Building Management System An Overview to BMS What

Building Management System An Overview to BMS
What is BMS ? 2 File Number
What is BMS? - A micro-processor based system which centralizes and simplifies… w controlling w monitoring w operation and… w management …of heating, air-conditioning, ventilation & other building services to achieve… » safe and comfortable working environment » energy saving & efficient operation » at reduced time & cost 3 File Number

BMS provides… Comfortable & safe environment for your building by controlling…. . w Air Handling Units w Fan Coil Units w Chillers w Pumps w Boilers w VFD’s and many more…. . 4 File Number
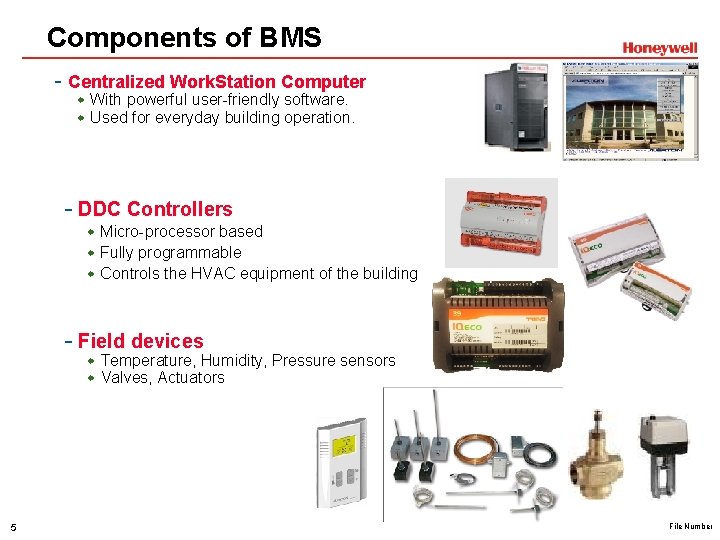
Components of BMS - Centralized Work. Station Computer w With powerful user-friendly software. w Used for everyday building operation. - DDC Controllers w Micro-processor based w Fully programmable w Controls the HVAC equipment of the building - Field devices w Temperature, Humidity, Pressure sensors w Valves, Actuators 5 File Number
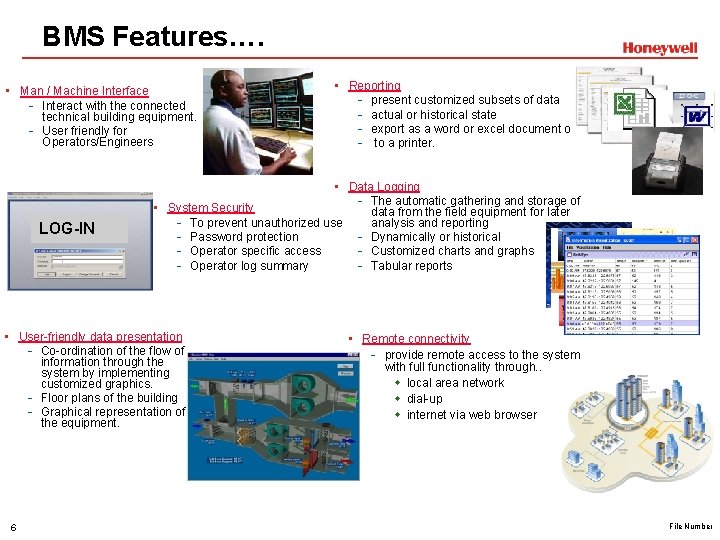
BMS Features…. • Man / Machine Interface - Interact with the connected technical building equipment. - User friendly for Operators/Engineers LOG-IN • Data Logging - The automatic gathering and storage of • System Security data from the field equipment for later analysis and reporting - To prevent unauthorized use - Dynamically or historical - Password protection - Customized charts and graphs - Operator specific access - Tabular reports - Operator log summary • User-friendly data presentation - Co-ordination of the flow of information through the system by implementing customized graphics. - Floor plans of the building - Graphical representation of the equipment. 6 • Reporting - present customized subsets of data - actual or historical state - export as a word or excel document or. . - to a printer. • Remote connectivity - provide remote access to the system with full functionality through. . w local area network w dial-up w internet via web browser File Number
