Bitte decken Sie die schraffierte Flche mit einem
Bitte decken Sie die schraffierte Fläche mit einem Bild ab. Please cover the shaded area with a picture. (24, 4 x 11, 0 cm) Software security in Automotive Systems Course 11 www. continental-corporation. com Interior Body and Security
Software Security in Automotive Systems Table Of Contents 34 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 2
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 3
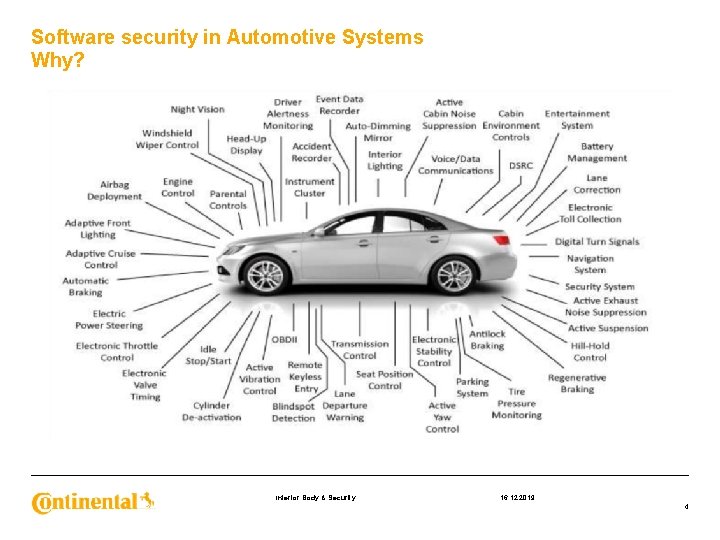
Software security in Automotive Systems Why? Interior Body & Security 16. 12. 2019 4
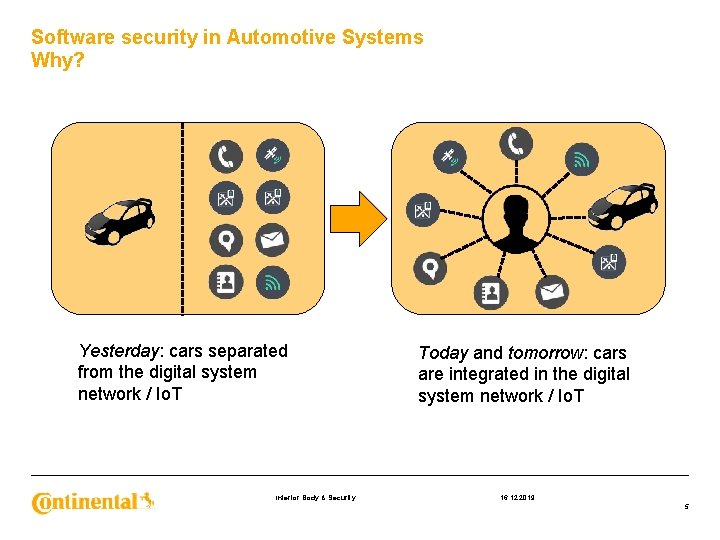
Software security in Automotive Systems Why? Yesterday: cars separated from the digital system network / Io. T Interior Body & Security Today and tomorrow: cars are integrated in the digital system network / Io. T 16. 12. 2019 5
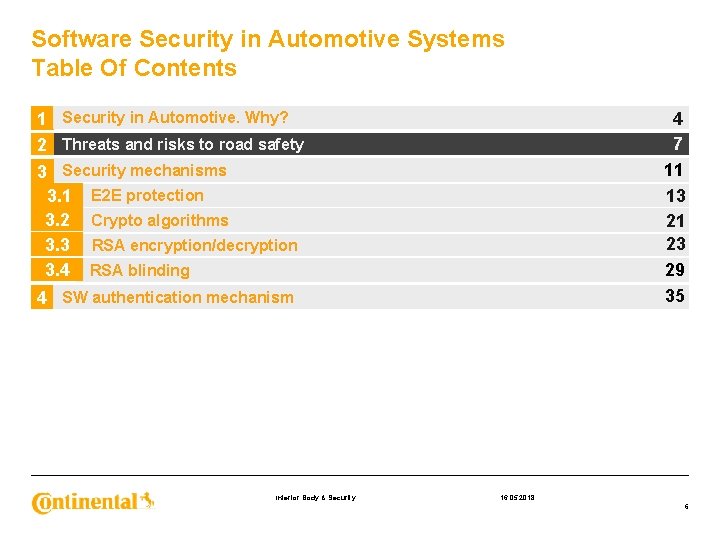
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 6
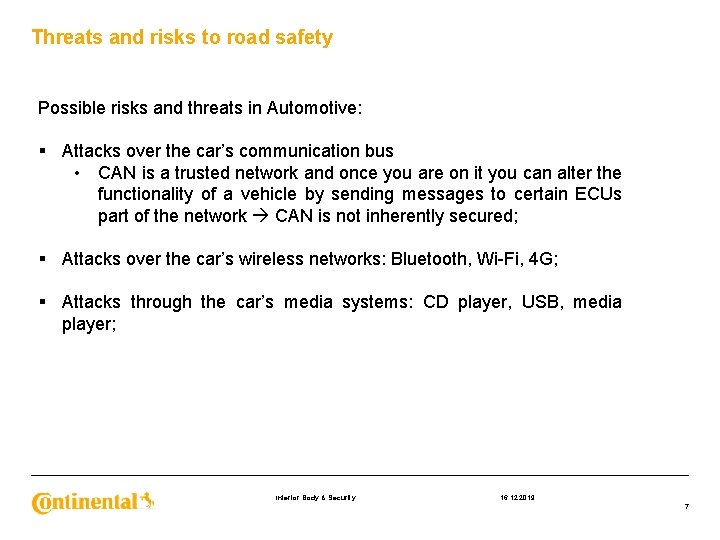
Threats and risks to road safety Possible risks and threats in Automotive: § Attacks over the car’s communication bus • CAN is a trusted network and once you are on it you can alter the functionality of a vehicle by sending messages to certain ECUs part of the network CAN is not inherently secured; § Attacks over the car’s wireless networks: Bluetooth, Wi-Fi, 4 G; § Attacks through the car’s media systems: CD player, USB, media player; Interior Body & Security 16. 12. 2019 7
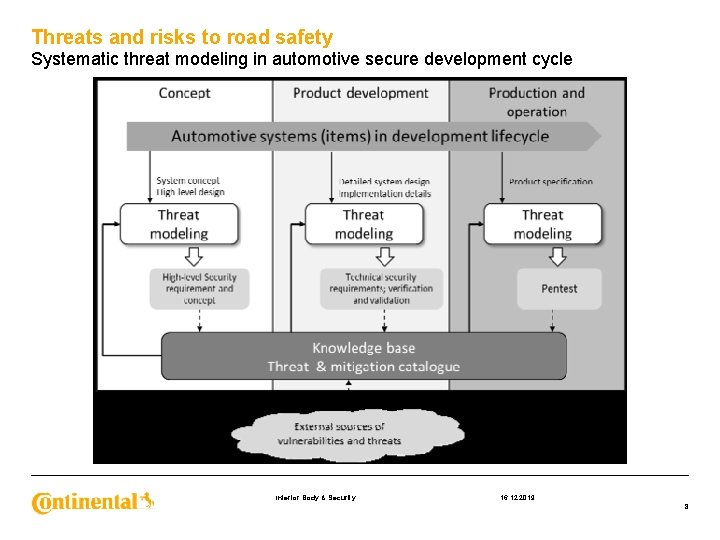
Threats and risks to road safety Systematic threat modeling in automotive secure development cycle Interior Body & Security 16. 12. 2019 8
