Bishop Chapter 14 Representing Identity csci 5233 Computer
Bishop: Chapter 14 Representing Identity csci 5233 Computer Security 1
Outline • Introduction • Naming & Certificates • Identity on the web • Anonymity csci 5233 Computer Security 2
What is identity? • An identity specifies a principal. – A principal is a unique entity. – What can be an entity? • Subjects: users, groups, roles e. g. , a user identification number (UID) identifies a user in a UNIX system • Objects: files, web pages, etc. + subjects e. g. , an URL identifies an object by specifying its location and the protocol used (such as http: //sce. cl. uh. edu/). csci 5233 Computer Security 3
Authentication vs identity • Authentication binds a principal to a representation of identity internal to the computer. • Two main purposes of using identities: – Accountability (logging, auditing) – Access control csci 5233 Computer Security 4
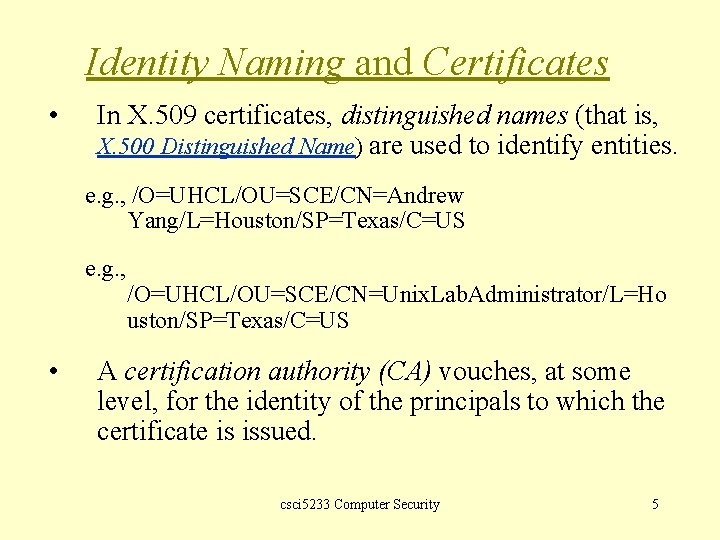
Identity Naming and Certificates • In X. 509 certificates, distinguished names (that is, X. 500 Distinguished Name) are used to identify entities. e. g. , /O=UHCL/OU=SCE/CN=Andrew Yang/L=Houston/SP=Texas/C=US e. g. , • /O=UHCL/OU=SCE/CN=Unix. Lab. Administrator/L=Ho uston/SP=Texas/C=US A certification authority (CA) vouches, at some level, for the identity of the principals to which the certificate is issued. csci 5233 Computer Security 5
![Structure of CAs • • [RFC 1422, S. Kent, 1993] Privacy Enhancement for internet Structure of CAs • • [RFC 1422, S. Kent, 1993] Privacy Enhancement for internet](http://slidetodoc.com/presentation_image_h2/8bf1271f08cce81b6b726b0335227189/image-6.jpg)
Structure of CAs • • [RFC 1422, S. Kent, 1993] Privacy Enhancement for internet Electronic Mail: Part II, Certificate. Based Key Management The certificate-based key management infrastructure organizes CAs into a hierarchical, tree-based structure. Each node in the tree corresponds to a CA. A Higher-level CA set policies that all subordinate CAs must follow; it certifies the subordinate CAs. csci 5233 Computer Security 6
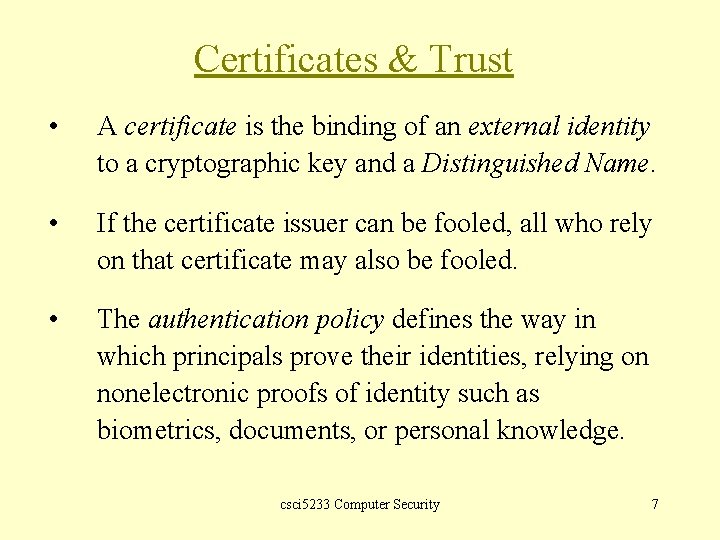
Certificates & Trust • A certificate is the binding of an external identity to a cryptographic key and a Distinguished Name. • If the certificate issuer can be fooled, all who rely on that certificate may also be fooled. • The authentication policy defines the way in which principals prove their identities, relying on nonelectronic proofs of identity such as biometrics, documents, or personal knowledge. csci 5233 Computer Security 7

