BLUE EYES TECHNOLOGY Blue Eyes TECHNOLOGY BLUE EYES
BLUE EYES TECHNOLOGY
Blue Eyes TECHNOLOGY • BLUE EYES is a technology, which aims at creating computational machines that have perceptual and sensory abilities like those of human beings. • The basic idea behind this technology is to give computer human power. • It provides technical means for monitoring and recording human-operator’s physiological condition.
How are blue and eyes related? As the idea is to monitor and record operator’s basic physiological parameters, the most important physiological activity is the movement of eyes. For a computer to sense the eye movement, wiring between operator and the system is required. But, this is a serious limitation of the operator’s mobility and disables his operations in large control rooms. So utilization of wireless technology becomes essential which can be implemented through blue tooth technology.
MOTIVATION Human error- A frequent reason of catastrophes and accidents. Weariness • Oversight • Temporal indisposition An aid to disabled persons. Availability of capable sensors.
What is Blue Eyes ? The complex solution for human-operator monitoring: -conscious brain involvement monitoring -triggering user-defined actions -data recording - use of BIOMETRICS What is Blue Eyes not? Doesn’t predict nor interfere with operator’s thoughts. Cannot force directly the operator to work
Who is Blue Eyes for ? Generic control rooms -Power station -Flight control centers Common application -A simpler system version for drivers -An aid to disabled people
What can we do with blue eyes technology? It has the ability to gather information about you and interact with you through special techniques like facial recognition, speech recognition, etc. It can even understand your emotions at the touch of the mouse. It can verify your identity, feel your presence, and start interacting with you. The machine can understand what a user wants, where he is looking at, and even realize his physical or emotional states.
Cont…… It realizes the urgency of the situation through the mouse. For instance if you ask the computer to dial to your friend at his office, it understands the situation and establishes a connection
KEY FEATURES Visual attention monitoring. Physiological condition monitoring. Operators position detection. Wireless data acquisition using Bluetooth technology. Real time user defined alarm triggering. Recorded data play back.
How can we give computer the human power? Affective Computing The process of making emotional computers with sensing abilities is known as affective computing. The steps used are: 1)Giving sensing abilities - to give machines the equivalent of the eyes, ears, and other sensory organs - voice-recognition software - cameras 2)Detecting human emotions -by biometric techniques 3)Respond properly

METHODS OF ACCOMPLISHING AFFECTIVE COMPUTING • Affect detection: detecting our emotional states from the expressions on our face • MAGIC pointing: Manual Acquisition with Gaze Tracking Technology • SUITOR: Simple User Interface Tracker • Emotion mouse: expected accuracy is 75%

MAIN BIOMETRIC TECNIQUES Facial expression detection -face recognition -expression detection Speech Recognition Emotion Mouse -IR sensor, thermosister chip, galvanic sensor Eye Gaze Tracking Jazz Multi Sensor

Emotion mouse
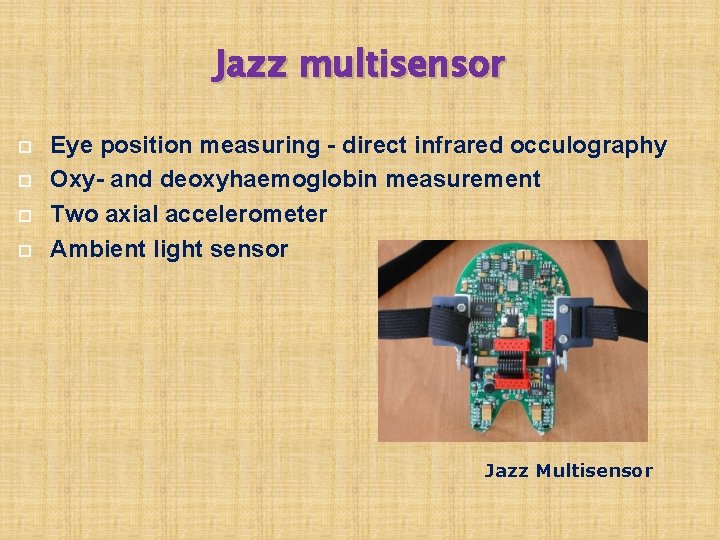
Jazz multisensor Eye position measuring - direct infrared occulography Oxy- and deoxyhaemoglobin measurement Two axial accelerometer Ambient light sensor Jazz Multisensor

