BLOCK 2 UNIT 6 CYBER SECURITY Ver IT
BLOCK 2 UNIT 6 CYBER SECURITY Ver IT AA-1 1
OBJECTIVES 6 a. Identify basic facts about Cyber Security Ver IT AA-1 2
OBJECTIVE 6 a Identify basic facts about Cyber Security • Cyber vulnerabilities • Vulnerability preventative measures • Identity management • Wireless network security Ver IT AA-1 3
Identify basic facts about Cyber Security Cyber vulnerabilities Common types of threats • Denial of Service • Unauthorized Access • Executing Command Illicitly • Destructive Behavior Ver IT AA-1 4
Identify basic facts about Cyber Security Cyber vulnerabilities Denial of Service (Do. S) • Easy to launch, difficult to track • Send more requests to the machine than it can handle • Reduces the system availability so legitimate request cannot be processed Ver IT AA-1 5
Identify basic facts about Cyber Security Cyber vulnerabilities Denial of Service (Do. S) • Do. S preventative measures include: – Run servers below capacity – Use packet filtering to prevent forged packets – Keep security patches up to date Ver IT AA-1 6
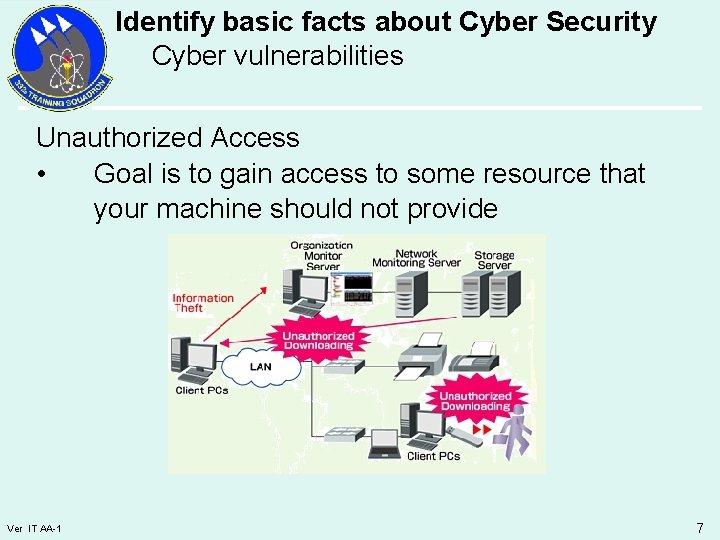
Identify basic facts about Cyber Security Cyber vulnerabilities Unauthorized Access • Goal is to gain access to some resource that your machine should not provide Ver IT AA-1 7
Identify basic facts about Cyber Security Cyber vulnerabilities Executing Commands Illicitly • Attacker gains access as a trusted user to run commands • By gaining normal user access, attacker may be able to change files • By gaining administrator access, attacker may be able to make configuration changes Ver IT AA-1 8
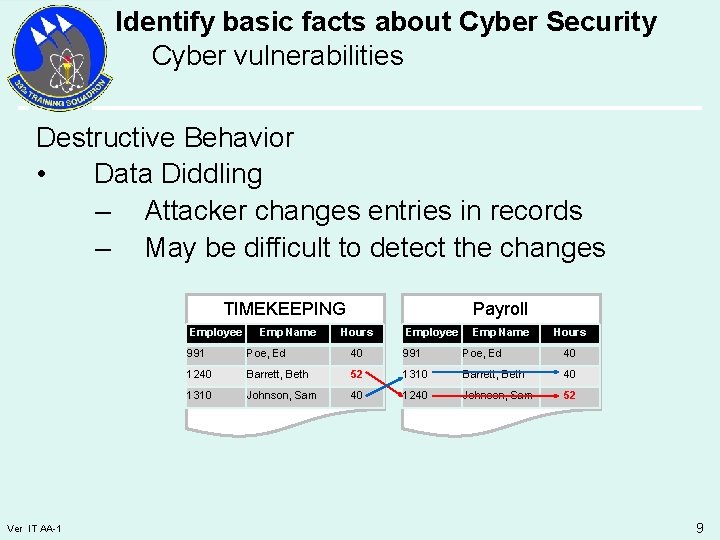
Identify basic facts about Cyber Security Cyber vulnerabilities Destructive Behavior • Data Diddling – Attacker changes entries in records – May be difficult to detect the changes TIMEKEEPING Employee Ver IT AA-1 Emp Name Payroll Hours Employee Emp Name Hours 991 Poe, Ed 40 1240 Barrett, Beth 52 1310 Barrett, Beth 40 1310 Johnson, Sam 40 1240 Johnson, Sam 52 9
Identify basic facts about Cyber Security Cyber vulnerabilities Destructive Behavior • Data destruction – Attacker deletes key files to impact computing capabilities Ver IT AA-1 10
Identify basic facts about Cyber Security Vulnerability Preventive Measures • • Ver IT AA-1 National efforts to identify & reduce vulnerabilities Initial efforts in four areas – The mechanisms of the Internet – Digital control systems/SCADA – Software – Physical security of cyber systems and transmission 11
Identify basic facts about Cyber Security Vulnerability Preventive Measures Secure the mechanisms of the Internet • Goal is development of secure and robust mechanisms • Efforts concentrated on three areas – Securing the Protocols – Improve Internet Routing – Improve Management Ver IT AA-1 12
Identify basic facts about Cyber Security Vulnerability Preventive Measures Secure the mechanisms of the Internet • Securing the Protocols – Ensure reliability & secure use of three key protocols that attackers may exploit • Internet Protocol (IP) • Domain Name System (DNS) • Border Gateway Protocol (BGP) Ver IT AA-1 13
Identify basic facts about Cyber Security Vulnerability Preventive Measures Secure the mechanisms of the Internet • Improve Internet Routing – Current routers are easy to disable through Do. S attacks – Strengthened source address verification needed to identify source of attack – Router out-of-band management developed so administrators can access router during Do. S attacks Ver IT AA-1 14
Identify basic facts about Cyber Security Vulnerability Preventive Measures Secure the mechanisms of the Internet • Improve Management – Best management practices need to be widely employed – Accomplished by • Adoption of improved security protocols • Development of secure router technology • Adoption by ISP’s of a “code of good conduct” Ver IT AA-1 15
