Biometrics Proof of Identity consistently accurate continuously reliable
Biometrics = Proof of Identity? consistently accurate, continuously reliable, completely compatible. This information is strictly for use by Ideco and its Associates. Reproduction and distribution is strictly prohibited. Copyright Ideco Group Ltd.
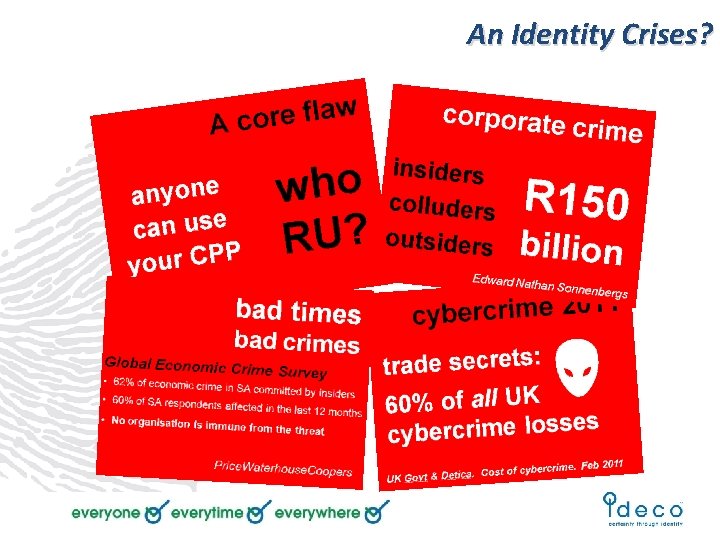
An Identity Crises?
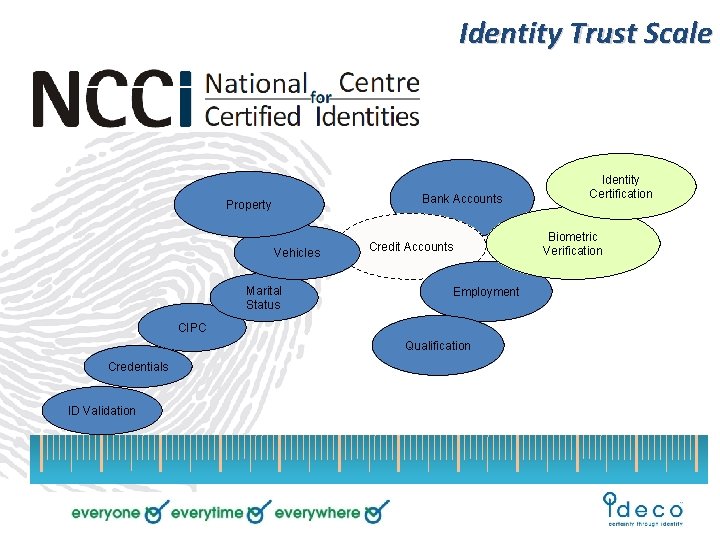
Identity Trust Scale Bank Accounts Property Vehicles Marital Status Credit Accounts Employment CIPC Qualification Credentials ID Validation Identity Certification Biometric Verification
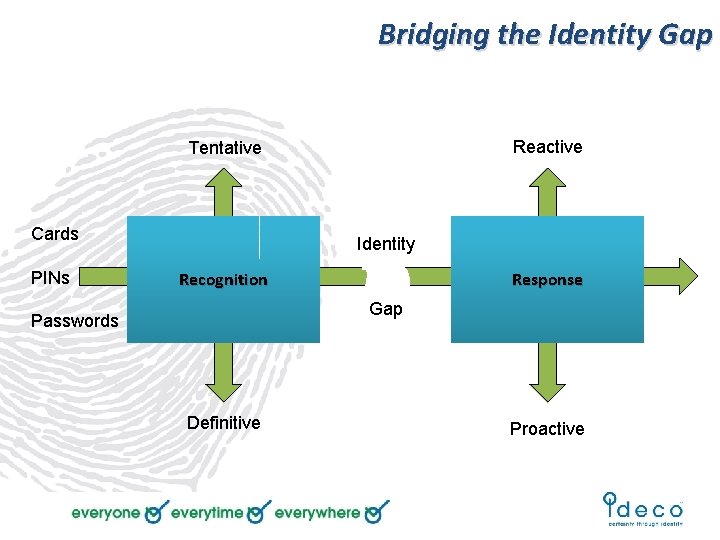
Bridging the Identity Gap Reactive Tentative Cards PINs Identity Recognition Response Gap Passwords Definitive Proactive
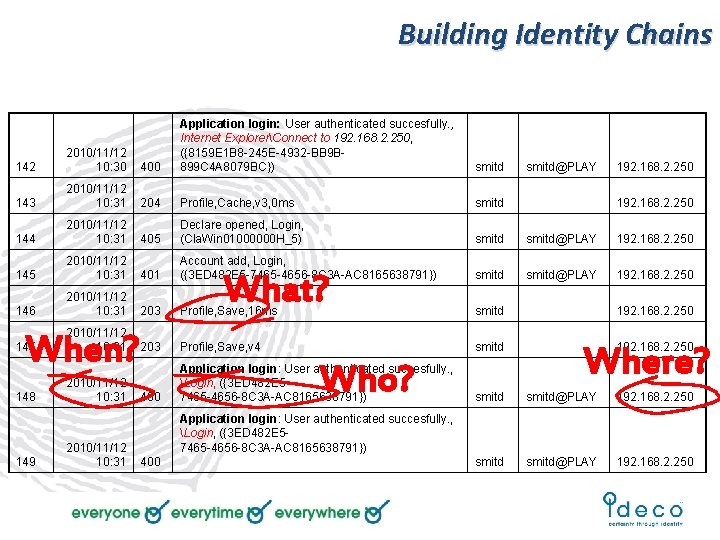
Building Identity Chains 142 2010/11/12 10: 30 400 Application login: User authenticated succesfully. , Internet ExplorerConnect to 192. 168. 2. 250, ({8159 E 1 B 8 -245 E-4932 -BB 9 B 899 C 4 A 8079 BC}) 143 2010/11/12 10: 31 204 Profile, Cache, v 3, 0 ms smitd 192. 168. 2. 250 144 2010/11/12 10: 31 405 Declare opened, Login, (Cla. Win 01000000 H_5) smitd@PLAY 192. 