Buffer Overflows Attacks and Defenses for the Vulnerability
Buffer Overflows: Attacks and Defenses for the Vulnerability of the Decade Crispin Cowan SANS 2000
Buffer Overflows Inject and execute attack code at the privilege of the vulnerable program. “exec(/bin/sh)”
Inject Code On the stack (automatic variables) On the heap (malloc’d variables) In static data areas Code does not need to be in the overflowing buffer.
Use Code Already There “exec(arg)” by making arg point to “/bin/sh”
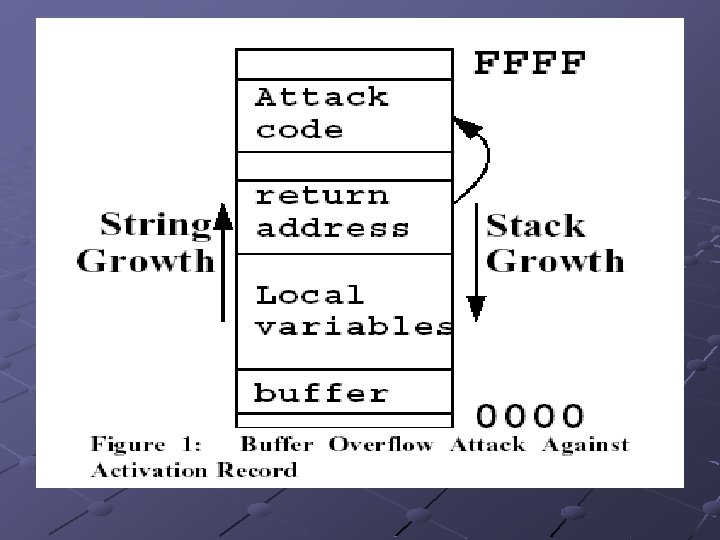
Jump to Attacker’s Code Activation Record n Overflow into return address on the stack and make it point at the code. Function pointers n Overflow into “void (*foo())()” and it point at the code.
Buffer Overflow Defenses Writing Correct Code n Vulnerable programs continue to emerge on a regular basis C has many error-prone idioms and a culture that favors performance over correctness. Static Analysis Tools n n Fortify – looks for vulnerable constructs Too many false positives.
Buffer Overflow Defenses Non-executable buffers n Non executable data segments Optimizing compiles emit code into program data segments n Non executable stack segments Highly effective against code injection on the stack but not against code injections on the heap or static variables.
Buffer Overflow Defenses Array Bound Checking n n Can run 12 x-30 x slower a[3] is checked but *(a+3) is not
Buffer Overflow Defenses Type safe languages: Java or ML n n There are millions of lines of C code in operating systems and security system applications Attack the Java Virtual Machine which is a C program
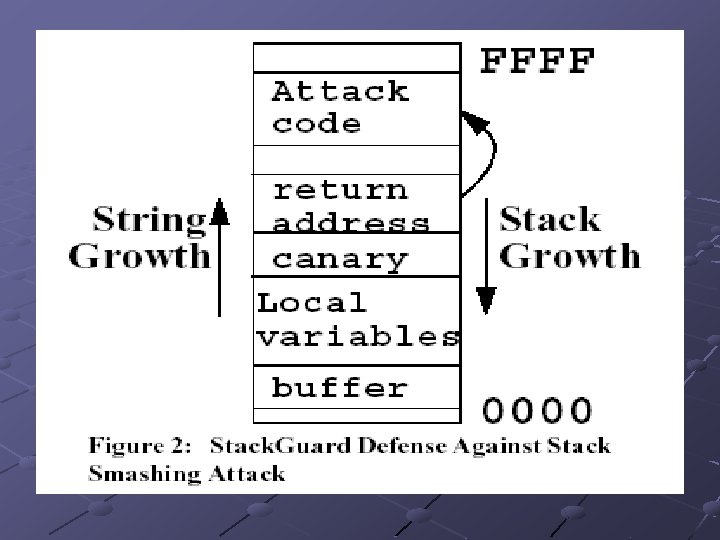
Canary Terminator Canary n 0 (null), CR, LF, -1 (EOF) Random Canary n 32 bit random number
Stack. Guard Compiler Recompiled Linux Prevented old and new attacks Execution cost of SSH and Apache was indistinguishable
Stack. Guard Compiler Performance n Pointer dereferencing occurs much less than array references There does not exist any bounds checking compiler capable of approaching the compatibility and performance of the Stack. Guard compiler
Point. Guard Compiler Put canary next to function pointers as well. Only the relative obscure form of buffer overflow attack that corrupts non-pointer variables to affect the program’s logic will escape Point. Guard (Morris worm)
Conclusion Use Safer Library : Strsafe. h Visual C++. NET /GS option n Similar to Stack. Guard
- Slides: 16