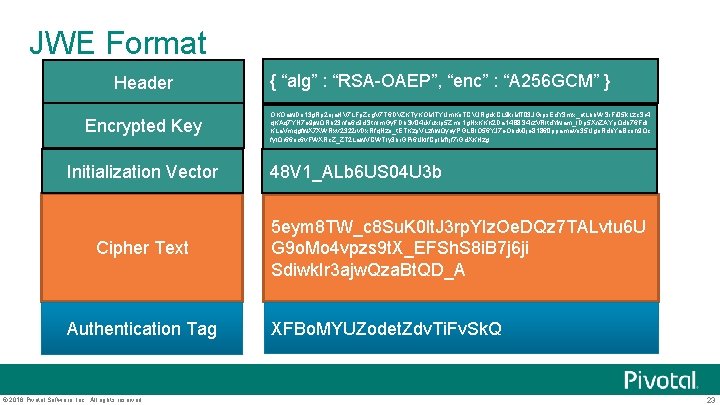
JWE Format Header Encrypted Key Initialization Vector Cipher Text Authentication Tag © 2016 Pivotal Software, Inc. All rights reserved. { “alg” : “RSA-OAEP”, “enc” : “A 256 GCM” } OKOaw. Do 13 g. Rp 2 oja. HV 7 LFp. Zcg. V 7 T 6 DVZKTy. KOMTYUm. Ko. TCVJRgck. CL 9 ki. MT 03 JGips. Ed. Y 3 mx_et. Lbb. WSr. Fr 05 k. Lzc. Sr 4 q. KAq 7 YN 7 e 9 jw. QRb 23 nfa 6 c 9 d. Stn. Im. Gy. FDb. Sv 04 u. Vux. Ip 5 Zms 1 g. Nx. KKK 2 Da 14 B 8 S 4 rz. VRltd. Ywam_l. Dp 5 Xn. ZAYp. Qdb 76 Fd. I KLa. Vmqgfw. X 7 XWRxv 2322 iv. Dx. Rfq. Nzo_t. ETKzp. VLzfiw. Qyey. PGLBIO 56 YJ 7 e. Obdv 0 je 81860 ppamavo 35 Ugo. Rdb. Ya. Bcoh 9 Qc fyl. Qr 66 oc 6 v. FWXRc. Z_ZT 2 Law. VCWTIy 3 br. GPi 6 Uklf. Cp. IMf. Ijf 7 i. Gd. XKHzg 48 V 1_ALb 6 US 04 U 3 b 5 eym 8 TW_c 8 Su. K 0 lt. J 3 rp. YIz. Oe. DQz 7 TALvtu 6 U G 9 o. Mo 4 vpzs 9 t. X_EFSh. S 8 i. B 7 j 6 ji Sdiwk. Ir 3 ajw. Qza. Bt. QD_A XFBo. MYUZodet. Zdv. Ti. Fv. Sk. Q 23
Example JWE document ey. Jhb. Gci. Oi. JSU 0 Ex. Xz. Ui. LCJra. WQi. Oi. Jmcm 9 kby 5 i. YWdna. W 5 z. QGhv. Ym. Jpd. G 9 u. Lm. V 4 YW 1 wb GUi. LCJlbm. Mi. Oi. JBMTI 4 Q 0 JDLUh. TMj. U 2 In 0. la. Lx. I 0 j-n. LH_Bg. LOXMoz. Kxmy 9 gffy 2 g. Tdvqzf. Tih. JBuuzxg 0 V 7 yk 1 WCln. Qe. PFv. G 2 Kpv. Sl. Wc 9 BRIaz. Drn 50 Rc. Rai__3 TDON 395 H 3 c 62 t. Iou. JJ 4 Xa. Rv. YHFj. ZTZ 2 GXfz 8 YAImcc 91 Tfk 0 WXC 2 F 5 Xbb 71 Cl. Q 1 DDH 151 tlp. H 77 f 2 ff 7 xi. Sxh 9 o. Sew. Yrc. GTSLUee. Ct 36 r 1 Kt 3 OSj 7 Ey. BQXo. Zl N 7 Ixbyh. MAfg. Ie 7 Mv 1 r. OTOI 5 I 8 NQqe. XXW 8 Vlz. Nmoxa. GMny 3 Yn. Gir 5 Wf 6 Qt 2 n. Bq 4 q. Da. Pdna. Au u. GUGEecel. IO 1 wx 1 Bpy. Ifgvfj. Oh. MBs 9 M 8 XL 223 Fg 47 xl. Gs. MXdfu. Y 4 jaq. Vw. bbd 5 s. Tk. Ywh. AIqf. Hsx 8 Day. A. 0 fys_TY_na 7 f 8 dw. Sf. XLi. Yd. Ha. A 2 Dx. Uj. D 67 ie. F 7 fc. Vb. IR 62 Jh Jv. GZ 4_FNVSi. Gc_raa 0 Hn. LQ 6 s 1 P 2 sv 3 Xzl 1 p 1 l_o 5 w. R_Rs. Szr. S 8 Zwn. I 3 