BGP Multiple Origin AS MOAS Conflict Analysis Xiaoliang
BGP Multiple Origin AS (MOAS) Conflict Analysis Xiaoliang Zhao, NCSU S. Felix Wu, UC Davis Allison Mankin, Dan Massey, USC/ISI Dan Pei, Lan Wang, Lixia Zhang, UCLA 10/23/2001 NANOG-23, October 23, 2001 NANOG 23 - Oakland
Definition of MOAS n BGP routes include a prefix and AS path – Example: 131. 179. 0. 0/16, Path: 4513, 11422, 52 n Origin AS: the last AS in the path – In the above example: AS 52 originated the path advertisement for prefix 131. 179/16 n Multiple Origin AS (MOAS): the same prefix announced by more than one origin AS 10/23/2001 NANOG 23 - Oakland 2
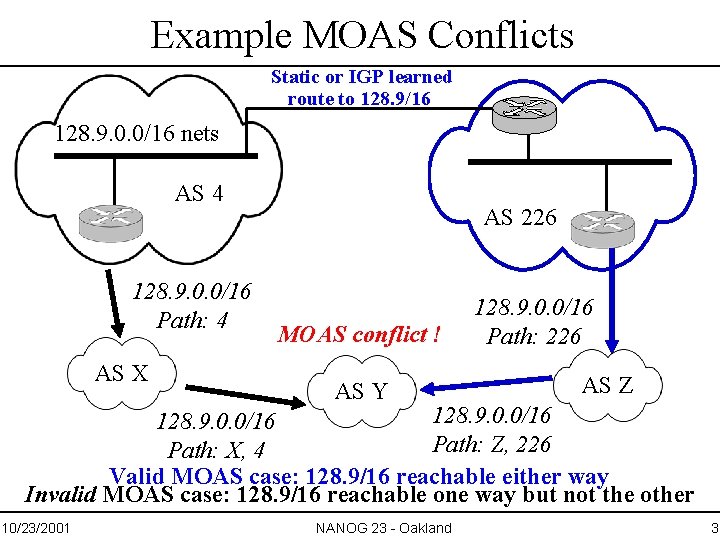
Example MOAS Conflicts Static or IGP learned route to 128. 9/16 128. 9. 0. 0/16 nets AS 4 128. 9. 0. 0/16 Path: 4 AS X AS 226 MOAS conflict ! AS Y 128. 9. 0. 0/16 Path: 226 AS Z 128. 9. 0. 0/16 Path: Z, 226 Path: X, 4 Valid MOAS case: 128. 9/16 reachable either way Invalid MOAS case: 128. 9/16 reachable one way but not the other 10/23/2001 NANOG 23 - Oakland 3
Talk Outline n Measurement data shows that MOAS exists n Some MOAS cases caused by faults Some MOAS cases due to operational need Important to distinguish the two n n – proposed solutions 10/23/2001 NANOG 23 - Oakland 4
Measurement Data Collection n Data collected from the Oregon Route Views – Peers with >50 routers from >40 different ASes. – Our analysis uses data [11/08/97 07/18/01] (1279 days total) n More than 38000 MOAS conflicts observed during this time period At a given moment, – The Route Views server observed 1364 MOAS conflicts – The views from 3 individual ISPs showed 30, 12 and 228 MOAS conflicts 10/23/2001 NANOG 23 - Oakland 5
