Best Practices for PIM Policy Management CA Services
Best Practices for PIM Policy Management CA Services Team March 18, 2015
agenda Basics of “Fine Grain Access Controls” Policies Policy Naming Standards Guidelines Process of Policy Implementation Sample Policies Policy Deployment Considerations 2 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.

Basics of “Fine Grain Access Control” Policies
Privileged Identity Manager Basics of “Fine Grain Access Controls” Policies Basics — Comprised of “selang” Commands — Apply Controls to Access a Resource − Monitor (Warning Mode) − Enforce — Provides Delegated Administrative Functions − Perform System Commands As Privileged Access Accounts (e. g. root) 4 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Policies Basics (cont) — Provides Additional Layer of Security — Central Distribution to Define and Deploy Policies — PIM Endpoint Agent Receives and Enforces Policy 5 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Policies Basics (cont) — PIM Rules − Define Accessors − Define Resources − Authorization of Accessors to Resources 6 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Basics (cont) — Accessors − Users and Groups (USER/XUSER or GROUP/XGROUP) − Logical Account (e. g. Backup Program) 7 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Basics (cont) — PIM Resources (Classes) − Files, Directories − Registry Keys/Registry Values − Ability to Surrogate “su” to an Account − Ability to Login to a Server − Access to Outbound TCP Service 8 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Basics (cont) — Define PIM Object — Common PIM Object Classes: − FILE − TERMINAL − PROGRAM − REGKEY − SURROGATE − SUDO 9 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Basics (cont) — Authorization − Read a file or directory, and/or only provide access via a specific program. − Able to shutdown a service − Able to login to a server from a specific terminal NOTE: Warning Mode is applied to an Object, and not an Authorization Rule 10 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Basics (cont) — Two Parts to PIM Policy − Deployment Script • PIM Rules Executed when Policy Deployed − Undeployment Script • PIM Rules Executed when Policy Undeployed 11 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.

Naming Standards
