BOTNET Kumar Mukherjee Mike Ladd Nazia Raoof Rajesh
BOTNET Kumar Mukherjee Mike Ladd Nazia Raoof Rajesh Radhakrishnan Bret Walker
Botnet Background • network of infected hosts, under control of a human operator (botmaster) • tens of thousands of nodes • victims claimed by remote exploits
Defining Characteristic • use of Command & Control (C&C) channels • used to disseminate botmaster's commands
Uses of Botnets Spam ID Theft Piracy DDOS • • • Ex. 1000 bots w/ 128 KBit/s connection > many corporate systems IP distribution makes filtering difficult
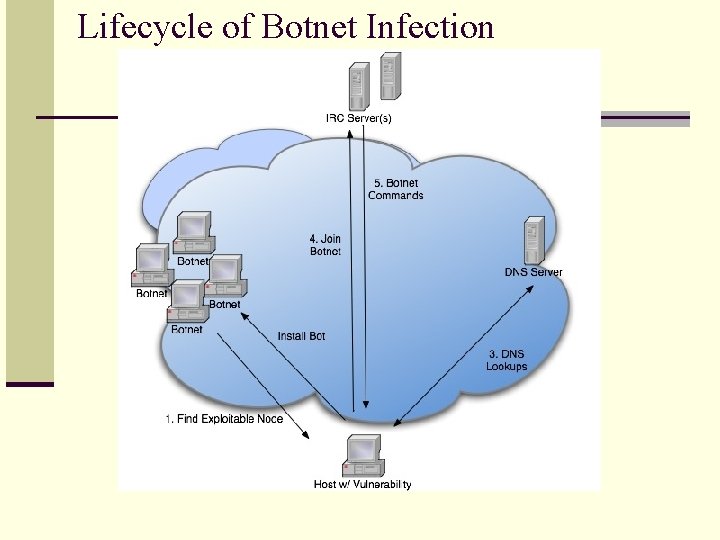
Lifecycle of Botnet Infection
Why IRC? • IRC designed for both point-to-point and point-to-multipoint communication • one-to-one, or one-to-group chat • flexible, open-source protocol
Bot-to-IRC Communication • authenticate to IRC server via PASS message • C&C channel authentication • Botmaster authenticates to bot population to issue commands
Bot-News: Kraken • • 400, 000+ nodes 50+ Forture 500 companies 2 x the size of ‘Storm’ Used for spam (bots sending 500, 000+ messages daily)
Bot-News: Kraken • Designed as image file • Regular updates to binary • C&C communication via customized UDP/TCP • Able to generate new domain names if C&C is disabled
Further Background • http: //www. honeynet. org/papers/bots/ • http: //www. wired. com/wired/archive/14. 11 /botnet_pr. html • http: //en. wikipedia. org/wiki/Storm_botnet
Methodology: Malware Collection Phase • Collection of as many bot binaries as possible • Distributed darknet used • 14 nodes access the darknet • Modified version of Nepenthes (a Malware collection framework) platform: -- Mimics the replies generated by vulnerable services in order to collect the first stage exploit or shellcodes -- Generate URL that are to retrieve binaries • Honeynet is used to compliment Nepenthes in order to catch exploits missed. -- Honeypots are unpatched Windows XP VM’s -- Honeypots become infected and compared later to a clean Windows XP image. -- Infected Honey pots are also allowed to sustain IRC connections until VM gets reimaged
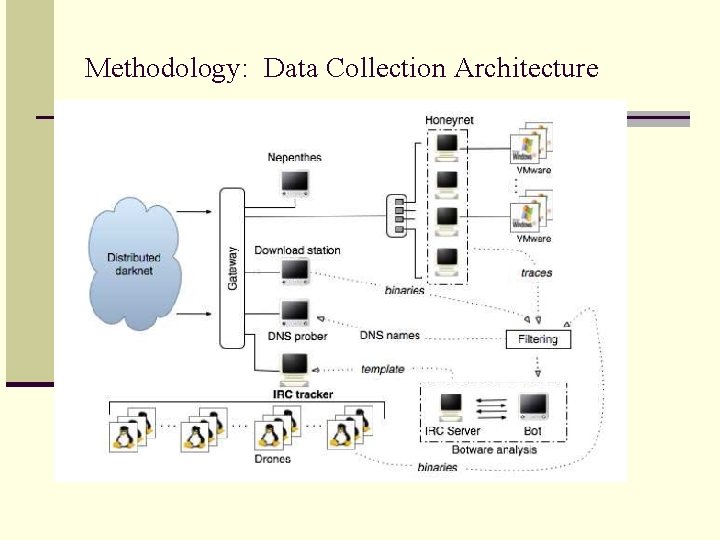
Methodology: Data Collection Architecture
Methodology: Gateway n Darknet routing to various parts of the internal network n Cross-infection prevention among honeypots n configuring honeypots in separate VLANSs n Termination of traffic across VLANs and gateways n Monitor and Analyze the malware traffic for infections n Dynamic rule insertion n block further inbound attack traffic towards honeypot that is infected n single malware instance honeypots due to lack of resources n Other funcitons n Triggering re-imaging with clean Windows images n pre-filtering and control during downloads n local DNS to resolve queries
Methodology: Defense Points n With the methodology we now have the ability to model other types of bots. n Although methodology utilized Windows OS, we can model it for other platforms n The methodology analyzes all aspects of bots and botnets.
