BOSTON HARTFORD STAMFORD NEW YORK NEWARK EAST BRUNSWICK
BOSTON | HARTFORD | STAMFORD | NEW YORK | NEWARK | EAST BRUNSWICK | PHILADELPHIA | WILMINGTON | WASHINGTON, DC DFARS Cybersecurity Compliance: Understanding Your Do. D Requirements Alexander Major Franklin Turner NHOA Annual Meeting, August 2018 Copyright © 2016 Mc. Carter & English, LLP www. mccarter. com
Who Are These Guys? ▪ Nearly two decades of experience representing clients of all sizes in complex, high-profile “bet the company” matters ▪ Significant experience in litigation, compliance, and cybersecurity matters ▪ Partners and Co-Leaders of the Government Contracts and Export Controls Practice Group at Mc. Carter & English LLP Copyright © 2016 Mc. Carter & English, LLP 2
Overview ▪ Defining “Cybersecurity” – – ▪ ▪ Patchwork of Laws & Regulations Regulatory Responses – – ▪ ▪ ▪ ▪ Why Do Hackers Hack? Costs of Cybercrime FAR NARA & the CUI Registry NIST DFARS IT Acquisition Requirements De-NIST-ifying Standards Cloud Computing Basics Federal Cloud Computing SLA Best Practices Threat Management Considerations Best Practices Copyright © 2016 Mc. Carter & English, LLP 3
Defining Cybersecurity Copyright © 2016 Mc. Carter & English, LLP 4
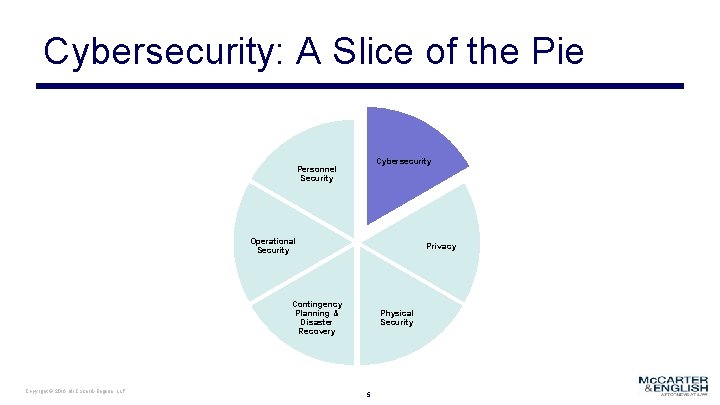
Cybersecurity: A Slice of the Pie Cybersecurity Personnel Security Operational Security Privacy Contingency Planning & Disaster Recovery Copyright © 2016 Mc. Carter & English, LLP Physical Security 5
Cybersecurity Copyright © 2016 Mc. Carter & English, LLP 6
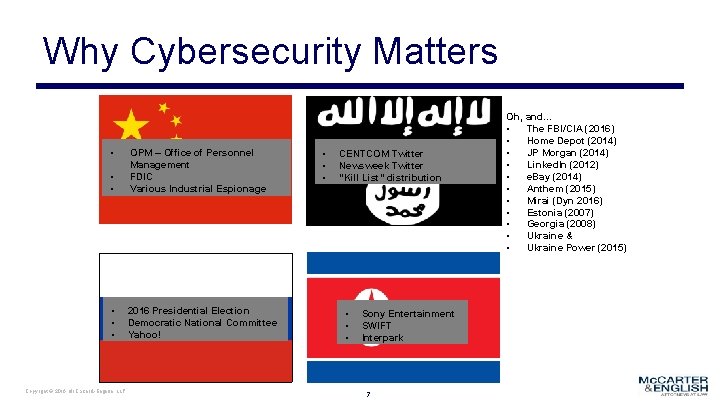
Why Cybersecurity Matters • • • OPM – Office of Personnel Management FDIC Various Industrial Espionage • • • 2016 Presidential Election Democratic National Committee Yahoo! Copyright © 2016 Mc. Carter & English, LLP • • • CENTCOM Twitter Newsweek Twitter “Kill List” distribution • • • Sony Entertainment SWIFT Interpark 7 Oh, and… • The FBI/CIA (2016) • Home Depot (2014) • JP Morgan (2014) • Linked. In (2012) • e. Bay (2014) • Anthem (2015) • Mirai (Dyn 2016) • Estonia (2007) • Georgia (2008) • Ukraine & • Ukraine Power (2015)
And let’s not forget…this guy Copyright © 2016 Mc. Carter & English, LLP 8
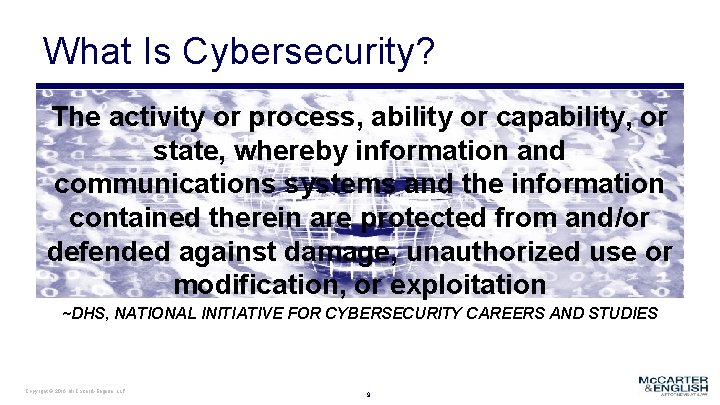
What Is Cybersecurity? The activity or process, ability or capability, or state, whereby information and communications systems and the information contained therein are protected from and/or defended against damage, unauthorized use or modification, or exploitation ~DHS, NATIONAL INITIATIVE FOR CYBERSECURITY CAREERS AND STUDIES Copyright © 2016 Mc. Carter & English, LLP 9
What Is Cybersecurity Not? ▪ ▪ ▪ “Compliance” Easy Static Risk-free Cheap And… Copyright © 2016 Mc. Carter & English, LLP 10
Why Do Hackers Hack? Copyright © 2016 Mc. Carter & English, LLP 11
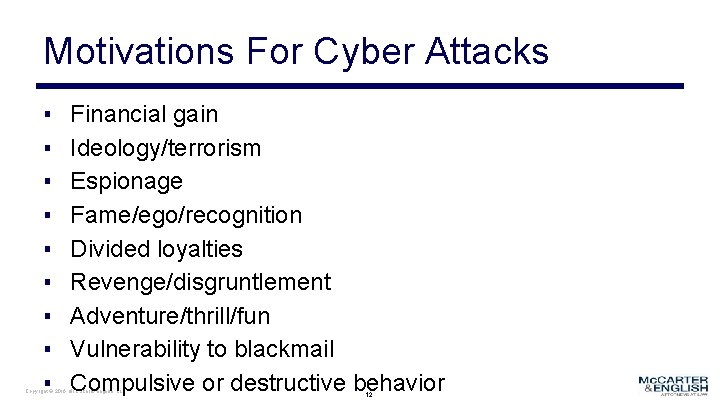
Motivations For Cyber Attacks ▪ ▪ ▪ ▪ ▪ Financial gain Ideology/terrorism Espionage Fame/ego/recognition Divided loyalties Revenge/disgruntlement Adventure/thrill/fun Vulnerability to blackmail Compulsive or destructive behavior Copyright © 2016 Mc. Carter & English, LLP 12

Maybe No Reason At All … Copyright © 2016 Mc. Carter & English, LLP 13
Understanding The Threat Copyright © 2016 Mc. Carter & English, LLP 14
