Block Ciphers Cryptography Lecture 2 Chantilly Academy Poorvi
Block Ciphers Cryptography Lecture 2: Chantilly Academy Poorvi Vora Department of Computer Science George Washington University
HW Assignment Decrypt the following texts: – etarq tqemu encrypted using the shift cipher – hjko me rtds encrypted using the Vigenère Cipher One is impossible to break without knowing the key. Which one? Why? 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 2
Issues with Shift and Vigenère Ciphers? 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 3
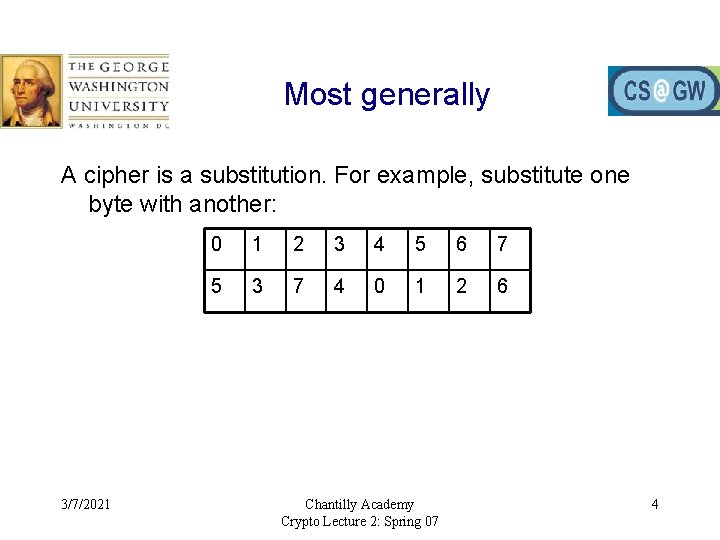
Most generally A cipher is a substitution. For example, substitute one byte with another: 3/7/2021 0 1 2 3 4 5 6 7 5 3 7 4 0 1 2 6 Chantilly Academy Crypto Lecture 2: Spring 07 4
However • It’s easy to break if you substitute one letter for another, or one set of 8 bits for another • So you take many, many bits and substitute them with others • Today’s block ciphers take 128 bits at a time, and substitute them with another 128 bits. • Can we just use a table like the on the previous slide? 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 5
Previous Block Cipher Standard: Data Encryption Standard (DES)
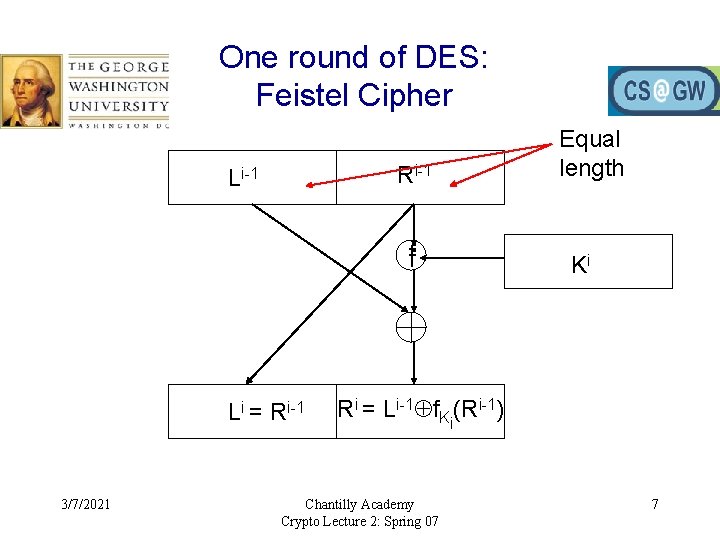
