Bit Locker Drive Encryption Hardware Enhanced Data Protection

Bit. Locker™ Drive Encryption Hardware Enhanced Data Protection Shon Eizenhoefer, Program Manager Microsoft Corporation
Agenda Security Background Bit. Locker™ Drive Encryption TPM Overview Building a Bit. Locker™ Capable System Additional Resources
Bit. Locker™ Drive Encryption gives you improved data protection on your Windows Vista and Windows Server codenamed “Longhorn” systems Notebooks – Often stolen, easily lost in transit Desktops – Often stolen, difficult to safely decommission Servers – High value targets, often kept in insecure locations All three can contain very sensitive IP and customer data Designed to provide a transparent user experience that requires little to no interaction on a protected system Prevents thieves from using another OS or software hacking tool to break OS file and system protections Prevents offline viewing of user data and OS files Provides enhanced data protection and boot validation through use of a Trusted Platform Module (TPM) v 1. 2
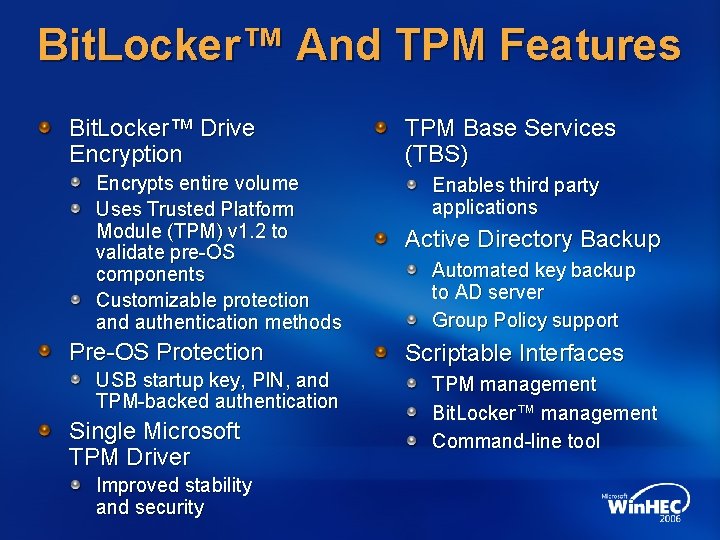
Bit. Locker™ And TPM Features Bit. Locker™ Drive Encryption Encrypts entire volume Uses Trusted Platform Module (TPM) v 1. 