Privileged Identity Manager Policy Naming Standards Establish Naming Conventions — <Environment>_<Purpose/Application>_<OS_Platform> − Environment • Production, Non-Producution, Development, Staging, UAT, etc. − Purpose/Application • Common Purpose (Corporate or Security Policy Focused) • Application (Oracle, or Backup Program, etc) − OS Platform • Common OS Platforms – AIX, Solaris, Su. SE, HPUX, Windows, etc 13 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
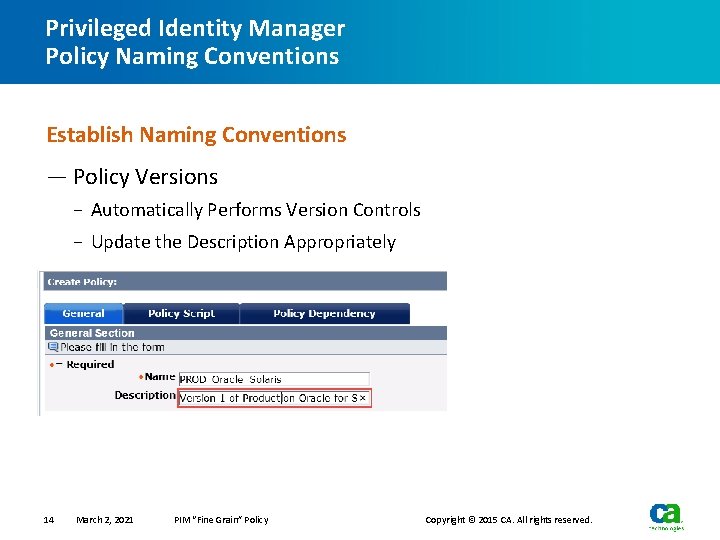
Privileged Identity Manager Policy Naming Conventions Establish Naming Conventions — Policy Versions − Automatically Performs Version Controls − Update the Description Appropriately 14 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Process of Policy Implementation
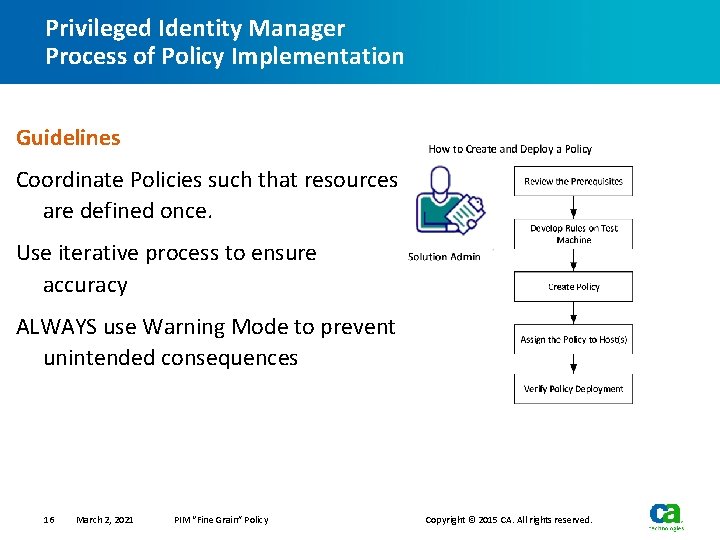
Privileged Identity Manager Process of Policy Implementation Guidelines Coordinate Policies such that resources are defined once. Use iterative process to ensure accuracy ALWAYS use Warning Mode to prevent unintended consequences 16 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
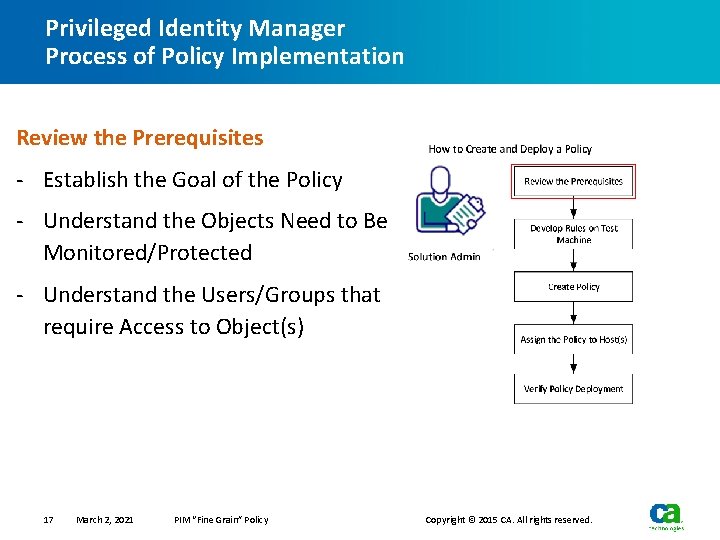
Privileged Identity Manager Process of Policy Implementation Review the Prerequisites - Establish the Goal of the Policy - Understand the Objects Need to Be Monitored/Protected - Understand the Users/Groups that require Access to Object(s) 17 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
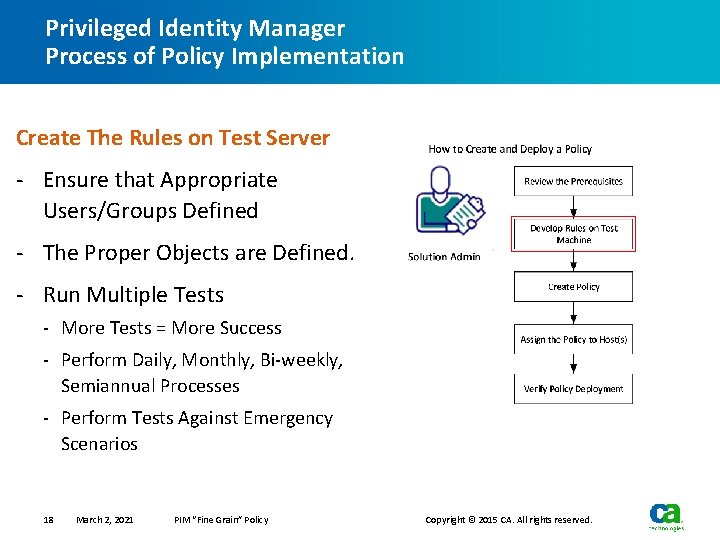
Privileged Identity Manager Process of Policy Implementation Create The Rules on Test Server - Ensure that Appropriate Users/Groups Defined - The Proper Objects are Defined. - Run Multiple Tests - More Tests = More Success - Perform Daily, Monthly, Bi-weekly, Semiannual Processes - Perform Tests Against Emergency Scenarios 18 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
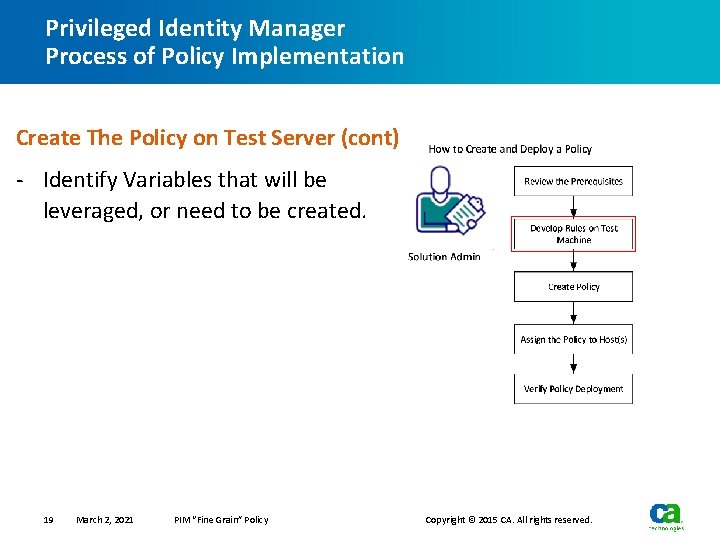
Privileged Identity Manager Process of Policy Implementation Create The Policy on Test Server (cont) - Identify Variables that will be leveraged, or need to be created. 19 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
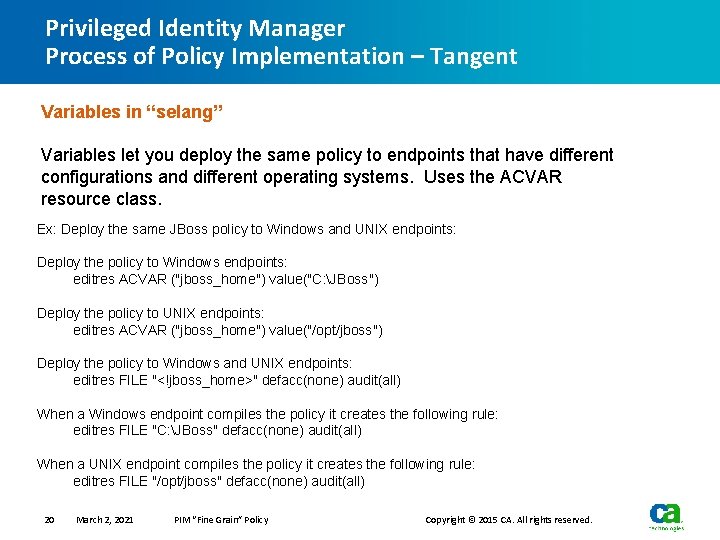
