Building a Campus Dshield Randy Marchany IT Security
Building a Campus Dshield Randy Marchany IT Security Lab VA Tech Blacksburg, VA 24060 marchany@vt. edu http: //security. vt. edu
VT Defense-in-Depth Strategy l l l Layer 1: Blocking Attacks: Network Based Layer 2: Blocking Attacks: Host Based Layer 3: Eliminating Security Vulnerabilities Layer 4: Supporting Authorized Users Layer 5: Tools to minimize business losses
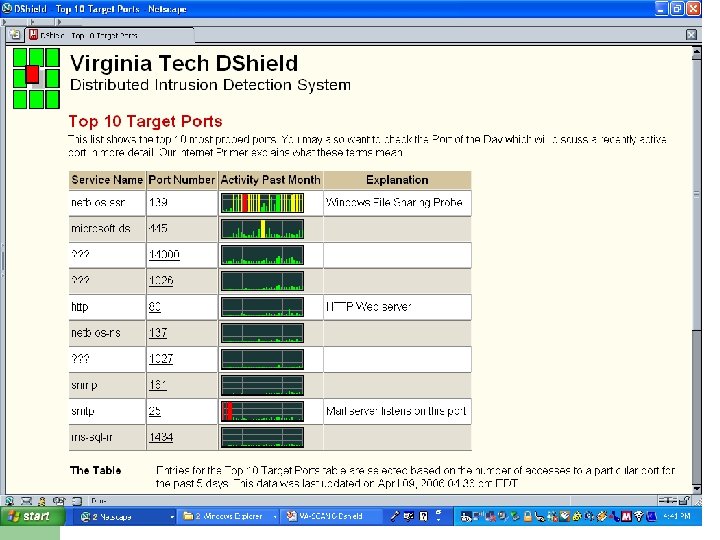
Putting the Pieces Together l l l l RDWEB – locate any device in our network DSHIELD – Collect Firewall logs SNORT – Sensors monitoring for patterns SAFETYNET – “pull” vulnerability scanner CHECKNET – “push” vulnerability scanner REMEDY – Trouble Ticket system used by Help Desk CENTRAL SYSLOG – collects syslogs
