BRK 3490 What are we covering How Azure

BRK 3490
What are we covering? • How Azure protects your data • How you can protect your data • How you can control and protect your keys using Azure Key Vault • How to use
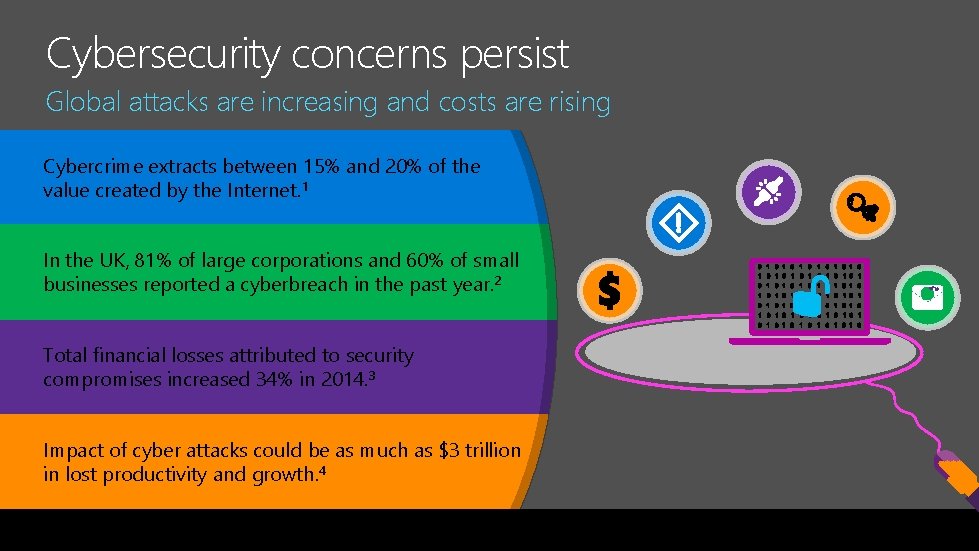
Cybersecurity concerns persist Global attacks are increasing and costs are rising Cybercrime extracts between 15% and 20% of the value created by the Internet. 1 In the UK, 81% of large corporations and 60% of small businesses reported a cyberbreach in the past year. 2 Total financial losses attributed to security compromises increased 34% in 2014. 3 Impact of cyber attacks could be as much as $3 trillion in lost productivity and growth. 4
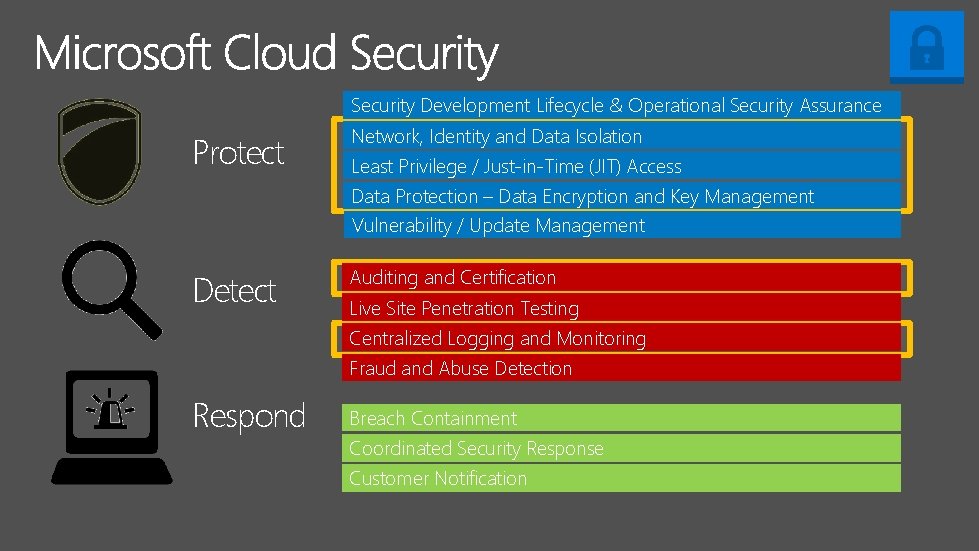
Security Development Lifecycle & Operational Security Assurance Protect Network, Identity and Data Isolation Least Privilege / Just-in-Time (JIT) Access Data Protection – Data Encryption and Key Management Vulnerability / Update Management Detect Auditing and Certification Live Site Penetration Testing Centralized Logging and Monitoring Fraud and Abuse Detection Respond Breach Containment Coordinated Security Response Customer Notification
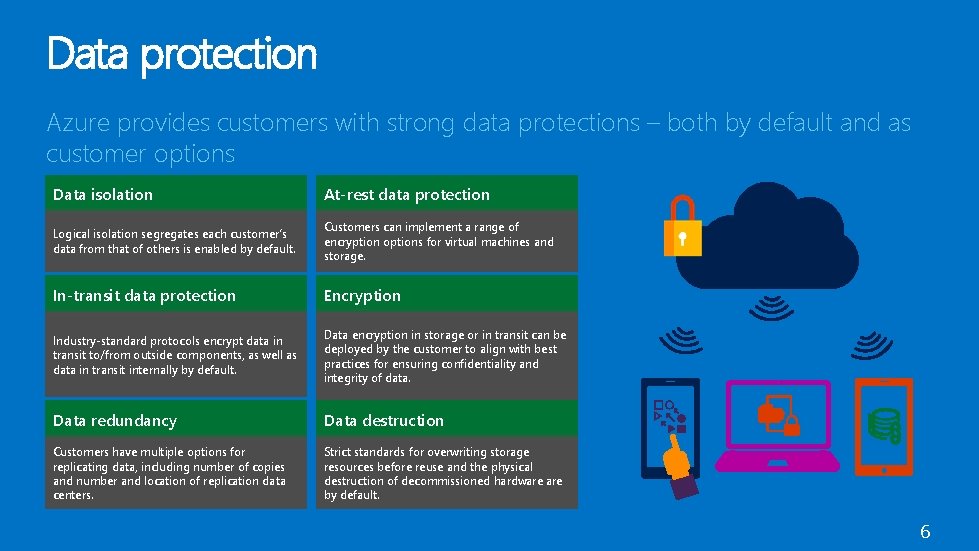
Data protection Azure provides customers with strong data protections – both by default and as customer options Data isolation At-rest data protection Logical isolation segregates each customer’s data from that of others is enabled by default. Customers can implement a range of encryption options for virtual machines and storage. In-transit data protection Encryption Industry-standard protocols encrypt data in transit to/from outside components, as well as data in transit internally by default. Data encryption in storage or in transit can be deployed by the customer to align with best practices for ensuring confidentiality and integrity of data. Data redundancy Data destruction Customers have multiple options for replicating data, including number of copies and number and location of replication data centers. Strict standards for overwriting storage resources before reuse and the physical destruction of decommissioned hardware by default. 