Threats and risks to road safety § Safety critical risks • Driver distraction (e. g. volume, wipers); • Engine shutoff or degradation; • Steering changes (autonomous vehicles); § Less Safety-Critical vehicle specific risks; • Theft of the car or contents; • Insurance or lease fraud; • Theft of information; • Vector for attacking mobile devices in the car; Interior Body & Security 16. 12. 2019 9
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 10
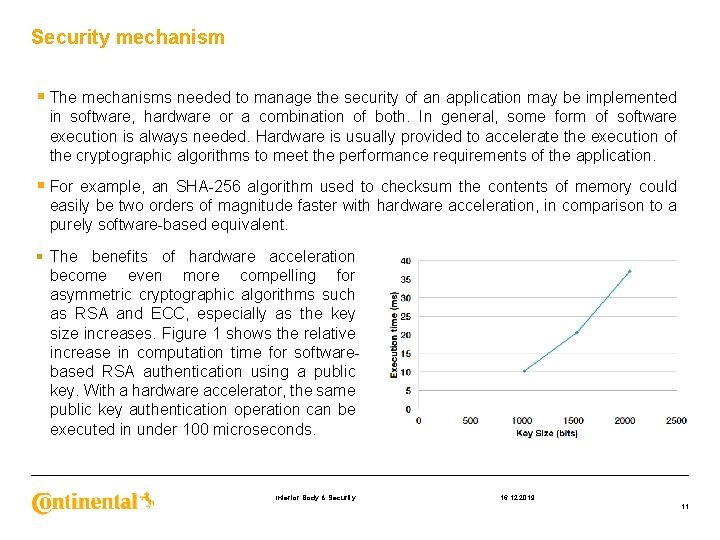
Security mechanism § The mechanisms needed to manage the security of an application may be implemented in software, hardware or a combination of both. In general, some form of software execution is always needed. Hardware is usually provided to accelerate the execution of the cryptographic algorithms to meet the performance requirements of the application. § For example, an SHA-256 algorithm used to checksum the contents of memory could easily be two orders of magnitude faster with hardware acceleration, in comparison to a purely software-based equivalent. § The benefits of hardware acceleration become even more compelling for asymmetric cryptographic algorithms such as RSA and ECC, especially as the key size increases. Figure 1 shows the relative increase in computation time for softwarebased RSA authentication using a public key. With a hardware accelerator, the same public key authentication operation can be executed in under 100 microseconds. Interior Body & Security 16. 12. 2019 11
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 12
Security mechanisms End to end (E 2 E) protection § E 2 E communication protection aims to detect and mitigate the causes for or effects of communication faults arising from: 1. (systematic) software faults 2. (random) hardware faults 3. Transient faults due to external faults; Interior Body & Security 16. 12. 2019 13