One round of DES: Feistel Cipher Ri-1 Li-1 ff Li = Ri-1 3/7/2021 Equal length Ki Ri = Li-1 f. Ki(Ri-1) Chantilly Academy Crypto Lecture 2: Spring 07 7
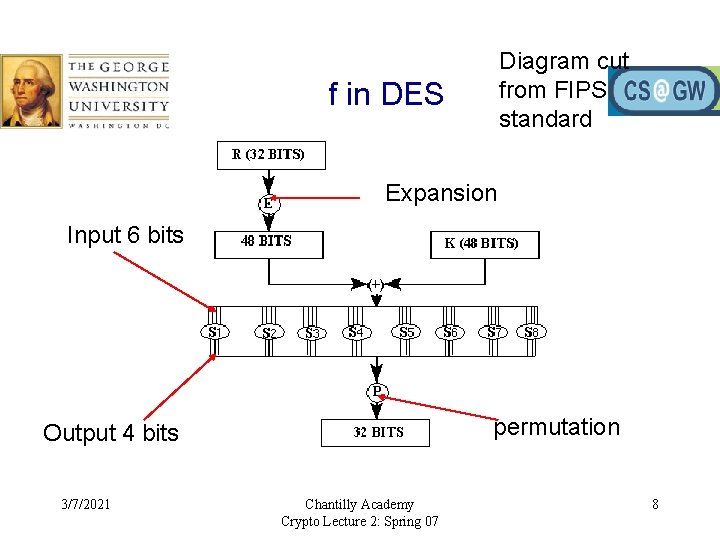
Diagram cut from FIPS standard f in DES Expansion Input 6 bits permutation Output 4 bits 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 8
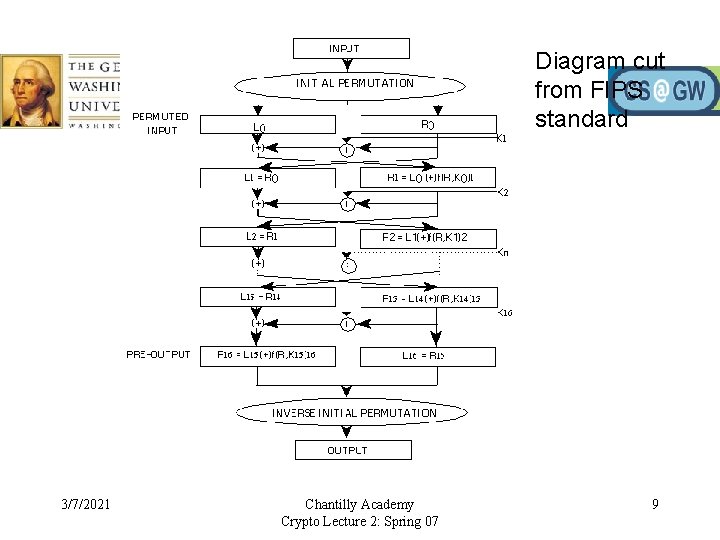
Diagram cut from FIPS standard 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 9
Attacks on DES 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 10
Current Block Cipher Standard Advanced Encryption Standard (AES)
Standardization 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 12
AES • Chosen for security, efficiency, implementation • Key lengths: – 128 bits (10 rounds) – 192 bits (12 rounds) – 256 bits (14 rounds) • Consists of: XOR with key, S-box substitution, permutation, mixcolumns 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 13
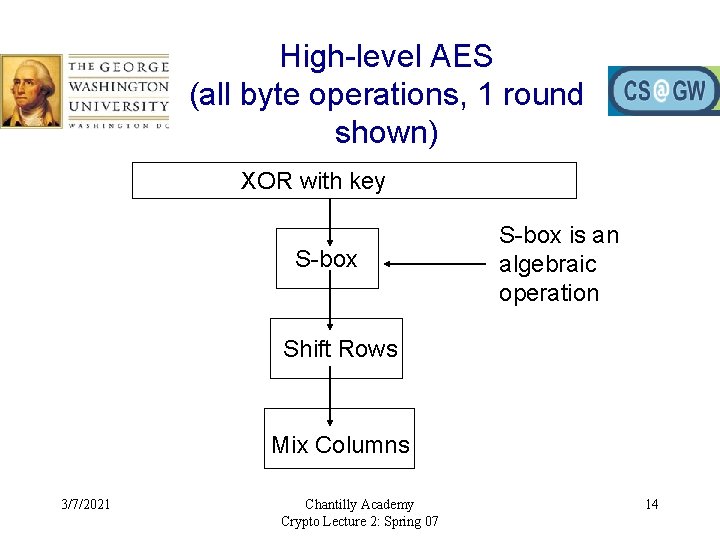
High-level AES (all byte operations, 1 round shown) XOR with key S-box is an algebraic operation Shift Rows Mix Columns 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 14
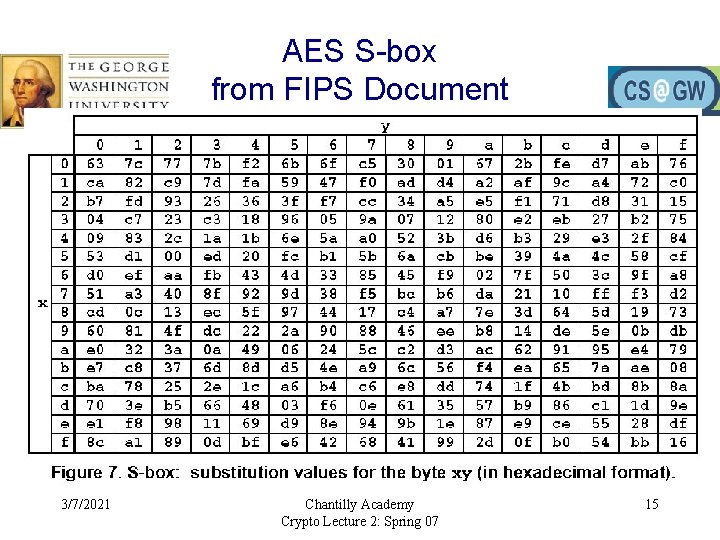
AES S-box from FIPS Document 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 15