Privileged Identity Manager Process of Policy Implementation – Tangent Variables in “selang” Variables let you deploy the same policy to endpoints that have different configurations and different operating systems. Uses the ACVAR resource class. Ex: Deploy the same JBoss policy to Windows and UNIX endpoints: Deploy the policy to Windows endpoints: editres ACVAR ("jboss_home") value("C: JBoss") Deploy the policy to UNIX endpoints: editres ACVAR ("jboss_home") value("/opt/jboss") Deploy the policy to Windows and UNIX endpoints: editres FILE "<!jboss_home>" defacc(none) audit(all) When a Windows endpoint compiles the policy it creates the following rule: editres FILE "C: JBoss" defacc(none) audit(all) When a UNIX endpoint compiles the policy it creates the following rule: editres FILE "/opt/jboss" defacc(none) audit(all) 20 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
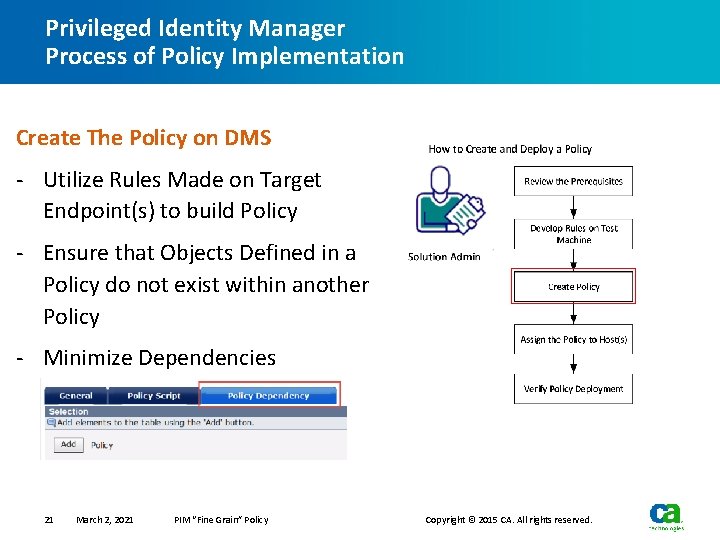
Privileged Identity Manager Process of Policy Implementation Create The Policy on DMS - Utilize Rules Made on Target Endpoint(s) to build Policy - Ensure that Objects Defined in a Policy do not exist within another Policy - Minimize Dependencies 21 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
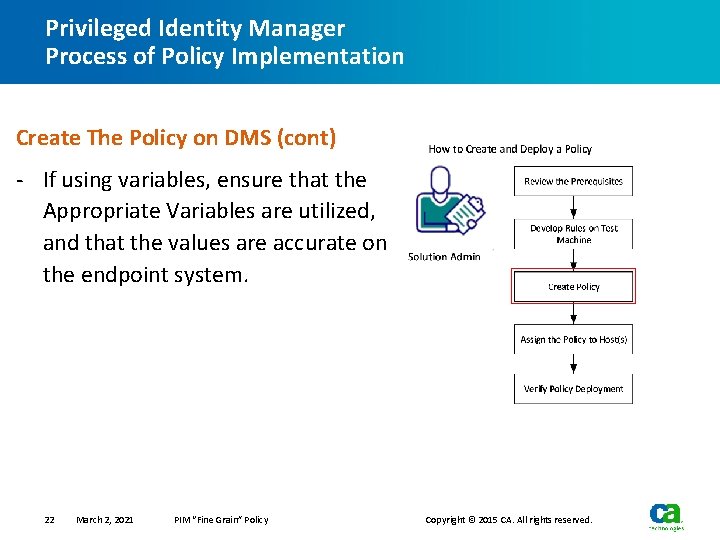
Privileged Identity Manager Process of Policy Implementation Create The Policy on DMS (cont) - If using variables, ensure that the Appropriate Variables are utilized, and that the values are accurate on the endpoint system. 22 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
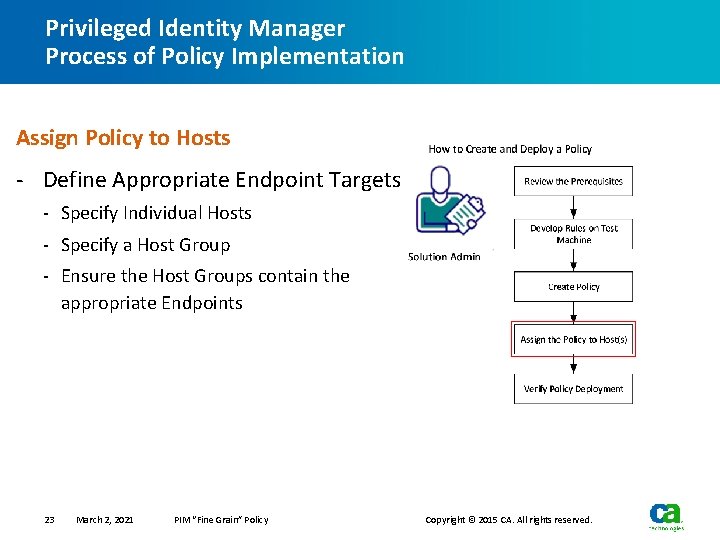
Privileged Identity Manager Process of Policy Implementation Assign Policy to Hosts - Define Appropriate Endpoint Targets - Specify Individual Hosts - Specify a Host Group - Ensure the Host Groups contain the appropriate Endpoints 23 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
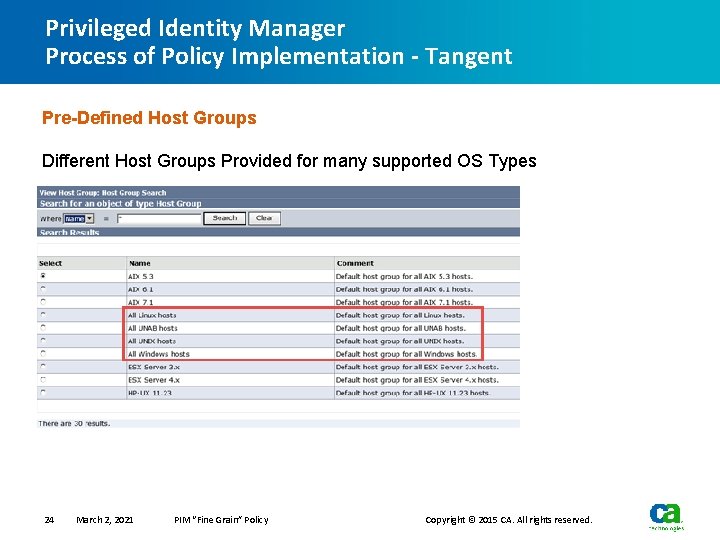
Privileged Identity Manager Process of Policy Implementation - Tangent Pre-Defined Host Groups Different Host Groups Provided for many supported OS Types 24 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
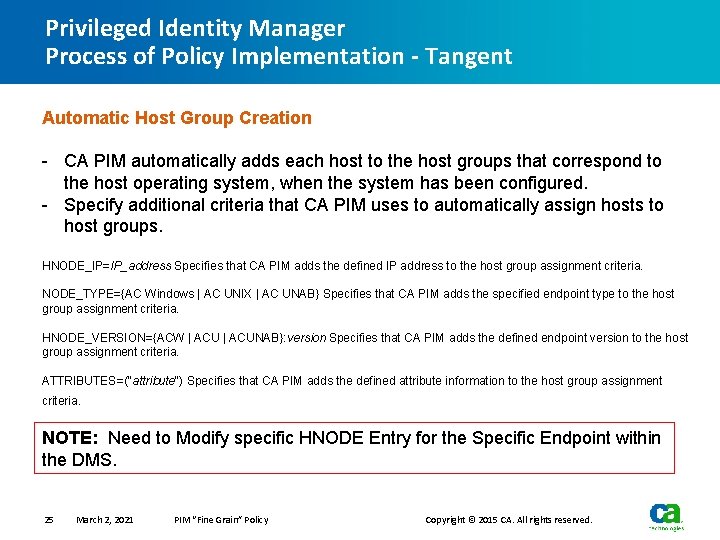
