Block Cipher introduction DES Description Feistel Sbox Exhaustive
Block Cipher- introduction � DES ü Description: Feistel, S-box ü Exhaustive Search, DC and LC ü Modes of Operation � AES ü Description: SPN, Branch number ü Security and Efficiency ü Modes of Operation � Other Ciphers ü Linear layer ü Confusion layer 1
DES (Data Encryption Standard) http: //en. wikipedia. org/wiki/Data_Encryption_Standard 2
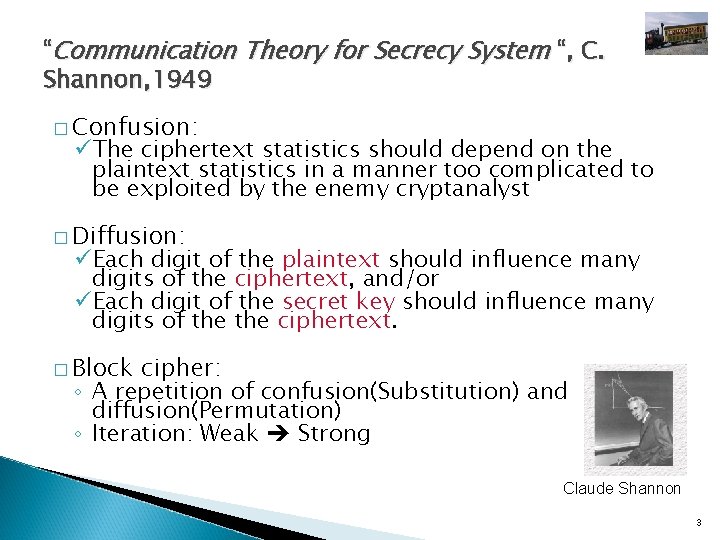
“Communication Theory for Secrecy System “, C. Shannon, 1949 � Confusion: üThe ciphertext statistics should depend on the plaintext statistics in a manner too complicated to be exploited by the enemy cryptanalyst � Diffusion: üEach digit of the plaintext should influence many digits of the ciphertext, and/or üEach digit of the secret key should influence many digits of the ciphertext. � Block cipher: ◦ A repetition of confusion(Substitution) and diffusion(Permutation) ◦ Iteration: Weak Strong Claude Shannon 3
News on Shannon’s Death 4
Block Cipher � Definition: q. Let Bn denote the set of bit strings of length n. q. A block cipher is an encryption algorithm E such that EK is a permutation of Bn for each key K � Characteristics ◦ ◦ ◦ Based on Shannon’s Theorem(1949) Same P => Same C {|P| = |C|} 64 bit, |P| |K| 56 bit Memoryless configuration Operate as stream cipher depending on mode Shortcut cryptanalysis (DC, LC etc) in 90’s * DC: Differential Cryptanalysis, LC: Linear Cryptanalysis 5

