Biometrics A tool for Information Security Authors Anil
Biometrics A tool for Information Security Authors: Anil K. Jain , Arun Ross and Sharath Pankanti Presented By: Payas Gupta
Outline Today’s security related concerns Commonly used Biometrics Variance in Biometrics Operation of Biometrics Systems Attacks on Biometric System Multi Biometric Systems Level of fusion in Biometric Systems
Today’s Security related Questions Is she really who she claims to be? Is this person authorized to use this facility? Is he in the watch list posted by the government? Biometrics, Science of recognizing an individual based on his or her physical or behavioral traits
Paper is all about Examining applications where biometrics can solve issues pertaining to information security Enumerating the fundamental challenges encountered by biometric systems in real-world applications Discussing solutions to address the problems of scalability and security in large-scale authentication systems
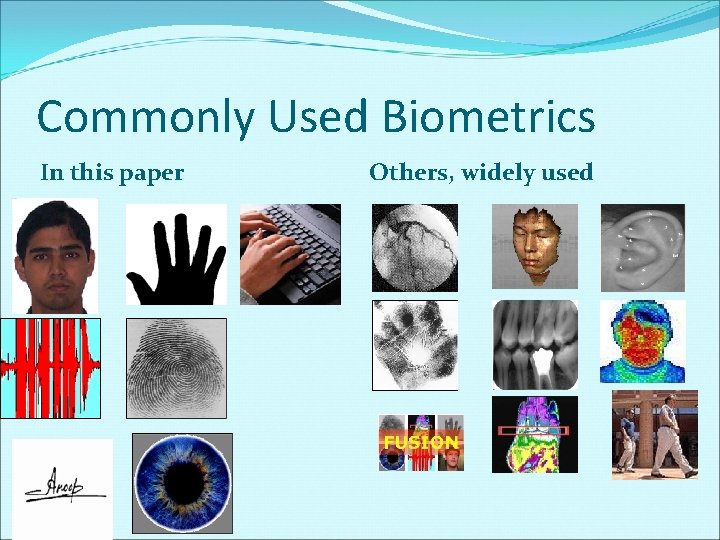
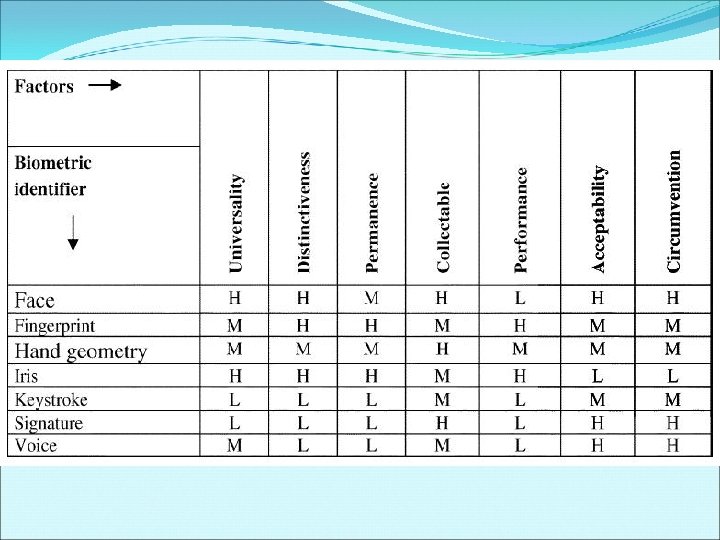
Commonly Used Biometrics In this paper Others, widely used
Research Going on… Heart Beat Galvanic Skin Conductivity Pulse Rate Brain tissues Respiration DNA
Face Location and shape of facial attributes Eyes, eyebrows, nose, lips and chin Global Analysis of face as weighted combination of no. of canonical faces. Disadvantages: Face could be an image (photograph) Difficult to locate the face if there is one Difficult to match from any pose Template Update Problem
Fingerprint Pattern of ridges and valleys on fingertip Fingerprint scanner, cheap approx. $30 Fingerprint of Identical twins are different Disadvantage: Large computation resource when in identification mode
Hand Geometry Human Hand Shape and size of palm Length and widths of fingers Relatively easy to use Inexpensive Environmental conditions do not affect Disadvantage Not very distinctive Individual jewelry Limitation in dexterity (e. g. Arthritis)
Iris, is bounded by pupil and the white portion of eye High accuracy and speed Each Iris is believed to be distinctive Ability to detect artificial Irises (contact lenses). Low FAR but could be high FRR Disadvantages: Considerable user participation expensive
Keystroke Hypothesis Behavioral biometric each person types on keyboard in a characteristic way. Not unique, but sufficiently different that permits identity verification Disadvantage: typing patterns change substantially between consecutive instances of typing the password different style of keyboard
Signature The way a person sign Excepted all throughout the world Behavioral Biometric Possibility of changing in emotional and physical conditions. Disadvantage: Professional forgers may be able to reproduce signatures that fool the system.
