Building Secure Distributed Systems DCS Days 26032009 The
Building Secure Distributed Systems DCS Days - 26/03/2009 The CIF model : Component Information Flow Lilia Sfaxi
Context and Contribution 2 Context Building secure distributed systems Needed expertise in systems and security Needed expertise in cryptography Difficulty of dynamic reconfiguration without breaking the security properties of the system Necessity of high level tools Programming abstractions Automatic code generation Verification of the generated code
Context and Contribution 3 Contribution High-level model : CIF (Component Information Flow) System architecture description : component-based model Security annotations Transformation tools : Verification of the security properties System code generation Models and languages Component-based model : Fractal Security-typed programming language : JIF Architecture Description Language : ADL (XML-based)
Outline 4 CIF Specification System representation System security : Inter and Intra component CIF Transformation CIF ADL Generation Code Generation Case study : The battleship game Conclusion and Future Work
Outline 5 CIF Specification System representation System security : Inter and Intra component CIF Transformation CIF ADL Generation Code Generation Case study : The battleship game Conclusion and Future Work
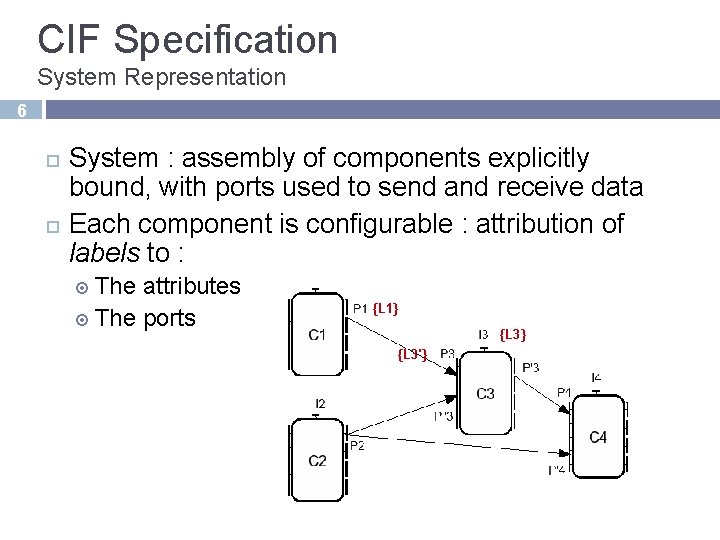
CIF Specification System Representation 6 System : assembly of components explicitly bound, with ports used to send and receive data Each component is configurable : attribution of labels to : The attributes The ports {L 1} {L 3'}
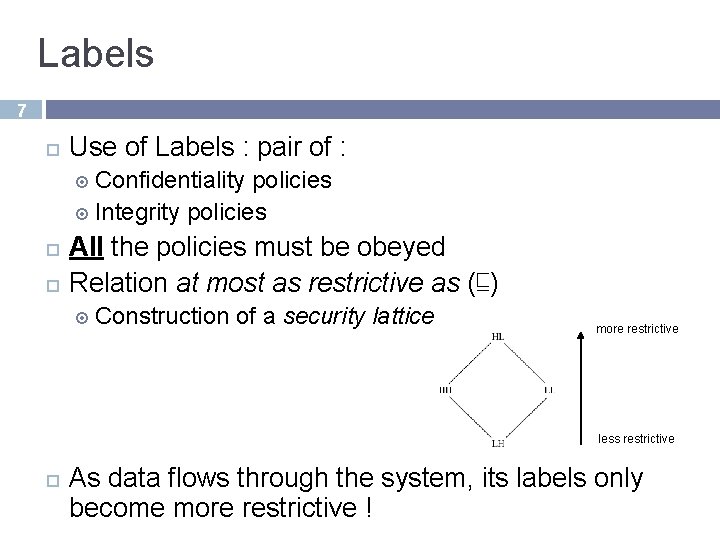
Labels 7 Use of Labels : pair of : Confidentiality policies Integrity policies All the policies must be obeyed Relation at most as restrictive as (⊑) Construction of a security lattice more restrictive less restrictive As data flows through the system, its labels only become more restrictive !