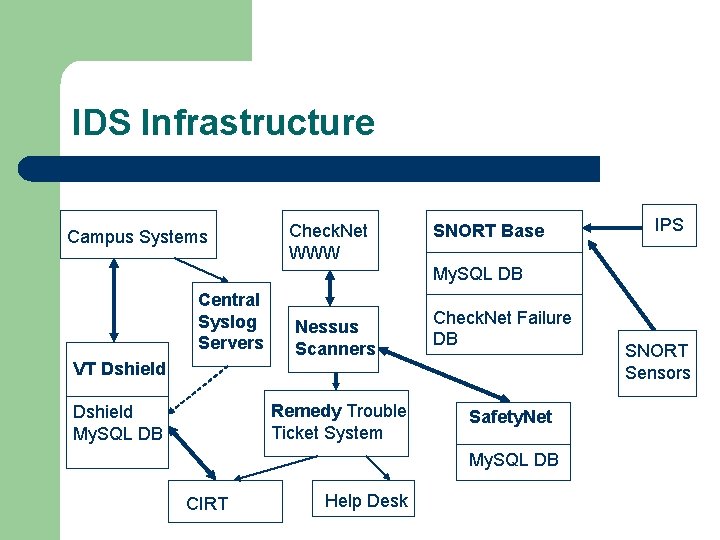
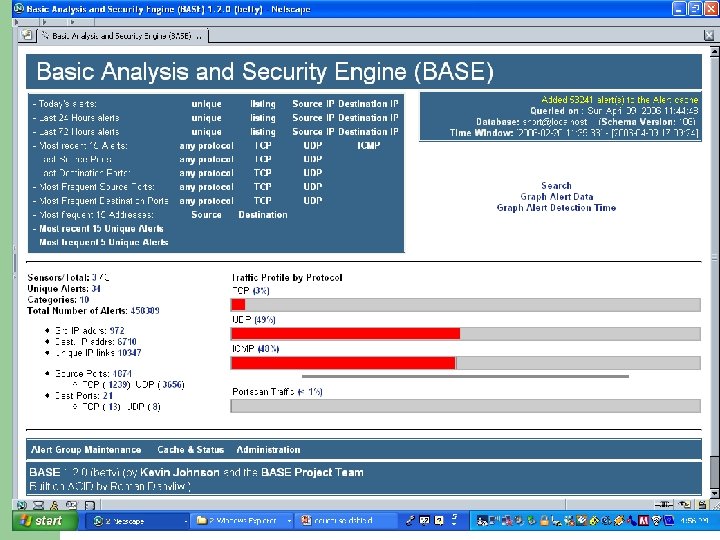
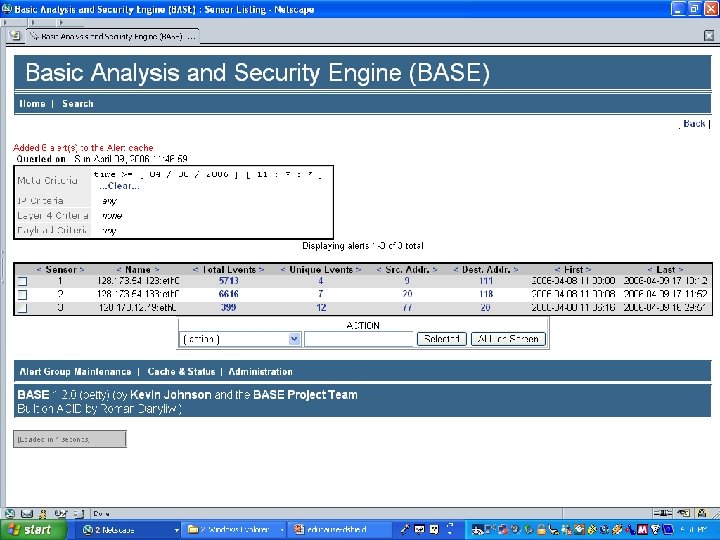
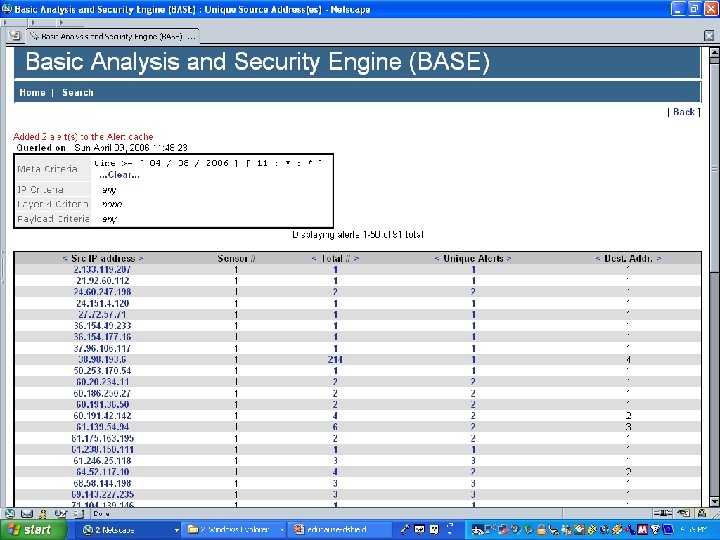
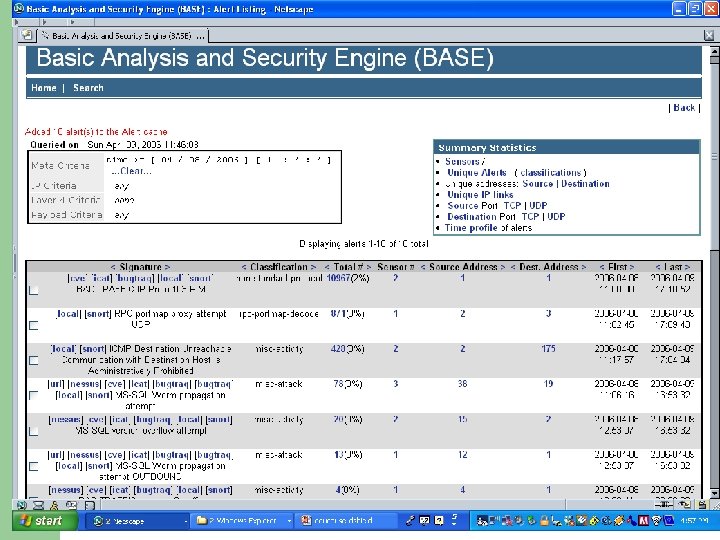
IDS Infrastructure Campus Systems Check. Net WWW SNORT Base IPS My. SQL DB Central Syslog Servers Nessus Scanners Check. Net Failure DB VT Dshield Remedy Trouble Ticket System Dshield My. SQL DB Safety. Net My. SQL DB CIRT Help Desk SNORT Sensors
VA Tech Defense in Depth l Layer 1: Blocking Attacks: Network Based – – – Network Intrusion Prevention Systems Discovery and mitigation Firewalls Secure Web Filtering Secure Email, Anti-Spam
