Bootstrapping Trust in Commodity Computers Bryan Parno Jonathan
Bootstrapping Trust in Commodity Computers Bryan Parno, Jonathan Mc. Cune, Adrian Perrig Carnegie Mellon University 1
A Travel Story 2
Trust is Critical Will I regret having done this? 3
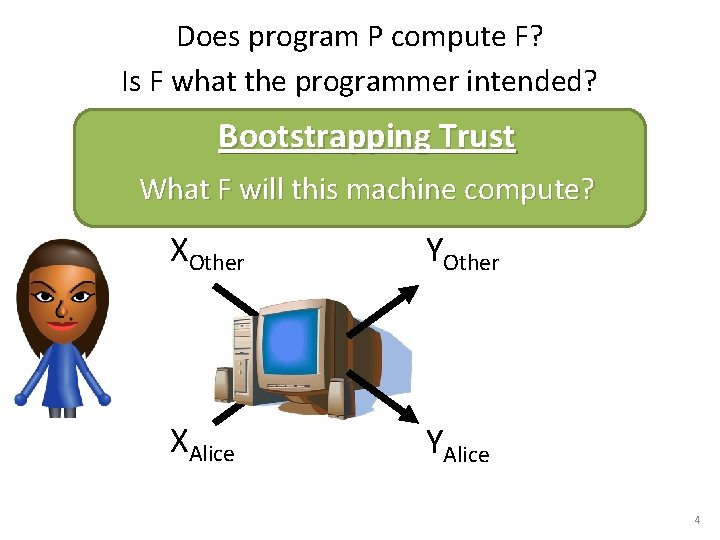
Does program P compute F? Is F what the programmer intended? Bootstrapping Trust What F will this machine compute? XOther YOther F XAlice YAlice 4
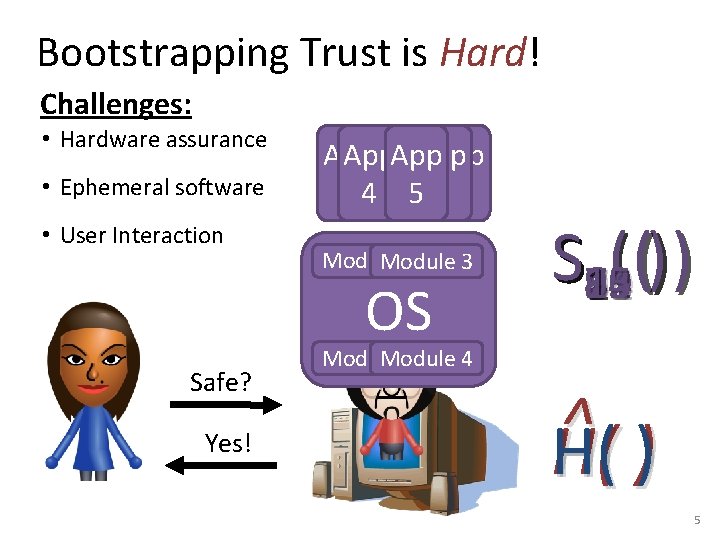
Bootstrapping Trust is Hard! Challenges: • Hardware assurance • Ephemeral software • User Interaction App App 1 4 5 N 23 Module 1 Module 3 OS Safe? Yes! S 15 ( ( ) ) 10 11 12 13 14 1 2 3 4 5 6 7 8 9 Module 4 Module 2 ^ H( ) 5
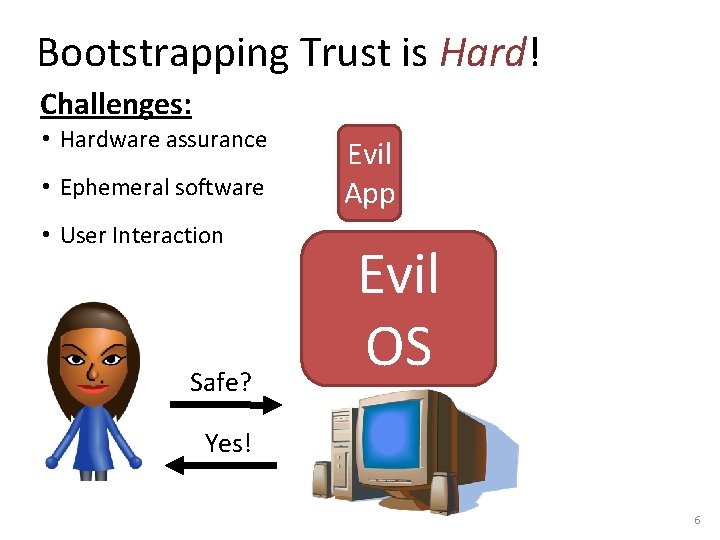
Bootstrapping Trust is Hard! Challenges: • Hardware assurance • Ephemeral software • User Interaction Safe? Evil App Evil OS Yes! 6
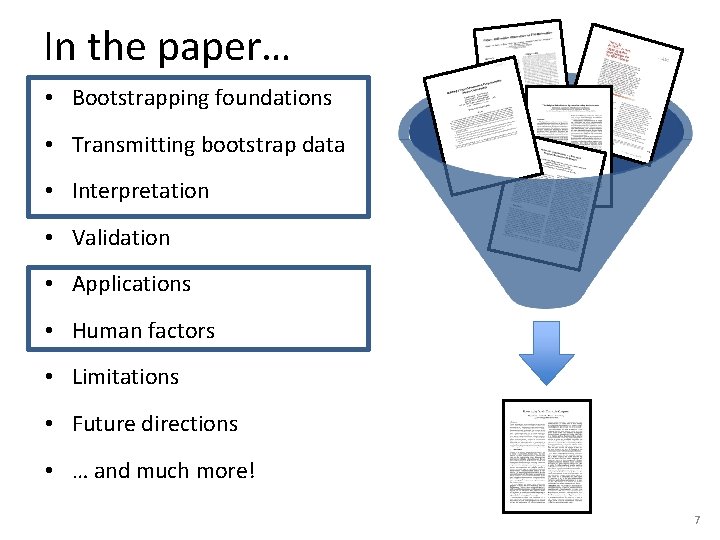
In the paper… • Bootstrapping foundations • Transmitting bootstrap data • Interpretation • Validation • Applications • Human factors • Limitations • Future directions • … and much more! 7
1) Establish Trust in Hardware • Hardware is durable • Establish trust via: – Trust in the manufacturer Open Question : Can we do better? – Physical security 8
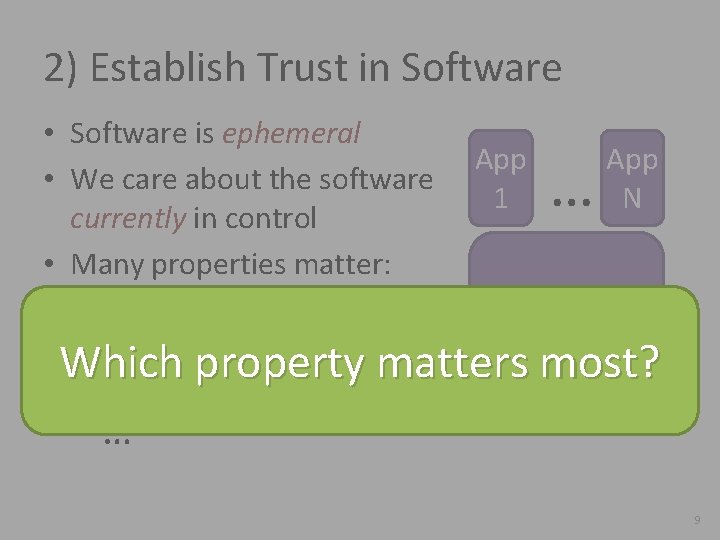
2) Establish Trust in Software • Software is ephemeral • We care about the software currently in control • Many properties matter: – Proper control flow – Type safety – Correct information flow App 1 … App N OS Which property matters most? … 9