Jvo 0 mkp. EEnl. Dm. Zv. Du_k 8 OWz. Jv 7 e. ZVEqi. WKdy. Vz. Fh. Ppiy. QU 28 GLOp. Rc 2 Vb. K 4 d. QKP d. NTj. PPEm. Rqca. Ge. TWZVye. SUvf 5 k 59 y. JZx. Ru. Sv. WFf 6 Kr. Ntm. Rd. Z 8 R 4 m. DOj. HSr. M_s 8 uw. IFcqt 4 r 5 GX 8 TKa. I 0 z. T 5 Cb. L 5 Qlw 3 s. Rc 7 u_hg 0 y. KVOi. Ryt. EAEs 3 v. Zkcf. Lk. P 6 nb. Xd. C_Pk. Md. NSoh. P 78 T 2 O 6_7 u. In. MGh. Fe. X 4 ct. HG 7 Vel. HGi. T 93 Jf. WDEQi 5_V 9 UN 1 rh. XNr. Yu 0 f. VMk. ZAKX 3 VWi 7 lz. A 6 BP 430 m. kv. Ku. FBXHe 5 m. Qr 4 lqgob. AUg © 2016 Pivotal Software, Inc. All rights reserved. 24
JWE Features A JWE document encoded in the compact serialization format can be safely included in URLs or HTTP authorization headers Payload of of the document is secured Useful to anyone wanting to transmit or store JSON objects © 2016 Pivotal Software, Inc. All rights reserved. 25
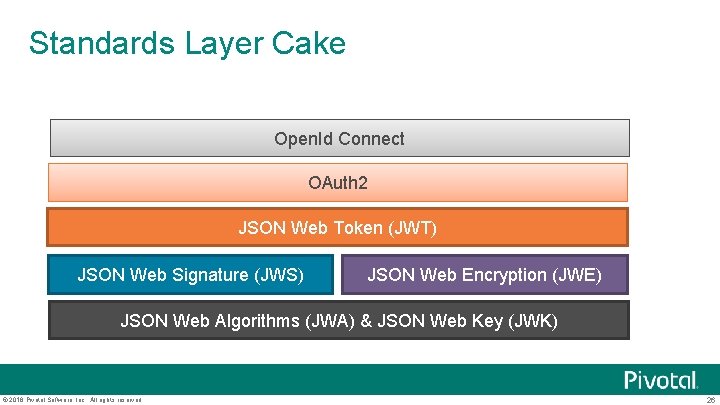
Standards Layer Cake Open. Id Connect OAuth 2 JSON Web Token (JWT) JSON Web Signature (JWS) JSON Web Encryption (JWE) JSON Web Algorithms (JWA) & JSON Web Key (JWK) © 2016 Pivotal Software, Inc. All rights reserved. 26
JSON Web Token (JWT) “JSON Web Token (JWT) is a compact, URL-safe means of representing claims to be transferred between two parties. The claims in a JWT are encoded as a JSON object that is used as the payload of a JSON Web Signature (JWS) structure or as the plaintext of a JSON Web Encryption (JWE) structure, enabling the claims to be digitally signed or integrity protected with a Message Authentication Code (MAC) and/or encrypted. ” RFC 7519 © 2016 Pivotal Software, Inc. All rights reserved. 27
JWT Token A JSON object that contains information that is useful for making security decisions § There are standard fields / claims that are part of JWT tokens The JSON object has been signed and formatted as a JWS document or encrypted and formatted as a JWE document The JWT token can be put into a URL parameter or an HTTP header jwt. io is a good resource to learn about JWT © 2016 Pivotal Software, Inc. All rights reserved. 28