6
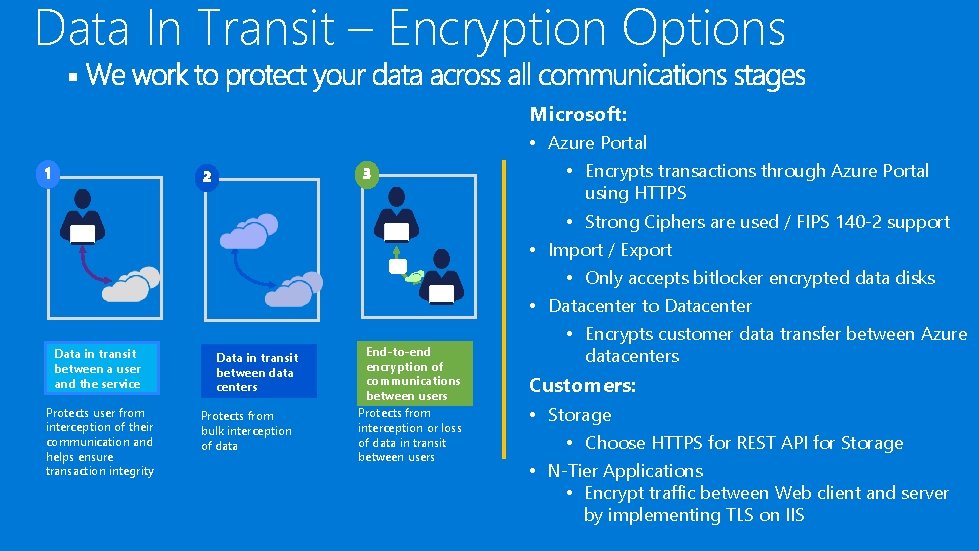
Data In Transit – Encryption Options § Microsoft: Data in transit between a user and the service Protects user from interception of their communication and helps ensure transaction integrity Data in transit between data centers Protects from bulk interception of data End-to-end encryption of communications between users Protects from interception or loss of data in transit between users • Azure Portal • Encrypts transactions through Azure Portal using HTTPS • Strong Ciphers are used / FIPS 140 -2 support • Import / Export • Only accepts bitlocker encrypted data disks • Datacenter to Datacenter • Encrypts customer data transfer between Azure datacenters Customers: • Storage • Choose HTTPS for REST API for Storage • N-Tier Applications • Encrypt traffic between Web client and server by implementing TLS on IIS
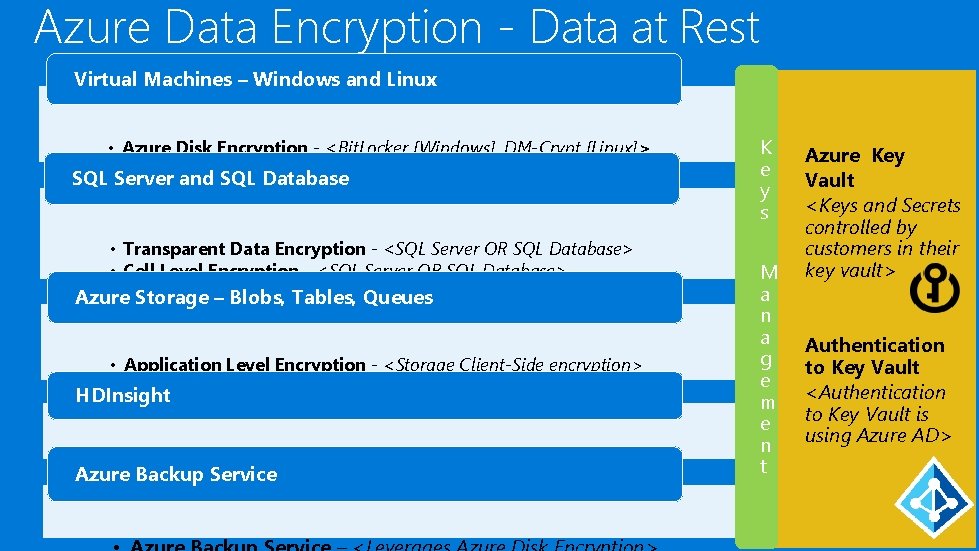
Azure Data Encryption - Data at Rest Virtual Machines – Windows and Linux • Azure Disk Encryption - <Bit. Locker [Windows], DM-Crypt [Linux]> ® Secure. VM> • Partner Volume Encryption – <Cloud. Link SQL Server and SQL Database • Transparent Data Encryption - <SQL Server OR SQL Database> • Cell Level Encryption - <SQL Server OR SQL Database> • Always Encrypted Azure Storage – Blobs, Tables, Queues • Application Level Encryption - <Storage Client-Side encryption> • Cloud Integrated Storage - <Stor. Simple> HDInsight • HDInsight – <Leverages Azure Storage, SQL Azure DB encryption> Azure Backup Service K e y s M a n a g e m e n t Azure Key Vault <Keys and Secrets controlled by customers in their key vault> Authentication to Key Vault <Authentication to Key Vault is using Azure AD>