A Simple Thought Experiment • Imagine a perfect algorithm for analyzing control flow – Guarantees a program always follows intended control flow • Does this suffice to bootstrap trust? Respects Type Safe control flow No! We want code identity P 10
What is Code Identity? • An attempt to capture the behavior of a program • Current state of the art is the collection of: – – Program binary Function f Program libraries Program configuration files Inputs to f Initial inputs • Often condensed into a hash of the above 11
Code Identity as Trust Foundation • From code identity, you may be able to infer: – Proper control flow – Type safety – Correct information flow … • Reverse is not true! 12
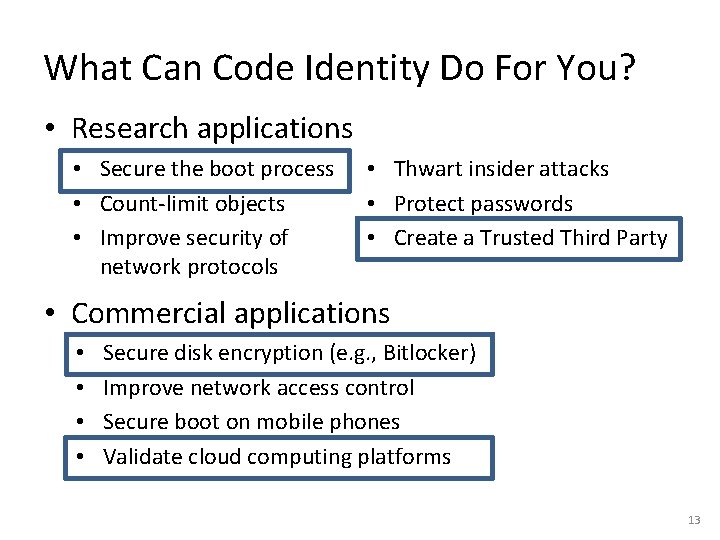
What Can Code Identity Do For You? • Research applications • Secure the boot process • Count-limit objects • Improve security of network protocols • Thwart insider attacks • Protect passwords • Create a Trusted Third Party • Commercial applications • • Secure disk encryption (e. g. , Bitlocker) Improve network access control Secure boot on mobile phones Validate cloud computing platforms 13
![Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-14.jpg)
Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer et al. ‘ 04], [Marchesini et al. ‘ 04], … YOther XOther F XAlice YAlice 14
![Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-15.jpg)
Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer et al. ‘ 04], [Marchesini et al. ‘ 04], … YOther XOther f 1 XAlice f 2 … f. N YAlice 15
![Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-16.jpg)