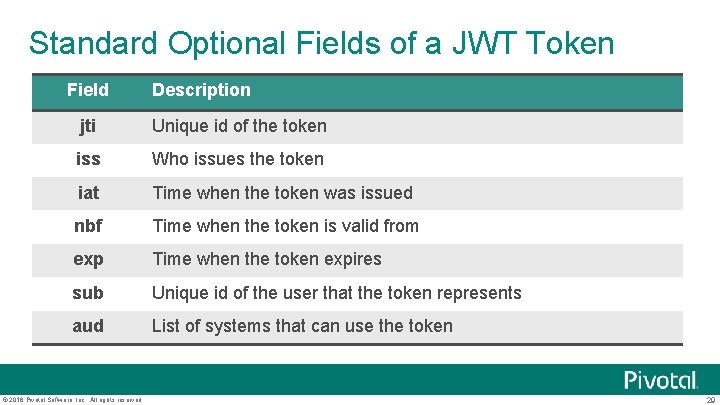
Standard Optional Fields of a JWT Token Field Description jti Unique id of the token iss Who issues the token iat Time when the token was issued nbf Time when the token is valid from exp Time when the token expires sub Unique id of the user that the token represents aud List of systems that can use the token © 2016 Pivotal Software, Inc. All rights reserved. 29
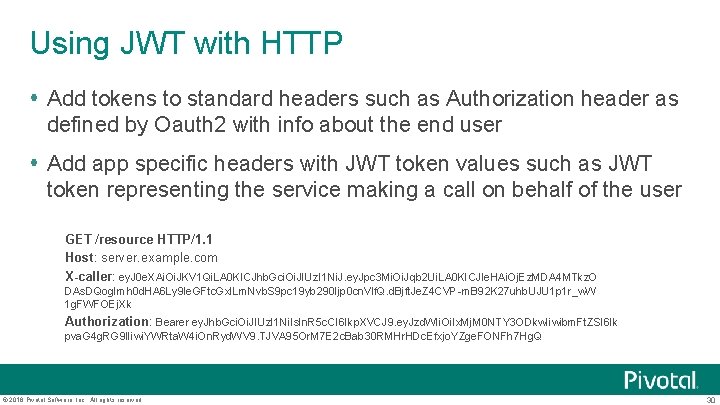
Using JWT with HTTP Add tokens to standard headers such as Authorization header as defined by Oauth 2 with info about the end user Add app specific headers with JWT token values such as JWT token representing the service making a call on behalf of the user GET /resource HTTP/1. 1 Host: server. example. com X-caller: ey. J 0 e. XAi. Oi. JKV 1 Qi. LA 0 KICJhb. Gci. Oi. JIUz. I 1 Ni. J. ey. Jpc 3 Mi. Oi. Jqb 2 Ui. LA 0 KICJle. HAi. Oj. Ez. MDA 4 MTkz. O DAs. DQog. Imh 0 d. HA 6 Ly 9 le. GFtc. Gxl. Lm. Nvb. S 9 pc 19 yb 290 Ijp 0 cn. Vlf. Q. d. Bjft. Je. Z 4 CVP-m. B 92 K 27 uhb. UJU 1 p 1 r_w. W 1 g. FWFOEj. Xk Authorization: Bearer ey. Jhb. Gci. Oi. JIUz. I 1 Ni. Is. In. R 5 c. CI 6 Ikp. XVCJ 9. ey. Jzd. WIi. Oi. Ix. Mj. M 0 NTY 3 ODkw. Iiwibm. Ft. ZSI 6 Ik pva. G 4 g. RG 9 l. Iiwi. YWRta. W 4 i. On. Ryd. WV 9. TJVA 95 Or. M 7 E 2 c. Bab 30 RMHr. HDc. Efxjo. YZge. FONFh 7 Hg. Q © 2016 Pivotal Software, Inc. All rights reserved. 30
Using with JMS / Rabbit. MQ Add the JWT token to a custom header in the outgoing JMS message © 2016 Pivotal Software, Inc. All rights reserved. 31
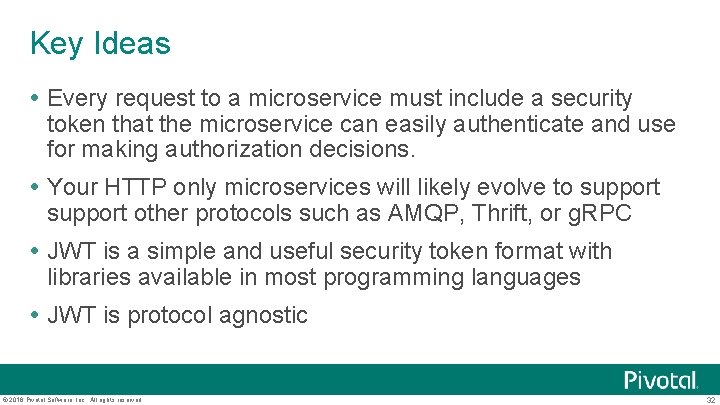