Design Criteria of DES � Provide a high level of security � Completely specify and easy to understand � Security must depend on hidden key, not algorithm � Available to all users � Adaptable for use in diverse applications � Economically implementable in electronic device � Efficient to use � Able to be validated � Exportable * Federal Register, May 15, 1973 6
DES(Data Encryption Standard) � Based on Lucifer (1972) � Developed by IBM and intervened by NSA � Adopted Federal Standard by NIST, revised every 5 years (~’ 98), � 64 bit block cipher, 56 bit key � 16 Round, Nonlinearity : S-box � Cryptanalysis like DC, LC, etc. after 1992 * DC: Differential Cryptanalysis, LC : Linear Cryptanalysis 7
FIPS Documents � � � FIPS PUB 46 -3, Data Encryption Standard”, 1977(83, 88, 93) (*) FIPS PUB 81, “DES modes of operation”, 1980(*) FIPS PUB 74, “Guidelines for implementing and using the NBS Data Encryption Standard”, 1981(*) FIPS PUB 113, “Computer Data Authentication”, 1985 FIPS PUB 140 -2, “Security Requirements for Cryptographic Modules”, 2001 * Federal Notice (July 26, 2004) Announcing Proposed Withdrawal of Federal Information Processing Standard (FIPS) for the Data Encryption Standard (DES) and Request for Comments “NIST determined that the strength of the DES algorithm is no longer