Establishing Code Identity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [Sailer et al. ‘ 04], [Marchesini et al. ‘ 04], … Chain of Trust Root of Trust ? Software 1 . . . Software N-1 Software N 16
![Trusted Boot: Recording Code Identity Root of Trust [Gasser et al. ’ 89], [England Trusted Boot: Recording Code Identity Root of Trust [Gasser et al. ’ 89], [England](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-17.jpg)
Trusted Boot: Recording Code Identity Root of Trust [Gasser et al. ’ 89], [England et al. ‘ 03], [Sailer et al. ‘ 04], … Software 1 SW 1 . . . SW 2 Software N-1 SW N-1 Software N SW N 17
![Attestation: Conveying Records to an External Entity [Gasser et al. ‘ 89], [Arbaugh et Attestation: Conveying Records to an External Entity [Gasser et al. ‘ 89], [Arbaugh et](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-18.jpg)
Attestation: Conveying Records to an External Entity [Gasser et al. ‘ 89], [Arbaugh et al. ‘ 97], [England et al. ‘ 03], [Sailer et al. ’ 04]… Software random # N-1 1 . . . Sign SW 1 ( Kpriv SW SW 1 2 N-1 N SW 2 random. SW # Software N ) N-1 SW N Controls Kpriv 18
![Interpreting Code Identity App 1…N Drivers 1…N Traditional [Gasser et al. ‘ 89], [Sailer Interpreting Code Identity App 1…N Drivers 1…N Traditional [Gasser et al. ‘ 89], [Sailer](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-19.jpg)
Interpreting Code Identity App 1…N Drivers 1…N Traditional [Gasser et al. ‘ 89], [Sailer et al. ‘ 04] Policy Enforcement [Marchesini et al. ‘ 04], [Jaeger et al. ’ 06] OS Bootloader Option ROMs BIOS 19