CIF Specification System Security 8 In CIF, needed security policies must be guaranteed at two levels Intra-component Inter-component Ports annotation Intra-component Secure component code
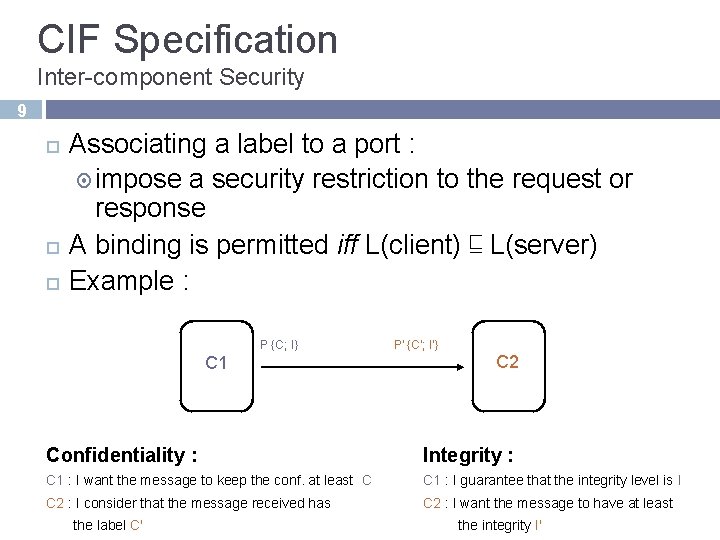
CIF Specification Inter-component Security 9 Associating a label to a port : impose a security restriction to the request or response A binding is permitted iff L(client) ⊑ L(server) Example : P {C; I} C 1 P' {C'; I'} C 2 Confidentiality : Integrity : C 1 : I want the message to keep the conf. at least C C 1 : I guarantee that the integrity level is I C 2 : I consider that the message received has C 2 : I want the message to have at least the label C' the integrity I'
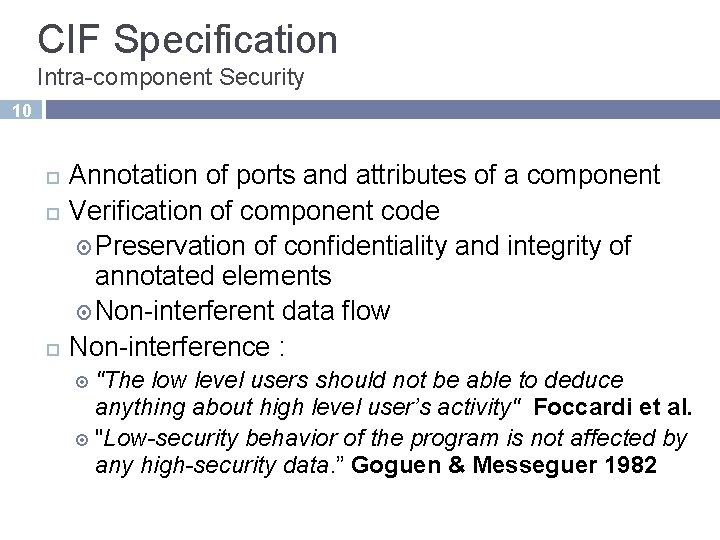
CIF Specification Intra-component Security 10 Annotation of ports and attributes of a component Verification of component code Preservation of confidentiality and integrity of annotated elements Non-interferent data flow Non-interference : "The low level users should not be able to deduce anything about high level user’s activity" Foccardi et al. "Low-security behavior of the program is not affected by any high-security data. ” Goguen & Messeguer 1982
Outline 11 CIF Specification System representation System security : Inter and Intra component CIF Transformation CIF ADL Generation Code Generation Case study : The battleship game Conclusion and Future Work
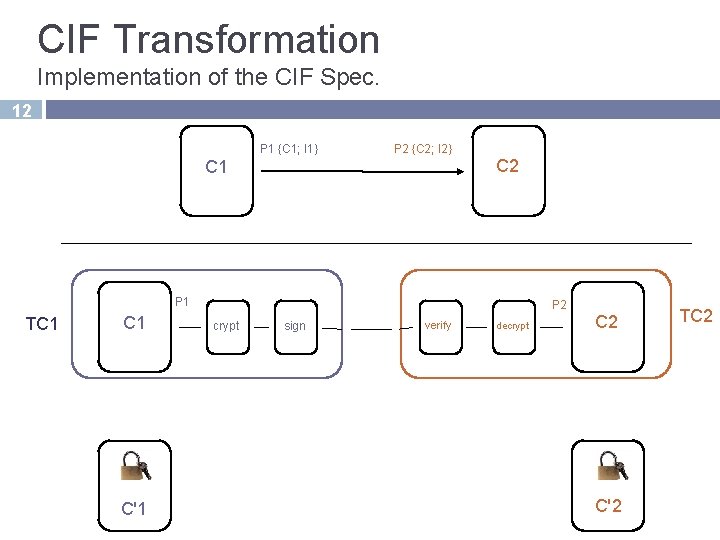
CIF Transformation Implementation of the CIF Spec. 12 P 1 {C 1; I 1} P 2 {C 2; I 2} C 2 C 1 P 1 TC 1 C'1 P 2 crypt sign verify decrypt C 2 C'2 TC 2