Privileged Identity Manager Process of Policy Implementation - Tangent Automatic Host Group Creation - CA PIM automatically adds each host to the host groups that correspond to the host operating system, when the system has been configured. - Specify additional criteria that CA PIM uses to automatically assign hosts to host groups. HNODE_IP=IP_address Specifies that CA PIM adds the defined IP address to the host group assignment criteria. NODE_TYPE={AC Windows | AC UNIX | AC UNAB} Specifies that CA PIM adds the specified endpoint type to the host group assignment criteria. HNODE_VERSION={ACW | ACUNAB}: version Specifies that CA PIM adds the defined endpoint version to the host group assignment criteria. ATTRIBUTES=("attribute") Specifies that CA PIM adds the defined attribute information to the host group assignment criteria. NOTE: Need to Modify specific HNODE Entry for the Specific Endpoint within the DMS. 25 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
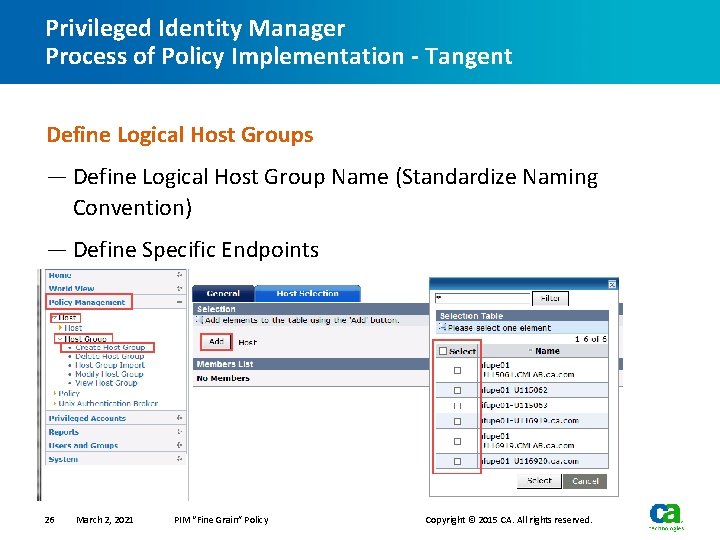
Privileged Identity Manager Process of Policy Implementation - Tangent Define Logical Host Groups — Define Logical Host Group Name (Standardize Naming Convention) — Define Specific Endpoints 26 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
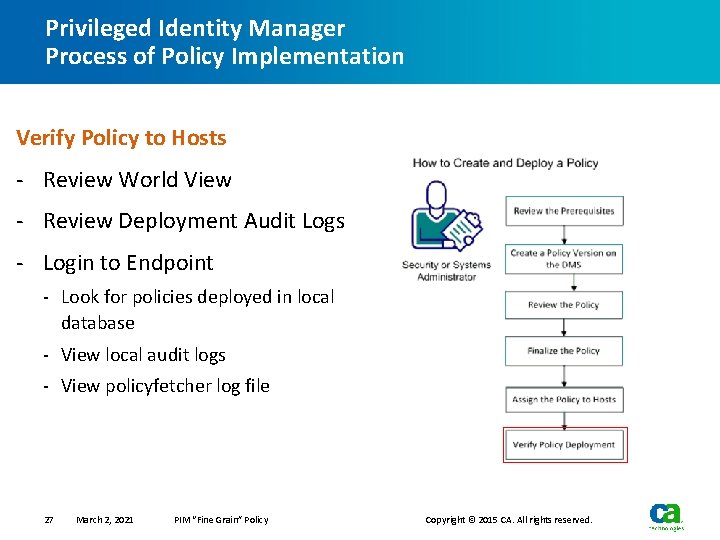
Privileged Identity Manager Process of Policy Implementation Verify Policy to Hosts - Review World View - Review Deployment Audit Logs - Login to Endpoint - Look for policies deployed in local database - View local audit logs - View policyfetcher log file 27 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Policies
Privileged Identity Manager Policies Sources for Constructing Policies — Review Last Audit Report/Audit Findings — Review Security Policy — Conduct Interviews: − IT Audit − IT Compliance − IT Security Operations − Enterprise Architecture − Management 29 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policies Translate the Obtained Information Into PIM Objects — Prevent Unauthorized Access to Specific Files/Directories − FILE Class Object — Prevent Unauthorized Access to Shared Accounts via “su” or “sudo” − SURROGATE Class Object — Prevent Unauthorized Login − TERMINAL Class Object 30 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policies Translate the Obtained Information Into PIM Objects (cont) — Disable Use of USB Drives on Windows − REGKEY Class Object − REGVAL Class Object — Prevent Unauthorized Access To Applications − FILE Class Object − PROGRAM Class Object — Prevent Unauthorized Shutting Down Of Process − PROCESS Class Object − FILE