A multifaceted approach to understanding the Botnet Phenomenon Results - I
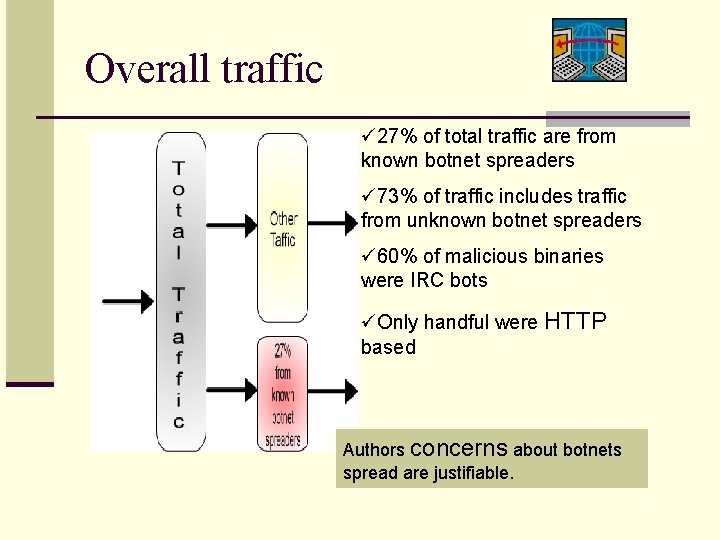
Overall traffic ü 27% of total traffic are from known botnet spreaders ü 73% of traffic includes traffic from unknown botnet spreaders ü 60% of malicious binaries were IRC bots üOnly handful were HTTP based Authors concerns about botnets spread are justifiable.
Traffic directed to vulnerable ports ü 76% of traffic targeted to vulnerable ports are from botnet spreaders üMalicious traffic to vulnerable ports cannot be differentiated between botnet and non-botnet traffic How much of total traffic was directed to vulnerable ports is desired.
Peak traffics ü 90% of total traffic during the peak time targets ports used by botnet spreaders ü 70% of traffic during the peak time sent shell exploits similar to those sent by botnet spreaders.
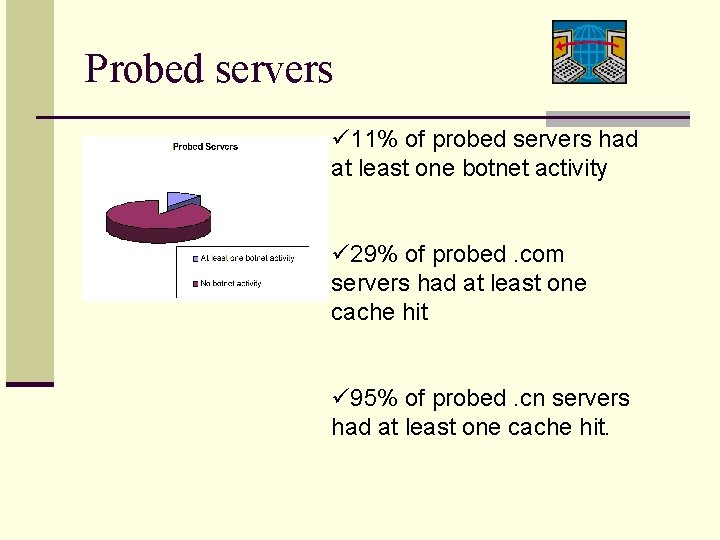
Probed servers ü 11% of probed servers had at least one botnet activity ü 29% of probed. com servers had at least one cache hit ü 95% of probed. cn servers had at least one cache hit.