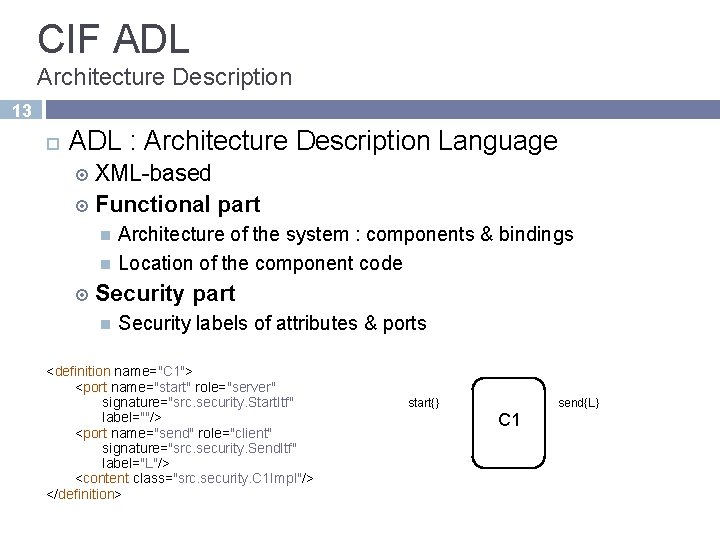
CIF ADL Architecture Description 13 ADL : Architecture Description Language XML-based Functional part Architecture of the system : components & bindings Location of the component code Security part Security labels of attributes & ports <definition name="C 1"> <port name="start" role="server" signature="src. security. Start. Itf" label=""/> <port name="send" role="client" signature="src. security. Send. Itf" label="L"/> <content class="src. security. C 1 Impl"/> </definition> start{} send{L} C 1
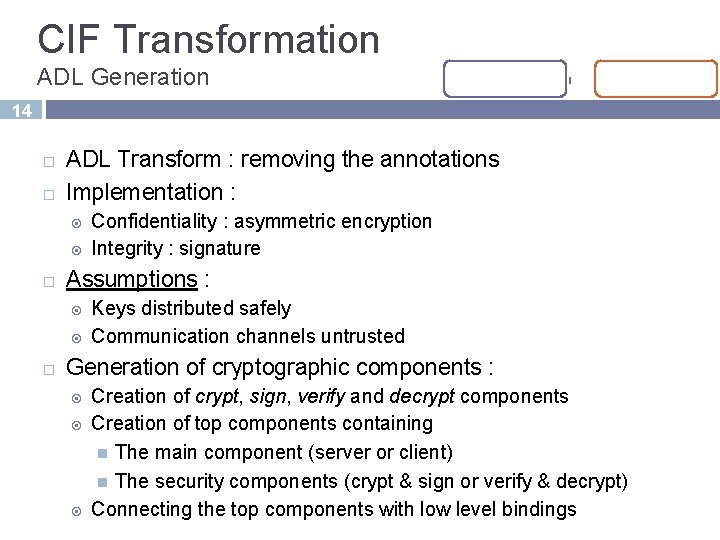
CIF Transformation ADL Generation 14 ADL Transform : removing the annotations Implementation : Assumptions : Confidentiality : asymmetric encryption Integrity : signature Keys distributed safely Communication channels untrusted Generation of cryptographic components : Creation of crypt, sign, verify and decrypt components Creation of top components containing The main component (server or client) The security components (crypt & sign or verify & decrypt) Connecting the top components with low level bindings
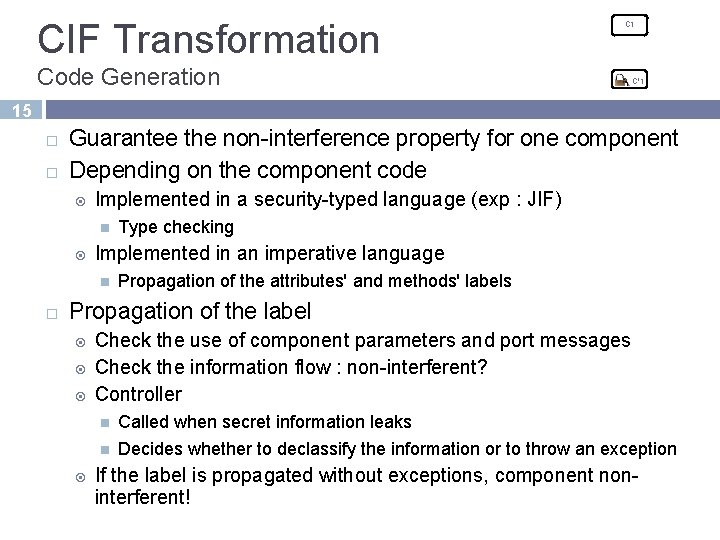
CIF Transformation C 1 Code Generation C'1 15 Guarantee the non-interference property for one component Depending on the component code Implemented in a security-typed language (exp : JIF) Implemented in an imperative language Type checking Propagation of the attributes' and methods' labels Propagation of the label Check the use of component parameters and port messages Check the information flow : non-interferent? Controller Called when secret information leaks Decides whether to declassify the information or to throw an exception If the label is propagated without exceptions, component noninterferent!
