Bezpenost Windows pro pokroil identita uivatele Ing Ondej
Bezpečnost Windows pro pokročilé: identita uživatele Ing. Ondřej Ševeček | GOPAS a. s. | MCM: Directory | MVP: Enterprise Security | CEH: Certified Ethical Hacker | CHFI: Computer Hacking Forensic Investigator ondrej@sevecek. com | www. sevecek. com | GOPAS: info@gopas, cz | www. gopas. cz | www. facebook. com/P. S. GOPAS
Kurzy v počítačové škole GOPAS § http: //www. gopas. cz § GOC 175 - Advanced Windows Security § GOC 171 - Active Directory Internals and Troubleshooting § GOC 172 - Kerberos Troubleshooting § GOC 173 - Enterprise PKI Deployment § GOC 169 - ISO 2700 x in Windows Environment § CHFI - Computer Hacking Forensic Investigator
User identity, SID and access token Advanced Windows Security
Windows Processes § Everything runs as a process • some code runs in Kernel mode, but mostly under identity of the calling process • interrupts, DPCs and file cache are executing without user context § Every process runs under a user identity • SYSTEM, Network Service, Local Service, local user, domain user § Access permissions are always checked • there is no root superuser as in unix
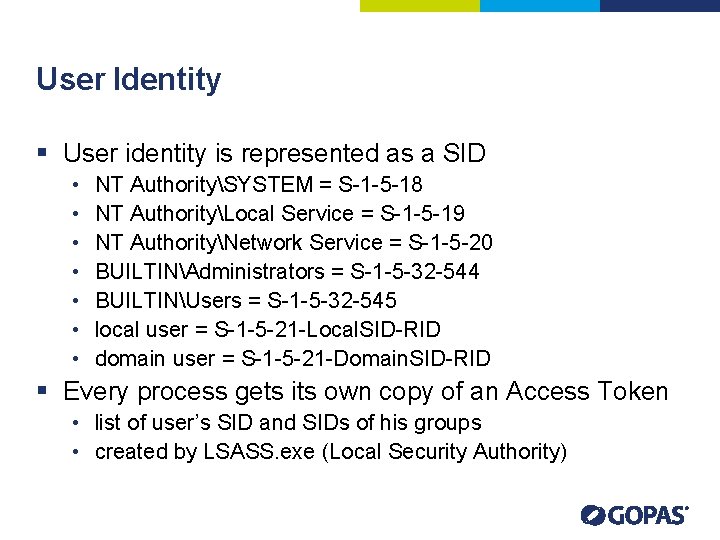
User Identity § User identity is represented as a SID • • NT AuthoritySYSTEM = S-1 -5 -18 NT AuthorityLocal Service = S-1 -5 -19 NT AuthorityNetwork Service = S-1 -5 -20 BUILTINAdministrators = S-1 -5 -32 -544 BUILTINUsers = S-1 -5 -32 -545 local user = S-1 -5 -21 -Local. SID-RID domain user = S-1 -5 -21 -Domain. SID-RID § Every process gets its own copy of an Access Token • list of user’s SID and SIDs of his groups • created by LSASS. exe (Local Security Authority)
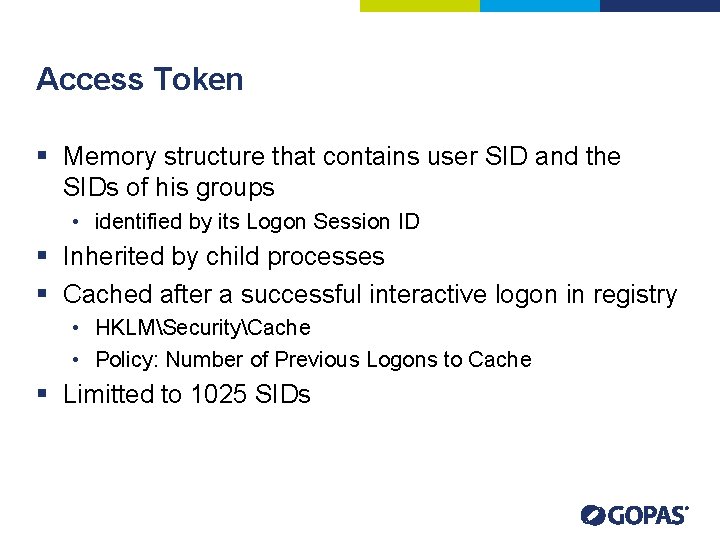