168. 2. 250 145 2010/11/12 10: 31 401 Account add, Login, ({3 ED 482 E 5 -7465 -4656 -8 C 3 A-AC 8165638791}) smitd@PLAY 192. 168. 2. 250 146 2010/11/12 10: 31 203 Profile, Save, 16 ms smitd 192. 168. 2. 250 147 2010/11/12 10: 31 203 Profile, Save, v 4 smitd 192. 168. 2. 250 148 2010/11/12 10: 31 400 Application login: User authenticated succesfully. , Login, ({3 ED 482 E 57465 -4656 -8 C 3 A-AC 8165638791}) smitd@PLAY 192. 168. 2. 250 When? 149 2010/11/12 10: 31 400 What? Who? smitd@PLAY 192. 168. 2. 250 Where? Application login: User authenticated succesfully. , Login, ({3 ED 482 E 57465 -4656 -8 C 3 A-AC 8165638791})
Agenda Biometric 101 Next generation applications DHA & National Identity Solutions Key success factors An integrated approach Chain of evidence
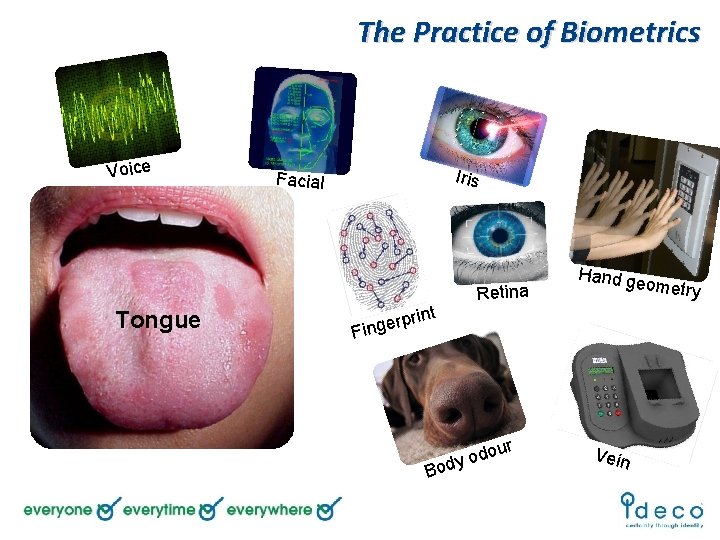
The Practice of Biometrics Voice Tongue Iris Facial t Retina Hand ge ometry rprin e g n i F B ur o d o ody Vein
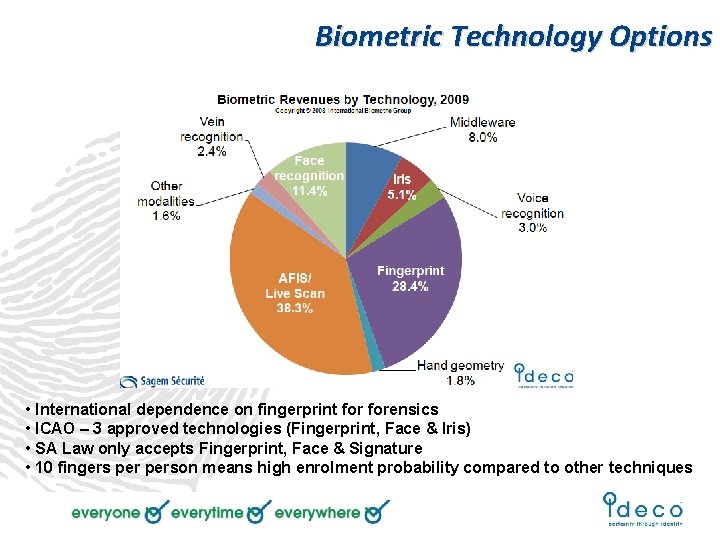
Biometric Technology Options • International dependence on fingerprint forensics • ICAO – 3 approved technologies (Fingerprint, Face & Iris) • SA Law only accepts Fingerprint, Face & Signature • 10 fingers person means high enrolment probability compared to other techniques