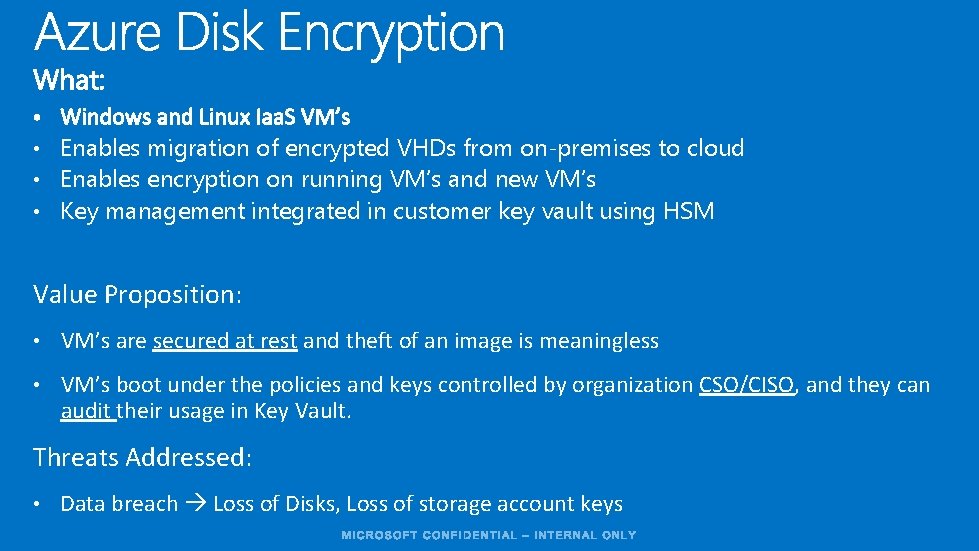
• Enables migration of encrypted VHDs from on-premises to cloud • Enables encryption on running VM’s and new VM’s • Key management integrated in customer key vault using HSM Value Proposition: • VM’s are secured at rest and theft of an image is meaningless • VM’s boot under the policies and keys controlled by organization CSO/CISO, and they can audit their usage in Key Vault. Threats Addressed: • Data breach Loss of Disks, Loss of storage account keys
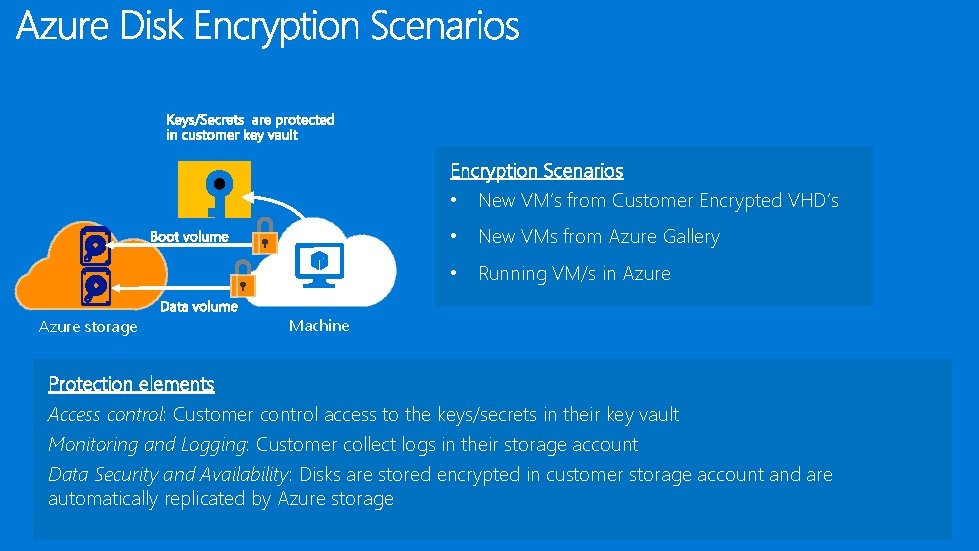
Encryption Scenarios • New VM’s from Customer Encrypted VHD’s • New VMs from Azure Gallery • Running VM/s in Azure storage Machine Protection elements Access control: Customer control access to the keys/secrets in their key vault Monitoring and Logging: Customer collect logs in their storage account Data Security and Availability: Disks are stored encrypted in customer storage account and are automatically replicated by Azure storage
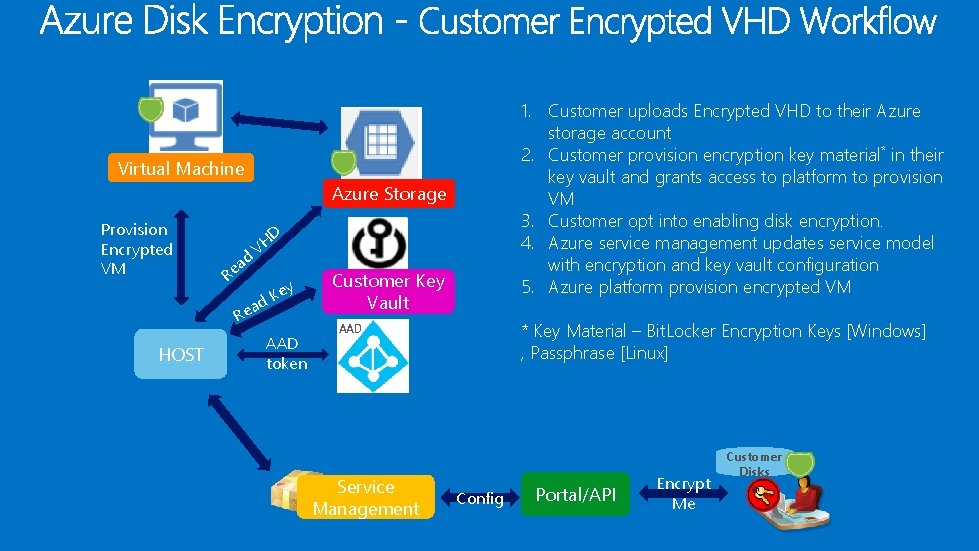
1. Customer uploads Encrypted VHD to their Azure storage account 2. Customer provision encryption key material* in their key vault and grants access to platform to provision VM 3. Customer opt into enabling disk encryption. 4. Azure service management updates service model with encryption and key vault configuration 5. Azure platform provision encrypted VM Virtual Machine Azure Storage Provision Encrypted VM D ad e R VH ad Re HOST y Ke AAD token Customer Key Vault * Key Material – Bit. Locker Encryption Keys [Windows] , Passphrase [Linux] AAD Service Management Config Portal/API Encrypt Me Customer Disks
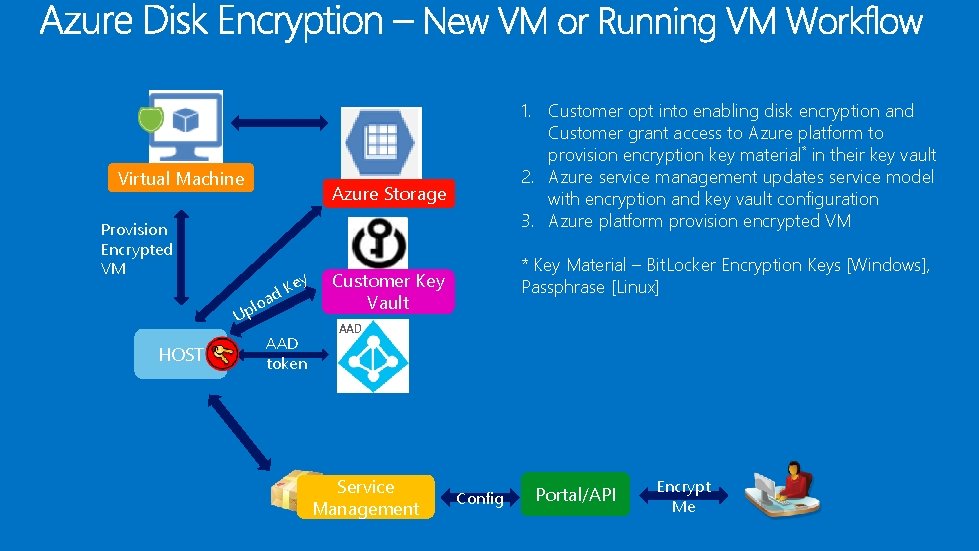