sufficient to adequately protect Federal government information. As a result, NIST proposes to withdraw FIPS 46 -3, and the associated FIPS 74 and FIPS 81. Future use of DES by Federal agencies is to be permitted only as a component function of the Triple Data Encryption Algorithm (TDEA). TDEA may be used for the protection of Federal information; however, NIST encourages agencies to implement the faster and stronger algorithm specified by FIPS 197, Advanced Encryption Standard (AES) instead. NIST proposes issuing TDEA implementation guidance as a NIST Recommendation via its ``Special Publication'' series (rather than as a FIPS) as Special Publication 800 -67, Recommendation for Implementation of the Triple Data Encryption Algorithm (TDEA). “ FIPS: Federal Information Processing Standard 8
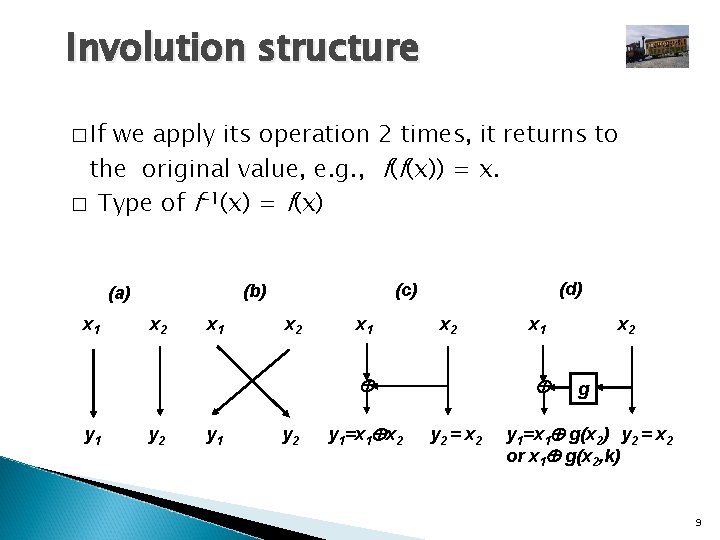
Involution structure � If we apply its operation 2 times, it returns to the original value, e. g. , f(f(x)) = x. � Type of f-1(x) = f(x) x 1 x 2 x 1 (d) (c) (b) (a) x 2 x 1 x 2 y 1 y 2 y 1=x 1 x 2 x 1 y 2 = x 2 g y 1=x 1 g(x 2) y 2 = x 2 or x 1 g(x 2, k) 9
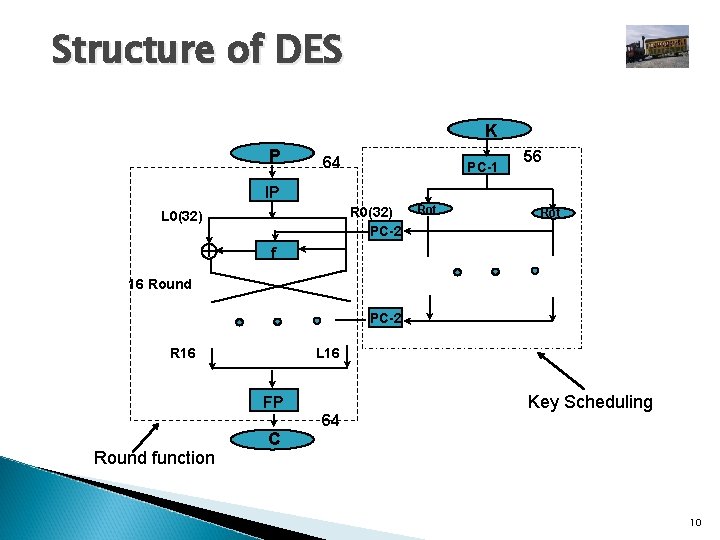
Structure of DES K P 64 PC-1 56 IP R 0(32) PC-2 L 0(32) Rot f 16 Round PC-2 R 16 L 16 FP 64 Round function Key Scheduling C 10
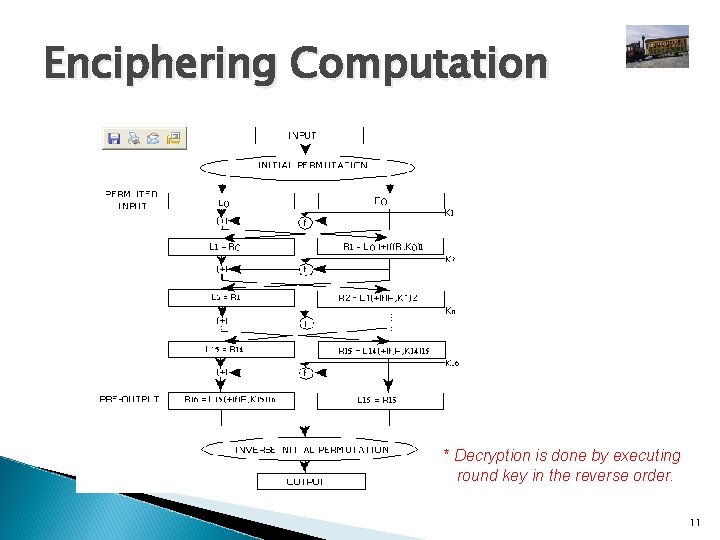
Enciphering Computation * Decryption is done by executing round key in the reverse order. 11