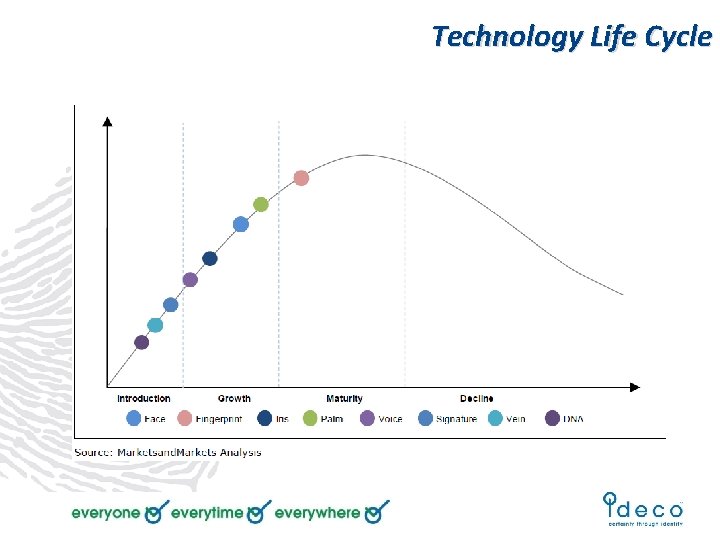
Technology Life Cycle
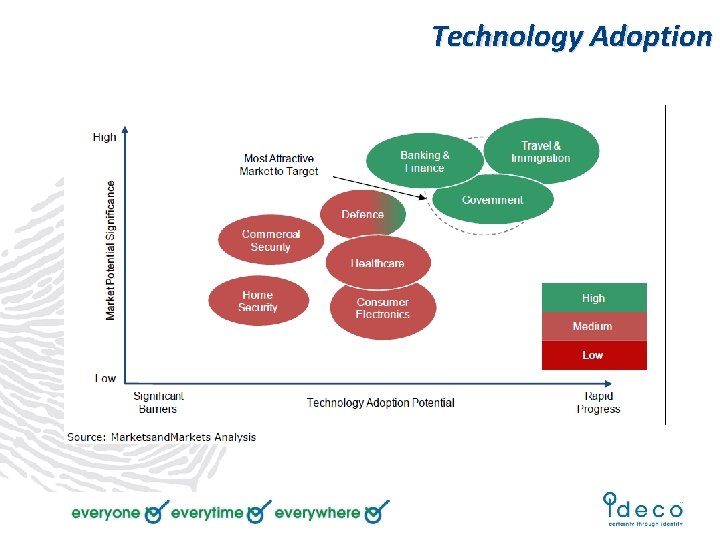
Technology Adoption
The practice of Biometrics
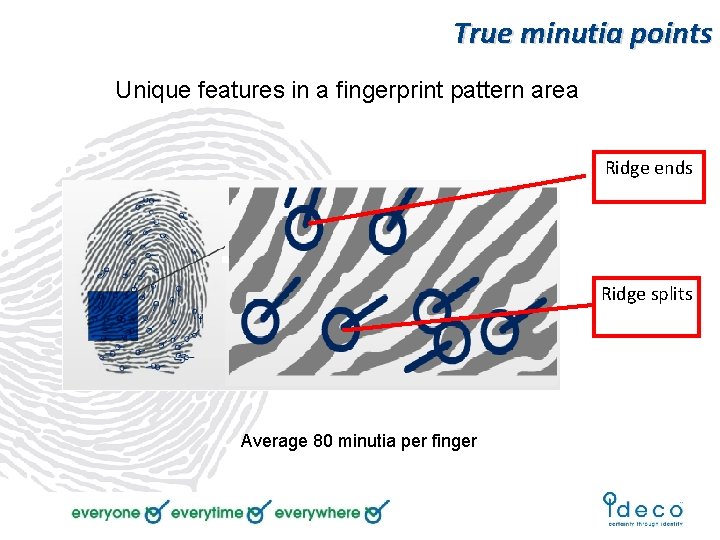
True minutia points Unique features in a fingerprint pattern area Ridge ends Ridge splits Average 80 minutia per finger
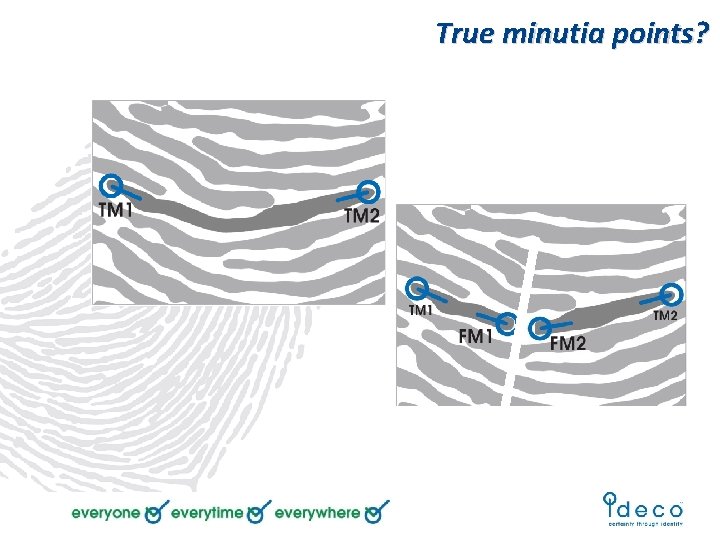
True minutia points?
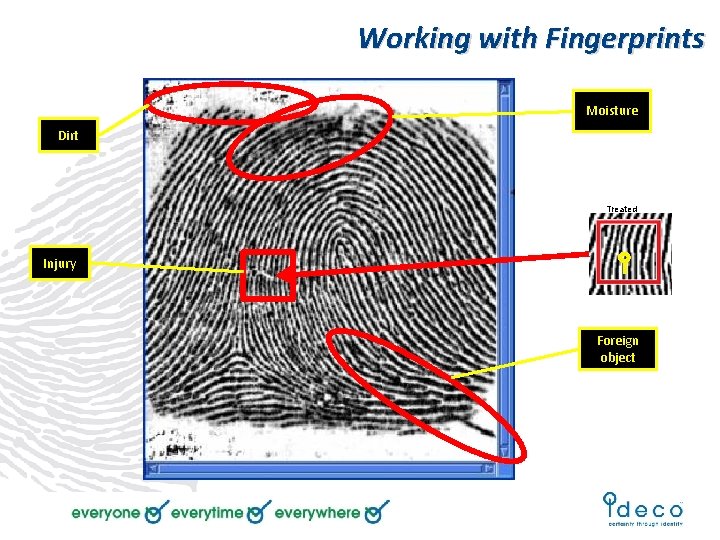
Working with Fingerprints Moisture Dirt Treated Injury Foreign object
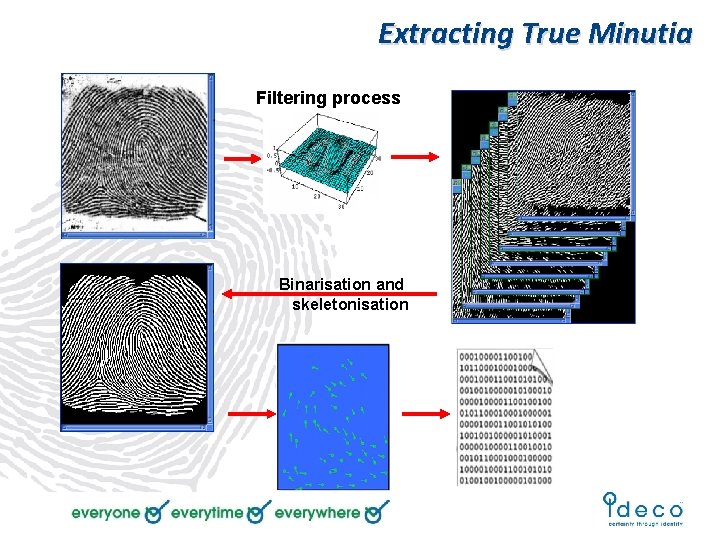
Extracting True Minutia Filtering process Binarisation and skeletonisation
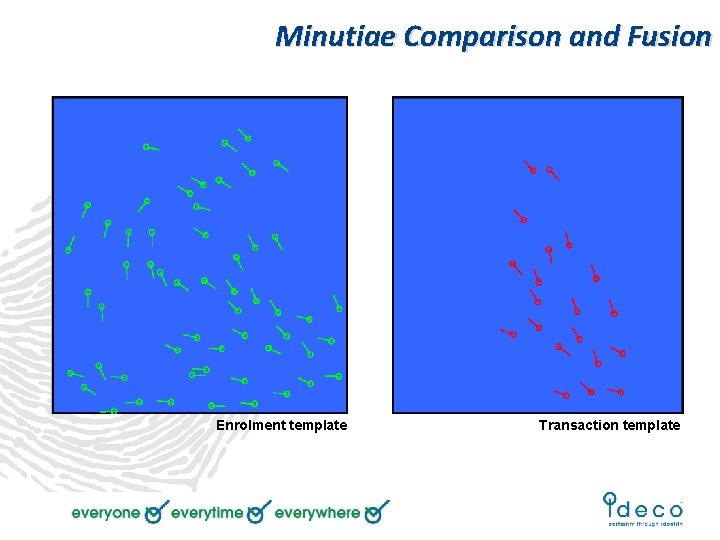
Minutiae Comparison and Fusion Enrolment template Transaction template
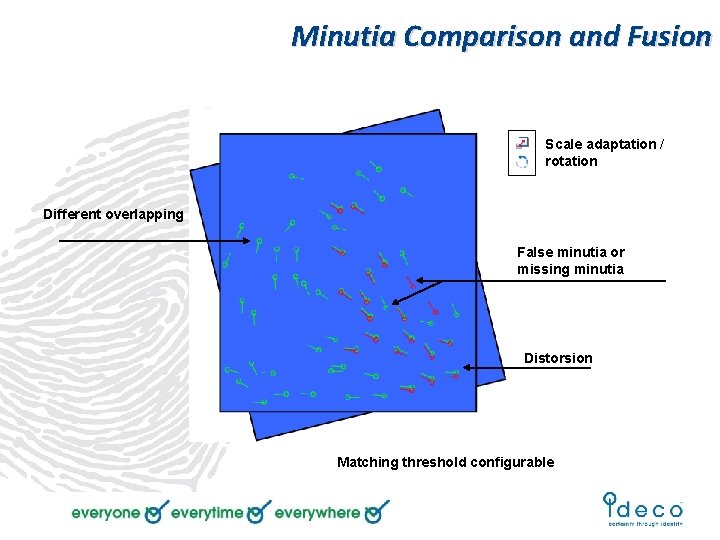
Minutia Comparison and Fusion Scale adaptation / rotation Different overlapping False minutia or missing minutia Distorsion Matching threshold configurable
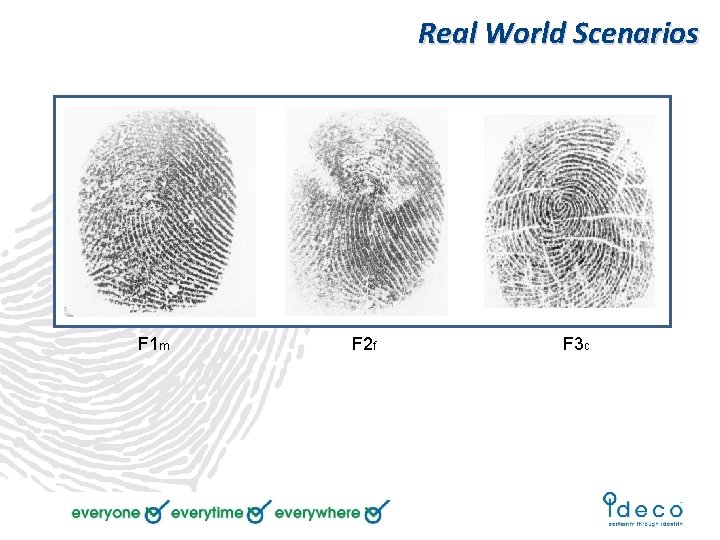
Real World Scenarios F 1 m F 2 f F 3 c
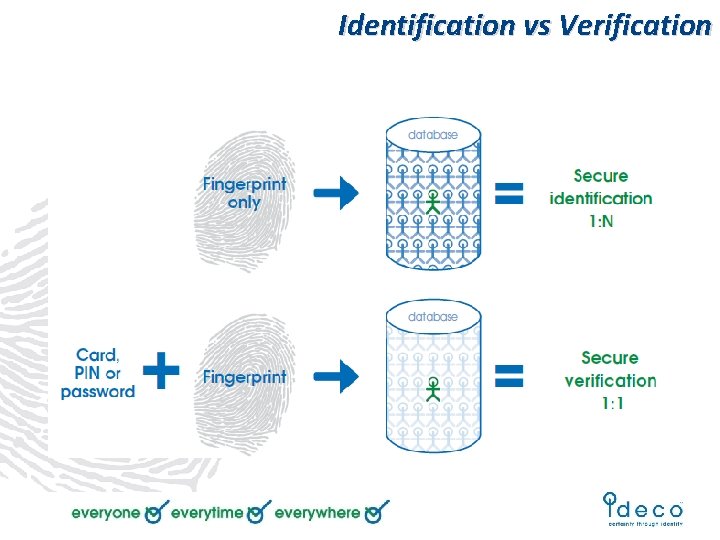