Outline 16 CIF Specification System representation System security : Inter and Intra component CIF Transformation CIF ADL Generation Code Generation Case study : The battleship game Conclusion and Future Work
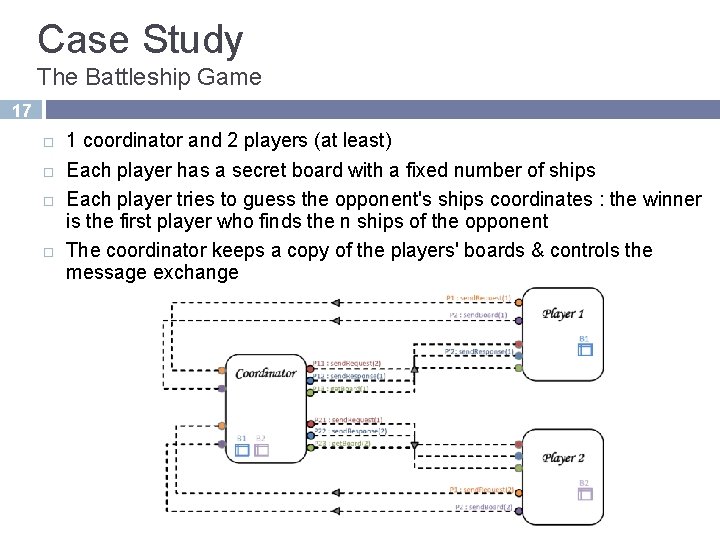
Case Study The Battleship Game 17 1 coordinator and 2 players (at least) Each player has a secret board with a fixed number of ships Each player tries to guess the opponent's ships coordinates : the winner is the first player who finds the n ships of the opponent The coordinator keeps a copy of the players' boards & controls the message exchange
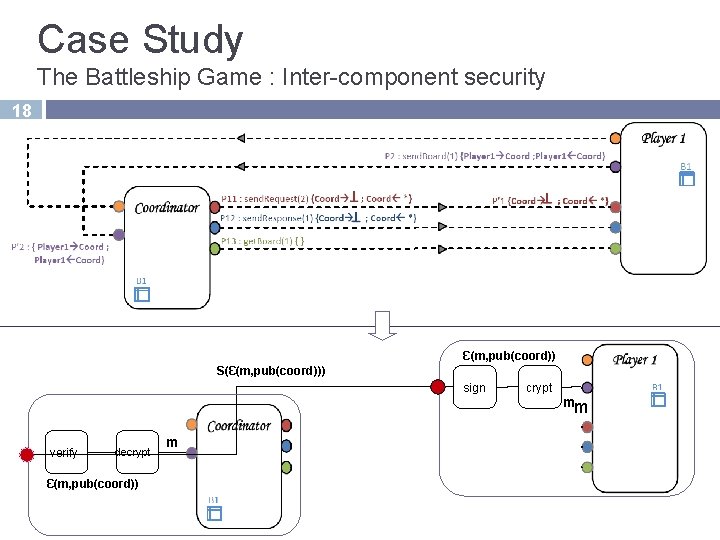
Case Study The Battleship Game : Inter-component security 18 Ɛ(m, pub(coord)) S(Ɛ(m, pub(coord))) sign crypt mm verify decrypt Ɛ(m, pub(coord)) m
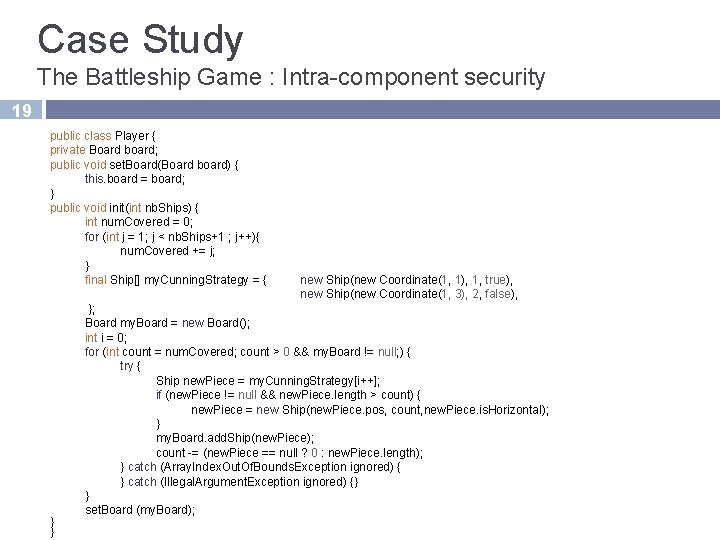
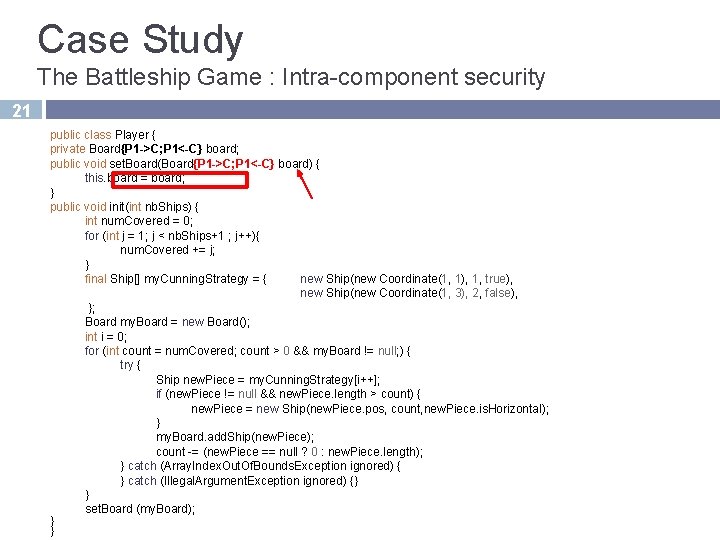
Case Study The Battleship Game : Intra-component security 19 public class Player { private Board board; public void set. Board(Board board) { this. board = board; } public void init(int nb. Ships) { int num. Covered = 0; for (int j = 1; j < nb. Ships+1 ; j++){ num. Covered += j; } final Ship[] my. Cunning. Strategy = { } } new Ship(new Coordinate(1, 1), 1, true), new Ship(new Coordinate(1, 3), 2, false), }; Board my. Board = new Board(); int i = 0; for (int count = num. Covered; count > 0 && my. Board != null; ) { try { Ship new. Piece = my. Cunning. Strategy[i++]; if (new. Piece != null && new. Piece. length > count) { new. Piece = new Ship(new. Piece. pos, count, new. Piece. is. Horizontal); } my. Board. add. Ship(new. Piece); count -= (new. Piece == null ? 0 : new. Piece. length); } catch (Array. Index. Out. Of. Bounds. Exception ignored) { } catch (Illegal. Argument. Exception ignored) {} } set. Board (my. Board);
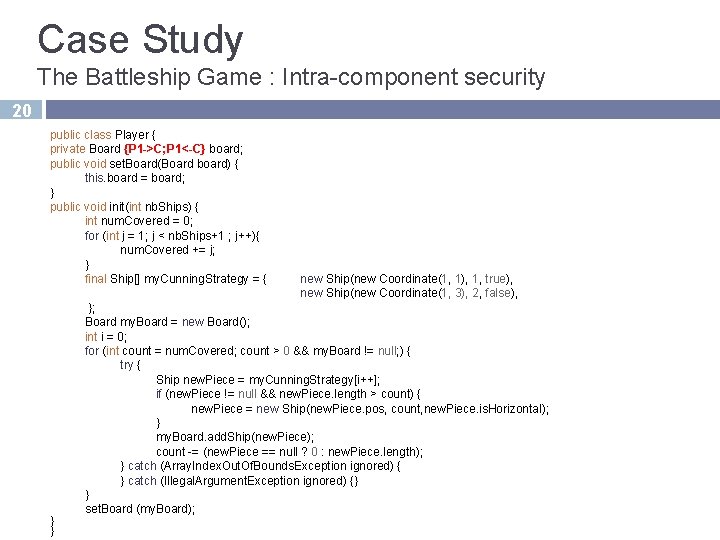
Case Study The Battleship Game : Intra-component security 20 public class Player { private Board {P 1 ->C; P 1<-C} board; public void set. Board(Board board) { this. board = board; } public void init(int nb. Ships) { int num. Covered = 0; for (int j = 1; j < nb. Ships+1 ; j++){ num. Covered += j; } final Ship[] my. Cunning. Strategy = { } } new Ship(new Coordinate(1, 1), 1, true), new Ship(new Coordinate(1, 3), 2, false), }; Board my. Board = new Board(); int i = 0; for (int count = num. Covered; count > 0 && my. Board != null; ) { try { Ship new. Piece = my. Cunning. Strategy[i++]; if (new. Piece != null && new. Piece. length > count) { new. Piece = new Ship(new. Piece. pos, count, new. Piece. is. Horizontal); } my. Board. add. Ship(new. Piece); count -= (new. Piece == null ? 0 : new. Piece. length); } catch (Array. Index. Out. Of. Bounds. Exception ignored) { } catch (Illegal. Argument. Exception ignored) {} } set. Board (my. Board);
