Bluetooth 1 Applications Technology And Performance Bluetooth A
Bluetooth: 1. Applications, Technology And Performance
Bluetooth < A cable replacement technology < 1 Mb/s symbol rate Why not use Wireless LANs? - power < Single chip radio + baseband - cost 4 at low power & low price point ($5) < Range 10+ meters
802. 11 < Replacement for Ethernet < Supported data rates 4 11, 5. 5, 2, 1 Mbps; and recently up to 20+Mbps @ 2. 4 GHz 4 up to 54 Mbps in 5. 7 GHz band (802. 11 a) < Range 4 Indoor 20 - 25 meters 4 Outdoor: 50 – 100 meters < Transmit power up to 100 m. W < Cost: 4 Chipsets $ 35 – 50 4 AP $200 - $1000 4 PCMCIA cards $100 - $150
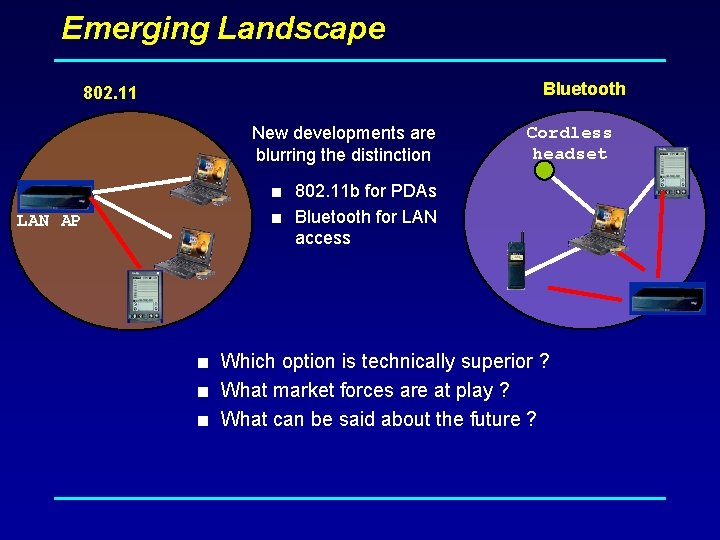
Emerging Landscape Bluetooth 802. 11 New developments are blurring the distinction Cordless headset < 802. 11 b for PDAs LAN AP < Bluetooth for LAN access < Which option is technically superior ? < What market forces are at play ? < What can be said about the future ?
Bluetooth working group history < February 1998: The Bluetooth SIG is formed 4 promoter company group: Ericsson, IBM, Intel, Nokia, Toshiba < May 1998: Public announcement of the Bluetooth SIG < July 1999: 1. 0 A spec (>1, 500 pages) is published < December 1999: ver. 1. 0 B is released < December 1999: The promoter group increases to 9 4 3 Com, Lucent, Microsoft, Motorola < March 2001: ver. 1. 1 is released < Aug 2001: There are 2, 491+ adopter companies
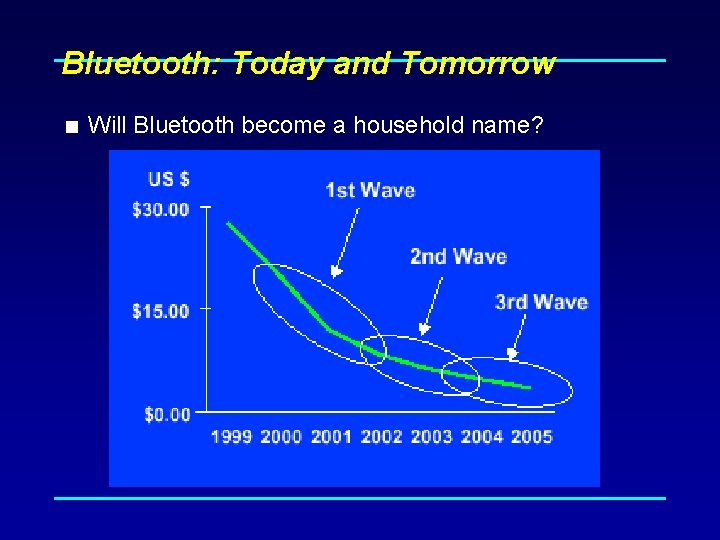
Bluetooth: Today and Tomorrow < Will Bluetooth become a household name?

New Applications
Synchronization User benefits < Automatic synchronization of calendars, address books, business cards < Push button synchronization < Proximity operation
Cordless Headset Cordless headset User benefits < Multiple device access < Cordless phone benefits < Hands free operation
Usage scenarios examples < Data Access Points < Synchronization < Headset < Conference Table < Cordless Computer < Business Card Exchange < Instant Postcard < Computer Speakerphone

Bluetooth. Technical overview and Protocol
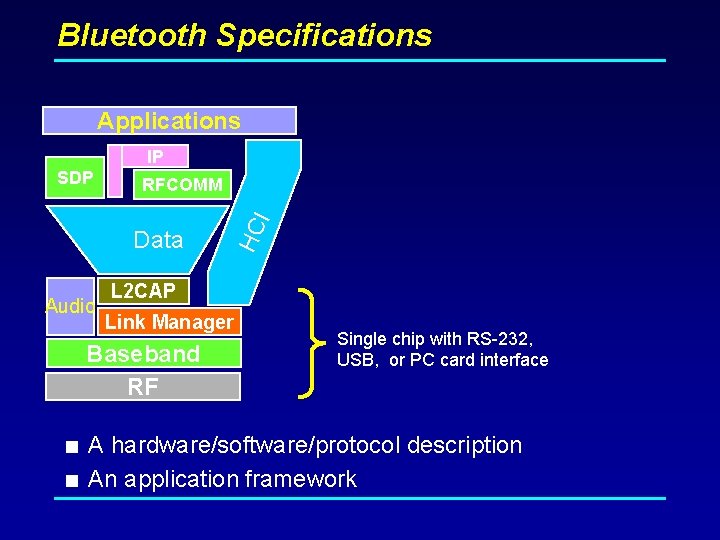
Bluetooth Specifications Applications IP RFCOMM Data Audio HC I SDP L 2 CAP Link Manager Baseband RF Single chip with RS-232, USB, or PC card interface < A hardware/software/protocol description < An application framework
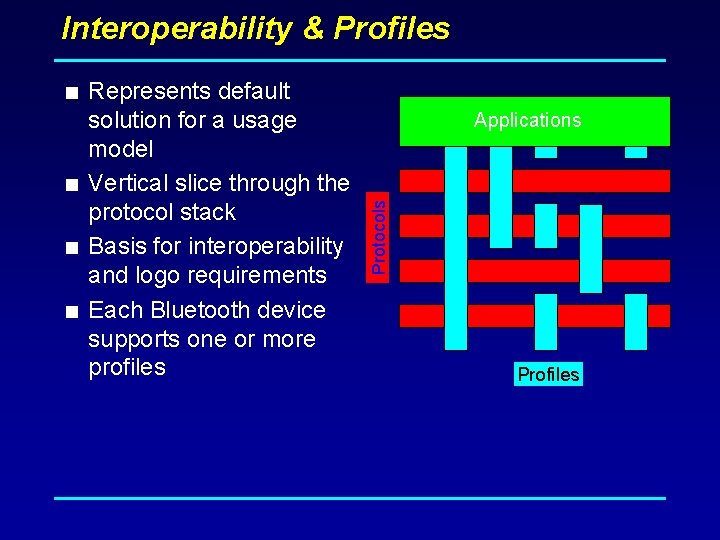
Interoperability & Profiles < Represents default Applications Protocols solution for a usage model < Vertical slice through the protocol stack < Basis for interoperability and logo requirements < Each Bluetooth device supports one or more profiles Profiles
Bluetooth Profiles (in version 1. 2 release) < Generic Access (discovery of Bluetooth devices) < Service Discovery (establish connection and Discover available services and connects devices) < Cordless Telephone < Intercom < Serial Port < Headset < Dial-up Networking < Fax < LAN Access < Generic Object Exchange < Object Push < File Transfer < Synchronization
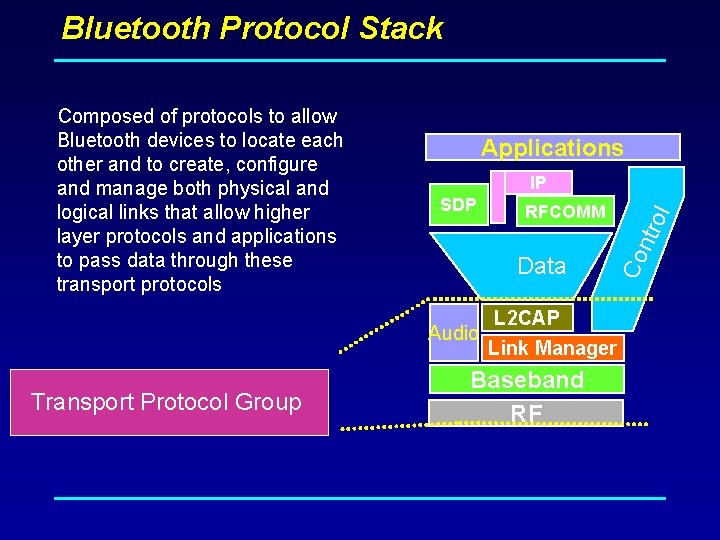
Bluetooth Protocol Stack Applications IP Data Audio Transport Protocol Group RFCOMM rol SDP Co nt Composed of protocols to allow Bluetooth devices to locate each other and to create, configure and manage both physical and logical links that allow higher layer protocols and applications to pass data through these transport protocols L 2 CAP Link Manager Baseband RF
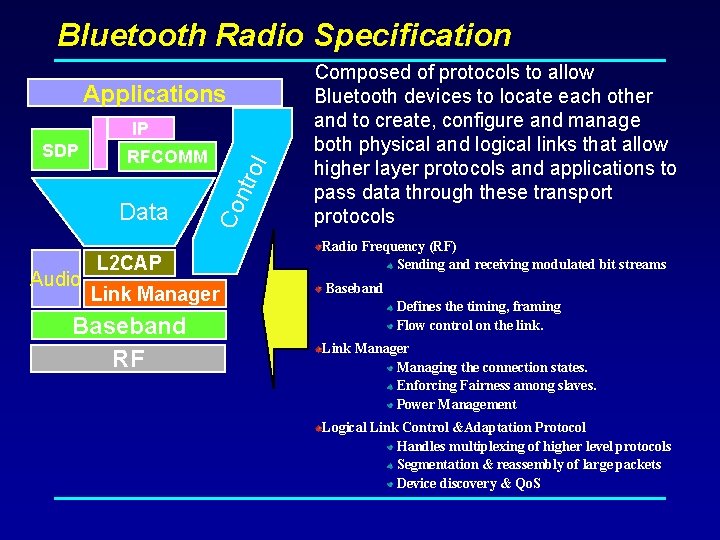
Bluetooth Radio Specification Applications IP Data Audio ol RFCOMM Co ntr SDP L 2 CAP Link Manager Baseband RF Composed of protocols to allow Bluetooth devices to locate each other and to create, configure and manage both physical and logical links that allow higher layer protocols and applications to pass data through these transport protocols Radio Frequency (RF) Sending and receiving modulated bit streams Baseband Defines the timing, framing Flow control on the link. Link Manager Managing the connection states. Enforcing Fairness among slaves. Power Management Logical Link Control &Adaptation Protocol Handles multiplexing of higher level protocols Segmentation & reassembly of large packets Device discovery & Qo. S
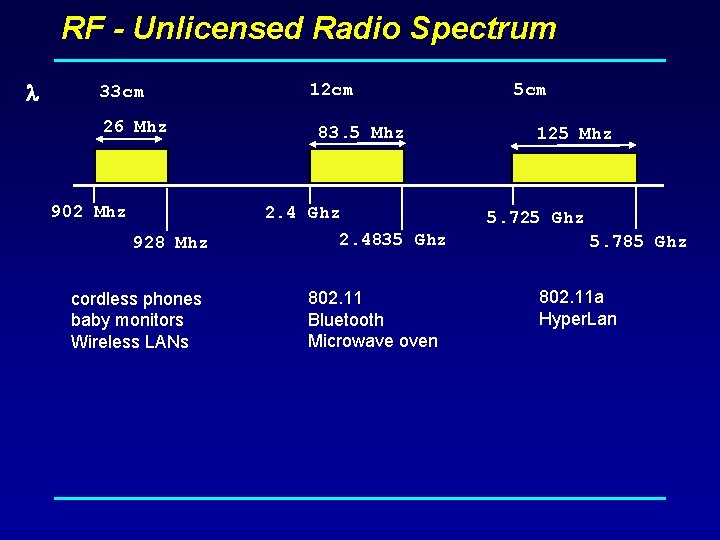
RF - Unlicensed Radio Spectrum 33 cm 26 Mhz 902 Mhz 12 cm 83. 5 Mhz 2. 4 Ghz 928 Mhz cordless phones baby monitors Wireless LANs 2. 4835 Ghz 802. 11 Bluetooth Microwave oven 5 cm 125 Mhz 5. 725 Ghz 5. 785 Ghz 802. 11 a Hyper. Lan
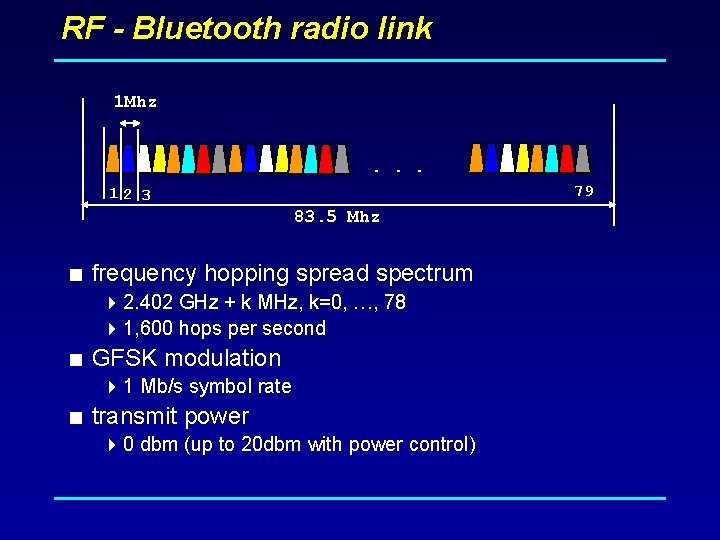
RF - Bluetooth radio link 1 Mhz . . . 79 12 3 83. 5 Mhz < frequency hopping spread spectrum 4 2. 402 GHz + k MHz, k=0, …, 78 4 1, 600 hops per second < GFSK modulation 4 1 Mb/s symbol rate < transmit power 4 0 dbm (up to 20 dbm with power control)
GFSK Differences & Advantages over FSK Modulation < Q: What are the physical Differences between an FSK & GFSK Modulator, and how do their results vary? < A 1: An FSK Modulator is much the same as a GFSK Modulator, but GFSK uses a Gaussian filter as well. In a GFSK modulator everything is the same as a FSK modulator except that before the baseband pulses (-1, 1) go into the FSK modulator, it is passed through a gaussian filter to make the pulse smoother so to limit its spectral width < A 2: Gaussian filtering is one of the very standard ways for reducing the spectral width, it is called Pulse Shaping. If we use -1 for fc-fd and 1 for fc+fd, once when we jump from -1 to 1 or 1 to -1, the modulated waveform changes rapidly, which introduces large out-of-band spectrum. If we change the pulse going from -1 to 1 as -1, -. 98, -. 93. . . 96, . 99, 1, and we use this smoother pulse to modulate the carrier, the out-of-band spectrum will be reduced.