What type of threat is it? Copyright © 2016 Mc. Carter & English, LLP 15
The Threat Intent + Skills + Tools + Opportunity Copyright © 2016 Mc. Carter & English, LLP 16
The Human Condition ▪ Most companies fail to recognize the human side of cybersecurity ▪ Crime is behavior, behavior varies – Benefits vs. Costs – Crime of opportunity – Crime as a reaction to negative emotions – Social control/Friends kept Copyright © 2016 Mc. Carter & English, LLP 17
The Human Condition ▪ 86% of ethical hackers hacked out of curiosity (Nuix “The Black Report”, 2018) – 35% for “entertainment or mischief” ▪ 88% of ethical hackers employ social engineering – 16% Phone-focused – 22% Physical – 62% Phishing ▪ 52% of hackers believe education is an extremely important countermeasure (Nuix “The Black Report”, 2017) Copyright © 2016 Mc. Carter & English, LLP 18
Costs of Cybercrime Copyright © 2016 Mc. Carter & English, LLP 19
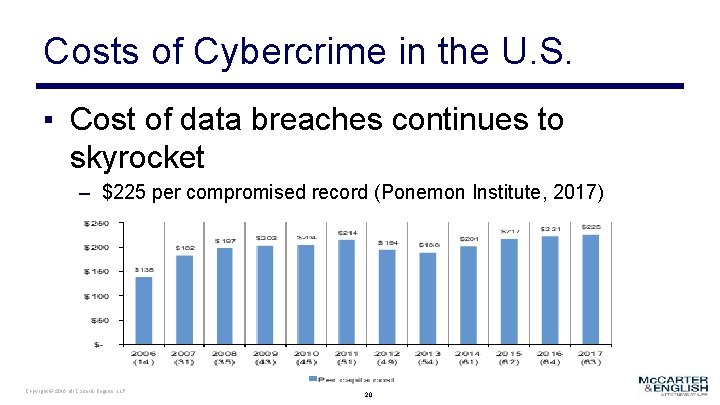
Costs of Cybercrime in the U. S. ▪ Cost of data breaches continues to skyrocket – $225 per compromised record (Ponemon Institute, 2017) Copyright © 2016 Mc. Carter & English, LLP 20
Costs of Cybercrime in the U. S. (Cont’d) ▪ $146 - indirect costs (e. g. , abnormal customer turnover, reputational harm, etc. ) ▪ $79 - direct costs incurred to resolve the breach (e. g. , investments in technologies, legal fees, etc. ) Copyright © 2016 Mc. Carter & English, LLP 21
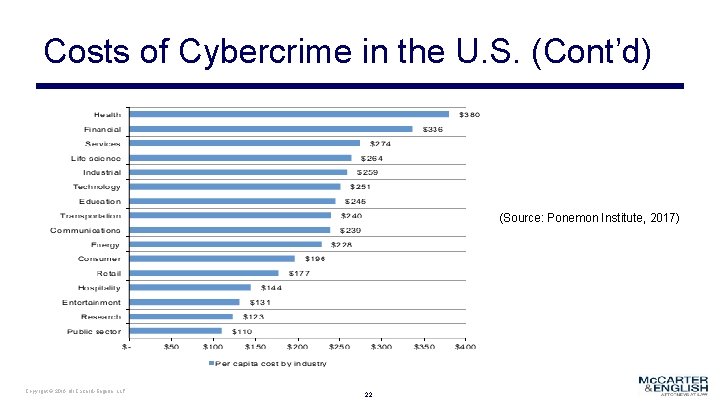
Costs of Cybercrime in the U. S. (Cont’d) (Source: Ponemon Institute, 2017) Copyright © 2016 Mc. Carter & English, LLP 22
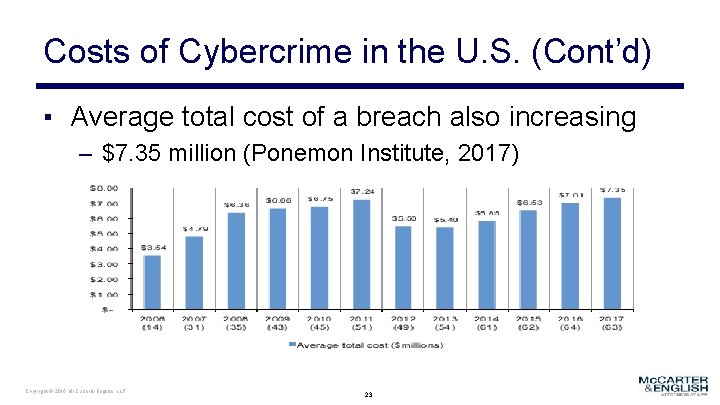
Costs of Cybercrime in the U. S. (Cont’d) ▪ Average total cost of a breach also increasing – $7. 35 million (Ponemon Institute, 2017) Copyright © 2016 Mc. Carter & English, LLP 23

Potential Impacts of a Breach ▪ ▪ ▪ ▪ Fraud ($$) Financial loss Brand damage/Embarrassment Data leak/Breach Intellectual property loss Identity theft Liability risk Copyright © 2016 Mc. Carter & English, LLP 24
Patchwork of Laws & Regulations Copyright © 2016 Mc. Carter & English, LLP 25
Understanding The Acronyms … ▪ Key acronyms: – Federal Information Security Management Act of 2002 (FISMA 2002) – Federal Information Security Modernization Act of 2014 (FISMA 2014) – National Archives and Records Administration Controlled Unclassified Information (NARA CUI) – National Institute of Standards and Technology (NIST) – Federal Information Processing Standards (FIPS) – Federal Risk and Authorization Management Program (Fed. RAMP) Copyright © 2016 Mc. Carter & English, LLP 26
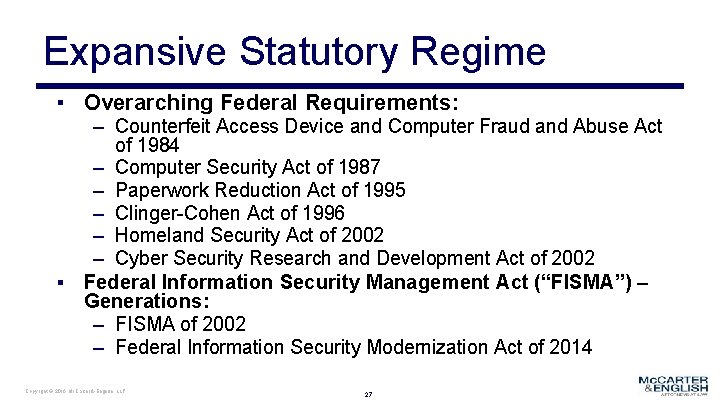
Expansive Statutory Regime ▪ Overarching Federal Requirements: ▪ – Counterfeit Access Device and Computer Fraud and Abuse Act of 1984 – Computer Security Act of 1987 – Paperwork Reduction Act of 1995 – Clinger-Cohen Act of 1996 – Homeland Security Act of 2002 – Cyber Security Research and Development Act of 2002 Federal Information Security Management Act (“FISMA”) – Generations: – FISMA of 2002 – Federal Information Security Modernization Act of 2014 Copyright © 2016 Mc. Carter & English, LLP 27
Regulatory Responses Copyright © 2016 Mc. Carter & English, LLP 28