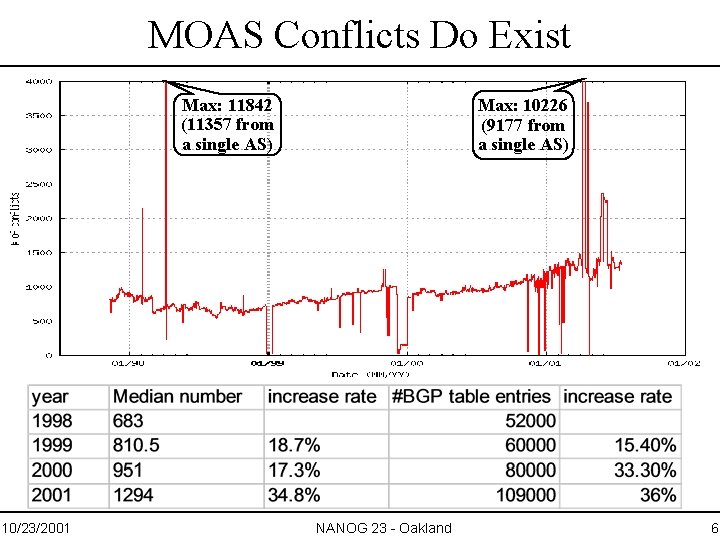
MOAS Conflicts Do Exist Max: 11842 (11357 from a single AS) 10/23/2001 Max: 10226 (9177 from a single AS) NANOG 23 - Oakland 6
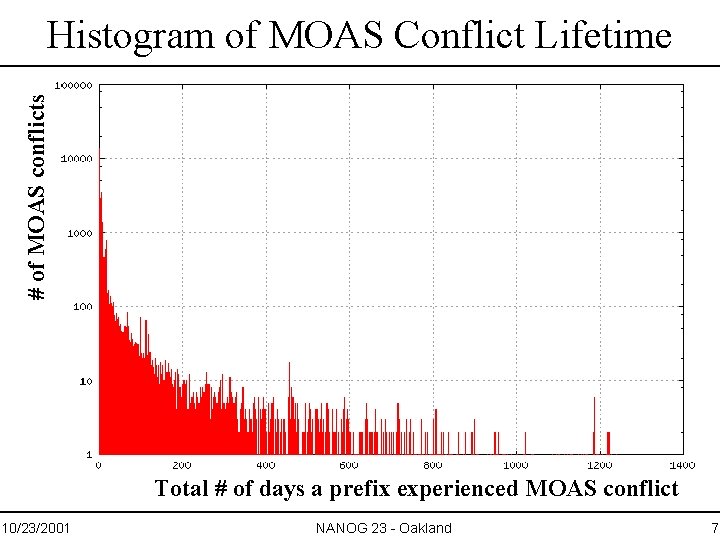
# of MOAS conflicts Histogram of MOAS Conflict Lifetime Total # of days a prefix experienced MOAS conflict 10/23/2001 NANOG 23 - Oakland 7
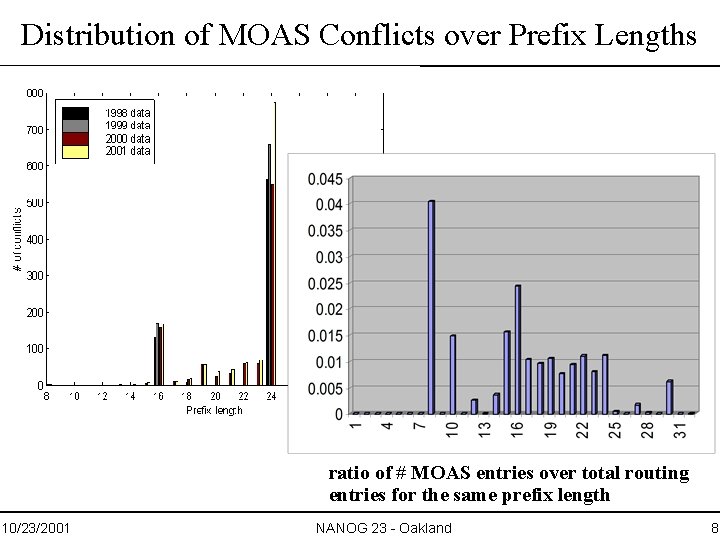
Distribution of MOAS Conflicts over Prefix Lengths ratio of # MOAS entries over total routing entries for the same prefix length 10/23/2001 NANOG 23 - Oakland 8
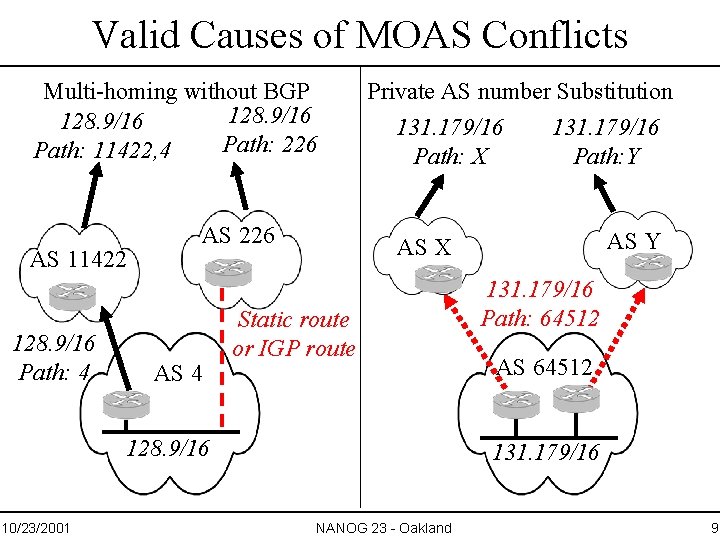
Valid Causes of MOAS Conflicts Multi-homing without BGP 128. 9/16 Path: 226 Path: 11422, 4 AS 11422 128. 9/16 Path: 4 AS 226 AS 4 Private AS number Substitution 131. 179/16 Path: X AS Y AS X Static route or IGP route 128. 9/16 10/23/2001 131. 179/16 Path: Y 131. 179/16 Path: 64512 AS 64512 131. 179/16 NANOG 23 - Oakland 9
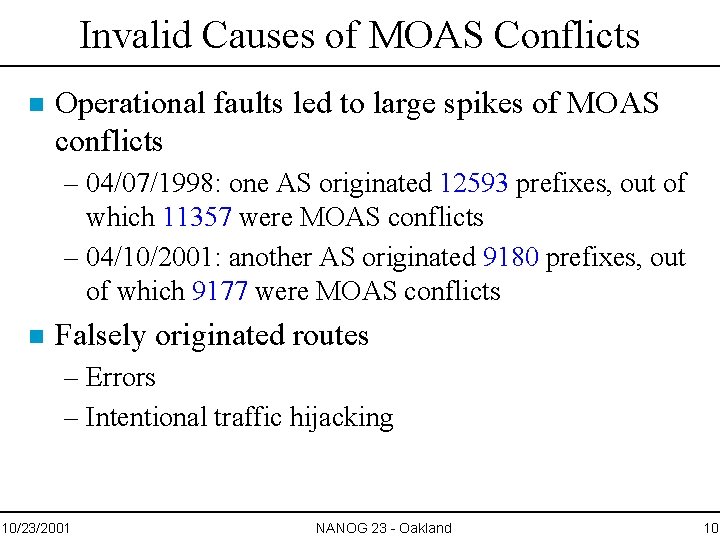
Invalid Causes of MOAS Conflicts n Operational faults led to large spikes of MOAS conflicts – 04/07/1998: one AS originated 12593 prefixes, out of which 11357 were MOAS conflicts – 04/10/2001: another AS originated 9180 prefixes, out of which 9177 were MOAS conflicts n Falsely originated routes – Errors – Intentional traffic hijacking 10/23/2001 NANOG 23 - Oakland 10