SYSTEM OVERVIEW Connection manager Atmel 89 C 52 microcontroller Bluetooth Jazz Multisensor Visualization module Bluetooth Data analysis Bluetooth technology provides means for creating a Personal Area Network linking the operators and the central system. Data logger
HARDWARE Data Acquisition Unit Atmel 89 C 52 microcontroller - system core Bluetooth module (based on ROK 101008) HD 44780 - small LCD display 24 C 16 - I 2 C EEPROM (on a removable ID card) MC 145483 - 13 bit PCM codec Jazz Multisensor interface beeper and LED indicators 6 AA batteries and voltage level monitor
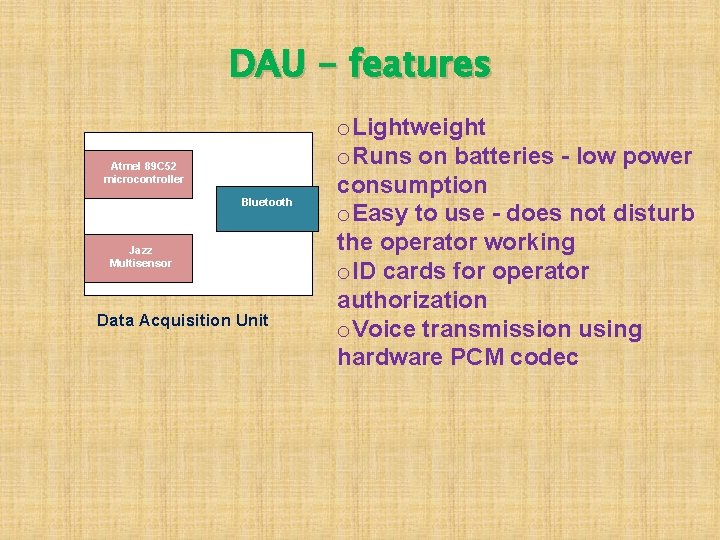
DAU - features Atmel 89 C 52 microcontroller Bluetooth Jazz Multisensor Data Acquisition Unit o. Lightweight o. Runs on batteries - low power consumption o. Easy to use - does not disturb the operator working o. ID cards for operator authorization o. Voice transmission using hardware PCM codec
Central System Unit Connection Manager Operator Manager Data Logger Module Data Analysis Module Alarm Dispatcher Module Visualization Module
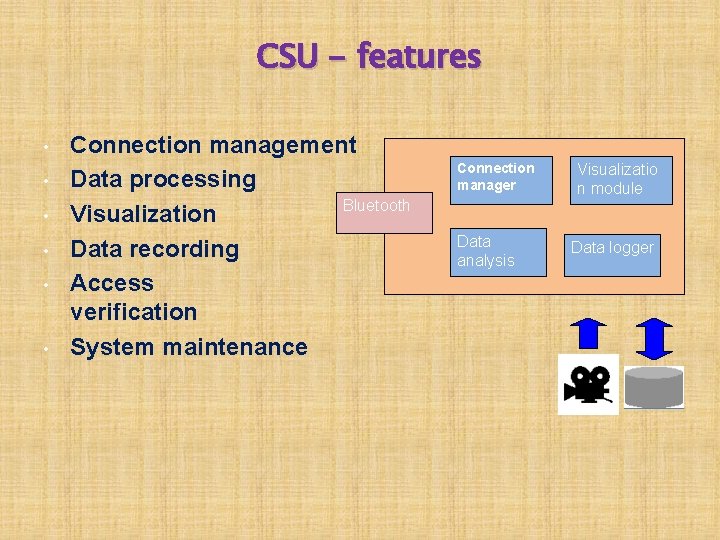
CSU - features • • • Connection management Data processing Bluetooth Visualization Data recording Access verification System maintenance Connection manager Data analysis Visualizatio n module Data logger
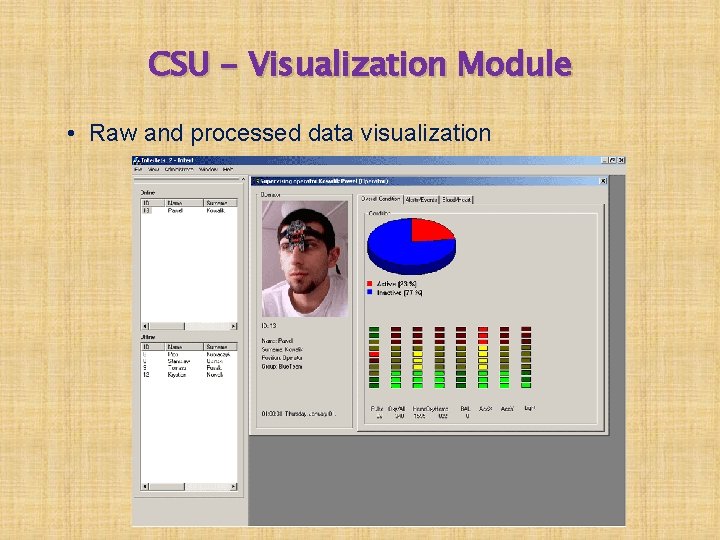
CSU - Visualization Module • Raw and processed data visualization
SOFTWARE Blue Eyes software is called “agent”. It analyzes and modifies the mother program, according to the user’s needs and moods.
Types of users Operators Supervisors System administrators
Operator: Operator is a person whose physiological parameters are supervised The operator wears the DAU The only functions offers to the operator are Authorization to the system and receiving alarm alerts. Authorization: Operator has to enter his personal PIN into DAU, if PIN is accepted, authorization is said to be complete. Receiving Alerts: This function supplies the operator with the most important alerts about his and his co-workers’ condition and mobile device state.
Supervisor: He is the person responsible for analyzing operators’ condition and performance. The supervisor receives tools for inspecting present values of the parameters (on-line browsing) as well as browsing the results of the long-term analysis (off-line browsing).
System Administrator: He is the user that maintains the system The administrator is delivered tools for adding new operators to the database. Defining alarm conditions. Configuring logging tools. Creating new analyzer modules.

