Bot Net Detection Techniques By Shreyas Sali Course
Bot. Net Detection Techniques By Shreyas Sali Course: Network Security (CSCI – 5235) Instructor: Dr. T Andrew Yang
Outline v Introduction to Botnet v Botnet Life-cycle v Botnet in Network Security v Botnet Uses v Botnet Detection v Preventing Botnet Infection v Botnet Research v Conclusion v References Page 2
Introduction to Botnet v. A Botnet is a network of compromised computers under the control of a remote attacker. v Botnet Terminology ü Bot Herder (Bot Master) ü Bot Client ü IRC Server ü Command Control Channel (C&C) Page 3
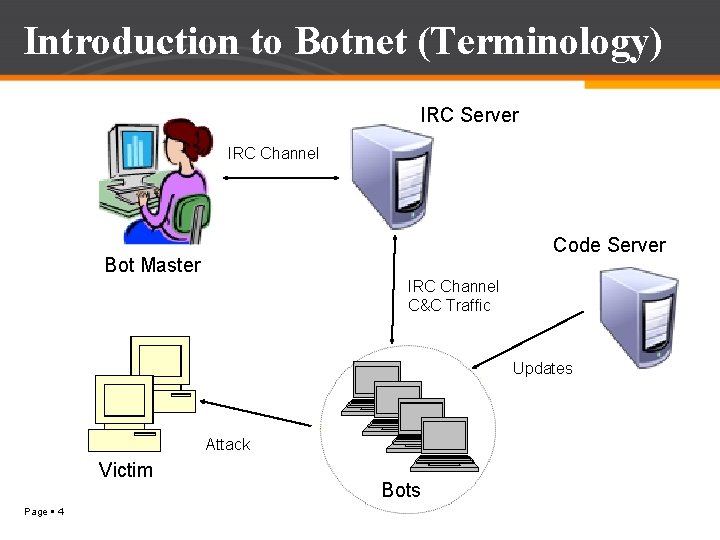
Introduction to Botnet (Terminology) IRC Server IRC Channel Code Server Bot Master IRC Channel C&C Traffic Updates Attack Victim Page 4 Bots
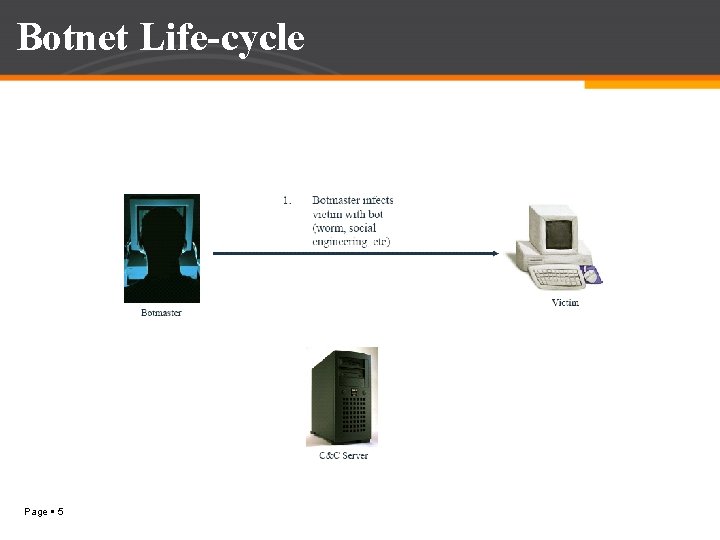
Botnet Life-cycle Page 5
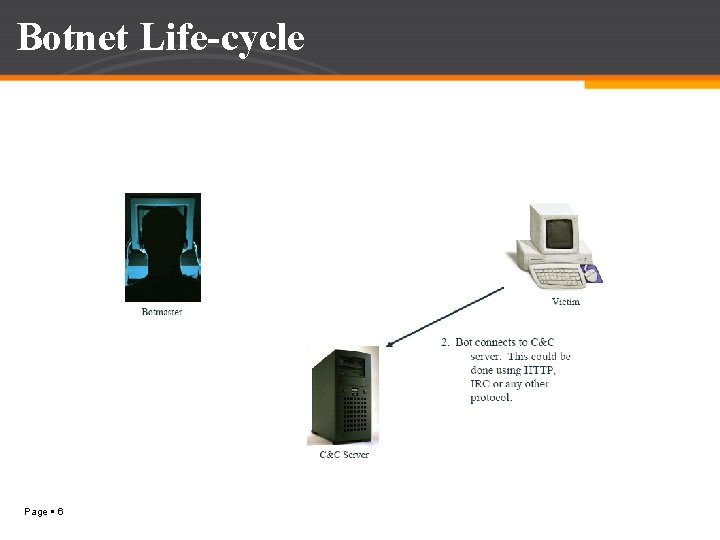
Botnet Life-cycle Page 6
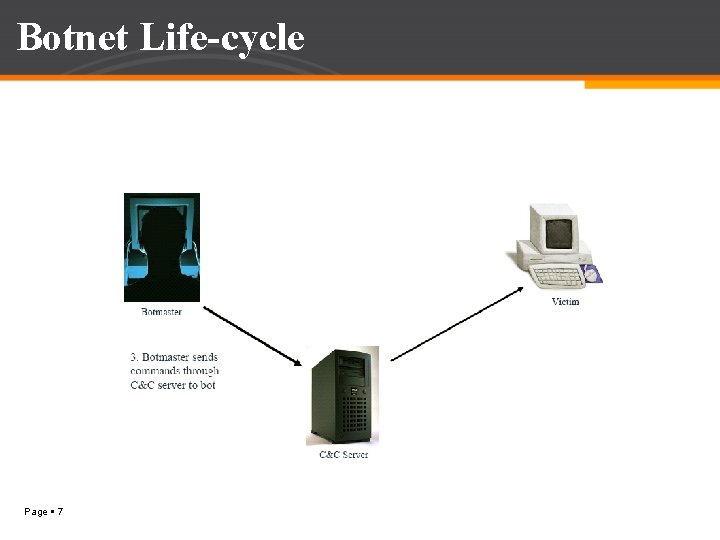
Botnet Life-cycle Page 7
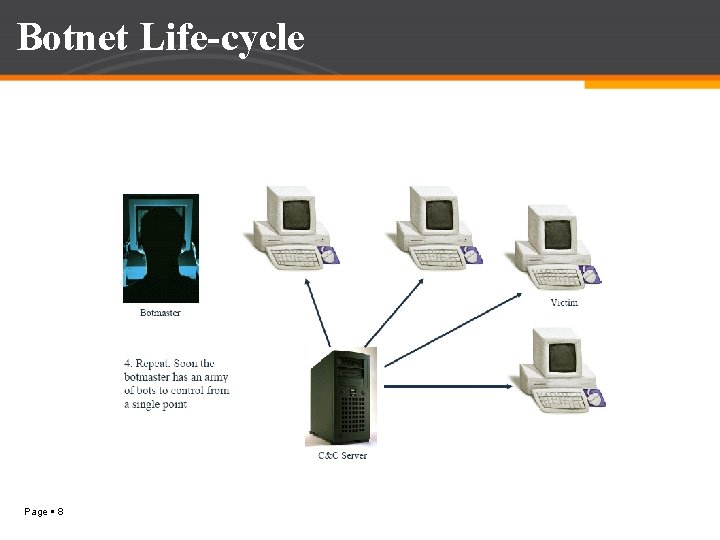
Botnet Life-cycle Page 8
Botnet In Network Security v Internet users are getting infected by bots v Many times corporate and end users are trapped in botnet attacks v Today 16 -25% of the computers connected to the internet are members of a botnet v In this network bots are located in various locations v It will become difficult to track illegal activities v This behavior makes botnet an attractive tool for intruders and increase threat against network security Page 9
