Brief Overview of Cryptography Outline cryptographic primitives symmetric
Brief Overview of Cryptography
Outline § cryptographic primitives – symmetric key ciphers • block ciphers • stream ciphers – asymmetric key ciphers – cryptographic hash functions § protocol primitives – – block cipher operation modes “enveloping” message authentication codes digital signatures § key management protocols – session key establishment with symmetric and asymmetric key techniques – Diffie-Hellman key exchange and the man-in-the-middle attack – public key certification 2
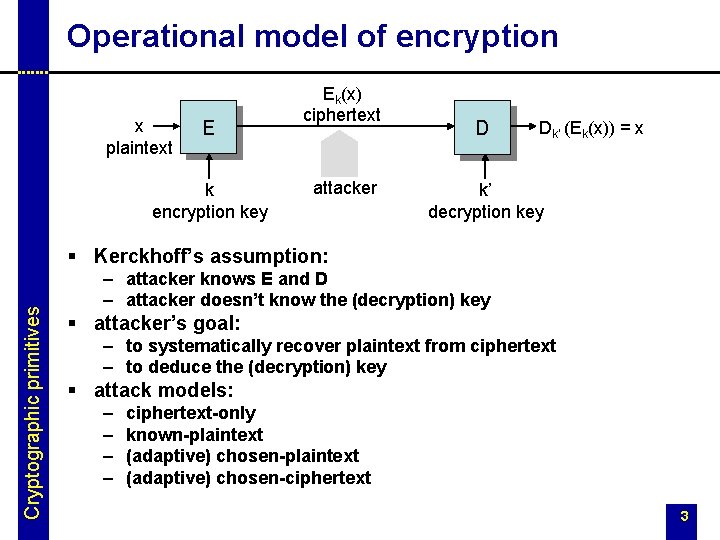
Operational model of encryption x plaintext E k encryption key Ek(x) ciphertext attacker D Dk’ (Ek(x)) = x k’ decryption key Cryptographic primitives § Kerckhoff’s assumption: – attacker knows E and D – attacker doesn’t know the (decryption) key § attacker’s goal: – to systematically recover plaintext from ciphertext – to deduce the (decryption) key § attack models: – – ciphertext-only known-plaintext (adaptive) chosen-ciphertext 3

Symmetric key encryption § it is easy to compute k from k’ (and vice versa) § often k = k’ § two main types: stream ciphers and block ciphers stream ciphers plaintext Cryptographic primitives . . . pseudo-random bit stream generator + . . . seed ciphertext block ciphers plaintext padding ciphertext block cipher key 4
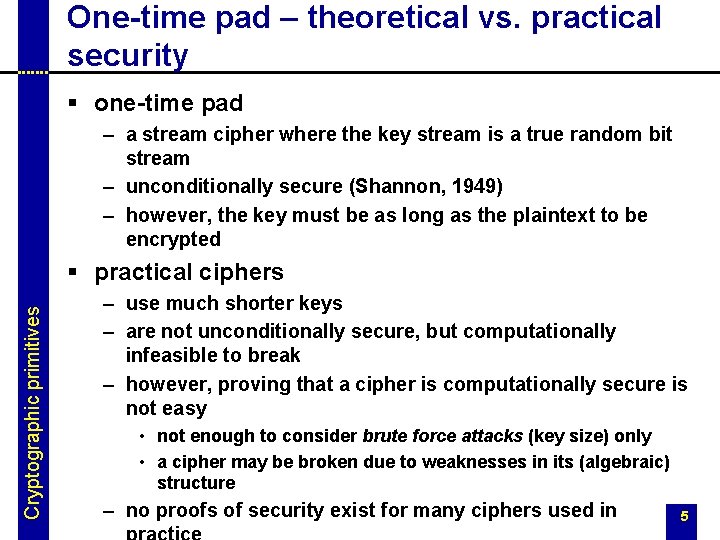
One-time pad – theoretical vs. practical security § one-time pad – a stream cipher where the key stream is a true random bit stream – unconditionally secure (Shannon, 1949) – however, the key must be as long as the plaintext to be encrypted Cryptographic primitives § practical ciphers – use much shorter keys – are not unconditionally secure, but computationally infeasible to break – however, proving that a cipher is computationally secure is not easy • not enough to consider brute force attacks (key size) only • a cipher may be broken due to weaknesses in its (algebraic) structure – no proofs of security exist for many ciphers used in 5
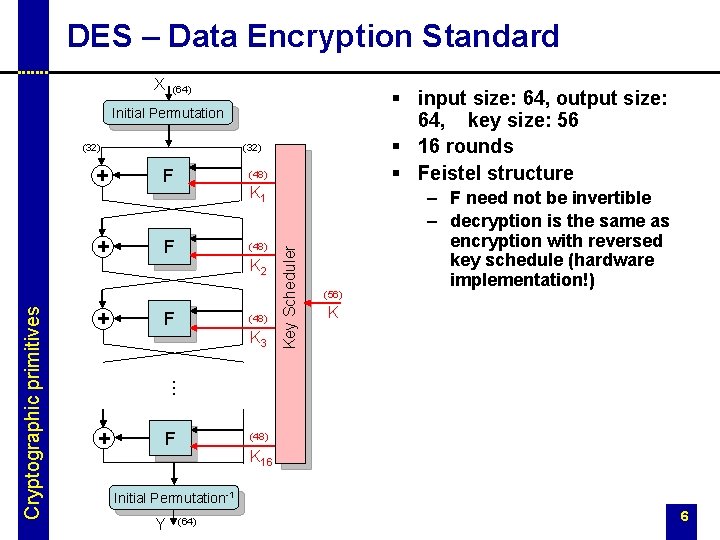
DES – Data Encryption Standard X (64) § input size: 64, output size: 64, key size: 56 § 16 rounds § Feistel structure Initial Permutation (32) F + F + F (48) K 1 (48) K 2 (48) K 3 Key Scheduler + (56) – F need not be invertible – decryption is the same as encryption with reversed key schedule (hardware implementation!) K … Cryptographic primitives (32) (48) K 16 Initial Permutation-1 Y (64) 6