Handling MOAS Conflicts n n n RFC 1930 recommends each prefix be originated from a single AS Today’s routing practice leads to MOAS in normal operations We must tell valid MOAS cases from invalid ones – Proposal 1: using BGP community attribute – Proposal 2: DNS-based solution 10/23/2001 NANOG 23 - Oakland 11
BGP-Based Solution n Define a new community attribute – Listing all the ASes allowed to originate a prefix n n Attach this MOAS community-attribute to BGP route announcement Enable BGP routers to detect faults and attacks – At least in most cases, we hope! 10/23/2001 NANOG 23 - Oakland 12
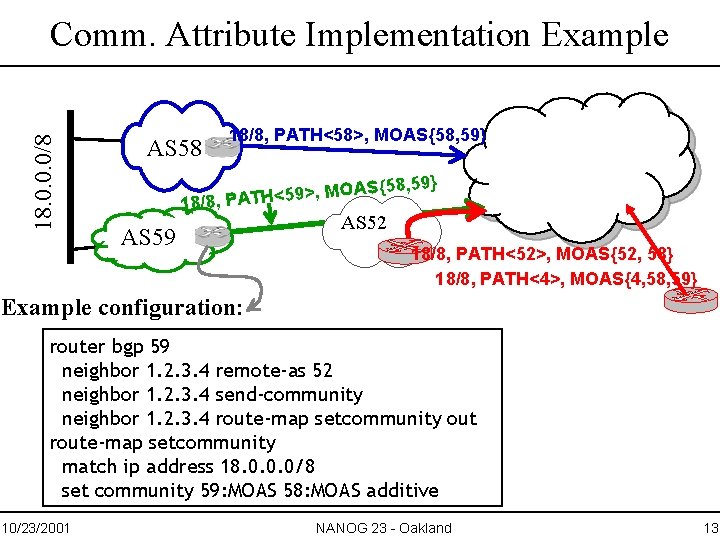
18. 0. 0. 0/8 Comm. Attribute Implementation Example AS 58 18/8, PATH<58>, MOAS{58, 59} O M , > 9 5 < H 18/8, PAT AS 59 AS 52 18/8, PATH<52>, MOAS{52, 58} 18/8, PATH<4>, MOAS{4, 58, 59} Example configuration: router bgp 59 neighbor 1. 2. 3. 4 remote-as 52 neighbor 1. 2. 3. 4 send-community neighbor 1. 2. 3. 4 route-map setcommunity out route-map setcommunity match ip address 18. 0. 0. 0/8 set community 59: MOAS 58: MOAS additive 10/23/2001 NANOG 23 - Oakland 13
Implementation Considerations n Quickly and incrementally deployable – Generating MOAS community attribute: configuration changes only – Detecting un-validated MOAS or a MOAS-CA conflict: • Short term: observable from monitoring platforms • Longer term: adding into BGP update processing n But community attributes may be dropped by a transit AS due to local configurations or policies – time to fix the handling of community attributes? 10/23/2001 NANOG 23 - Oakland 14