Botnet is Used For Page 10 Bot Master
How Botnet is Used? v Distributed Denial of Service (DDo. S) attacks v Sending Spams v Phishing (fake websites) v Addware (Trojan horse) v Spyware (keylogging, information harvesting) v Click Fraud So It is really Important to Detect this attack Page 11
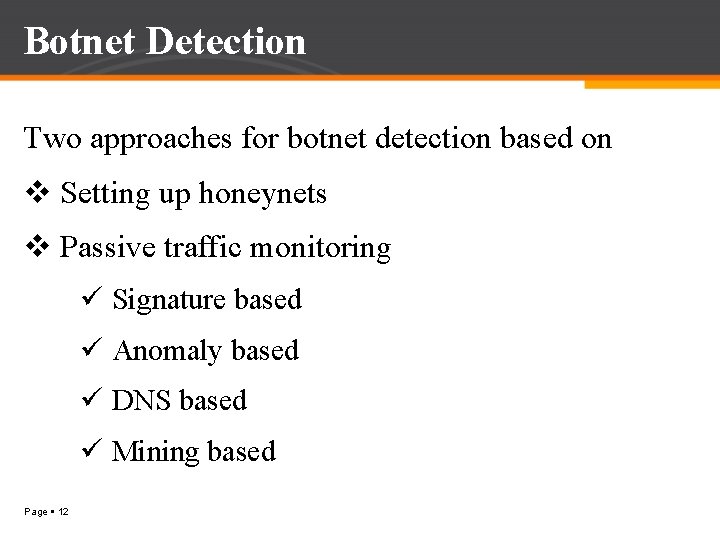
Botnet Detection Two approaches for botnet detection based on v Setting up honeynets v Passive traffic monitoring ü Signature based ü Anomaly based ü DNS based ü Mining based Page 12
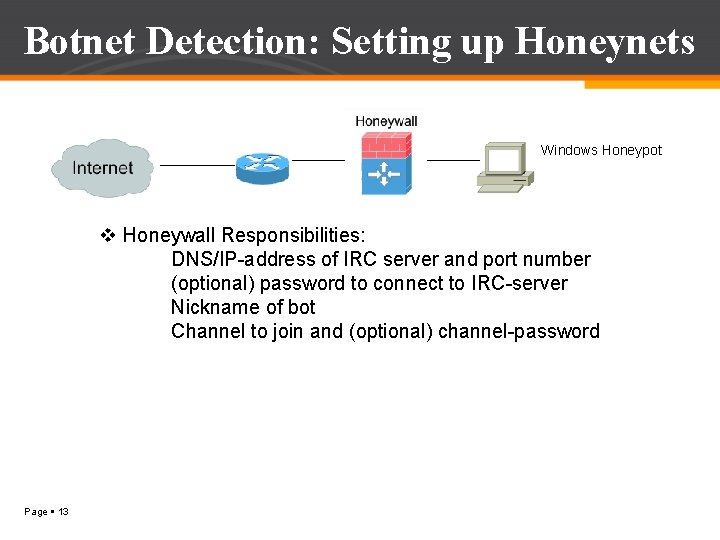
Botnet Detection: Setting up Honeynets Windows Honeypot v Honeywall Responsibilities: DNS/IP-address of IRC server and port number (optional) password to connect to IRC-server Nickname of bot Channel to join and (optional) channel-password Page 13
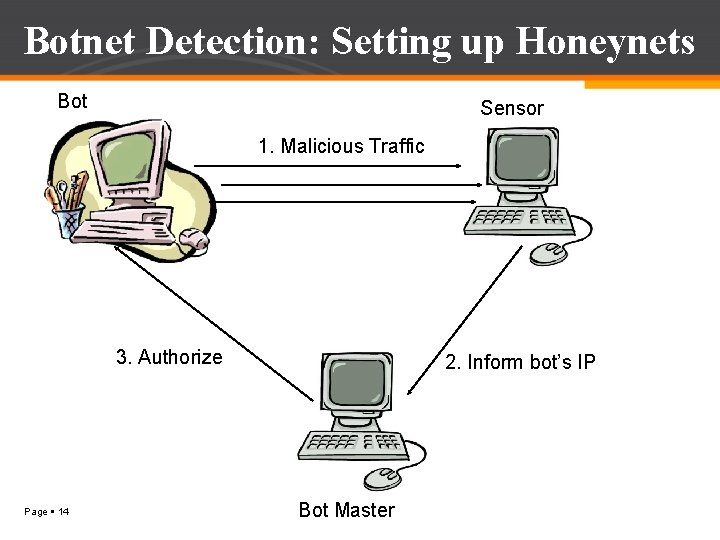
Botnet Detection: Setting up Honeynets Bot Sensor 1. Malicious Traffic 3. Authorize Page 14 2. Inform bot’s IP Bot Master
Botnet Detection: Traffic Monitoring ü Signature based: Detection of known botnets ü Anomaly based: Detect botnet using following anomalies • High network latency • High volume of traffic • Traffic on unusual port • Unusual system behaviour ü DNS based: Analysis of DNS traffic generated by botnets Page 15