Blue Eyes enabled devices POD The first blue Eye enabled mass production device It’s a car manufactured by TOYOTA It could keep the driver alert and active It could tell the driver to go slow if he is driving too fast It could hear the driver some sort of interesting music when he is getting bored.
Contd…. PONG It’s a robot released by IBM designed for demonstrating the new technology Its equipped with a computer capable of analyzing a person's glances and other forms of expressions of feelings It smiles when the person calls his name It expresses loneliness when it loses sight of the person
SECURE PAD an electronic badge that can identify the wearer and track his movements and activities with an array of sensors It knows who you are and where you are, and it has a pretty good idea of what you are doing and when you are doing it. The device was designed for a major health-care provider to track the activities of doctors and other personnel at large medical facilities it's interchangeable
APPLICATIONS OF BLUE EYES enables the computer to adapt a working style that fits users personality to increase his productivity The technology can also be incorporated into automobiles Blue Eyes is going to find its way in the routines of human beings with application such as TV, washing machine etc. In a company, the supervisor can be given the power to access the database containing his employees profile, which is linked with Blue Eyes technology. hereby he can evaluate the performance of his employees.
CONCLUSION The wireless link between the sensors worn by the operator and the supervising system makes it possible to improve overall reliability, safety and assures proper quality of system performance. These new possibilities can cover areas such as industry, transportation, military command centers or operation theaters. Researchers are attempting to add more capabilities to computers that will allow them to interact like humans, recognize human presents, talk, listen, or even guess their feelings. It avoids potential threats resulting from human errors, such as weariness, oversight, tiredness.

THANK YOU FOR YOUR ATTENTION

ANY QUESTIONS?
- Slides: 32