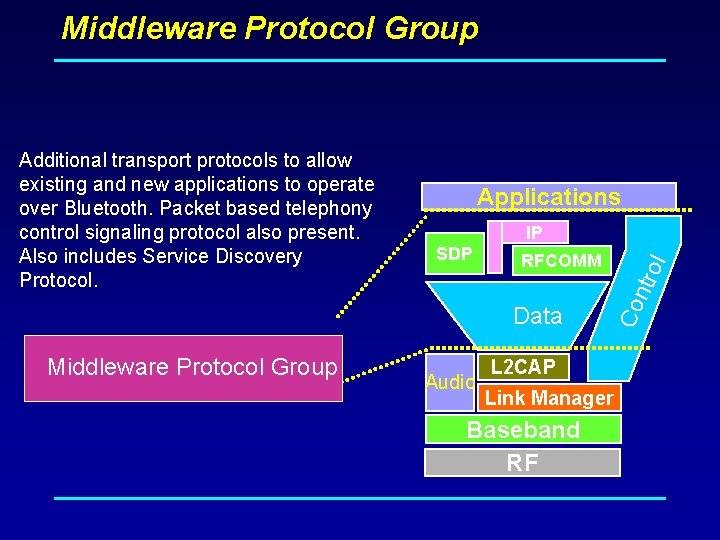
Middleware Protocol Group Applications IP RFCOMM Data Middleware. Protocol. Group Audio rol SDP Co nt Additional transport protocols to allow existing and new applications to operate over Bluetooth. Packet based telephony control signaling protocol also present. Also includes Service Discovery Protocol. L 2 CAP Link Manager Baseband RF
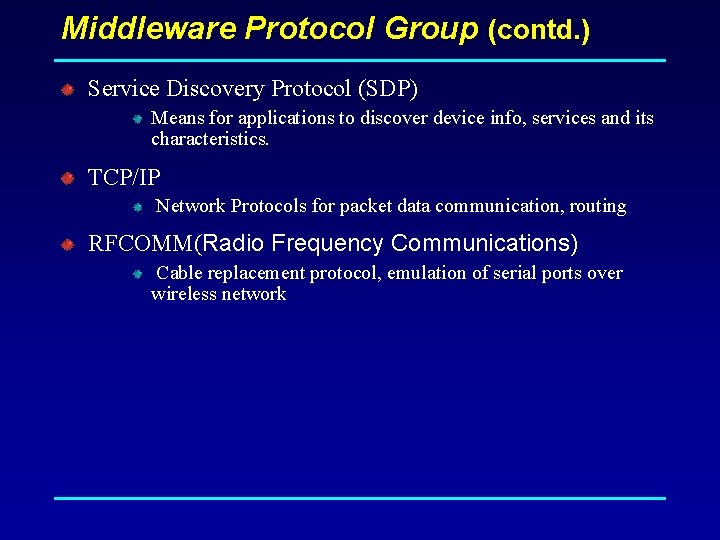
Middleware Protocol Group (contd. ) Service Discovery Protocol (SDP) Means for applications to discover device info, services and its characteristics. TCP/IP Network Protocols for packet data communication, routing RFCOMM(Radio Frequency Communications) Cable replacement protocol, emulation of serial ports over wireless network
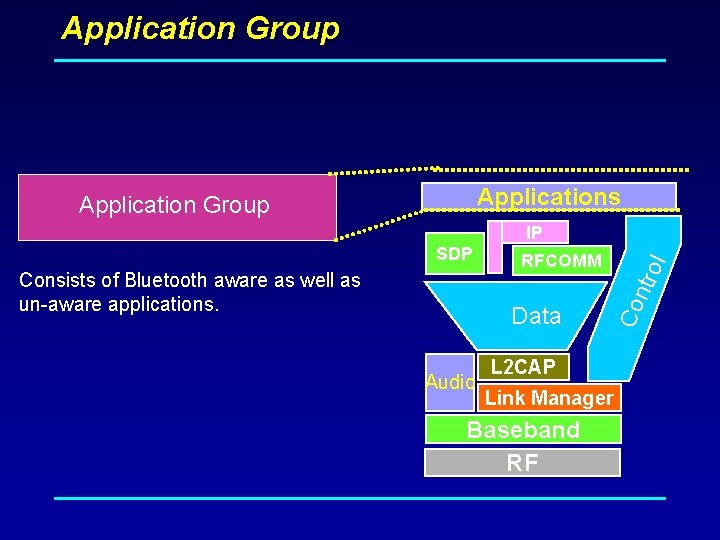
Application Group Applications Application Group IP Data Audio rol Consists of Bluetooth aware as well as un-aware applications. RFCOMM Co nt SDP L 2 CAP Link Manager Baseband RF
Review Format And Power Mode
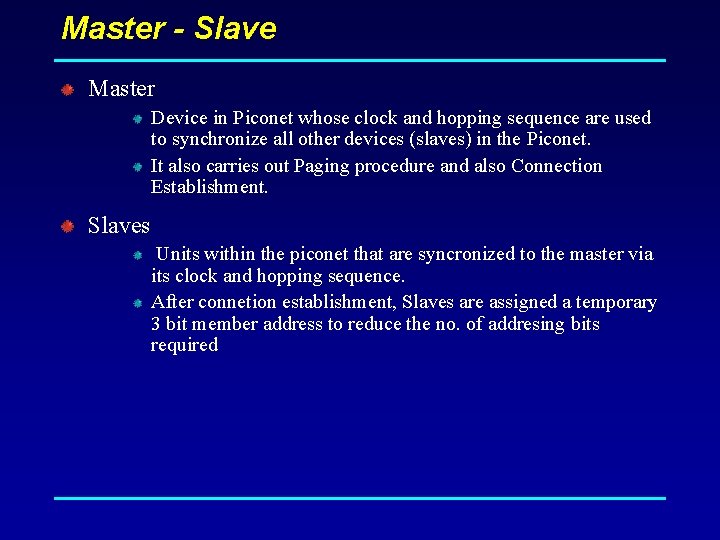
Master - Slave Master Device in Piconet whose clock and hopping sequence are used to synchronize all other devices (slaves) in the Piconet. It also carries out Paging procedure and also Connection Establishment. Slaves Units within the piconet that are syncronized to the master via its clock and hopping sequence. After connetion establishment, Slaves are assigned a temporary 3 bit member address to reduce the no. of addresing bits required
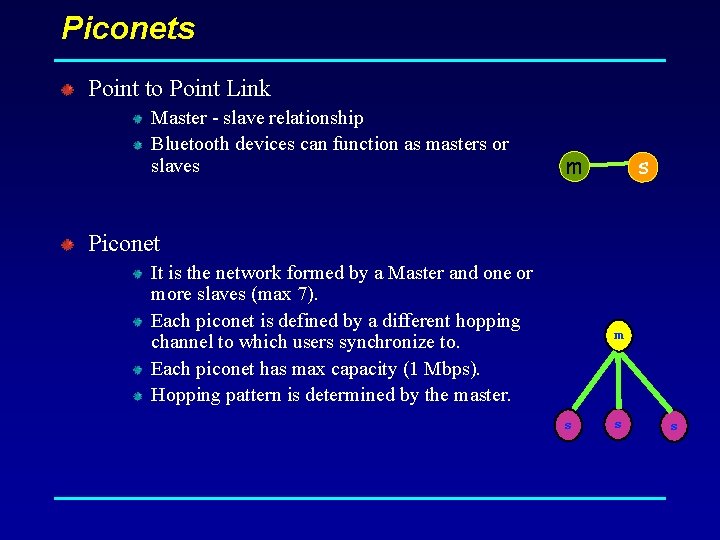
Piconets Point to Point Link Master - slave relationship Bluetooth devices can function as masters or slaves m s Piconet It is the network formed by a Master and one or more slaves (max 7). Each piconet is defined by a different hopping channel to which users synchronize to. Each piconet has max capacity (1 Mbps). Hopping pattern is determined by the master. m s s s
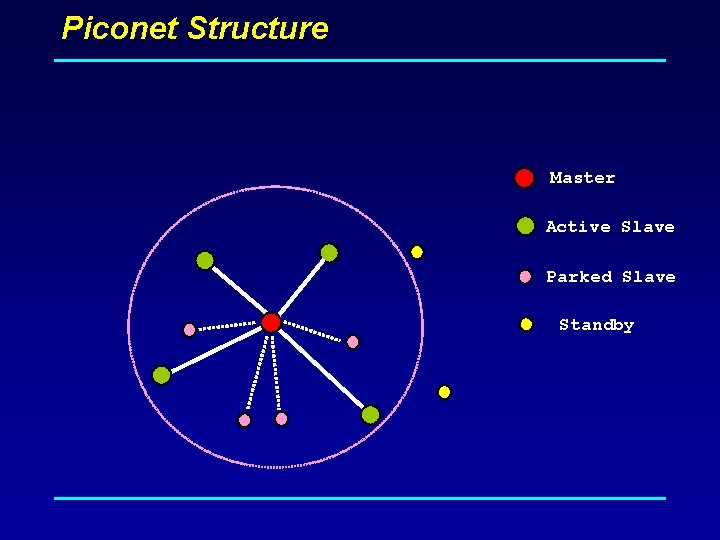
Piconet Structure Master Active Slave Parked Slave Standby
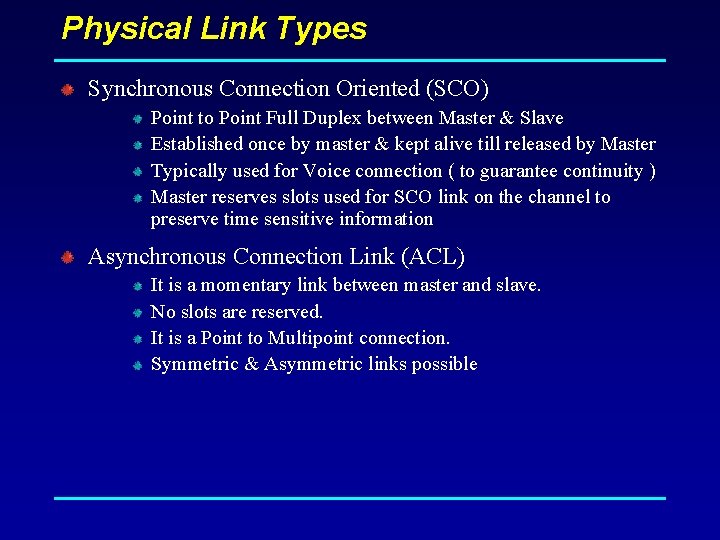
Physical Link Types Synchronous Connection Oriented (SCO) Point to Point Full Duplex between Master & Slave Established once by master & kept alive till released by Master Typically used for Voice connection ( to guarantee continuity ) Master reserves slots used for SCO link on the channel to preserve time sensitive information Asynchronous Connection Link (ACL) It is a momentary link between master and slave. No slots are reserved. It is a Point to Multipoint connection. Symmetric & Asymmetric links possible
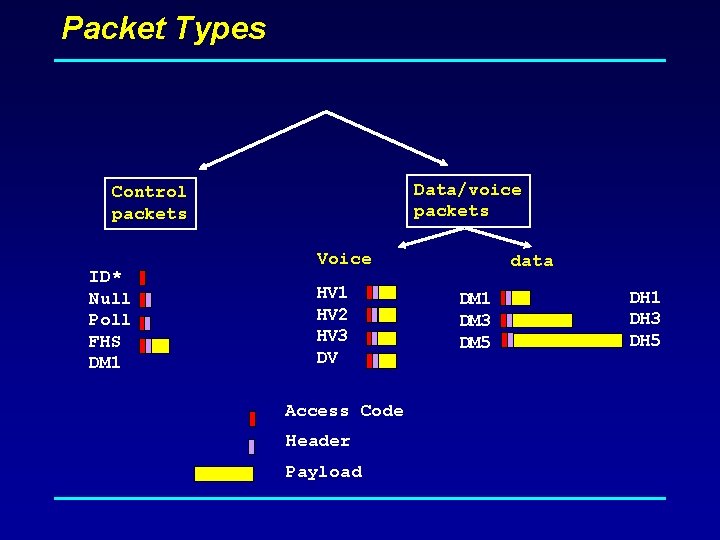
Packet Types Data/voice packets Control packets ID* Null Poll FHS DM 1 Voice HV 1 HV 2 HV 3 DV Access Code Header Payload data DM 1 DM 3 DM 5 DH 1 DH 3 DH 5
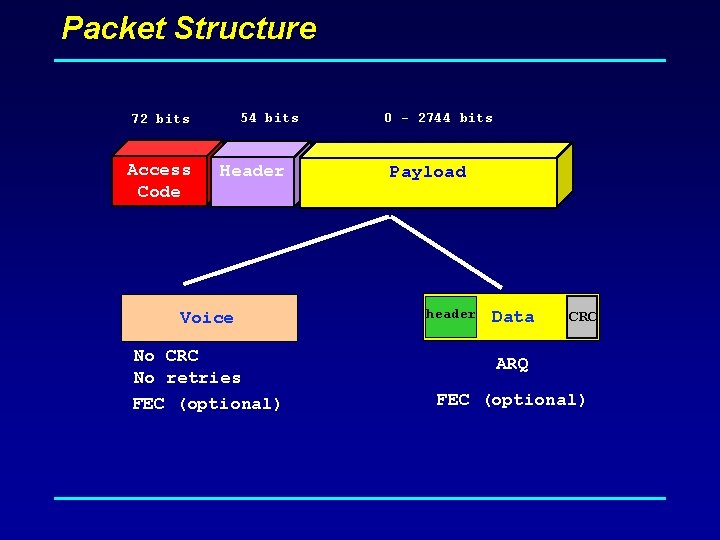
Packet Structure 54 bits 72 bits Access Code Header Voice No CRC No retries FEC (optional) 0 - 2744 bits Payload header Data CRC ARQ FEC (optional)
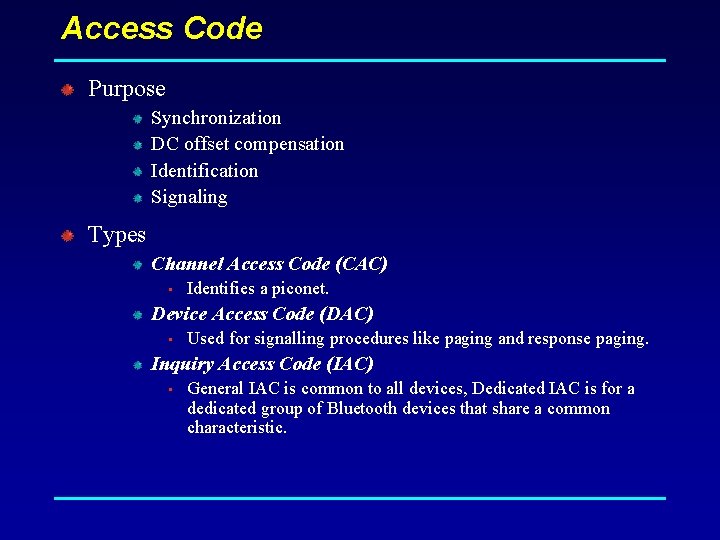
Access Code Purpose Synchronization DC offset compensation Identification Signaling Types Channel Access Code (CAC) • Identifies a piconet. Device Access Code (DAC) • Used for signalling procedures like paging and response paging. Inquiry Access Code (IAC) • General IAC is common to all devices, Dedicated IAC is for a dedicated group of Bluetooth devices that share a common characteristic.
