BDDs Theorem Proving Binary Decision Diagrams Dr Eng
BDDs & Theorem Proving Binary Decision Diagrams Dr. Eng. Amr T. Abdel-Hamid Network Protocols NETW 703 Lectures are based on slides by: • K. Havelund & Agroce, Reliable Software: Testing and Monitoring, CMU. • E. Clarke, Formal Methods, to be updated by course name • S. Tahar, E. Cerny and X. Song, “ Formal Verification of Systems”. Spring 2020
Binary Decision Diagrams Network Protocols Ø Ordered binary decision diagrams (OBDDs) are a canonical form for Boolean formulas. Ø OBDDs are often substantially more compact than traditional normal forms. Ø Moreover, they can be manipulated very efficiently. Ø Introduced at: Ø R. E. Bryant. Graph-based algorithms for boolean function manipulation. IEEE Transactions on Computers, C-35(8), 1986. Dr. Amr Talaat
Binary Decision Trees Network Protocols Ø A Binary decision tree is a rooted, directed tree with two types of vertices, terminal vertices and nonterminal vertices. Ø Each nonterminal vertex v is labeled by a variable var(v) and has two successors: Ø low (v) corresponding to the case where the variable is assigned 0, and high (v) corresponding to the case where the variable is assigned 1. Ø Each terminal vertex v is labeled by value(v) which is either 0 or 1 Dr. Amr Talaat
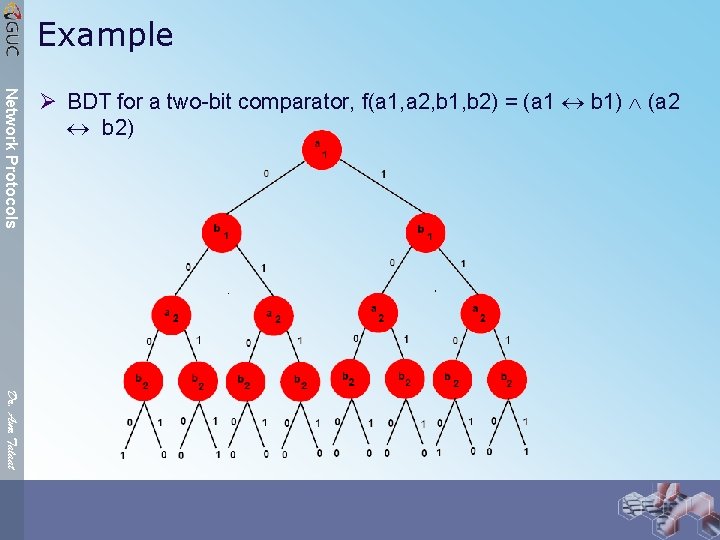
Example Network Protocols Ø BDT for a two-bit comparator, f(a 1, a 2, b 1, b 2) = (a 1 b 1) (a 2 b 2) Dr. Amr Talaat
Binary Decision Diagram Network Protocols Ø i. e. exactly like decision TREE Dr. Amr Talaat
Reduced Ordered BDDs Network Protocols Ø In practical applications, it is desirable to have a canonical representation for Boolean functions. Ø This simplifies tasks like checking equivalence of two formulas and deciding if a given formula is satisfiable or not. Ø Such a representation must guarantee that two Boolean functions are logically equivalent if and Ø only if they have isomorphic representations. Dr. Amr Talaat

Reduced Ordered BDD Network Protocols Dr. Amr Talaat Ø Canonical Form property Ø A canonical representation for Boolean functions is desirable: Ø two Boolean functions are logically equivalent iff they have isomorphic representations Ø This simplifies checking equivalence of two formulas and deciding if a formula is satisfiable Ø Two BDDs are isomorphic if there exists a bijection h between the graphs such that Ø Terminals are mapped to terminals and nonterminals are mapped to nonterminals Ø For every terminal vertex v, value(v) = value(h(v)), and Ø For every nonterminal vertex v: var(v) = var(h(v)), h(low(v)) = low(h(v)), and h(high(v)) = high(h(v))
Canonical Form property Network Protocols Ø Bryant (1986) showed that BDDs are a canonical representation for Boolean functions under two restrictions: Ø the variables appear in the same order along each path from the root to a terminal Ø there are no isomorphic subtrees or redundant vertices Dr. Amr Talaat