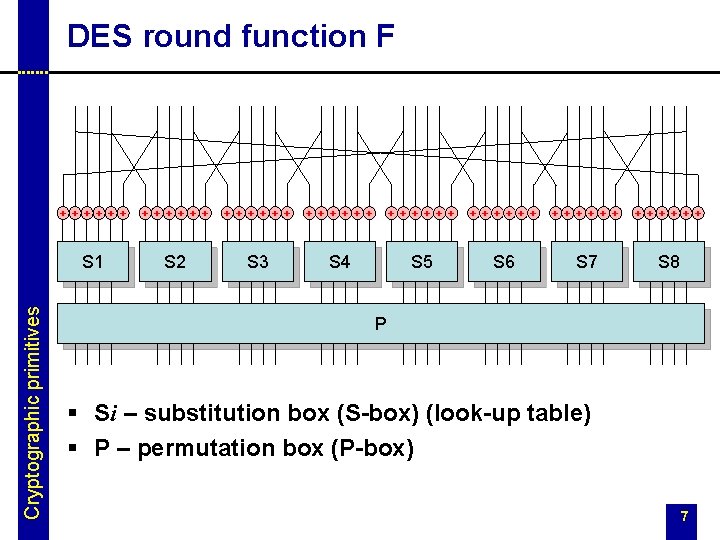
Cryptographic primitives DES round function F + + + + + + + + + + + + S 1 S 2 S 3 S 4 S 5 S 6 S 7 S 8 P § Si – substitution box (S-box) (look-up table) § P – permutation box (P-box) 7
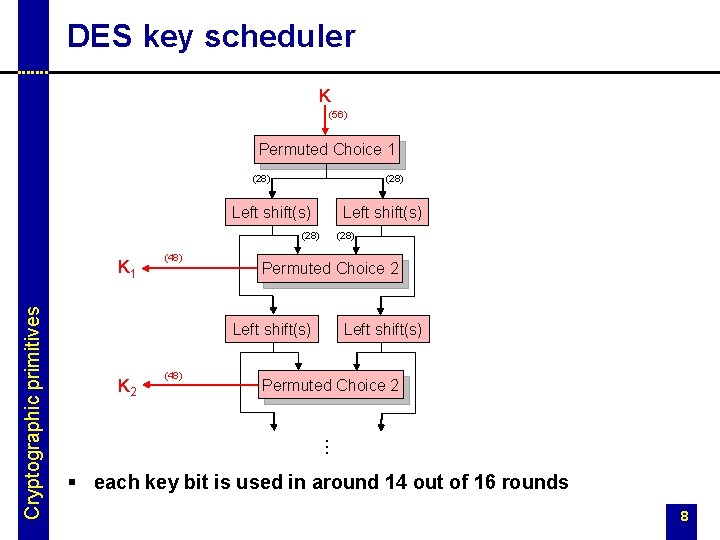
DES key scheduler K (56) Permuted Choice 1 (28) Left shift(s) (28) (48) Permuted Choice 2 Left shift(s) K 2 (48) Left shift(s) Permuted Choice 2 … Cryptographic primitives K 1 (28) § each key bit is used in around 14 out of 16 rounds 8
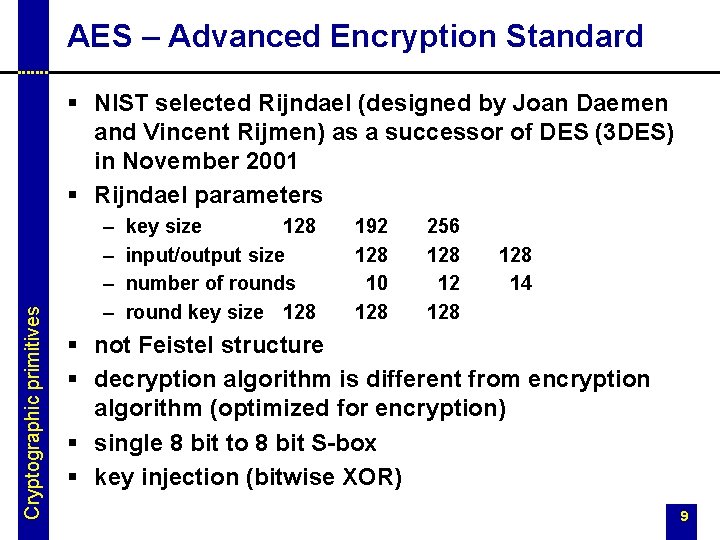
AES – Advanced Encryption Standard Cryptographic primitives § NIST selected Rijndael (designed by Joan Daemen and Vincent Rijmen) as a successor of DES (3 DES) in November 2001 § Rijndael parameters – – key size 128 input/output size number of rounds round key size 128 192 128 10 128 256 128 128 14 § not Feistel structure § decryption algorithm is different from encryption algorithm (optimized for encryption) § single 8 bit to 8 bit S-box § key injection (bitwise XOR) 9
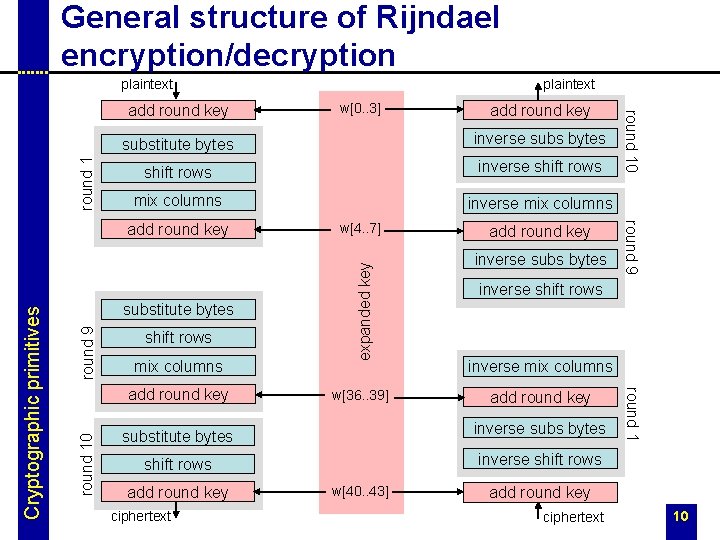
General structure of Rijndael encryption/decryption plaintext shift rows inverse shift rows mix columns inverse mix columns round 9 mix columns w[36. . 39] inverse subs bytes inverse shift rows inverse mix columns add round key substitute bytes inverse subs bytes shift rows inverse shift rows add round key ciphertext w[40. . 43] round 1 add round key round 9 shift rows w[4. . 7] expanded key round 1 inverse subs bytes substitute bytes round 10 add round key substitute bytes add round key Cryptographic primitives w[0. . 3] round 10 add round key plaintext add round key ciphertext 10
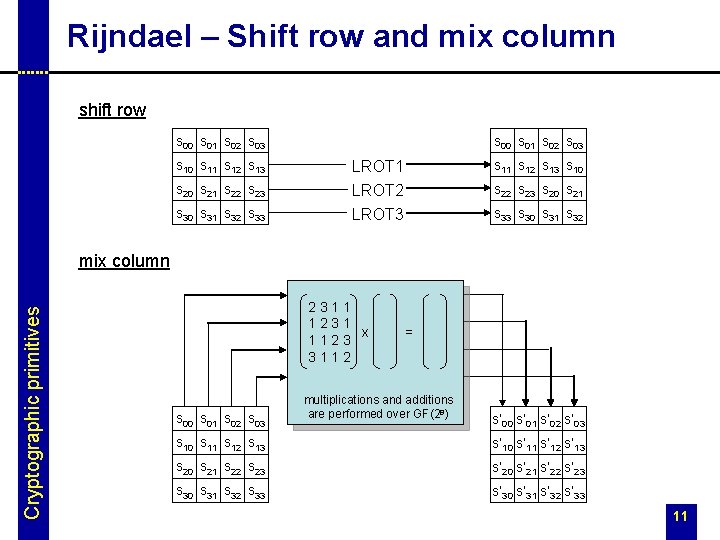
Rijndael – Shift row and mix column shift row s 00 s 01 s 02 s 03 s 10 s 11 s 12 s 13 s 20 s 21 s 22 s 23 s 30 s 31 s 32 s 33 s 00 s 01 s 02 s 03 s 11 s 12 s 13 s 10 LROT 1 LROT 2 LROT 3 s 22 s 23 s 20 s 21 s 33 s 30 s 31 s 32 Cryptographic primitives mix column 2311 1231 x 1123 3112 s 00 s 01 s 02 s 03 = multiplications and additions are performed over GF(28) s’ 00 s’ 01 s’ 02 s’ 03 s 10 s 11 s 12 s 13 s’ 10 s’ 11 s’ 12 s’ 13 s 20 s 21 s 22 s 23 s’ 20 s’ 21 s’ 22 s’ 23 s 30 s 31 s 32 s 33 s’ 30 s’ 31 s’ 32 s’ 33 11
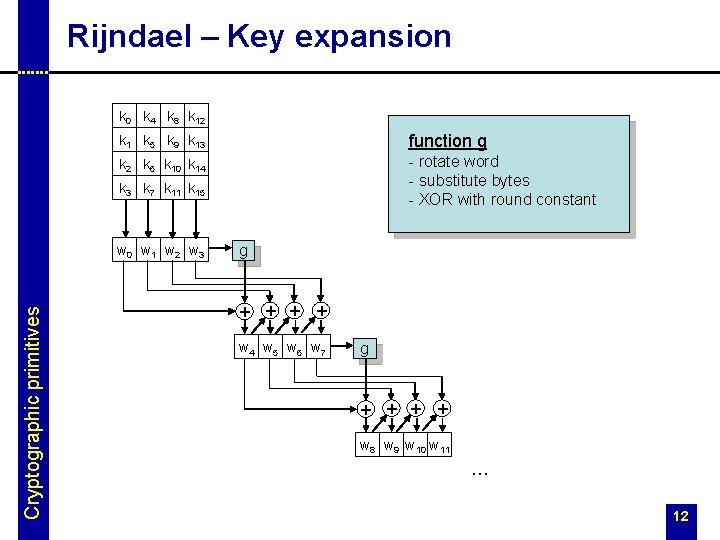