Voice Physical + Behavioral Biometric Depends on: Shape and size of vocal tracts, mouth, nasal cavities and lips Disadvantages: Physical part are invariant from each other But, behavioral part changes from age, emotional state and medical conditions (cold). Background noise
Variance in Biometrics Major Problem

Inconsistent Presentation
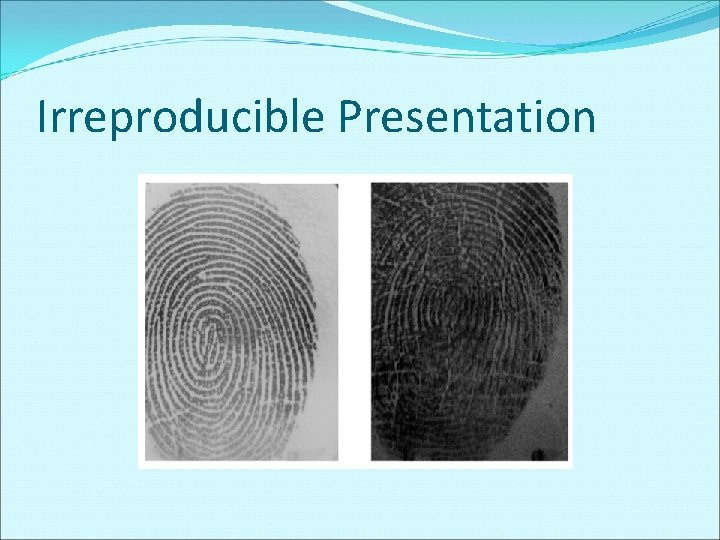
Irreproducible Presentation
Imperfect Representation Acquisition
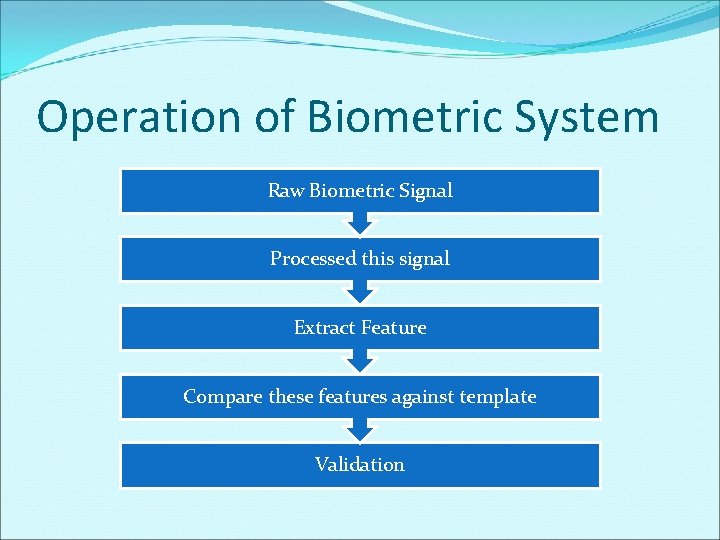
Operation of Biometric System Raw Biometric Signal Processed this signal Extract Feature Compare these features against template Validation
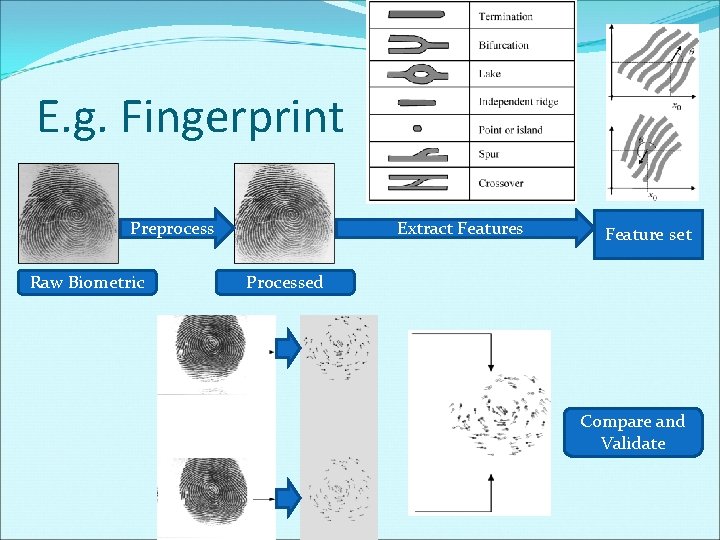
E. g. Fingerprint Preprocess Raw Biometric Extract Features Feature set Processed Compare and Validate
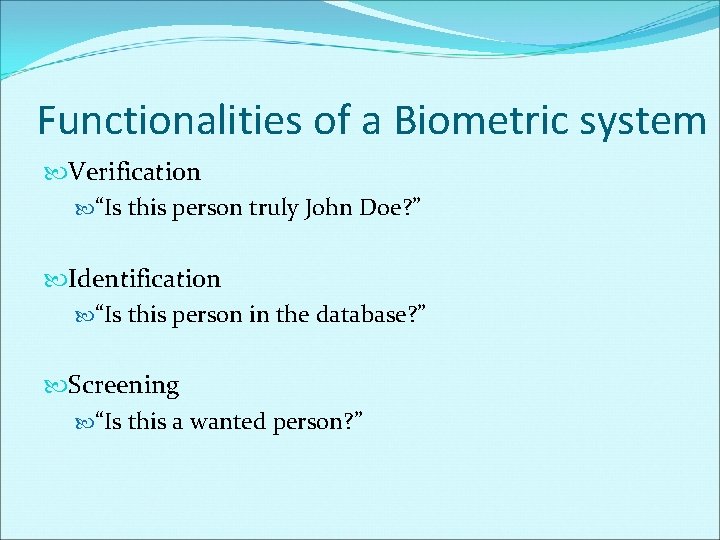
Functionalities of a Biometric system Verification “Is this person truly John Doe? ” Identification “Is this person in the database? ” Screening “Is this a wanted person? ”