Virtual Machine Azure Storage Provision Encrypted VM loa p U HOST 1. Customer opt into enabling disk encryption and Customer grant access to Azure platform to provision encryption key material* in their key vault 2. Azure service management updates service model with encryption and key vault configuration 3. Azure platform provision encrypted VM y e d. K AAD token * Key Material – Bit. Locker Encryption Keys [Windows], Passphrase [Linux] Customer Key Vault AAD Service Management Config Portal/API Encrypt Me
![• Secrets like Bit. Locker Encryption Keys [BEK] or Linux Pass. Phrase are • Secrets like Bit. Locker Encryption Keys [BEK] or Linux Pass. Phrase are](http://slidetodoc.com/presentation_image/2b567d75ceed2bf3370b1231bdcb0cd5/image-14.jpg)
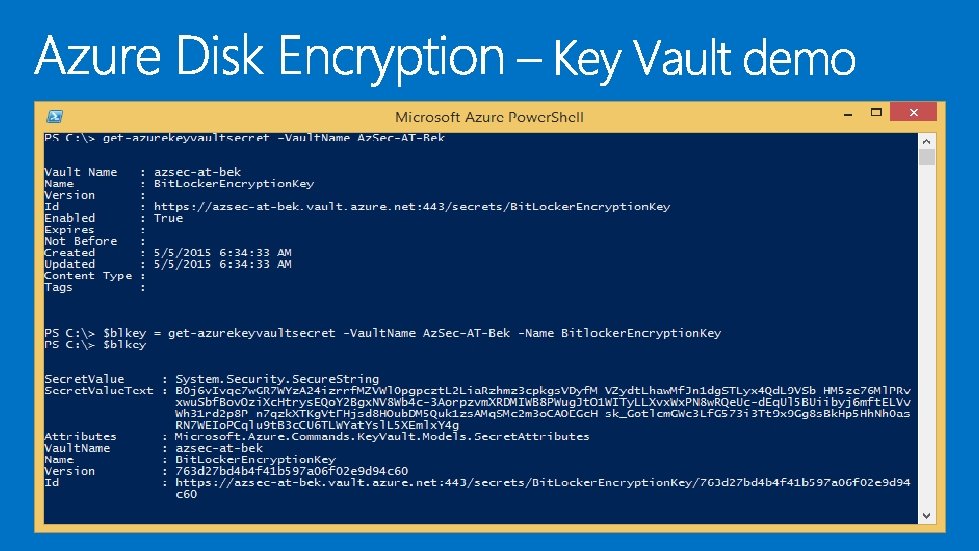
• Secrets like Bit. Locker Encryption Keys [BEK] or Linux Pass. Phrase are stored protected in customer control in their key vault container • Secrets are encrypted by customer controlled Key Encryption Key [KEK – RSA 2048] • Customer grant [explicit] Read or Write access to their key vault container to Azure to enable disk encryption • Customer specify key vault uri to allow access to Azure to their keys and secrets • Azure do not have ANY default access to customer key vault for disk encryption feature Secret Keys Contoso. BEK [encrypted by Contoso. KEK] – Bit. Locker Windows Contoso. KEK Contoso. Pass. Phrase [encrypted by Contoso. KEK] – Linux Microsoft Confidential
• Users encrypt their data on the client side before uploading to Azure Storage, and also decrypt it after downloading the storage service never sees the keys and is incapable of decrypting the data
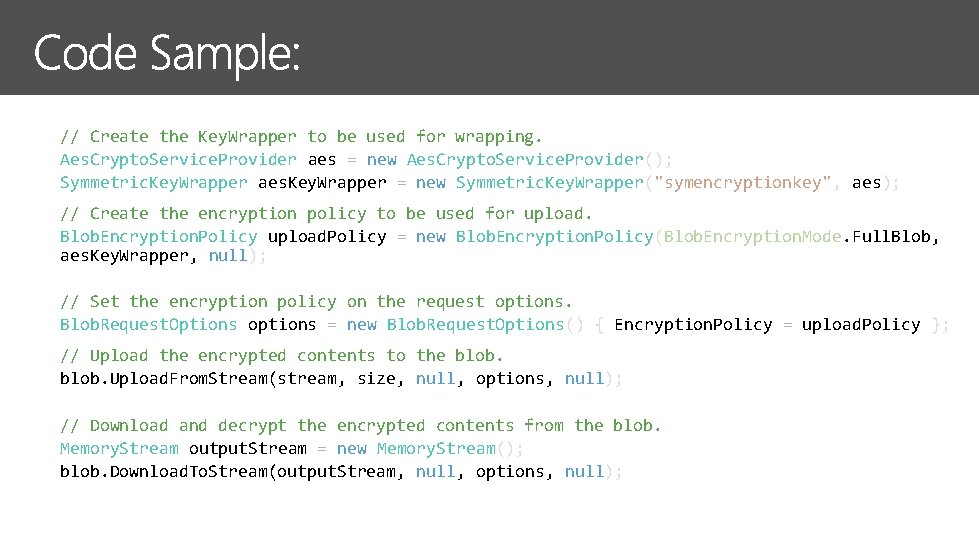
§ § § // Create the Key. Wrapper to be used for wrapping. Aes. Crypto. Service. Provider aes = new Aes. Crypto. Service. Provider(); Symmetric. Key. Wrapper aes. Key. Wrapper = new Symmetric. Key. Wrapper("symencryptionkey", aes); § § § // Create the encryption policy to be used for upload. Blob. Encryption. Policy upload. Policy = new Blob. Encryption. Policy(Blob. Encryption. Mode. Full. Blob, aes. Key. Wrapper, null); // Set the encryption policy on the request options. Blob. Request. Options options = new Blob. Request. Options() { Encryption. Policy = upload. Policy }; § § § // Upload the encrypted contents to the blob. Upload. From. Stream(stream, size, null, options, null); // Download and decrypt the encrypted contents from the blob. Memory. Stream output. Stream = new Memory. Stream(); blob. Download. To. Stream(output. Stream, null, options, null);
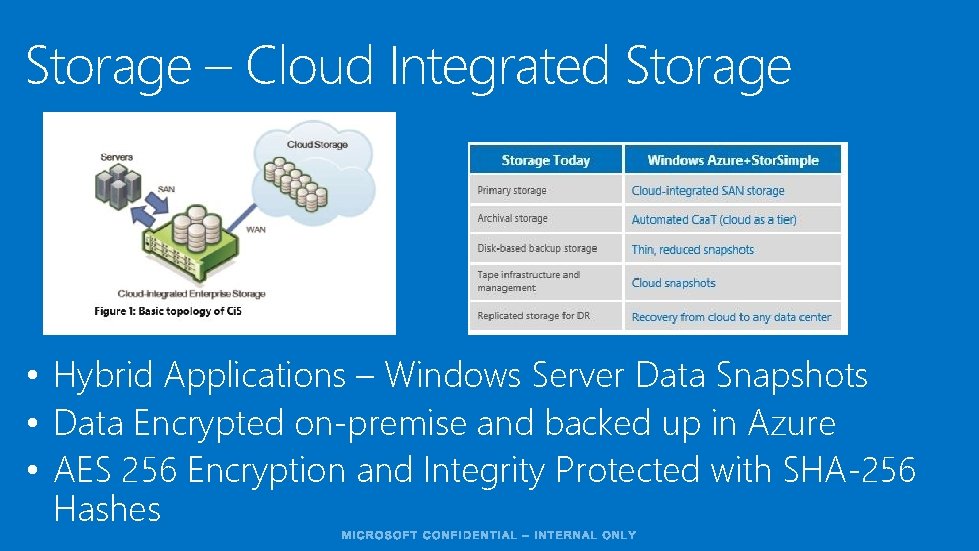
Storage – Cloud Integrated Storage • Hybrid Applications – Windows Server Data Snapshots • Data Encrypted on-premise and backed up in Azure • AES 256 Encryption and Integrity Protected with SHA-256 Hashes
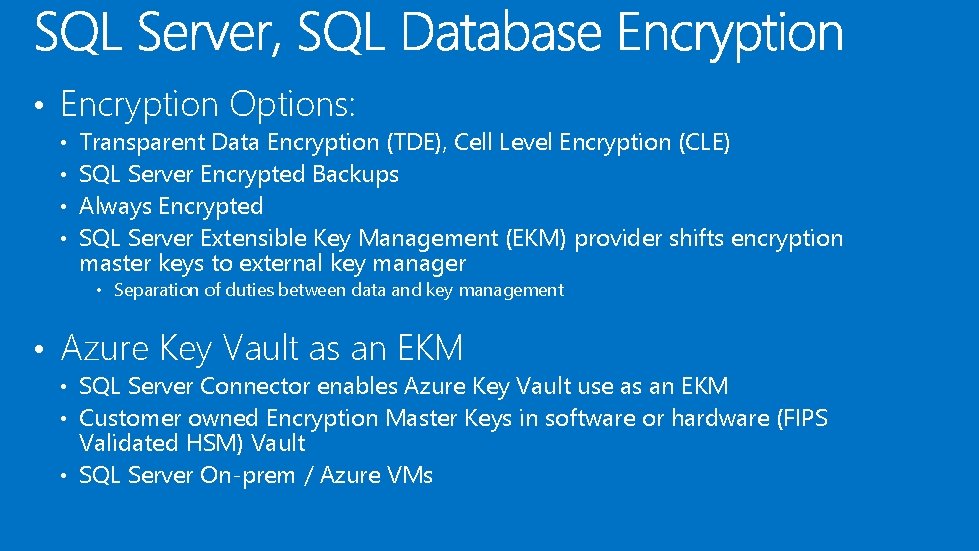
• Encryption Options: • • Transparent Data Encryption (TDE), Cell Level Encryption (CLE) SQL Server Encrypted Backups Always Encrypted SQL Server Extensible Key Management (EKM) provider shifts encryption master keys to external key manager • Separation of duties between data and key management • Azure Key Vault as an EKM • SQL Server Connector enables Azure Key Vault use as an EKM • Customer owned Encryption Master Keys in software or hardware (FIPS Validated HSM) Vault • SQL Server On-prem / Azure VMs
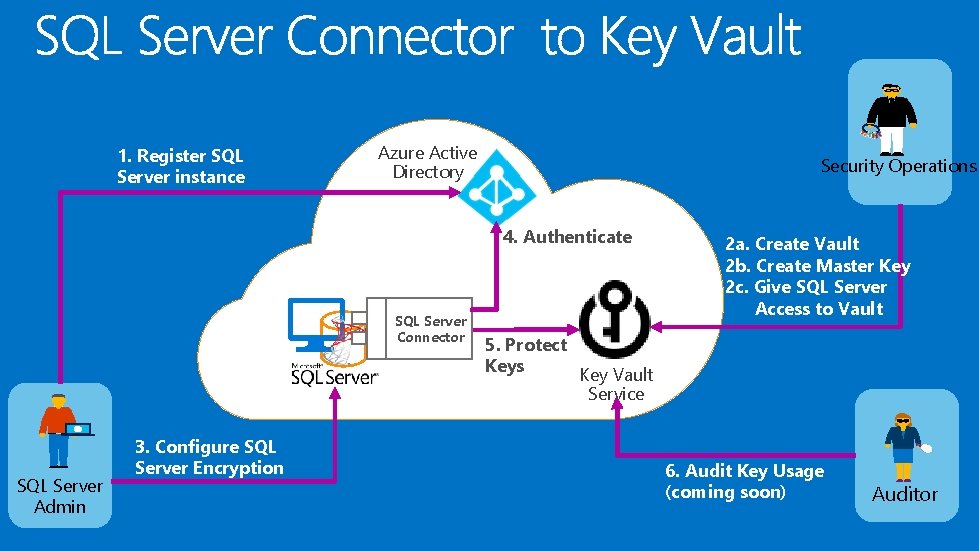
1. Register SQL Server instance Azure Active Directory Security Operations 4. Authenticate SQL Server Connector SQL Server Admin 3. Configure SQL Server Encryption 2 a. Create Vault 2 b. Create Master Key 2 c. Give SQL Server Access to Vault 5. Protect Keys Key Vault Service 6. Audit Key Usage (coming soon) Auditor
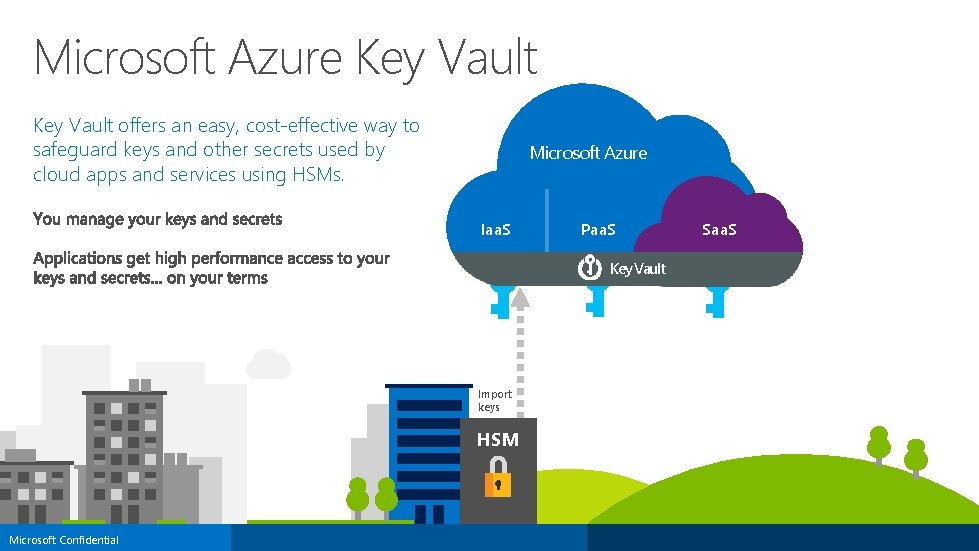
Microsoft Azure Key Vault offers an easy, cost-effective way to safeguard keys and other secrets used by cloud apps and services using HSMs. Microsoft Azure Iaa. S Paa. S Key Vault Import keys HSM Microsoft Confidential Saa. S