BMS Features…. • Alarm Management - the presentation in the sequence of importance and time of. . w potentially dangerous situations w process value deviations - guiding the operator to take appropriate action through. . w audible and visual indications w Email, SMS - alarm summary w Time, date, priority and description • Time Scheduling - time-based start/stop of the equipment - saves energy cost and efficient operation - effective for lighting, occupancy control - can be as daily, weekly, for holidays or events • Event recording - automatic logging of… w operator activities and commands w processes related to connected devices w workstations and printers. 7 File Number

Why we need this? 8 File Number
Why we need this? • Improved indoor environment quality - Comfortable living and working environment – domestic or commercial - Better temperature and humidity control - Good air quality • Faster response to. . - occupant needs - end-user complaints - trouble conditions • Maintenance Savings. - efficient control gives less wear and strain of mechanical equipment. - provides longer life - runtime monitoring alerts timely maintenance of equipment - avoids expensive failures • Energy Savings - eliminates unnecessary system operation. - accurate energy usage information - helps you to take steps to reduce energy consumption like… w Optimum-Start w Night-Purging w Time-Scheduling 9 File Number
Why we need this? • Consolidater Facility Control… - One point centralized operation - Simpler operation - Reduces time and resources • Reduced operator training - on-screen instructions - user-friendly graphic displays - simpler operation programmed for routine and repetitive operation • Maintenance Savings. - efficient control gives less wear and strain of mechanical equipment. - provides longer life - runtime monitoring alerts timely maintenance of equipment - avoids expensive failures 10 File Number
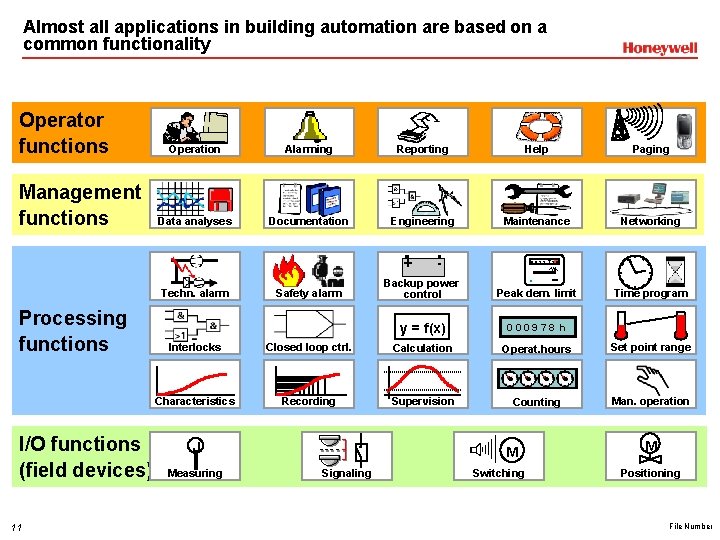
Almost all applications in building automation are based on a common functionality Operator functions Management functions Operation Alarming Reporting Help Paging Data analyses Documentation Engineering Maintenance Networking + Techn. alarm Processing functions I/O functions (field devices) 11 Safety alarm - 0029738 k. Wh Backup power control Peak dem. limit y = f(x) 000978 h s Time program Interlocks Closed loop ctrl. Calculation Operat. hours Set point range Characteristics Recording Supervision Counting Man. operation J Measuring M Signaling Switching M Positioning File Number
