Best Practices for Vendor Management and Cybersecurity GCs
Best Practices for Vendor Management and Cybersecurity GC’s Role in Mitigating Cyber Risk for Third Parties

The Age of Change. The Risk At Hand The “New Digital Economy” requires greater technology integration, openness, close supplier relationships and quicker speed-to-market. S&P 500 companies will be replaced by 2027 Companies are requiring that you share and connect your data and systems with and to 3 rd Party providers of services, cloud, mobile, etc. through the internet Executives think adopting outsourcing via the internet is a critical business model Sources: Yale University, HFS Research 2
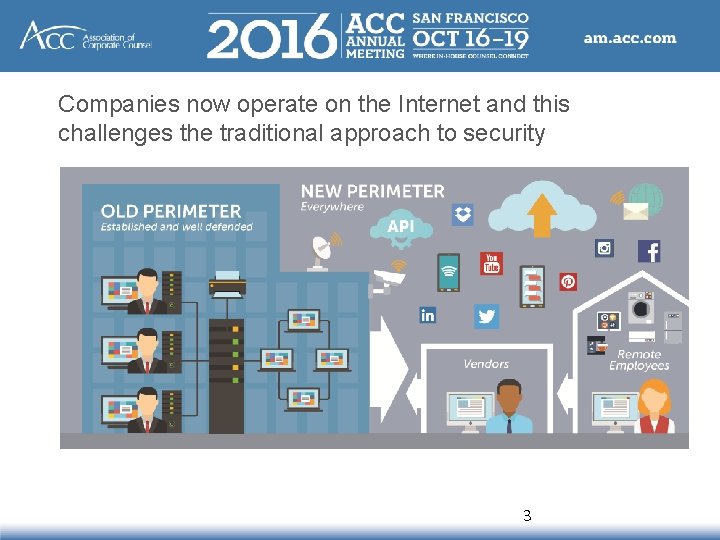
Companies now operate on the Internet and this challenges the traditional approach to security 3
The New Normal According to the Ponemon Institute, the three occurrences that have the greatest impact on brand reputation are environmental disasters, poor customer service, and data breaches Over the last 24+ months, the “tip of the iceberg” of 3 rd Party security risk in the extended perimeter. Hackers stole PII for 78 million people Estimated $100+ million 4
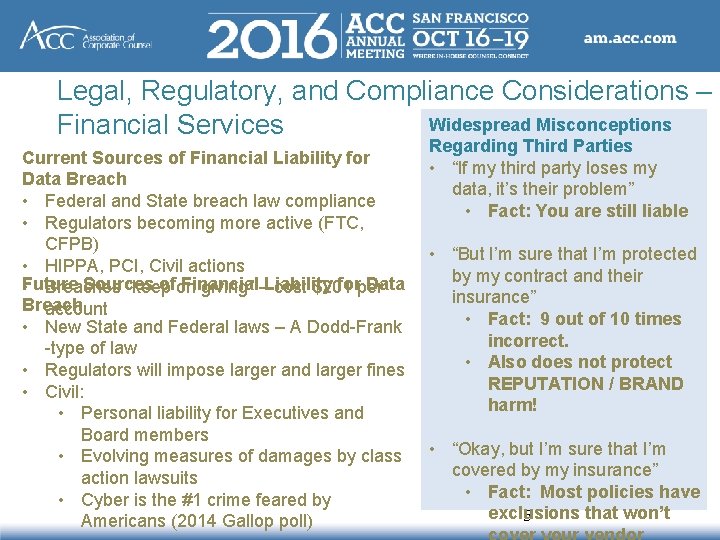
Legal, Regulatory, and Compliance Considerations – Widespread Misconceptions Financial Services Current Sources of Financial Liability for Data Breach • Federal and State breach law compliance • Regulators becoming more active (FTC, CFPB) • HIPPA, PCI, Civil actions Future Sources ofon Financial forper Data • Breaches “keep giving” –Liability cost $201 Breach account • New State and Federal laws – A Dodd-Frank -type of law • Regulators will impose larger and larger fines • Civil: • Personal liability for Executives and Board members • Evolving measures of damages by class action lawsuits • Cyber is the #1 crime feared by