2 to validate pre-OS components Customizable protection and authentication methods Pre-OS Protection USB startup key, PIN, and TPM-backed authentication Single Microsoft TPM Driver Improved stability and security TPM Base Services (TBS) Enables third party applications Active Directory Backup Automated key backup to AD server Group Policy support Scriptable Interfaces TPM management Bit. Locker™ management Command-line tool
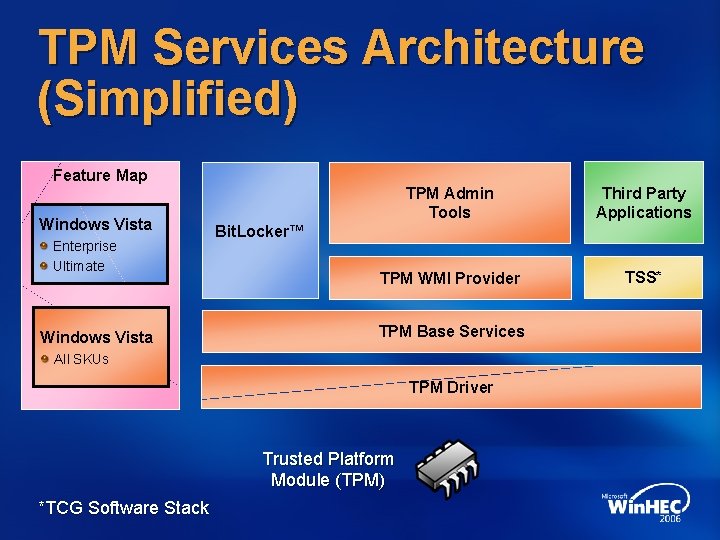
TPM Services Architecture (Simplified) Feature Map Windows Vista Enterprise Ultimate Windows Vista TPM Admin Tools Third Party Applications TPM WMI Provider TSS* Bit. Locker™ TPM Base Services All SKUs TPM Driver Trusted Platform Module (TPM) *TCG Software Stack
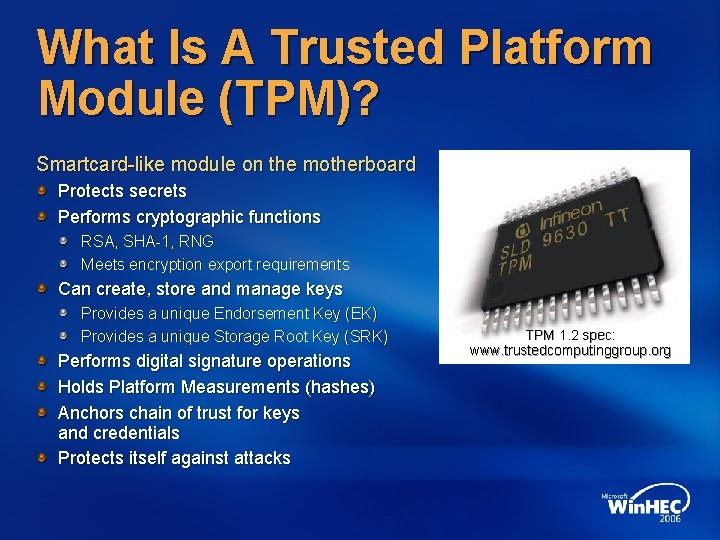
What Is A Trusted Platform Module (TPM)? Smartcard-like module on the motherboard Protects secrets Performs cryptographic functions RSA, SHA-1, RNG Meets encryption export requirements Can create, store and manage keys Provides a unique Endorsement Key (EK) Provides a unique Storage Root Key (SRK) Performs digital signature operations Holds Platform Measurements (hashes) Anchors chain of trust for keys and credentials Protects itself against attacks TPM 1. 2 spec: www. trustedcomputinggroup. org
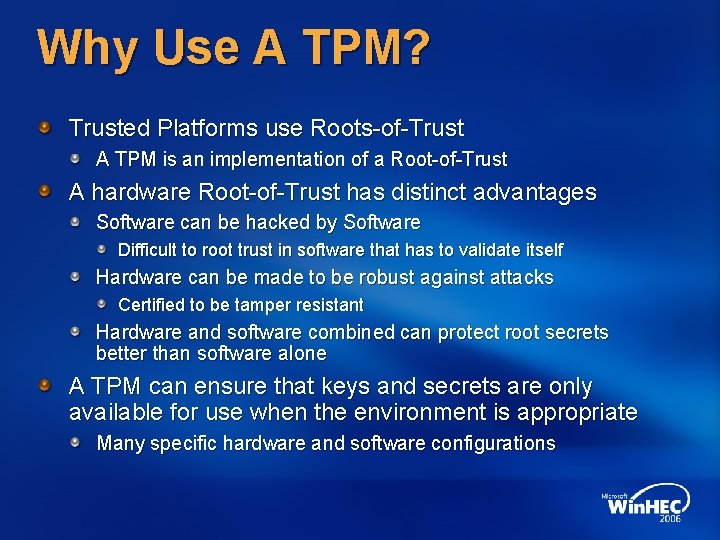
Why Use A TPM? Trusted Platforms use Roots-of-Trust A TPM is an implementation of a Root-of-Trust A hardware Root-of-Trust has distinct advantages Software can be hacked by Software Difficult to root trust in software that has to validate itself Hardware can be made