Reduced Ordered Binary Decision Diagrams (ROBDDs): CREATION Network Protocols Ø Canonical Form Property Ø Requirement (1): Impose total order “<” on the variables in the formula: if vertex u has a nonterminal successor v, then var(u) < var(v) Ø Requirement (2): repeatedly apply three transformation rules (or implicitly in operations such as disjunction or conjunction) Dr. Amr Talaat
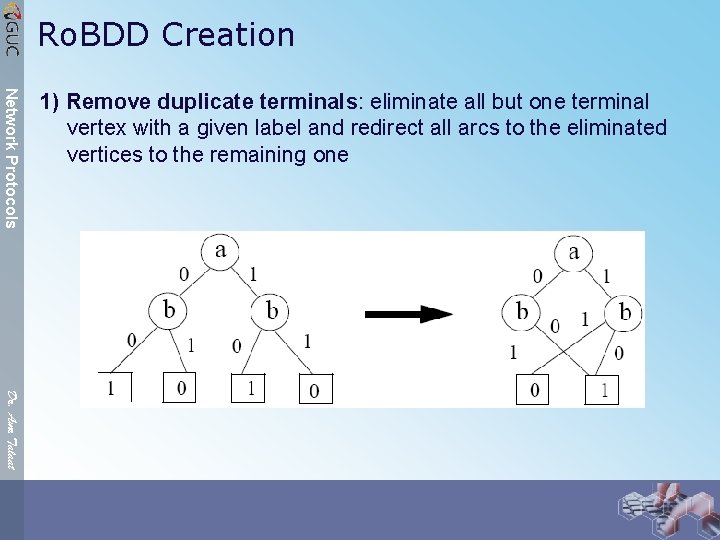
Ro. BDD Creation Network Protocols 1) Remove duplicate terminals: eliminate all but one terminal vertex with a given label and redirect all arcs to the eliminated vertices to the remaining one Dr. Amr Talaat
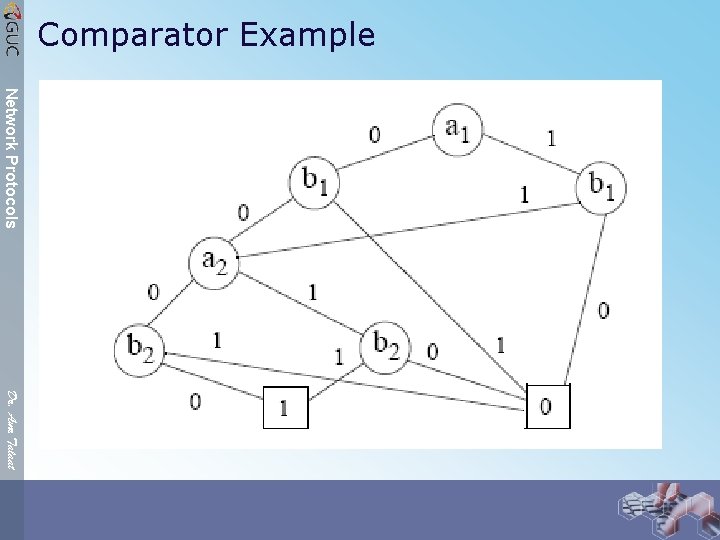
Comparator Example Network Protocols Dr. Amr Talaat
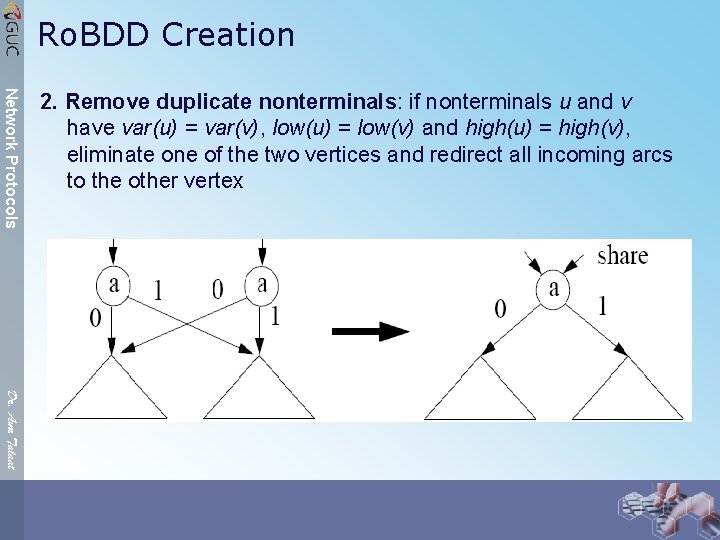
Ro. BDD Creation Network Protocols 2. Remove duplicate nonterminals: if nonterminals u and v have var(u) = var(v), low(u) = low(v) and high(u) = high(v), eliminate one of the two vertices and redirect all incoming arcs to the other vertex Dr. Amr Talaat
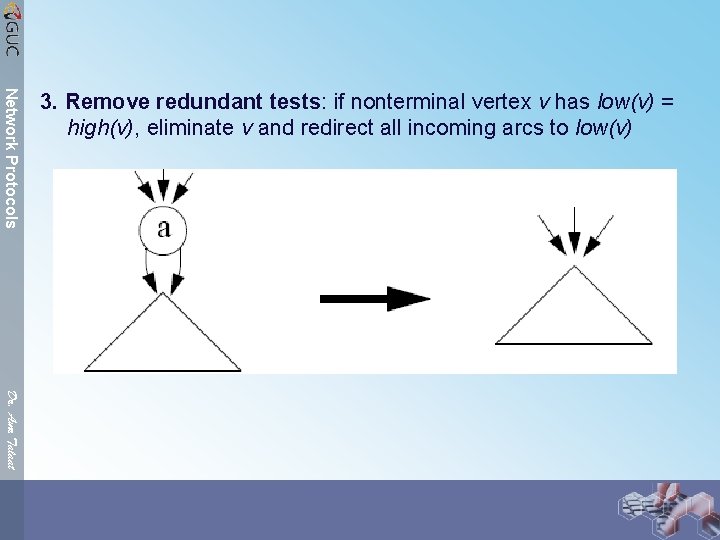
Network Protocols 3. Remove redundant tests: if nonterminal vertex v has low(v) = high(v), eliminate v and redirect all incoming arcs to low(v) Dr. Amr Talaat
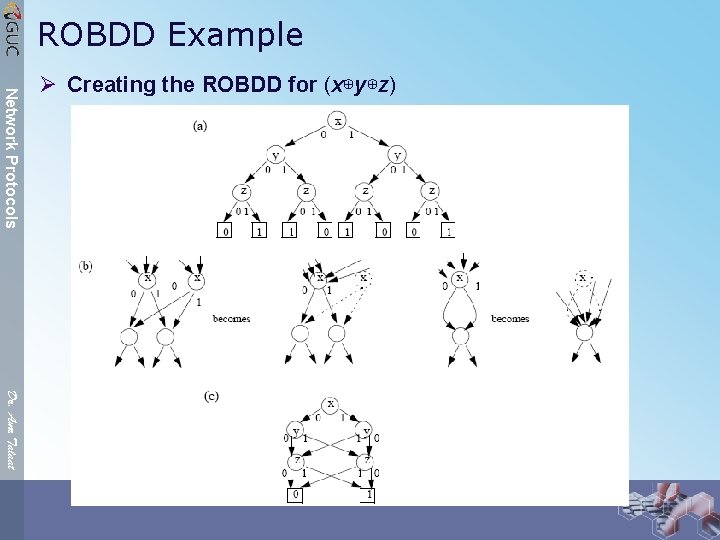
ROBDD Example Network Protocols Ø Creating the ROBDD for (x⊕y⊕z) Dr. Amr Talaat
Canonical Form Property (cont’d) Network Protocols Ø A canonical form is obtained by applying the transformation rules until no further application is possible Ø Bryant showed how this can be done by a procedure called Reduce in linear time Ø Applications: Ø checking equivalence: verify isomorphism between ROBDDs Ø non-satisfiability: verify if ROBDD has only one terminal node, labeled by 0 Ø tautology: verify if ROBDD has only one terminal node, labeled by 1 Dr. Amr Talaat
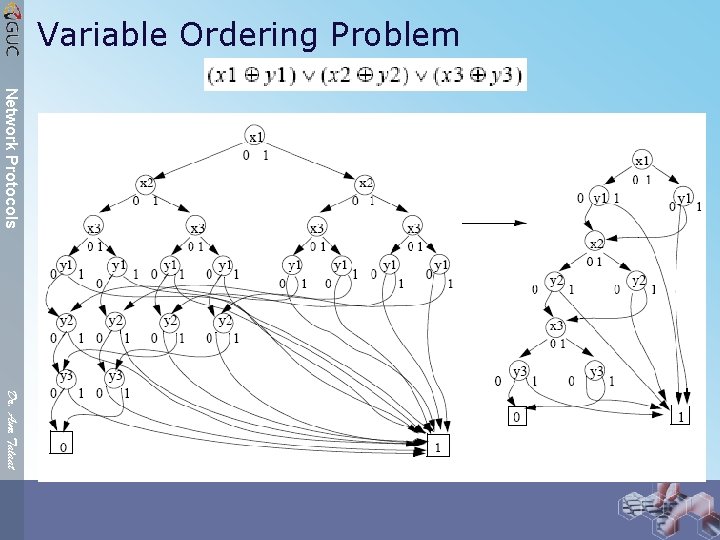
Variable Ordering Problem Network Protocols Dr. Amr Talaat
Variable Ordering Problem Network Protocols Ø The problem of finding the optimal variable order is NP-complete Ø Some Boolean functions have exponential size ROBDDs for any order (e. g. , multiplier) Ø Heuristics for Variable Ordering Ø Heuristics developed for finding a good variable order (if it exists) Ø Intuition for these heuristics comes from the observation that ROBDDs tend to be smaller when related variables are close together in the order Ø Variables appearing in a subcircuit are related: they determine the subcircuit’s output should usually be close together in the order Ø Dynamic Variable Ordering Ø Useful if no obvious static ordering heuristic applies Ø During verification operations (e. g. , reachability analysis) functions change, hence initial order is not good later on Ø Good ROBDD packages periodically internally reorder variables to reduce ROBDD size Dr. Amr Talaat Ø Basic approach based on neighboring variable exchange Ø Among a number of trials the best is taken, and the exchange is repeated
Model Checking Network Protocols Ø The Good: Ø If it works, model checking (unlike theorem proving) is a push -button tool. Ø The Bad: Ø If the system is too large, model checking cannot be applied because of state explosion. Ø & The Ugly Ø The system (and/or property) then needs to be suitably “abstracted” in order to use model checking. Dr. Amr Talaat