Botnet Types üTotal botnets captured 192 ü 34 of 192 botnets captured were type I botnets (worm-like) ü 158 of them were type II
Botnets and Network types When channel was set to topic ü 80% of targeted scanning was aimed at CLASS A networks ü 89% of localized scanning was aimed at CLASS B networks When channel was set to botmaster commands ü 88% of targeted scanning was aimed at CLASS A networks ü 82% of localized scanning was aimed at CLASS B networks
DNS & IRC tracker views Both DNS & IRC tracker views demonstrated three type of growth pattern: ü semi exponential growth ü Staircase type growth ü Linear growth ØSemi-exponential growth exhibited random scanning activity ØStaircase type growth exhibited intermittent activity ØLinear growth pattern exhibit time scoped activity
Key Points based on results ü Botnets pose serious threats to the internet ü Major contributor of unwanted traffic on the internet ü IRC is the dominant protocol used in the Botnet communications ü Botnets have achieved a high degree of sophistication in terms of self-protection mechanisms and modular package structures
Effective Botnet Sizes Footprint Size vs. Effective Size • Significantly smaller • At most 3, 000 bots online w/ networks of up to 10 k bots Smaller effective sizes limit certain activities: • Timely commands • DDo. S attacks Effective botnet sizes fluctuate with timezone changes
Lifetime Botnets have relatively long lifetimes • Even after they’re shut down, live on average for 47 days • 84% of servers up longer than the 3 month survey • 55% of those botnets still scanning the Internet • If taken offline, able to be brought back online quickly Bots do not stay long on IRC channels • Average time ~ 25 minutes • 90% stayed less than 50 minutes • High churn rate Botmasters spend great lengths of time managing and monitoring their botnets
Botnet Software Dissection 49% disable firewall and anti-virus software Many run inetd, which is used to identify the user of a computer. Used to verify bots joining an IRC channel 40% execute a System Security Monitor command, securing client machines from further exploitation Average of 15 exploits per botnet binary -- bots can infect machines in a variety of ways Windows XP constitutes 82. 6% of observed exploited hosts, with 99% of those hosts running SP 1 or less
Insight from an “Insider’s View” Botmasters range in skill level Botmasters: 1. Share information about networks 2. Tweak their bots to use the network efficiently 3. Prune misbehaving bots and exploit “super-bots” Botmasters are probably leasing their bots or attacking each other Most commands (75%) are for control, scanning and cloning. 7% are for attacking.
Related Work n Honeynet group was the first to do an informal study n Freiling et al. on countering certain classes of DDo. S attacks n Cooke et al. on prevalence of botnets by measuring elapsed n n time before an un-patched system was infected by a botnet Barford et al. on an in-depth anaylsis on bot software sourcecode Vrable et al. presented Potemkin, a scalable virtual honeynet system Cui et al. presented Role. Player—a protocol independent lightweight responder that tries to overcome some of these limitations by reverting to a real server when the responder fails to produce the proper response Dagon et al. provide an initial analytical model for capturing the spreading behavior of botnets.
Conclusion Long presence and few formal studies One of the most severe threats to the Internet. Our knowledge of botnet behavior is incomplete To improve our understanding, we present a composite view Results show that botnets are a major contributor to the overall unwanted traffic on the Internet n Botnet scanning behavior is markedly different from that seen by autonomous malware (e. g. , worms) because of its manual orchestration n IRC is still the dominant protocol used for C&C communications n Use is adapted to satisfy different botmasters’ needs n Botnet footprints are usually much larger n Graybox testing technique enabled us to understand the level of sophistication reached by bot software today n n n
- Slides: 29