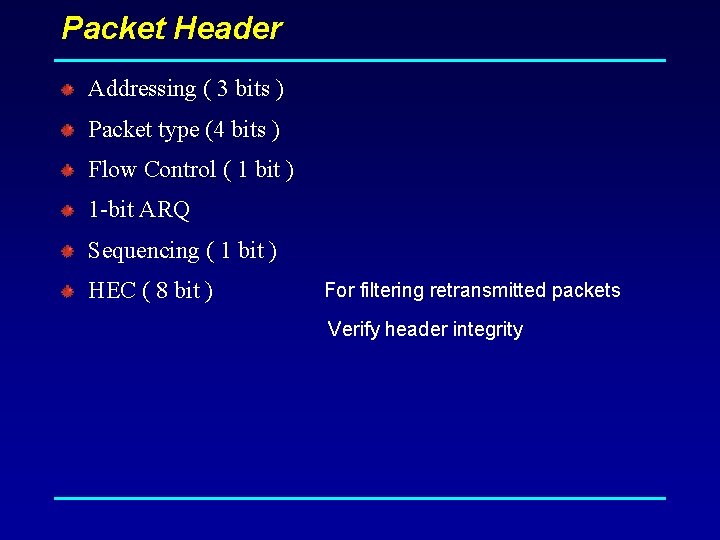
Packet Header Addressing ( 3 bits ) Packet type (4 bits ) Flow Control ( 1 bit ) 1 -bit ARQ Sequencing ( 1 bit ) HEC ( 8 bit ) For filtering retransmitted packets Verify header integrity
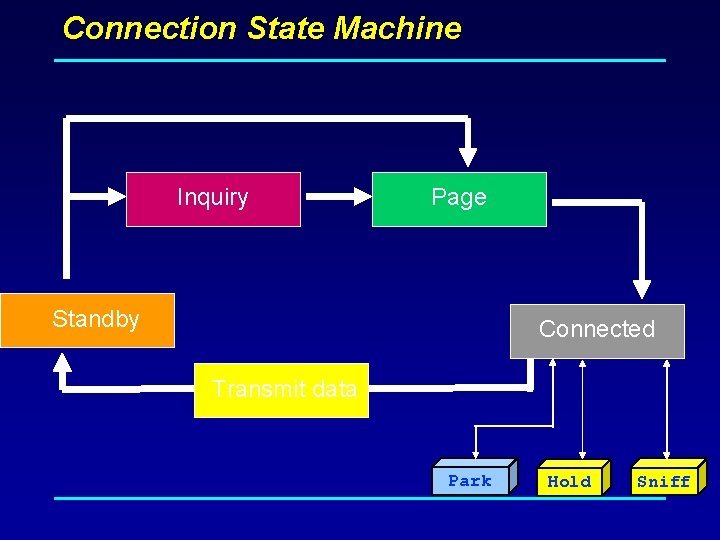
Connection State Machine Inquiry Page Standby Connected Transmit data Park Hold Sniff
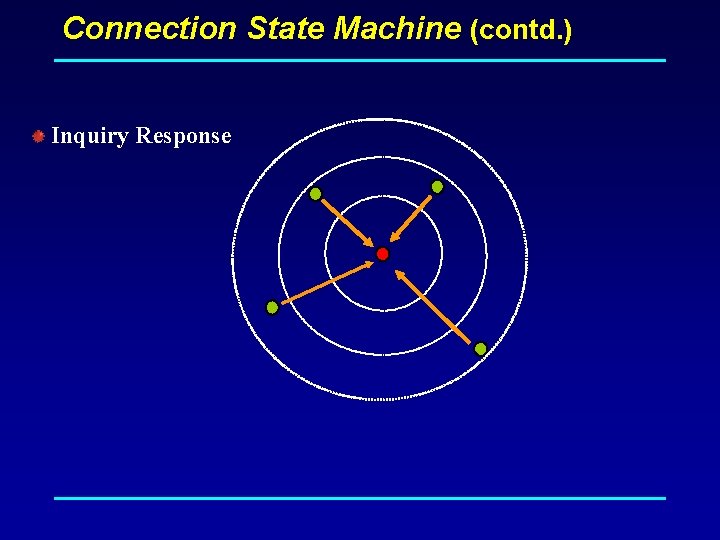
Connection State Machine (contd. ) Inquiry Scan A device that wants to be discovered will periodically enter this mode and listen for inquiry packets. Inquiry Device sends an Inquiry packet addressed to GIAC or DIAC Transmission is repeated on the inquiry hop sequence of frequencies. Inquiry Response When an inquiry message is received in the inquiry scan state, a response packet (FHS) containing the responding device address must be sent after a random number of slots.
Connection State Machine (contd. ) Inquiry Response
Connection State Machine (contd. ) Page The master uses the clock information, about the slave to be paged, to determine where in the hop sequence, the slave might be listening in the page scan mode. The master sends a page message Page Scan The page scan substate can be entered by the slave from the standby state or the connection state. It listens to packets addressed to its DAC. Page Response On receiving the page message, the slave enters the slave page response substate. It sends back a page response consisting of its ID packet which contains its DAC, at the frequency for the next slot from the one in which page message was received.
Security Measures Limited/Restricted Access to authorized users. Both Link Level Encryption & Authentication. Personal Identification Numbers (PIN) for device access. Long encryption keys are used (128 bit keys). These keys are not transmitted over wireless. Other parameters are transmitted over wireless which in combination with certain information known to the device, can generate the keys. Further encryption can be done at the application layer. Security values Device Address-Public Authentication Key(128 bits)-Private Encryption Key(8 -128 bits)-Private Random Number