VA Tech Defense in Depth l Layer 2: Blocking Attacks: Host Based – – Personal firewalls Spyware removal Scan & Block/Quarantine Networks Antivirus
VA Tech Defense in Depth l Layer 3: Eliminating Security Vulnerabilities – – – Vulnerability management & remediation Patch management Configuration management Security configuration compliance Application security testing
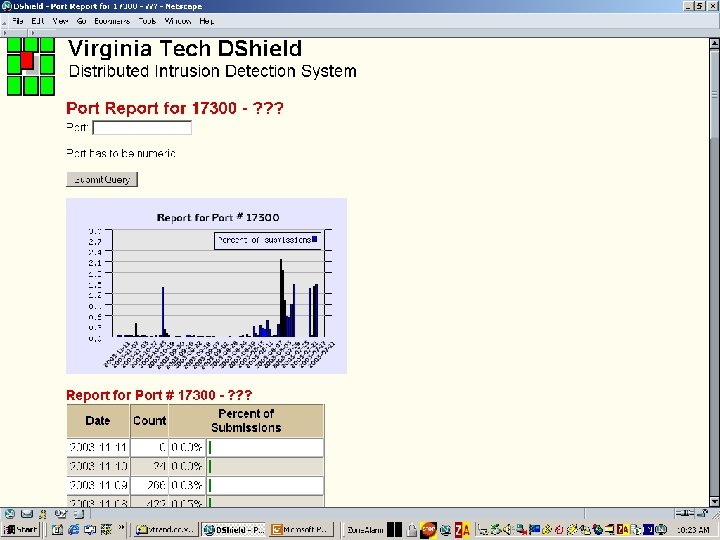
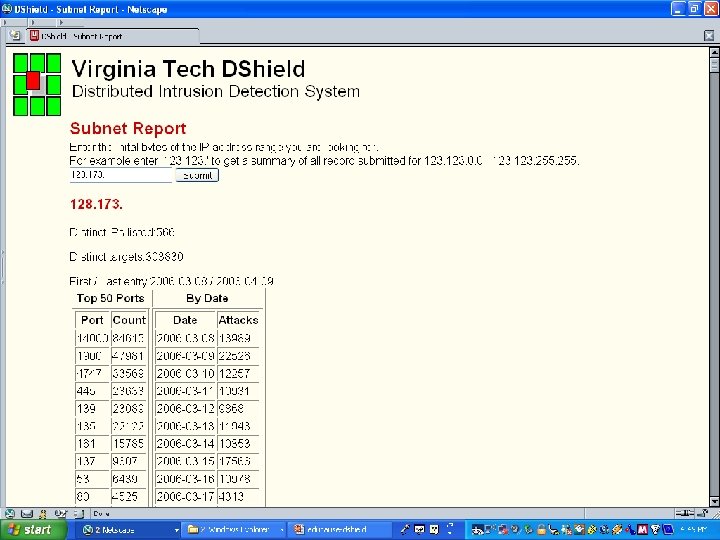
Putting the Pieces Together l l l REN-ISAC weather reports Dshield. org IPS Netflows UCONN netreg VSC scanners
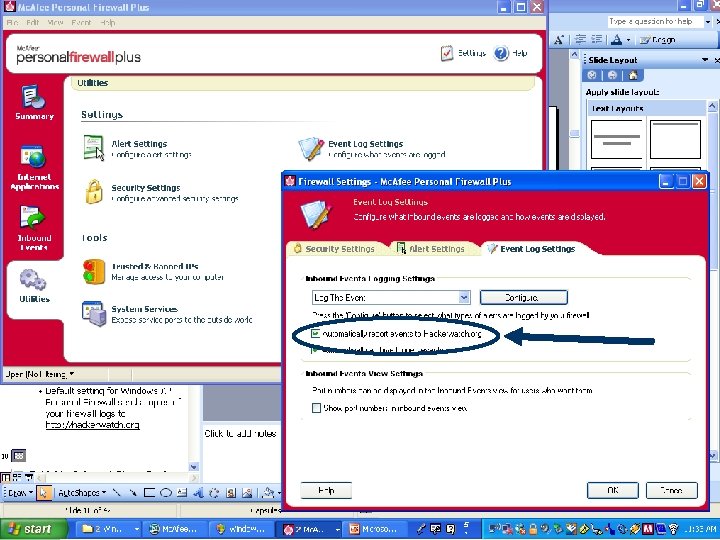
You Already Belong to a “Dshield” l l Default setting for Windows XP Personal Firewall sends copies of your firewall logs to http: //hackerwatch. org Why not belong to one that you know about?