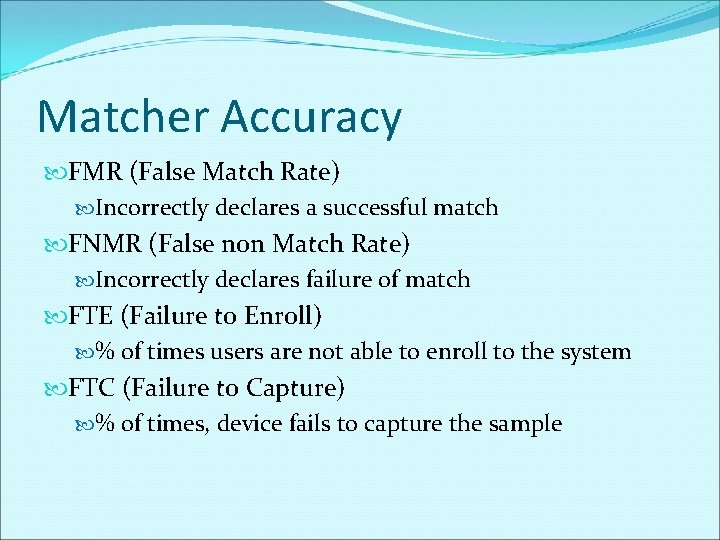
Matcher Accuracy FMR (False Match Rate) Incorrectly declares a successful match FNMR (False non Match Rate) Incorrectly declares failure of match FTE (Failure to Enroll) % of times users are not able to enroll to the system FTC (Failure to Capture) % of times, device fails to capture the sample
Attacks on a Biometric system
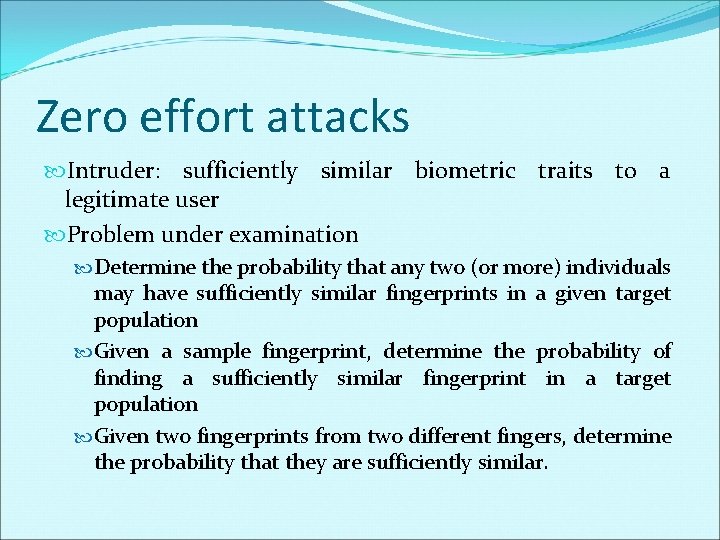
Zero effort attacks Intruder: sufficiently similar biometric traits to a legitimate user Problem under examination Determine the probability that any two (or more) individuals may have sufficiently similar fingerprints in a given target population Given a sample fingerprint, determine the probability of finding a sufficiently similar fingerprint in a target population Given two fingerprints from two different fingers, determine the probability that they are sufficiently similar.