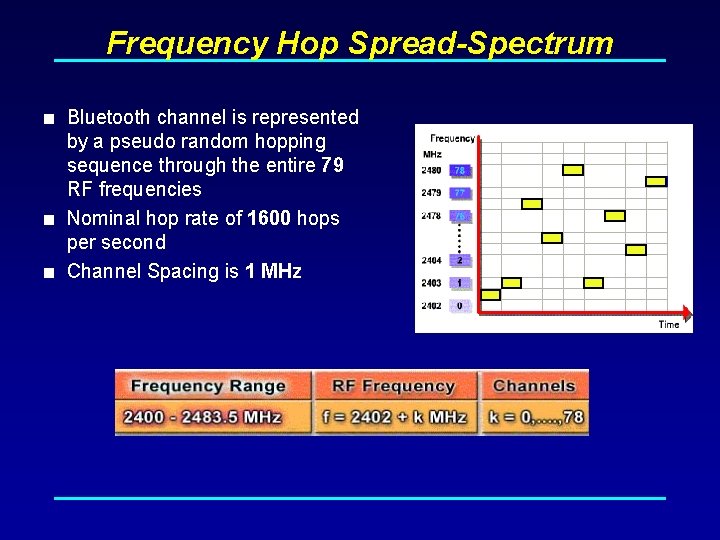
Frequency Hop Spread-Spectrum < Bluetooth channel is represented by a pseudo random hopping sequence through the entire 79 RF frequencies < Nominal hop rate of 1600 hops per second < Channel Spacing is 1 MHz
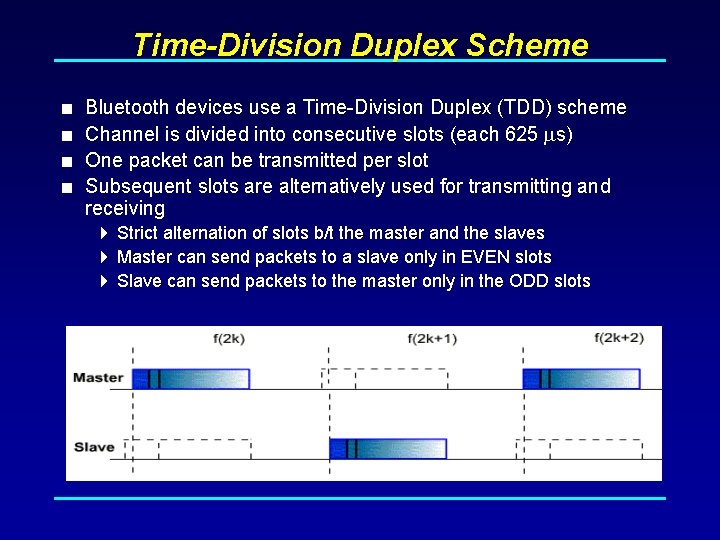
Time-Division Duplex Scheme < Bluetooth devices use a Time-Division Duplex (TDD) scheme < Channel is divided into consecutive slots (each 625 s) < One packet can be transmitted per slot < Subsequent slots are alternatively used for transmitting and receiving 4 Strict alternation of slots b/t the master and the slaves 4 Master can send packets to a slave only in EVEN slots 4 Slave can send packets to the master only in the ODD slots
Review of basic concepts
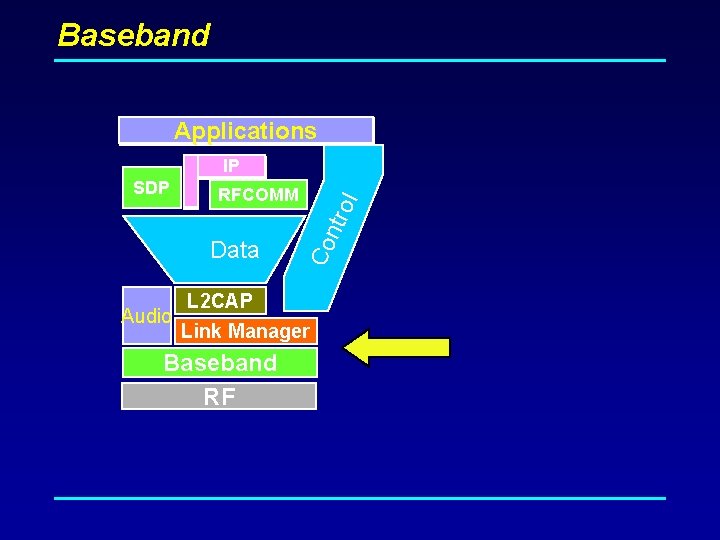
Baseband Applications Audio ol ntr Data Co SDP IP RFCOMM L 2 CAP Link Manager Baseband RF
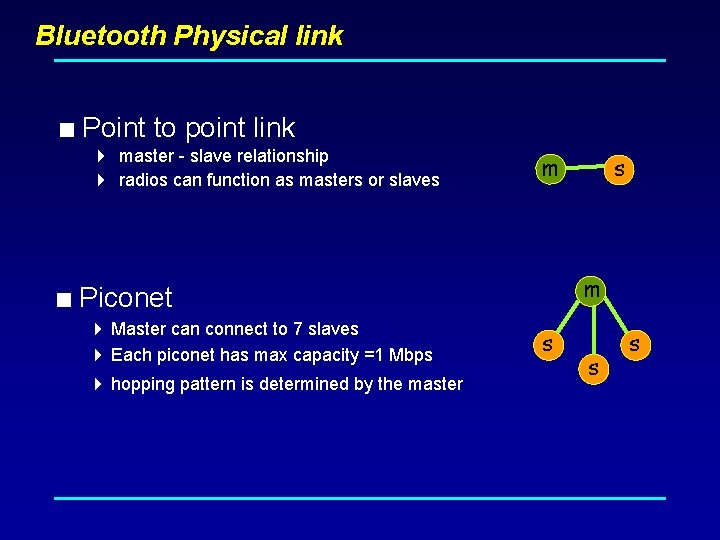
Bluetooth Physical link < Point to point link 4 master - slave relationship 4 radios can function as masters or slaves m m < Piconet 4 Master can connect to 7 slaves 4 Each piconet has max capacity =1 Mbps 4 hopping pattern is determined by the master s s
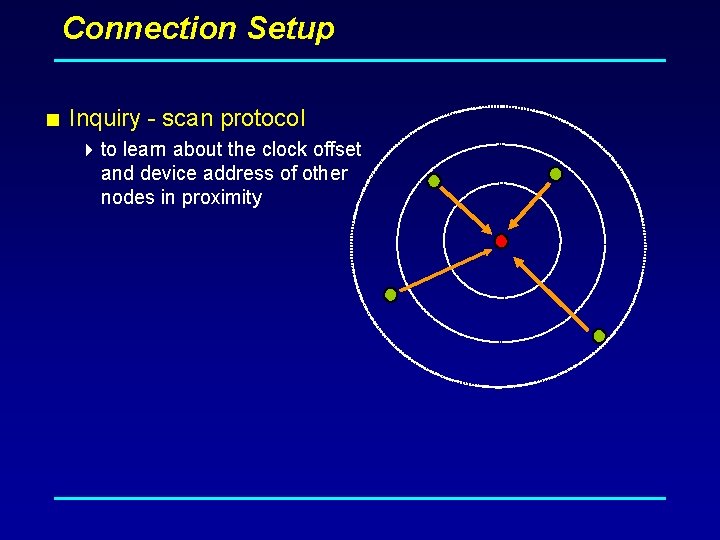
Connection Setup < Inquiry - scan protocol 4 to learn about the clock offset and device address of other nodes in proximity
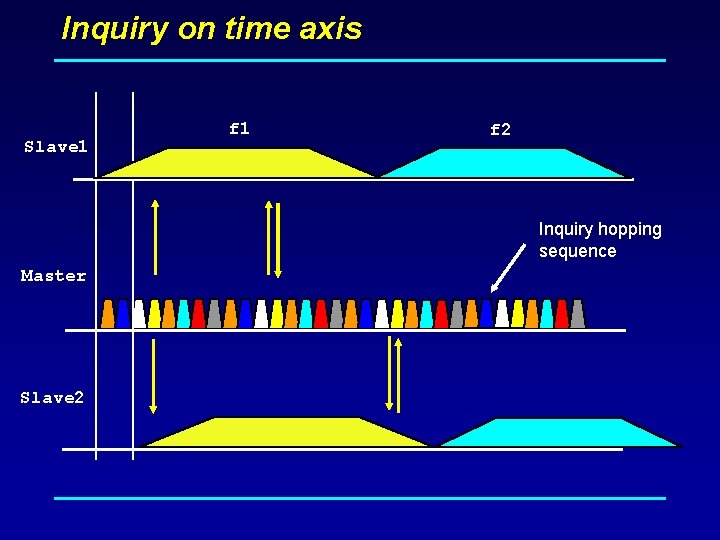
Inquiry on time axis Slave 1 f 2 Inquiry hopping sequence Master Slave 2
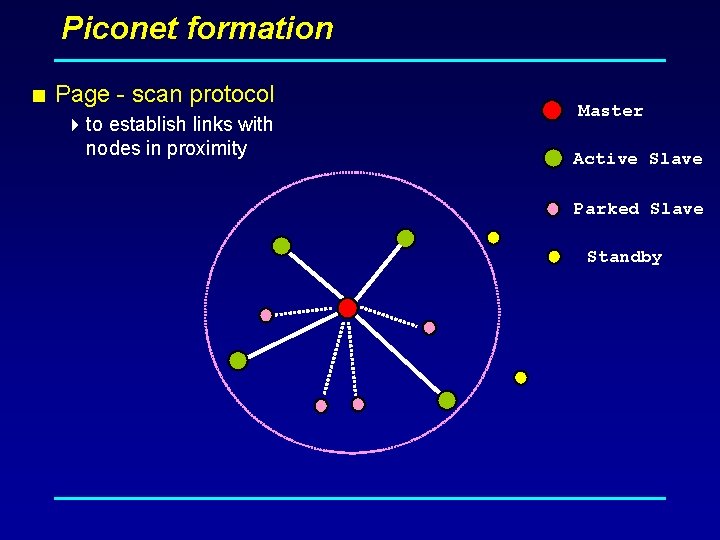
Piconet formation < Page - scan protocol 4 to establish links with nodes in proximity Master Active Slave Parked Slave Standby
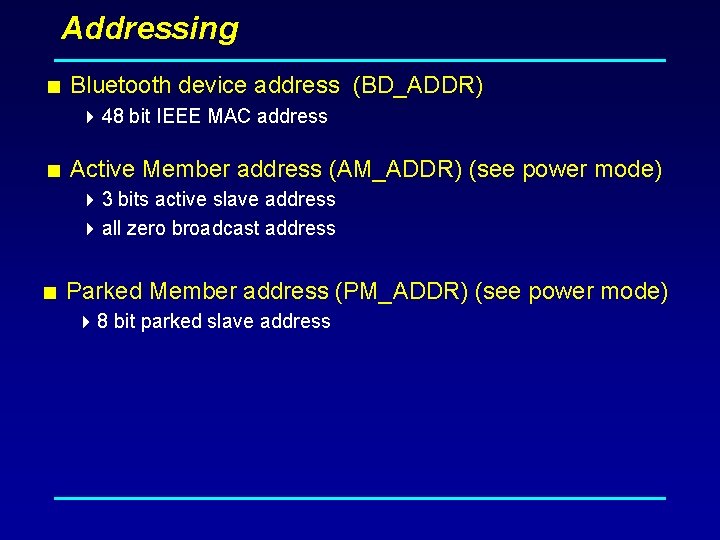
Addressing < Bluetooth device address (BD_ADDR) 4 48 bit IEEE MAC address < Active Member address (AM_ADDR) (see power mode) 4 3 bits active slave address 4 all zero broadcast address < Parked Member address (PM_ADDR) (see power mode) 4 8 bit parked slave address
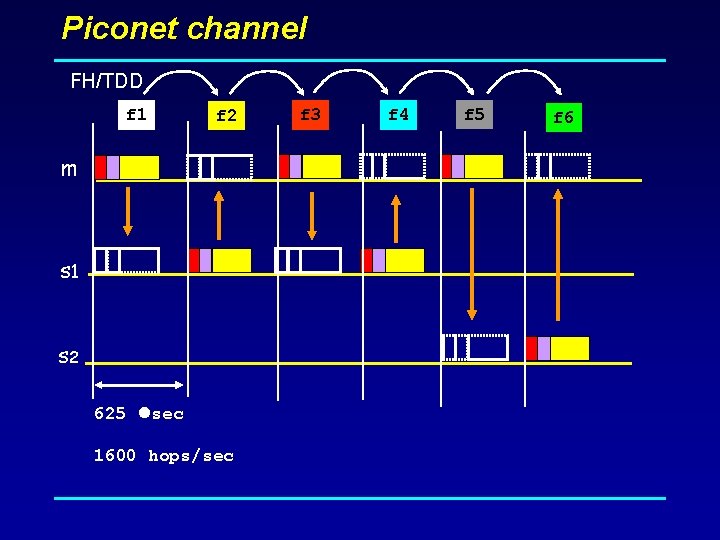
Piconet channel FH/TDD f 1 f 2 m s 1 s 2 625 sec 1600 hops/sec f 3 f 4 f 5 f 6