Security mechanisms End to end (E 2 E) protection With respect to the exchange of information in safety-related systems, the mechanisms for the in-time detection of causes for faults, or effects of faults as those listed below, can be used to design suitable safety concepts (i. e. to achieve freedom from interference between system elements sharing a common communication infrastructure). § loss of information; § insertion of information; § masquerade or incorrect addressing of information; § incorrect sequence of information; § corruption of information; § asymmetric information sent from a sender to multiple receivers; § information from a sender received by only a subset of the receivers; § blocking access to a communication channel. Interior Body & Security 16. 12. 2019 14
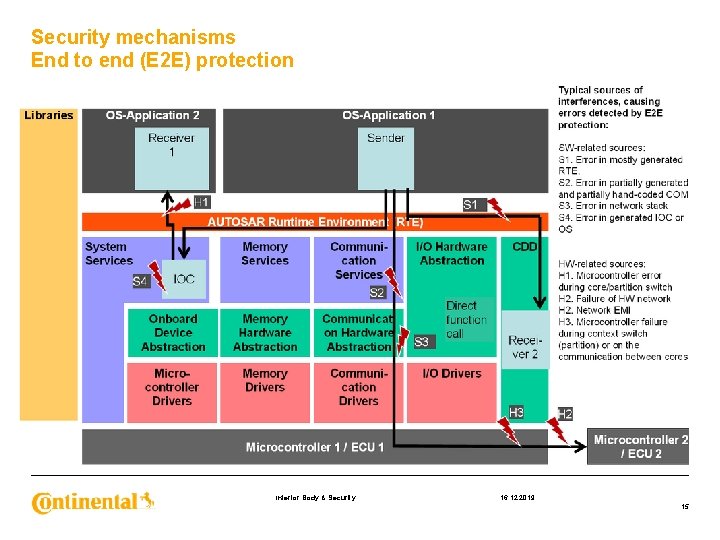
Security mechanisms End to end (E 2 E) protection Interior Body & Security 16. 12. 2019 15
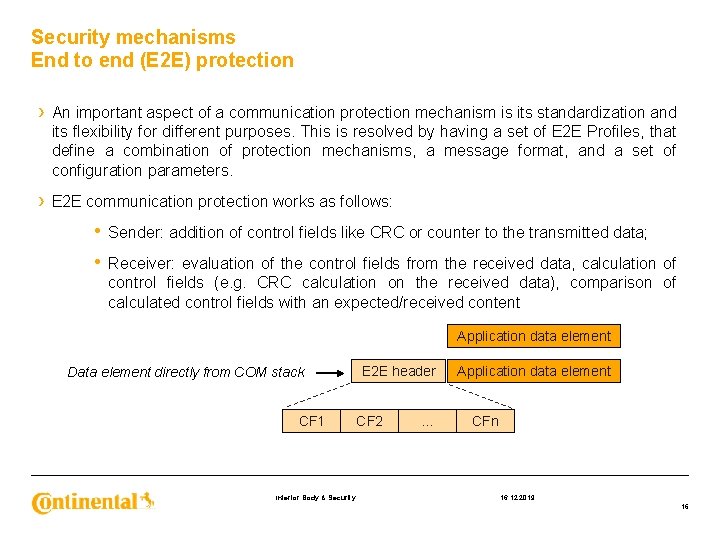
Security mechanisms End to end (E 2 E) protection › An important aspect of a communication protection mechanism is its standardization and its flexibility for different purposes. This is resolved by having a set of E 2 E Profiles, that define a combination of protection mechanisms, a message format, and a set of configuration parameters. › E 2 E communication protection works as follows: • Sender: addition of control fields like CRC or counter to the transmitted data; • Receiver: evaluation of the control fields from the received data, calculation of control fields (e. g. CRC calculation on the received data), comparison of calculated control fields with an expected/received content Application data element Data element directly from COM stack CF 1 Interior Body & Security E 2 E header CF 2 … Application data element CFn 16. 12. 2019 16