Case Study The Battleship Game : Intra-component security 21 public class Player { private Board{P 1 ->C; P 1<-C} board; public void set. Board(Board{P 1 ->C; P 1<-C} board) { this. board = board; } public void init(int nb. Ships) { int num. Covered = 0; for (int j = 1; j < nb. Ships+1 ; j++){ num. Covered += j; } final Ship[] my. Cunning. Strategy = { new Ship(new Coordinate(1, 1), 1, true), new Ship(new Coordinate(1, 3), 2, false), }; Board my. Board = new Board(); int i = 0; for (int count = num. Covered; count > 0 && my. Board != null; ) { try { Ship new. Piece = my. Cunning. Strategy[i++]; if (new. Piece != null && new. Piece. length > count) { new. Piece = new Ship(new. Piece. pos, count, new. Piece. is. Horizontal); } my. Board. add. Ship(new. Piece); count -= (new. Piece == null ? 0 : new. Piece. length); } catch (Array. Index. Out. Of. Bounds. Exception ignored) { } catch (Illegal. Argument. Exception ignored) {} } set. Board (my. Board); } }
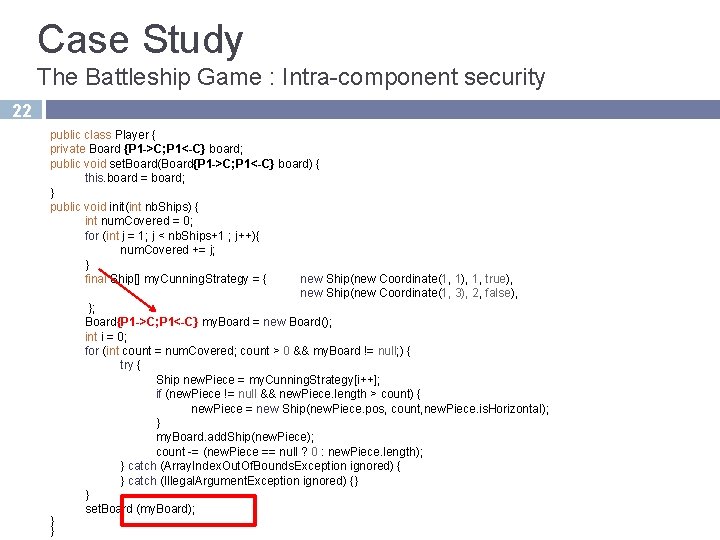
Case Study The Battleship Game : Intra-component security 22 public class Player { private Board {P 1 ->C; P 1<-C} board; public void set. Board(Board{P 1 ->C; P 1<-C} board) { this. board = board; } public void init(int nb. Ships) { int num. Covered = 0; for (int j = 1; j < nb. Ships+1 ; j++){ num. Covered += j; } final Ship[] my. Cunning. Strategy = { new Ship(new Coordinate(1, 1), 1, true), new Ship(new Coordinate(1, 3), 2, false), }; Board{P 1 ->C; P 1<-C} my. Board = new Board(); int i = 0; for (int count = num. Covered; count > 0 && my. Board != null; ) { try { Ship new. Piece = my. Cunning. Strategy[i++]; if (new. Piece != null && new. Piece. length > count) { new. Piece = new Ship(new. Piece. pos, count, new. Piece. is. Horizontal); } my. Board. add. Ship(new. Piece); count -= (new. Piece == null ? 