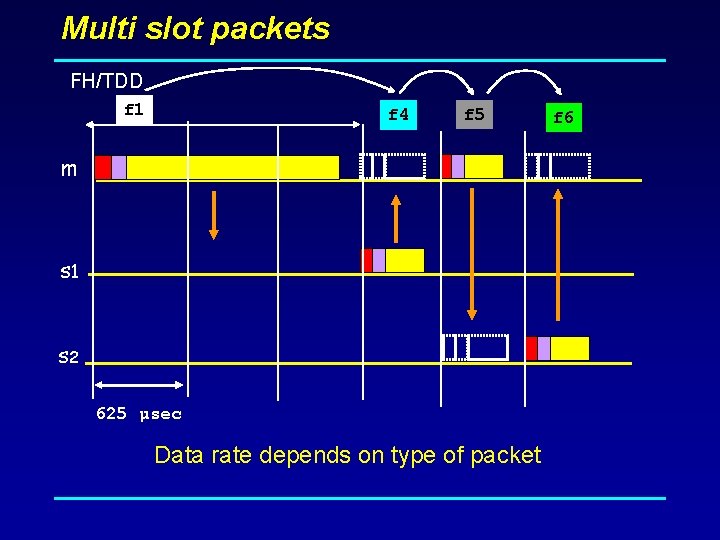
Multi slot packets FH/TDD f 1 f 4 f 5 m s 1 s 2 625 µsec Data rate depends on type of packet f 6
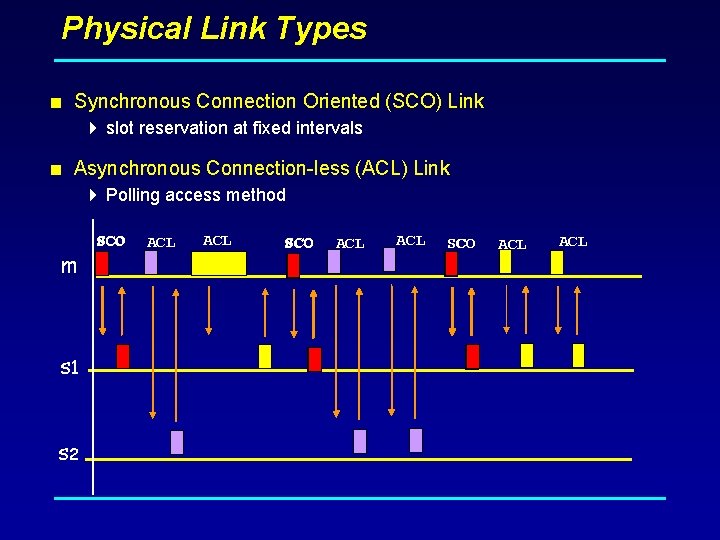
Physical Link Types < Synchronous Connection Oriented (SCO) Link 4 slot reservation at fixed intervals < Asynchronous Connection-less (ACL) Link 4 Polling access method m s 1 s 2 SCO ACL ACL SCO ACL
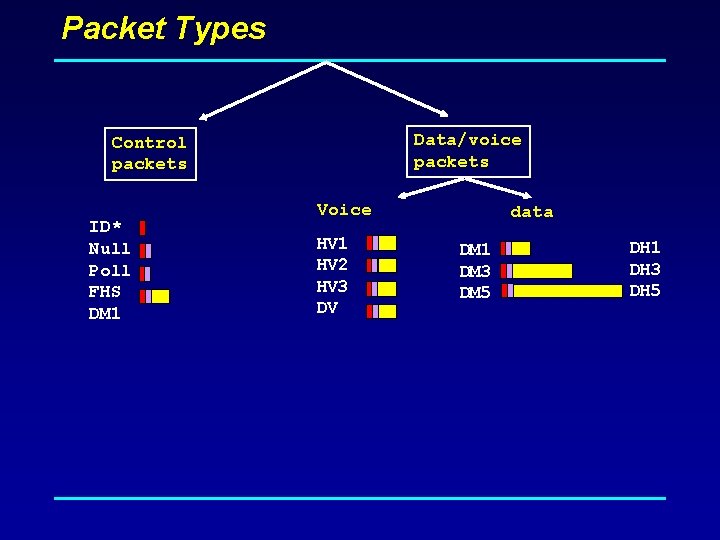
Packet Types Data/voice packets Control packets ID* Null Poll FHS DM 1 Voice HV 1 HV 2 HV 3 DV data DM 1 DM 3 DM 5 DH 1 DH 3 DH 5
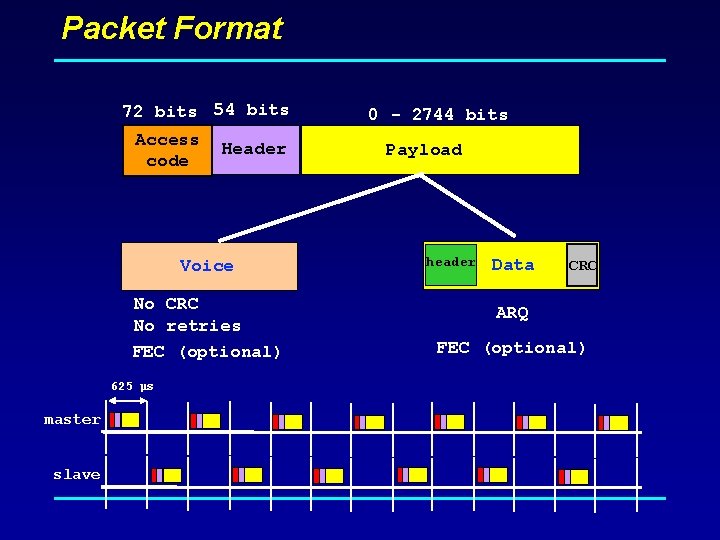
Packet Format 72 bits 54 bits Access code Header Voice No CRC No retries FEC (optional) 625 µs master slave 0 - 2744 bits Payload header Data CRC ARQ FEC (optional)
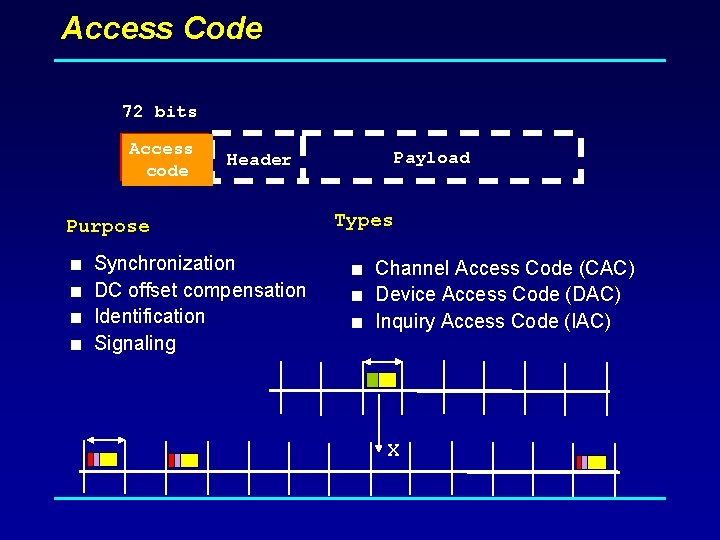
Access Code 72 bits Access code Header Purpose < Synchronization < DC offset compensation < Identification < Signaling Payload Types < Channel Access Code (CAC) < Device Access Code (DAC) < Inquiry Access Code (IAC) X
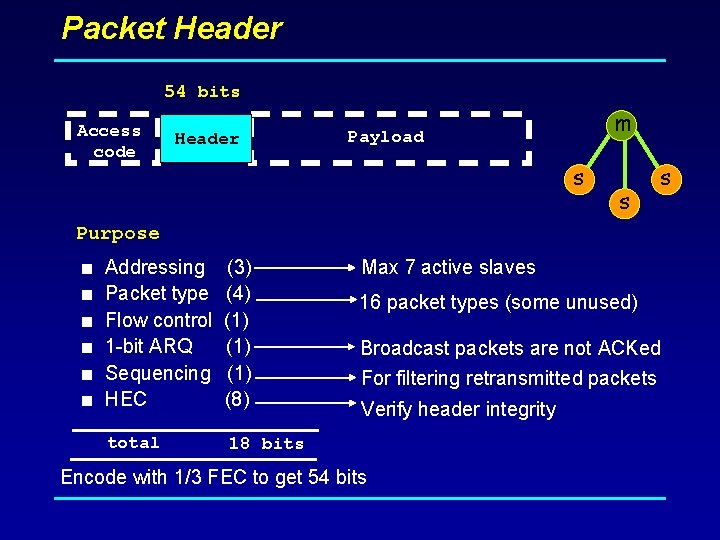
Packet Header 54 bits Access code Header m Payload s s s Purpose < Addressing Max 7 active slaves < 16 packet types (some unused) < < (3) Packet type (4) Flow control (1) 1 -bit ARQ (1) Sequencing (1) HEC (8) total Broadcast packets are not ACKed For filtering retransmitted packets Verify header integrity 18 bits Encode with 1/3 FEC to get 54 bits
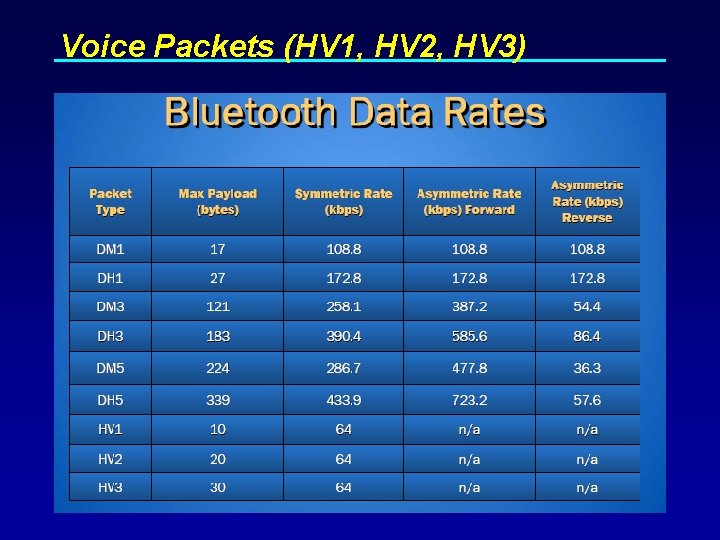
Voice Packets (HV 1, HV 2, HV 3)
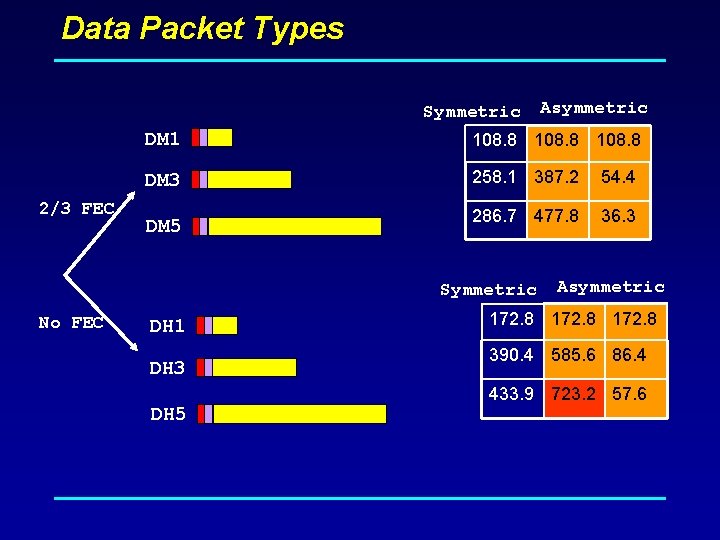
Data Packet Types Symmetric 2/3 FEC DM 1 108. 8 DM 3 258. 1 387. 2 54. 4 286. 7 477. 8 36. 3 DM 5 Symmetric No FEC Asymmetric DH 1 DH 3 DH 5 Asymmetric 172. 8 390. 4 585. 6 86. 4 433. 9 723. 2 57. 6
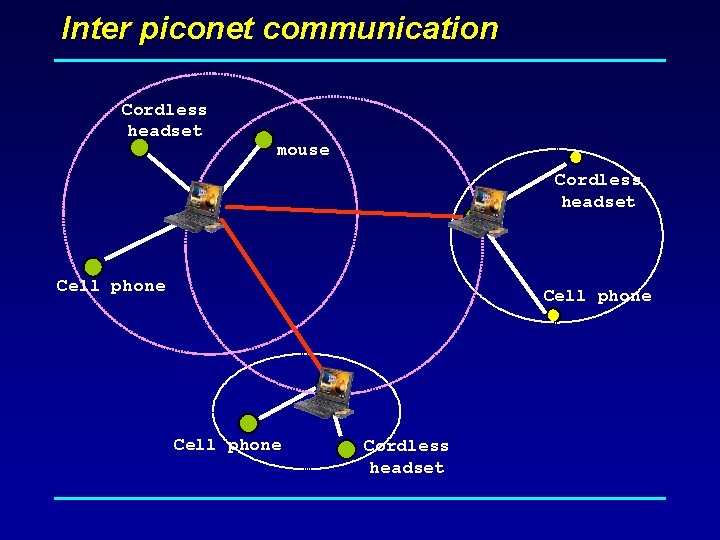
Inter piconet communication Cordless headset mouse Cordless headset Cell phone Cordless headset
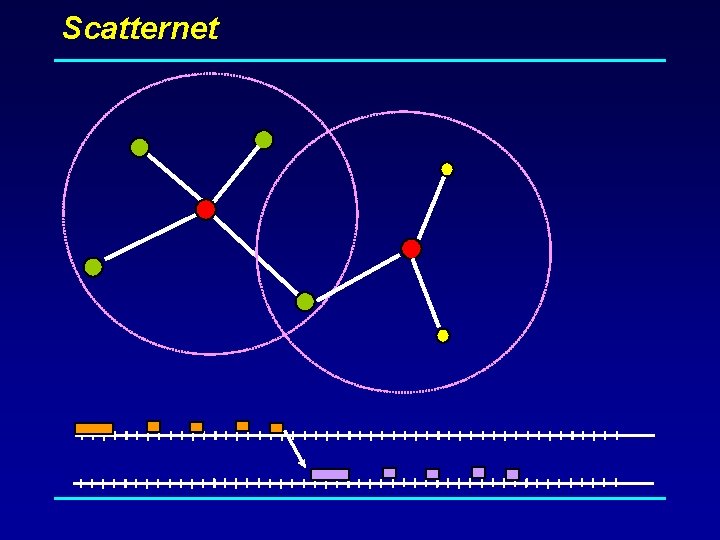
Scatternet
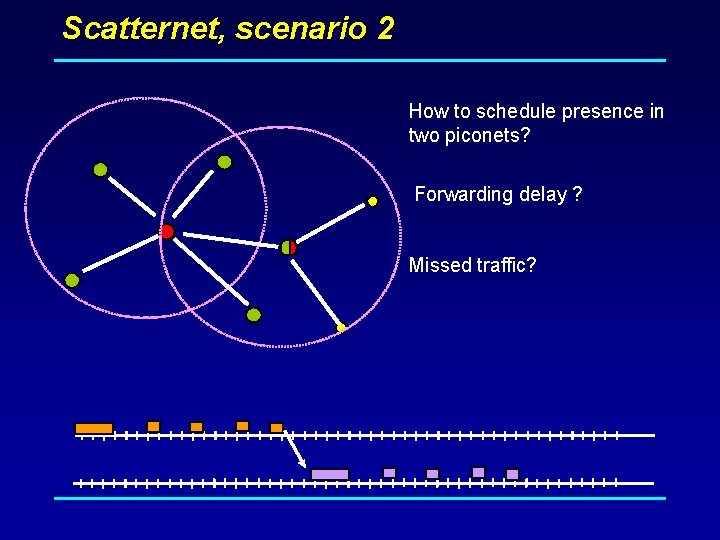
Scatternet, scenario 2 How to schedule presence in two piconets? Forwarding delay ? Missed traffic?