Adversary Attacks Physical traits can be obtained from face, fingerprints.
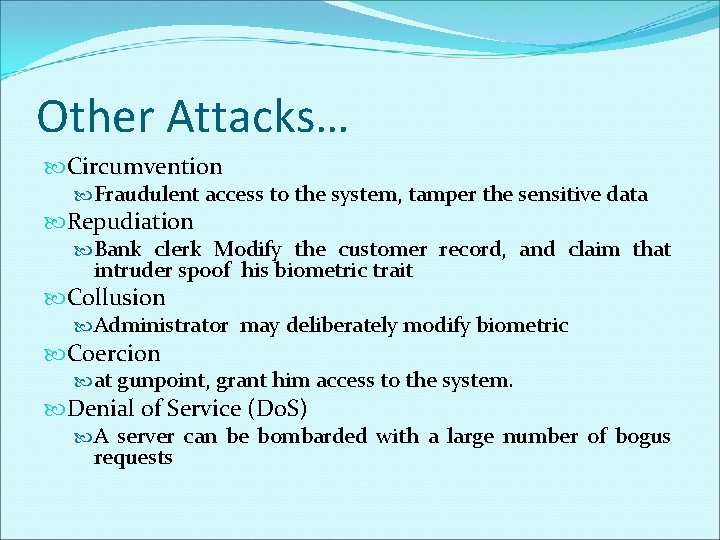
Other Attacks… Circumvention Fraudulent access to the system, tamper the sensitive data Repudiation Bank clerk Modify the customer record, and claim that intruder spoof his biometric trait Collusion Administrator may deliberately modify biometric Coercion at gunpoint, grant him access to the system. Denial of Service (Do. S) A server can be bombarded with a large number of bogus requests
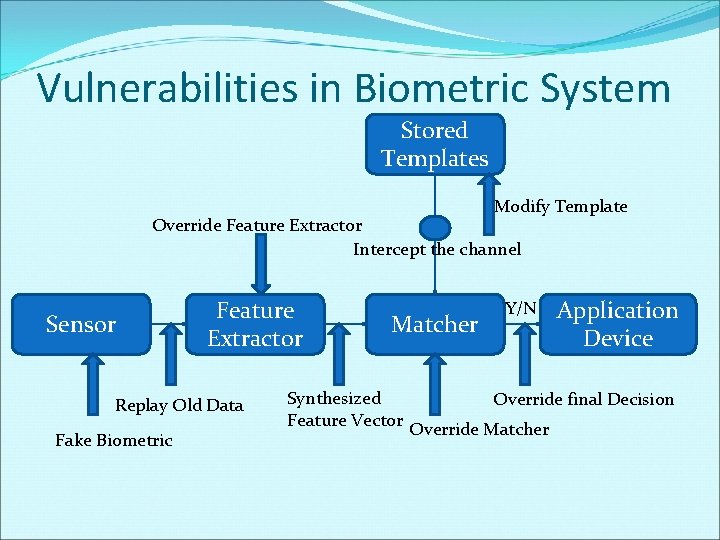
Vulnerabilities in Biometric System Stored Templates Modify Template Override Feature Extractor Intercept the channel Sensor Feature Extractor Replay Old Data Fake Biometric Matcher Synthesized Feature Vector Y/N Application Device Override final Decision Override Matcher
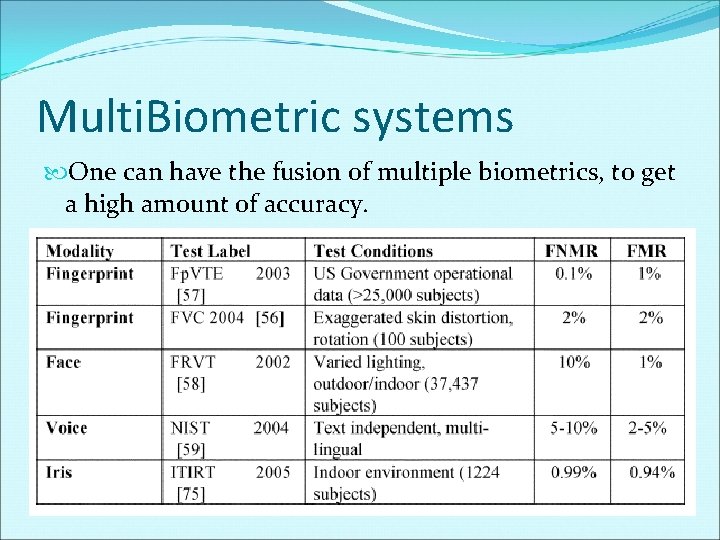
Multi. Biometric systems One can have the fusion of multiple biometrics, to get a high amount of accuracy.