to be robust against attacks Certified to be tamper resistant Hardware and software combined can protect root secrets better than software alone A TPM can ensure that keys and secrets are only available for use when the environment is appropriate Many specific hardware and software configurations
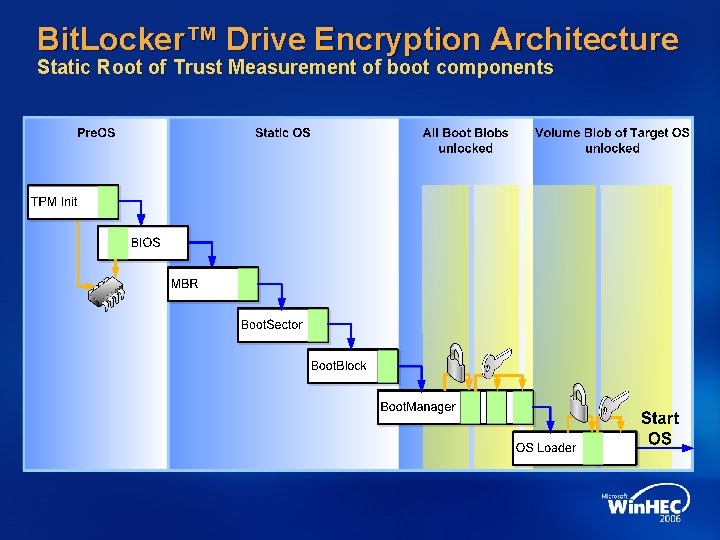
Bit. Locker™ Drive Encryption Architecture Static Root of Trust Measurement of boot components
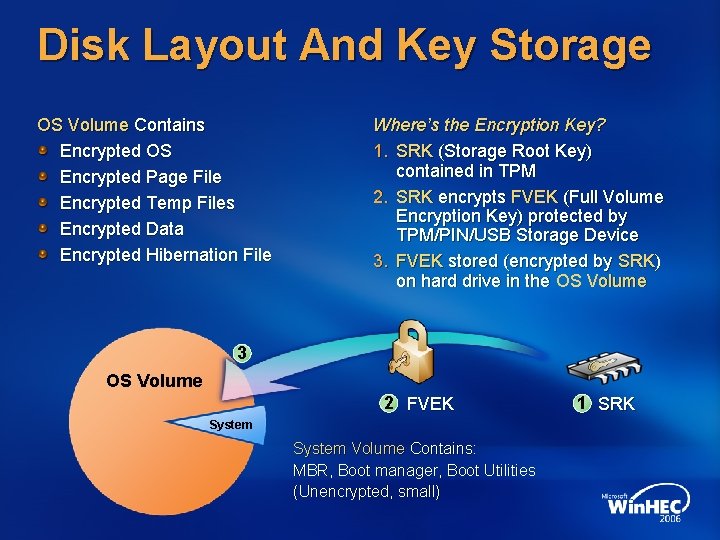
Disk Layout And Key Storage OS Volume Contains Encrypted OS Encrypted Page File Encrypted Temp Files Encrypted Data Encrypted Hibernation File Where’s the Encryption Key? 1. SRK (Storage Root Key) contained in TPM 2. SRK encrypts FVEK (Full Volume Encryption Key) protected by TPM/PIN/USB Storage Device 3. FVEK stored (encrypted by SRK) on hard drive in the OS Volume 3 OS Volume 2 FVEK System Volume Contains: MBR, Boot manager, Boot Utilities (Unencrypted, small) 1 SRK
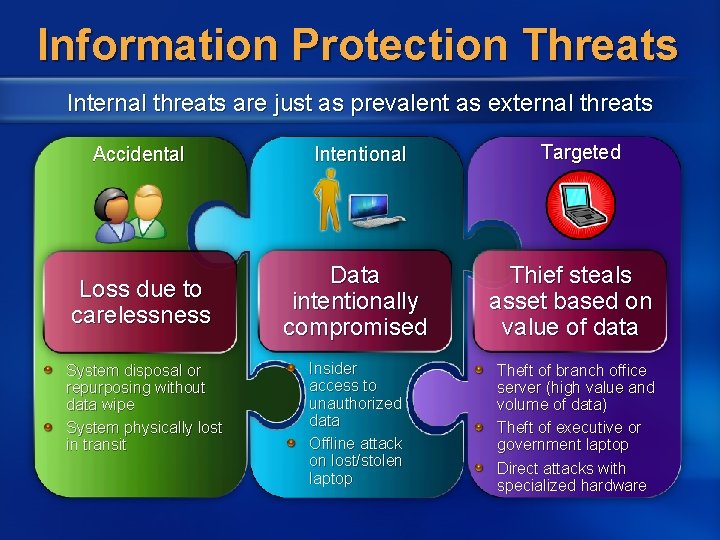
Information Protection Threats Internal threats are just as prevalent as external threats Accidental Intentional Loss due to carelessness Data intentionally compromised System disposal or repurposing without data wipe System physically lost in transit Insider access to unauthorized data Offline attack on lost/stolen laptop Targeted Thief steals asset based on value of data Theft of branch office server (high value and volume of data) Theft of executive or government laptop Direct attacks with specialized hardware