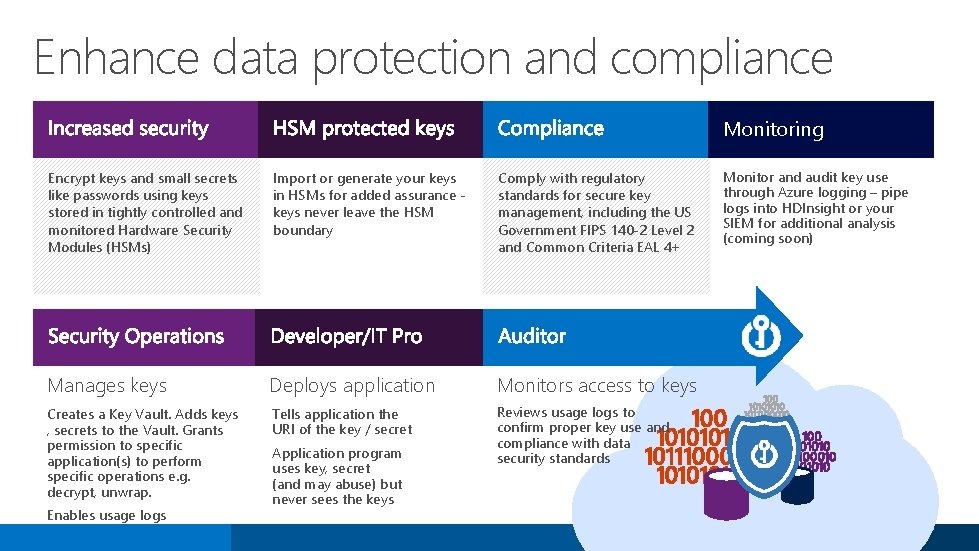
Enhance data protection and compliance Monitoring Encrypt keys and small secrets like passwords using keys stored in tightly controlled and monitored Hardware Security Modules (HSMs) Import or generate your keys in HSMs for added assurance keys never leave the HSM boundary Comply with regulatory standards for secure key management, including the US Government FIPS 140 -2 Level 2 and Common Criteria EAL 4+ Manages keys Deploys application Monitors access to keys Creates a Key Vault. Adds keys , secrets to the Vault. Grants permission to specific application(s) to perform specific operations e. g. decrypt, unwrap. Tells application the URI of the key / secret Reviews usage logs to confirm proper key use and compliance with data security standards Enables usage logs Application program uses key, secret (and may abuse) but never sees the keys Monitor and audit key use through Azure logging – pipe logs into HDInsight or your SIEM for additional analysis (coming soon)
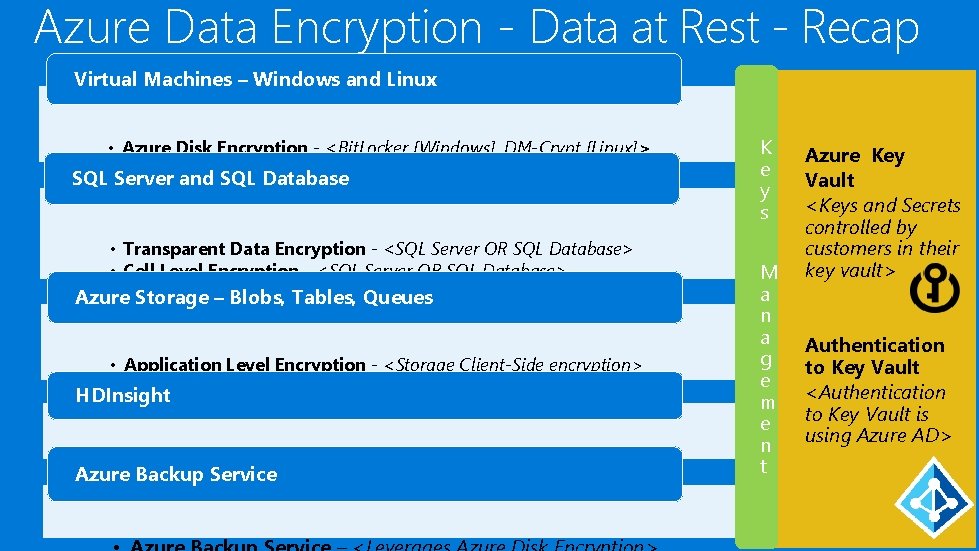
Azure Data Encryption - Data at Rest - Recap Virtual Machines – Windows and Linux • Azure Disk Encryption - <Bit. Locker [Windows], DM-Crypt [Linux]> ® Secure. VM> • Partner Volume Encryption – <Cloud. Link SQL Server and SQL Database • Transparent Data Encryption - <SQL Server OR SQL Database> • Cell Level Encryption - <SQL Server OR SQL Database> • Always Encrypted Azure Storage – Blobs, Tables, Queues • Application Level Encryption - <Storage Client-Side encryption> • Cloud Integrated Storage - <Stor. Simple> HDInsight • HDInsight – <Leverages Azure Storage, SQL Azure DB encryption> Azure Backup Service K e y s M a n a g e m e n t Azure Key Vault <Keys and Secrets controlled by customers in their key vault> Authentication to Key Vault <Authentication to Key Vault is using Azure AD>