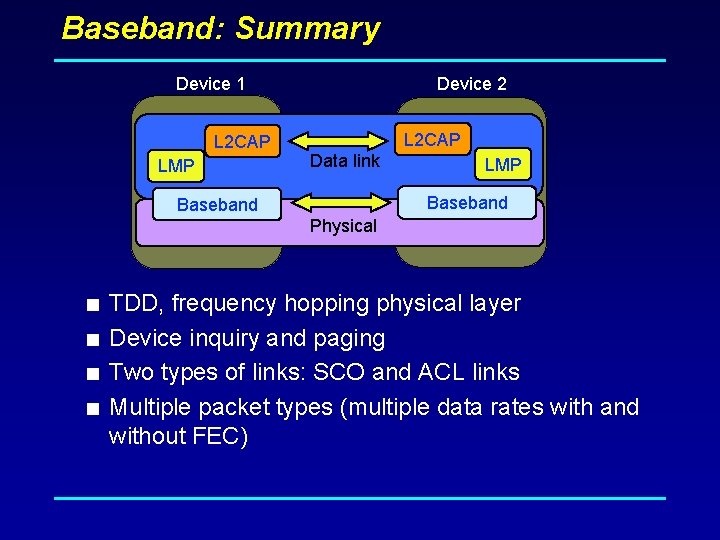
Baseband: Summary Device 1 L 2 CAP LMP Device 2 L 2 CAP Data link LMP Baseband Physical < TDD, frequency hopping physical layer < Device inquiry and paging < Two types of links: SCO and ACL links < Multiple packet types (multiple data rates with and without FEC)
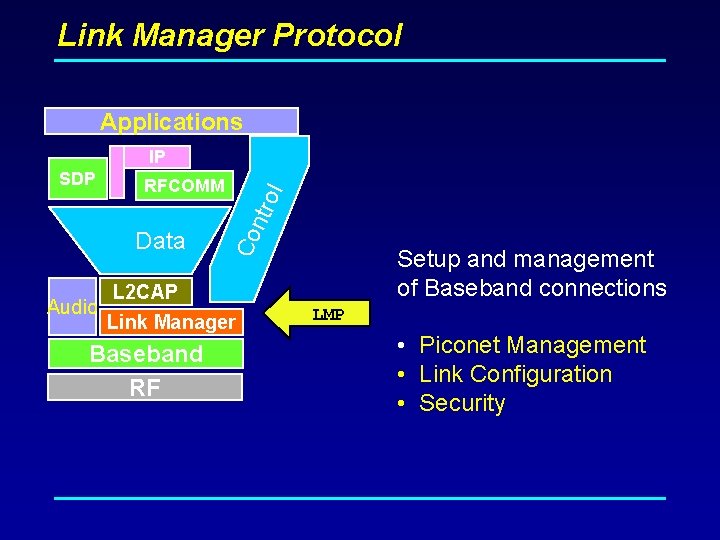
Link Manager Protocol Applications IP Data Audio ol RFCOMM Co ntr SDP Setup and management of Baseband connections L 2 CAP Link Manager Baseband RF LMP • Piconet Management • Link Configuration • Security
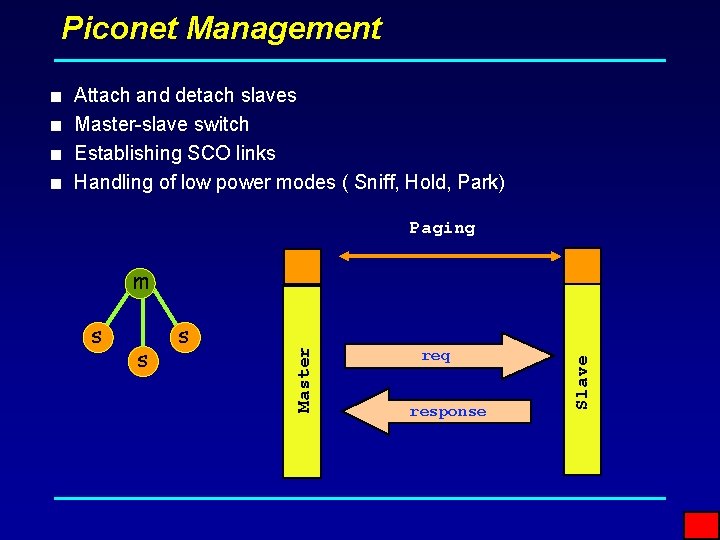
Piconet Management < Attach and detach slaves < Master-slave switch < Establishing SCO links < Handling of low power modes ( Sniff, Hold, Park) Paging s s req response Slave s Master m
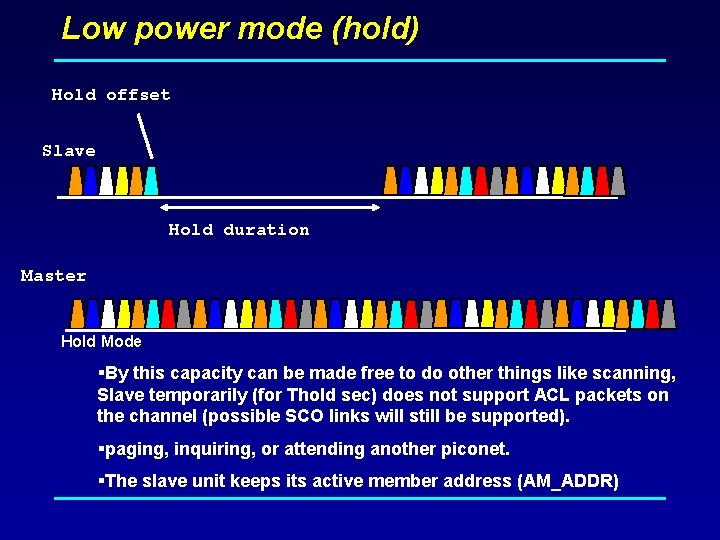
Low power mode (hold) Hold offset Slave Hold duration Master Hold Mode §By this capacity can be made free to do other things like scanning, Slave temporarily (for Thold sec) does not support ACL packets on the channel (possible SCO links will still be supported). §paging, inquiring, or attending another piconet. §The slave unit keeps its active member address (AM_ADDR)
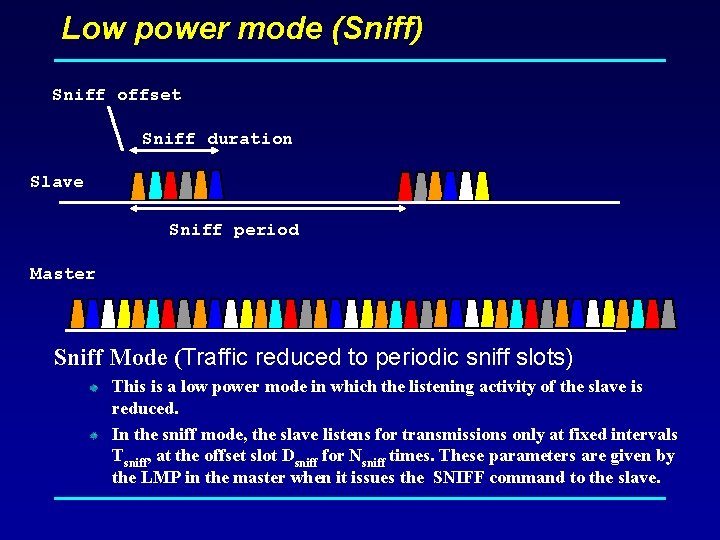
Low power mode (Sniff) Sniff offset Sniff duration Slave Sniff period Master Sniff Mode (Traffic reduced to periodic sniff slots) This is a low power mode in which the listening activity of the slave is reduced. In the sniff mode, the slave listens for transmissions only at fixed intervals Tsniff, at the offset slot Dsniff for Nsniff times. These parameters are given by the LMP in the master when it issues the SNIFF command to the slave.
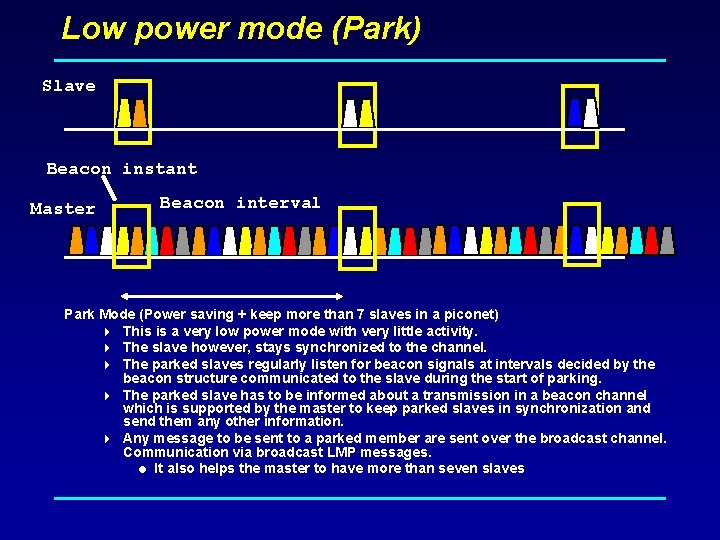
Low power mode (Park) Slave Beacon instant Master Beacon interval Park Mode (Power saving + keep more than 7 slaves in a piconet) 4 This is a very low power mode with very little activity. 4 The slave however, stays synchronized to the channel. 4 The parked slaves regularly listen for beacon signals at intervals decided by the beacon structure communicated to the slave during the start of parking. 4 The parked slave has to be informed about a transmission in a beacon channel which is supported by the master to keep parked slaves in synchronization and send them any other information. 4 Any message to be sent to a parked member are sent over the broadcast channel. Communication via broadcast LMP messages. = It also helps the master to have more than seven slaves
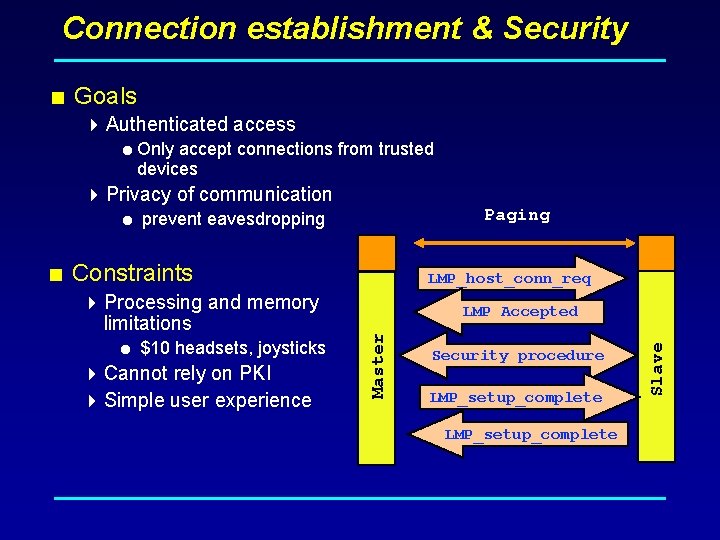
Connection establishment & Security < Goals 4 Authenticated access = Only accept connections from trusted devices 4 Privacy of communication Paging = prevent eavesdropping 4 Cannot rely on PKI 4 Simple user experience LMP Accepted Security procedure LMP_setup_complete Slave = $10 headsets, joysticks LMP_host_conn_req Master < Constraints 4 Processing and memory limitations
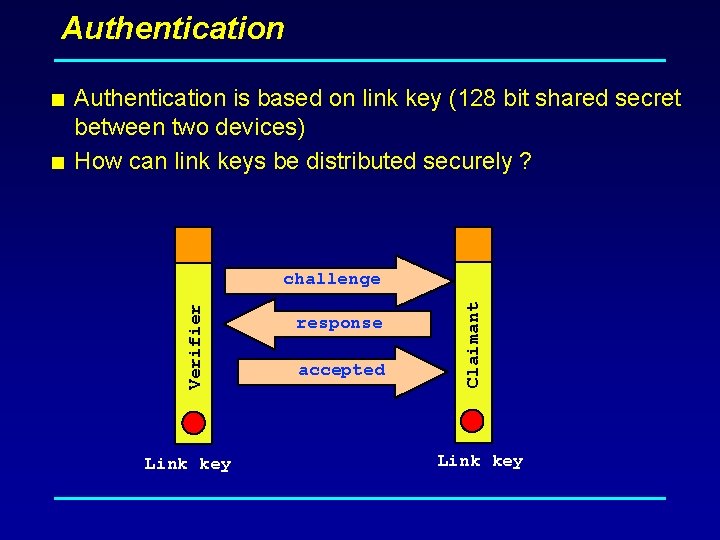
Authentication < Authentication is based on link key (128 bit shared secret between two devices) < How can link keys be distributed securely ? Link key response accepted Claimant Verifier challenge Link key
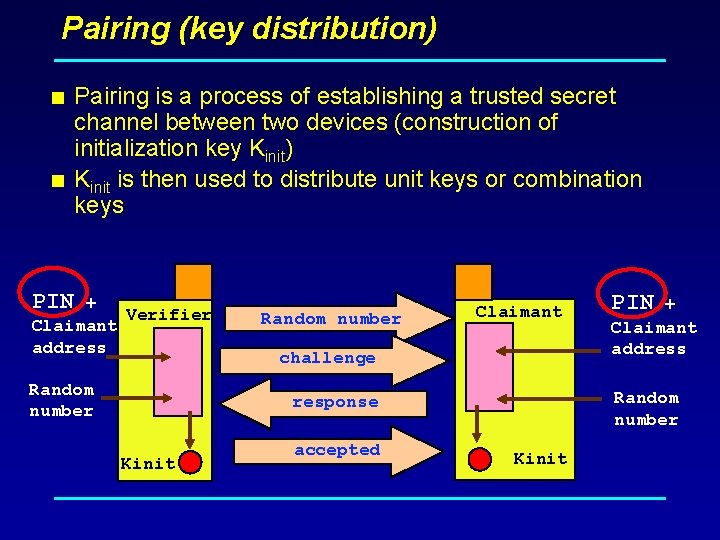
Pairing (key distribution) < Pairing is a process of establishing a trusted secret channel between two devices (construction of initialization key Kinit) < Kinit is then used to distribute unit keys or combination keys PIN + Verifier Claimant address Random number Claimant challenge Kinit + Claimant address Random number response accepted PIN Kinit
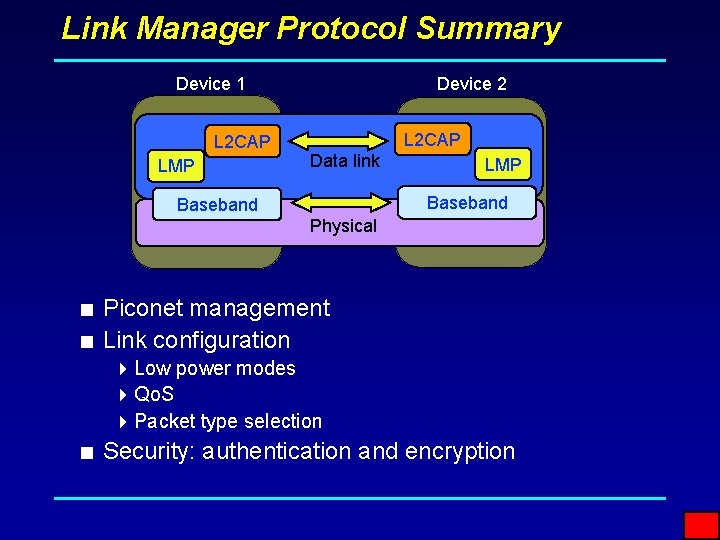
Link Manager Protocol Summary Device 1 L 2 CAP LMP Device 2 L 2 CAP Data link LMP Baseband Physical < Piconet management < Link configuration 4 Low power modes 4 Qo. S 4 Packet type selection < Security: authentication and encryption
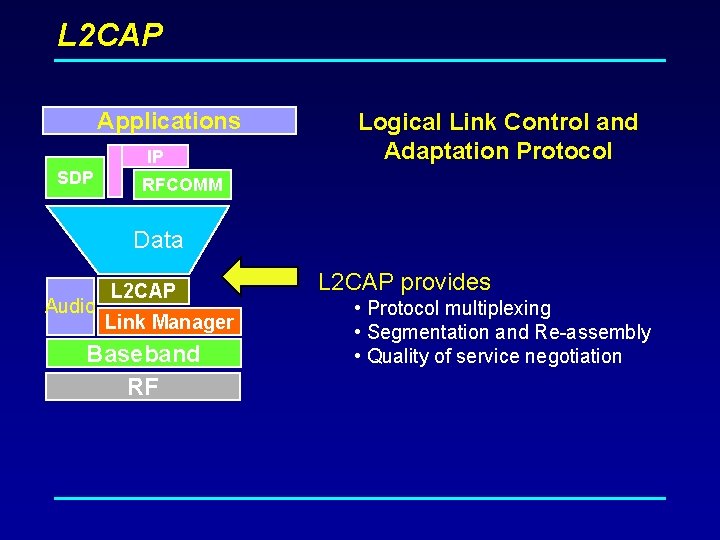