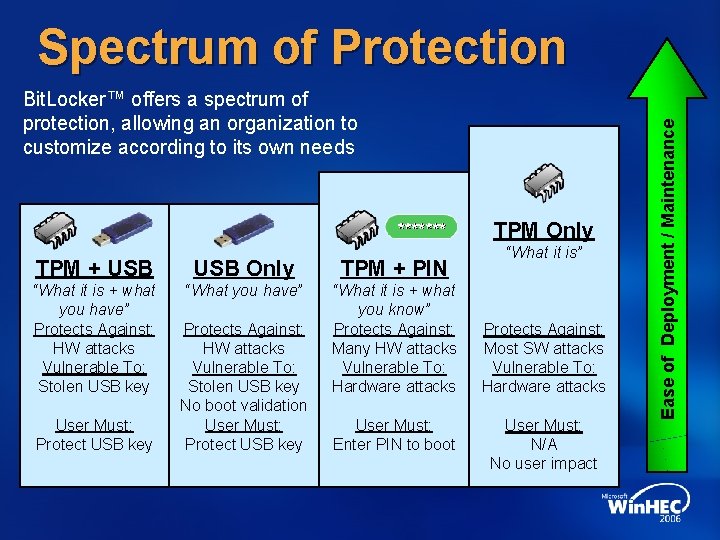
Bit. Locker™ offers a spectrum of protection, allowing an organization to customize according to its own needs TPM Only TPM + USB Only TPM + PIN “What it is + what you have” Protects Against: HW attacks Vulnerable To: Stolen USB key “What you have” “What it is + what you know” Protects Against: Many HW attacks Vulnerable To: Hardware attacks User Must: Protect USB key Protects Against: HW attacks Vulnerable To: Stolen USB key No boot validation User Must: Protect USB key User Must: Enter PIN to boot “What it is” Protects Against: Most SW attacks Vulnerable To: Hardware attacks User Must: N/A No user impact Ease of Deployment / Maintenance Spectrum of Protection
Bit. Locker™ Interface Microsoft System Integrity Team
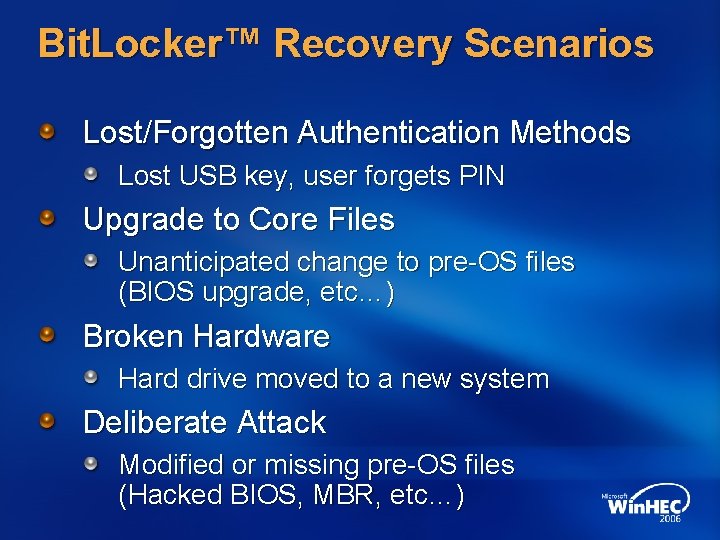
Bit. Locker™ Recovery Scenarios Lost/Forgotten Authentication Methods Lost USB key, user forgets PIN Upgrade to Core Files Unanticipated change to pre-OS files (BIOS upgrade, etc…) Broken Hardware Hard drive moved to a new system Deliberate Attack Modified or missing pre-OS files (Hacked BIOS, MBR, etc…)
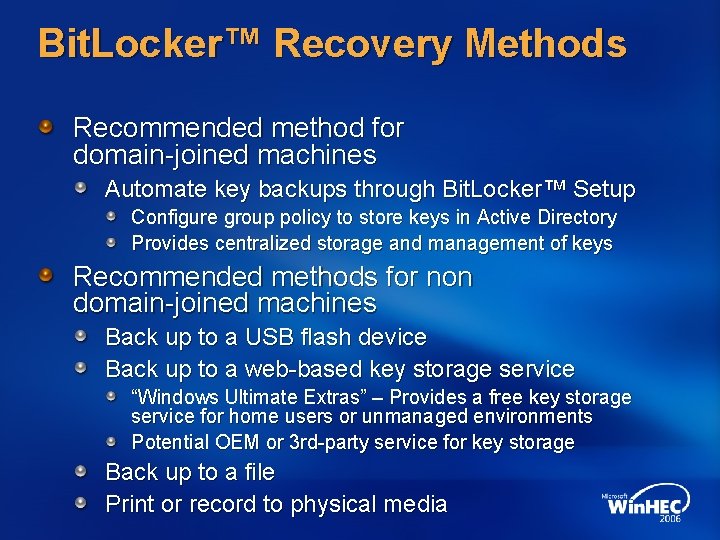