Class Object − PROGRAM Class Object 31 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policies Additional Information About PIM Objects — List Can be Found on the CA WIKI Pages (https: //wiki. ca. com) 32 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policies Sample Policies are provided on the ENTM server. Sample policies include examples for securing Applications, OSs, and more. 33 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policies Caveat for Sample Policies - CA recommends customization of policy to your specifications. - CA recommends thorough testing for each policy in the target environment before you deploy it. 34 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Policy Deployment Considerations
Privileged Identity Manager Policy Deployment Considerations Create Deployment and Undeployment Scripts - Utilize a Text Editor (e. g. Notepad++) to create deployment and Undeployment scripts - Always Include Comments in the scripts - Create a Policy Directory on the ENTM Server, to store scripts - Solution Administrators will Login to ENTM Server to create/modify policies 36 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
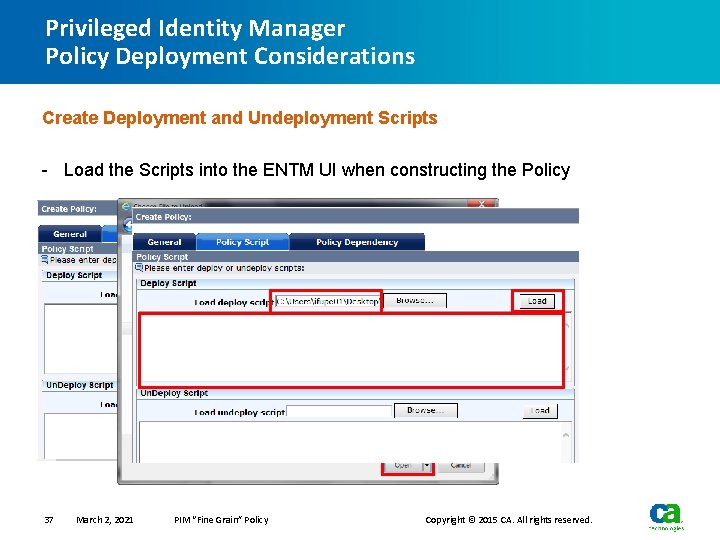
Privileged Identity Manager Policy Deployment Considerations Create Deployment and Undeployment Scripts - Load the Scripts into the ENTM UI when constructing the Policy 37 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policy Deployment Considerations Determine Desired Effect for Undeployment Scripts — If no deployment script defined in PIM Policy, during undeployment, PIM Agent will undo what was done during deployment. − Monitored/Protected Resources Rules and Authorizations are GONE!!! — Develop an Undeployment Script for Desired Effect − For Example: At time of policy undeployment, define resources into warning mode. 38 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policy Deployment Considerations Be Concise — Limit the size of the deployment and undeployment scripts in terms of number of lines − No more than 800 lines of rules and comments (ideal would be under 200) 39 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policy Deployment Considerations Usage of Variables — Best Configured During Post Installation Step of Agent Deployment — Refrain from utilizing too many