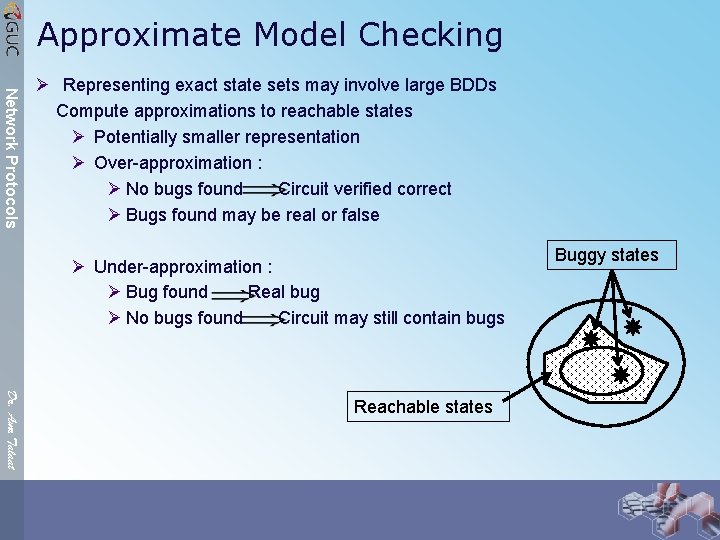
Approximate Model Checking Network Protocols Ø Representing exact state sets may involve large BDDs Compute approximations to reachable states Ø Potentially smaller representation Ø Over-approximation : Ø No bugs found Circuit verified correct Ø Bugs found may be real or false Ø Under-approximation : Ø Bug found Real bug Ø No bugs found Circuit may still contain bugs Dr. Amr Talaat Reachable states Buggy states
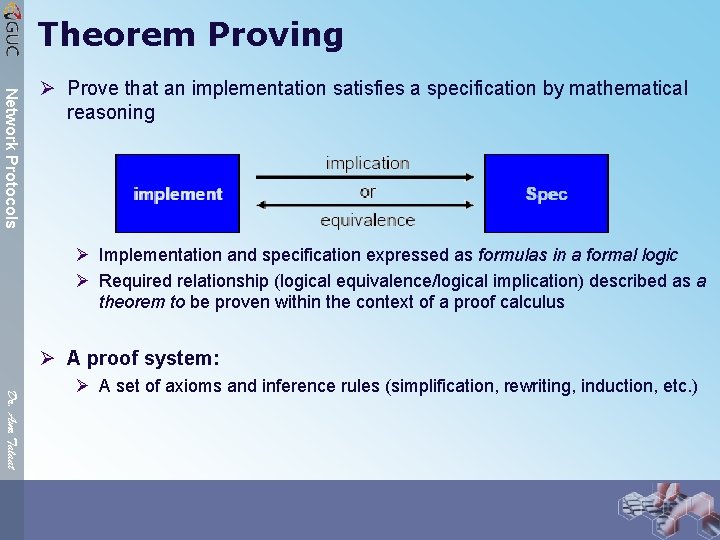
Theorem Proving Network Protocols Ø Prove that an implementation satisfies a specification by mathematical reasoning Ø Implementation and specification expressed as formulas in a formal logic Ø Required relationship (logical equivalence/logical implication) described as a theorem to be proven within the context of a proof calculus Ø A proof system: Dr. Amr Talaat Ø A set of axioms and inference rules (simplification, rewriting, induction, etc. )
Theorem Proving Idea Network Protocols Ø Properties specified in a Logical Language (SPEC) Ø System behavior also in the same language (DES) Ø Establish (DES -> SPEC) as a theorem. Ø A logical System: Ø A language defining constants, functions and predicates Ø A no. of axioms expressing properties of the constants, function, types, etc. Ø Inference Rules Ø A Theorem Ø `follows' from axioms by application of inference rules has a proof Dr. Amr Talaat
First-Order Logic Network Protocols Dr. Amr Talaat Ø Propositional logic: reasoning about complete sentences. Ø First-order logic: also reasoning about individual objects and relationships between them. Ø Syntax Ø Objects (in FOL) are denoted by expressions called terms: Ø Constants a, b, c, . . . ; Variables u, v, w, . . . ; Ø f(t 1, t 2, . . . , tn) where t 1, t 2, . . . , tn are terms and f a function symbol of n arguments Ø Predicates: Ø true (T) and false (F) Ø p(t 1, t 2, . . . , tn) where t 1, t 2, . . . , tn are terms and p a predicate symbol of n arguments
First-Order Logic (cont. ) Network Protocols Ø Formulas: Ø Predicates: ØP and Q formulas, then P, P Q, P Q are formulas Ø x a variable, P a formula, then x. P, x. Q are formulas (x is not free in P, Q) Dr. Amr Talaat
First-Order Logic (cont’d) Network Protocols Dr. Amr Talaat Ø The Validity Problem of FOL Ø To decide the validity formulas of FOL, the truth table method does not work! Ø Reason: must deal with structures not just truth assignments. Ø Structures need not be finite. . . Ø Semi-decidable (partially solvable) Ø There is an algorithm which starts with an input, and 1. if the input is valid then it terminates after a finite number of steps, and outputs the correct value (Yes or No) 2. if the input is not valid then it reaches a reject halt or loops forever Ø Theorem (Church-Turing, 1936) The validity problem formulas of FOL is undecidable, but semidecidable. Ø Some subsets of FOL are decidable.