Honeywell/Trend Introduction – Corporate-ACS-E&ES 12 File Number
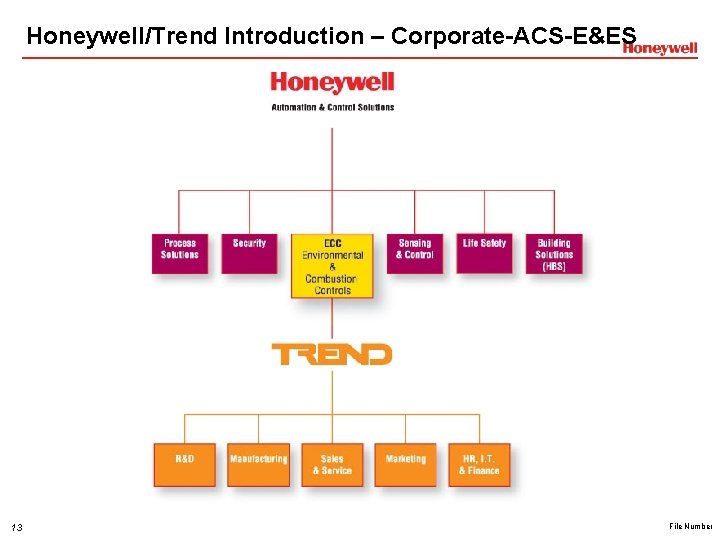
Honeywell/Trend Introduction – Corporate-ACS-E&ES 13 File Number
HVAC Design Criteria 14 File Number
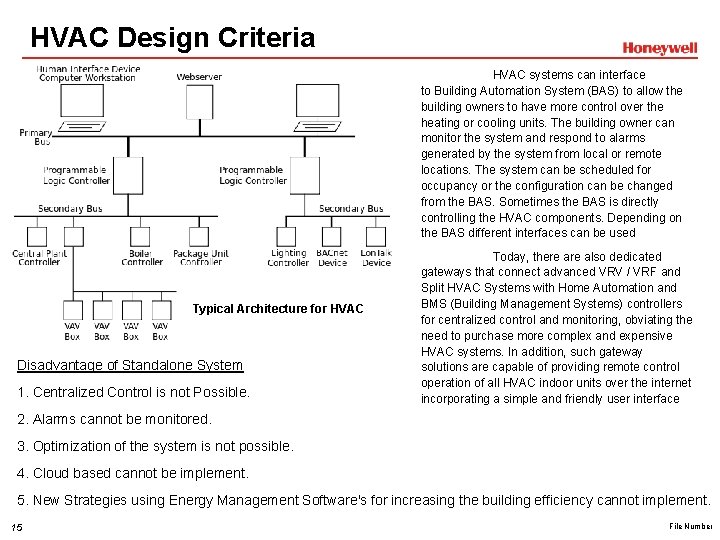
HVAC Design Criteria HVAC systems can interface to Building Automation System (BAS) to allow the building owners to have more control over the heating or cooling units. The building owner can monitor the system and respond to alarms generated by the system from local or remote locations. The system can be scheduled for occupancy or the configuration can be changed from the BAS. Sometimes the BAS is directly controlling the HVAC components. Depending on the BAS different interfaces can be used Typical Architecture for HVAC Disadvantage of Standalone System 1. Centralized Control is not Possible. Today, there also dedicated gateways that connect advanced VRV / VRF and Split HVAC Systems with Home Automation and BMS (Building Management Systems) controllers for centralized control and monitoring, obviating the need to purchase more complex and expensive HVAC systems. In addition, such gateway solutions are capable of providing remote control operation of all HVAC indoor units over the internet incorporating a simple and friendly user interface 2. Alarms cannot be monitored. 3. Optimization of the system is not possible. 4. Cloud based cannot be implement. 5. New Strategies using Energy Management Software's for increasing the building efficiency cannot implement. 15 File Number
Smart Building 16 File Number
What is Smart building? Smart building technologies can improve buildings’ energy efficiency and indoor environmental quality. Smart Building: A building that provides a productive and cost-effective environment through optimization of its four basic components - structure, systems, services and management - and the interrelationships between them. " 17 File Number
BMS Software 18 File Number
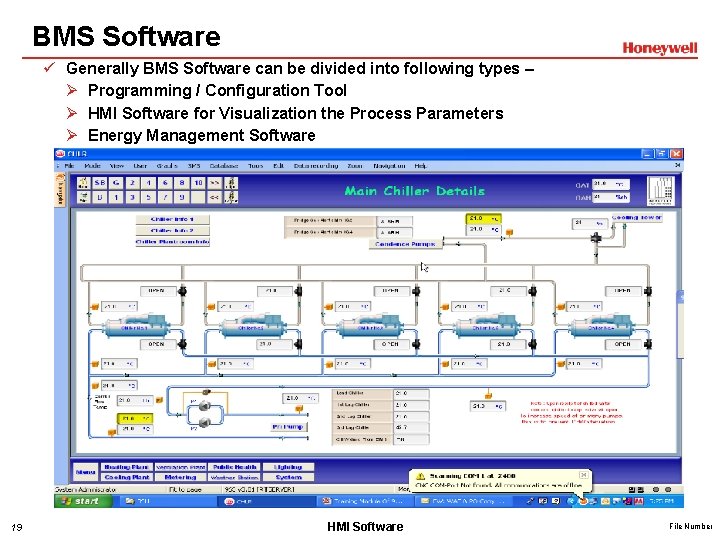