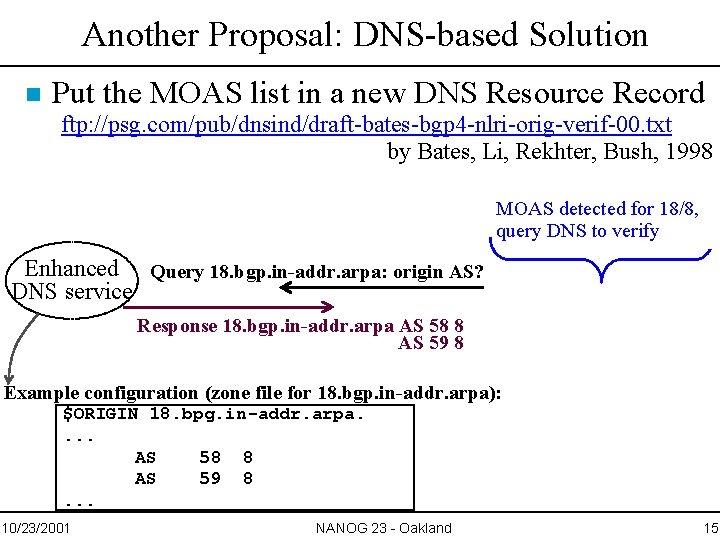
Another Proposal: DNS-based Solution n Put the MOAS list in a new DNS Resource Record ftp: //psg. com/pub/dnsind/draft-bates-bgp 4 -nlri-orig-verif-00. txt by Bates, Li, Rekhter, Bush, 1998 MOAS detected for 18/8, query DNS to verify Enhanced Query 18. bgp. in-addr. arpa: origin AS? DNS service Response 18. bgp. in-addr. arpa AS 58 8 AS 59 8 Example configuration (zone file for 18. bgp. in-addr. arpa): $ORIGIN 18. bpg. in-addr. arpa. . AS 58 8 AS 59 8. . . 10/23/2001 NANOG 23 - Oakland 15
Issues to Consider for the DNS Solution n Provides a general prefix to origin AS mapping database n Complementary to Community-attribute Approach – Check with DNS when community tag indicates a potential problem – DNSSEC, once available, authenticates the MOAS list n But requires changes to DNS and BGP n DNS may be vulnerable without DNSSEC – When would DNSSEC be ready? n Routing system querying naming system: circular dependency? 10/23/2001 NANOG 23 - Oakland 16
Summary n MOAS conflicts exist today – Some due to operational need; some due to faults n Blind acceptance of MOAS could be dangerous – An open door for traffic hijacking n We plan to finalize the solution and bring to IETF Send all questions to fniisc@isi. edu For more info about FNIISC project: http: //fniisc. nge. isi. edu 10/23/2001 NANOG 23 - Oakland 17
- Slides: 17