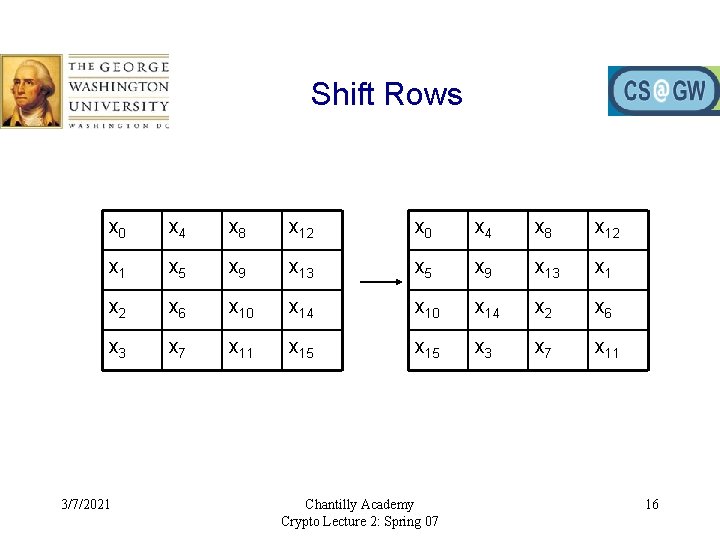
Shift Rows x 0 x 4 x 8 x 12 x 1 x 5 x 9 x 13 x 1 x 2 x 6 x 10 x 14 x 2 x 6 x 3 x 7 x 11 x 15 x 3 x 7 x 11 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 16
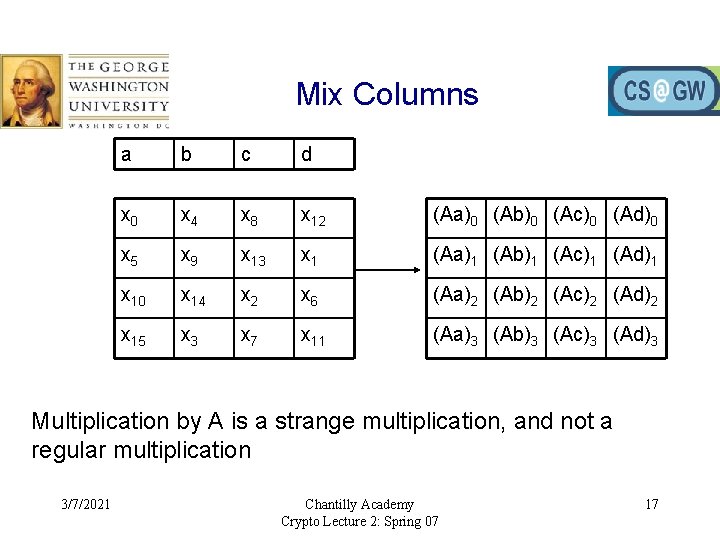
Mix Columns a b c d x 0 x 4 x 8 x 12 (Aa)0 (Ab)0 (Ac)0 (Ad)0 x 5 x 9 x 13 x 1 (Aa)1 (Ab)1 (Ac)1 (Ad)1 x 10 x 14 x 2 x 6 (Aa)2 (Ab)2 (Ac)2 (Ad)2 x 15 x 3 x 7 x 11 (Aa)3 (Ab)3 (Ac)3 (Ad)3 Multiplication by A is a strange multiplication, and not a regular multiplication 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 17
Key Schedule A key is 4 words; each word is 4 bytes The key has to generate 10 other keys to get a total of 11 for a 10 -round AES 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 18
Block Cipher Modes as originally developed for DES • Electronic Codebook (ECB) Mode – Regular, each 64 -bit plaintext encrypted with the same key • Cipher Block Chaining (CBC) Mode – 64 -bit ciphertext XORed with next plaintext, then encrypted – yi = e. K(yi-1 xi) • Stream Cipher Modes: yi = xi zi – Output Feedback (OFB) Mode: zi = e. K(zi-1) – Cipher Feedback (CFB) Mode: zi = e. K(yi-1) 3/7/2021 Chantilly Academy Crypto Lecture 2: Spring 07 19
- Slides: 19