Higher-Order Logic Network Protocols Dr. Amr Talaat Ø First-order logic: only domain variables can be quantified. Ø Second-order logic: quantification over subsets of variables (i. e. , over predicates). Ø Higher-order logics: quantification over arbitrary predicates and functions. Ø Higher-Order Logic: Ø Variables can be functions and predicates, Ø Functions and predicates can take functions as arguments and return functions as values, Ø Quantification over functions and predicates. Ø Since arguments and results of predicates and functions can themselves be predicates or functions, this imparts a first-class status to functions, and allows them to be manipulated just like ordinary values
HOL Network Protocols Ø Example 1: (mathematical induction) Ø P. [P(0) ( n. P(n) P(n+1))] n. P(n) (Impossible to express it in FOL) Ø Example 2: Function Rise defined as Rise (c, t) = c(t) c(t+1) Ø Rise expresses the notion that a signal c rises at time t. Dr. Amr Talaat
Higher-Order Logic Network Protocols Dr. Amr Talaat Ø Advantage: Ø high expressive power! Ø Disadvantages: Ø Incompleteness of a sound proof system for most higher-order logics Ø Theorem (Gödel, 1931) Ø “There is no complete deduction system for the second-order logic” Ø Inconsistencies can arise in higher-order systems if semantics not carefully defined Ø “Russell Paradox”: Ø Let P be defined by P(Q) = ¬Q(Q). Ø By substituting P for Q, leads to P(P) = ¬P(P),
Theorem Proving Systems Network Protocols Ø Some theorem proving systems: Ø Boyer-Moore (first-order logic) Ø HOL (higher-order logic) Ø PVS (higher-order logic) Ø Lambda (higher-order logic) From PVS website: Dr. Amr Talaat “PVS is a large and complex system and it takes a long while to learn to use it effectively. You should be prepared to invest six months to become a moderately skilled user”