Rijndael – Key expansion k 0 k 4 k 8 k 12 k 1 k 5 k 9 k 13 function g k 2 k 6 k 10 k 14 - rotate word - substitute bytes - XOR with round constant k 3 k 7 k 11 k 15 Cryptographic primitives w 0 w 1 w 2 w 3 g + + w 4 w 5 w 6 w 7 g + + w 8 w 9 w 10 w 11 … 12
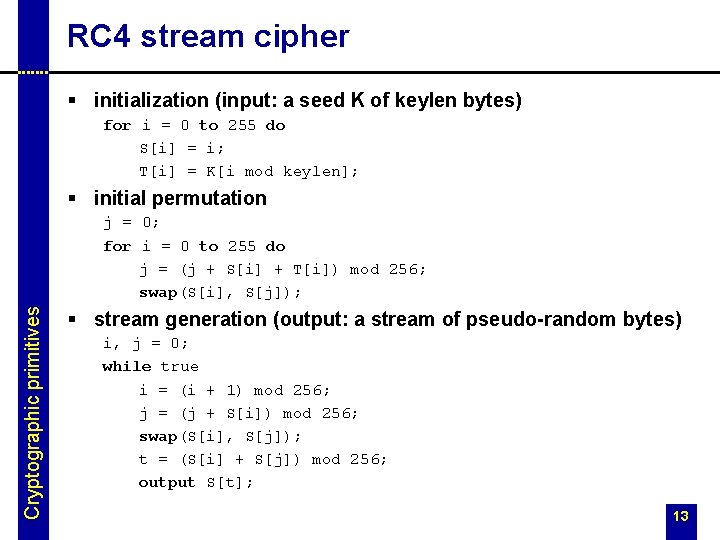
RC 4 stream cipher § initialization (input: a seed K of keylen bytes) for i = 0 to 255 do S[i] = i; T[i] = K[i mod keylen]; § initial permutation Cryptographic primitives j = 0; for i = 0 to 255 do j = (j + S[i] + T[i]) mod 256; swap(S[i], S[j]); § stream generation (output: a stream of pseudo-random bytes) i, j = 0; while true i = (i + 1) mod 256; j = (j + S[i]) mod 256; swap(S[i], S[j]); t = (S[i] + S[j]) mod 256; output S[t]; 13

Asymmetric key encryption x plaintext E Cryptographic primitives k encryption key Ek(x) ciphertext attacker D Dk’ (Ek(x)) = x k’ decryption key § breakthrough of Diffie and Hellman, 1976 § it is hard (computationally infeasible) to compute k’ from k § k can be made public (public-key cryptography) 14
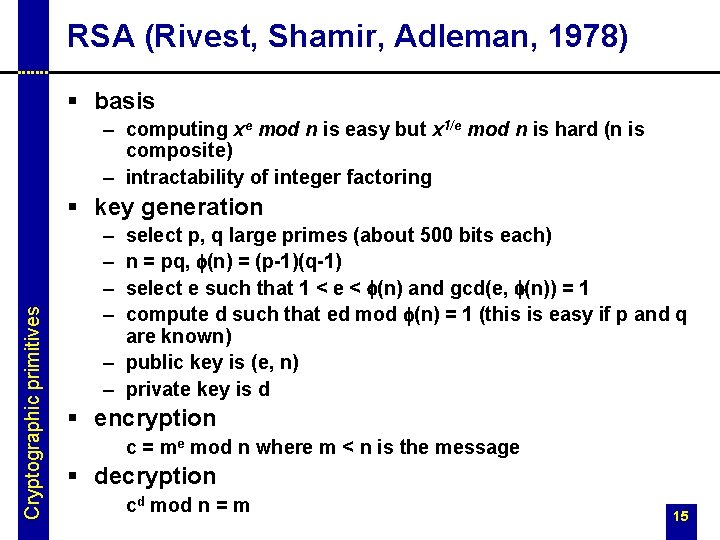
RSA (Rivest, Shamir, Adleman, 1978) § basis – computing xe mod n is easy but x 1/e mod n is hard (n is composite) – intractability of integer factoring Cryptographic primitives § key generation – – select p, q large primes (about 500 bits each) n = pq, f(n) = (p-1)(q-1) select e such that 1 < e < f(n) and gcd(e, f(n)) = 1 compute d such that ed mod f(n) = 1 (this is easy if p and q are known) – public key is (e, n) – private key is d § encryption c = me mod n where m < n is the message § decryption cd mod n = m 15
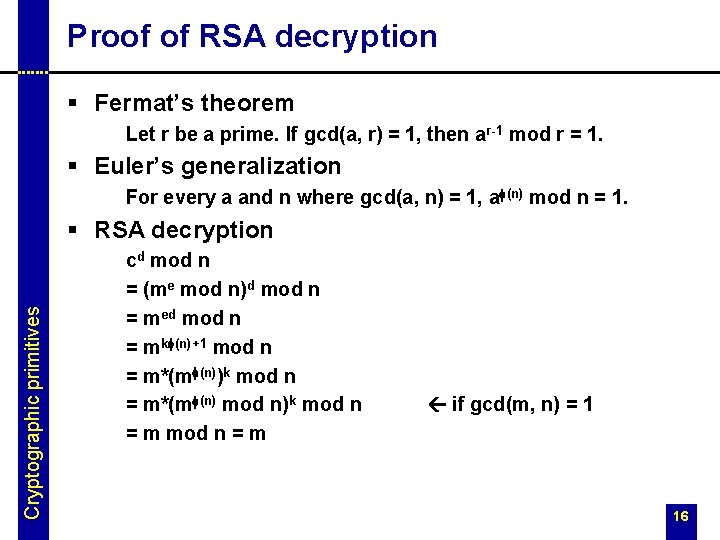
Proof of RSA decryption § Fermat’s theorem Let r be a prime. If gcd(a, r) = 1, then ar-1 mod r = 1. § Euler’s generalization For every a and n where gcd(a, n) = 1, af(n) mod n = 1. Cryptographic primitives § RSA decryption cd mod n = (me mod n)d mod n = med mod n = mkf(n)+1 mod n = m*(mf(n))k mod n = m*(mf(n) mod n)k mod n = m if gcd(m, n) = 1 16

Proof of RSA decryption cont’d § RSA decryption if gcd(m, n) > 1 – either p|m or q|m – assume without loss of generality that p|m – note that in this case, q|m cannot hold since otherwise m ³ pq = n – this means that gcd(m, q) = 1 cd mod p = med mod p = 0 cd mod q = med mod q = mk(p-1)(q-1)+1 mod q = m*(m (q-1)) k(p-1) mod q = m*(m (q-1) mod q) k(p-1) mod q = m mod q p, q|(cd – m) cd – m = spq = sn cd = sn + m cd mod n = m 17
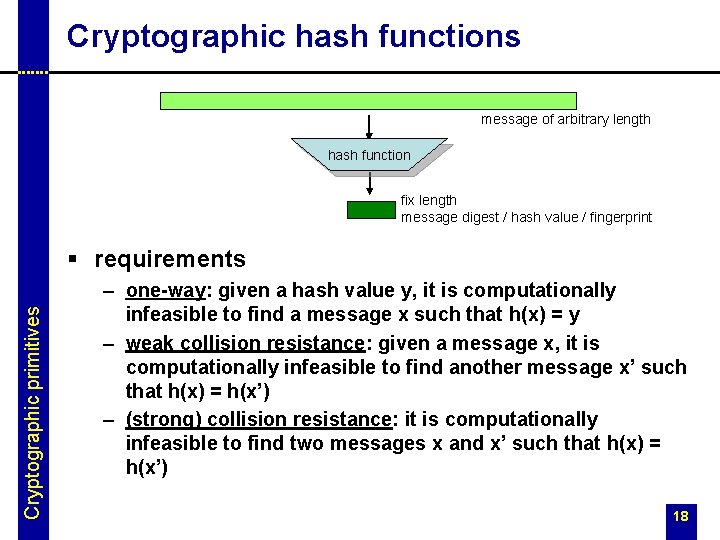