Bit. Locker™ Recovery Methods Recommended method for domain-joined machines Automate key backups through Bit. Locker™ Setup Configure group policy to store keys in Active Directory Provides centralized storage and management of keys Recommended methods for non domain-joined machines Back up to a USB flash device Back up to a web-based key storage service “Windows Ultimate Extras” – Provides a free key storage service for home users or unmanaged environments Potential OEM or 3 rd-party service for key storage Back up to a file Print or record to physical media
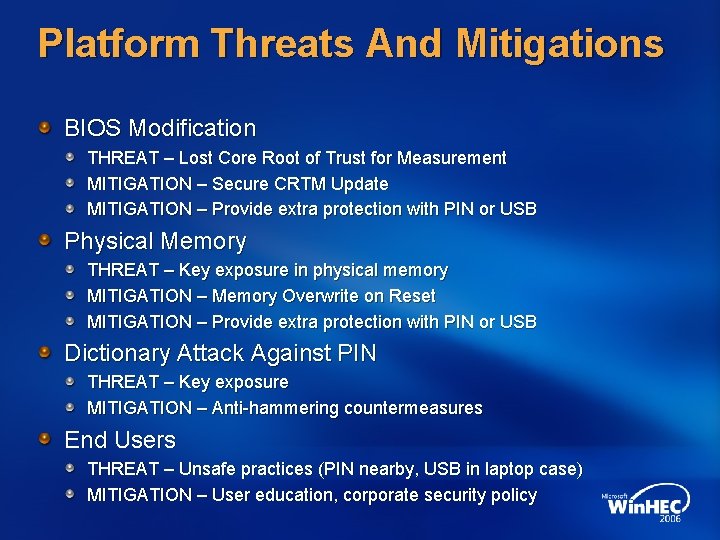
Platform Threats And Mitigations BIOS Modification THREAT – Lost Core Root of Trust for Measurement MITIGATION – Secure CRTM Update MITIGATION – Provide extra protection with PIN or USB Physical Memory THREAT – Key exposure in physical memory MITIGATION – Memory Overwrite on Reset MITIGATION – Provide extra protection with PIN or USB Dictionary Attack Against PIN THREAT – Key exposure MITIGATION – Anti-hammering countermeasures End Users THREAT – Unsafe practices (PIN nearby, USB in laptop case) MITIGATION – User education, corporate security policy
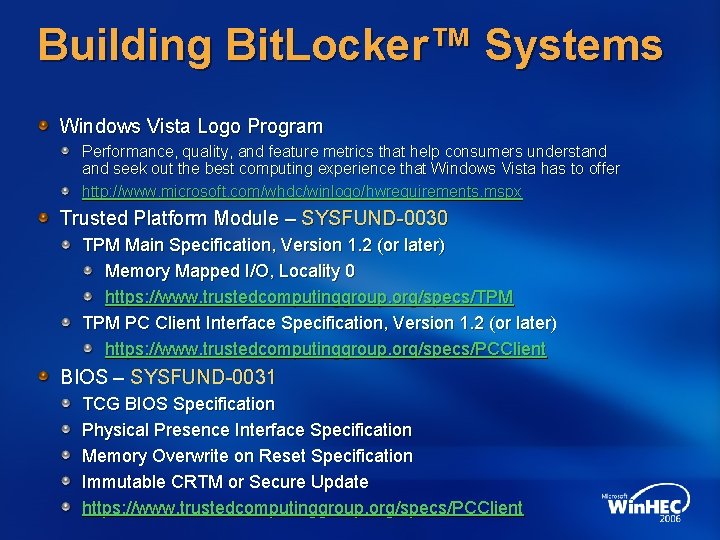
Building Bit. Locker™ Systems Windows Vista Logo Program Performance, quality, and feature metrics that help consumers understand seek out the best computing experience that Windows Vista has to offer http: //www. microsoft. com/whdc/winlogo/hwrequirements. mspx Trusted Platform Module – SYSFUND-0030 TPM Main Specification, Version 1. 