Your Contractual Response ▪ Dictated by your Specific Contractual Requirements: – FAR Clauses – CUI Registry – DFARS Clauses – NIST SP 800 -171 Copyright © 2016 Mc. Carter & English, LLP 29
FEDERAL ACQUISITION REGULATION Copyright © 2016 Mc. Carter & English, LLP 30
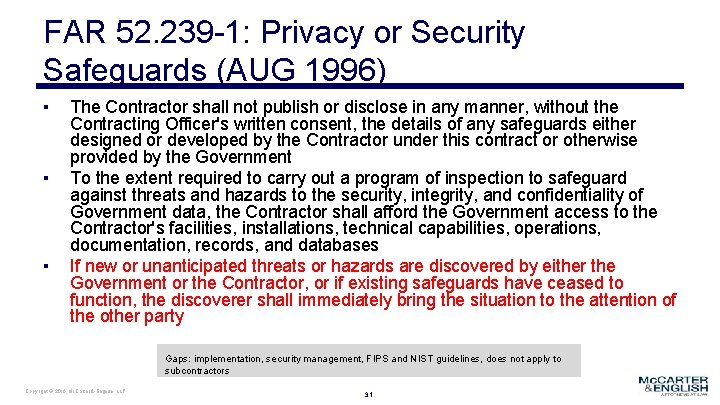
FAR 52. 239 -1: Privacy or Security Safeguards (AUG 1996) ▪ ▪ ▪ The Contractor shall not publish or disclose in any manner, without the Contracting Officer's written consent, the details of any safeguards either designed or developed by the Contractor under this contract or otherwise provided by the Government To the extent required to carry out a program of inspection to safeguard against threats and hazards to the security, integrity, and confidentiality of Government data, the Contractor shall afford the Government access to the Contractor's facilities, installations, technical capabilities, operations, documentation, records, and databases If new or unanticipated threats or hazards are discovered by either the Government or the Contractor, or if existing safeguards have ceased to function, the discoverer shall immediately bring the situation to the attention of the other party Gaps: implementation, security management, FIPS and NIST guidelines, does not apply to subcontractors Copyright © 2016 Mc. Carter & English, LLP 31
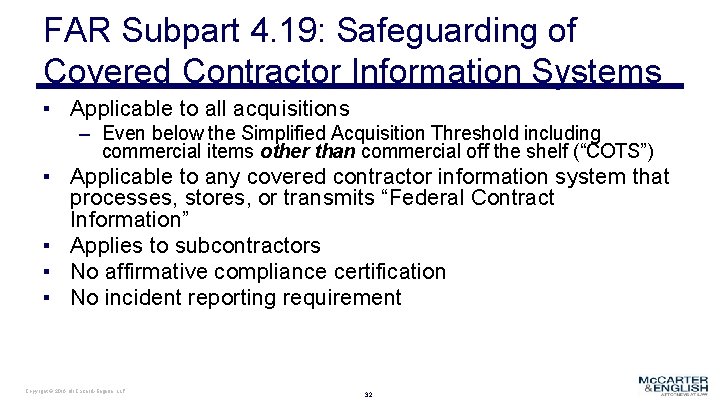
FAR Subpart 4. 19: Safeguarding of Covered Contractor Information Systems ▪ Applicable to all acquisitions – Even below the Simplified Acquisition Threshold including commercial items other than commercial off the shelf (“COTS”) ▪ Applicable to any covered contractor information system that processes, stores, or transmits “Federal Contract Information” ▪ Applies to subcontractors ▪ No affirmative compliance certification ▪ No incident reporting requirement Copyright © 2016 Mc. Carter & English, LLP 32
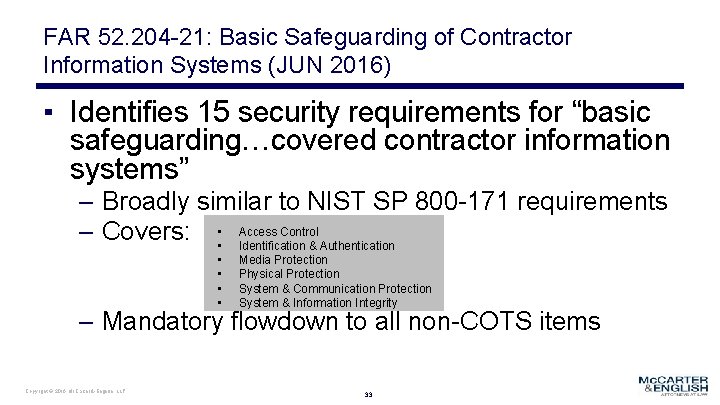
FAR 52. 204 -21: Basic Safeguarding of Contractor Information Systems (JUN 2016) ▪ Identifies 15 security requirements for “basic safeguarding…covered contractor information systems” – Broadly similar to NIST SP 800 -171 requirements – Covers: • • Access Control Identification & Authentication • • Media Protection Physical Protection System & Communication Protection System & Information Integrity – Mandatory flowdown to all non-COTS items Copyright © 2016 Mc. Carter & English, LLP 33
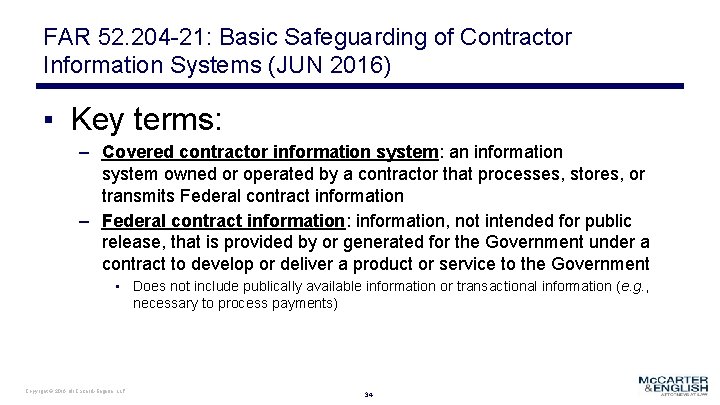
FAR 52. 204 -21: Basic Safeguarding of Contractor Information Systems (JUN 2016) ▪ Key terms: – Covered contractor information system: an information system owned or operated by a contractor that processes, stores, or transmits Federal contract information – Federal contract information: information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government • Does not include publically available information or transactional information (e. g. , necessary to process payments) Copyright © 2016 Mc. Carter & English, LLP 34
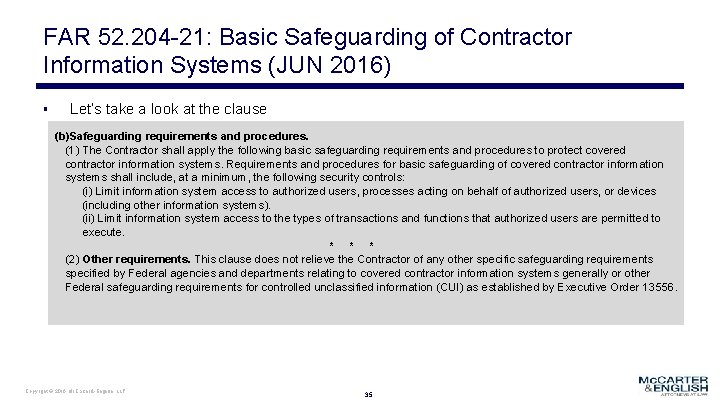