Key Ideas Every request to a microservice must include a security token that the microservice can easily authenticate and use for making authorization decisions. Your HTTP only microservices will likely evolve to support other protocols such as AMQP, Thrift, or g. RPC JWT is a simple and useful security token format with libraries available in most programming languages JWT is protocol agnostic © 2016 Pivotal Software, Inc. All rights reserved. 32
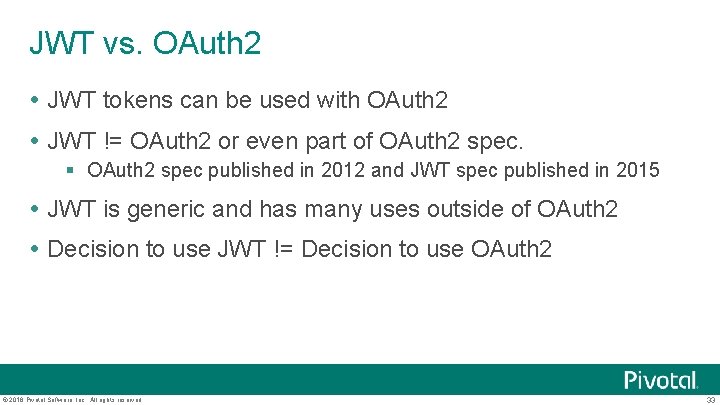
JWT vs. OAuth 2 JWT tokens can be used with OAuth 2 JWT != OAuth 2 or even part of OAuth 2 spec. § OAuth 2 spec published in 2012 and JWT spec published in 2015 JWT is generic and has many uses outside of OAuth 2 Decision to use JWT != Decision to use OAuth 2 © 2016 Pivotal Software, Inc. All rights reserved. 33
Problems to solve What format should security token use? How are tokens supposed to be obtained? What libraries should be used for authentication and authorization when implementing microservices? What information should be in the token? © 2016 Pivotal Software, Inc. All rights reserved. 34
How are JWT tokens obtained? Get your JWT Tokens from an OAuth 2/Open. Id Connect Server © 2016 Pivotal Software, Inc. All rights reserved. 35
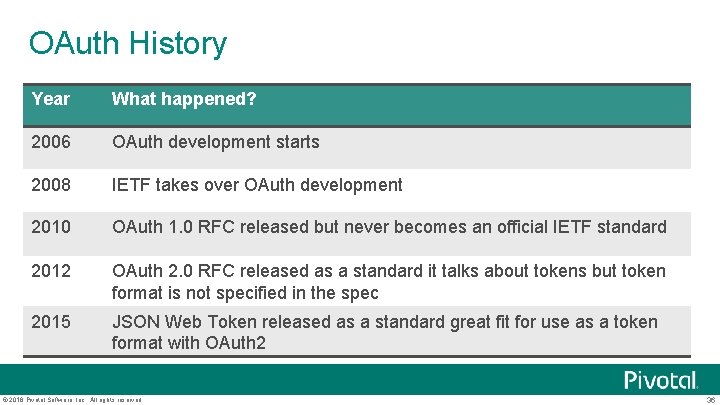
OAuth History Year What happened? 2006 OAuth development starts 2008 IETF takes over OAuth development 2010 OAuth 1. 0 RFC released but never becomes an official IETF standard 2012 OAuth 2. 0 RFC released as a standard it talks about tokens but token format is not specified in the spec 2015 JSON Web Token released as a standard great fit for use as a token format with OAuth 2 © 2016 Pivotal Software, Inc. All rights reserved. 36
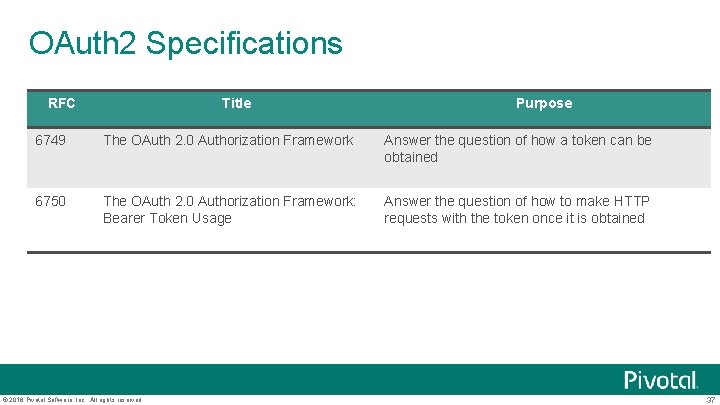
OAuth 2 Specifications RFC Title Purpose 6749 The OAuth 2. 0 Authorization Framework Answer the question of how a token can be obtained 6750 The OAuth 2. 0 Authorization Framework: Bearer Token Usage Answer the question of how to make HTTP requests with the token once it is obtained © 2016 Pivotal Software, Inc. All rights reserved. 37