Levels of fusion in multibiom. Feature Level Score Level Decision Level
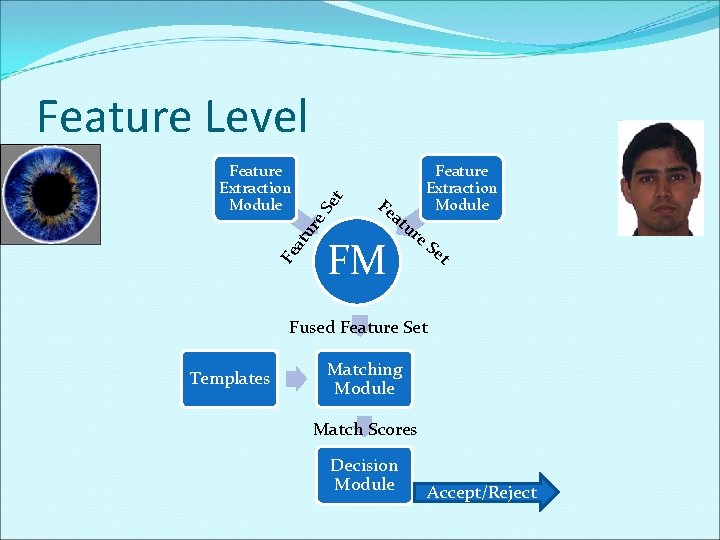
Fe at ur e. S Feature Extraction Module et Feature Level Fe at FM Feature Extraction Module ur e. S et Fused Feature Set Templates Matching Module Match Scores Decision Module Accept/Reject
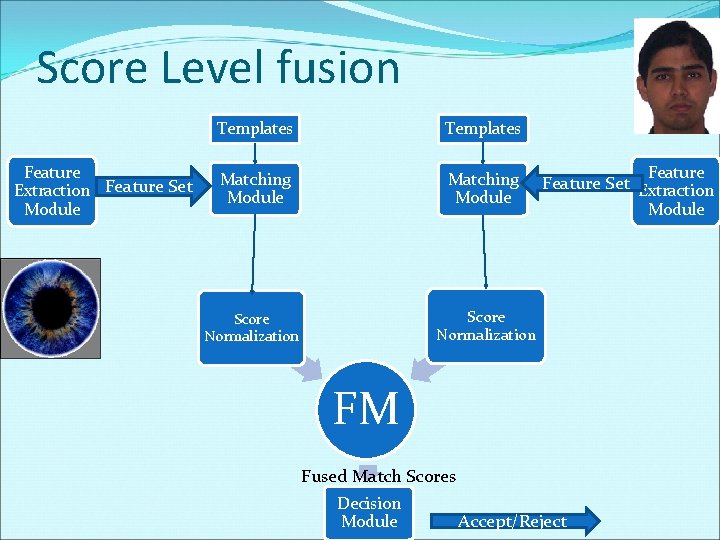
Score Level fusion Feature Extraction Feature Set Module Templates Matching Module Score Normalization FM Fused Match Scores Decision Module Feature Set Extraction Accept/Reject Module
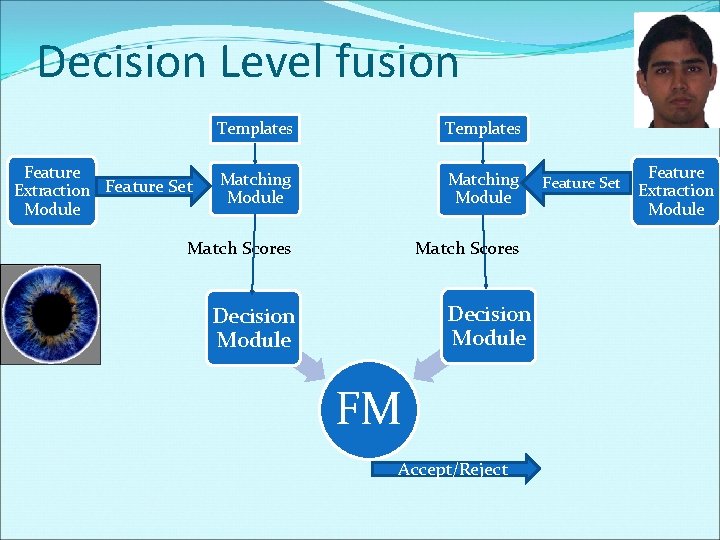