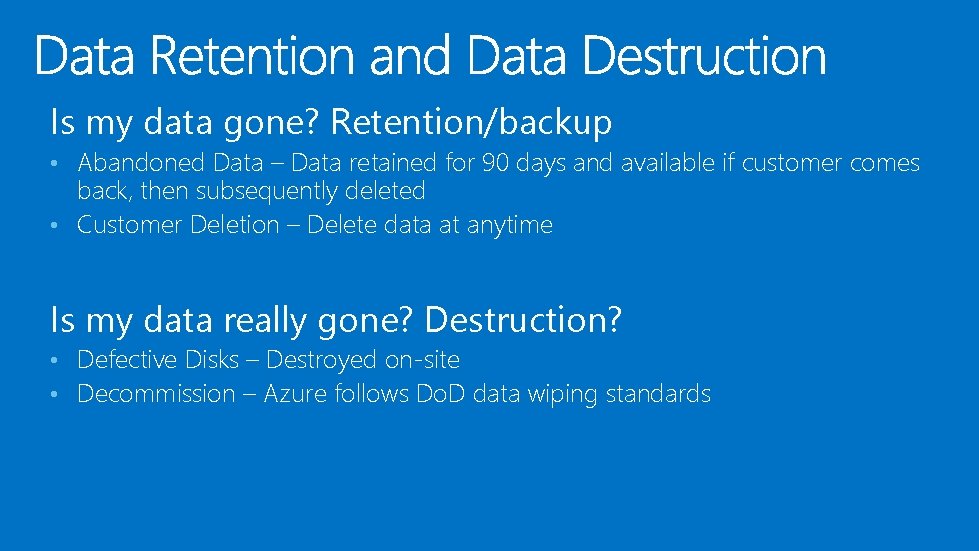
Is my data gone? Retention/backup • Abandoned Data – Data retained for 90 days and available if customer comes back, then subsequently deleted • Customer Deletion – Delete data at anytime Is my data really gone? Destruction? • Defective Disks – Destroyed on-site • Decommission – Azure follows Do. D data wiping standards

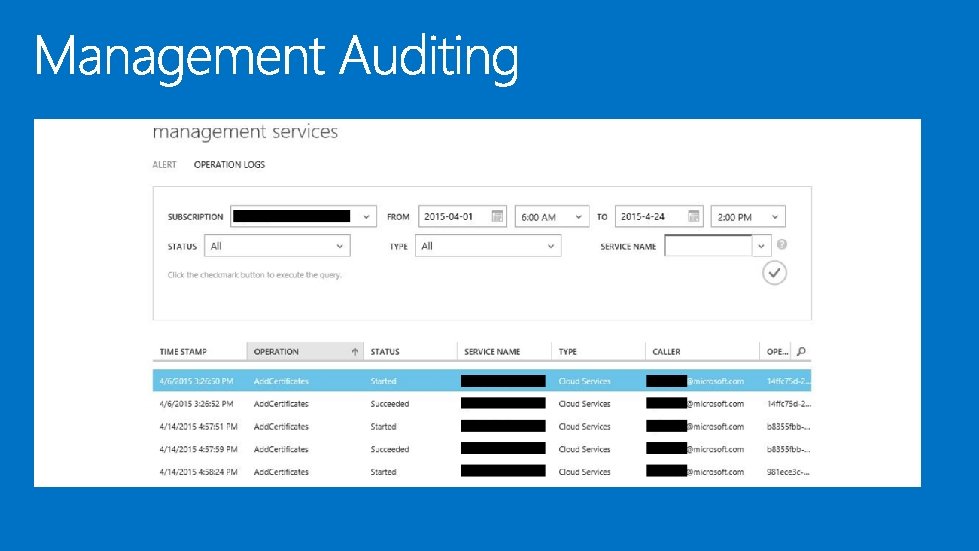
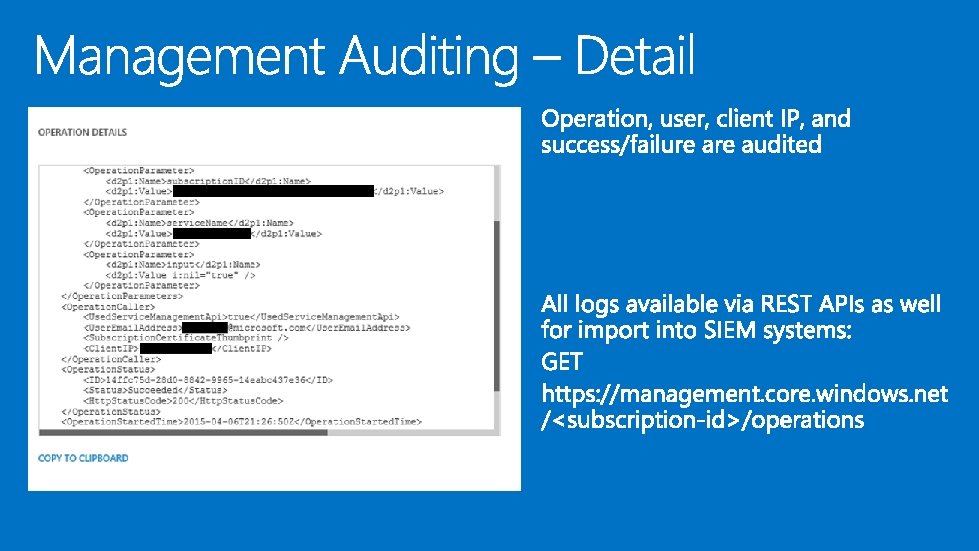
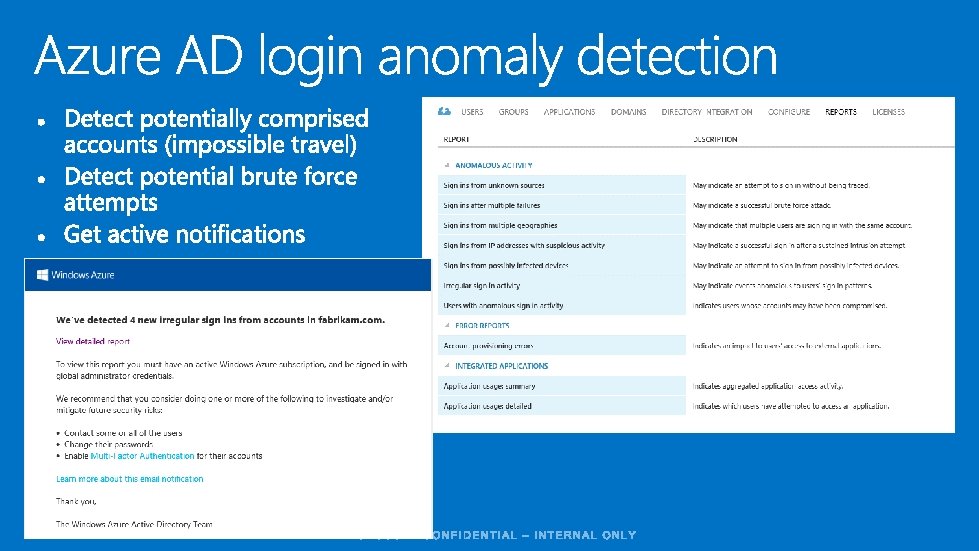
All data is encrypted, though not done yet Fundamentals are key! Mitigate risk of compromised accounts Multi-Factor Authentication (Azure MFA / Windows Server ADFS) Limit excessive permissions – least privilege Azure AD Role Based Access Control (RBAC) Azure AD Privileged Identity Management (temporary/’JIT’ access controls) Detect insider compromise or abuse of privileges Azure auditing and logging Azure AD anomaly detection and analysis
Compromised accounts Accounts with weak authentication methods (passwords) can be compromised (e. g. spear-phishing) Secure your user accounts with Azure MFA Can be used with Azure Active Directory or Windows Server Active Directory Federation Services (ADFS) Provides a second factor (e. g. phone or device) as a second factor Secure your user accounts with Smart Cards with Windows Server ADFS & AAD Use your existing PKI (Smart Card, Virtual Smart Card) to secure accounts by using Azure AD accounts federated to your on premises infrastructure
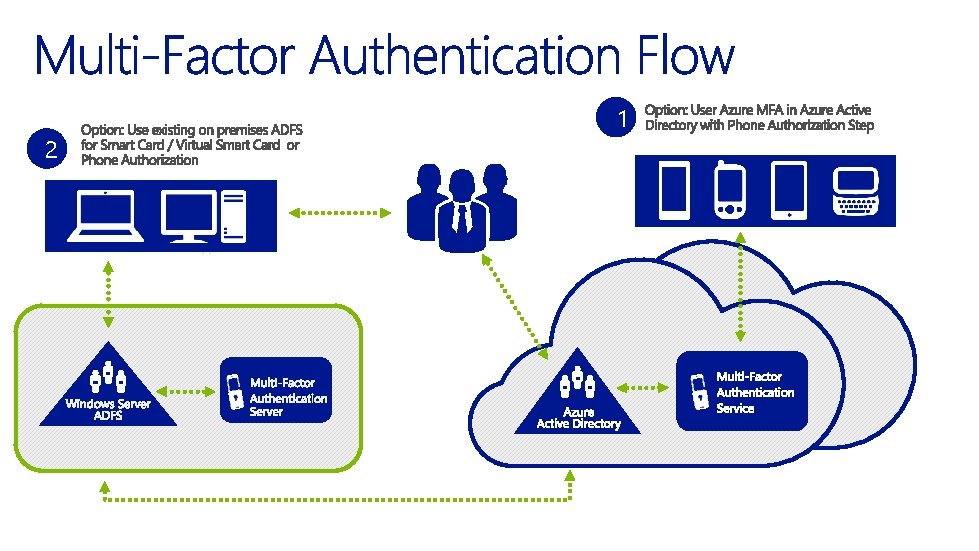
2 1
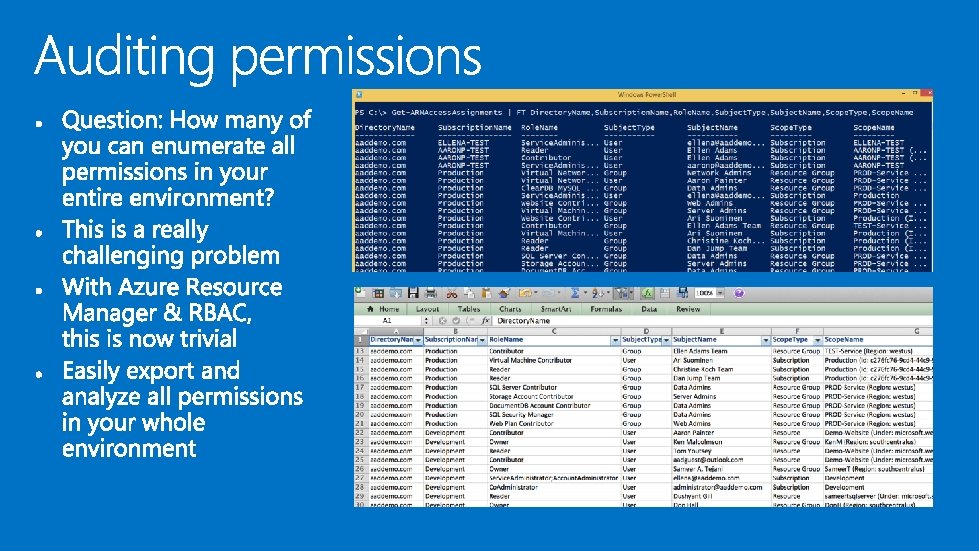
Limiting Permissions to sensitive data should follow ‘least privilege’ principal – only grant access necessary for role. Azure RBAC (20 built-in roles, custom coming soon) General: Readers, Contributors, Owners Resource Specific: e. g. Virtual. Machine-Contributor, SQLDB Contributor … Assign Users, Groups, and Service Principals Key Vault Access Control Very fine grained access controls to key vaults for user and service principals Create, verify, sign, wrap/unwrap, etc. (able to enforce segregation of duties)