HOL Network Protocols Ø HOL (Higher-Order Logic) developed at University of Cambridge Ø Interactive environment (in ML, Meta Language) for machine assisted theorem proving in higherorder logic (a proof assistant) Ø Steps of a proof are implemented by applying inference rules chosen by the user; HOL checks that the steps are safe Ø All inferences rules are built on top of eight primitive inference rules Ø Mechanism to carry out backward proofs by applying built-in ML functions called tactics and tacticals Ø By building complex tactics, the user can customize proof strategies Ø Numerous applications in software and hardware verification Dr. Amr Talaat
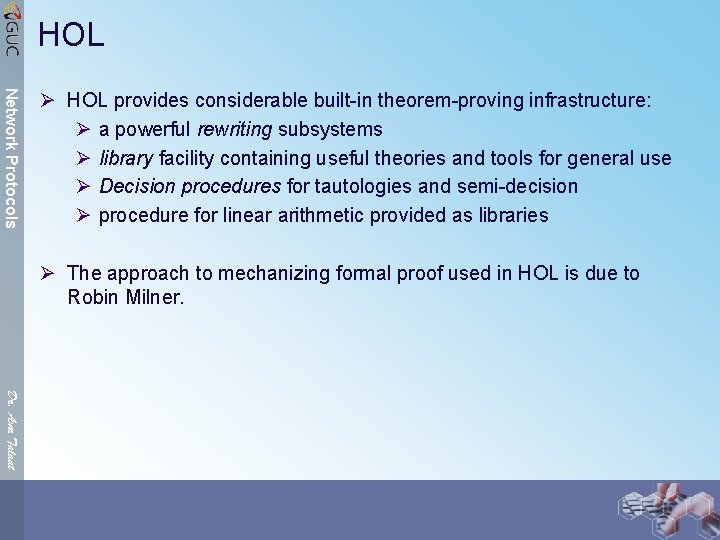
HOL Network Protocols Ø HOL provides considerable built-in theorem-proving infrastructure: Ø a powerful rewriting subsystems Ø library facility containing useful theories and tools for general use Ø Decision procedures for tautologies and semi-decision Ø procedure for linear arithmetic provided as libraries Ø The approach to mechanizing formal proof used in HOL is due to Robin Milner. Dr. Amr Talaat
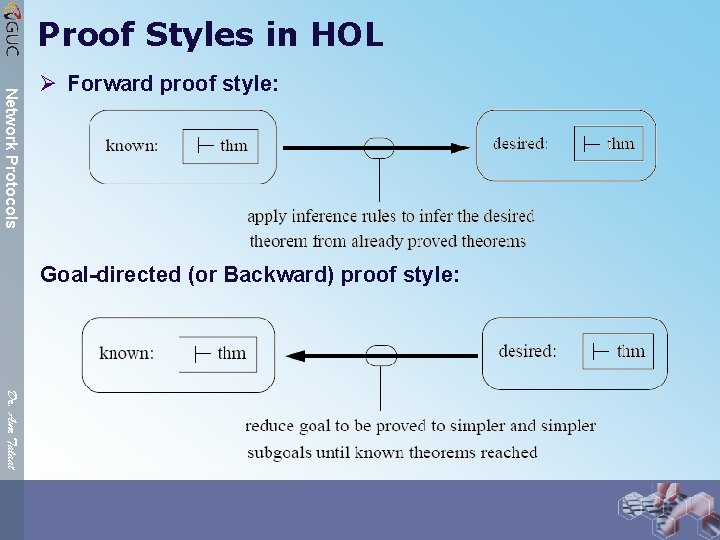
Proof Styles in HOL Network Protocols Ø Forward proof style: Goal-directed (or Backward) proof style: Dr. Amr Talaat
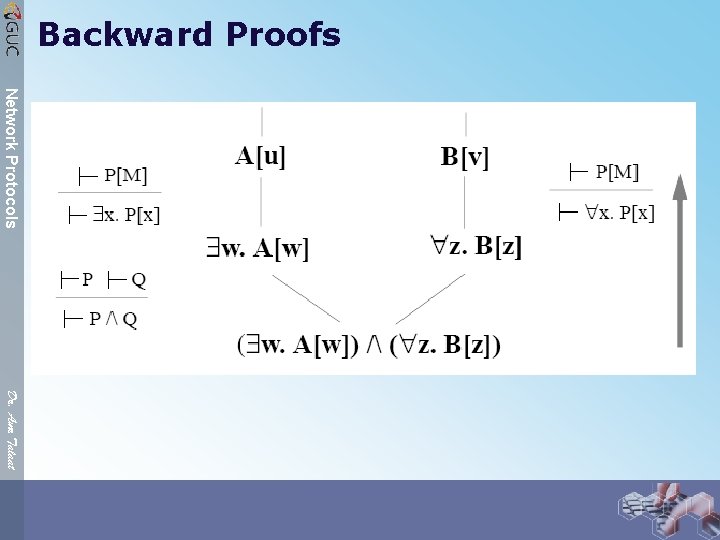
Backward Proofs Network Protocols Dr. Amr Talaat
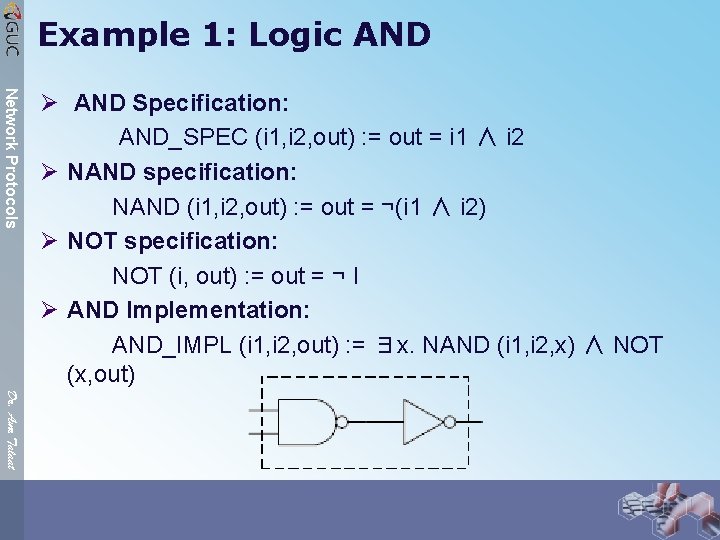
Example 1: Logic AND Network Protocols Ø AND Specification: AND_SPEC (i 1, i 2, out) : = out = i 1 ∧ i 2 Ø NAND specification: NAND (i 1, i 2, out) : = out = ¬(i 1 ∧ i 2) Ø NOT specification: NOT (i, out) : = out = ¬ I Ø AND Implementation: AND_IMPL (i 1, i 2, out) : = ∃x. NAND (i 1, i 2, x) ∧ NOT (x, out) Dr. Amr Talaat
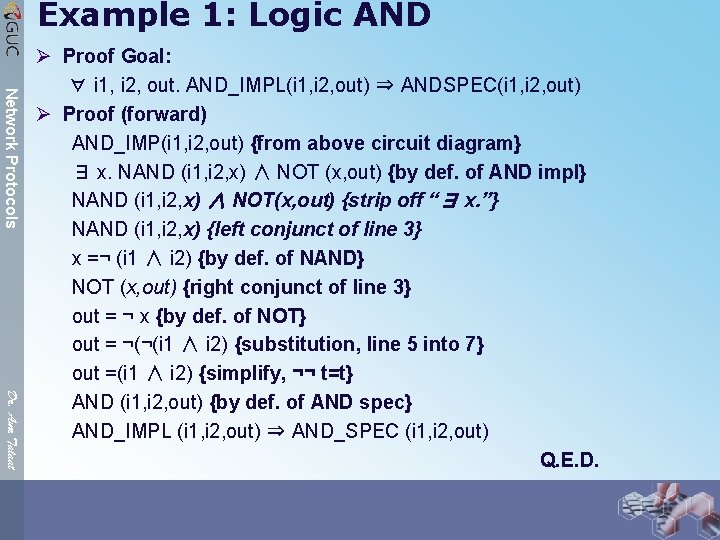
Example 1: Logic AND Network Protocols Dr. Amr Talaat Ø Proof Goal: ∀ i 1, i 2, out. AND_IMPL(i 1, i 2, out) ⇒ ANDSPEC(i 1, i 2, out) Ø Proof (forward) AND_IMP(i 1, i 2, out) {from above circuit diagram} ∃ x. NAND (i 1, i 2, x) ∧ NOT (x, out) {by def. of AND impl} NAND (i 1, i 2, x) ∧ NOT(x, out) {strip off “∃ x. ”} NAND (i 1, i 2, x) {left conjunct of line 3} x =¬ (i 1 ∧ i 2) {by def. of NAND} NOT (x, out) {right conjunct of line 3} out = ¬ x {by def. of NOT} out = ¬(¬(i 1 ∧ i 2) {substitution, line 5 into 7} out =(i 1 ∧ i 2) {simplify, ¬¬ t=t} AND (i 1, i 2, out) {by def. of AND spec} AND_IMPL (i 1, i 2, out) ⇒ AND_SPEC (i 1, i 2, out) Q. E. D.