BMS Software ü Generally BMS Software can be divided into following types – Ø Programming / Configuration Tool Ø HMI Software for Visualization the Process Parameters Ø Energy Management Software 19 HMI Software File Number
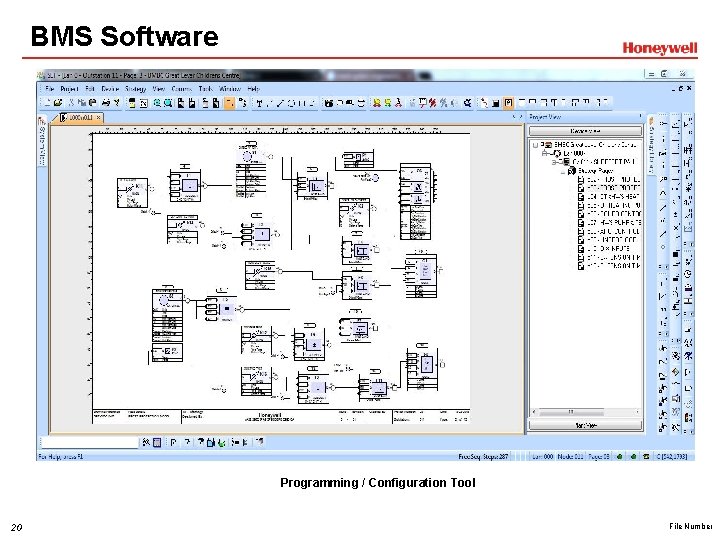
BMS Software Programming / Configuration Tool 20 File Number
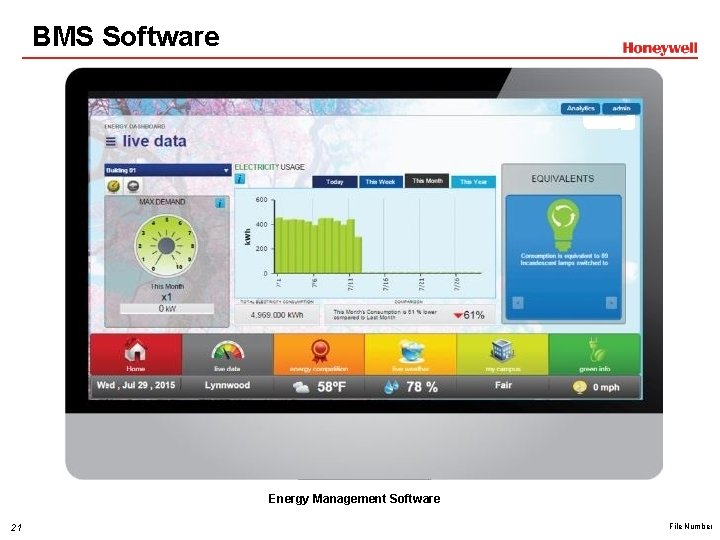
BMS Software Energy Management Software 21 File Number
Plant Controllers 22 File Number
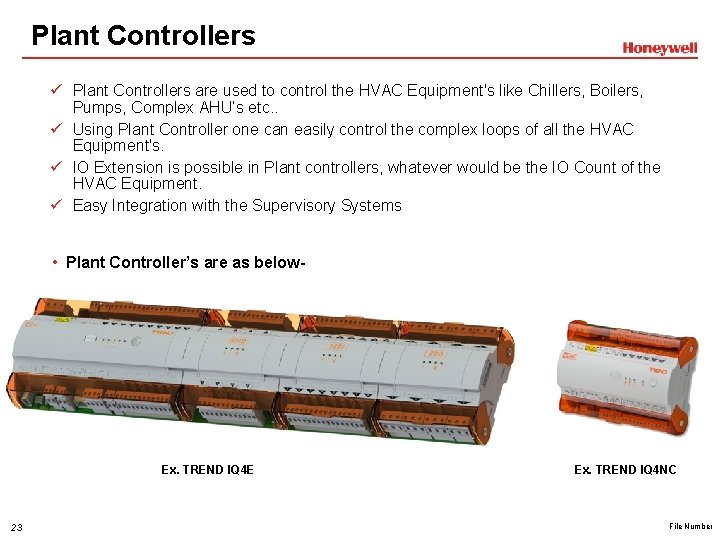
Plant Controllers ü Plant Controllers are used to control the HVAC Equipment's like Chillers, Boilers, Pumps, Complex AHU’s etc. . ü Using Plant Controller one can easily control the complex loops of all the HVAC Equipment's. ü IO Extension is possible in Plant controllers, whatever would be the IO Count of the HVAC Equipment. ü Easy Integration with the Supervisory Systems • Plant Controller’s are as below- Ex. TREND IQ 4 E 23 Ex. TREND IQ 4 NC File Number
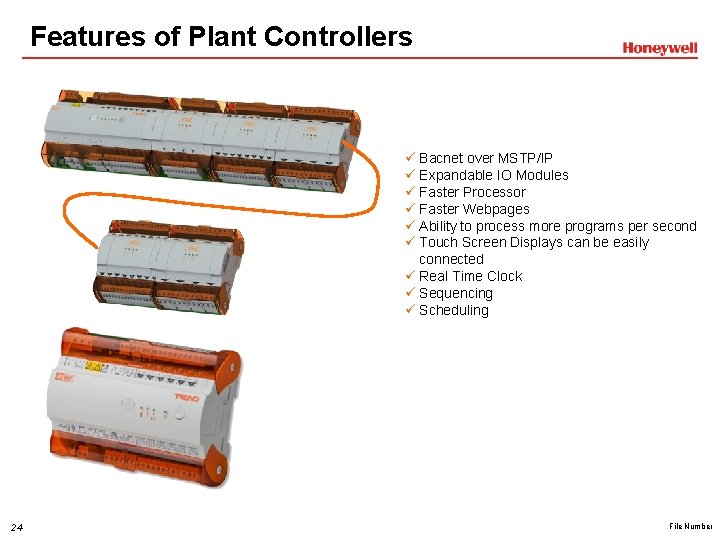
Features of Plant Controllers ü Bacnet over MSTP/IP ü Expandable IO Modules ü Faster Processor ü Faster Webpages ü Ability to process more programs per second ü Touch Screen Displays can be easily connected ü Real Time Clock ü Sequencing ü Scheduling 24 File Number
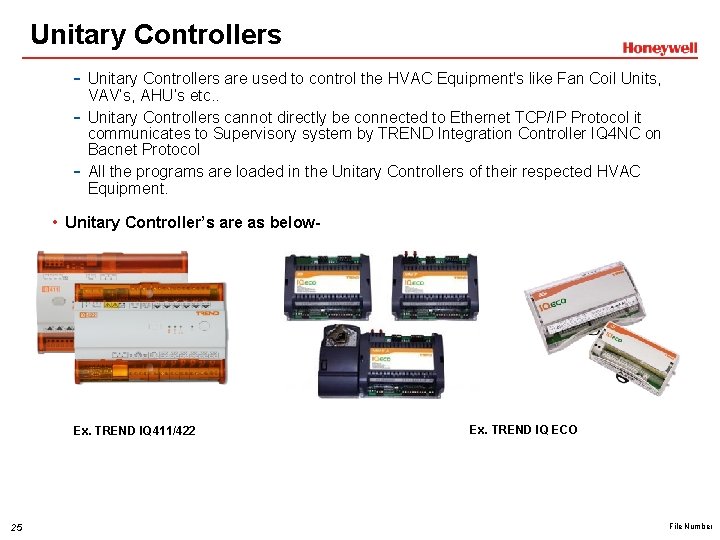
Unitary Controllers - Unitary Controllers are used to control the HVAC Equipment's like Fan Coil Units, - VAV’s, AHU’s etc. . Unitary Controllers cannot directly be connected to Ethernet TCP/IP Protocol it communicates to Supervisory system by TREND Integration Controller IQ 4 NC on Bacnet Protocol All the programs are loaded in the Unitary Controllers of their respected HVAC Equipment. • Unitary Controller’s are as below- Ex. TREND IQ 411/422 25 Ex. TREND IQ ECO File Number
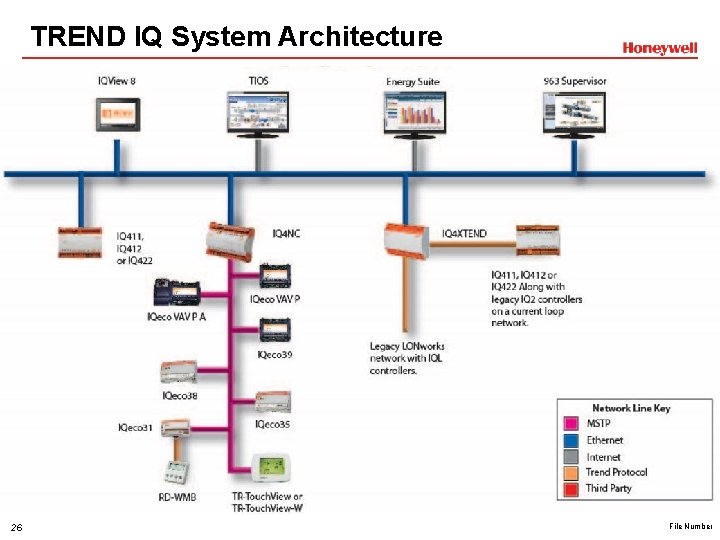
TREND IQ System Architecture 26 File Number
Network Display 27 File Number
Network Display Features ü Color graphics pages (schematic) ü Viewing of inputs, outputs, directories, alarms, and plots ü Adjustment of knobs, switches, and time zones. ü Graphing of logged data ü Configurable users to ensure system security ü Communicates with all controllers on network (not autodialed networks) ü DHCP enabled ü Ethernet, current loop LAN, or RS 232 network connection ü Panel, surface, or embedded mounting ü Color touch screen LCD display 28 File Number
