BOTNETS A K A ZOMBIE COMPUTING Presented by
BOTNETS A. K. A ZOMBIE COMPUTING Presented by : Matthew Sulkosky COSC 316 (Host Security)
ROADMAP • What is a Bot? • Methods of Infection • How Botnets Work • Ramifications • Methods of Protection • Case Study : Conficker Worm • Implications
WHAT IS A BOT? • A “Bot” is a type of malware that is designed to allow an attacker control over your system. Many refer the infected machines as “zombies”, because they only do the attacker’s bidding. • Bots rarely are singular, usually they are part of a network of Infected computers called a Bot. Net. • Botnets can vary in size from hundreds of bots to millions of bots. The Conficker Worm has formed a Botnet is estimated between 9 to 12 million in size. • Warning signs include: computer slowdown, mysterious messages, crashing, etc.
METHODS OF INFECTION • There are numerous ways to be infected. A common method is for an attacker to place a Trojan horse on the machine, then use it to install the bot. • There are numerous ways for a computer to become infected, other form of include: • Email Attachments • Zero day exploits • Social Engineering • Web Exploits • File Sharing
HOW THE BOTNETS WORK • The attacker who controls the bots or botnet are called botherder or controller. • Often an application, client program, is used by the controller to issue commands to the botnet. • This allows for efficient operation of the botnets, and commands to be issued to one or more of the bots at a time. • The connections between the bots and controller is known as a command-control infrastructure.
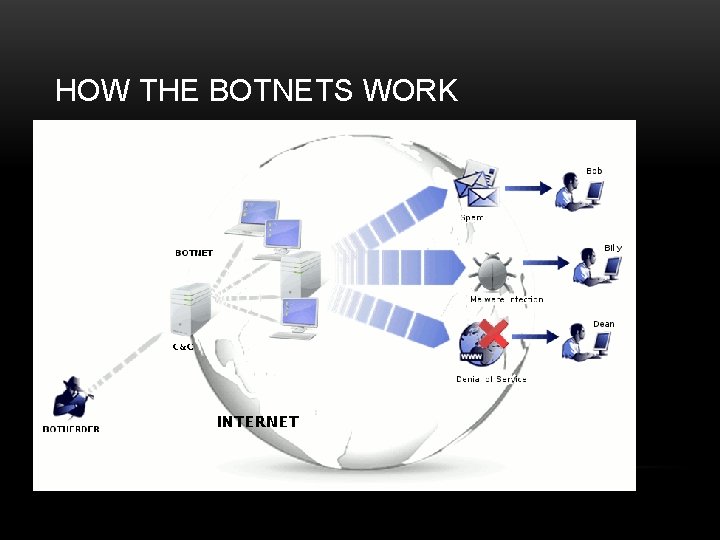
HOW THE BOTNETS WORK
IMPLICATIONS • Botnets can be used for a variety of purposes. • In my opinion they are one of the most dynamic forms of malware. • Since bots follow the commands of a central attacker, they can do anything that a hacker can think of. • The common uses fit into the categories of : Cyber attacks, Spam generators, Distributors, Storage, or Fraud.
IMPLICATIONS • Cyber attacks such as Denial of Service in order to extort money or carry out an agenda. • Spam generators are a common use of botnets. It is estimated that 60% of spam emails are bot generated. • Distribution of malware is another use of botnets. They spread viruses, Trojan horses, rootkits, and can create new bots. • Theft of personal or propriety information • Storage of illicit or questionable information. Could be anything from personal information to violated copyright software. • Clickfraud is a major use for botnets, the bots automatically click on webpage advertising to generate revenue for the page owner.
METHODS OF PROTECTION • The Best Methods of Protection against bot infection: • Anti-virus software • Keep all software up to date and install new patches • Increased security settings for web browsers • Don’t open unverified email attachments • Limit user capabilities when online
METHOD OF PROTECTION • Inorder to Stop a Botnet: • There is only one effective way to kill it • Shut Down the C&C server • Typically done by legal authorities such as national Computer Emergency Response Teams (CERT). • However, controller’s often implement their network through multiple C&C Servers for redundancy purposes or switch machines to make it more difficult to eliminate.
CASE STUDY : CONFICKER WORM • First discover of the Conficker worm was in 2008 -2009. • It is a worm that uses a combination of exploits to gain access to computer’s core operating system and add them to the Botnet. • The well known methods are: exploitation of a vulnerability in security update 658644 (MS 08 -67), targeting networks with open share or weak passwords, using Auto. Play. • Multiple variants of the Conficker worm, each can vary in infection medium and the command-control infrastructure.