0 : new. Piece. length); } catch (Array. Index. Out. Of. Bounds. Exception ignored) { } catch (Illegal. Argument. Exception ignored) {} } set. Board (my. Board); } }
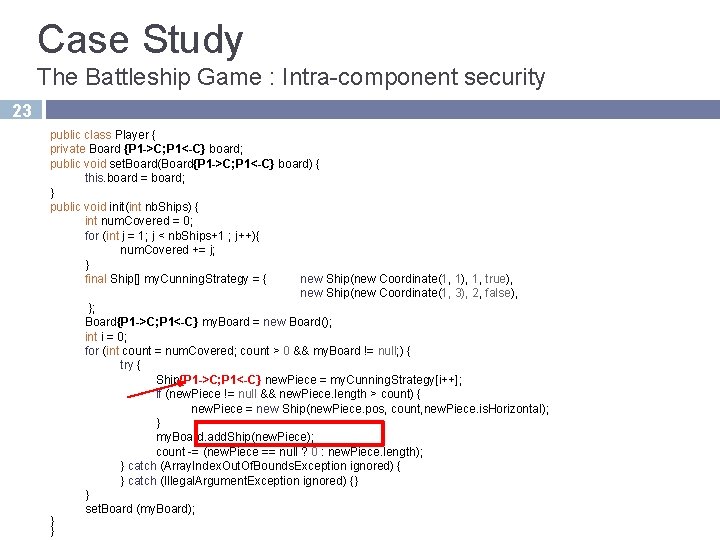
Case Study The Battleship Game : Intra-component security 23 public class Player { private Board {P 1 ->C; P 1<-C} board; public void set. Board(Board{P 1 ->C; P 1<-C} board) { this. board = board; } public void init(int nb. Ships) { int num. Covered = 0; for (int j = 1; j < nb. Ships+1 ; j++){ num. Covered += j; } final Ship[] my. Cunning. Strategy = { new Ship(new Coordinate(1, 1), 1, true), new Ship(new Coordinate(1, 3), 2, false), }; Board{P 1 ->C; P 1<-C} my. Board = new Board(); int i = 0; for (int count = num. Covered; count > 0 && my. Board != null; ) { try { Ship{P 1 ->C; P 1<-C} new. Piece = my. Cunning. Strategy[i++]; if (new. Piece != null && new. Piece. length > count) { new. Piece = new Ship(new. Piece. pos, count, new. Piece. is. Horizontal); } my. Board. add. Ship(new. Piece); count -= (new. Piece == null ? 0 : new. Piece. length); } catch (Array. Index. Out. Of. Bounds. Exception ignored) { } catch (Illegal. Argument. Exception ignored) {} } set. Board (my. Board); } }
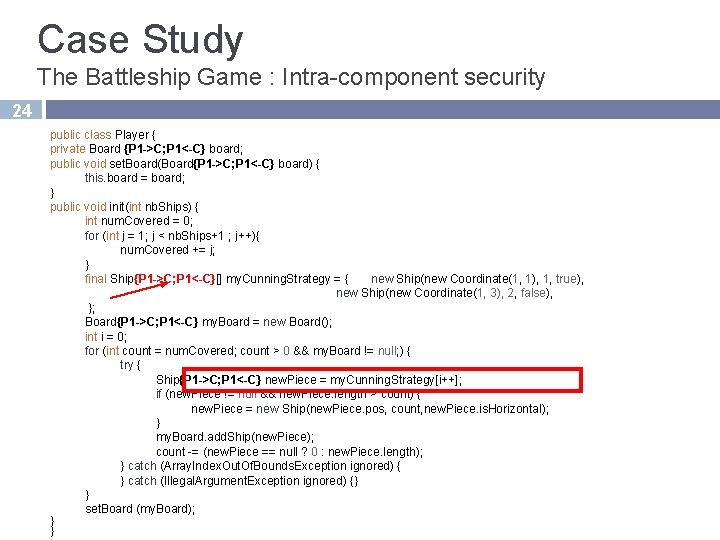