Initial Permutation & Final Permutation FP= IP-1 IP 58 60 62 64 57 59 61 63 50 52 54 56 49 51 53 55 42 44 46 48 41 43 45 47 34 36 38 40 33 35 37 39 26 28 30 32 25 27 29 31 18 20 22 24 17 19 21 23 10 12 14 16 9 11 13 15 2 4 6 8 1 3 5 7 40 39 38 37 36 35 34 33 8 7 6 5 4 3 2 1 48 47 46 45 44 43 42 41 16 56 15 55 14 54 13 53 12 52 11 51 10 50 9 49 24 23 22 21 20 19 18 17 64 63 62 61 60 59 58 57 32 31 30 29 28 27 26 25 cf. ) The 58 th bit of x is the first bit of IP(x) IP & FP have no cryptanalytic significance. 12

f-function of DES 13
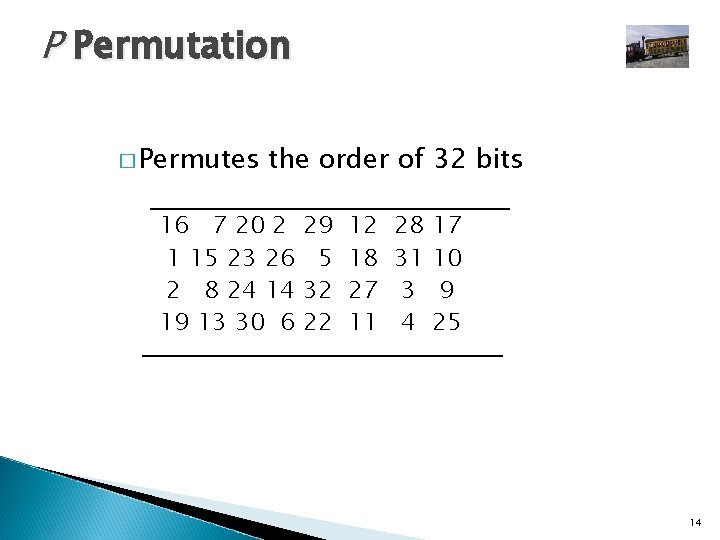
P Permutation � Permutes the order of 32 bits 16 7 20 2 1 15 23 26 2 8 24 14 19 13 30 6 29 5 32 22 12 18 27 11 28 31 3 4 17 10 9 25 14
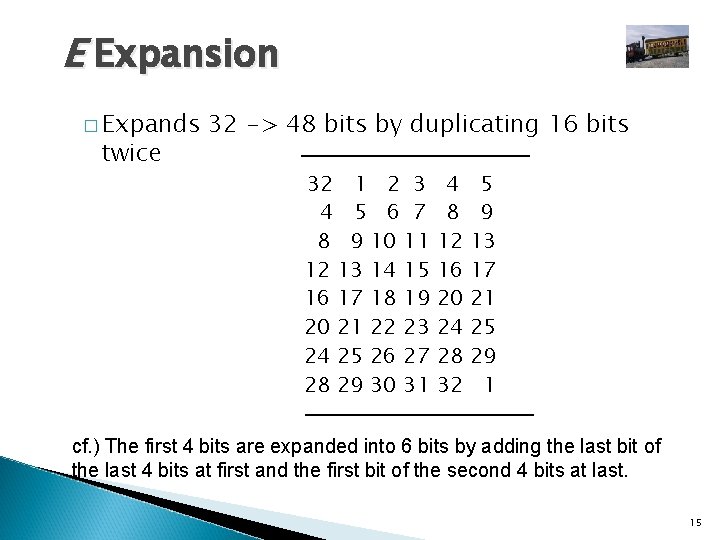
E Expansion � Expands twice 32 -> 48 bits by duplicating 16 bits 32 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 4 8 12 16 20 24 28 32 5 9 13 17 21 25 29 1 cf. ) The first 4 bits are expanded into 6 bits by adding the last bit of the last 4 bits at first and the first bit of the second 4 bits at last. 15

DES Key Scheduling 16

Permutated Choice-1(PC-1) � 64 -> 56 bits 57 1 10 19 63 7 14 21 49 41 33 25 17 9 58 50 42 34 26 18 2 59 51 43 35 27 11 3 60 52 44 36 55 47 39 31 23 15 62 54 46 38 30 22 6 61 53 45 37 29 13 5 28 20 12 4 cf. ) Do not use the parity check bits. 17