Americans (2014 Gallop poll) Regarding Third Parties • “If my third party loses my data, it’s their problem” • Fact: You are still liable • “But I’m sure that I’m protected by my contract and their insurance” • Fact: 9 out of 10 times incorrect. • Also does not protect REPUTATION / BRAND harm! • “Okay, but I’m sure that I’m covered by my insurance” • Fact: Most policies have exclusions that won’t 5
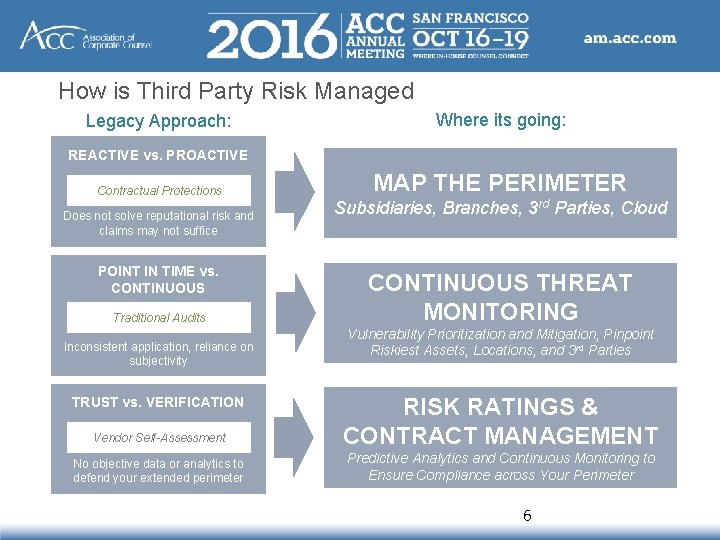
How is Third Party Risk Managed Legacy Approach: Where its going: REACTIVE vs. PROACTIVE Contractual Protections Does not solve reputational risk and claims may not suffice POINT IN TIME vs. CONTINUOUS Traditional Audits Inconsistent application, reliance on subjectivity MAP THE PERIMETER Subsidiaries, Branches, 3 rd Parties, Cloud CONTINUOUS THREAT MONITORING Vulnerability Prioritization and Mitigation, Pinpoint Riskiest Assets, Locations, and 3 rd Parties Vendor Self-Assessment RISK RATINGS & CONTRACT MANAGEMENT No objective data or analytics to defend your extended perimeter Predictive Analytics and Continuous Monitoring to Ensure Compliance across Your Perimeter TRUST vs. VERIFICATION 6
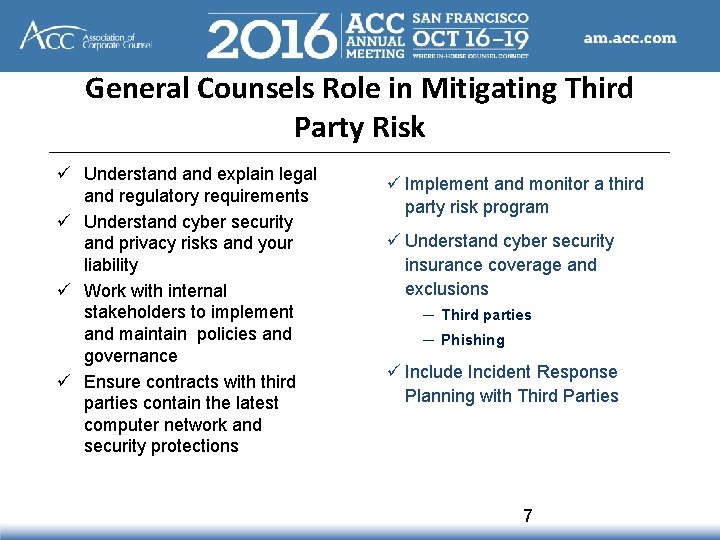
General Counsels Role in Mitigating Third Party Risk ü Understand explain legal and regulatory requirements ü Understand cyber security and privacy risks and your liability ü Work with internal stakeholders to implement and maintain policies and governance ü Ensure contracts with third parties contain the latest computer network and security protections ü Implement and monitor a third party risk program ü Understand cyber security insurance coverage and exclusions ─ Third parties ─ Phishing ü Include Incident Response Planning with Third Parties 7
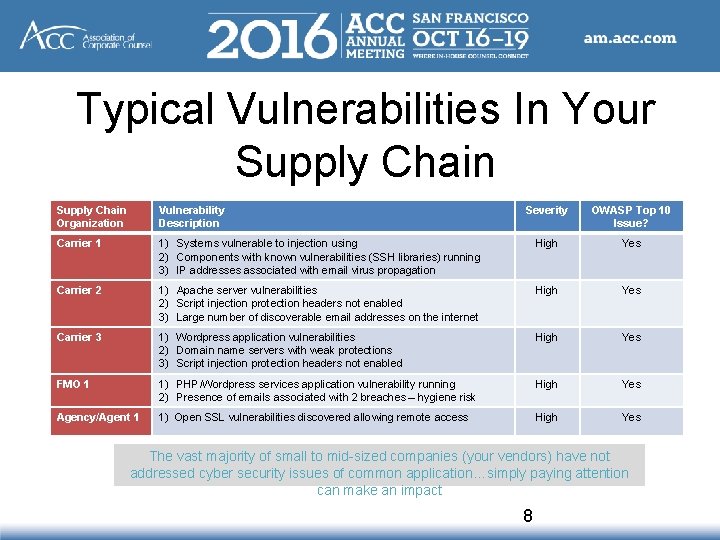