Decision Level fusion Templates Matching Module Match Scores Feature Extraction Feature Set Module Decision Module FM Accept/Reject Feature Set Feature Extraction Module
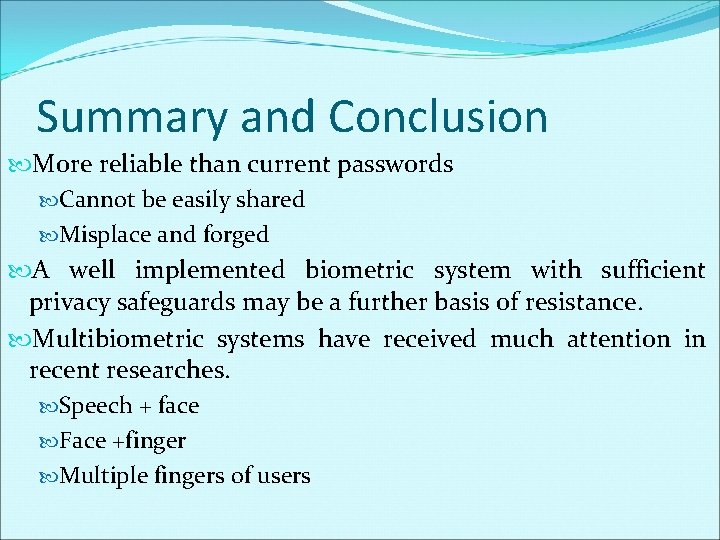
Summary and Conclusion More reliable than current passwords Cannot be easily shared Misplace and forged A well implemented biometric system with sufficient privacy safeguards may be a further basis of resistance. Multibiometric systems have received much attention in recent researches. Speech + face Face +finger Multiple fingers of users
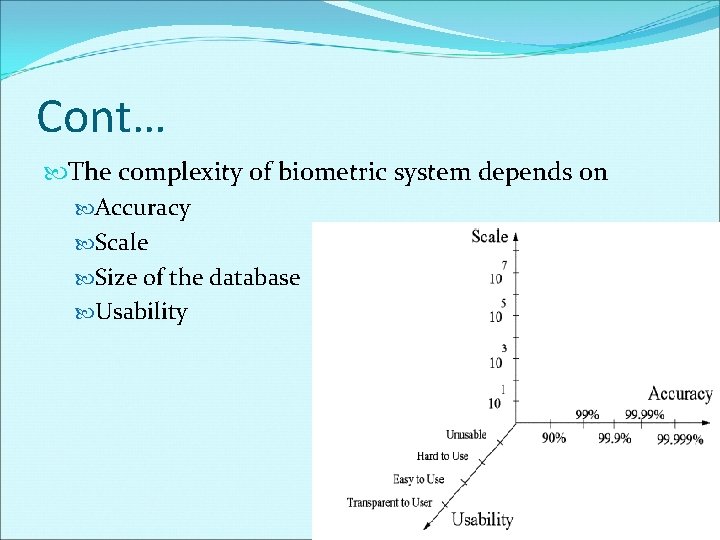
Cont… The complexity of biometric system depends on Accuracy Scale Size of the database Usability
Thank you Questions / Comments?
- Slides: 35