Certificates & Trust • The goal of certificates is to bind a correct pair of identity and public key. • PGP certificates include a series of signature fields, each of which contains a level of trust. • The Open. PGP specification defines 4 levels of trusts: 1. Generic: no assertions 2. Persona (i. e. , anonymous): no verification of the binding between the user name and the principal 3. Casual: some verification 4. Positive: substantial verification csci 5233 Computer Security 8
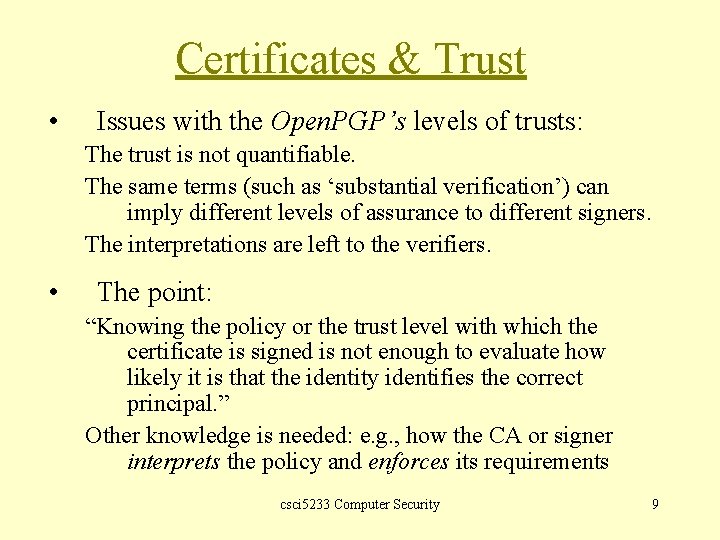
Certificates & Trust • Issues with the Open. PGP’s levels of trusts: The trust is not quantifiable. The same terms (such as ‘substantial verification’) can imply different levels of assurance to different signers. The interpretations are left to the verifiers. • The point: “Knowing the policy or the trust level with which the certificate is signed is not enough to evaluate how likely it is that the identity identifies the correct principal. ” Other knowledge is needed: e. g. , how the CA or signer interprets the policy and enforces its requirements csci 5233 Computer Security 9
Identity on the Internet • Host identity: How is a computer identified on the Internet? – – • ISO/OSI 7 -layer model The possibility of ‘spoofing’ a computer’s IP or MAC address Static vs Dynamic Identifiers – The NAT (Network Address Translation) protocol csci 5233 Computer Security 10
Domain Name Services • DNS provides an association between a host name and an IP address. • If the association is corrupted, the identifier in question will be associated with the wrong host (sometimes the malicious one). • Attacks on the DNS: Bellovin, Schuba csci 5233 Computer Security 11
State and Cookies • The HTTP protocol is a stateless protocol: basically request/response • Other mechanisms (such as cookies or sessions) are needed to maintain states between a client and a server. • Def. 14 -4: A cookie is a token that contains information about the state of a transaction on a network. • pp. 369 -370: Values in the cookies • Cookies may contain sensitive information. Protecting the confidentiality of the cookies may be critical. csci 5233 Computer Security 12
Anonymity on the Web • Anonymity: The ability to hide the identity of a host • When would anonymity be needed? • Examples: anonymous remailers, mixers Ø More details in the ‘network security’ course csci 5233 Computer Security 13
- Slides: 13