2 (or later) Memory Mapped I/O, Locality 0 https: //www. trustedcomputinggroup. org/specs/TPM PC Client Interface Specification, Version 1. 2 (or later) https: //www. trustedcomputinggroup. org/specs/PCClient BIOS – SYSFUND-0031 TCG BIOS Specification Physical Presence Interface Specification Memory Overwrite on Reset Specification Immutable CRTM or Secure Update https: //www. trustedcomputinggroup. org/specs/PCClient
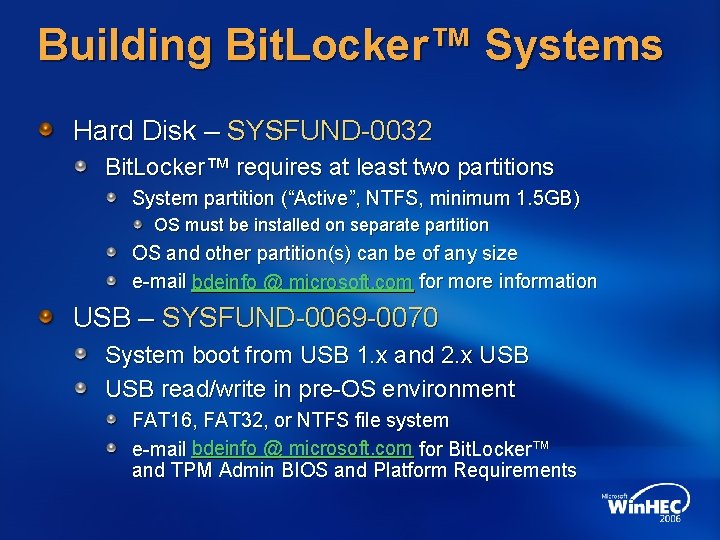
Building Bit. Locker™ Systems Hard Disk – SYSFUND-0032 Bit. Locker™ requires at least two partitions System partition (“Active”, NTFS, minimum 1. 5 GB) OS must be installed on separate partition OS and other partition(s) can be of any size e-mail bdeinfo @ microsoft. com for more information USB – SYSFUND-0069 -0070 System boot from USB 1. x and 2. x USB read/write in pre-OS environment FAT 16, FAT 32, or NTFS file system e-mail bdeinfo @ microsoft. com for Bit. Locker™ and TPM Admin BIOS and Platform Requirements
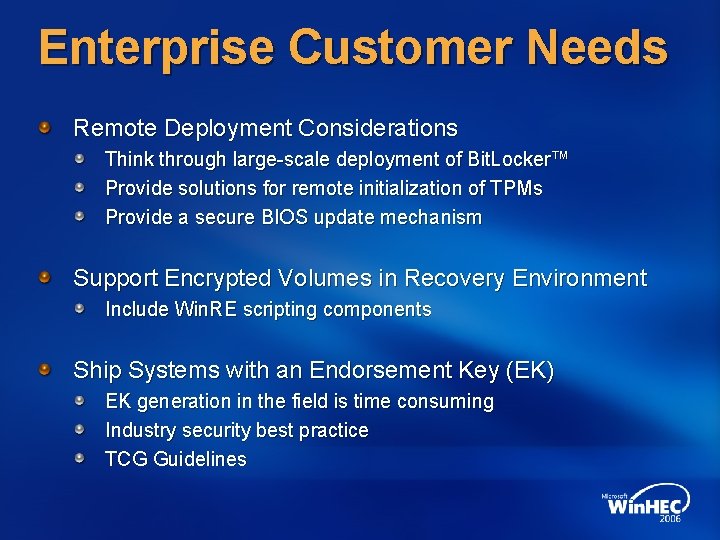
Enterprise Customer Needs Remote Deployment Considerations Think through large-scale deployment of Bit. Locker™ Provide solutions for remote initialization of TPMs Provide a secure BIOS update mechanism Support Encrypted Volumes in Recovery Environment Include Win. RE scripting components Ship Systems with an Endorsement Key (EK) EK generation in the field is time consuming Industry security best practice TCG Guidelines