Identification vs Verification
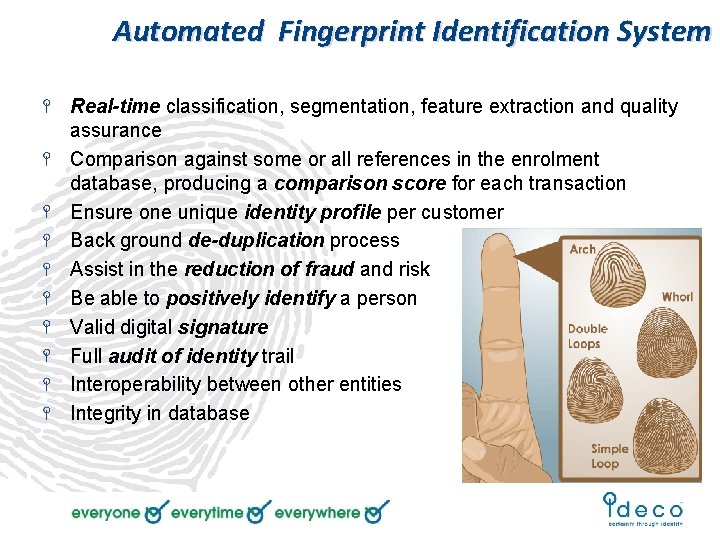
Automated Fingerprint Identification System Real-time classification, segmentation, feature extraction and quality assurance Comparison against some or all references in the enrolment database, producing a comparison score for each transaction Ensure one unique identity profile per customer Back ground de-duplication process Assist in the reduction of fraud and risk Be able to positively identify a person Valid digital signature Full audit of identity trail Interoperability between other entities Integrity in database
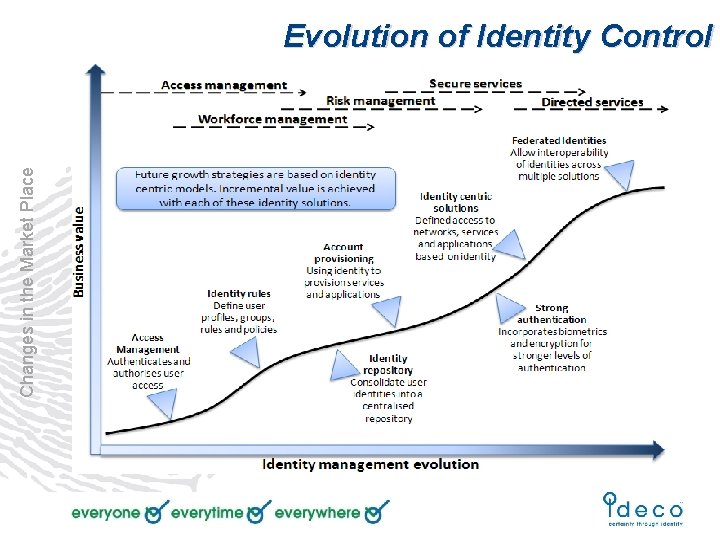
Changes in the Market Place Evolution of Identity Control

Changes in the Market Place DHA Smart. ID & OFV

Online Fingerprint Verification Live Demo
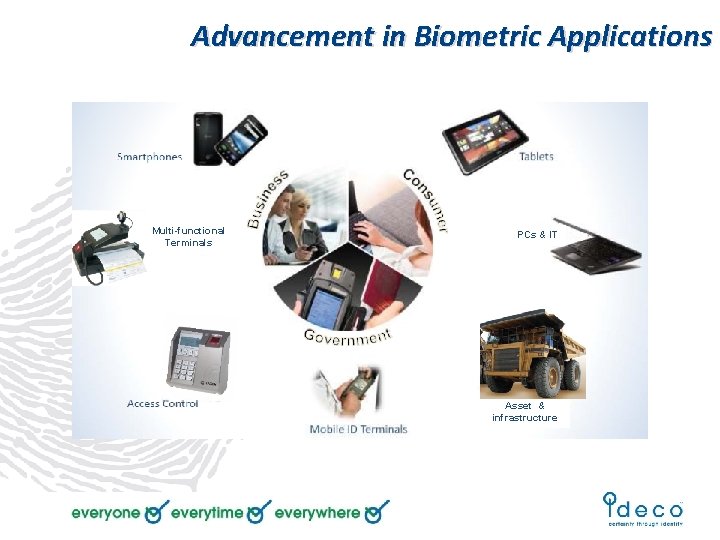
Advancement in Biometric Applications Multi-functional Terminals PCs & IT Asset & infrastructure

Advancement in Biometric Equipment
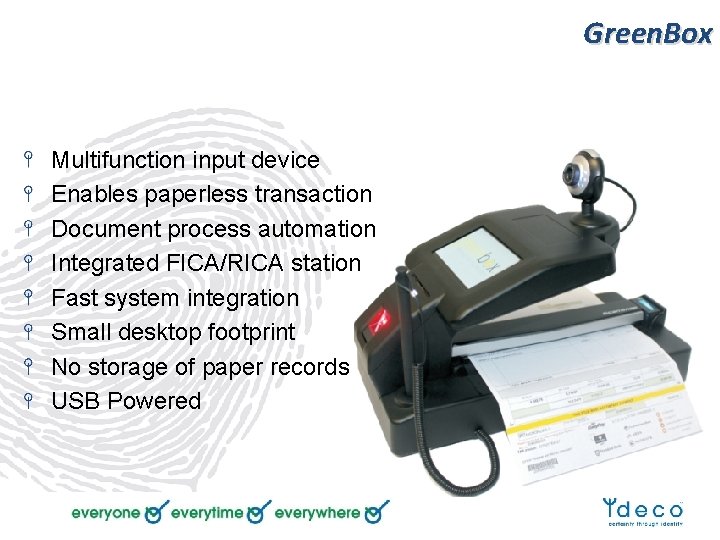
Green. Box Multifunction input device Enables paperless transaction Document process automation Integrated FICA/RICA station Fast system integration Small desktop footprint No storage of paper records USB Powered