![Interpreting Code Identity Traditional [Gasser et al. ‘ 89], [Sailer et al. ‘ 04] Interpreting Code Identity Traditional [Gasser et al. ‘ 89], [Sailer et al. ‘ 04]](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-20.jpg)
Interpreting Code Identity Traditional [Gasser et al. ‘ 89], [Sailer et al. ‘ 04] Virtual Machine Policy Enforcement [Marchesini et al. ‘ 04], [Jaeger et al. ’ 06] Virtualization [England et al. ‘ 03], [Garfinkel et al. ‘ 03] Virtual Machine Monitor Bootloader Option ROMs BIOS 20
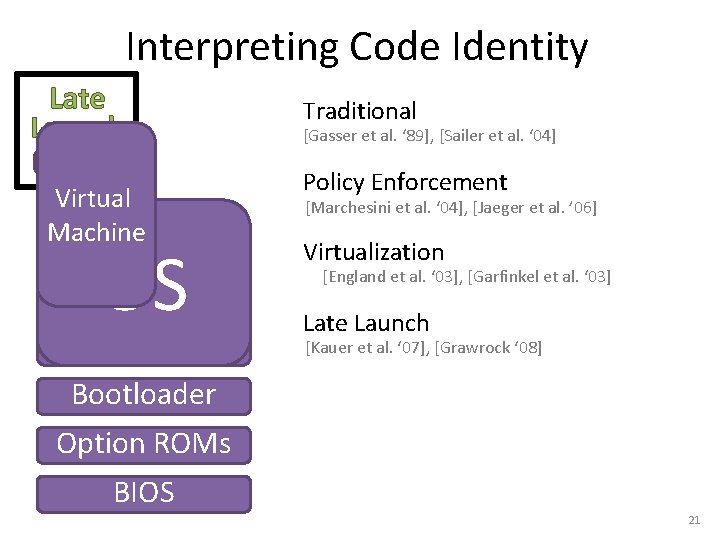
Interpreting Code Identity Late Launch VMM Virtual Machine OS Virtual Machine Monitor Traditional [Gasser et al. ‘ 89], [Sailer et al. ‘ 04] Policy Enforcement [Marchesini et al. ‘ 04], [Jaeger et al. ’ 06] Virtualization [England et al. ‘ 03], [Garfinkel et al. ‘ 03] Late Launch [Kauer et al. ‘ 07], [Grawrock ‘ 08] Bootloader Option ROMs BIOS 21
![Interpreting Code Identity Late Launch Traditional [Gasser et al. ‘ 89], [Sailer et al. Interpreting Code Identity Late Launch Traditional [Gasser et al. ‘ 89], [Sailer et al.](http://slidetodoc.com/presentation_image/1e4e8209dcc611274ad577c00da66ebd/image-22.jpg)
Interpreting Code Identity Late Launch Traditional [Gasser et al. ‘ 89], [Sailer et al. ‘ 04] Flicker Policy Enforcement [Marchesini et al. ‘ 04], [Jaeger et al. ’ 06] OS S Virtualization [England et al. ‘ 03], [Garfinkel et al. ‘ 03] Late Launch [Kauer et al. ‘ 07], [Grawrock ‘ 08] Flicker Targeted Late Launch [Mc. Cune et al. ‘ 07] Attested 22
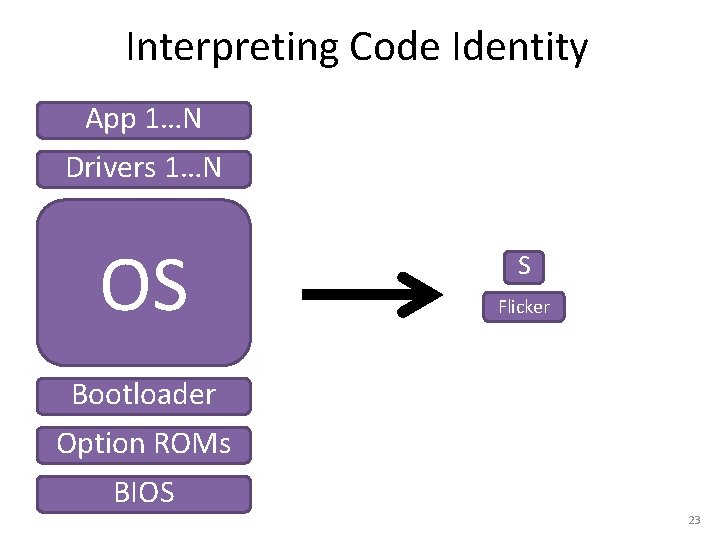