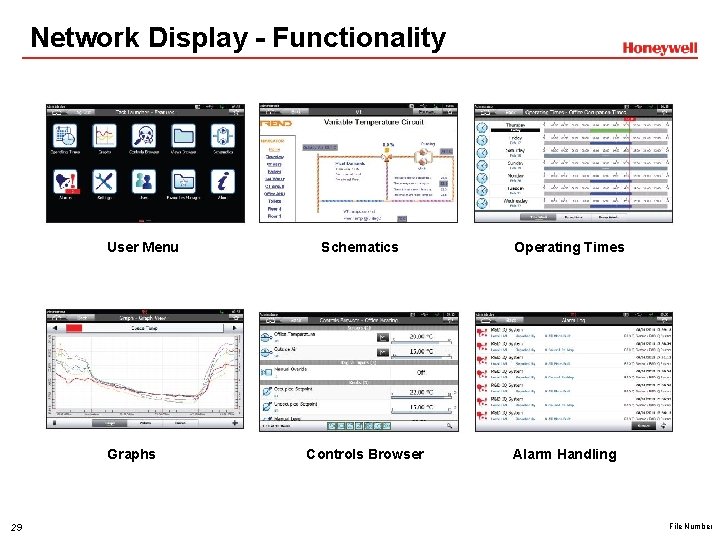
Network Display - Functionality User Menu Graphs 29 Schematics Controls Browser Operating Times Alarm Handling File Number

Cyber Security 30 File Number
What is Cyber Security? • It is referred as Information Technology Security • Focusing on protecting: • Computers • Networks • Programs and Data • From unintended or unauthorized access, change or destruction. 31 File Number
Why is Cyber Security Important? • Who uses the Internet? • Big Businesses • Financial Institutions • Hospitals • Governments • Military • What do they do and what do they do with the information? • Collect, process and store confidential information on computers • Transmit that data across networks to other computers • What do they/we need to do? Protect sensitive business and personal information. 32 File Number
How On-line attacks damage consumer trust? • Customers are making more transactions online and trust in a brand is paramount • What happens if your information ends up in the wrong hands? • Would you shop on-line with them again? • The challenge is being able to identify the risks and take action • Currently, brand owners only know about approximately 10% of the threats. 33 File Number
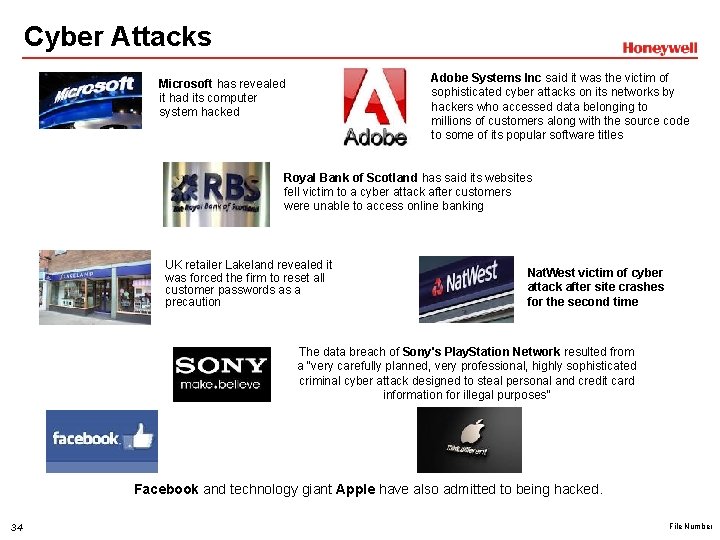
Cyber Attacks Adobe Systems Inc said it was the victim of sophisticated cyber attacks on its networks by hackers who accessed data belonging to millions of customers along with the source code to some of its popular software titles Microsoft has revealed it had its computer system hacked Royal Bank of Scotland has said its websites fell victim to a cyber attack after customers were unable to access online banking UK retailer Lakeland revealed it was forced the firm to reset all customer passwords as a precaution Nat. West victim of cyber attack after site crashes for the second time The data breach of Sony's Play. Station Network resulted from a "very carefully planned, very professional, highly sophisticated criminal cyber attack designed to steal personal and credit card information for illegal purposes” Facebook and technology giant Apple have also admitted to being hacked. 34 File Number
