BOTNETS A BIGGEST THREAT TO INERNET Presented By
BOTNETS A BIGGEST THREAT TO INERNET Presented By : Ramesh kumar 08 EBKIT 049
A Quick Glance Ø Ø Ø Ø Introduction History How do they work ? Protocols What are they used for ? Types of BOTS Prevention Conclusion
INTRODUCTION Botnets are networks of computers taken hostage by malware that controls them and makes them to act in other nefarious ways. Ø A "botnet" is a collection of computers that have been infected with remote-control software. Ø Runs autonomously and automatically. Ø User unaware Ø
History Ø Originally used in IRC as a way to allow automated tasks to be done • Protect a channel, kick a user out of a channel etc. Ø Ø Eventually evolved into a way to automate malicious tasks Started with Do. S/DDo. S against servers • TFN, stacheldraht, trinoo (1999)
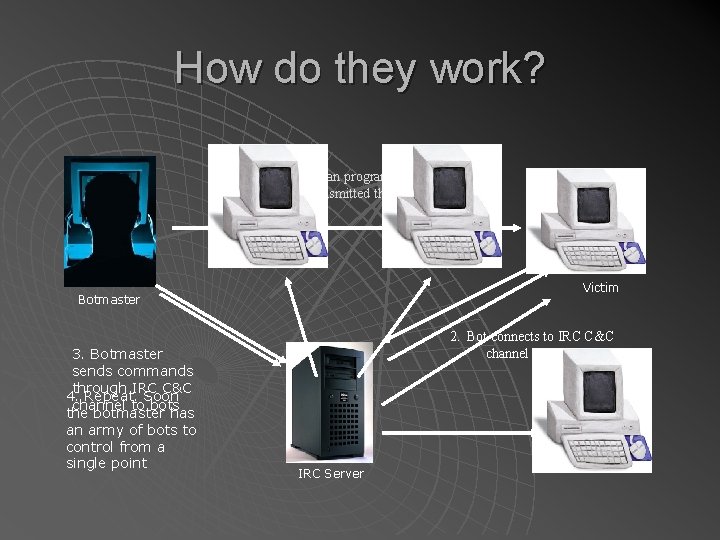
How do they work? Worm/Trojan program that's usually transmitted through a spam. Victim Botmaster 3. Botmaster sends commands through IRC C&C 4. Repeat. Soon channel to bots the botmaster has an army of bots to control from a single point 2. Bot connects to IRC C&C channel IRC Server
PROTOCOLS ØIRC ØHTTP ØP 2 P
Some Important points Ø Size of Botnets: 50, 000 or more BOTS in a single botnet. 1000 new bots each day. Ø Ø IRC hides IP’S. Different botnets can be connected through IRC Botnets can be rented Botnet controller is always unidentified.
Malicious activities Ø Ø Ø Distributed Denial-of-Service (DDo. S) attacks. Spamming Sniffing Keylogging Spreading new malware Mass identity theft (Phishing)
GOOD APPLICATIONS Ø Online games/Polling Ø Instant Messenger Ø Search Engines
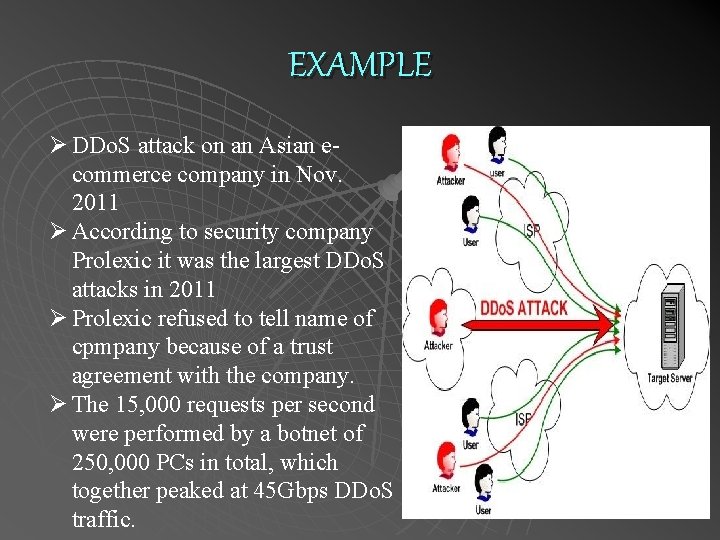
EXAMPLE Ø DDo. S attack on an Asian ecommerce company in Nov. 2011 Ø According to security company Prolexic it was the largest DDo. S attacks in 2011 Ø Prolexic refused to tell name of cpmpany because of a trust agreement with the company. Ø The 15, 000 requests per second were performed by a botnet of 250, 000 PCs in total, which together peaked at 45 Gbps DDo. S traffic.
TYPES OF BOTS Ø Ø Agobot: Most sophisticated. 20, 000 lines c/c++ code IRC based command/control. Capable of many Do. S attack types. Traffic sniffers/key logging. SDBot: Simpler than Agobot, 2, 000 lines C code. Non-malicious at base. Easily extended for malicious purposes. • Scanning • Do. S Attacks • Sniffers
TYPES OF BOTS Ø Ø Spy. Bot: <3, 000 lines C code. Possibly evolved from SDBot. Similar command/control engine. No attempts to hide malicious purposes. GT Bot: Functions based on m. IRC scripting capabilities. Hide. Window program hides bot on local system. Port scanning, Do. S attacks, exploits for RPC.
PREVENTION Using anti-virus and anti-spyware software and keeping it up to date. Ø Setting your operating system software to download and install security patches automatically. Ø Being cautious about opening any attachments or downloading files from emails you receive. Ø Using a firewall to protect your computer from hacking attacks while it is connected to the Internet. Cont… Ø
PREVENTION Disconnecting from the Internet when you're away from your computer. Ø Downloading free software only from sites you know and trust. Ø Taking action immediately if your computer is infected. Ø
CONCLUSION Botnet a large army of networked computers. Ø Used in many malicious activities. Ø Works automatically and autonomously. Ø Hence biggest threat to INTERNET Ø
THANK YOU
- Slides: 16