Typical Vulnerabilities In Your Supply Chain Organization Vulnerability Description Severity OWASP Top 10 Issue? Carrier 1 1) Systems vulnerable to injection using 2) Components with known vulnerabilities (SSH libraries) running 3) IP addresses associated with email virus propagation High Yes Carrier 2 1) Apache server vulnerabilities 2) Script injection protection headers not enabled 3) Large number of discoverable email addresses on the internet High Yes Carrier 3 1) Wordpress application vulnerabilities 2) Domain name servers with weak protections 3) Script injection protection headers not enabled High Yes FMO 1 1) PHP/Wordpress services application vulnerability running 2) Presence of emails associated with 2 breaches – hygiene risk High Yes Agency/Agent 1 1) Open SSL vulnerabilities discovered allowing remote access High Yes The vast majority of small to mid-sized companies (your vendors) have not addressed cyber security issues of common application…simply paying attention can make an impact 8
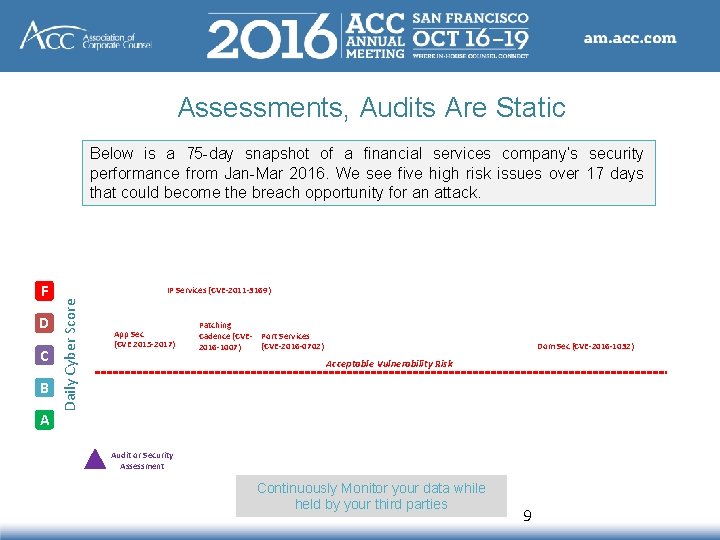
Assessments, Audits Are Static Below is a 75 -day snapshot of a financial services company’s security performance from Jan-Mar 2016. We see five high risk issues over 17 days that could become the breach opportunity for an attack. D C B A IP Services (CVE-2011 -3169) Daily Cyber Score F App Sec (CVE 2015 -2017) Patching Cadence (CVE- Port Services (CVE-2016 -0702) 2016 -1007) Dom Sec (CVE-2016 -1032) Acceptable Vulnerability Risk Audit or Security Assessment Continuously Monitor your data while held by your third parties 9
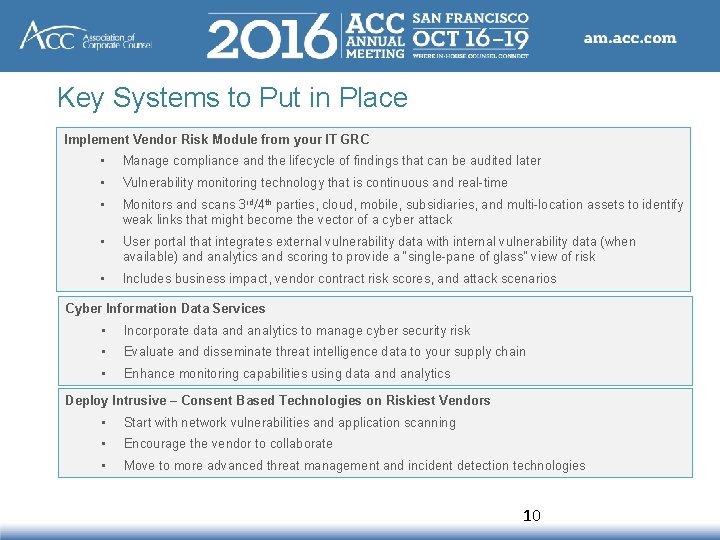
Key Systems to Put in Place Implement Vendor Risk Module from your IT GRC • Manage compliance and the lifecycle of findings that can be audited later • Vulnerability monitoring technology that is continuous and real-time • Monitors and scans 3 rd/4 th parties, cloud, mobile, subsidiaries, and