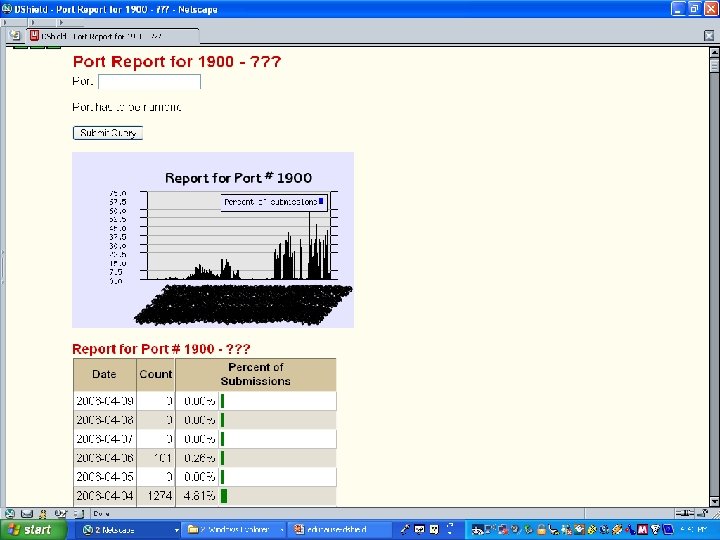
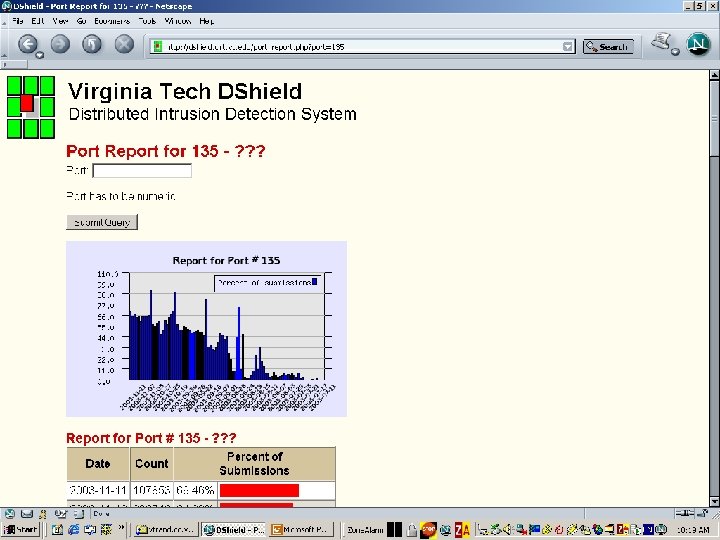
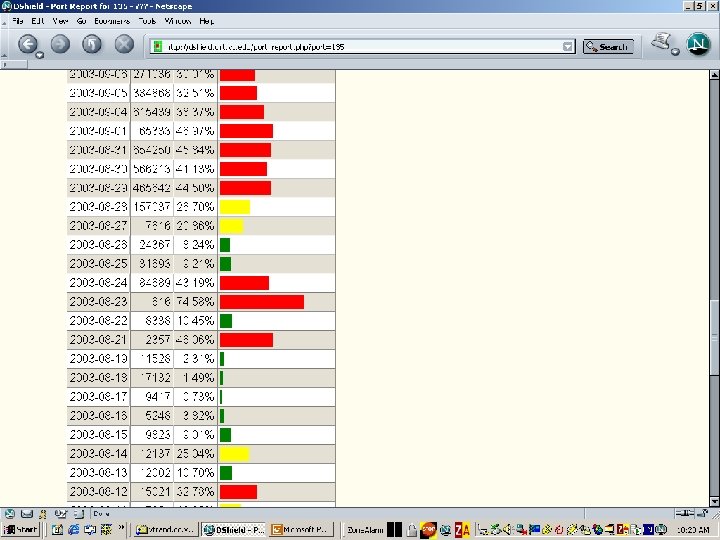
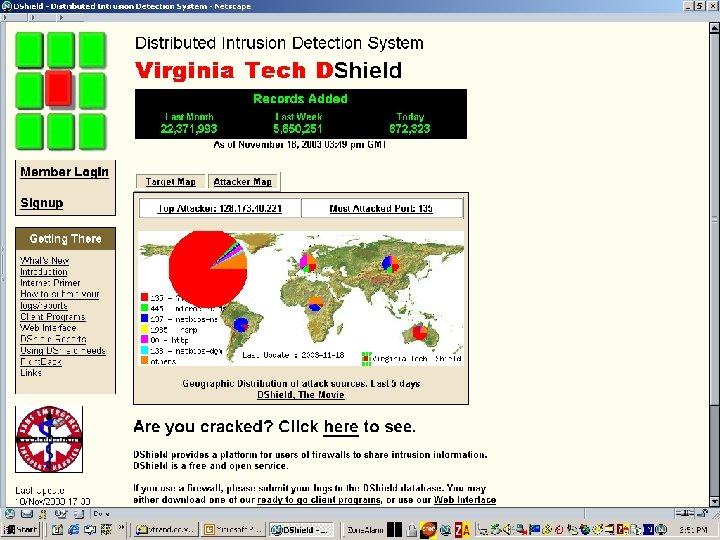
Dshield – Internet Storm Center l l Internet Storm Center concept was developed after analysts noted that time zones provided an early warning system for some attacks Attacks originating in Asia occurred 12+ hours before hitting North America – People coming to work and logging in their computers

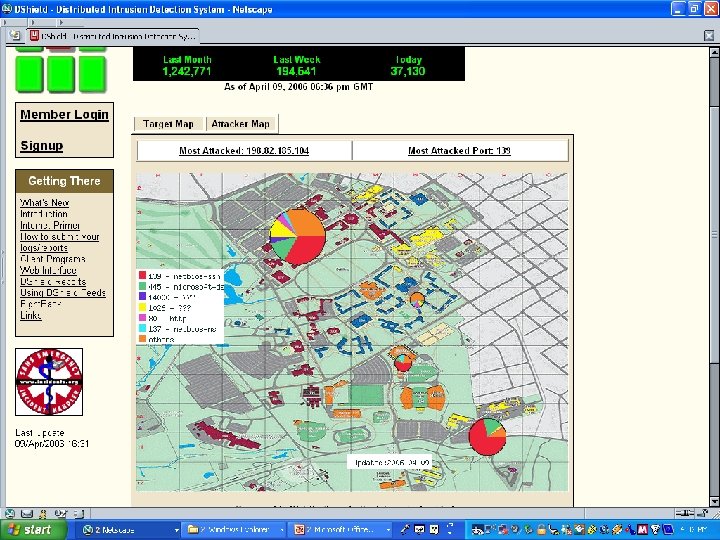
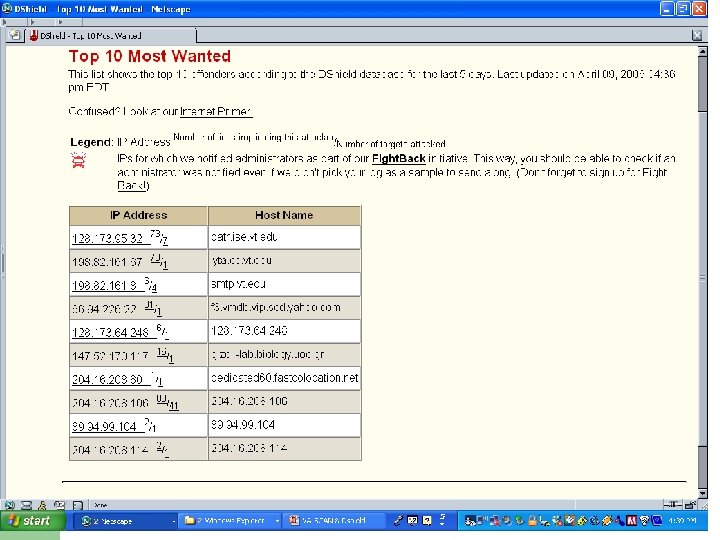
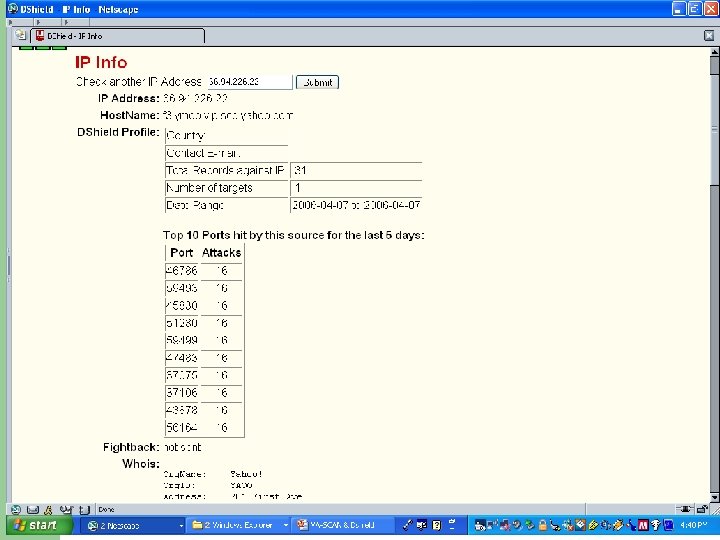
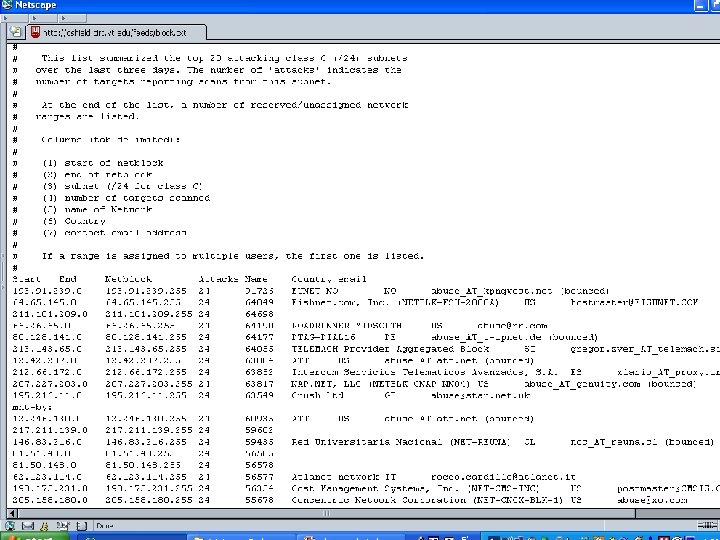