Cryptographic hash functions message of arbitrary length hash function fix length message digest / hash value / fingerprint Cryptographic primitives § requirements – one-way: given a hash value y, it is computationally infeasible to find a message x such that h(x) = y – weak collision resistance: given a message x, it is computationally infeasible to find another message x’ such that h(x) = h(x’) – (strong) collision resistance: it is computationally infeasible to find two messages x and x’ such that h(x) = h(x’) 18
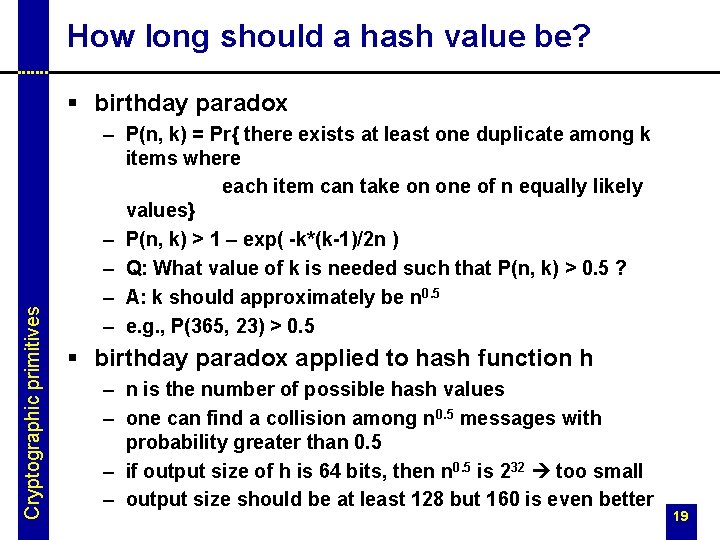
How long should a hash value be? Cryptographic primitives § birthday paradox – P(n, k) = Pr{ there exists at least one duplicate among k items where each item can take on one of n equally likely values} – P(n, k) > 1 – exp( -k*(k-1)/2 n ) – Q: What value of k is needed such that P(n, k) > 0. 5 ? – A: k should approximately be n 0. 5 – e. g. , P(365, 23) > 0. 5 § birthday paradox applied to hash function h – n is the number of possible hash values – one can find a collision among n 0. 5 messages with probability greater than 0. 5 – if output size of h is 64 bits, then n 0. 5 is 232 too small – output size should be at least 128 but 160 is even better 19
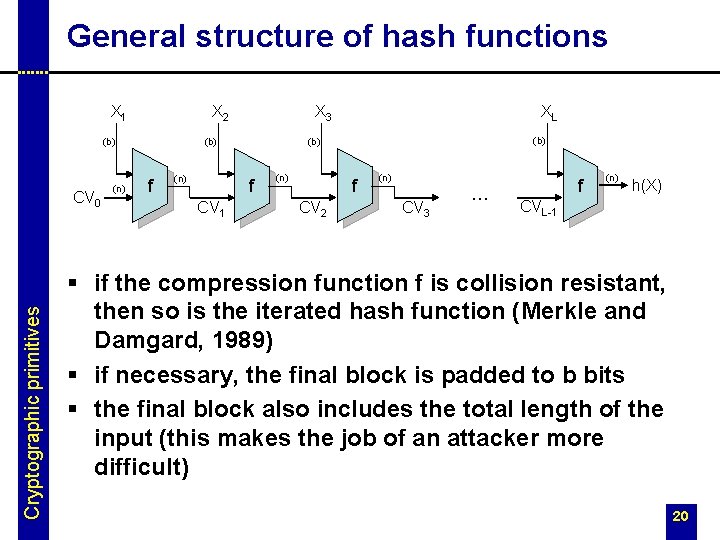
General structure of hash functions X 2 X 1 (b) Cryptographic primitives CV 0 (n) f (n) (b) f CV 1 XL X 3 (n) f CV 2 (n) CV 3 … f (n) h(X) CVL-1 § if the compression function f is collision resistant, then so is the iterated hash function (Merkle and Damgard, 1989) § if necessary, the final block is padded to b bits § the final block also includes the total length of the input (this makes the job of an attacker more difficult) 20
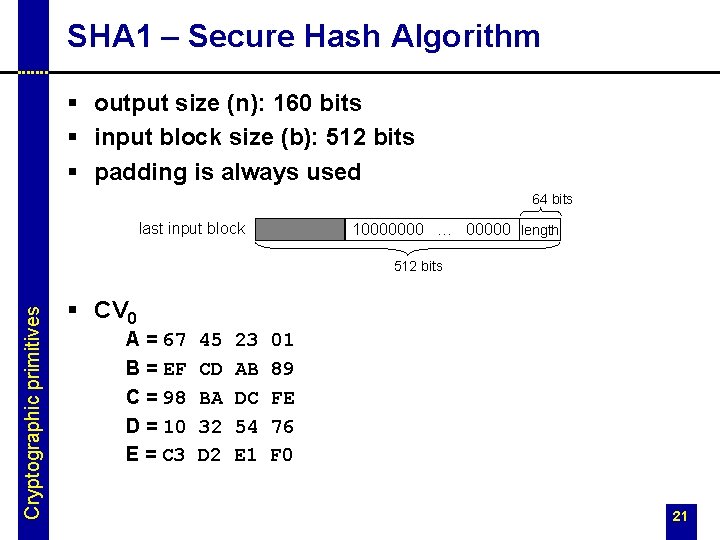
SHA 1 – Secure Hash Algorithm § output size (n): 160 bits § input block size (b): 512 bits § padding is always used 64 bits last input block 10000000 … 00000 length Cryptographic primitives 512 bits § CV 0 A = 67 B = EF C = 98 D = 10 E = C 3 45 CD BA 32 D 2 23 AB DC 54 E 1 01 89 FE 76 F 0 21
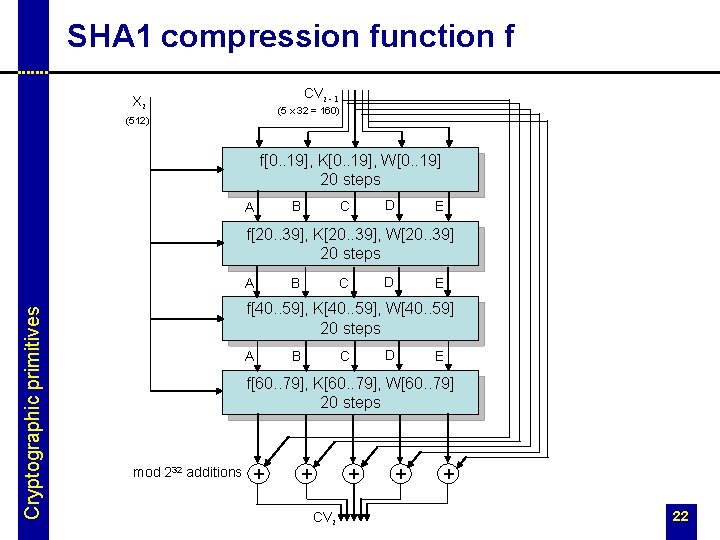
SHA 1 compression function f CVi - 1 Xi (5 x 32 = 160) (512) f[0. . 19], K[0. . 19], W[0. . 19] 20 steps A B C D E f[20. . 39], K[20. . 39], W[20. . 39] 20 steps Cryptographic primitives A B C D E f[40. . 59], K[40. . 59], W[40. . 59] 20 steps A B C D E f[60. . 79], K[60. . 79], W[60. . 79] 20 steps mod 232 additions + + + CVi + + 22