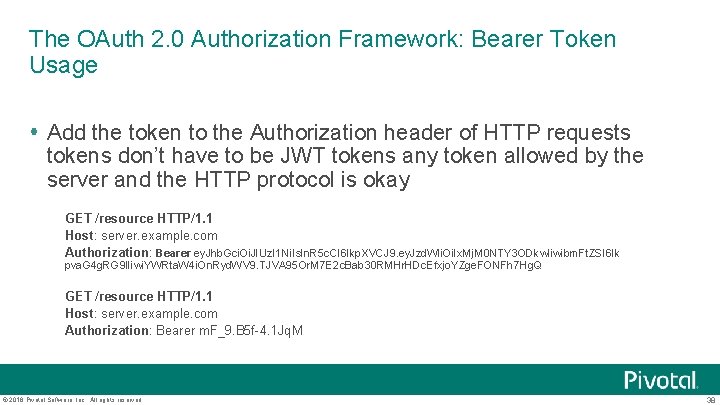
The OAuth 2. 0 Authorization Framework: Bearer Token Usage Add the token to the Authorization header of HTTP requests tokens don’t have to be JWT tokens any token allowed by the server and the HTTP protocol is okay GET /resource HTTP/1. 1 Host: server. example. com Authorization: Bearer ey. Jhb. Gci. Oi. JIUz. I 1 Ni. Is. In. R 5 c. CI 6 Ikp. XVCJ 9. ey. Jzd. WIi. Oi. Ix. Mj. M 0 NTY 3 ODkw. Iiwibm. Ft. ZSI 6 Ik pva. G 4 g. RG 9 l. Iiwi. YWRta. W 4 i. On. Ryd. WV 9. TJVA 95 Or. M 7 E 2 c. Bab 30 RMHr. HDc. Efxjo. YZge. FONFh 7 Hg. Q GET /resource HTTP/1. 1 Host: server. example. com Authorization: Bearer m. F_9. B 5 f-4. 1 Jq. M © 2016 Pivotal Software, Inc. All rights reserved. 38
Four ways to get a token with OAuth 2 Authorization code Implicit Resource owner password credentials Client credentials Why do we need 4 ways to get a token? © 2016 Pivotal Software, Inc. All rights reserved. 39
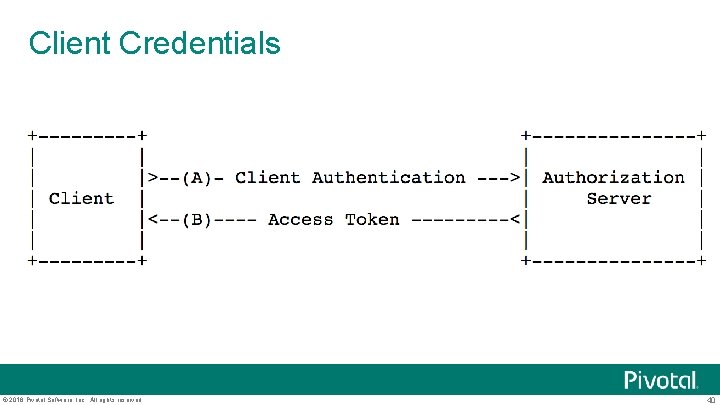
Client Credentials © 2016 Pivotal Software, Inc. All rights reserved. 40
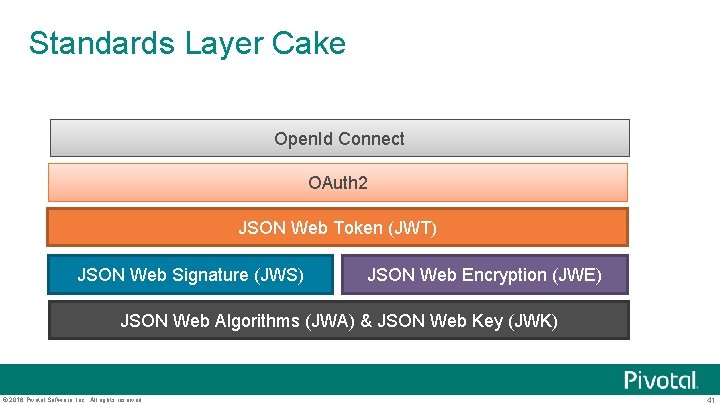
Standards Layer Cake Open. Id Connect OAuth 2 JSON Web Token (JWT) JSON Web Signature (JWS) JSON Web Encryption (JWE) JSON Web Algorithms (JWA) & JSON Web Key (JWK) © 2016 Pivotal Software, Inc. All rights reserved. 41
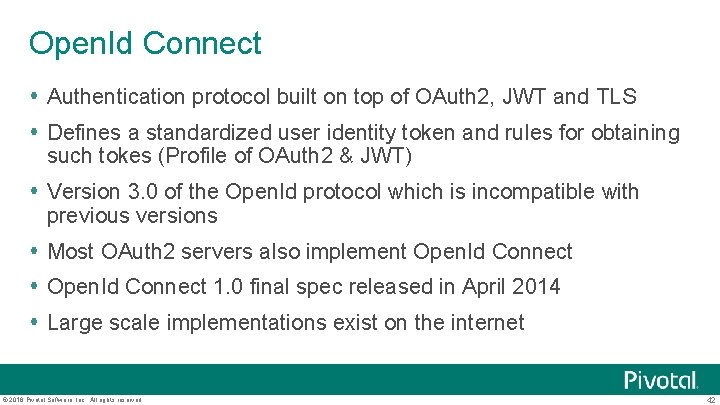
Open. Id Connect Authentication protocol built on top of OAuth 2, JWT and TLS Defines a standardized user identity token and rules for obtaining such tokes (Profile of OAuth 2 & JWT) Version 3. 0 of the Open. Id protocol which is incompatible with previous versions Most OAuth 2 servers also implement Open. Id Connect 1. 0 final spec released in April 2014 Large scale implementations exist on the internet © 2016 Pivotal Software, Inc. All rights reserved. 42
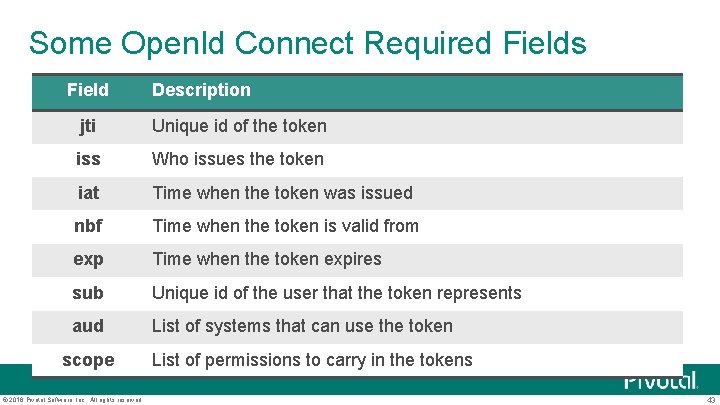