So what’s the Risk. . ? What’s the worst that could happen? Switch the lights off in a supermarket Shut down the HVAC plant in a server room Or interact with the system in some ingenious manner Perspective is important! 35 File Number
IT Networking basic - VLAN 36 File Number
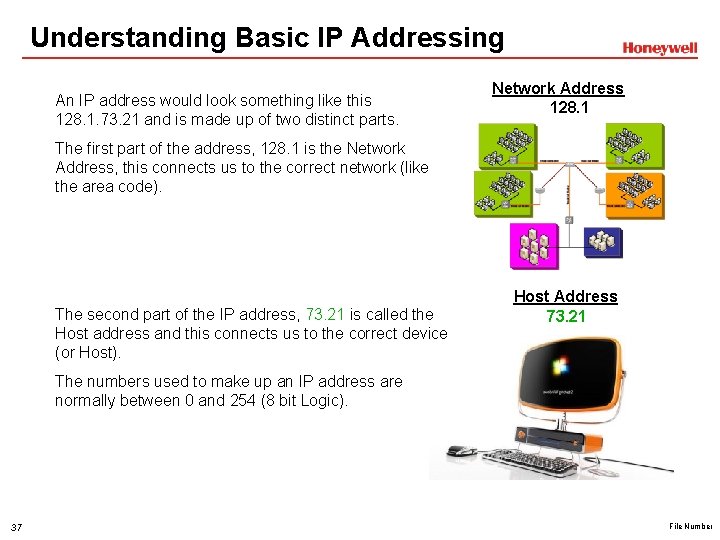
Understanding Basic IP Addressing An IP address would look something like this 128. 1. 73. 21 and is made up of two distinct parts. Network Address 128. 1 The first part of the address, 128. 1 is the Network Address, this connects us to the correct network (like the area code). The second part of the IP address, 73. 21 is called the Host address and this connects us to the correct device (or Host). Host Address 73. 21 The numbers used to make up an IP address are normally between 0 and 254 (8 bit Logic). 37 File Number
Understanding Basic IP Addressing - Classes Many different sizes of network are needed in the IT world, from small home networks that maybe have 3 or 4 devices sharing an internet connection to huge multinational companies, with thousands of PCs in just one building. Network Address 128. 1 To account for varying size of networks, the IP address can be formatted in a number of different ways. In the previous example, we split the IP address in the middle. Network Address 128. 1 Host Address 73. 21 This is referred to as a Class B Network, we can have 16, 384 networks each with 65, 534 addresses. 38 File Number
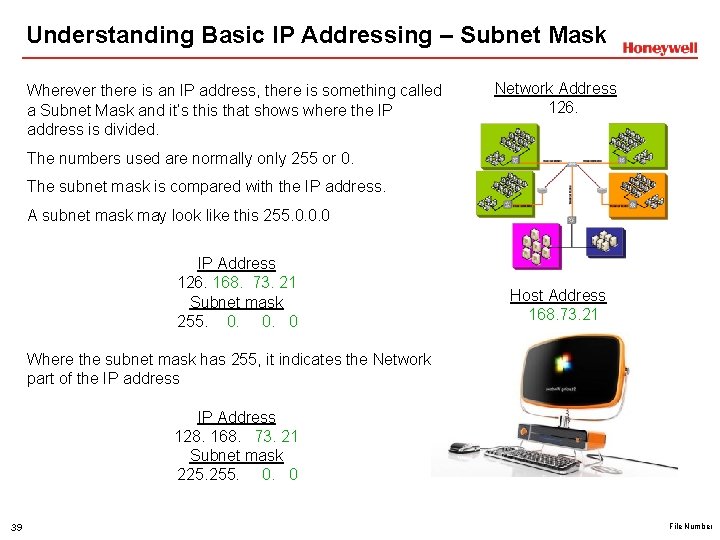
Understanding Basic IP Addressing – Subnet Mask Wherever there is an IP address, there is something called a Subnet Mask and it’s this that shows where the IP address is divided. Network Address 126. The numbers used are normally only 255 or 0. The subnet mask is compared with the IP address. A subnet mask may look like this 255. 0. 0. 0 IP Address 126. 168. 73. 21 Subnet mask 255. 0. 0. 0 Host Address 168. 73. 21 Where the subnet mask has 255, it indicates the Network part of the IP address IP Address 128. 168. 73. 21 Subnet mask 225. 255. 0. 0 39 File Number
ADSL Connectivity and Remote Connectivity 40 File Number
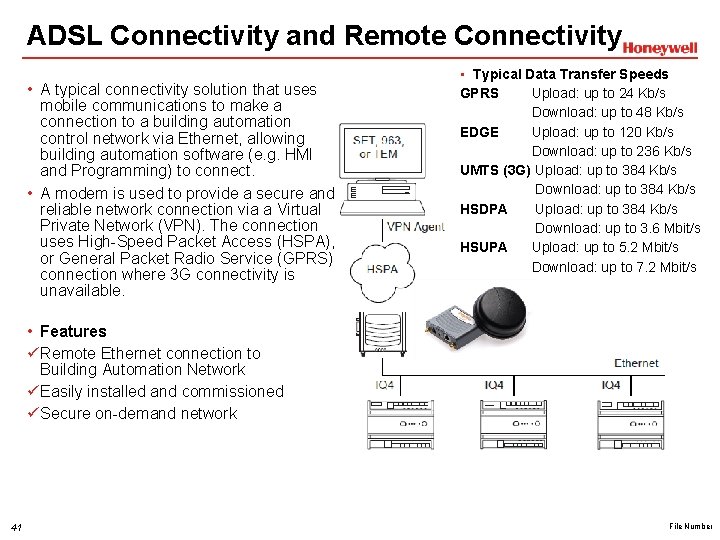
