Bridging Broadcast Scenarios Carlos Ribeiro CTBC Telecom Bridging
Bridging & Broadcast Scenarios Carlos Ribeiro CTBC Telecom
Bridging on the Access Network • Access network topology – The Service Provider need to have full control over the access network topology – For the Spanning Tree Protocol, this means that the SP must always be the root of the spanning tree topology • Nightmare scenarios – Multiple EFM-based SP connected together – Multihomed EFM accesses – Who is in charge of the resulting network?
Single Copy Broadcast • Desired behavior – Allows for very efficient use of bandwidth – Well suited for multimedia applications • Digital video distribution • Digital audio distribution • Conflicts with P 2 P emulation mode – Broadcast frames need to be copied for every user! • Potential issues – Spanning Tree Topology, broadcast floods
Case studies • Objectives – Show do some proposed topologies behave with regards to single copy broadcast • Assumptions – EPON works in P 2 P emulation mode – Single Copy Broadcast is enabled • A single frame is sent to all stations downstream – No special ‘routing’ behavior for SCB • SCB is always on the downstream; upstream traffic is always subject to P 2 P emulation rules • If a P 2 P emulation port is disabled by the STP protocol, then it will discard all broadcast frames received
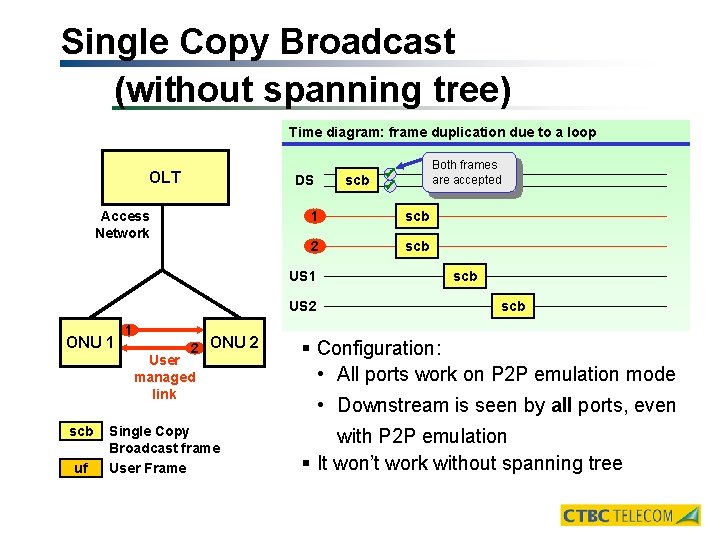
Single Copy Broadcast (without spanning tree) Time diagram: frame duplication due to a loop OLT DS Access Network 1 scb 2 scb US 1 US 2 ONU 1 1 2 ONU 2 User managed link scb uf Single Copy Broadcast frame User Frame scb Both frames are accepted scb § Configuration: • All ports work on P 2 P emulation mode • Downstream is seen by all ports, even with P 2 P emulation § It won’t work without spanning tree
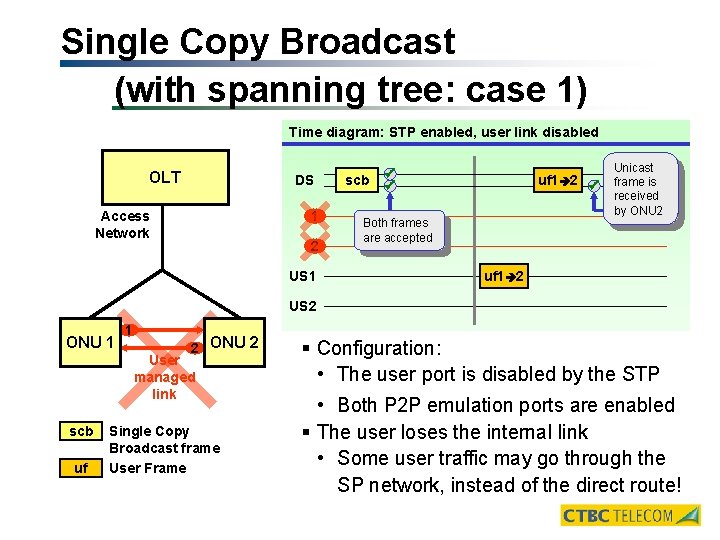
Single Copy Broadcast (with spanning tree: case 1) Time diagram: STP enabled, user link disabled OLT DS 1 Access Network 2 US 1 scb uf 1 2 Both frames are accepted Unicast frame is received by ONU 2 uf 1 2 US 2 ONU 1 1 2 ONU 2 User managed link scb uf Single Copy Broadcast frame User Frame § Configuration: • The user port is disabled by the STP • Both P 2 P emulation ports are enabled § The user loses the internal link • Some user traffic may go through the SP network, instead of the direct route!