Mobi. Check Fully configurable Multiple input fields / devices Online ID checks against NCCI Verification or identification Records on secure cloud servers Business rule driven Identity based transactions Secure online access to records
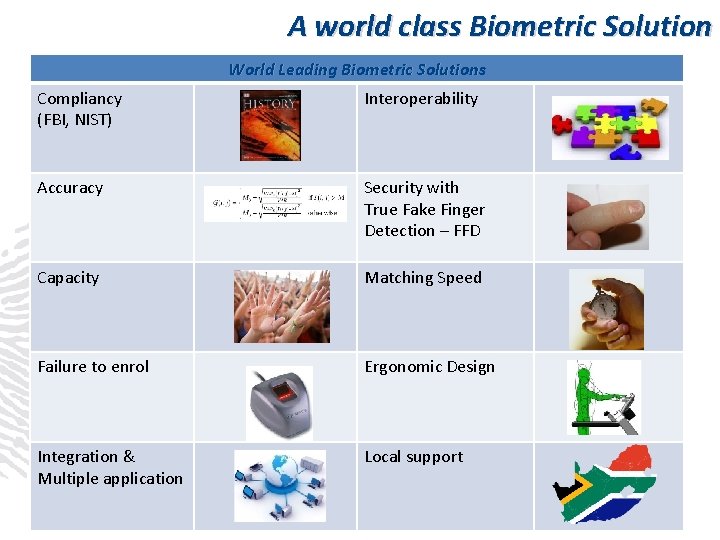
A world class Biometric Solution World Leading Biometric Solutions Compliancy (FBI, NIST) Interoperability Accuracy Security with True Fake Finger Detection – FFD Capacity Matching Speed Failure to enrol Ergonomic Design Integration & Multiple application Local support
An Integrated Approach Direct integration to business systems Aligned with current business processes AFIS functionality scalable to business requirements All development tools and integration support Windows, Linux and Android support Fully compliant to industry standards Best in class at affordable pricing Full maintenance and support program
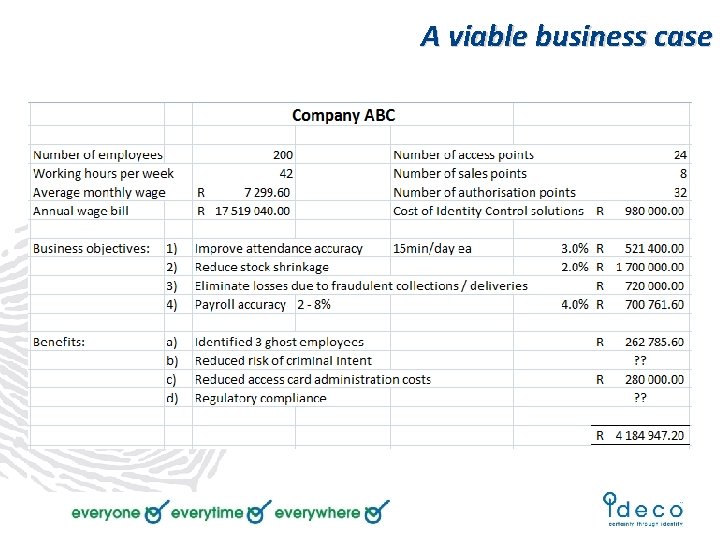
A viable business case

Critical Success Factors FTE, FAR, Speed, db Size Image and / or Template Protecting customer identities Comply to International standards Compatible to civil systems Expert use in court of law Clear growth path