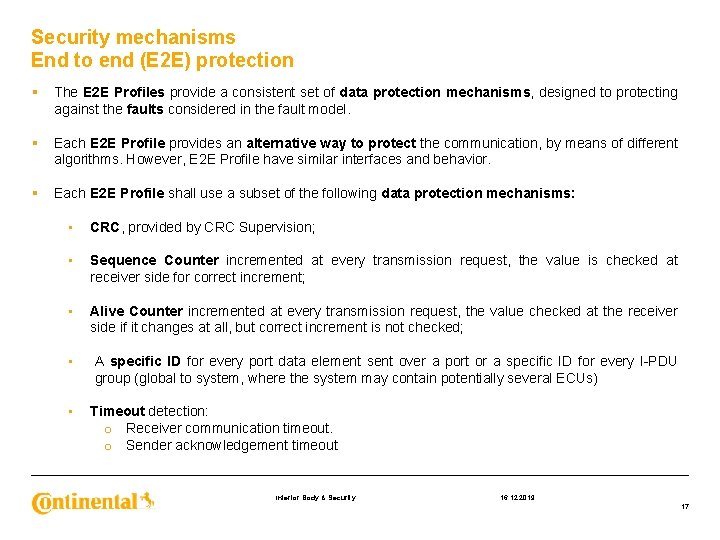
Security mechanisms End to end (E 2 E) protection § The E 2 E Profiles provide a consistent set of data protection mechanisms, designed to protecting against the faults considered in the fault model. § Each E 2 E Profile provides an alternative way to protect the communication, by means of different algorithms. However, E 2 E Profile have similar interfaces and behavior. § Each E 2 E Profile shall use a subset of the following data protection mechanisms: • CRC, provided by CRC Supervision; • Sequence Counter incremented at every transmission request, the value is checked at receiver side for correct increment; • Alive Counter incremented at every transmission request, the value checked at the receiver side if it changes at all, but correct increment is not checked; • A specific ID for every port data element sent over a port or a specific ID for every I-PDU group (global to system, where the system may contain potentially several ECUs) • Timeout detection: o Receiver communication timeout. o Sender acknowledgement timeout Interior Body & Security 16. 12. 2019 17
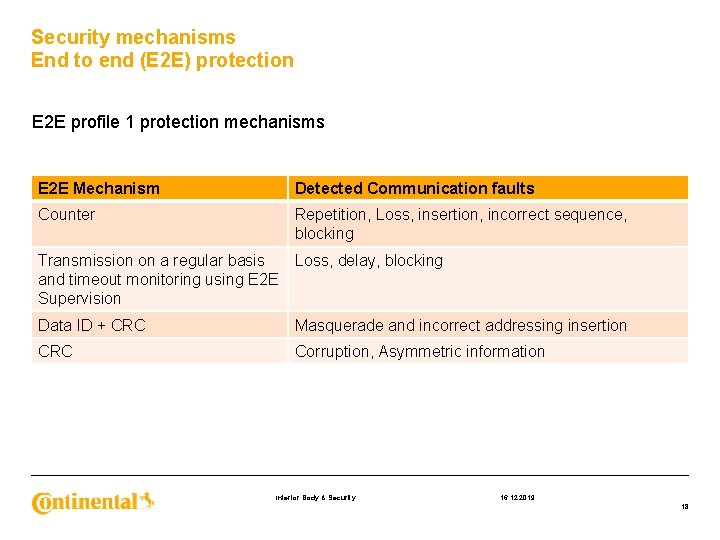
Security mechanisms End to end (E 2 E) protection E 2 E profile 1 protection mechanisms E 2 E Mechanism Detected Communication faults Counter Repetition, Loss, insertion, incorrect sequence, blocking Transmission on a regular basis and timeout monitoring using E 2 E Supervision Loss, delay, blocking Data ID + CRC Masquerade and incorrect addressing insertion CRC Corruption, Asymmetric information Interior Body & Security 16. 12. 2019 18