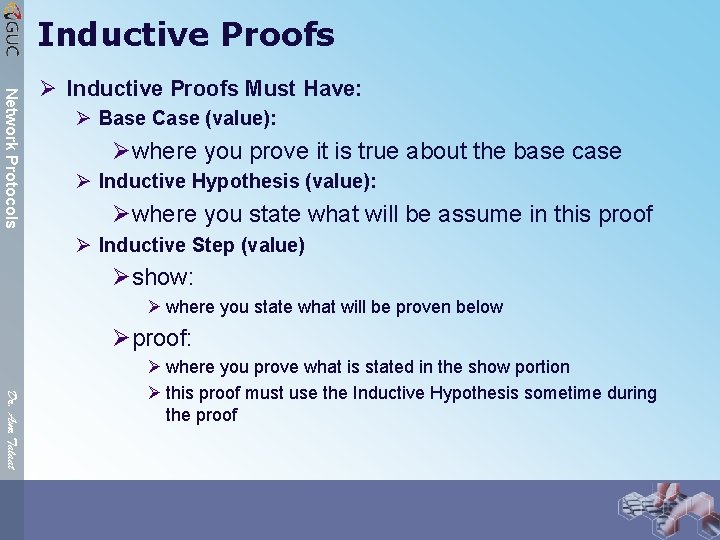
Inductive Proofs Network Protocols Ø Inductive Proofs Must Have: Ø Base Case (value): Øwhere you prove it is true about the base case Ø Inductive Hypothesis (value): Øwhere you state what will be assume in this proof Ø Inductive Step (value) Øshow: Ø where you state what will be proven below Øproof: Dr. Amr Talaat Ø where you prove what is stated in the show portion Ø this proof must use the Inductive Hypothesis sometime during the proof
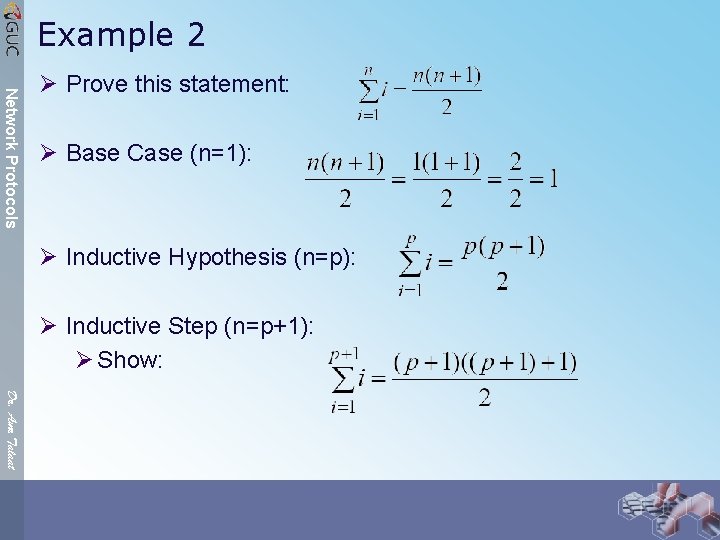
Example 2 Network Protocols Ø Prove this statement: Ø Base Case (n=1): Ø Inductive Hypothesis (n=p): Ø Inductive Step (n=p+1): Ø Show: Dr. Amr Talaat
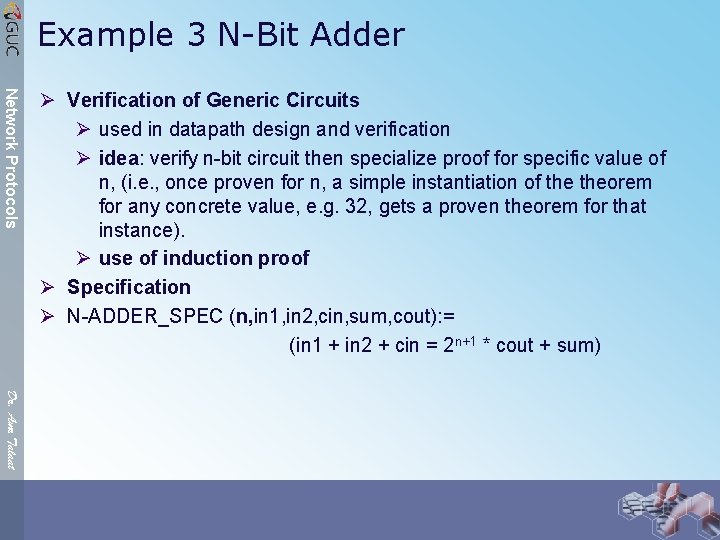
Example 3 N-Bit Adder Network Protocols Ø Verification of Generic Circuits Ø used in datapath design and verification Ø idea: verify n-bit circuit then specialize proof for specific value of n, (i. e. , once proven for n, a simple instantiation of theorem for any concrete value, e. g. 32, gets a proven theorem for that instance). Ø use of induction proof Ø Specification Ø N-ADDER_SPEC (n, in 1, in 2, cin, sum, cout): = (in 1 + in 2 + cin = 2 n+1 * cout + sum) Dr. Amr Talaat
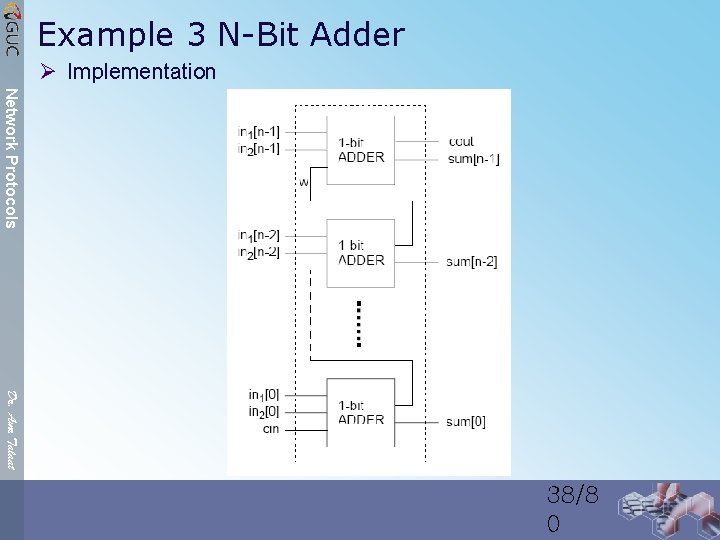
Example 3 N-Bit Adder Ø Implementation Network Protocols Dr. Amr Talaat 38/8 0
![Example 3 N-Bit Adder Network Protocols Ø Recursive Definition: N-ADDER_IMP(n, in 1[0. . n-1], Example 3 N-Bit Adder Network Protocols Ø Recursive Definition: N-ADDER_IMP(n, in 1[0. . n-1],](http://slidetodoc.com/presentation_image_h2/a1af5ec9552e959fcab7f653953d6af4/image-39.jpg)
Example 3 N-Bit Adder Network Protocols Ø Recursive Definition: N-ADDER_IMP(n, in 1[0. . n-1], in 2[0. . n-1], cin, sum[0. . n-1], cout): = ∃ w. N-ADDER_IMP(n-1, in 1[0. . n-2], in 2[0. . n-2], cin, sum[0. . n-2], w) ∧ NADDER_IMP(1, in 1[n-1], in 2[n-1], w, sum[n-1], cout) Notes: Ø N-ADDER_IMP(1, in 1[i], in 2[i], cin, sum[i], cout) = ADDER_IMP(in 1[i], in 2[i], cin, sum[i], cout) Dr. Amr Talaat Ø Data abstraction function (vn: bitvec → nat) to relate bit vectors to natural numbers: Ø vn(x[0]): = bn(x[0]) Ø vn(x[0, n]): = 2 n * bn(x[n]) + vn(x[0, n-1] 39/8 0