FAR 52. 204 -21: Basic Safeguarding of Contractor Information Systems (JUN 2016) ▪ Let’s take a look at the clause (b)Safeguarding requirements and procedures. (1) The Contractor shall apply the following basic safeguarding requirements and procedures to protect covered contractor information systems. Requirements and procedures for basic safeguarding of covered contractor information systems shall include, at a minimum, the following security controls: (i) Limit information system access to authorized users, processes acting on behalf of authorized users, or devices (including other information systems). (ii) Limit information system access to the types of transactions and functions that authorized users are permitted to execute. * * * (2) Other requirements. This clause does not relieve the Contractor of any other specific safeguarding requirements specified by Federal agencies and departments relating to covered contractor information systems generally or other Federal safeguarding requirements for controlled unclassified information (CUI) as established by Executive Order 13556. Copyright © 2016 Mc. Carter & English, LLP 35
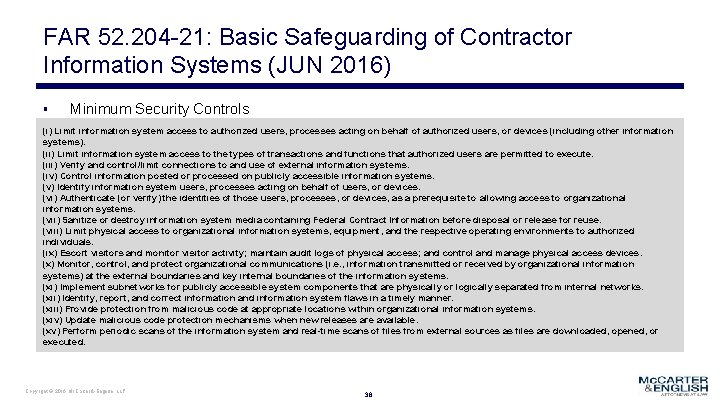
FAR 52. 204 -21: Basic Safeguarding of Contractor Information Systems (JUN 2016) ▪ Minimum Security Controls (i) Limit information system access to authorized users, processes acting on behalf of authorized users, or devices (including other information systems). (ii) Limit information system access to the types of transactions and functions that authorized users are permitted to execute. (iii) Verify and control/limit connections to and use of external information systems. (iv) Control information posted or processed on publicly accessible information systems. (v) Identify information system users, processes acting on behalf of users, or devices. (vi) Authenticate (or verify) the identities of those users, processes, or devices, as a prerequisite to allowing access to organizational information systems. (vii) Sanitize or destroy information system media containing Federal Contract Information before disposal or release for reuse. (viii) Limit physical access to organizational information systems, equipment, and the respective operating environments to authorized individuals. (ix) Escort visitors and monitor visitor activity; maintain audit logs of physical access; and control and manage physical access devices. (x) Monitor, control, and protect organizational communications (i. e. , information transmitted or received by organizational information systems) at the external boundaries and key internal boundaries of the information systems. (xi) Implement subnetworks for publicly accessible system components that are physically or logically separated from internal networks. (xii) Identify, report, and correct information and information system flaws in a timely manner. (xiii) Provide protection from malicious code at appropriate locations within organizational information systems. (xiv) Update malicious code protection mechanisms when new releases are available. (xv) Perform periodic scans of the information system and real-time scans of files from external sources as files are downloaded, opened, or executed. Copyright © 2016 Mc. Carter & English, LLP 36
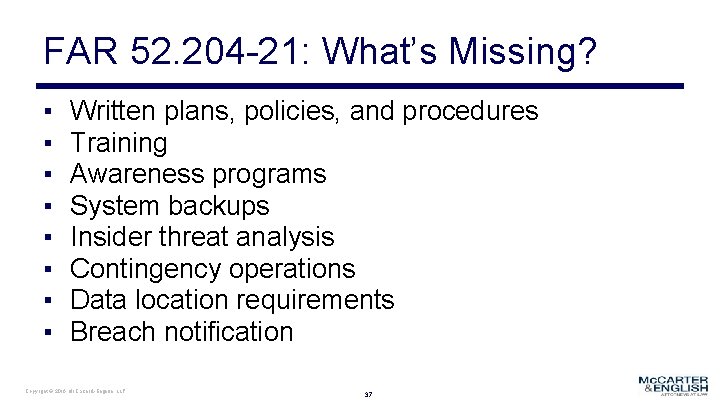
FAR 52. 204 -21: What’s Missing? ▪ ▪ ▪ ▪ Written plans, policies, and procedures Training Awareness programs System backups Insider threat analysis Contingency operations Data location requirements Breach notification Copyright © 2016 Mc. Carter & English, LLP 37