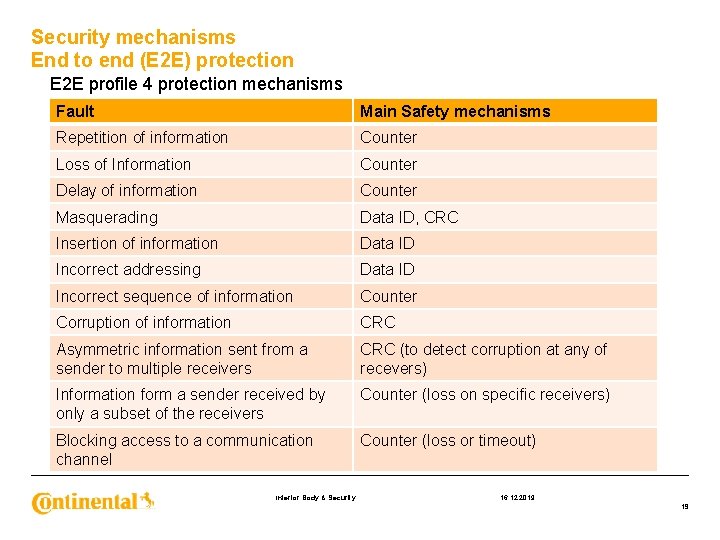
Security mechanisms End to end (E 2 E) protection E 2 E profile 4 protection mechanisms Fault Main Safety mechanisms Repetition of information Counter Loss of Information Counter Delay of information Counter Masquerading Data ID, CRC Insertion of information Data ID Incorrect addressing Data ID Incorrect sequence of information Counter Corruption of information CRC Asymmetric information sent from a sender to multiple receivers CRC (to detect corruption at any of recevers) Information form a sender received by only a subset of the receivers Counter (loss on specific receivers) Blocking access to a communication channel Counter (loss or timeout) Interior Body & Security 16. 12. 2019 19
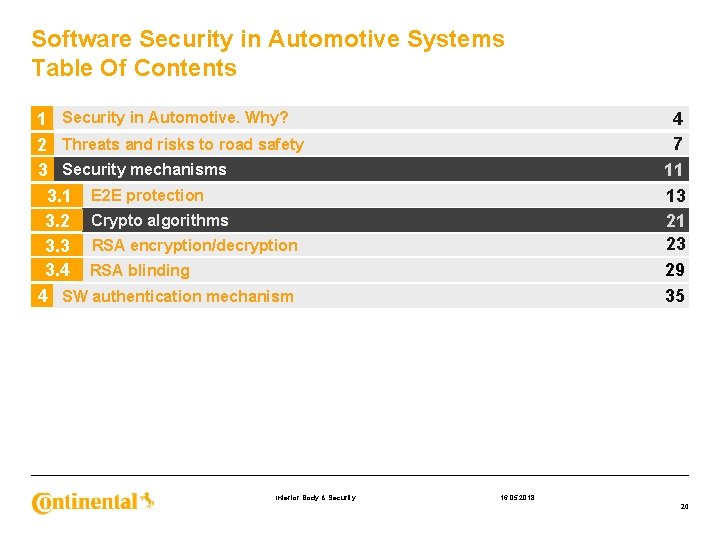
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 20
Security mechanisms Crypto algorithms › Crypto(graphic) algorithms are essentially mathematical computations designed to perform encryption and decryption of a message. The two main categories of algorithms are symmetric and asymmetric. › Symmetric cryptography algorithms use the same key for encryption and decryption. The key must therefore be kept secret by all entities that use the key for secure communications. This may pose a problem with distributing the key to new entities, unless a method such as Diffie-Hellman is used, as described in the Secret Key Exchange section below. Interior Body & Security 16. 12. 2019 21
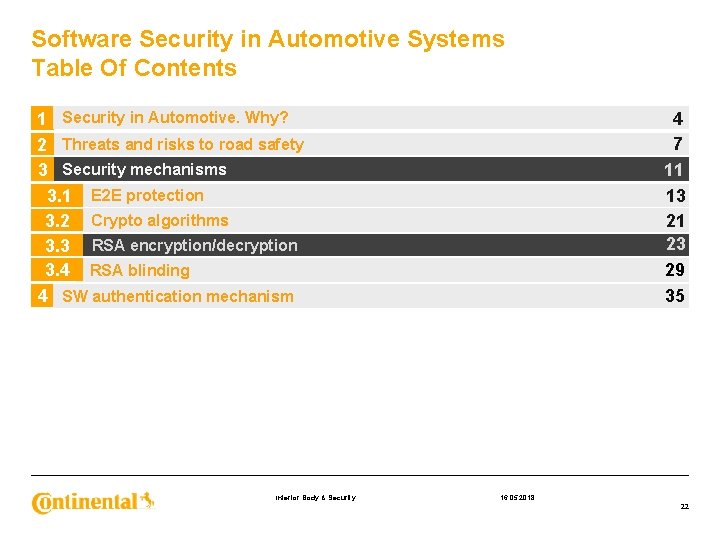
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 22