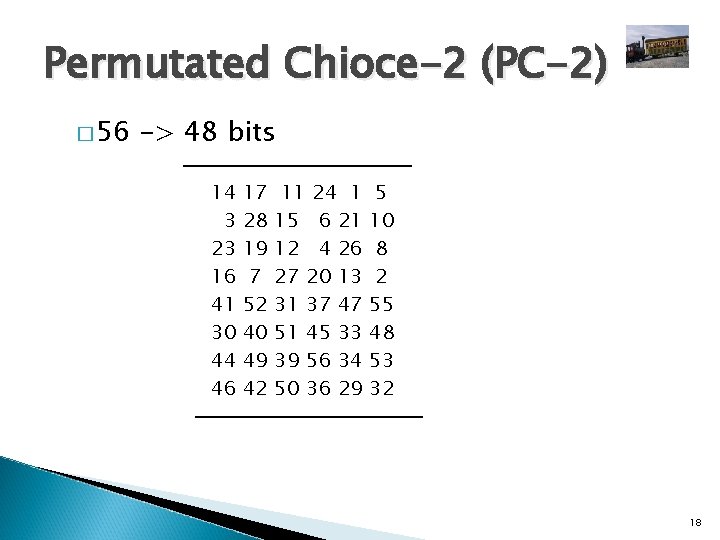
Permutated Chioce-2 (PC-2) � 56 -> 48 bits 14 3 23 16 41 30 44 46 17 28 19 7 52 40 49 42 11 24 1 15 6 21 12 4 26 27 20 13 31 37 47 51 45 33 39 56 34 50 36 29 5 10 8 2 55 48 53 32 18
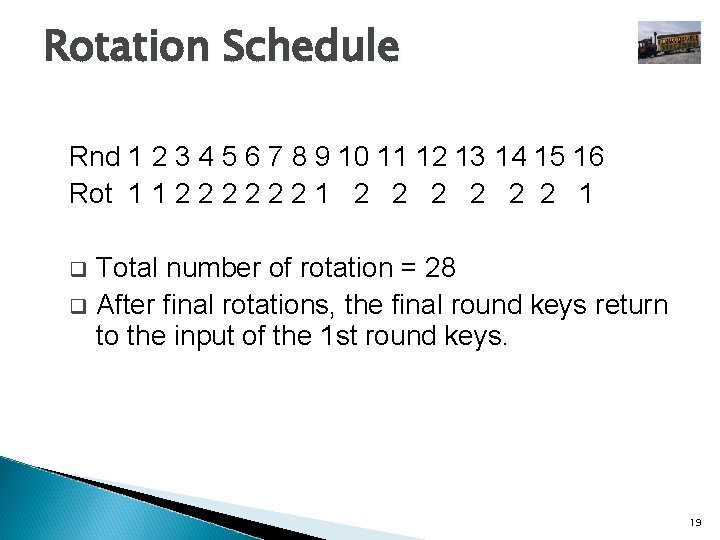
Rotation Schedule Rnd 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 Rot 1 1 2 2 2 1 Total number of rotation = 28 q After final rotations, the final round keys return to the input of the 1 st round keys. q 19

DES S-boxes � 8 S-boxes (6 -> 4 bits) � each row : permutation of 0 -15 � 4 rows : choose by MSB & LSB of input � some known design criteria ◦ not linear (affine) ◦ Any one bit of the inputs changes at least two output bits ◦ S(x) and S(x 001100) differs at least 2 bits ◦ S(x) S(x 11 ef 00) for any ef={00. 01. 10. 11} ◦ Resistance against DC etc. ◦ The actual design principles have never been revealed (U. S. classified information) 20
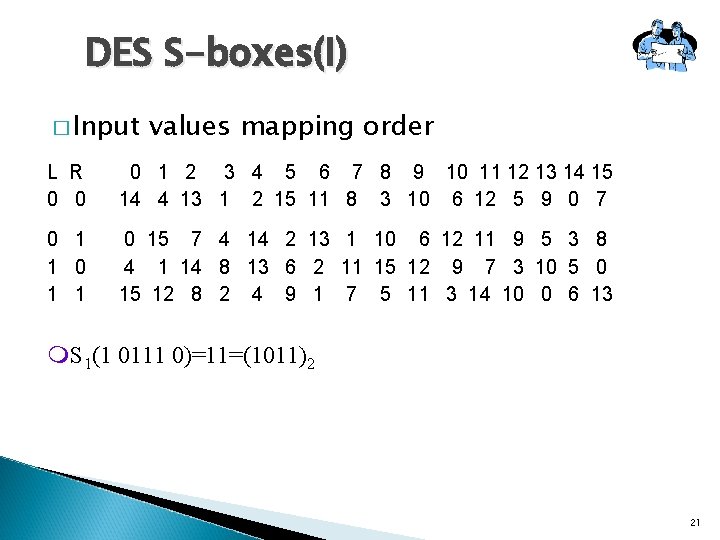
DES S-boxes(I) � Input values mapping order L R 0 0 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 14 4 13 1 2 15 11 8 3 10 6 12 5 9 0 7 0 1 1 0 15 7 4 14 2 13 1 10 6 12 11 9 5 3 8 4 1 14 8 13 6 2 11 15 12 9 7 3 10 5 0 15 12 8 2 4 9 1 7 5 11 3 14 10 0 6 13 m. S 1(1 0111 0)=11=(1011)2 21
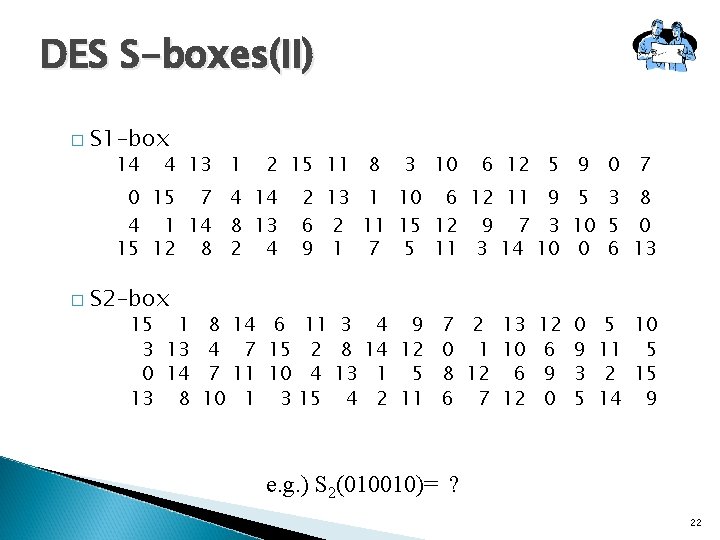