DOD FEDERAL ACQUISITION REGULATION SUPPLEMENT (DFARS) Copyright © 2016 Mc. Carter & English, LLP 38
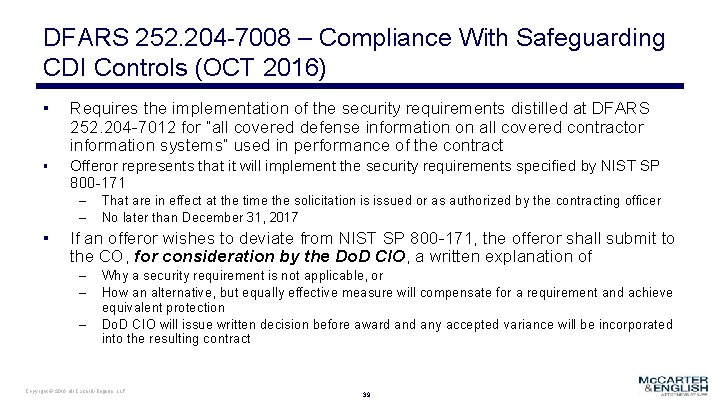
DFARS 252. 204 -7008 – Compliance With Safeguarding CDI Controls (OCT 2016) ▪ Requires the implementation of the security requirements distilled at DFARS 252. 204 -7012 for “all covered defense information on all covered contractor information systems” used in performance of the contract ▪ Offeror represents that it will implement the security requirements specified by NIST SP 800 -171 – – ▪ That are in effect at the time the solicitation is issued or as authorized by the contracting officer No later than December 31, 2017 If an offeror wishes to deviate from NIST SP 800 -171, the offeror shall submit to the CO, for consideration by the Do. D CIO, a written explanation of – – – Why a security requirement is not applicable, or How an alternative, but equally effective measure will compensate for a requirement and achieve equivalent protection Do. D CIO will issue written decision before award any accepted variance will be incorporated into the resulting contract Copyright © 2016 Mc. Carter & English, LLP 39
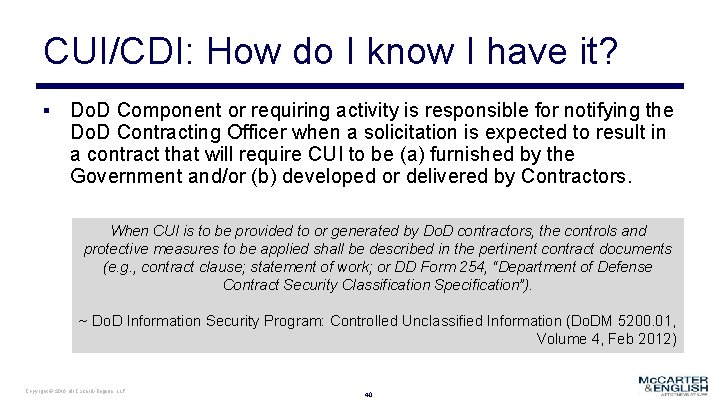
CUI/CDI: How do I know I have it? ▪ Do. D Component or requiring activity is responsible for notifying the Do. D Contracting Officer when a solicitation is expected to result in a contract that will require CUI to be (a) furnished by the Government and/or (b) developed or delivered by Contractors. When CUI is to be provided to or generated by Do. D contractors, the controls and protective measures to be applied shall be described in the pertinent contract documents (e. g. , contract clause; statement of work; or DD Form 254, “Department of Defense Contract Security Classification Specification”). ~ Do. D Information Security Program: Controlled Unclassified Information (Do. DM 5200. 01, Volume 4, Feb 2012) Copyright © 2016 Mc. Carter & English, LLP 40
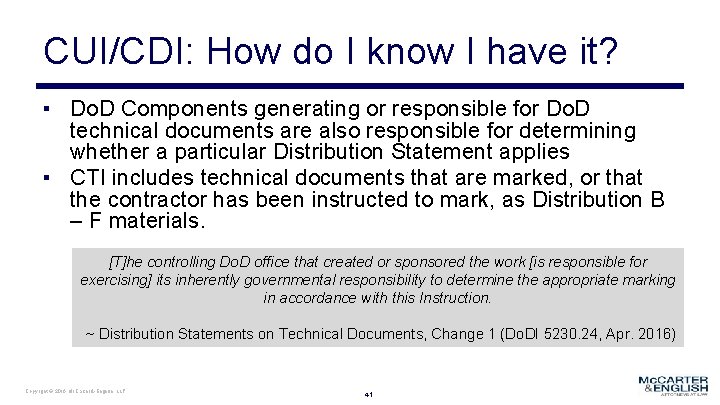
CUI/CDI: How do I know I have it? ▪ Do. D Components generating or responsible for Do. D technical documents are also responsible for determining whether a particular Distribution Statement applies ▪ CTI includes technical documents that are marked, or that the contractor has been instructed to mark, as Distribution B – F materials. [T]he controlling Do. D office that created or sponsored the work [is responsible for exercising] its inherently governmental responsibility to determine the appropriate marking in accordance with this Instruction. ~ Distribution Statements on Technical Documents, Change 1 (Do. DI 5230. 24, Apr. 2016) Copyright © 2016 Mc. Carter & English, LLP 41
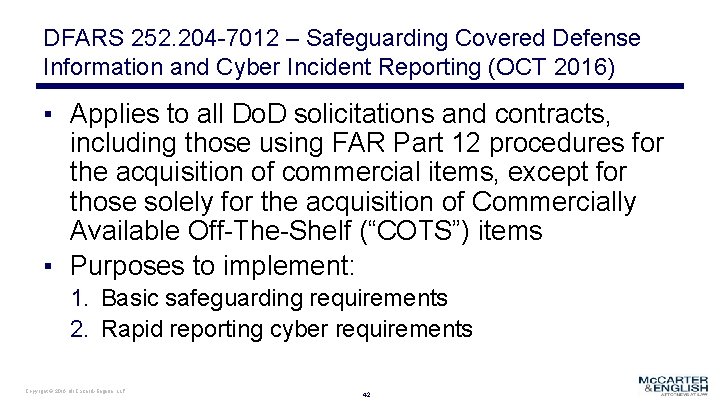
DFARS 252. 204 -7012 – Safeguarding Covered Defense Information and Cyber Incident Reporting (OCT 2016) ▪ Applies to all Do. D solicitations and contracts, including those using FAR Part 12 procedures for the acquisition of commercial items, except for those solely for the acquisition of Commercially Available Off-The-Shelf (“COTS”) items ▪ Purposes to implement: 1. Basic safeguarding requirements 2. Rapid reporting cyber requirements Copyright © 2016 Mc. Carter & English, LLP 42