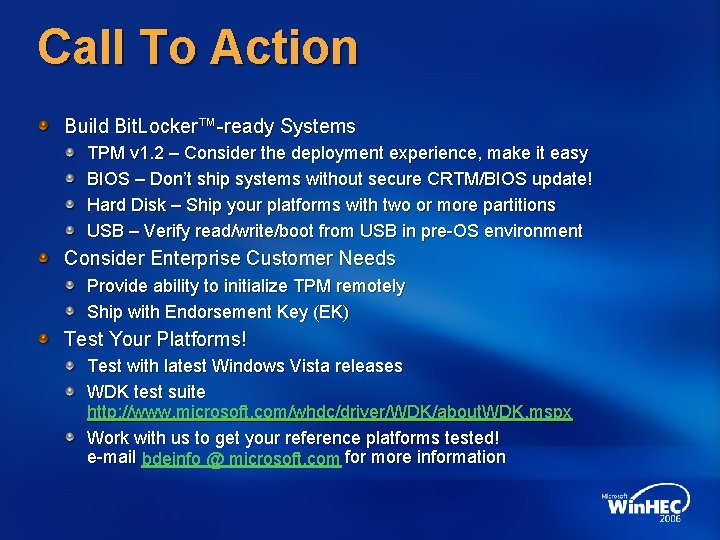
Call To Action Build Bit. Locker™-ready Systems TPM v 1. 2 – Consider the deployment experience, make it easy BIOS – Don’t ship systems without secure CRTM/BIOS update! Hard Disk – Ship your platforms with two or more partitions USB – Verify read/write/boot from USB in pre-OS environment Consider Enterprise Customer Needs Provide ability to initialize TPM remotely Ship with Endorsement Key (EK) Test Your Platforms! Test with latest Windows Vista releases WDK test suite http: //www. microsoft. com/whdc/driver/WDK/about. WDK. mspx Work with us to get your reference platforms tested! e-mail bdeinfo @ microsoft. com for more information
Additional Resources Web Resources Specs and Whitepapers http: //www. microsoft. com/whdc/system/platform/hwsecurity/default. mspx Windows Logo Program Testing http: //www. microsoft. com/whdc/Get. Start/testing. mspx TCG http: //www. trustedcomputinggroup. org Related Sessions Enterprise and Server Use of Microsoft Bit. Locker™ Drive Encryption (CPA 027) Windows Vista and Windows Server Longhorn Security Platform Enhancements (CPA 127) Bit. Locker™ Questions or Ideas Bdeinfo @ microsoft. com Bit. Locker™ Blog http: //blogs. msdn. com/si_team/default. aspx

Questions?
© 2006 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.
- Slides: 24