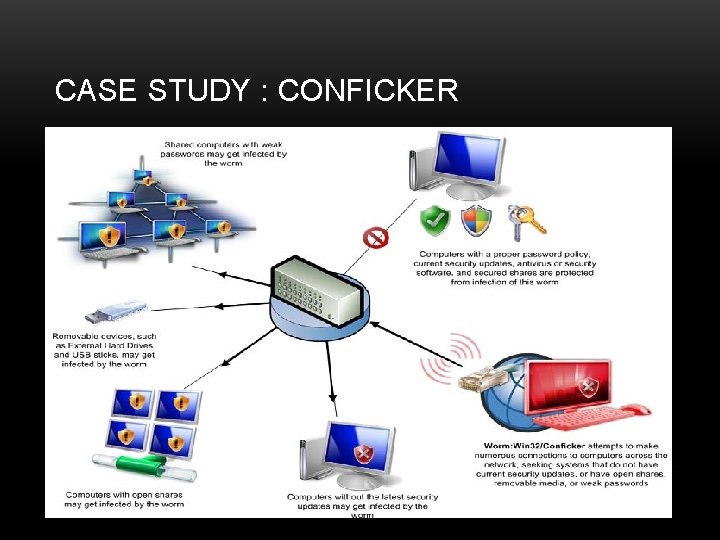
CASE STUDY : CONFICKER
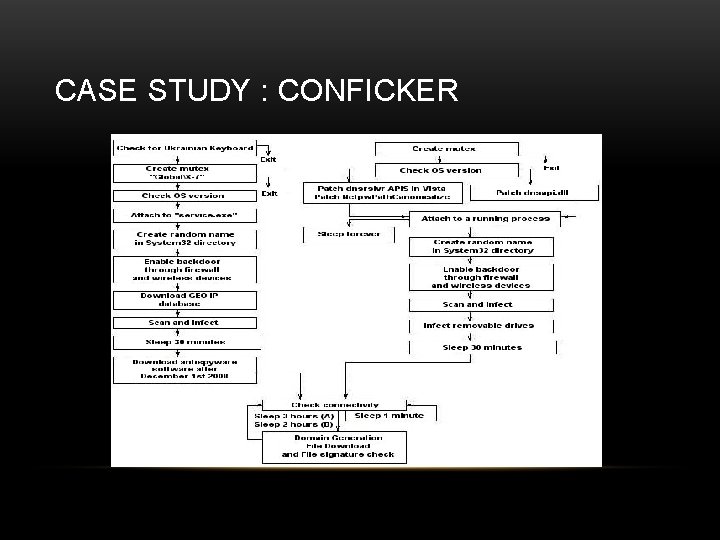
CASE STUDY : CONFICKER
CASE STUDY : CONFICKER WORM • Two largest variants are A and B, both use the same exploitation techniques. • C&C infrastructure • Conficker Variant A • Every 3 hours a list of 250 domain names are generated an URL request is sent to TCP port 80. If a Windows binary is returned and is validated against a public key stored by the worm. • Conficker Variant B • Differences include: Checks for commands every 2 hours, GEO IP included in Variant B, doesn’t attempt to download fake antivirus, attempts to disable host security, and antireverse engineering features
CASE STUDY : CONFICKER WORM • Variant C • Takes a big step up from variants A & B in C&C infrastructure. It can utilize a P 2 P structure. • It allows for infected hosts to find other Conficker C peers using IP mappings, distribute/receive cryptographically signed content (only by Conficker Author), and execute verified content. • Basically, each infected machine serves as a client and a server in order to spread and execute botmaster commands. It eliminates the Achilles' heel of variants A & B.
CASE STUDY : CONFICKER WORM • Variant C • Still has the capability for the C&C infrastructure of variant A & B. Generates 50, 000 domains that possible could be the controller, of which 500 are chosen daily to query. • Unlike A&B, who queried on five second intervals, variant C issues queries in random intervals between 10 and 50 seconds. • The other major updates to this variant are: • Virtual Machine Detection • Website blocking • Removal Prevention Features.

WORKS CITED • Osborne, Charlie. “Symantec takes on one of the largest botnets in history. ” CNET, 1 October 2013. Web. 28 October 2013. • “About Botnets. ” F-Secure, n. d. Web. 28 October 2013 • Rouse, Margaret. “Botnet (Zombie Army). ” Search. Security. Tech. Target, February 2013. Web. 28 October 2013 • “Bots and Botnets – A Growing Threat” Symantec. Norton. n. d. Web. 28 October 2013. • Microsoft Support Site. Safety and Security, 2013. Web, 10 November 2013. • Burton, Kelly. “The Conficker Worm”. SANS, n. d. Web 10 November 2013 • Porras, Phillip, Saidi, Hassan, and Yegneswaran, Vinod. "An Analysis of Conficker's Logic and Rendezvous Points. " SRI. February 4, 2009. Web. 10 November 2013. • Fitzgibbon, Niall and Wood, Mike. "Conficker. C A Technical Analysis. " Sophos. April 1, 2009. Web. 10 November 2013.
- Slides: 17