multi-location assets to identify weak links that might become the vector of a cyber attack • User portal that integrates external vulnerability data with internal vulnerability data (when available) and analytics and scoring to provide a “single-pane of glass” view of risk • Includes business impact, vendor contract risk scores, and attack scenarios Cyber Information Data Services • Incorporate data and analytics to manage cyber security risk • Evaluate and disseminate threat intelligence data to your supply chain • Enhance monitoring capabilities using data and analytics Deploy Intrusive – Consent Based Technologies on Riskiest Vendors • Start with network vulnerabilities and application scanning • Encourage the vendor to collaborate • Move to more advanced threat management and incident detection technologies 10
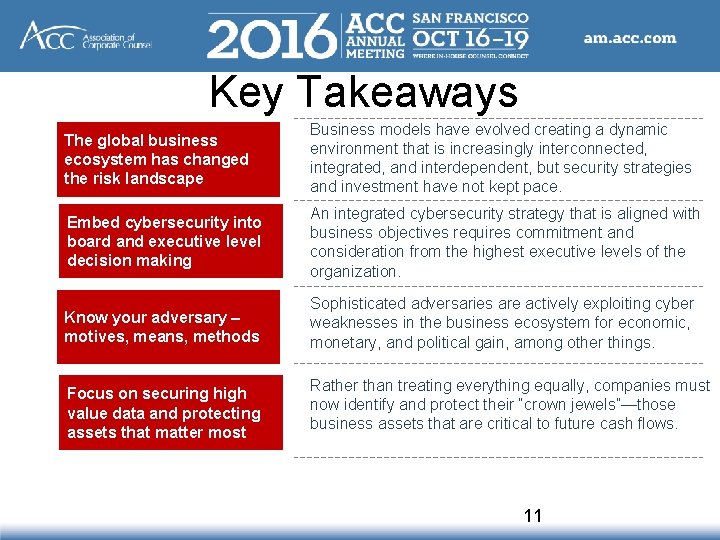
Key Takeaways The global business ecosystem has changed the risk landscape Business models have evolved creating a dynamic environment that is increasingly interconnected, integrated, and interdependent, but security strategies and investment have not kept pace. Embed cybersecurity into board and executive level decision making An integrated cybersecurity strategy that is aligned with business objectives requires commitment and consideration from the highest executive levels of the organization. Know your adversary – motives, means, methods Sophisticated adversaries are actively exploiting cyber weaknesses in the business ecosystem for economic, monetary, and political gain, among other things. Focus on securing high value data and protecting assets that matter most Rather than treating everything equally, companies must now identify and protect their “crown jewels”—those business assets that are critical to future cash flows. 11
- Slides: 11