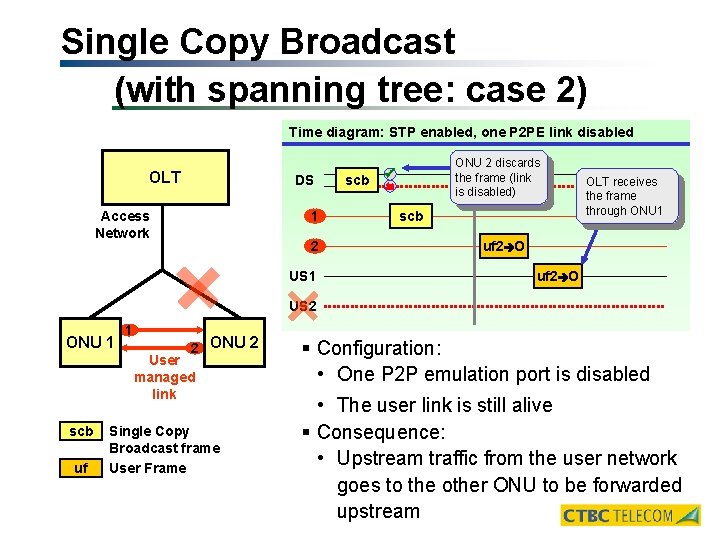
Single Copy Broadcast (with spanning tree: case 2) Time diagram: STP enabled, one P 2 PE link disabled OLT DS 1 Access Network 2 US 1 scb ONU 2 discards the frame (link is disabled) scb OLT receives the frame through ONU 1 uf 2 O US 2 ONU 1 1 2 ONU 2 User managed link scb uf Single Copy Broadcast frame User Frame § Configuration: • One P 2 P emulation port is disabled • The user link is still alive § Consequence: • Upstream traffic from the user network goes to the other ONU to be forwarded upstream
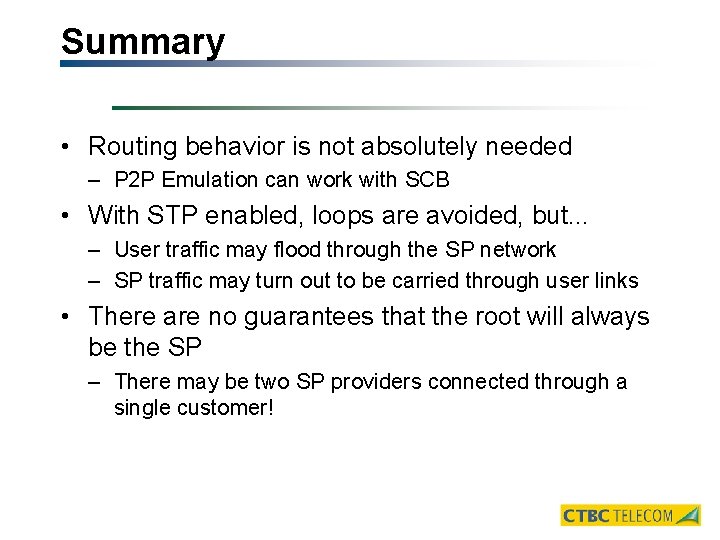
Summary • Routing behavior is not absolutely needed – P 2 P Emulation can work with SCB • With STP enabled, loops are avoided, but. . . – User traffic may flood through the SP network – SP traffic may turn out to be carried through user links • There are no guarantees that the root will always be the SP – There may be two SP providers connected through a single customer!
Additional ideas • Force VLANs in the access network – All ports should apply SP-specific VLAN tags – All frames which enter the access network with VLAN tags applied should be tunneled with ‘VLAN-inside-VLAN’, or 802. 1 q inside 802. 1 q – This implementation resembles a ‘administrative domain’ paradigm, as already implemented for routed networks – Comment: to require 802. 1 q implementation may be beyond 802. 3 ah scope; but so is the requirement to use a router for SE support. • Special MAC addresses – Reserve MAC addresses for the applications that use single copy broadcast on the downstream – Apply filtering to avoid loops on the network
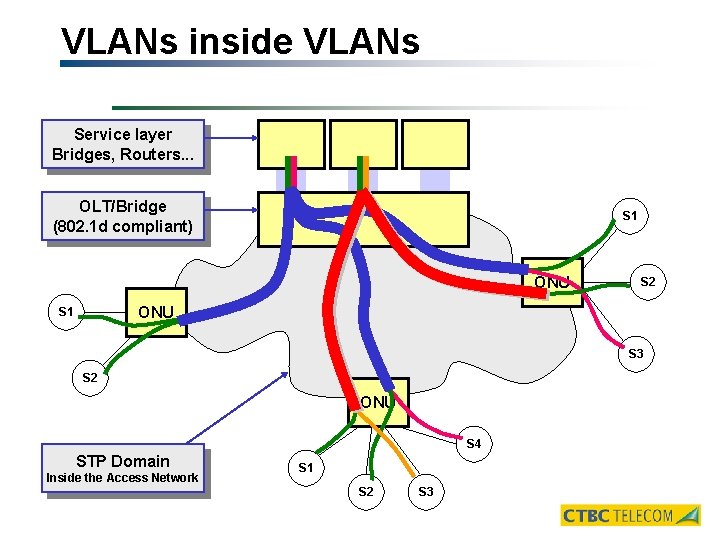
VLANs inside VLANs Service layer Bridges, Routers. . . OLT/Bridge (802. 1 d compliant) S 1 ONU S 2 ONU S 1 S 3 S 2 ONU S 4 STP Domain Inside the Access Network S 1 S 2 S 3
VLANs inside VLANs SP Requirements • A standard way to implement VLAN-inside-VLAN – Encapsulation levels: • 1 level of encapsulation only • ‘n’ levels of encapsulation • Arbitrary encapsulation – Maximum frame size (depends on the maximum encapsulation allowed) • A standard way to provision and manage VLANs – Standard MIBs – Standard VLAN-to-VLAN mapping features
- Slides: 11