Security mechanisms RSA encryption/decryption § The RSA cryptosystem was invented by Ron Rivest, Adi Shamir and Len Adleman, and first publicized in the August 1977 issue of Scientific American. § The cryptosystem is most commonly used for providing privacy and ensuring authenticity of digital data. § These days RSA is deployed in many commercial systems : web servers and browsers to secure web traffic, it is used to ensure privacy and authenticity of Email, it is used to secure remote login sessions and it is at the heart of electronic credit-card payment systems. In short RSA is frequently used in applications where security of digital data is a concern. § Since initial publication the RSA system has been analyzed for vulnerability by researchers, and although these led to a number of fascinating attacks, the mostly only showed the danger of improper use of RSA. Interior Body & Security 16. 12. 2019 23
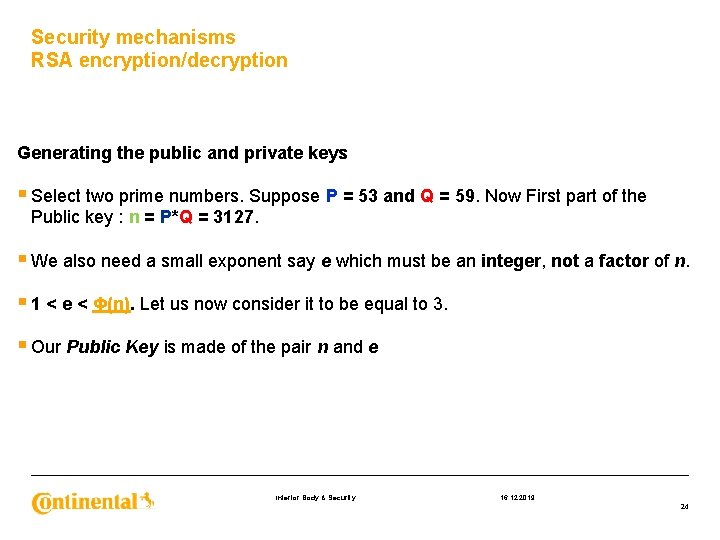
Security mechanisms RSA encryption/decryption Generating the public and private keys § Select two prime numbers. Suppose P = 53 and Q = 59. Now First part of the Public key : n = P*Q = 3127. § We also need a small exponent say e which must be an integer, not a factor of n. § 1 < e < Φ(n). Let us now consider it to be equal to 3. § Our Public Key is made of the pair n and e Interior Body & Security 16. 12. 2019 24
Security mechanisms RSA encryption/decryption Generating the public and private keys § We need to calculate Φ(n), such that Φ(n) = (P-1)(Q-1) so, Φ(n) = 3016 § Now calculate Private Key, d : d = (k*Φ(n) + 1) / e for some integer k For k = 2, value of d is 2011. § Now we have the pair of public and private keys: § Public Key ( n = 3127, e = 3) § Private Key (n = 3127, d = 2011) Interior Body & Security 16. 12. 2019 25