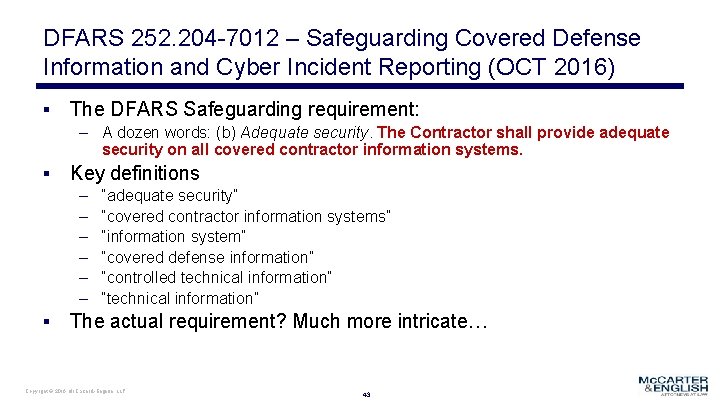
DFARS 252. 204 -7012 – Safeguarding Covered Defense Information and Cyber Incident Reporting (OCT 2016) ▪ The DFARS Safeguarding requirement: – A dozen words: (b) Adequate security. The Contractor shall provide adequate security on all covered contractor information systems. ▪ Key definitions – – – “adequate security” “covered contractor information systems” “information system” “covered defense information” “controlled technical information” “technical information” ▪ The actual requirement? Much more intricate… Copyright © 2016 Mc. Carter & English, LLP 43
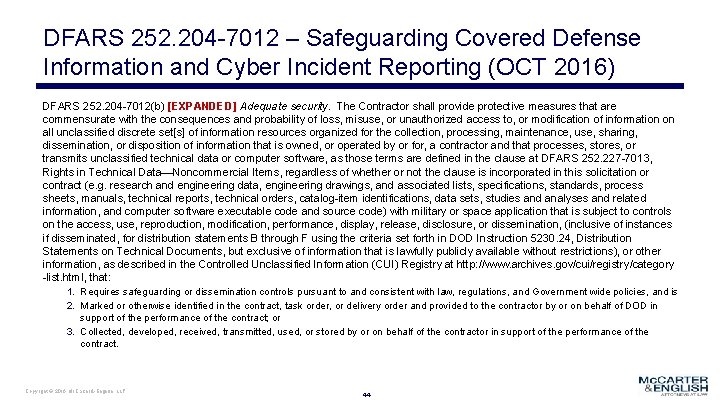
DFARS 252. 204 -7012 – Safeguarding Covered Defense Information and Cyber Incident Reporting (OCT 2016) DFARS 252. 204 -7012(b) [EXPANDED] Adequate security. The Contractor shall provide protective measures that are commensurate with the consequences and probability of loss, misuse, or unauthorized access to, or modification of information on all unclassified discrete set[s] of information resources organized for the collection, processing, maintenance, use, sharing, dissemination, or disposition of information that is owned, or operated by or for, a contractor and that processes, stores, or transmits unclassified technical data or computer software, as those terms are defined in the clause at DFARS 252. 227 -7013, Rights in Technical Data—Noncommercial Items, regardless of whether or not the clause is incorporated in this solicitation or contract (e. g. research and engineering data, engineering drawings, and associated lists, specifications, standards, process sheets, manuals, technical reports, technical orders, catalog-item identifications, data sets, studies and analyses and related information, and computer software executable code and source code) with military or space application that is subject to controls on the access, use, reproduction, modification, performance, display, release, disclosure, or dissemination, (inclusive of instances if disseminated, for distribution statements B through F using the criteria set forth in DOD Instruction 5230. 24, Distribution Statements on Technical Documents, but exclusive of information that is lawfully publicly available without restrictions), or other information, as described in the Controlled Unclassified Information (CUI) Registry at http: //www. archives. gov/cui/registry/category -list. html, that: 1. Requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and Government wide policies, and is 2. Marked or otherwise identified in the contract, task order, or delivery order and provided to the contractor by or on behalf of DOD in support of the performance of the contract; or 3. Collected, developed, received, transmitted, used, or stored by or on behalf of the contractor in support of the performance of the contract. Copyright © 2016 Mc. Carter & English, LLP 44
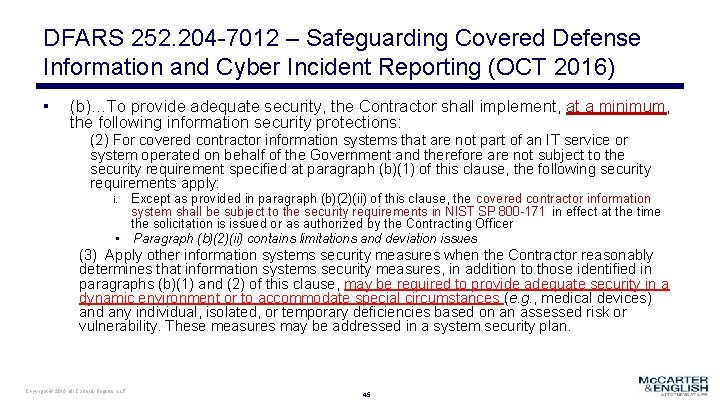