Botnet Detection: Traffic Monitoring ü Mining based: • Botnet C&C traffic is difficult to detect • Anomaly based techniques are not useful • Data Mining techniques – Classification, Clustering Page 16
Botnet Detection v Determining the source of a botnet-based attack is challenging: v Traditional approach: ü Every zombie host is an attacker ü Botnets can exist in a benign state for an arbitrary amount of time before they are used for a specific attack v New trend: ü P 2 P networks Page 17
Preventing Botnet Infections ü Use a Firewall ü Patch regularly and promptly ü Use Antivirus (AV) software ü Deploy an Intrusion Prevention System (IPS) ü Implement application-level content filtering ü Define a Security Policy and ü Share Policies with your users systematically Page 18
Botnet Research v Logging onto herder IRC server to get info v Passive monitoring üEither listening between infected machine and herder or spoofing infected PC v Active monitoring: Poking around in the IRC server v Sniffing traffic between bot & control channel Page 19
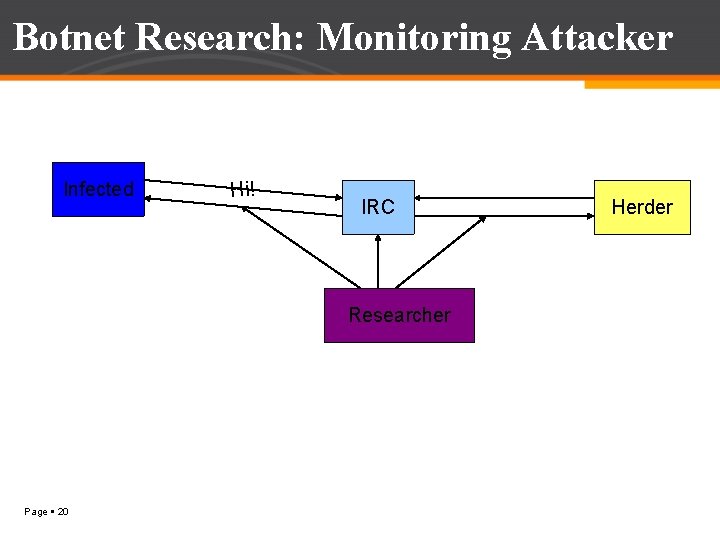
Botnet Research: Monitoring Attacker Infected Hi! IRC Researcher Page 20 Herder