L 2 CAP Applications IP SDP Logical Link Control and Adaptation Protocol RFCOMM Data Audio L 2 CAP Link Manager Baseband RF L 2 CAP provides • Protocol multiplexing • Segmentation and Re-assembly • Quality of service negotiation
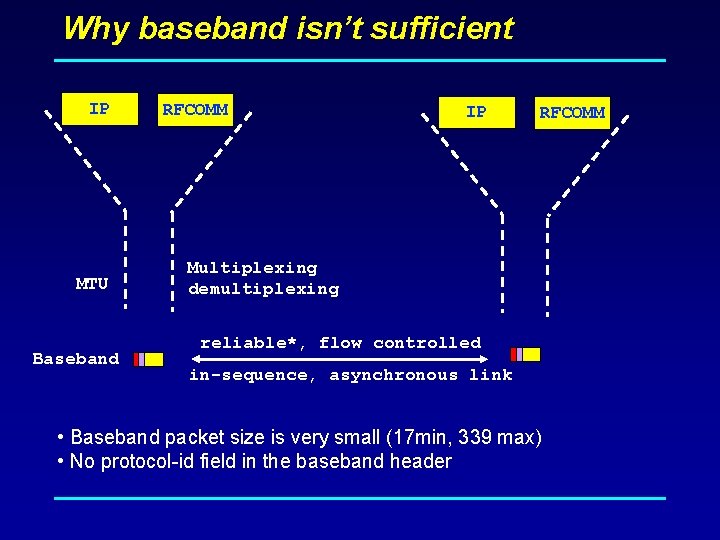
Why baseband isn’t sufficient IP MTU Baseband RFCOMM IP RFCOMM Multiplexing demultiplexing reliable*, flow controlled in-sequence, asynchronous link • Baseband packet size is very small (17 min, 339 max) • No protocol-id field in the baseband header
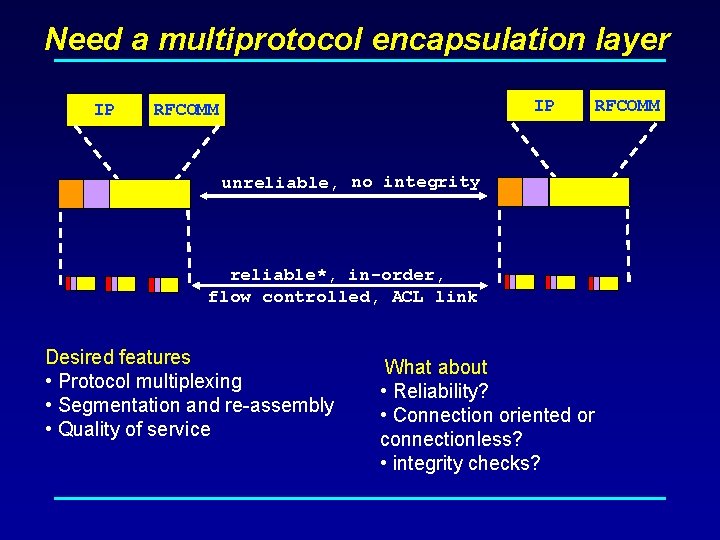
Need a multiprotocol encapsulation layer IP IP RFCOMM unreliable, no integrity reliable*, in-order, flow controlled, ACL link Desired features • Protocol multiplexing • Segmentation and re-assembly • Quality of service What about • Reliability? • Connection oriented or connectionless? • integrity checks? RFCOMM
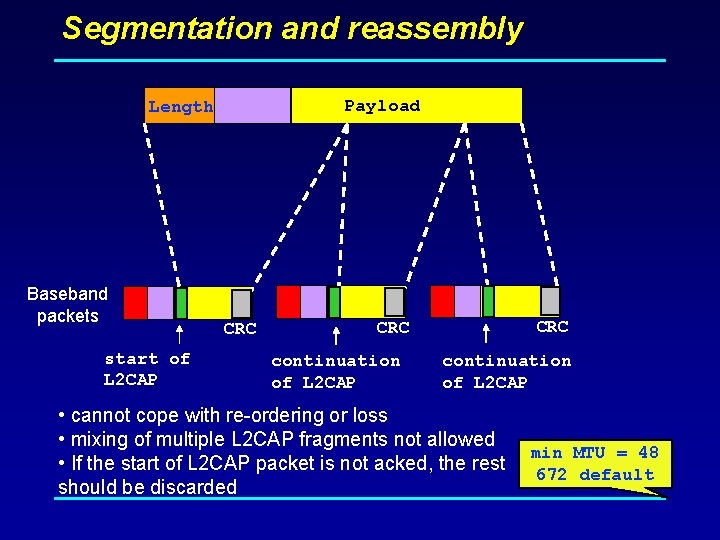
Segmentation and reassembly Payload Length Baseband packets start of L 2 CAP CRC CRC continuation of L 2 CAP • cannot cope with re-ordering or loss • mixing of multiple L 2 CAP fragments not allowed • If the start of L 2 CAP packet is not acked, the rest should be discarded min MTU = 48 672 default
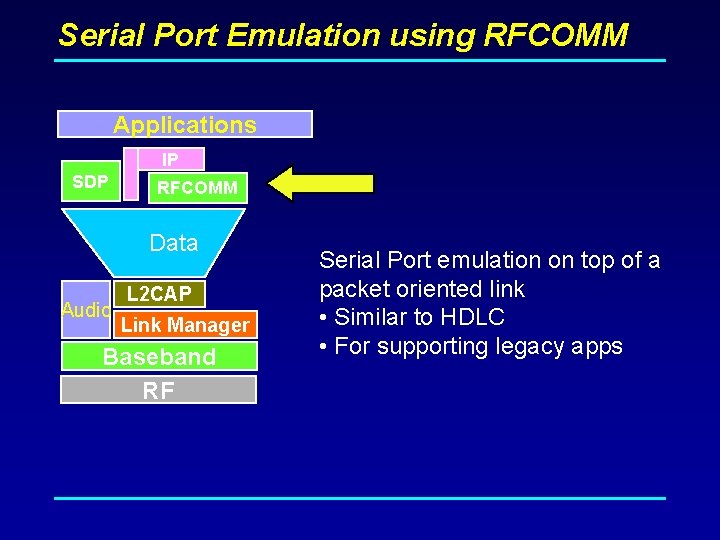
Serial Port Emulation using RFCOMM Applications IP SDP RFCOMM Data Audio L 2 CAP Link Manager Baseband RF Serial Port emulation on top of a packet oriented link • Similar to HDLC • For supporting legacy apps
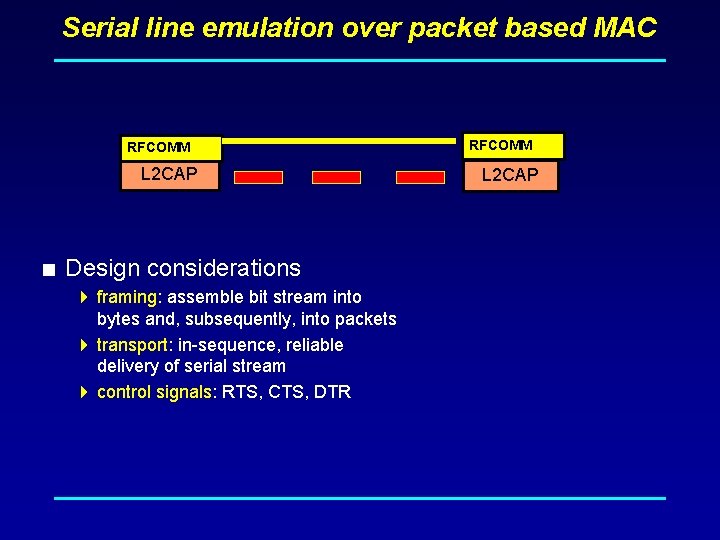
Serial line emulation over packet based MAC RFCOMM L 2 CAP < Design considerations 4 framing: assemble bit stream into bytes and, subsequently, into packets 4 transport: in-sequence, reliable delivery of serial stream 4 control signals: RTS, CTS, DTR RFCOMM L 2 CAP
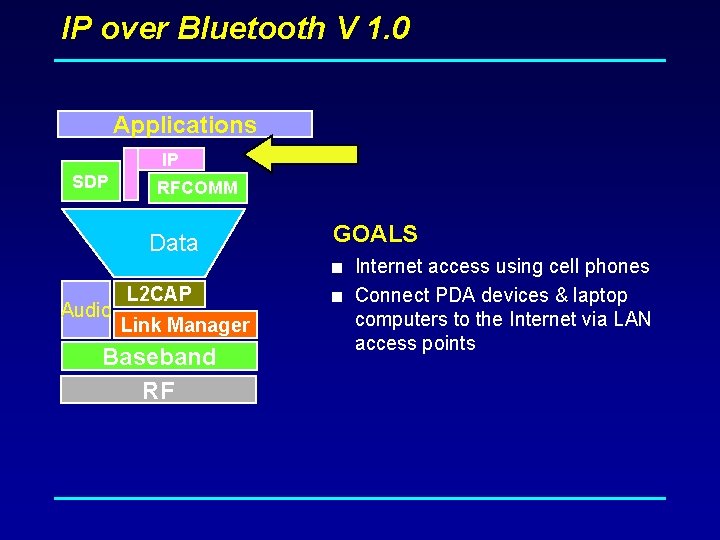
IP over Bluetooth V 1. 0 Applications IP SDP RFCOMM Data Audio L 2 CAP Link Manager Baseband RF GOALS < Internet access using cell phones < Connect PDA devices & laptop computers to the Internet via LAN access points
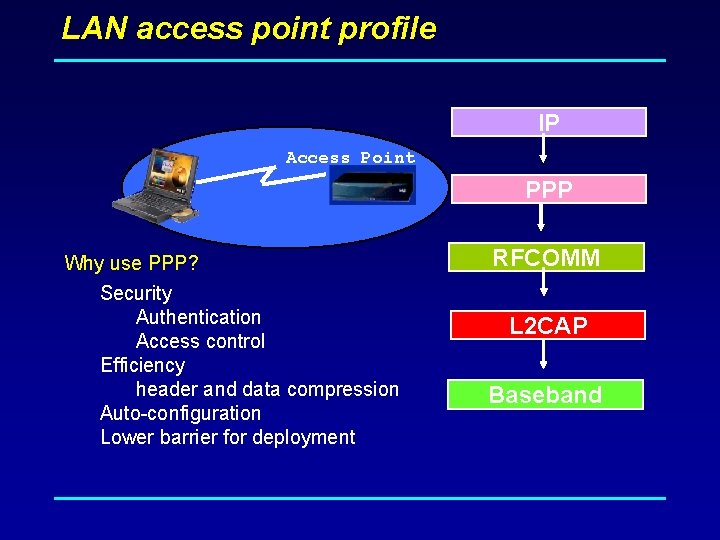
LAN access point profile IP Access Point PPP Why use PPP? Security Authentication Access control Efficiency header and data compression Auto-configuration Lower barrier for deployment RFCOMM L 2 CAP Baseband
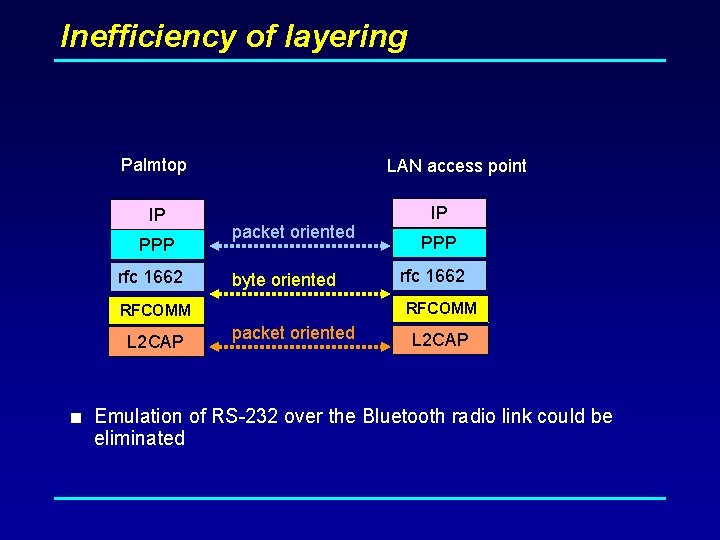
Inefficiency of layering Palmtop IP PPP rfc 1662 LAN access point packet oriented byte oriented PPP rfc 1662 RFCOMM L 2 CAP IP packet oriented L 2 CAP < Emulation of RS-232 over the Bluetooth radio link could be eliminated
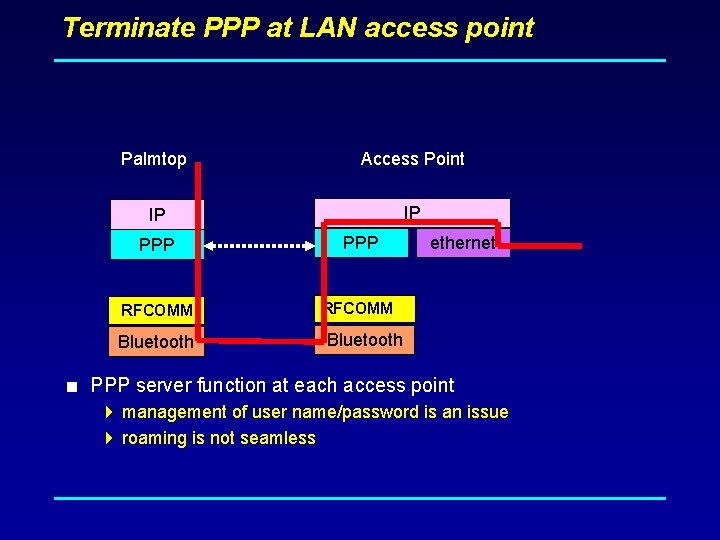
Terminate PPP at LAN access point Palmtop Access Point IP IP PPP RFCOMM Bluetooth ethernet Bluetooth < PPP server function at each access point 4 management of user name/password is an issue 4 roaming is not seamless
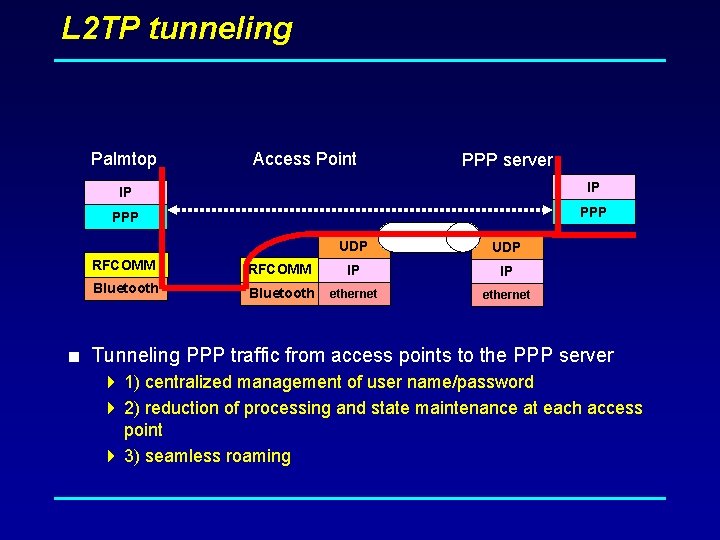
L 2 TP tunneling Palmtop Access Point PPP server IP IP PPP UDP RFCOMM IP IP Bluetooth ethernet < Tunneling PPP traffic from access points to the PPP server 4 1) centralized management of user name/password 4 2) reduction of processing and state maintenance at each access point 4 3) seamless roaming
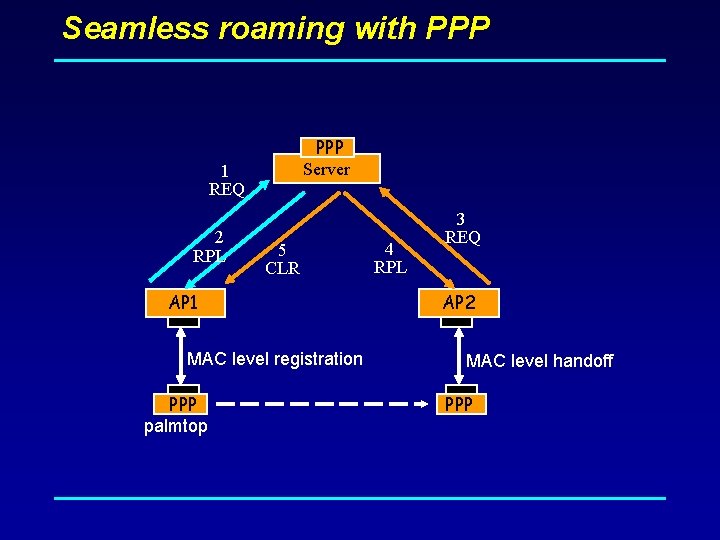
Seamless roaming with PPP Server 1 REQ 2 RPL 5 CLR AP 1 MAC level registration PPP palmtop 4 RPL 3 REQ AP 2 MAC level handoff PPP

Bluetooth Current Market Outlook
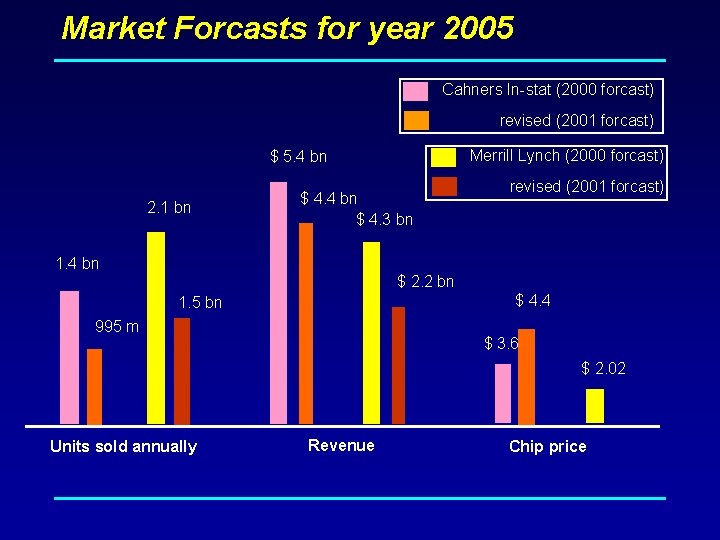
Market Forcasts for year 2005 Cahners In-stat (2000 forcast) revised (2001 forcast) Merrill Lynch (2000 forcast) $ 5. 4 bn 2. 1 bn $ 4. 4 bn $ 4. 3 bn 1. 4 bn revised (2001 forcast) $ 2. 2 bn $ 4. 4 1. 5 bn 995 m $ 3. 6 $ 2. 02 Units sold annually Revenue Chip price
Value to carriers: Synchronization and Push < More bits over the air < Utilization of unused capacity during non-busy periods < Higher barrier for switching service providers