![SHA 1 compression function f cont’d A B C D + f[t] LROT 30 SHA 1 compression function f cont’d A B C D + f[t] LROT 30](http://slidetodoc.com/presentation_image_h/d3b20ef4b0fb960b1e8b09354191a8cc/image-23.jpg)
SHA 1 compression function f cont’d A B C D + f[t] LROT 30 Cryptographic primitives mod 232 additions + LROT 5 A E B C D + W[t] + K[t] E 23
 t = 0. . SHA 1 compression function f cont’d § f[t](B, C, D) t = 0. .](http://slidetodoc.com/presentation_image_h/d3b20ef4b0fb960b1e8b09354191a8cc/image-24.jpg)
SHA 1 compression function f cont’d § f[t](B, C, D) t = 0. . 19 f[t](B, C, D) = (B Ù C) Ú (ØB Ù D) t = 20. . 39 f[t](B, C, D) = B Å C Å D t = 40. . 59 f[t](B, C, D) = (B Ù C) Ú (B Ù D) Ú (C Ù D) t = 60. . 79 f[t](B, C, D) = B Å C Å D Cryptographic primitives § W[t] W[0. . 15] = Xi t = 16. . 79 W[t-3]) W[t] = LROT 1(W[t-16] Å W[t-14] Å W[t-8] Å § K[t] t = 0. . 19 K[t] = 5 A 82 79 t = 20. . 39 K[t] = 6 E t = 40. . 59 K[t] = 8 F t = 60. . 79 K[t] = CA 99 D 9 EB A 1 1 B BC DC 62 C 1 D 6 [230 x 21/2] [230 x 31/2] [230 x 51/2] [230 x 101/2] 24
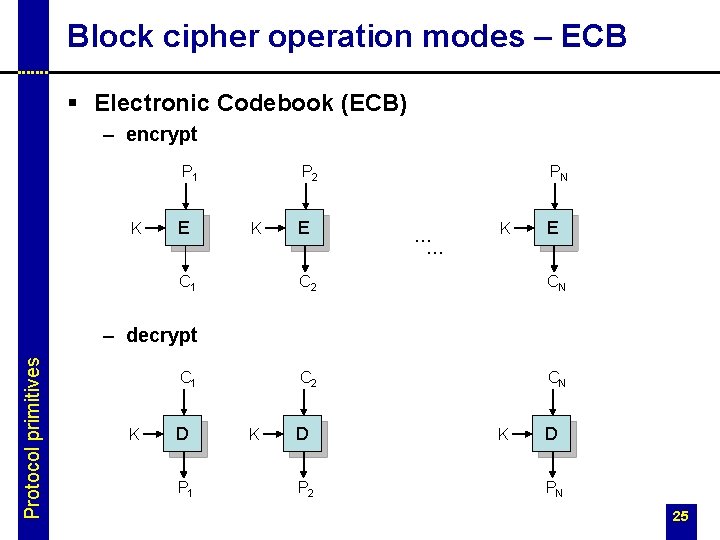
Block cipher operation modes – ECB § Electronic Codebook (ECB) – encrypt P 1 K E P 2 K C 1 E PN … … K E C 2 CN Protocol primitives – decrypt C 1 K D P 2 K D PN 25
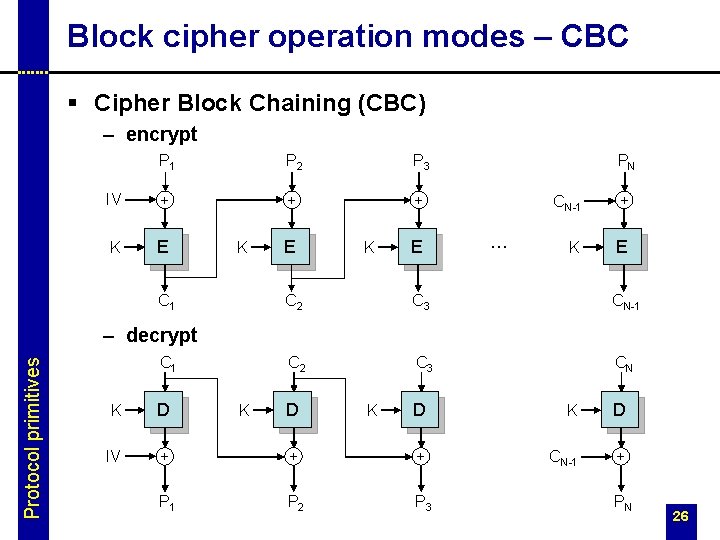
Block cipher operation modes – CBC § Cipher Block Chaining (CBC) – encrypt P 1 P 2 P 3 IV + + + K E K C 1 E K E PN … CN-1 + K E C 2 C 3 CN-1 C 2 C 3 CN Protocol primitives – decrypt C 1 K D IV + P 1 K D D K D + + CN-1 + P 2 P 3 K PN 26
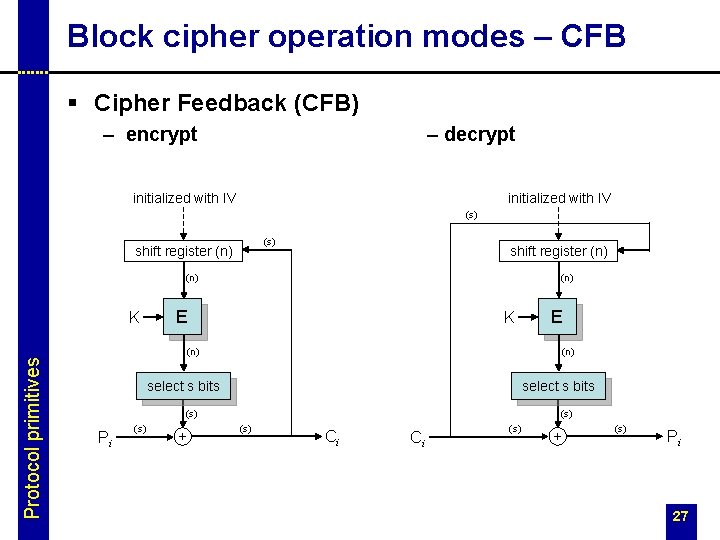
Block cipher operation modes – CFB § Cipher Feedback (CFB) – encrypt – decrypt initialized with IV (s) shift register (n) (n) Protocol primitives K E K (n) select s bits (s) Pi (s) + E (s) Ci Ci (s) + (s) Pi 27
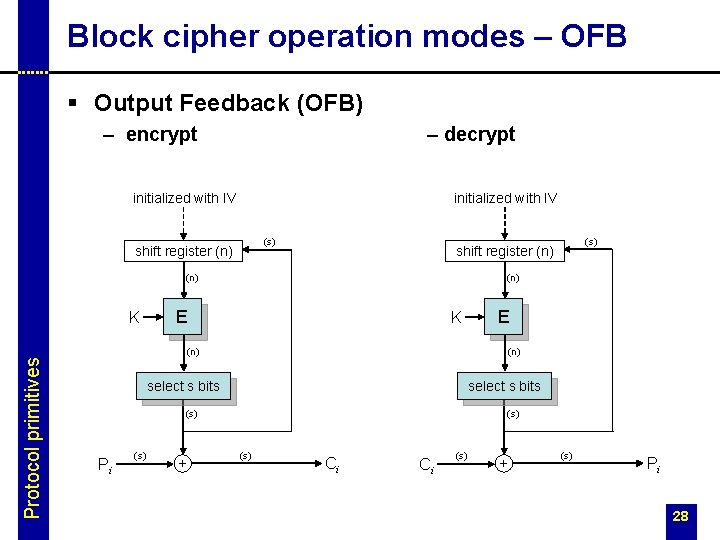
Block cipher operation modes – OFB § Output Feedback (OFB) – encrypt – decrypt initialized with IV (s) shift register (n) (n) Protocol primitives K E K select s bits (s) (s) + E (n) Pi (s) shift register (n) (s) Ci Ci (s) + (s) Pi 28
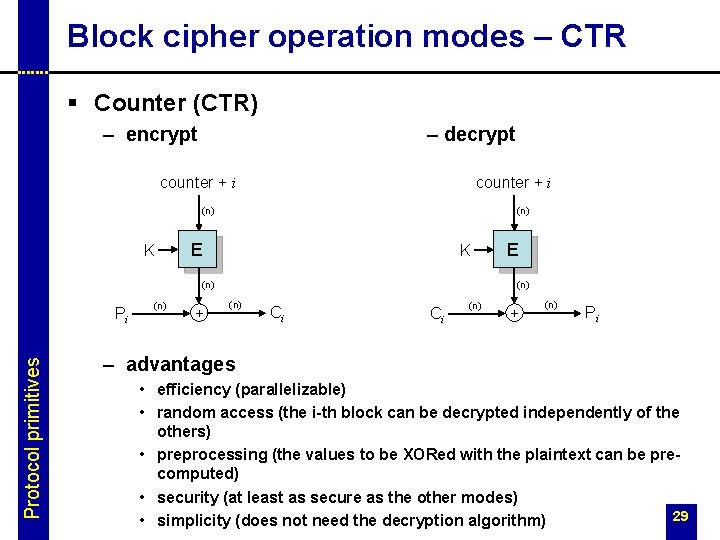
Block cipher operation modes – CTR § Counter (CTR) – encrypt – decrypt counter + i (n) K (n) E K (n) Protocol primitives Pi (n) + E (n) Ci Ci (n) + (n) Pi – advantages • efficiency (parallelizable) • random access (the i-th block can be decrypted independently of the others) • preprocessing (the values to be XORed with the plaintext can be precomputed) • security (at least as secure as the other modes) 29 • simplicity (does not need the decryption algorithm)