Some Open. Id Connect Required Fields Field Description jti Unique id of the token iss Who issues the token iat Time when the token was issued nbf Time when the token is valid from exp Time when the token expires sub Unique id of the user that the token represents aud List of systems that can use the token scope © 2016 Pivotal Software, Inc. All rights reserved. List of permissions to carry in the tokens 43
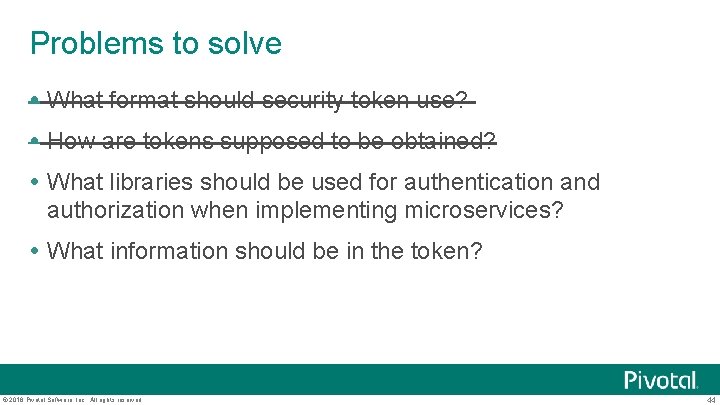
Problems to solve What format should security token use? How are tokens supposed to be obtained? What libraries should be used for authentication and authorization when implementing microservices? What information should be in the token? © 2016 Pivotal Software, Inc. All rights reserved. 44
Freddy BBQ © 2016 Pivotal Software, Inc. All rights reserved. 45
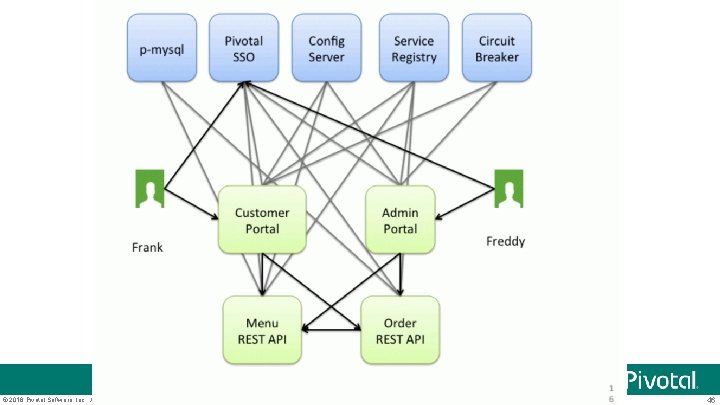
© 2016 Pivotal Software, Inc. All rights reserved. 46
Problems to solve What format should security token use? How are tokens supposed to be obtained? What libraries should be used for authentication and authorization when implementing microservices? What information should be in the token? © 2016 Pivotal Software, Inc. All rights reserved. 47
Microservice Security Patterns © 2016 Pivotal Software, Inc. All rights reserved. 48
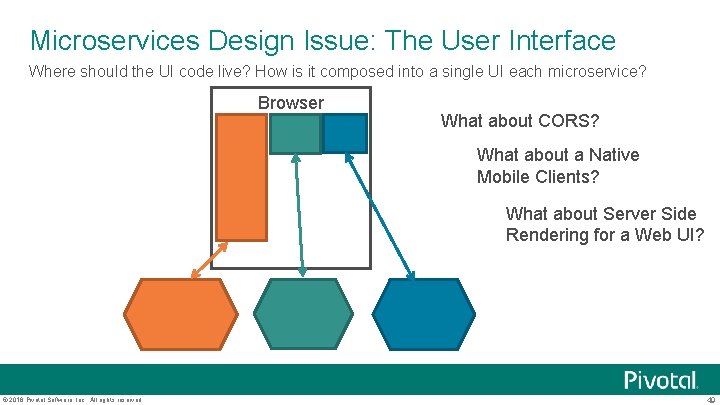
Microservices Design Issue: The User Interface Where should the UI code live? How is it composed into a single UI each microservice? Browser What about CORS? What about a Native Mobile Clients? What about Server Side Rendering for a Web UI? © 2016 Pivotal Software, Inc. All rights reserved. 49
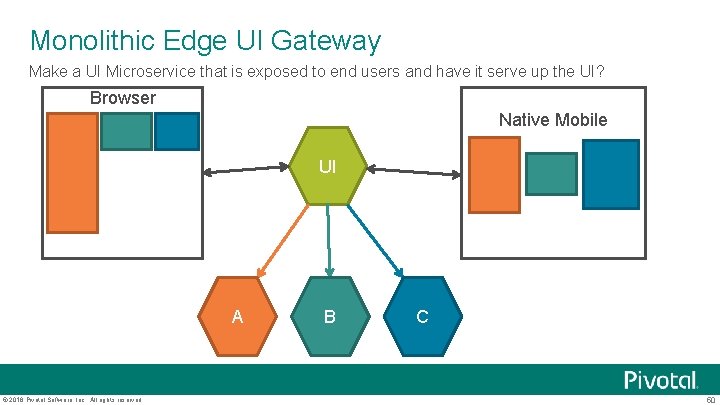
Monolithic Edge UI Gateway Make a UI Microservice that is exposed to end users and have it serve up the UI? Browser Native Mobile UI A © 2016 Pivotal Software, Inc. All rights reserved. B C 50
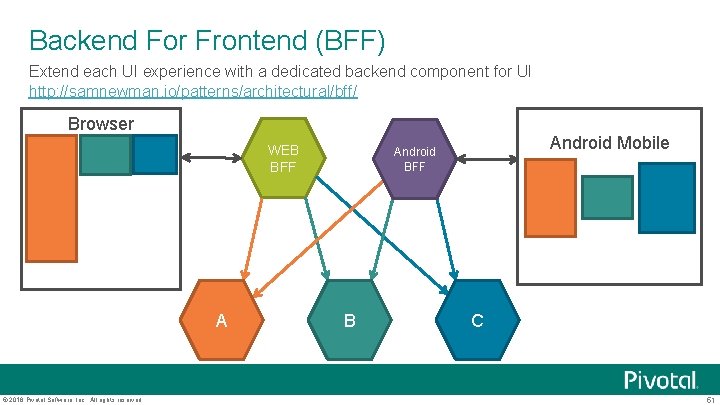