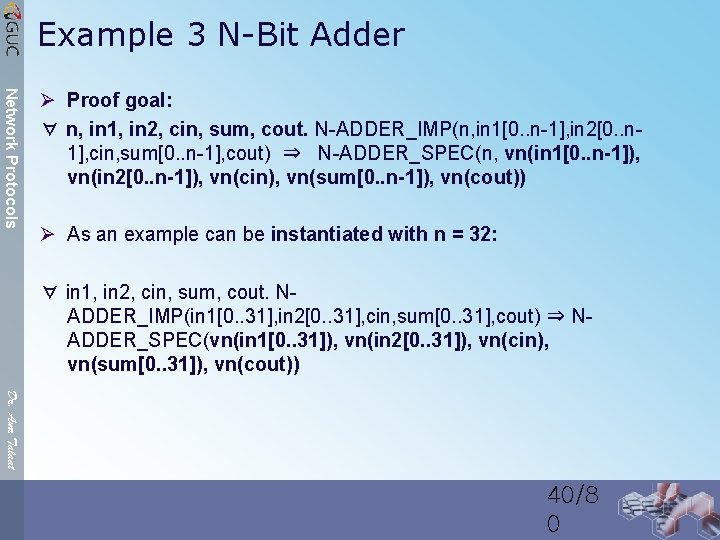
Example 3 N-Bit Adder Network Protocols Ø Proof goal: ∀ n, in 1, in 2, cin, sum, cout. N-ADDER_IMP(n, in 1[0. . n-1], in 2[0. . n 1], cin, sum[0. . n-1], cout) ⇒ N-ADDER_SPEC(n, vn(in 1[0. . n-1]), vn(in 2[0. . n-1]), vn(cin), vn(sum[0. . n-1]), vn(cout)) Ø As an example can be instantiated with n = 32: ∀ in 1, in 2, cin, sum, cout. NADDER_IMP(in 1[0. . 31], in 2[0. . 31], cin, sum[0. . 31], cout) ⇒ NADDER_SPEC(vn(in 1[0. . 31]), vn(in 2[0. . 31]), vn(cin), vn(sum[0. . 31]), vn(cout)) Dr. Amr Talaat 40/8 0
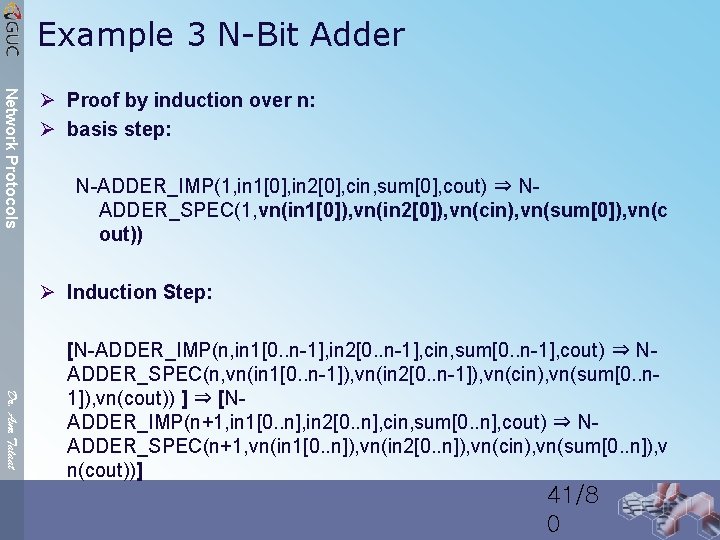
Example 3 N-Bit Adder Network Protocols Ø Proof by induction over n: Ø basis step: N-ADDER_IMP(1, in 1[0], in 2[0], cin, sum[0], cout) ⇒ NADDER_SPEC(1, vn(in 1[0]), vn(in 2[0]), vn(cin), vn(sum[0]), vn(c out)) Ø Induction Step: Dr. Amr Talaat [N-ADDER_IMP(n, in 1[0. . n-1], in 2[0. . n-1], cin, sum[0. . n-1], cout) ⇒ NADDER_SPEC(n, vn(in 1[0. . n-1]), vn(in 2[0. . n-1]), vn(cin), vn(sum[0. . n 1]), vn(cout)) ] ⇒ [NADDER_IMP(n+1, in 1[0. . n], in 2[0. . n], cin, sum[0. . n], cout) ⇒ NADDER_SPEC(n+1, vn(in 1[0. . n]), vn(in 2[0. . n]), vn(cin), vn(sum[0. . n]), v n(cout))] 41/8 0
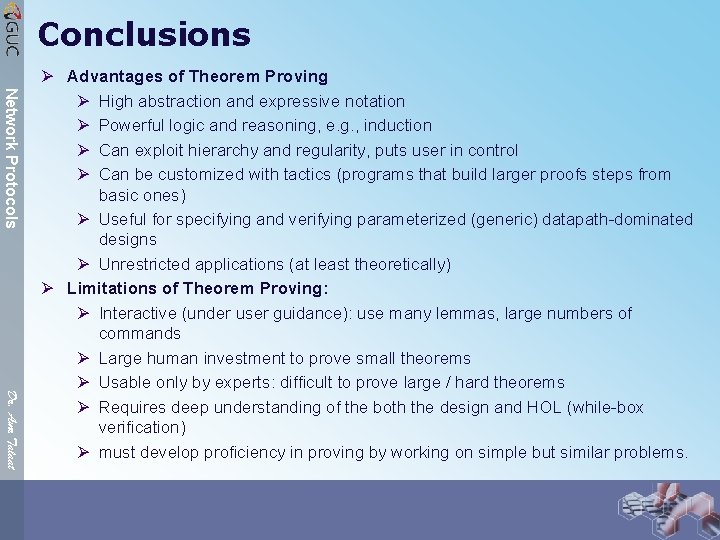
Conclusions Network Protocols Dr. Amr Talaat Ø Advantages of Theorem Proving Ø High abstraction and expressive notation Ø Powerful logic and reasoning, e. g. , induction Ø Can exploit hierarchy and regularity, puts user in control Ø Can be customized with tactics (programs that build larger proofs steps from basic ones) Ø Useful for specifying and verifying parameterized (generic) datapath-dominated designs Ø Unrestricted applications (at least theoretically) Ø Limitations of Theorem Proving: Ø Interactive (under user guidance): use many lemmas, large numbers of commands Ø Large human investment to prove small theorems Ø Usable only by experts: difficult to prove large / hard theorems Ø Requires deep understanding of the both the design and HOL (while-box verification) Ø must develop proficiency in proving by working on simple but similar problems.