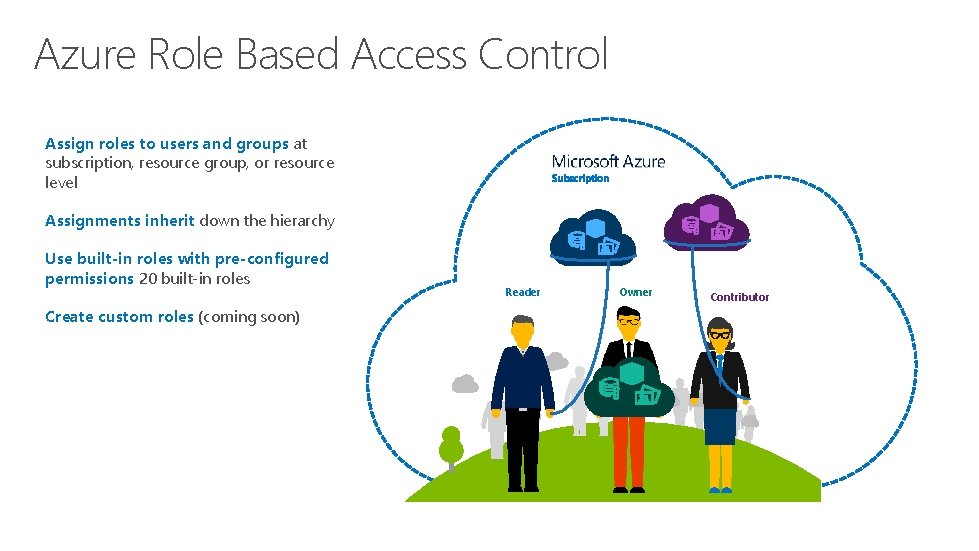
Azure Role Based Access Control Assign roles to users and groups at subscription, resource group, or resource level Subscription Assignments inherit down the hierarchy Use built-in roles with pre-configured permissions 20 built-in roles Create custom roles (coming soon) Reader Owner Contributor
RBAC Example Resource Group == Employee. Benefits. App -Virtual Machines, SQL DB, Storage Accounts Employee. Benefits. App Role Assignments - Owners == HR IT Admins - Contributors == HR IT Dev. Ops Team -Readers == HR Benefits Team
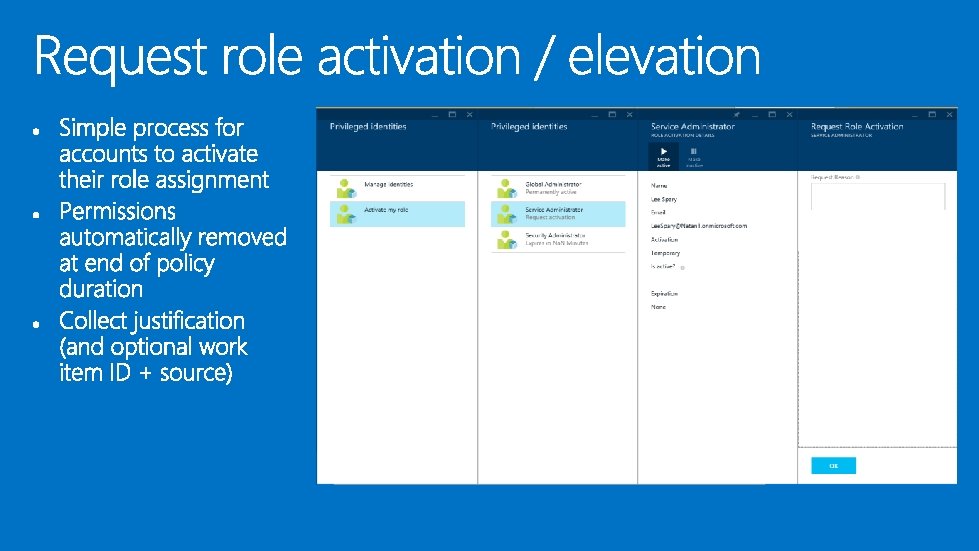
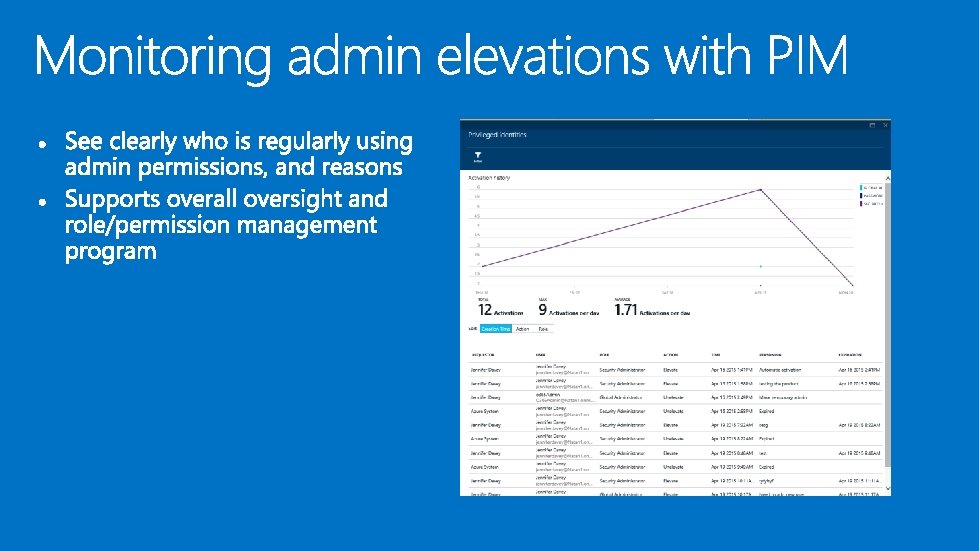
Superuser accounts have special risk and deserve special management. • Enable “Just In Time” (JIT) privileged access • Microsoft uses this paradigm to protect Azure • No standing access • Temporary, specifically scoped elevations to resolve incidents & provide support • Customers can now benefit from this learning – Azure AD Privileged Identity Management
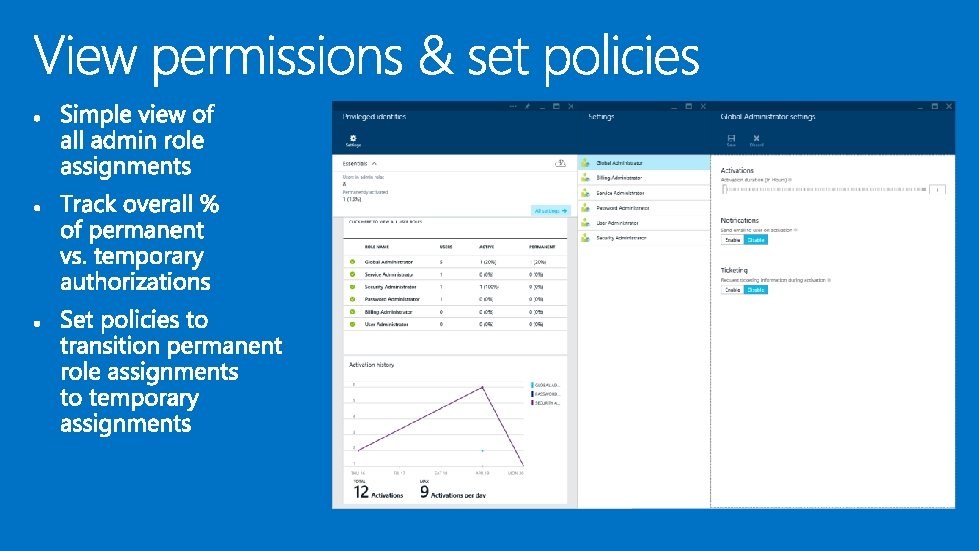
• Discover current admin permissions in one view • Set temporary authorization policies for Azure AD management roles • Global, billing, password, service, and user administrators can use PIM • Collect justification & work item reference for every elevation/activation • Coming soon – support for Azure RBAC




how-to-enable-tde- yptography(v=vs. 110). aspx rchive/2015/04/28/client-
NO PURCHASE NECESSARY. Open only to event attendees. Winners must be present to win. Game ends May 9 th, 2015. For Official Rules, see The Cloud and Enterprise Lounge or myignite. com/challenge
http: //myignite. microsoft. com

- Slides: 49