Security mechanisms RSA encryption/decryption Generating the public and private keys § We need to calculate Φ(n), such that Φ(n) = (P-1)(Q-1) so, Φ(n) = 3016 § Now calculate Private Key, d : d = (k*Φ(n) + 1) / e for some integer k For k = 2, value of d is 2011. § Now we have the pair of public and private keys: § Public Key ( n = 3127, e = 3) § Private Key (n = 3127, d = 2011) Interior Body & Security 16. 12. 2019 26
Security mechanisms RSA encryption/decryption Encryption § Convert letters to numbers : H = 8 and I = 9; § Thus Encrypted Data c = 89 e mod n; § Thus our Encrypted Data comes out to be 1394. Decryption § Now we will decrypt 1394; § Decrypted Data = cd mod n; § Thus our Encrypted Data comes out to be 89 8 = H and I = 9 i. e. "HI". Interior Body & Security 16. 12. 2019 27
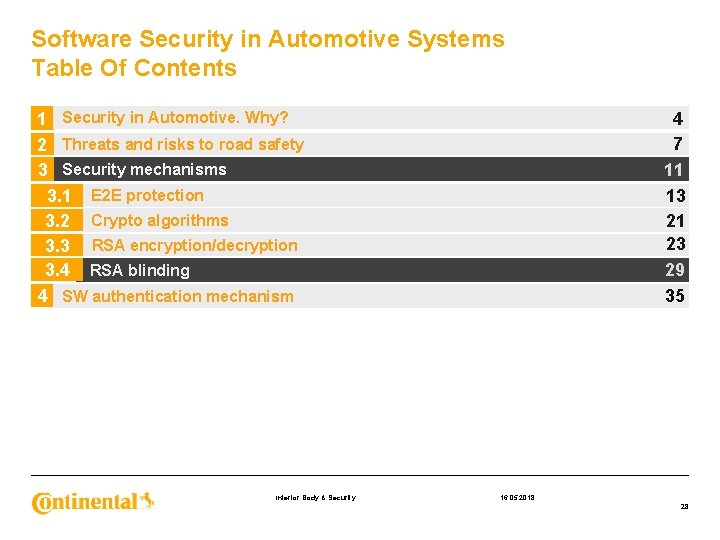
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 28
Security mechanisms RSA blinding Author of the message m Signing authority - blinded message m’ SW/HW entity SW entity Interior Body & Security 16. 12. 2019 29
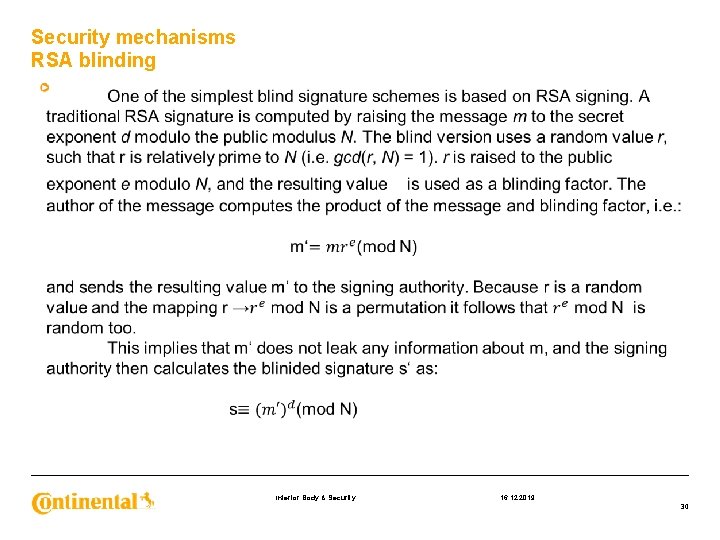
Security mechanisms RSA blinding Interior Body & Security 16. 12. 2019 30
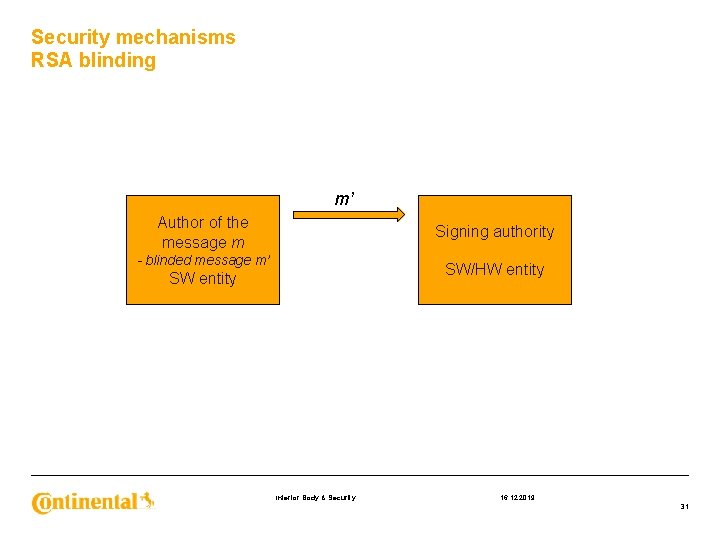
Security mechanisms RSA blinding m’ Author of the message m Signing authority - blinded message m’ SW/HW entity SW entity Interior Body & Security 16. 12. 2019 31
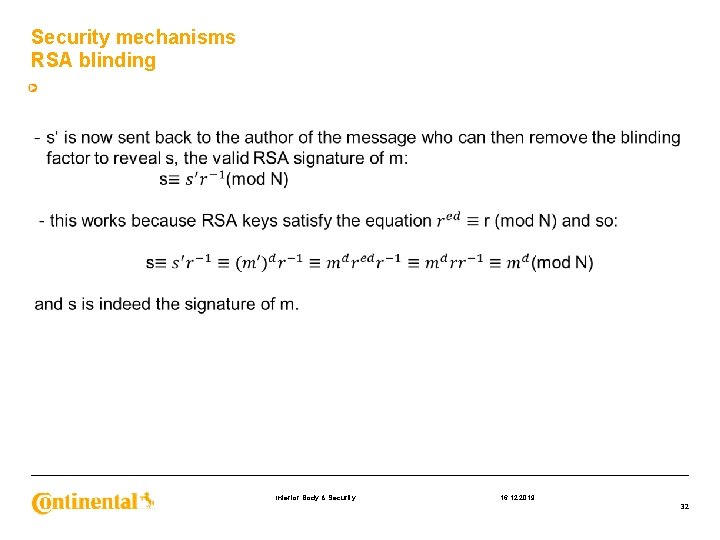
Security mechanisms RSA blinding Interior Body & Security 16. 12. 2019 32
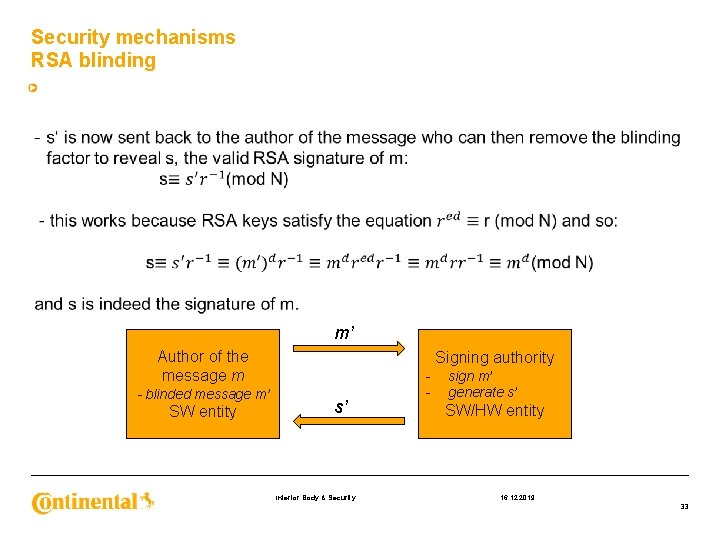
Security mechanisms RSA blinding m’ Author of the message m - blinded message m’ SW entity Signing authority s’ Interior Body & Security - sign m’ generate s’ SW/HW entity 16. 12. 2019 33