We are not alone Network Protocols Theorem proving Dr. Amr Talaat Model checking Testing
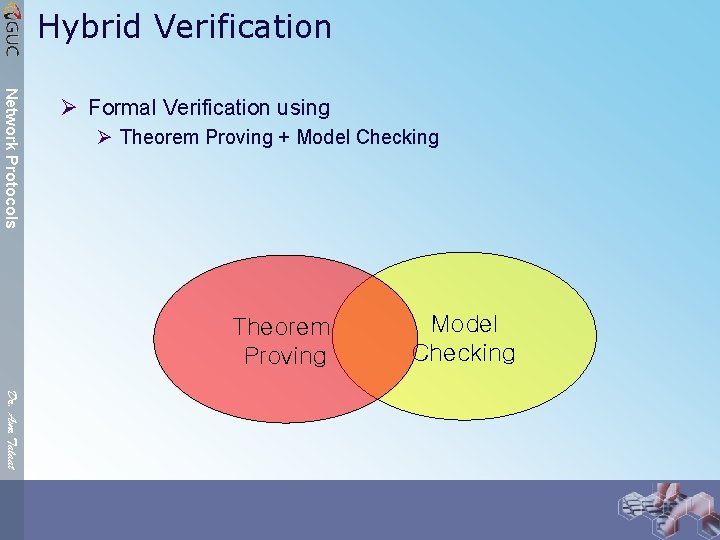
Hybrid Verification Network Protocols Ø Formal Verification using Ø Theorem Proving + Model Checking Theorem Proving Model Checking Dr. Amr Talaat
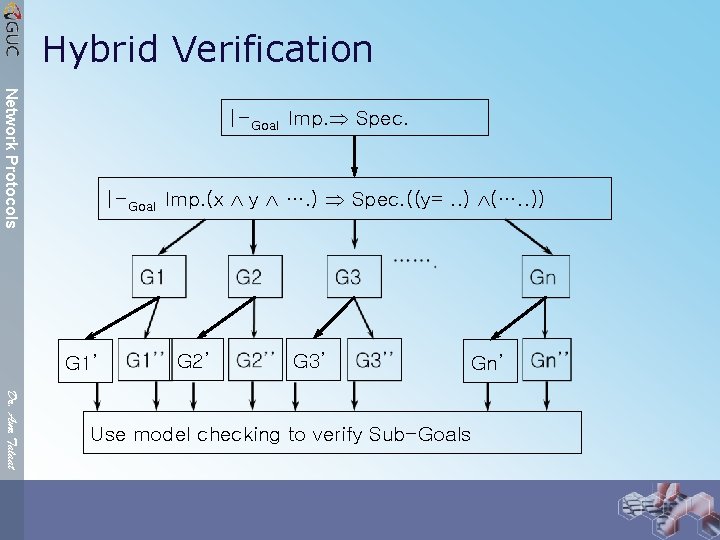
Hybrid Verification Network Protocols |-Goal Imp. Spec. |-Goal Imp. (x y …. ) Spec. ((y=. . ) (…. . )) G 1’ G 2’ G 3’ Gn’ Dr. Amr Talaat Use model checking to verify Sub-Goals
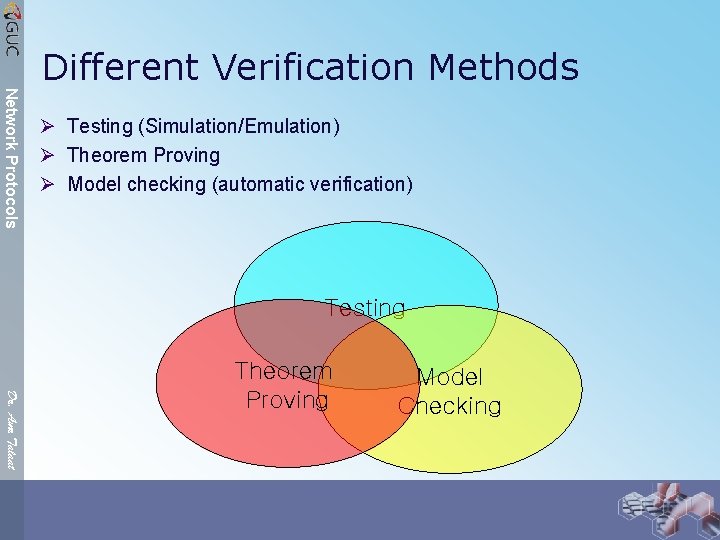
Different Verification Methods Network Protocols Ø Testing (Simulation/Emulation) Ø Theorem Proving Ø Model checking (automatic verification) Testing Dr. Amr Talaat Theorem Proving Model Checking
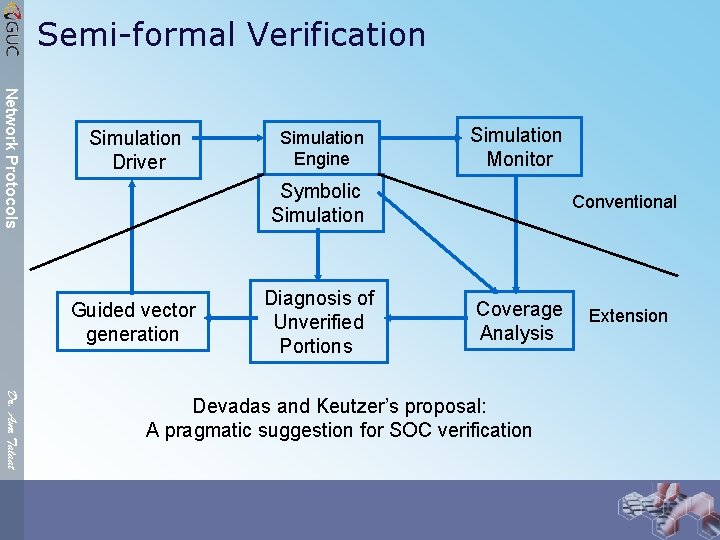
Semi-formal Verification Network Protocols Simulation Driver Simulation Engine Simulation Monitor Symbolic Simulation Guided vector generation Diagnosis of Unverified Portions Conventional Coverage Analysis Dr. Amr Talaat Devadas and Keutzer’s proposal: A pragmatic suggestion for SOC verification Extension
Semi-formal Verification Network Protocols Ø Smart simulation: Ø Use properties to generate directed test vectors. Ø Maximize chances of detecting bugs at small cost Ø Coverage metrics crucial? Ø Use metrics to determine ØUnexercised parts of design: Guide vector generation ØAdequacy of verification: When to stop? Dr. Amr Talaat
Did you find the BUG yet? Network Protocols Ø Verification and testing problem is an open question with multi-Billion $ Research per year. Ø A great Masters Research Topic Dr. Amr Talaat
A Final Proof Network Protocols Ø Ø Software engineers want to be real engineers. Real engineers use mathematics. Formal methods are the mathematics of software engineering. Therefore, software engineers should use formal methods. Mike Holloway, NASA Dr. Amr Talaat
Scientists Quotes Network Protocols “Teaching to unsuspecting youngsters the effective use of formal methods is one of the joys of life because it is so extremely rewarding” “A formula is worth a thousand pictures” Edsger Wybe Dijkstra (1930– 2002) Dr. Amr Talaat
- Slides: 51