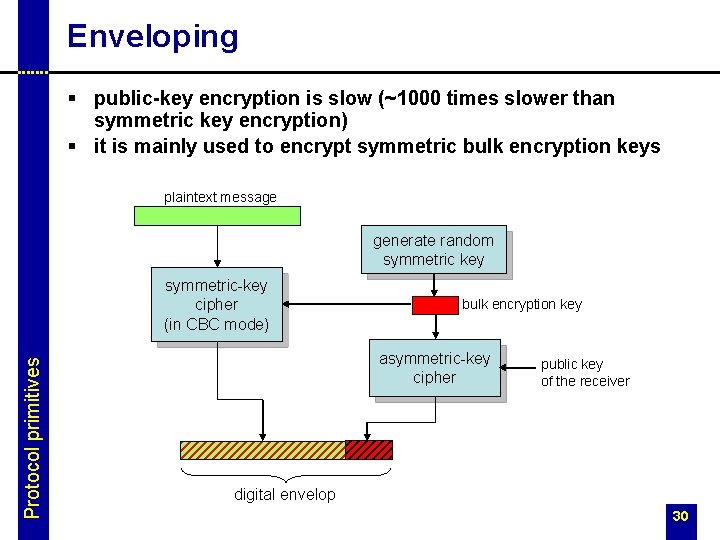
Enveloping § public-key encryption is slow (~1000 times slower than symmetric key encryption) § it is mainly used to encrypt symmetric bulk encryption keys plaintext message generate random symmetric key Protocol primitives symmetric-key cipher (in CBC mode) bulk encryption key asymmetric-key cipher public key of the receiver digital envelop 30
Message Authentication Codes (MAC) § used to protect the integrity of messages § also called cryptographic checksums § computation of a MAC involves a secret (shared key) § can be based on an encryption function E Protocol primitives Y 1 = EK(X 1) Yi = EK(Xi + Yi-1) MACK(X) = Ylast § or a hash function h MACK(X) = h(X|K) § or both MACK(X) = EK(h(X)) 31
HMAC Protocol primitives § definition HMACK(X) = h( (K+ + opad) | h( (K+ + ipad) | X ) ) where – h is a hash function with input block size b and output size n – K+ is K padded with 0 s on the left to obtain a length of b bits – ipad is 00110110 repeated b/8 times – opad is 01011100 repeated b/8 times – + is XOR and | is concatenation § design objectives – – to use available hash functions easy replacement of the embedded hash function preserve performance of the original hash function handle keys in a simple way 32
Digital signatures § similar to MACs but – unforgeable by the receiver – verifiable by a third party Protocol primitives § used for message authentication and nonrepudiation (of message origin) § based on public-key cryptography – signature generation is based on the private key of the sender – signature verification is based on the public key of the sender § example: RSA based digital signature – public key: (e, n); private key: (d, n) – signature generation (input: m; output: s) s(m) = md mod n – signature verification (input: s, m; output: yes/no) 33
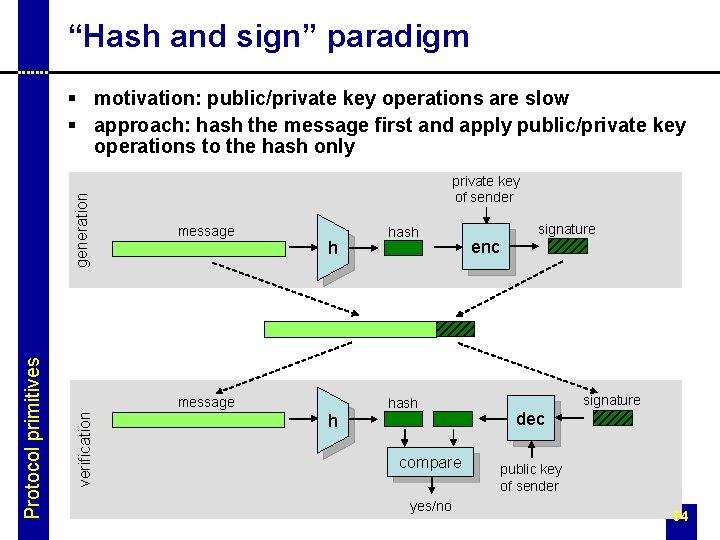
“Hash and sign” paradigm private key of sender message h message verification Protocol primitives generation § motivation: public/private key operations are slow § approach: hash the message first and apply public/private key operations to the hash only h hash compare yes/no enc signature dec public key of sender 34
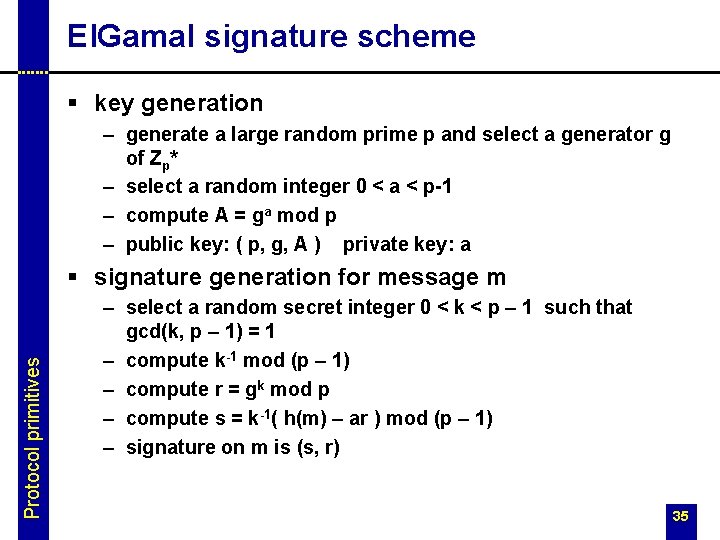