Software Security in Automotive Systems Table Of Contents 34 9 7 11 13 21 23 29 35 1 Security in Automotive. Why? 2 Threats and risks to road safety 3 Security mechanisms 3. 1 E 2 E protection 3. 2 Crypto algorithms 3. 3 RSA encryption/decryption 3. 4 RSA blinding 4 SW authentication mechanism Interior Body & Security 16. 05. 2018 34
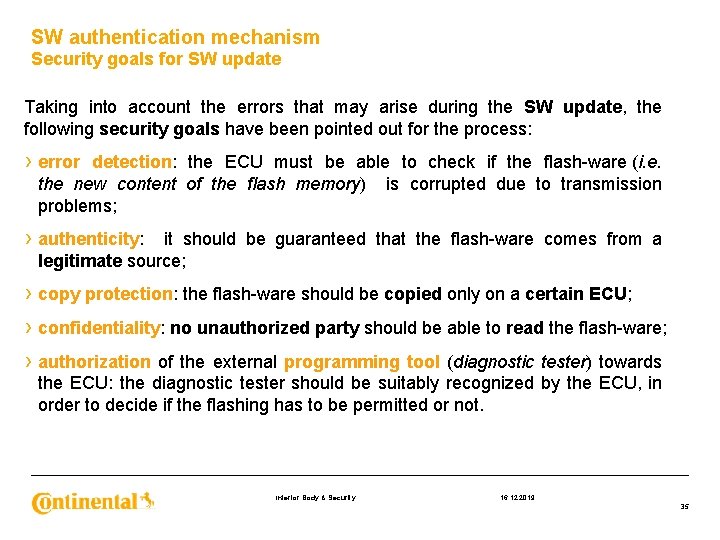
SW authentication mechanism Security goals for SW update Taking into account the errors that may arise during the SW update, the following security goals have been pointed out for the process: › error detection: the ECU must be able to check if the flash-ware (i. e. the new content of the flash memory) is corrupted due to transmission problems; › authenticity: it should be guaranteed that the flash-ware comes from a legitimate source; › copy protection: the flash-ware should be copied only on a certain ECU; › confidentiality: no unauthorized party should be able to read the flash-ware; › authorization of the external programming tool (diagnostic tester) towards the ECU: the diagnostic tester should be suitably recognized by the ECU, in order to decide if the flashing has to be permitted or not. Interior Body & Security 16. 12. 2019 35
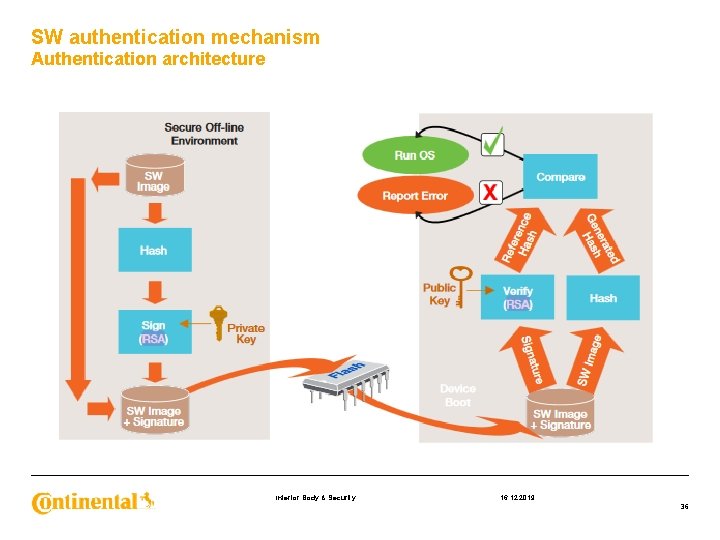
SW authentication mechanism Authentication architecture Interior Body & Security 16. 12. 2019 36
Software security in Automotive Systems › “Twenty Years of Attacks on the RSA Cryptosystem”, DAN Boneh › “ACEA Principles of Automobile Cybersecurity”, European Automobile Manufacturer’s Association › “E 2 E Protocol Specification”, AUTOSAR › Continental Documents Interior Body & Security 16. 12. 2019 37
- Slides: 37