Interpreting Code Identity App 1…N Drivers 1…N OS S Flicker Bootloader Option ROMs BIOS 23
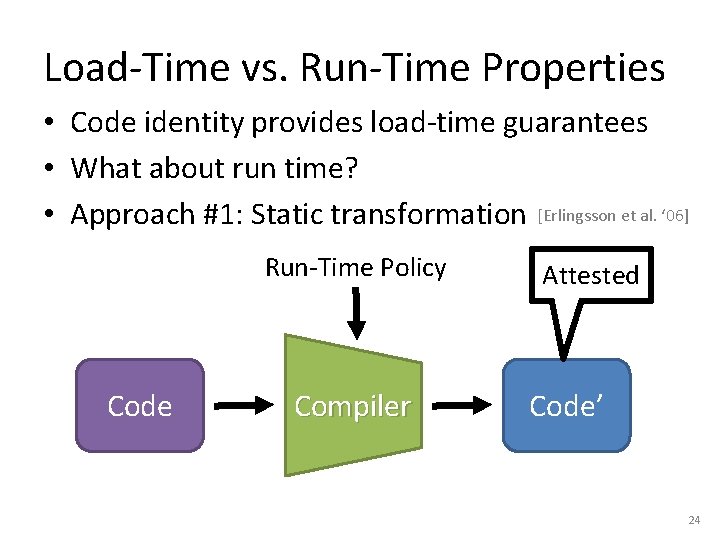
Load-Time vs. Run-Time Properties • Code identity provides load-time guarantees • What about run time? • Approach #1: Static transformation [Erlingsson et al. ‘ 06] Run-Time Policy Code Compiler Attested Code’ 24
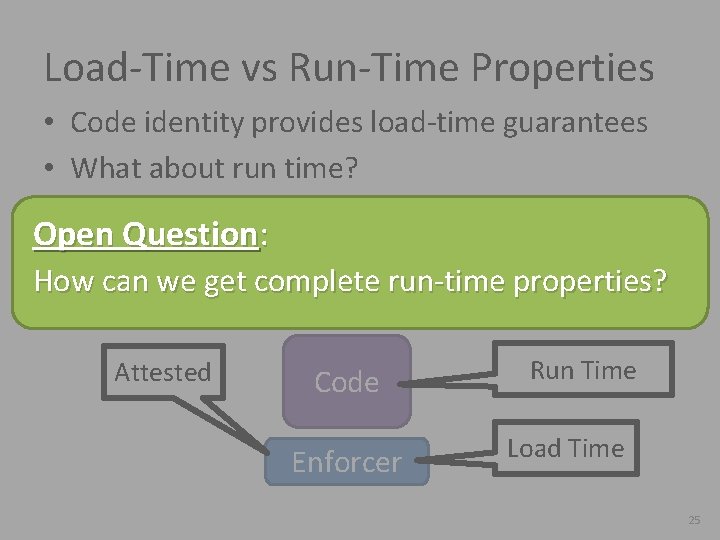
Load-Time vs Run-Time Properties • Code identity provides load-time guarantees • What about run time? • Approach #1: Static transformation [Erlingsson et al. ‘ 06] Open Question: • Approach #2: Run-Time Enforcement layer How can we get complete run-time [Haldar et al. ‘ 04], properties? [Kil et al. ‘ 09] Attested Code Enforcer Run Time Load Time 25
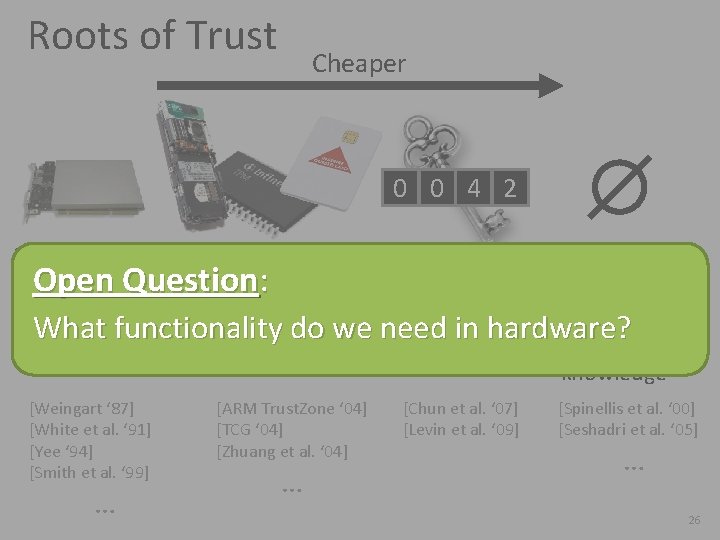
Roots of Trust Cheaper 0 0 4 2 • General • Special • Timing-based purpose attestation Open Question : • Tamper • No physical • Require What functionality do we need in hardware? responding defenses detailed HW knowledge [Weingart ‘ 87] [White et al. ‘ 91] [Yee ‘ 94] [Smith et al. ‘ 99] … [ARM Trust. Zone ‘ 04] [TCG ‘ 04] [Zhuang et al. ‘ 04] … [Chun et al. ‘ 07] [Levin et al. ‘ 09] [Spinellis et al. ‘ 00] [Seshadri et al. ‘ 05] … 26
Human Factors SW SW 1 2 N-1 N Open Questions: SW SW How should SW 1 SW 2 N-1 be communicated to Alice? N What does Alice do with a failed attestation? How can Alice trust her device? 27
Conclusions • Code identity is critical to bootstrapping trust • Assorted hardware roots of trust available • Many open questions remain! Thank you! parno@cmu. edu 28
- Slides: 28