DFARS 252. 204 -7012 – Safeguarding Covered Defense Information and Cyber Incident Reporting (OCT 2016) ▪ (b)…To provide adequate security, the Contractor shall implement, at a minimum, the following information security protections: (2) For covered contractor information systems that are not part of an IT service or system operated on behalf of the Government and therefore are not subject to the security requirement specified at paragraph (b)(1) of this clause, the following security requirements apply: Except as provided in paragraph (b)(2)(ii) of this clause, the covered contractor information system shall be subject to the security requirements in NIST SP 800 -171 in effect at the time the solicitation is issued or as authorized by the Contracting Officer • Paragraph (b)(2)(ii) contains limitations and deviation issues i. (3) Apply other information systems security measures when the Contractor reasonably determines that information systems security measures, in addition to those identified in paragraphs (b)(1) and (2) of this clause, may be required to provide adequate security in a dynamic environment or to accommodate special circumstances (e. g. , medical devices) and any individual, isolated, or temporary deficiencies based on an assessed risk or vulnerability. These measures may be addressed in a system security plan. Copyright © 2016 Mc. Carter & English, LLP 45
NIST & DFARS Compliance THE BIGGER PICTURE Copyright © 2016 Mc. Carter & English, LLP 46
NIST SP 800 -171 – Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations ABSTRACT …[P]rovides federal agencies with recommended requirements for protecting the confidentiality of CUI: (i) when the CUI is resident in nonfederal information systems and organizations; (ii) when the information systems where the CUI resides are not used or operated by contractors of federal agencies or other organizations on behalf of those agencies; and (iii) where there are no specific safeguarding requirements for protecting the confidentiality of CUI prescribed by the authorizing law, regulation, or government-wide policy for the CUI category or subcategory listed in the CUI Registry. Copyright © 2016 Mc. Carter & English, LLP 47
NIST SP 800 -171 – Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations Cautionary Note In addition to the security objective of confidentiality, the objectives of integrity and availability remain a high priority for organizations that are concerned with establishing and maintaining a comprehensive information security program. While the primary purpose of this publication is to define requirements to protect the confidentiality of CUI, there is a close relationship between confidentiality and integrity since many of the underlying security mechanisms at the information system level support both security objectives. Organizations that are interested in or required to comply with the recommendations in this publication are strongly advised to review the complete listing of security controls in the moderate baseline in Appendix E to ensure that their individual security plans and security control deployments provide the necessary and sufficient protection to address the range of cyber and kinetic threats to organizational missions and business operations…. Copyright © 2016 Mc. Carter & English, LLP 48