ADSL Connectivity and Remote Connectivity • A typical connectivity solution that uses mobile communications to make a connection to a building automation control network via Ethernet, allowing building automation software (e. g. HMI and Programming) to connect. • A modem is used to provide a secure and reliable network connection via a Virtual Private Network (VPN). The connection uses High-Speed Packet Access (HSPA), or General Packet Radio Service (GPRS) connection where 3 G connectivity is unavailable. • Typical Data Transfer Speeds GPRS Upload: up to 24 Kb/s Download: up to 48 Kb/s EDGE Upload: up to 120 Kb/s Download: up to 236 Kb/s UMTS (3 G) Upload: up to 384 Kb/s Download: up to 384 Kb/s HSDPA Upload: up to 384 Kb/s Download: up to 3. 6 Mbit/s HSUPA Upload: up to 5. 2 Mbit/s Download: up to 7. 2 Mbit/s • Features ü Remote Ethernet connection to Building Automation Network ü Easily installed and commissioned ü Secure on-demand network 41 File Number
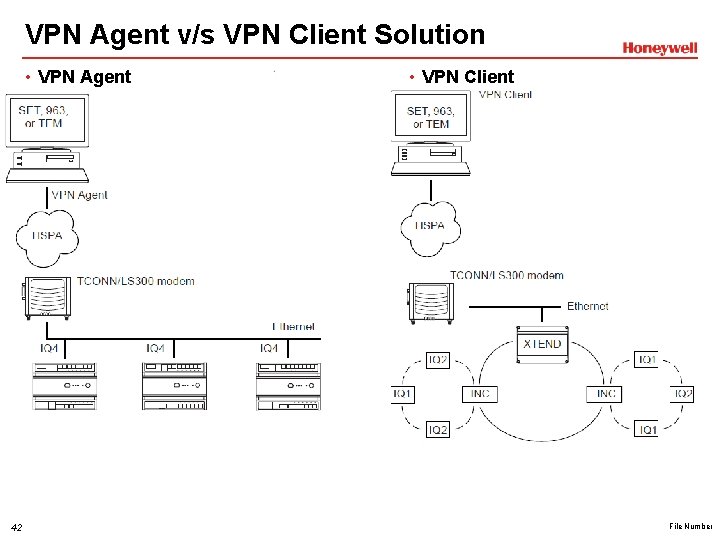
VPN Agent v/s VPN Client Solution • VPN Agent 42 • VPN Client File Number
VPN Agent & VPN Client VPN Agent The VPN Agent requires Windows 8, Windows 8. 1, Windows 2000 Service Pack 3 or later, Windows XP, Windows 7, Windows Vista, Windows Server 2003, Windows Server 2008 or Windows Small Business Server. Both 32 -bit and 64 -bit versions are supported. The VPN Agent runs as a background Windows task and has minimal space and memory requirements. VPN Client • The VPN Client requires Windows 8, Windows 8. 1, Windows 2000 Service Pack 3 or later, Windows XP or Windows 2003 Server (including SBS 2003). • If the VPN Client is behind a NAT device, the following updates are required: üWindows 2000 requires NAT-T (Nat-Traversal) update (see Microsoft KB 818043). The NAT-T update for Windows 2000 can be downloaded from Microsoft at http: //v 4. windowsupdate. microsoft. com/catalog (Windows Update Catalog). Install the Update Catalog. Select ‘Find updates for Microsoft Windows operating systems’ and the select the ‘Advanced Search’ option. Enter 818043 as then search term which will provide a link to the NAT-T update. üWindows XP requires Service Pack 2 üNo updates are required for Windows 2003 Servers 43 File Number
Field Devices 44 File Number
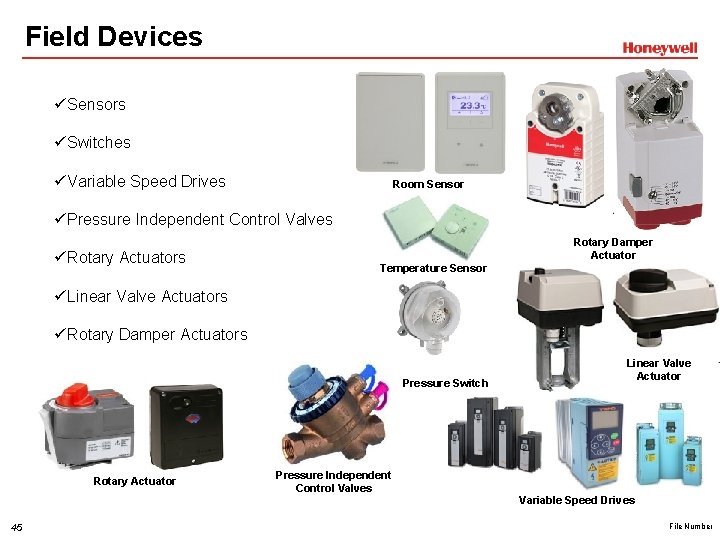