Dshield l l Similar to weather reporting infrastructure Mapping probes similar to mapping weather fronts Admins could look at the data real-time and use this info to prepare for an attack Similar to looking at a weather map to prepare for tomorrow’s weather
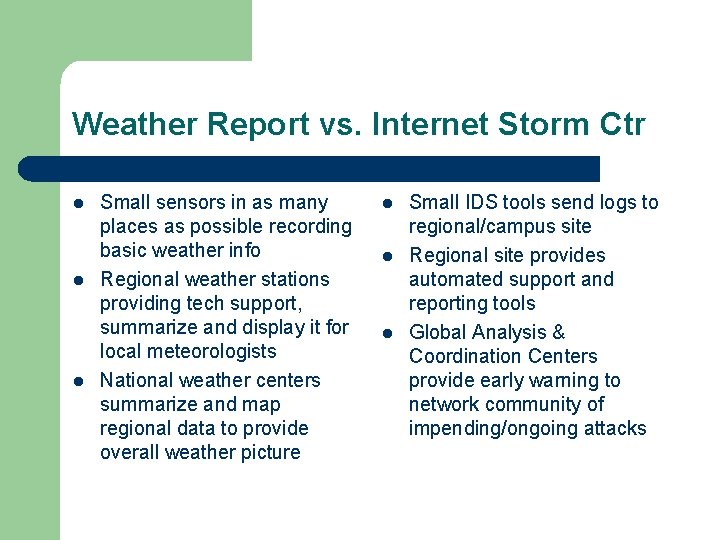
Weather Report vs. Internet Storm Ctr l l l Small sensors in as many places as possible recording basic weather info Regional weather stations providing tech support, summarize and display it for local meteorologists National weather centers summarize and map regional data to provide overall weather picture l l l Small IDS tools send logs to regional/campus