Variables within Deployment/Undeployment Scripts − Remember “Concise Rules” 40 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policy Deployment Considerations Policy Dependencies — Minimize its usage — Refrain from “stacking” policy dependencies 41 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policy Deployment Considerations Limit Resource Definition — Refrain from defining a previously identified PIM Object in multiple policies. − Policy Deviation Calculator will “complain” on all PIM Policies associated with same PIM Object − Increase Chance of Incorrect Policy Authorization Conflicts 42 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
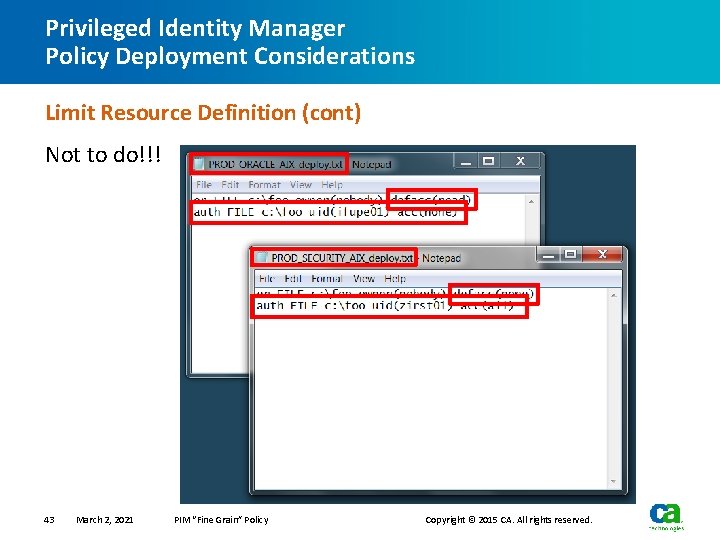
Privileged Identity Manager Policy Deployment Considerations Limit Resource Definition (cont) Not to do!!! 43 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Privileged Identity Manager Policy Deployment Considerations Policy Naming — Refrain from Special Characters - $ # ‘ ` “ | ! — Change between Uppercase and Lowercase — Use Underscores 44 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Q&A
Q&A — Ask a question… − In the Web. Ex Q&A or Chat windows. − Press *6 or #6 to unmute your line. − Or… in the CA Security Community! ca. com/talksecurity Follow @CASecurity and @CA_Community on Twitter! 46 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
Join CA Communities! Visit communities. ca. com to register. — LEARN about best practices and use cases. Lower your TCO and maximize impact. — CONNECT with product management and support. Ask a question or submit an idea for a future release. — SHARE your experience and expertise with other CA customers and partners. 47 March 2, 2021 PIM “Fine Grain” Policy — Follow the CA Security Community: ca. com/talksecurity — Products covered: − − − − CA Single Sign-On CA Identity Suite CA Privileged Identity Manager CA Secure Cloud CA Data Protection CA Risk Authentication CA Strong Authentication CA Directory Copyright © 2015 CA. All rights reserved.
Additional Information About Presenter Peter Paul M Ifurung Senior Services Architect, CA Services Dealt with Privileged Identity Manager since Jan 1996. Email: Peter. Paul. Ifurung@ca. com Phone: 650. 759. 5456 48 March 2, 2021 PIM “Fine Grain” Policy Copyright © 2015 CA. All rights reserved.