DES S-boxes(II) � S 1 -box 14 4 13 1 2 15 11 8 0 15 7 4 14 4 1 14 8 13 15 12 8 2 4 � S 2 -box 15 1 8 3 13 4 0 14 7 13 8 10 3 10 6 12 5 9 0 7 2 13 1 10 6 12 11 9 5 3 8 6 2 11 15 12 9 7 3 10 5 0 9 1 7 5 11 3 14 10 0 6 13 14 6 11 7 15 2 11 10 4 1 3 15 3 8 13 4 4 9 7 2 13 12 0 14 12 0 1 10 6 9 1 5 8 12 6 9 3 2 11 6 7 12 0 5 5 10 11 5 2 15 14 9 e. g. ) S 2(010010)= ? 22
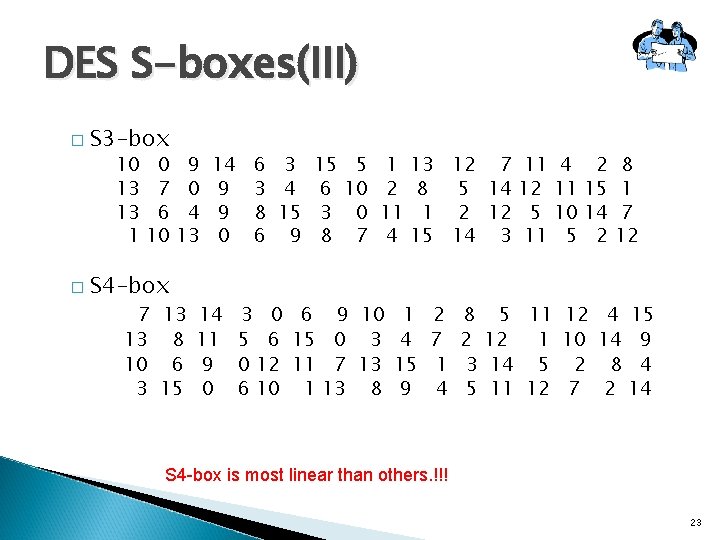
DES S-boxes(III) � S 3 -box 10 13 13 1 � 0 7 6 10 S 4 -box 9 0 4 13 14 9 9 0 6 3 3 4 8 15 6 9 15 6 3 8 5 10 0 7 1 2 11 4 13 12 7 11 8 5 14 12 1 2 12 5 15 14 3 11 7 13 14 3 0 6 9 10 1 13 8 11 5 6 15 0 3 4 10 6 9 0 12 11 7 13 15 0 6 10 1 13 8 9 2 7 1 4 4 11 10 5 2 15 14 2 8 1 7 12 8 5 11 12 4 15 2 12 1 10 14 9 3 14 5 2 8 4 5 11 12 7 2 14 S 4 -box is most linear than others. !!! 23
Criticism of DES �Short key size : 112 -> 56 bits by NSA �Classified design criteria �Revision of standard every 5 yrs after 1977 by NIST �No more standard 24

Cryptographic properties � (P, C) dependency with fixed Key : after 5 round � (K, C) dependency with fixed plaintext : after 5 round � Avalanche effect � Cyclic Test : Random function � Algebraic structure : Not a group i. e. , E(K 1, E(K 2, P)) E(K 3, P) 25
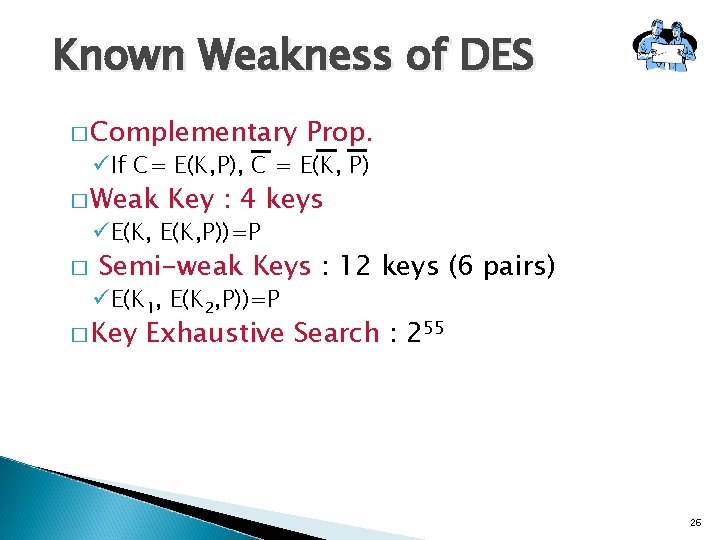
Known Weakness of DES � Complementary Prop. üIf C= E(K, P), C = E(K, P) � Weak Key : 4 keys üE(K, P))=P � Semi-weak Keys : 12 keys (6 pairs) üE(K 1, E(K 2, P))=P � Key Exhaustive Search : 255 26
- Slides: 26