site Regional site provides automated support and reporting tools Global Analysis & Coordination Centers provide early warning to network community of impending/ongoing attacks
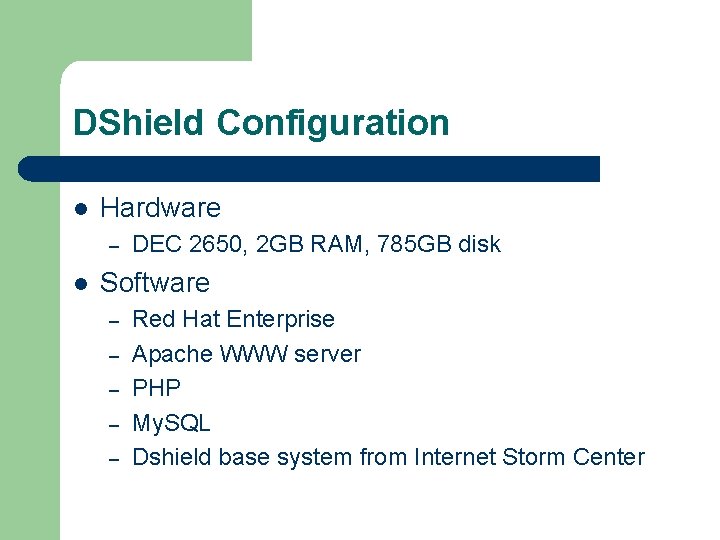
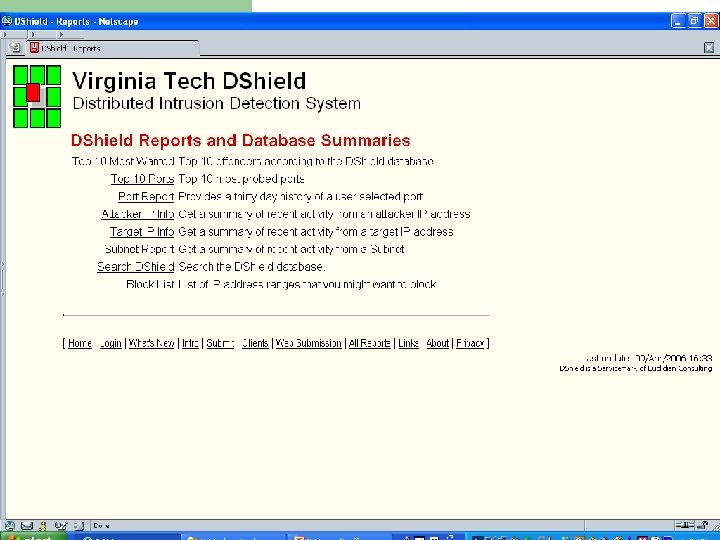
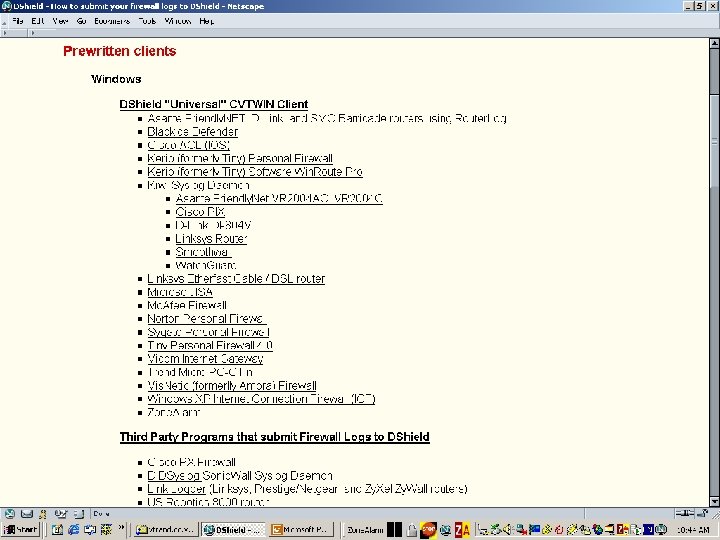
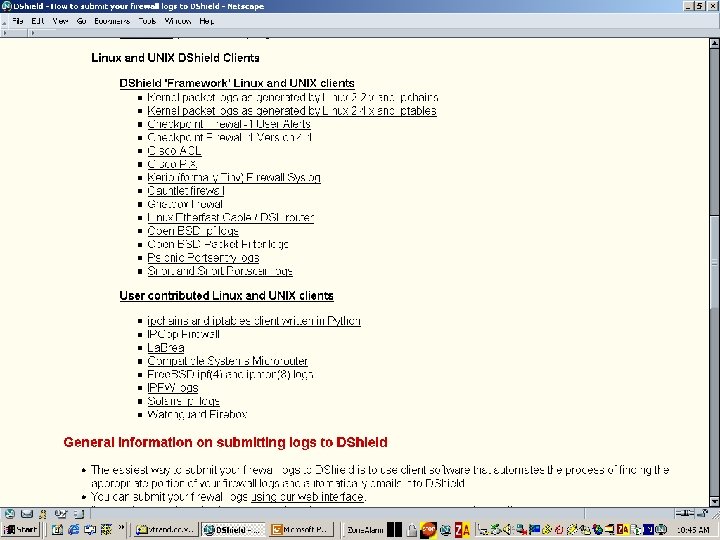
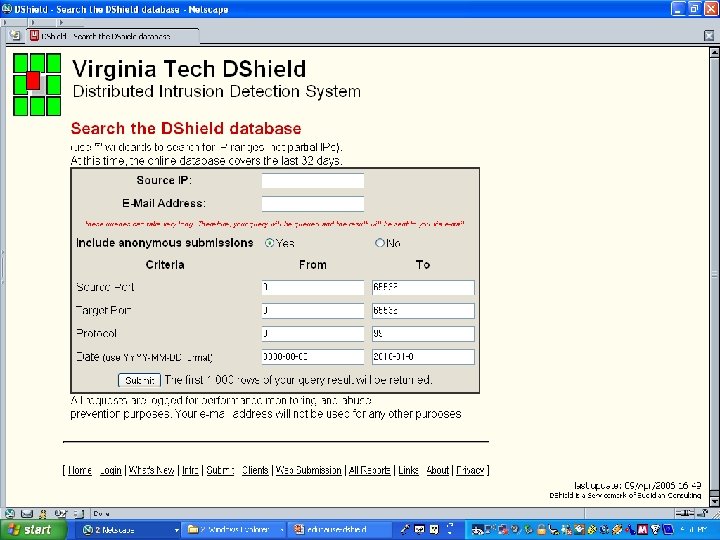
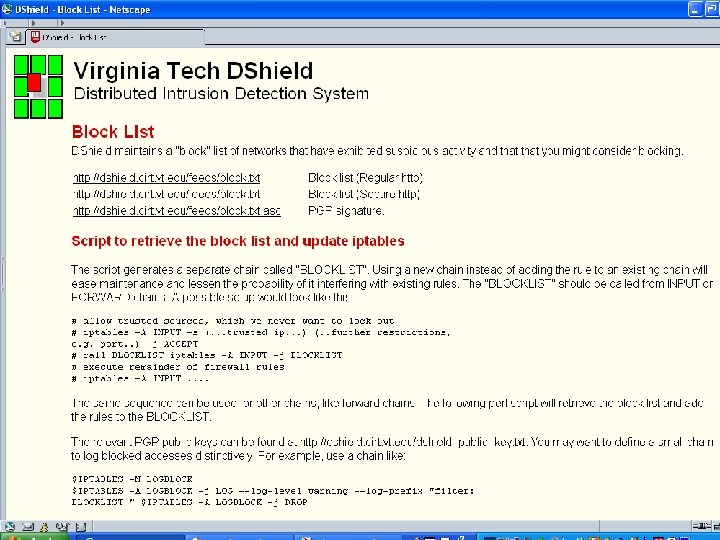
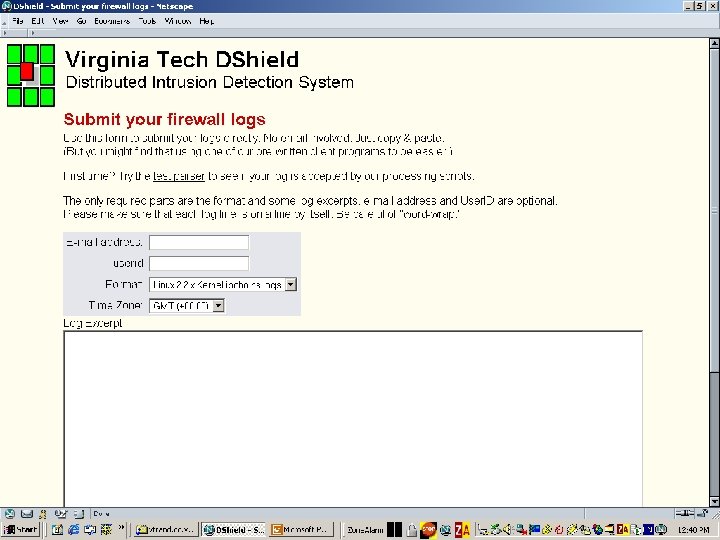
DShield Configuration l Hardware – l DEC 2650, 2 GB RAM, 785 GB disk Software – – – Red Hat Enterprise Apache WWW server PHP My. SQL Dshield base system from Internet Storm Center