End Of Presentation Basics (cont) — Define Object Syntax COMMAND CLASS NAME OPTIONS 49 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Sample Access Control Rule – Commands − editres (er) − newres (nr) − chres (cr) − rmres (rr) 50 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Sample PIM Resource Classes − FILE − PROGRAM − PROCESS − SURROGATE 51 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Sample Access Control Resource Names − /tmp/foo − % systemroot % Program FilesCAAccess. Control − SSH 52 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Sample Access Control Definition Rules er FILE /tmp/foo owner(nobody) defacc(none) audit(none) er TCP SSH defacc(read) owner(nobody) audit(none) er SURROGATE USER. root defacc(read) owner(nobody) audit(failure) 53 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Define Accessors − User Account − OS Group − Logical User (Service Account) − Logical Group (group defined within AC environment) 54 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — USER objects − Created by AC Administrator − Import Tools − Manually Created − Based on the OS User − Can be created to represent a logical user (SPECIALPGM) 55 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Differences between USER and XUSER objects − USER objects need to be maintained − USER objects need to be joined to appropriate groups − XUSER objects are dynamic (group membership) − XUSER objects tied to OS 56 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — GROUP objects − Created by AC Administrator − Import Tools − Manually Created − Maintained − Based on the OS Groups − Defined Logical Groups (i. e. J unior Sysadmins) 57 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — XGROUP − Need to be created by AC Administrator − Need to be the same name as the OS group (case-sensitive depending on OS) − Can be created during rules creation 58 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies — Define Authorizations − AC Class − Object − User(s) and/or Group(s) − Type of Access (read, write, del, chdir, exec) − Program or Conditional Access 59 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies Syntax AUTH CLASS OBJ ECT USER/GROUP ACCESS OPTION Sample Authorizations auth FILE /tmp/foo xgid(users) acc(read) auth FILE /tmp/foo xgid(secadmin) acc(read write) via(pgm(/bin/vi)) 60 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies Differences Between Default Access and Access — The Default Access applies to accounts that are either not explicitly defined or not a member of a group that is explicitly defined with a different set of access — Example er file /tmp/foo owner(nobody) defacc(none) auth file /tmp/foo uid(ifupe 01) acc(all) auth file /tmp/foo gid(admins) acc(read) 61 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies - Authorization Conflicts − By default, most specific rule applies − User Authorization overrides Group Authorizations − User Member of Two Groups with different access • Defined by “accumulate group rights” setoptions setting − Access of “none” prevents any other PACL authorizations from working 62 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
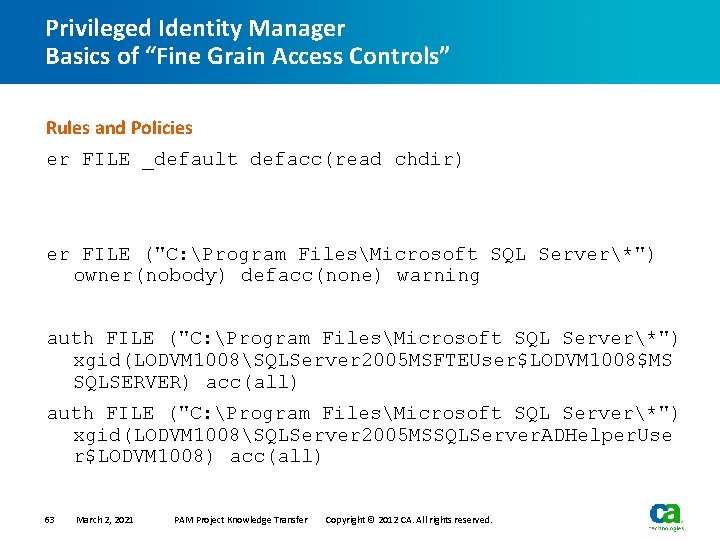
Privileged Identity Manager Basics of “Fine Grain Access Controls” Rules and Policies er FILE _default defacc(read chdir) er FILE ("C: Program FilesMicrosoft SQL Server*") owner(nobody) defacc(none) warning auth FILE ("C: Program FilesMicrosoft SQL Server*") xgid(LODVM 1008SQLServer 2005 MSFTEUser$LODVM 1008$MS SQLSERVER) acc(all) auth FILE ("C: Program FilesMicrosoft SQL Server*") xgid(LODVM 1008SQLServer 2005 MSSQLServer. ADHelper. Use r$LODVM 1008) acc(all) 63 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