Conclusion v Botnets pose a significant and growing threat against cyber security v It provides key platform for many cyber crimes (DDOS) v As network security has become integral part of our life and botnets have become the most serious threat to it v It is very important to detect botnet attack and find the solution for it Page 21
References v. B. Saha and A, Gairola, “Botnet: An overview, ” CERT-In White Paper. CIWP-2005 -05, 2005 v Peer to Peer Botnet detection for cyber-security: A data mining approach - ACM Portal Mohammad M. Masud, Jing Gao, Latifur Khan, Jiawei Han, Bhavani Thuraisingham v A Survey of Botnet and Botnet Detection Feily, M. ; Shahrestani, A. ; Ramadass, S. ; Emerging Security Information, Systems and Technologies, 2009. SECURWARE '09. Third International Conference on Digital Object Publication Year: 2009 , Page(s): 268 – 273 IEEE CONFERENCES v Honeynet-based Botnet Scan Traffic Analysis Zhichun Li, Anup Goyal, and Yan Chen Northwestern University, Evanston, IL 60208 v Detecting Botnets Using Command Control Traffic As. Sadhan, B. ; Moura, J. M. F. ; Lapsley, D. ; Jones, C. ; Strayer, W. T. ; Network Computing and Applications, 2009. NCA 2009. Eighth IEEE International Symposium. Publication Year: 2009 , Page(s): 156 – 162 IEEE CONFERENCES v Spamming botnets: signatures and characteristics Yinglian Xie, Fang Yu Page 22
QUESTIONS Page 23
Thank you Page 24
- Slides: 24