El. Gamal signature scheme § key generation – generate a large random prime p and select a generator g of Zp* – select a random integer 0 < a < p-1 – compute A = ga mod p – public key: ( p, g, A ) private key: a Protocol primitives § signature generation for message m – select a random secret integer 0 < k < p – 1 such that gcd(k, p – 1) = 1 – compute k-1 mod (p – 1) – compute r = gk mod p – compute s = k-1( h(m) – ar ) mod (p – 1) – signature on m is (s, r) 35
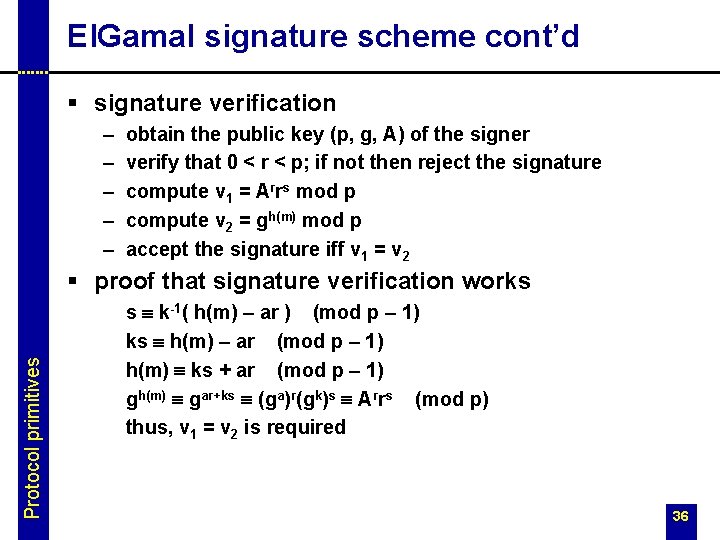
El. Gamal signature scheme cont’d § signature verification – – – obtain the public key (p, g, A) of the signer verify that 0 < r < p; if not then reject the signature compute v 1 = Arrs mod p compute v 2 = gh(m) mod p accept the signature iff v 1 = v 2 Protocol primitives § proof that signature verification works s º k-1( h(m) – ar ) (mod p – 1) ks º h(m) – ar (mod p – 1) h(m) º ks + ar (mod p – 1) gh(m) º gar+ks º (ga)r(gk)s º Arrs (mod p) thus, v 1 = v 2 is required 36
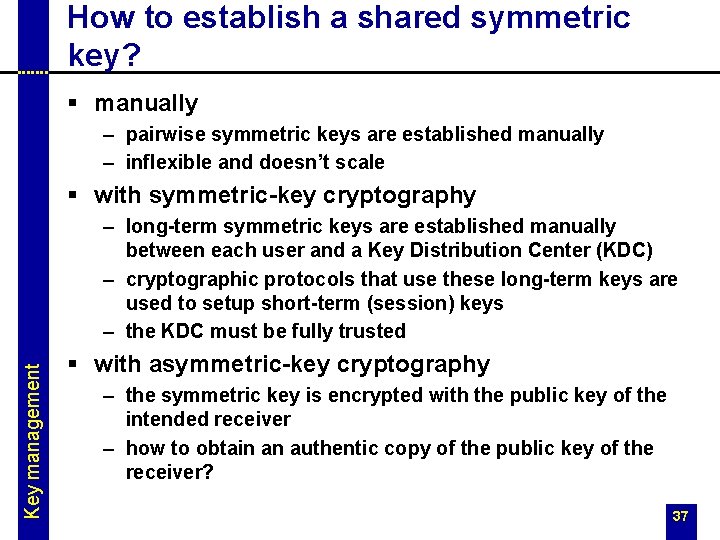
How to establish a shared symmetric key? § manually – pairwise symmetric keys are established manually – inflexible and doesn’t scale § with symmetric-key cryptography Key management – long-term symmetric keys are established manually between each user and a Key Distribution Center (KDC) – cryptographic protocols that use these long-term keys are used to setup short-term (session) keys – the KDC must be fully trusted § with asymmetric-key cryptography – the symmetric key is encrypted with the public key of the intended receiver – how to obtain an authentic copy of the public key of the receiver? 37
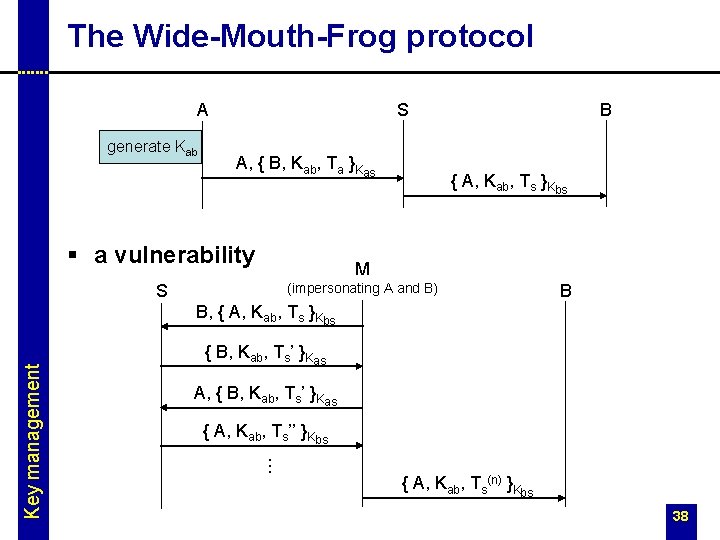
The Wide-Mouth-Frog protocol A generate Kab S A, { B, Kab, Ta }Kas § a vulnerability B { A, Kab, Ts }Kbs M (impersonating A and B) S B { B, Kab, Ts’ }Kas A, { B, Kab, Ts’ }Kas { A, Kab, Ts’’ }Kbs . . . Key management B, { A, Kab, Ts }Kbs { A, Kab, Ts(n) }Kbs 38
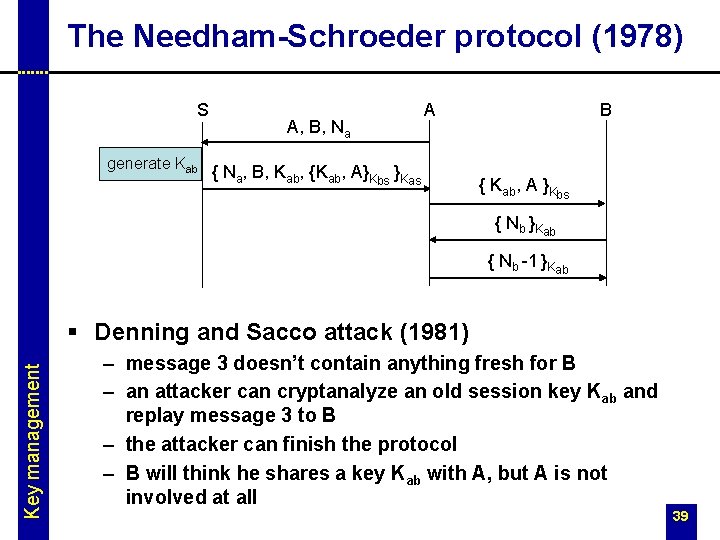
The Needham-Schroeder protocol (1978) S generate Kab A, B, Na A { Na, B, Kab, {Kab, A}Kbs }Kas B { Kab, A }Kbs { Nb }Kab { Nb -1 }Kab Key management § Denning and Sacco attack (1981) – message 3 doesn’t contain anything fresh for B – an attacker can cryptanalyze an old session key Kab and replay message 3 to B – the attacker can finish the protocol – B will think he shares a key Kab with A, but A is not involved at all 39
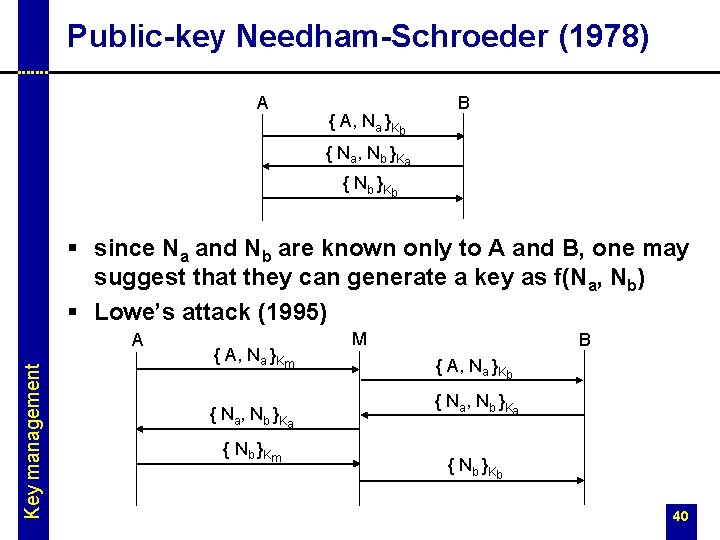
Public-key Needham-Schroeder (1978) A { A, Na }Kb B { Na, Nb }Ka { Nb }Kb § since Na and Nb are known only to A and B, one may suggest that they can generate a key as f(Na, Nb) § Lowe’s attack (1995) Key management A { A, Na }Km { Na, Nb }Ka { Nb }Km M B { A, Na }Kb { Na, Nb }Ka { Nb }Kb 40