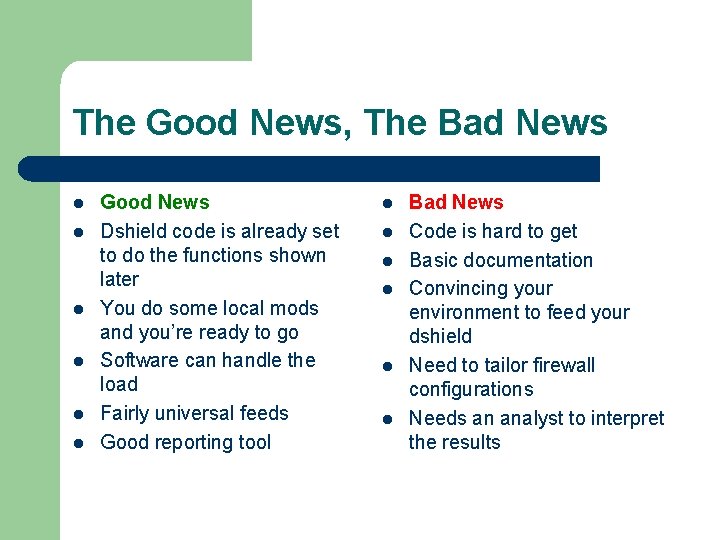
The Good News, The Bad News l l l Good News Dshield code is already set to do the functions shown later You do some local mods and you’re ready to go Software can handle the load Fairly universal feeds Good reporting tool l l l Bad News Code is hard to get Basic documentation Convincing your environment to feed your dshield Need to tailor firewall configurations Needs an analyst to interpret the results
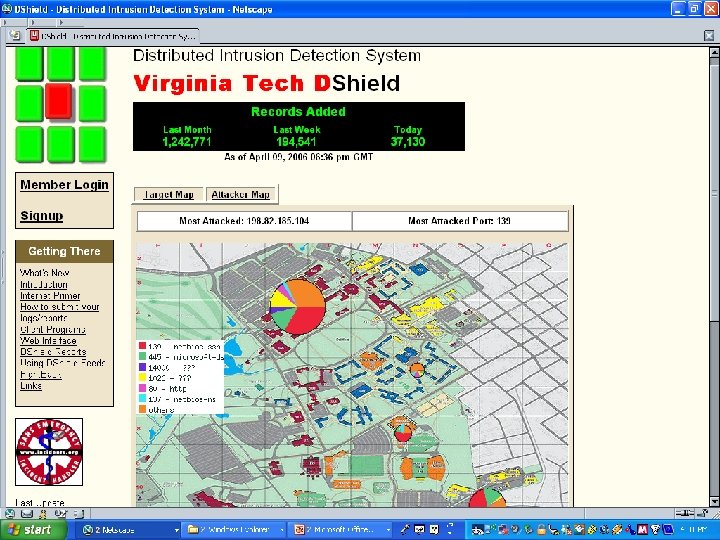
References l l http: //isc. sans. org http: //dshield. cirt. vt. edu Randy Marchany – – VA Tech IT Security Lab 1300 Torgersen Hall, VA Tech Blacksburg, VA 24060 540 -231 -9523, marchany@vt. edu