Value to carriers: Cell phone as an IP gateway Will Pilot and cell phone eventually merge? < More bits over the air < Enhanced user experience 4 Palmpilot has a better UI than a cell phone < Growth into other vertical markets
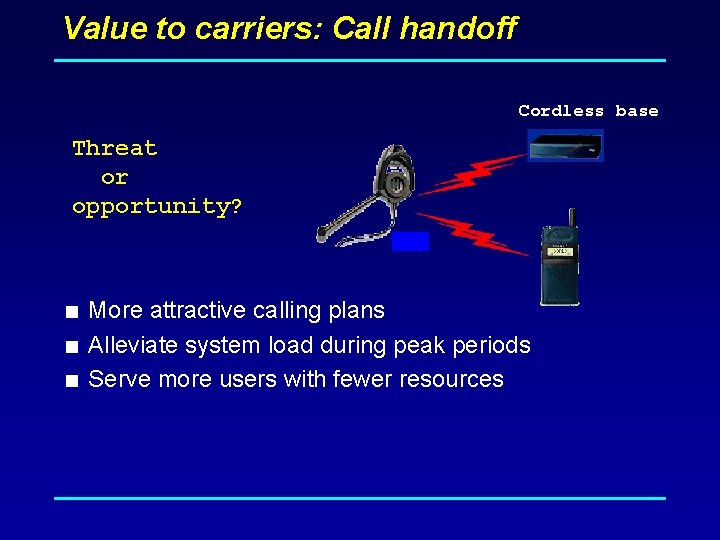
Value to carriers: Call handoff Cordless base Threat or opportunity? < More attractive calling plans < Alleviate system load during peak periods < Serve more users with fewer resources
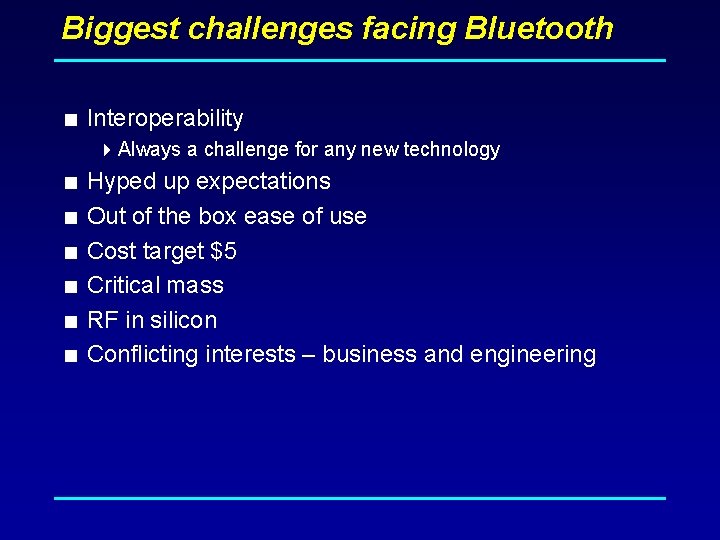
Biggest challenges facing Bluetooth < Interoperability 4 Always a challenge for any new technology < Hyped up expectations < Out of the box ease of use < Cost target $5 < Critical mass < RF in silicon < Conflicting interests – business and engineering
![References < [1] IEEE 802. 11, “Wireless LAN MAC and Physical Layer Specification, ” References < [1] IEEE 802. 11, “Wireless LAN MAC and Physical Layer Specification, ”](http://slidetodoc.com/presentation_image_h/dfa49e035adf8e4975f25c2942d601e6/image-86.jpg)
References < [1] IEEE 802. 11, “Wireless LAN MAC and Physical Layer Specification, ” June 1997. < [2] Hirt, W. ; Hassner, M. ; Heise, N. “Ir. DA–VFIr (16 Mb/s): modulation code and system design. ” IEEE Personal Communications, vol. 8, (no. 1), IEEE, Feb. 2001. < [3] Lansford, J. ; Bahl, P. “The design and implementation of Home. RF: a radio frequency wireless networking standard for the connected home. ” Proceedings of the IEEE, Oct. 2000. < [4] Specification of Bluetooth System, ver. 1. 0, July 1999
![References (cnt) < [5] Haartsen, J. C. “The Bluetooth radio system. ”, IEEE Personal References (cnt) < [5] Haartsen, J. C. “The Bluetooth radio system. ”, IEEE Personal](http://slidetodoc.com/presentation_image_h/dfa49e035adf8e4975f25c2942d601e6/image-87.jpg)
References (cnt) < [5] Haartsen, J. C. “The Bluetooth radio system. ”, IEEE Personal < < < Communications, IEEE, Feb. 2000. [6] Haartsen, J. C. ‘Bluetooth towards ubiquitous wireless connectivity. ’, Revue HF, Soc. Belge Ing. Telecommun. & Electron, 2000. p. 8– 16. [7] Rathi, S. “Bluetooth protocol architecture. ” Dedicated Systems Magazine, Dedicated Systems Experts, Oct. –Dec. 2000. [8] Haartsen, J. C. ; Mattisson, S. “Bluetooth–a new low–power radio interface providing short–range connectivity. ” Proceedings of the IEEE, Oct. 2000. [9] Gilb, J. P. K “Bluetooth radio architectures. ” 2000 IEEE Radio Frequency Integrated Circuits (RFIC) Symposium Digest of Papers, Boston, MA, USA, 11– 13 June 2000.
![References (cnt) < [10] N. Benvenuto, G. Cherubini, “Algoritmi e circuiti per le < References (cnt) < [10] N. Benvenuto, G. Cherubini, “Algoritmi e circuiti per le <](http://slidetodoc.com/presentation_image_h/dfa49e035adf8e4975f25c2942d601e6/image-88.jpg)
References (cnt) < [10] N. Benvenuto, G. Cherubini, “Algoritmi e circuiti per le < < < telecomunicazioni”, Ed. Libreria Progetto. [11] The Bluetooth Special Interest Group, Documentation available at http: //www. bluetooth. com/ [12] IEEE 802. 15 Working Group for WPANs™; http: //www. manta. ieee. org/groups/802/15/ [13] Barker, P. ; Boucouvalas, A. C. ; Vitsas, V. “Performance modelling of the Ir. DA infrared wireless communications protocol. ” International Journal of Communication Systems, vol. 13, Wiley, Nov. –Dec. 2000. [14] Tokarz, K. ; Zielinski, B. “Performance evaluation of Ir. DA wireless transmission. ” 7 th Conference on Computer Networks, Zakopane, Poland, 14– 16 June 2000. [15] ETSI RES, “Digital European Cordless Telecommunications (DECT), Common interface Part 1: Overview, ” ETS 300 175– 1, 1996.
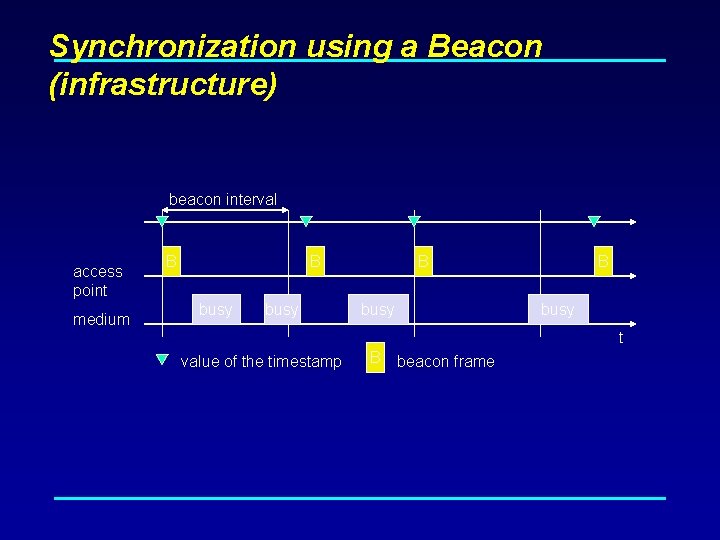
Synchronization using a Beacon (infrastructure) beacon interval access point medium B B busy t value of the timestamp B beacon frame
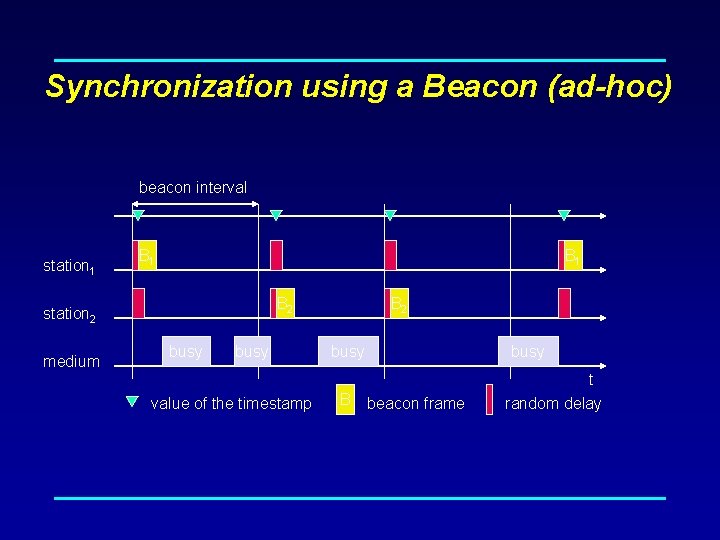
Synchronization using a Beacon (ad-hoc) beacon interval station 1 B 1 B 2 station 2 medium busy value of the timestamp B 2 busy B busy beacon frame t random delay
- Slides: 90