Some risks to consider
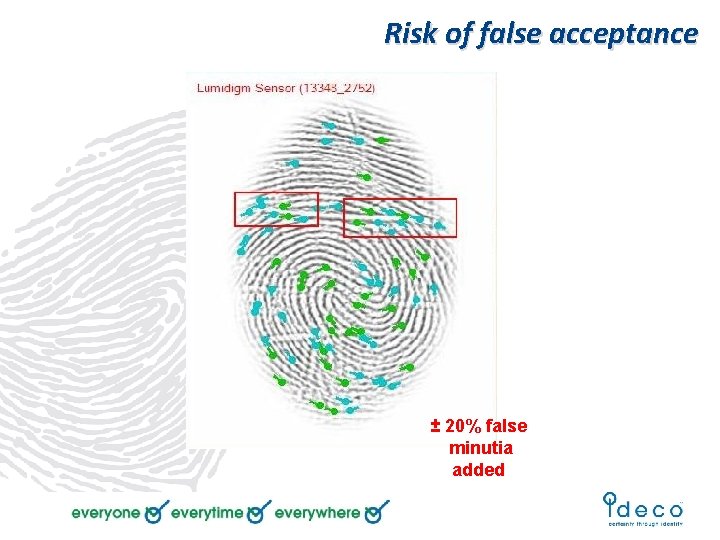
Risk of false acceptance ± 20% false minutia added
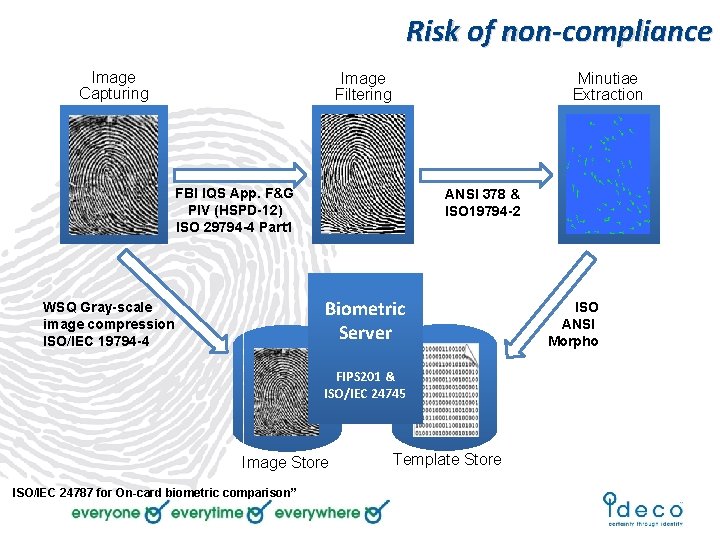
Risk of non-compliance Image Capturing Image Filtering Minutiae Extraction FBI IQS App. F&G PIV (HSPD-12) ISO 29794 -4 Part 1 ANSI 378 & ISO 19794 -2 Biometric Server WSQ Gray-scale image compression ISO/IEC 19794 -4 FIPS 201 & ISO/IEC 24745 Image Store ISO/IEC 24787 for On-card biometric comparison” Template Store ISO ANSI Morpho
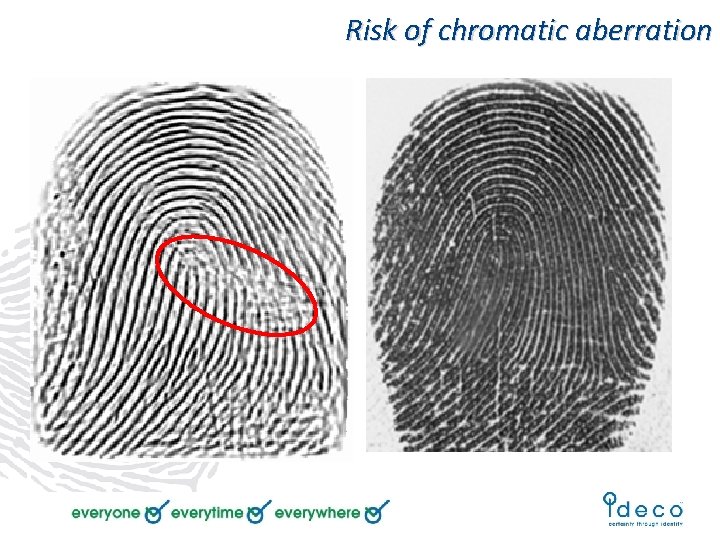
Risk of chromatic aberration
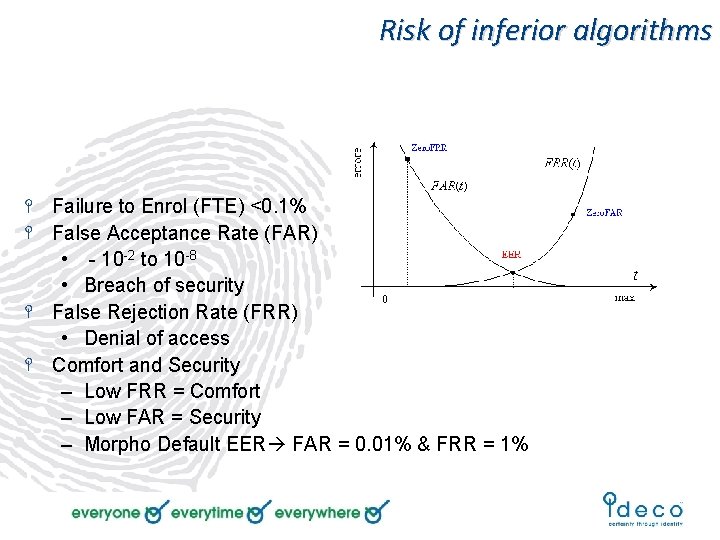
Risk of inferior algorithms Failure to Enrol (FTE) <0. 1% False Acceptance Rate (FAR) • - 10 -2 to 10 -8 • Breach of security False Rejection Rate (FRR) • Denial of access Comfort and Security – Low FRR = Comfort – Low FAR = Security – Morpho Default EER FAR = 0. 01% & FRR = 1%

Risk of inferior optics
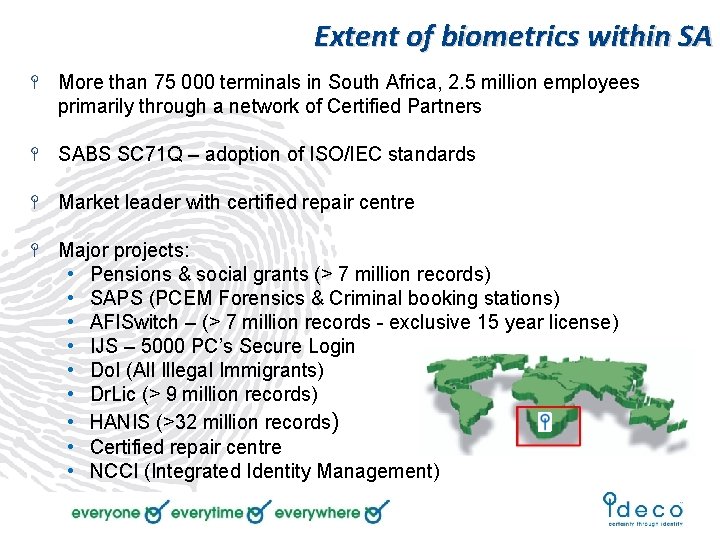