Backend For Frontend (BFF) Extend each UI experience with a dedicated backend component for UI http: //samnewman. io/patterns/architectural/bff/ Browser WEB BFF A © 2016 Pivotal Software, Inc. All rights reserved. Android Mobile Android BFF B C 51
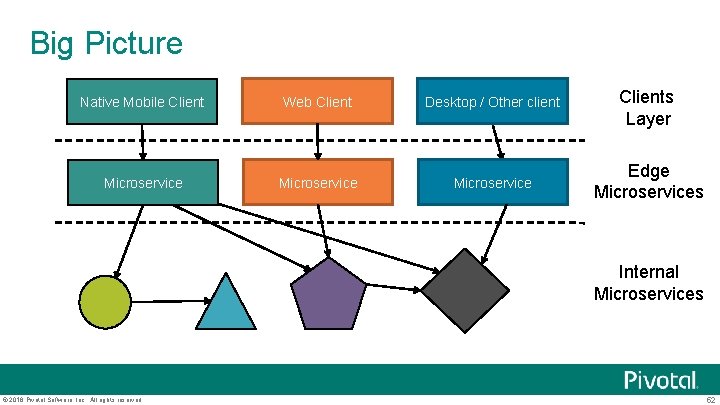
Big Picture Native Mobile Client Web Client Desktop / Other client Clients Layer Microservice Edge Microservices Internal Microservices © 2016 Pivotal Software, Inc. All rights reserved. 52
How to protect access to a microservice? Microservice A © 2016 Pivotal Software, Inc. All rights reserved. Microservice B 53
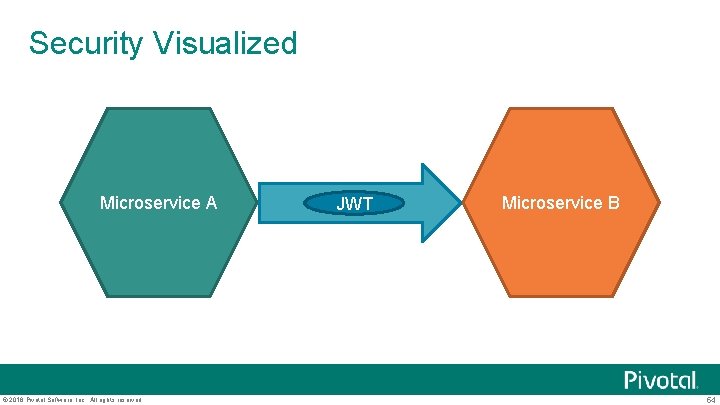
Security Visualized Microservice A © 2016 Pivotal Software, Inc. All rights reserved. JWT Microservice B 54
Microservice Security Programming Model A microservice gets a request that includes a JWT token Microservices checks that the JWT token is valid Token contains the scopes that the user is authorized to do Microservice uses info in the token to make an access control decision Keep the model simple it needs to scale! No exceptions! Easy to implement with spring based frameworks © 2016 Pivotal Software, Inc. All rights reserved. 55
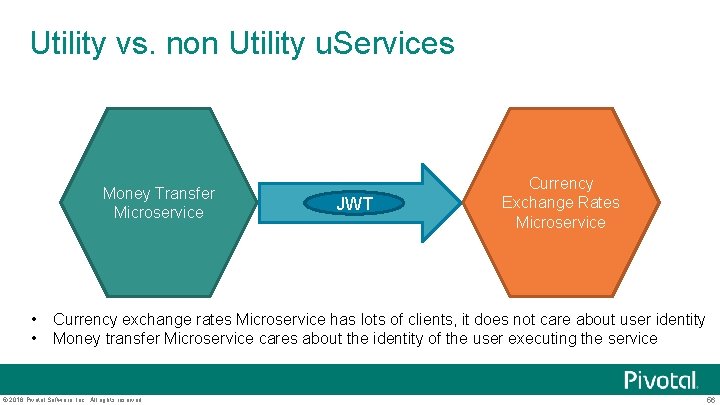
Utility vs. non Utility u. Services Money Transfer Microservice • • JWT Currency Exchange Rates Microservice Currency exchange rates Microservice has lots of clients, it does not care about user identity Money transfer Microservice cares about the identity of the user executing the service © 2016 Pivotal Software, Inc. All rights reserved. 56
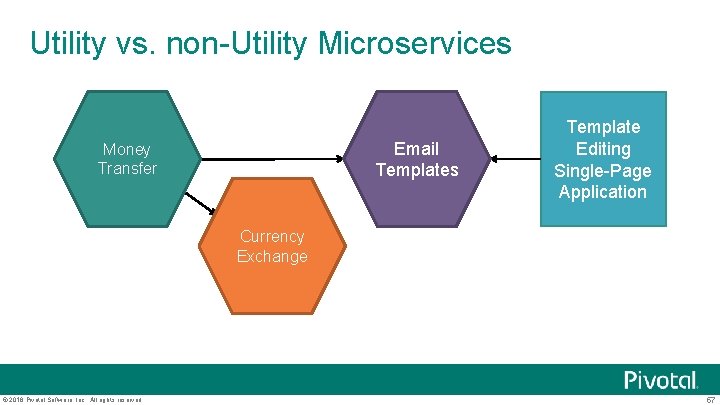
Utility vs. non-Utility Microservices Email Templates Money Transfer Template Editing Single-Page Application Currency Exchange © 2016 Pivotal Software, Inc. All rights reserved. 57