Identify basic facts about Cyber Security Vulnerability Preventive Measures Foster trusted DCS/SCADA systems • Data Control System/Supervisory Control and Data Acquisition Systems (DCS/SCADA) – Present in almost every sector of our economy – Water, transportation, energy, manufacturing, etc – Increasingly use internet – Systems need increased security Ver IT AA-1 16
Identify basic facts about Cyber Security Vulnerability Preventive Measures Reduce and Remediate Software Vulnerabilities • Data Software flaws allow malicious actors to exploit current software • 3500 software vulnerabilities reported annually • Usually corrected by manufacturer • Distributed as a patch Ver IT AA-1 17
Identify basic facts about Cyber Security Vulnerability Preventive Measures Improve Physical Security of Cyber Systems • Protect key physical links and provide redundancy • Dependant infrastructures can cause impacts on what would seem to be unrelated systems • Infrastructures must be developed to increase reliability and redundancy Ver IT AA-1 18
Identify basic facts about Cyber Security Identity Management • • Ver IT AA-1 Goal: Secure cyber information 4 objectives to meet the goal – Authentication and Identification: verifies that you are who you say you are – Data Integrity: Alerts recipient of data modifications during transmission, storage, and processing – Non-repudiation: Provides accountability through a digital signature - Legally binding – Confidentiality: Protects data from unauthorized view 19
Identify basic facts about Cyber Security Identity Management • • Ver IT AA-1 Objectives and Goal are met through use of Do. D Public Key Infrastructure (PKI) & Common Access Card (CAC) PKI utilizes Public Key Encryption & Certificates Certificate binds your identity to the public key A Digital Signature is as legally binding as a hand written signature 20
Identify basic facts about Cyber Security Identity Management • • • Ver IT AA-1 E-mail is like a postcard written in pencil – Easily read and changed by others Digital Signature is like writing the postcard in ink – Easily read, but not easily changed by others Digital Signature and Encryption is like writing the postcard in ink, and sealing it in an envelope – Not easily read or changed by others 21
Identify basic facts about Cyber Security Identity Management • Ver IT AA-1 CAC contains 3 certificates assigned to you 1. Identity Certificate: • Identifies you to network devices and applications • Digital signature on non-email data 2. E-mail Signature Certificate: • Contains your public key used to verify digital signature on e-mail messages 22
Identify basic facts about Cyber Security Identity Management • • Ver IT AA-1 CAC contains 3 certificates assigned to you (Cont. ) 3. E-mail Encryption Certificate: • Contains your public key for others to encrypt email, and private key to decrypt Certificates and Keys are protected by Personal Identification Number (PIN) 23
Identify basic facts about Cyber Security Wireless Network Security Wireless Security Guidelines • Change default admin password & username – Default administrator name and passwords are commonly known • Turn on encryption – Protect the passphrase or key • Change default SSID – Service Set Identifier – Default name advertises a poorly configured network Ver IT AA-1 24
Identify basic facts about Cyber Security Wireless Network Security Wireless Security Guidelines • Disable SSID broadcast – If you do not need the SSID advertised, then turn off the broadcast • Enable MAC filtering – Specify the MAC address of devices authorized to connect • Do not auto-connect to open WI-FI networks • Assign static IP addresses to devices • Enable firewalls on each computer and the router Ver IT AA-1 25
Summary Identify basic facts about Cyber Security • Cyber vulnerabilities • Vulnerability preventative measures • Identity management • Wireless network security Ver IT AA-1 26
- Slides: 26