Extent of biometrics within SA More than 75 000 terminals in South Africa, 2. 5 million employees primarily through a network of Certified Partners SABS SC 71 Q – adoption of ISO/IEC standards Market leader with certified repair centre Major projects: • Pensions & social grants (> 7 million records) • SAPS (PCEM Forensics & Criminal booking stations) • AFISwitch – (> 7 million records - exclusive 15 year license) • IJS – 5000 PC’s Secure Login • Do. I (All Illegal Immigrants) • Dr. Lic (> 9 million records) • HANIS (>32 million records) • Certified repair centre • NCCI (Integrated Identity Management)

@ your service Thank you
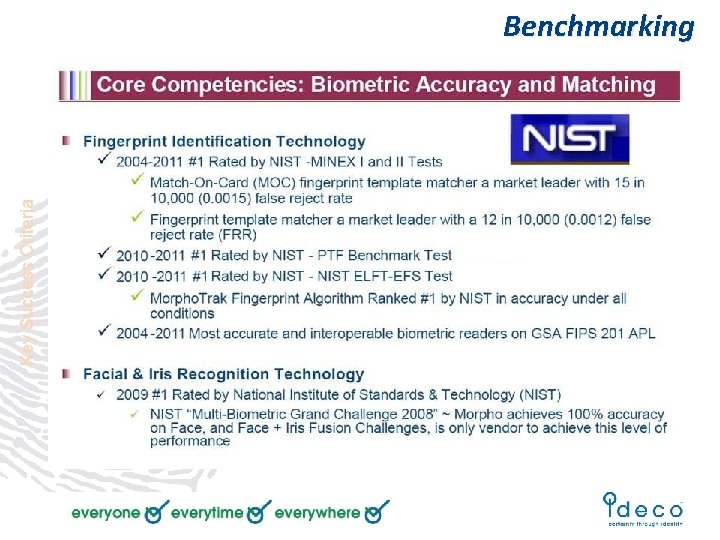
Key Success Criteria Benchmarking
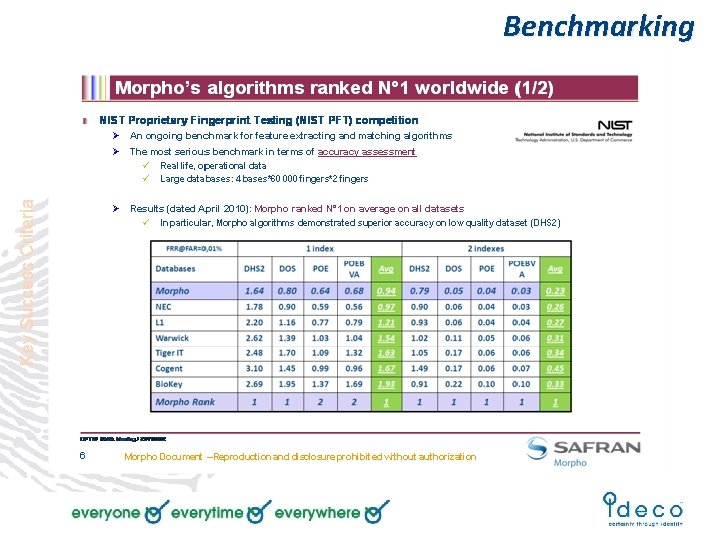
Key Success Criteria Benchmarking
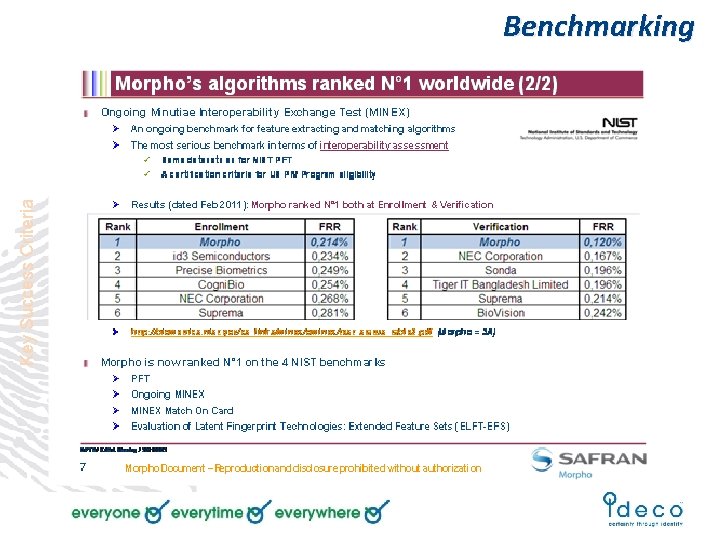
Key Success Criteria Benchmarking
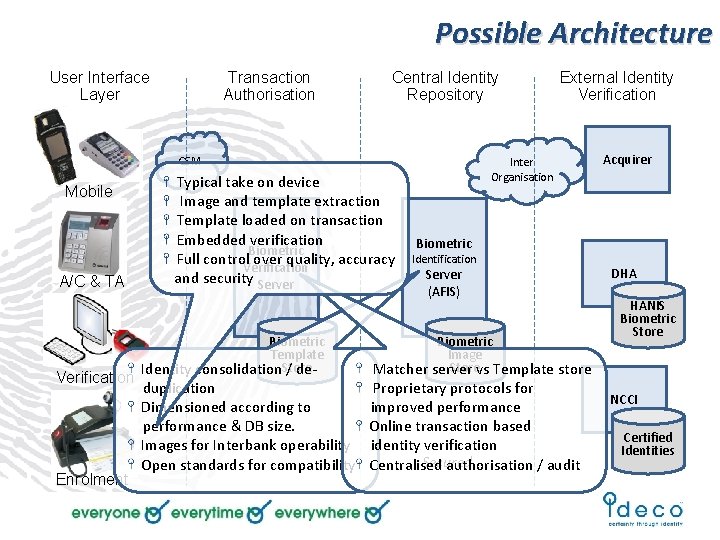
Possible Architecture User Interface Layer Transaction Authorisation Central Identity Repository GSM Mobile A/C & TA Verification Enrolment Typical take on device Image and template extraction Template loaded on transaction Embedded verification Biometric Full control. Verification over quality, accuracy and security Server Biometric Template Identity consolidation. Store / de- duplication Dimensioned according to performance & DB size. Images for Interbank operability Open standards for compatibility External Identity Verification Inter Organisation Acquirer Biometric Identification Server (AFIS) Biometric Image Storevs Template store Matcher server Proprietary protocols for improved performance Online transaction based identity verification Secured Centralised authorisation / audit DHA HANIS Biometric Store NCCI Certified Identities
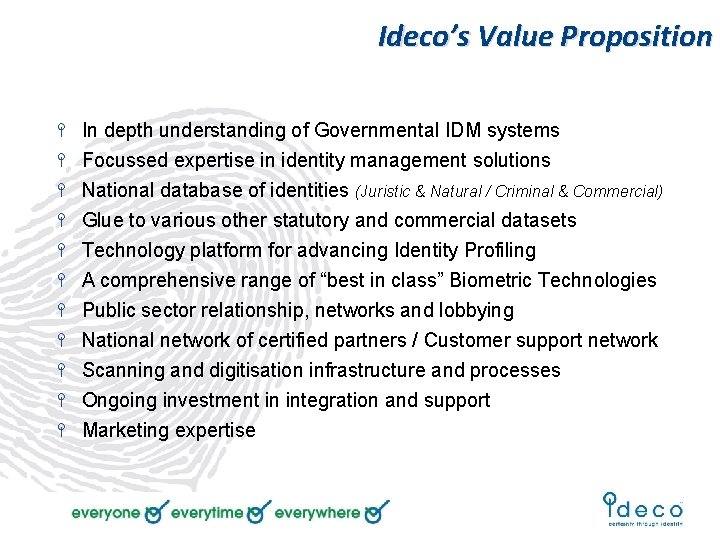
Ideco’s Value Proposition In depth understanding of Governmental IDM systems Focussed expertise in identity management solutions National database of identities (Juristic & Natural / Criminal & Commercial) Glue to various other statutory and commercial datasets Technology platform for advancing Identity Profiling A comprehensive range of “best in class” Biometric Technologies Public sector relationship, networks and lobbying National network of certified partners / Customer support network Scanning and digitisation infrastructure and processes Ongoing investment in integration and support Marketing expertise
- Slides: 44