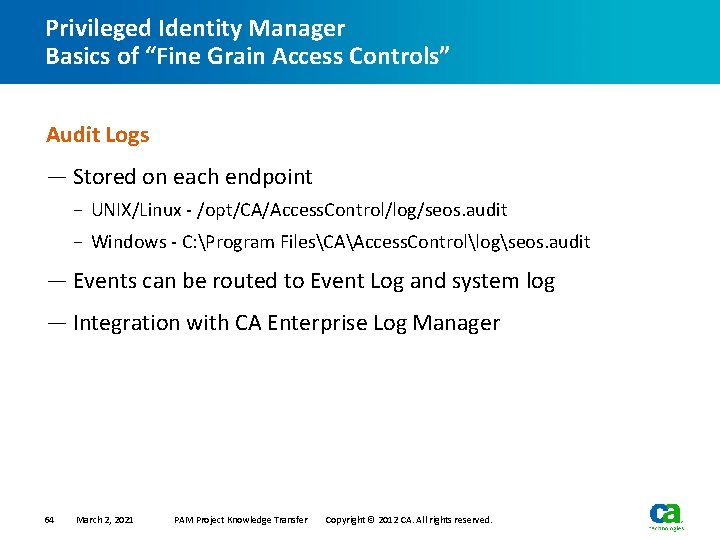
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Stored on each endpoint − UNIX/Linux - /opt/CA/Access. Control/log/seos. audit − Windows - C: Program FilesCAAccess. Controllogseos. audit — Events can be routed to Event Log and system log — Integration with CA Enterprise Log Manager 64 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Active audit file is protected by AC — Data is stored in proprietary format — Require AC tools to view − /opt/CA/Access. Control/bin/seaudit − C: Program FilesCAAccess. Controlbinseaudit − Endpoint Manager UI 65 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Configured to roll over − Size − Period (daily, weekly, monthly) − Append Time/Date Stamp 66 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Audit events show up based on AC object audit flag − er FILE /tmp/foo defacc(none) audit(failure) − eu ifupe 01 admin auditor audit(loginfailure loginsuccess failure) 67 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
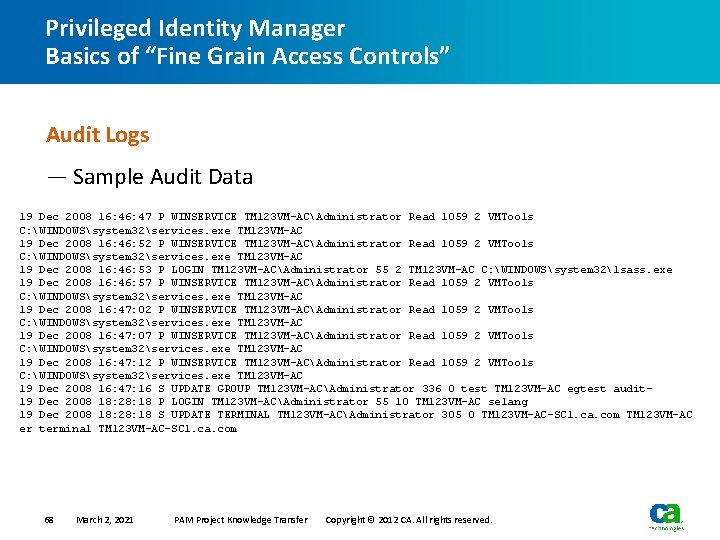
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Sample Audit Data 19 Dec 2008 16: 47 P WINSERVICE TM 123 VM-ACAdministrator Read 1059 2 VMTools C: WINDOWSsystem 32services. exe TM 123 VM-AC 19 Dec 2008 16: 46: 52 P WINSERVICE TM 123 VM-ACAdministrator Read 1059 2 VMTools C: WINDOWSsystem 32services. exe TM 123 VM-AC 19 Dec 2008 16: 46: 53 P LOGIN TM 123 VM-ACAdministrator 55 2 TM 123 VM-AC C: WINDOWSsystem 32lsass. exe 19 Dec 2008 16: 46: 57 P WINSERVICE TM 123 VM-ACAdministrator Read 1059 2 VMTools C: WINDOWSsystem 32services. exe TM 123 VM-AC 19 Dec 2008 16: 47: 02 P WINSERVICE TM 123 VM-ACAdministrator Read 1059 2 VMTools C: WINDOWSsystem 32services. exe TM 123 VM-AC 19 Dec 2008 16: 47: 07 P WINSERVICE TM 123 VM-ACAdministrator Read 1059 2 VMTools C: WINDOWSsystem 32services. exe TM 123 VM-AC 19 Dec 2008 16: 47: 12 P WINSERVICE TM 123 VM-ACAdministrator Read 1059 2 VMTools C: WINDOWSsystem 32services. exe TM 123 VM-AC 19 Dec 2008 16: 47: 16 S UPDATE GROUP TM 123 VM-ACAdministrator 336 0 test TM 123 VM-AC egtest audit 19 Dec 2008 18: 28: 18 P LOGIN TM 123 VM-ACAdministrator 55 10 TM 123 VM-AC selang 19 Dec 2008 18: 28: 18 S UPDATE TERMINAL TM 123 VM-ACAdministrator 305 0 TM 123 VM-AC-SC 1. ca. com TM 123 VM-AC er terminal TM 123 VM-AC-SC 1. ca. com 68 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — First Three Columns are same for all events − Date of the Event − Time of the Event − Return Code — Remaining Columns Dependent upon type of Event − Event type − Accessor/Class − Access type − Stage code 69 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Remaining Columns Dependent upon type of Event (cont) − Audit record code − Resource − Terminal/Program − Command 70 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
Privileged Identity Manager Basics of “Fine Grain Access Controls” Audit Logs — Return Codes − D – AC denied access to the resource − F – Attempt to update the local database failed − M – Message event stating that AC is either starting or stopping − O – User logging out of server − P – AC permitted access to the resource − S – Attempt to update the local database successful − W – Warning event indicating that AC should have denied access to the resource by the object is in Warning Mode 71 March 2, 2021 PAM Project Knowledge Transfer Copyright © 2012 CA. All rights reserved.
- Slides: 71