Field Devices ü Sensors ü Switches ü Variable Speed Drives Room Sensor ü Pressure Independent Control Valves ü Rotary Actuators Temperature Sensor Rotary Damper Actuator ü Linear Valve Actuators ü Rotary Damper Actuators Pressure Switch Rotary Actuator 45 Pressure Independent Control Valves Linear Valve Actuator Variable Speed Drives File Number
Energy Manager 46 File Number
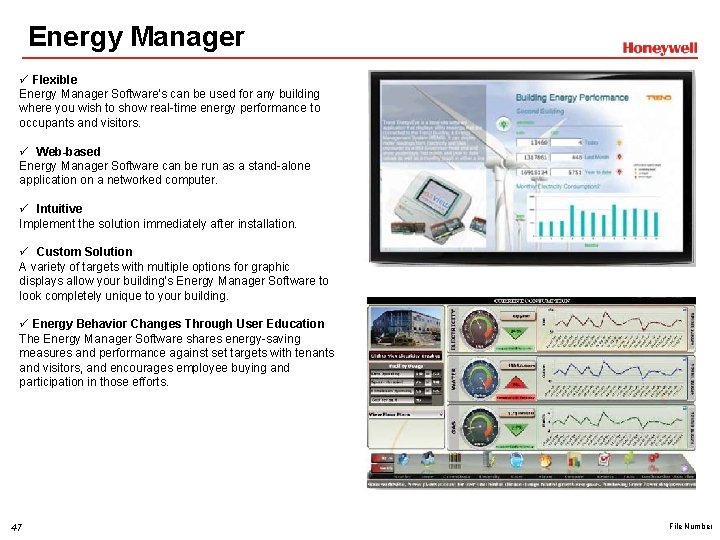
Energy Manager ü Flexible Energy Manager Software's can be used for any building where you wish to show real-time energy performance to occupants and visitors. ü Web-based Energy Manager Software can be run as a stand-alone application on a networked computer. ü Intuitive Implement the solution immediately after installation. ü Custom Solution A variety of targets with multiple options for graphic displays allow your building’s Energy Manager Software to look completely unique to your building. ü Energy Behavior Changes Through User Education The Energy Manager Software shares energy-saving measures and performance against set targets with tenants and visitors, and encourages employee buying and participation in those efforts. 47 File Number

Cloud Based Solutions 48 File Number
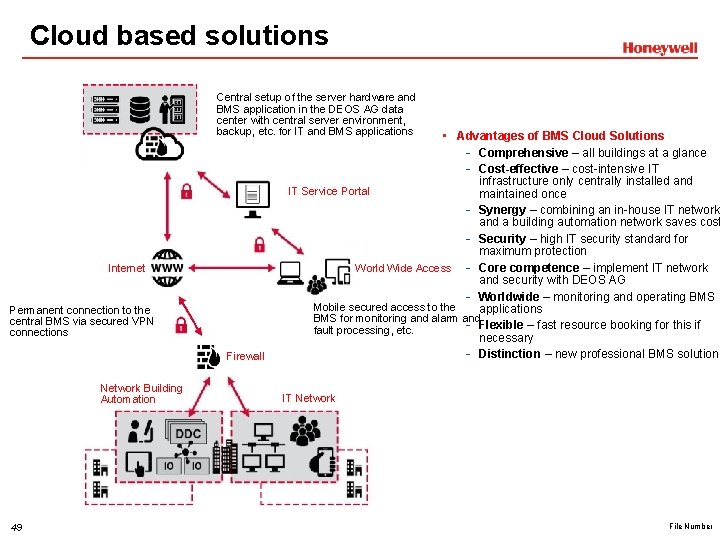
Cloud based solutions Central setup of the server hardware and BMS application in the DEOS AG data center with central server environment, backup, etc. for IT and BMS applications Internet Permanent connection to the central BMS via secured VPN connections Firewall Network Building Automation 49 • Advantages of BMS Cloud Solutions - Comprehensive – all buildings at a glance - Cost-effective – cost-intensive IT infrastructure only centrally installed and IT Service Portal maintained once - Synergy – combining an in-house IT network and a building automation network saves cost - Security – high IT security standard for maximum protection World Wide Access - Core competence – implement IT network and security with DEOS AG - Worldwide – monitoring and operating BMS Mobile secured access to the applications BMS for monitoring and alarm and - Flexible – fast resource booking for this if fault processing, etc. necessary - Distinction – new professional BMS solution IT Network File Number
Thanks!! 50 File Number
- Slides: 50