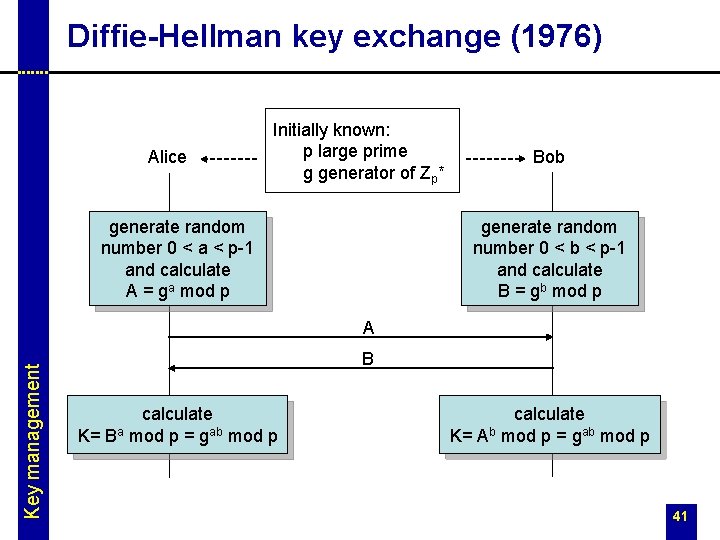
Diffie-Hellman key exchange (1976) Alice Initially known: p large prime g generator of Zp* generate random number 0 < a < p-1 and calculate A = ga mod p Bob generate random number 0 < b < p-1 and calculate B = gb mod p Key management A B calculate K= Ba mod p = gab mod p calculate K= Ab mod p = gab mod p 41
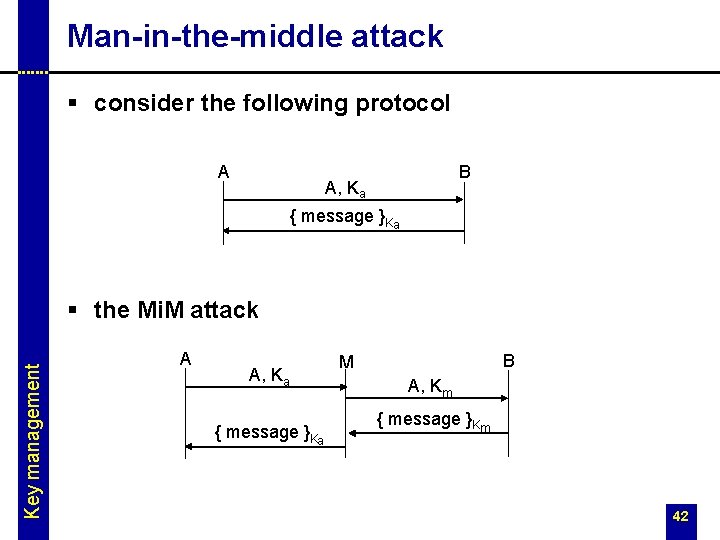
Man-in-the-middle attack § consider the following protocol A B A, Ka { message }Ka Key management § the Mi. M attack A A, Ka { message }Ka B M A, Km { message }Km 42
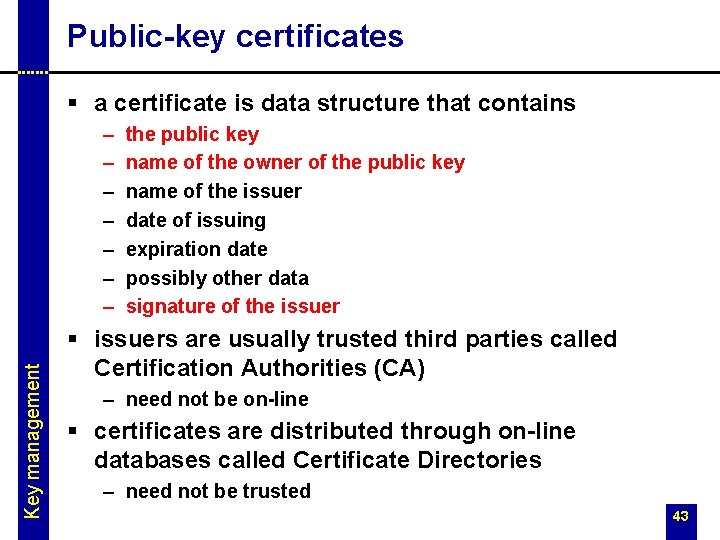
Public-key certificates § a certificate is data structure that contains Key management – – – – the public key name of the owner of the public key name of the issuer date of issuing expiration date possibly other data signature of the issuer § issuers are usually trusted third parties called Certification Authorities (CA) – need not be on-line § certificates are distributed through on-line databases called Certificate Directories – need not be trusted 43
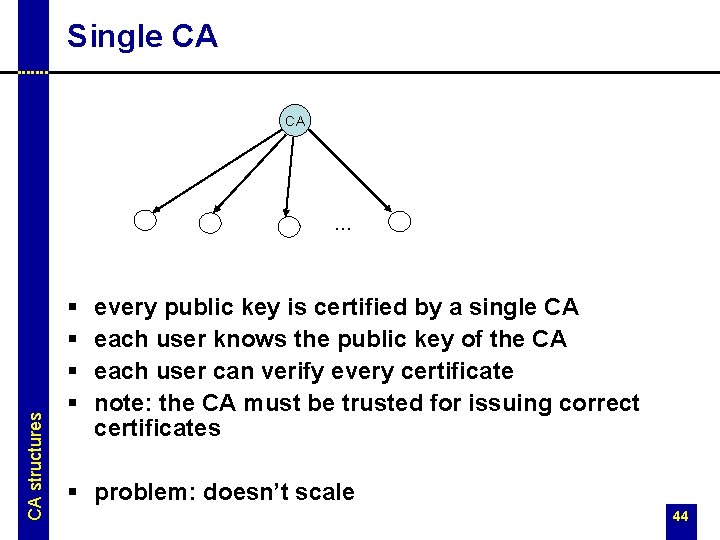
Single CA CA CA structures … § § every public key is certified by a single CA each user knows the public key of the CA each user can verify every certificate note: the CA must be trusted for issuing correct certificates § problem: doesn’t scale 44
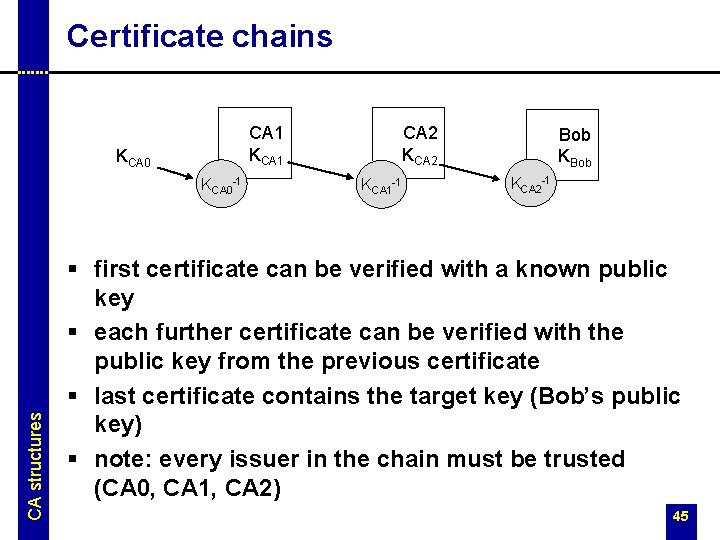
Certificate chains KCA 0 -1 CA structures CA 2 KCA 2 CA 1 KCA 1 -1 Bob KCA 2 -1 § first certificate can be verified with a known public key § each further certificate can be verified with the public key from the previous certificate § last certificate contains the target key (Bob’s public key) § note: every issuer in the chain must be trusted (CA 0, CA 1, CA 2) 45
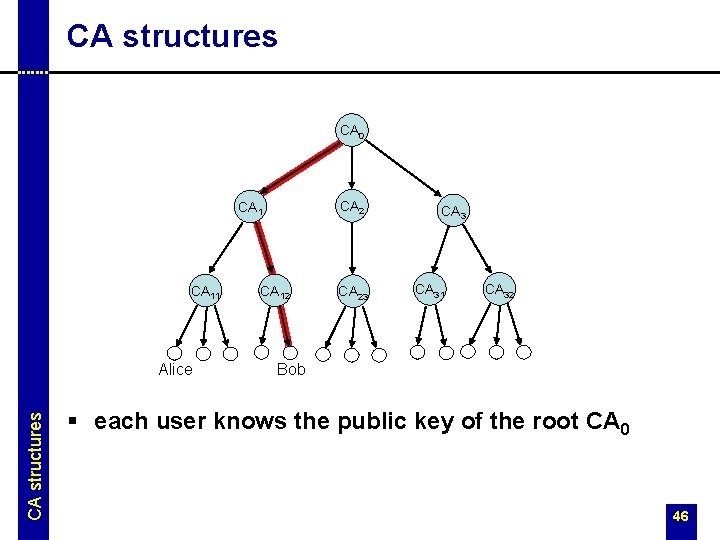
CA structures CA 0 CA 2 CA 11 CA structures Alice CA 12 CA 23 CA 31 CA 32 Bob § each user knows the public key of the root CA 0 46
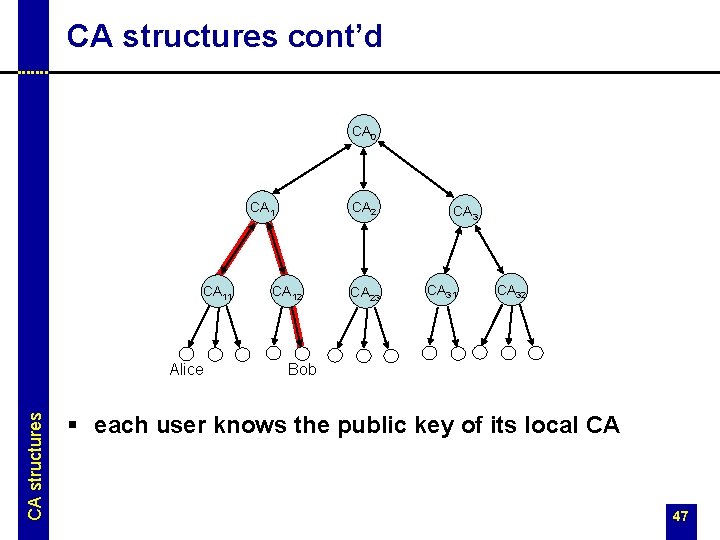
CA structures cont’d CA 0 CA 2 CA 11 CA structures Alice CA 12 CA 23 CA 31 CA 32 Bob § each user knows the public key of its local CA 47
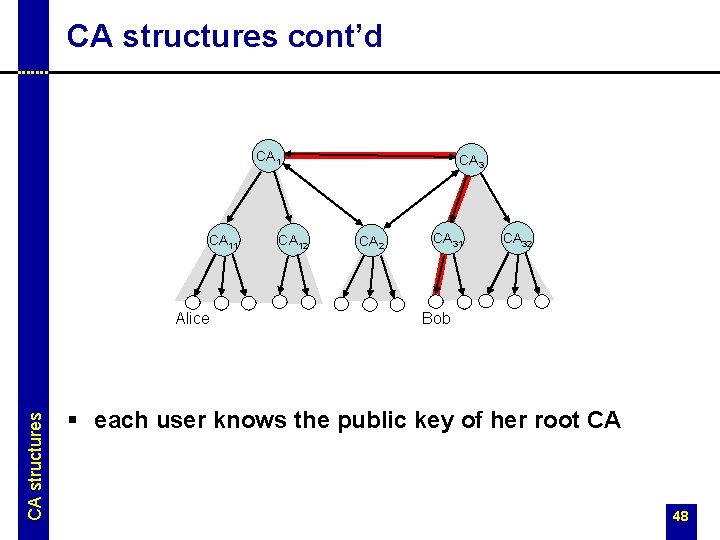
CA structures cont’d CA 11 CA structures Alice CA 12 CA 3 CA 2 CA 31 CA 32 Bob § each user knows the public key of her root CA 48
- Slides: 48