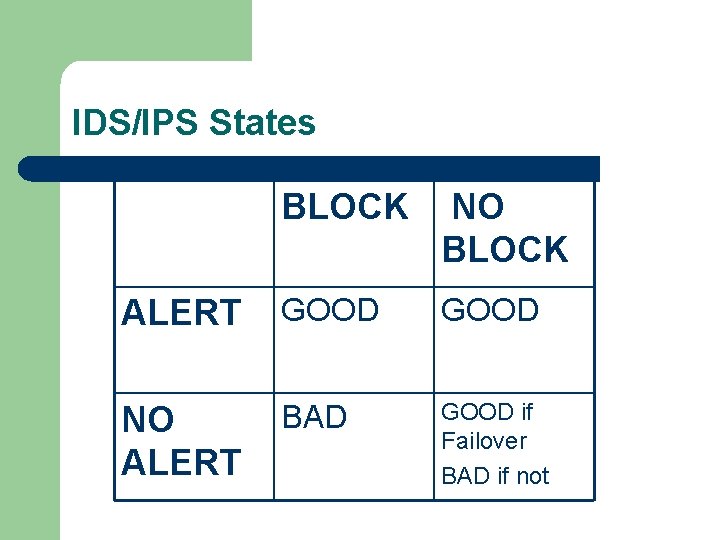
IDS/IPS States BLOCK NO BLOCK ALERT GOOD NO ALERT BAD GOOD if Failover BAD if not
VA Tech Defense in Depth l Layer 4: Supporting Authorized Users – – – – ID and access management File Encryption Secure communications PKI VPN IPSEC based VPN SSL VPN Secure remote access
VA Tech Defense in Depth l Layer 5: Tools to minimize business losses – – – – Security information management Business transaction integrity monitoring Security skills development (training) Forensic tools Regulatory compliance tools Business recovery Backup
- Slides: 42