Access Token § Memory structure that contains user SID and the SIDs of his groups • identified by its Logon Session ID § Inherited by child processes § Cached after a successful interactive logon in registry • HKLMSecurityCache • Policy: Number of Previous Logons to Cache § Limitted to 1025 SIDs
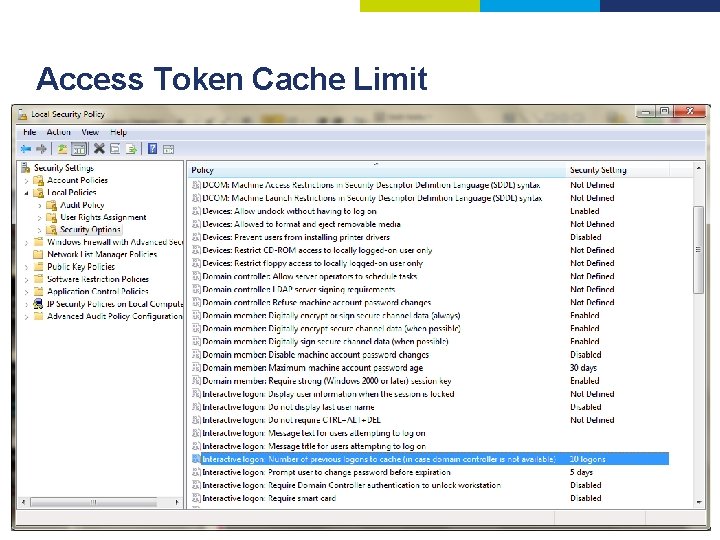
Access Token Cache Limit
Tools for Access Token § WHOAMI /ALL • built into Vista/2008 and newer • member of Support Tools for 2003/xp and older § PROCEXP • Process Explorer • download from http: //live. sysinternals. com § PSEXEC • download from http: //live. sysinternals. com § ADUC Attribute Editor • Active Directory Users and Computers console • Select View – Advanced Features • Can show user and group SIDs in AD
System SIDs § Some SIDs are added automatically § INTERACTIVE, NETWORK, BATCH, REMOTE INTERACTIVE LOGON § Everyone, Authenticated Users, This Organization, NTLM Authentication
Everyone vs. Authenticated Users § Windows 2000 • Everyone = Authenticated Users + Anonymous Logon § Windows XP+ • Everyone = Authenticated Users • can be changed back in security policy Let Everyone permissions apply to Anonymous Users
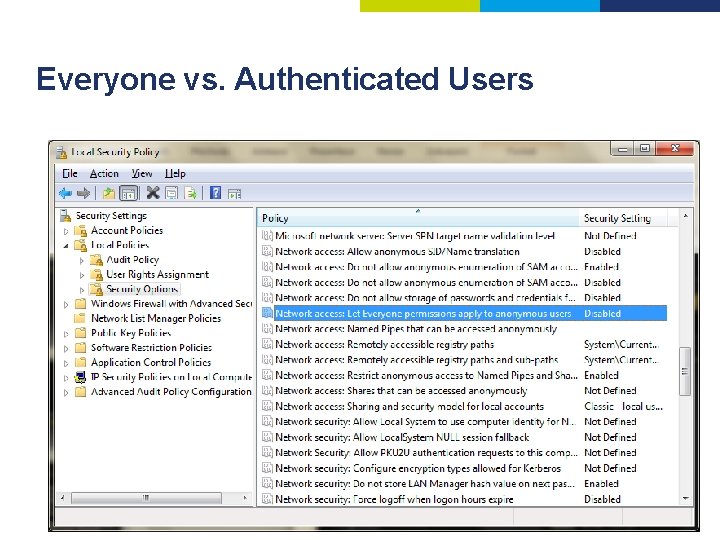
Everyone vs. Authenticated Users
Děkuji za pozornost Ing. Ondřej Ševeček | GOPAS a. s. | MCM: Directory | MVP: Enterprise Security | CEH: Certified Ethical Hacker | CHFI: Computer Hacking Forensic Investigator ondrej@sevecek. com | www. sevecek. com | GOPAS: info@gopas, cz | www. gopas. cz | www. facebook. com/P. S. GOPAS
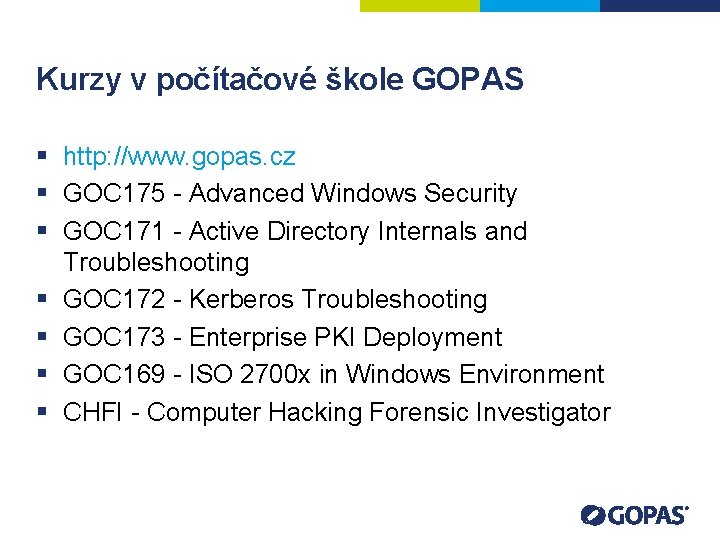
Kurzy v počítačové škole GOPAS § http: //www. gopas. cz § GOC 175 - Advanced Windows Security § GOC 171 - Active Directory Internals and Troubleshooting § GOC 172 - Kerberos Troubleshooting § GOC 173 - Enterprise PKI Deployment § GOC 169 - ISO 2700 x in Windows Environment § CHFI - Computer Hacking Forensic Investigator
- Slides: 13