Money Transfer makes utility calls Money Transfer calls Currency Exchange service § Provide client credentials to the OAuth 2 server and get an access token with the scope to lookup exchange rates § Make call with the access token that is returned § OAuth 2 client credentials flow Money Transfer calls Email Templates service § Provide client credentials to the OAuth 2 server and get an access token with the scope to merge email templates § Make a call with the access token that is returned § OAuth 2 client credentials flow © 2016 Pivotal Software, Inc. All rights reserved. 58
Employee edits an email template Employee is using the editor in the Email Templates microservice to create a new email template for “we have transferred your money” Template Editing Single-Page Application obtains an Open. ID token from the OAuth 2 Server using the authorization code flow requesting the scope for template. edit Sends requests to Email Templates microservice using obtained token © 2016 Pivotal Software, Inc. All rights reserved. 59
Email Template Microservice Point of View From the point of view of the Email Templates microservice it can not tell if it is being invoked as a utility microservice or not It just gets a JWT token which can have one of two scopes § template. edit § template. execute Makes decisions based on the scopes in the JWT token © 2016 Pivotal Software, Inc. All rights reserved. 60
Scopes are Microservice Specific BFF UI microservice define its own scopes for the operations it supports Clients of BFF get JWT Open. Id tokens and send them with requests BFF makes utility calls to backing microservices BFF exchanges Open. ID token for microservice-specific tokens © 2016 Pivotal Software, Inc. All rights reserved. 61
Problems to solve What format should security token use? How are tokens supposed to be obtained? What libraries should be used for authentication and authorization when implementing microservices? What information should be in the token? © 2016 Pivotal Software, Inc. All rights reserved. 62

- Slides: 63