NIST SP 800 -171 – What’s Missing? ▪ ▪ Built upon critical assumption that contractor has in place – Information security policies and procedures addressing all 14 of the security requirement families identified in 800 -171 – The creation and maintenance of security and audit records – A incident response plan – Plans to address privacy and security architecture, including supporting life cycle and configuration management plans – Codes of conduct that address cybersecurity and penalties for failing to abide Does not address data integrity and availability – Inadvertent deletion, changes – Data validity and accuracy – Data back up – Ransomware – Distributed denial of service attacks Copyright © 2016 Mc. Carter & English, LLP 49
DFARS 252. 204 -7012 – Safeguarding Covered Defense Information and Cyber Incident Reporting (OCT 2016) DFARS 252. 204 -7012(b) [EXPANDED] Adequate security. The Contractor shall provide protective measures that are commensurate with the consequences and probability of loss, misuse, or unauthorized access to, or modification of information on all unclassified discrete set[s] of information resources organized for the collection, processing, maintenance, use, sharing, dissemination, or disposition of information that is owned, or operated by or for, a contractor and that processes, stores, or transmits unclassified technical data or computer software, as those terms are defined in the clause at DFARS 252. 227 -7013, Rights in Technical Data—Noncommercial Items, regardless of whether or not the clause is incorporated in this solicitation or contract (e. g. research and engineering data, engineering drawings, and associated lists, specifications, standards, process sheets, manuals, technical reports, technical orders, catalog-item identifications, data sets, studies and analyses and related information, and computer software executable code and source code) with military or space application that is subject to controls on the access, use, reproduction, modification, performance, display, release, disclosure, or dissemination, (inclusive of instances if disseminated, for distribution statements B through F using the criteria set forth in DOD Instruction 5230. 24, Distribution Statements on Technical Documents, but exclusive of information that is lawfully publicly available without restrictions), or other information, as described in the Controlled Unclassified Information (CUI) Registry at http: //www. archives. gov/cui/registry/category-list. html, that: 1. Requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and Government wide policies, and is 2. Marked or otherwise identified in the contract, task order, or delivery order and provided to the contractor by or on behalf of DOD in support of the performance of the contract; or 3. Collected, developed, received, transmitted, used, or stored by or on behalf of the contractor in support of the performance of the contract. Copyright © 2016 Mc. Carter & English, LLP 50
That was a lot! Questions? We’re here to help… Alexander W. Major | Partner Franklin C. Turner | Partner Mc. CARTER & ENGLISH, LLP T: 202 -753 -3440 C: 410 -935 -0037 F: 202 -354 -4604 amajor@mccarter. com T: 202 -753 -3432 C: 757 -508 -8333 F: 202 -354 -4641 fturner@mccarter. com Copyright © 2016 Mc. Carter & English, LLP 51
- Slides: 51