Case Study The Battleship Game : Intra-component security 24 public class Player { private Board {P 1 ->C; P 1<-C} board; public void set. Board(Board{P 1 ->C; P 1<-C} board) { this. board = board; } public void init(int nb. Ships) { int num. Covered = 0; for (int j = 1; j < nb. Ships+1 ; j++){ num. Covered += j; } final Ship{P 1 ->C; P 1<-C}[] my. Cunning. Strategy = { new Ship(new Coordinate(1, 1), 1, true), new Ship(new Coordinate(1, 3), 2, false), }; Board{P 1 ->C; P 1<-C} my. Board = new Board(); int i = 0; for (int count = num. Covered; count > 0 && my. Board != null; ) { try { Ship{P 1 ->C; P 1<-C} new. Piece = my. Cunning. Strategy[i++]; if (new. Piece != null && new. Piece. length > count) { new. Piece = new Ship(new. Piece. pos, count, new. Piece. is. Horizontal); } my. Board. add. Ship(new. Piece); count -= (new. Piece == null ? 0 : new. Piece. length); } catch (Array. Index. Out. Of. Bounds. Exception ignored) { } catch (Illegal. Argument. Exception ignored) {} } set. Board (my. Board); } }
Outline 25 CIF Specification System representation System security : Inter and Intra component CIF Transformation CIF ADL Generation Code Generation Case study : The battleship game Conclusion and Future Work
Conclusion 26 CIF Component-based model Builds distributed systems secure by construction User specifies security requirements At a high level of abstraction Association of labels to attributes and ports of the component Tools to automate security implementation Inside a component : Generation of JIF code Between components Insertion of cryptographic components
Future Work 27 Key distribution Secure deployment Safe reconfiguration Privacy
Thank you for your attention DCS Days - 26/03/2009 Lilia Sfaxi
- Slides: 28