Basic Cryptography C Edward Chow CS 691 Chapter
Basic Cryptography C. Edward Chow CS 691 – Chapter 9 of Matt Bishopz Chapter 8 of Tanenbaum cs 691 1 chow
Topics to be Covered n n n cs 691 Introduction to Cryptography l Substitution Ciphers l Transposition Ciphers l One Time Pads: Quantum Cryptography Two Fundamental Cryptographic Principles Symmetric Key Algorithms Public Key Algorithms Key Management: Digital Signatures 2 chow
Cryptography Greek words for “Secret Writing”. Cipher vs. Code 1. Cipher: a character to character or bit to bit transformation without regard to linguistic sturcture of the msg. 2. Code: replace one word woth another word or symbol. e. g. , Navajo code WWII (chay da gahi nail tsaidi(“tortoise killer). n The art of devising ciphers is called cryptography n The art of breaking ciphers is called cryptanalysis n Cryptography and cryptanalysis is collectively known as Cryptology. n n cs 691 3 chow
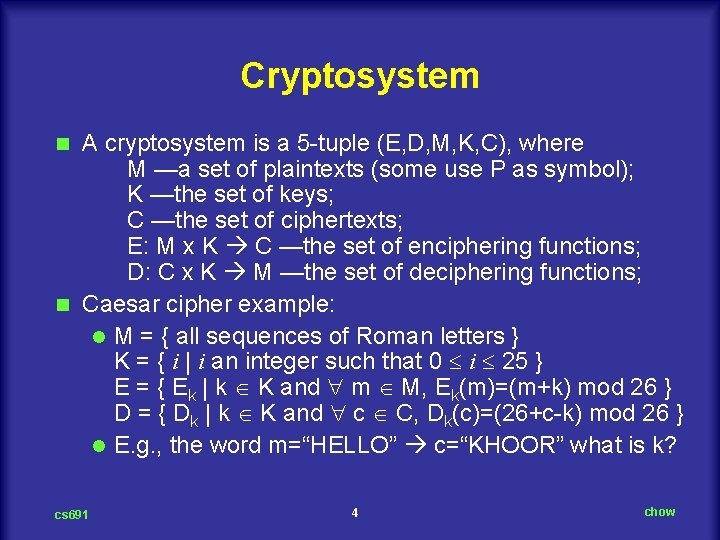
Cryptosystem A cryptosystem is a 5 tuple (E, D, M, K, C), where M —a set of plaintexts (some use P as symbol); K —the set of keys; C —the set of ciphertexts; E: M x K C —the set of enciphering functions; D: C x K M —the set of deciphering functions; n Caesar cipher example: l M = { all sequences of Roman letters } K = { i | i an integer such that 0 i 25 } E = { Ek | k K and m M, Ek(m)=(m+k) mod 26 } D = { Dk | k K and c C, Dk(c)=(26+c k) mod 26 } l E. g. , the word m=“HELLO” c=“KHOOR” what is k? n cs 691 4 chow

Encryption Model (Symmetric-Key Cipher) Adapted from Tanenbaum Computer Networks Figure 8. 2 Here P=M, and key is moved as subscript of functions. cs 691 5 chow
Basic Encryption Methods n Two categories: l Substitution Ciphers: each letter or group of letters is replaced by another letter or another group of letters. It preserves the order of the plaintext symbol but disguise them. – E. g. , Caesar cipher; mono alphabetic substitution (each letter map onto another letter; 26!=4 x 10^26 possible keys) l Transposition Ciphers: Reorder the letters but do not disguise them. – E. g. , Rail Fence cipher m=“HELLOWORLD” distribute the letter up and down between two rows from left to right; then output row wise. HLOOL c=“HLOOLELWRD” ELWRD cs 691 6 chow
Kerckhof’s Principle “All crypto algorithms must be public; only the keys are secret” “La Cryptographie Militaire, ” J. des Sciences Militaires, vol. 9, pp. 5 38, Jan. 1883 and pp. 161 191, Feb. 1883. n Trying to keep the algorithm secret (security by obscurity principle? ) never works. Reasons: l Logistic issue: Too much effort to invent, test, and install new algorithm l “Publish the algorithm and let academic cryptologists to break the system. If no one succeeded in 5 years, it must be pretty solid. ” n Real secrecy in the key, its length a major design issue cs 691 7 chow
Key Length and Work Factor n n n 2 digit key 100 combinations. 6 digit key 1 million combinations. 64 bit keys to prevent kid brother from reading your email. 128 bit keys for routine commercial use >256 bits keep major governments at bay. cs 691 8 chow
3 Variations of Cryptoanalysis or Cipher Attacks Ciphertext only: cryptoanalyst has some ciphertext; no (does not know the corresponding) plaintext; no key; no E or D functions. n Known plaintext: some matched ciphertext and plaintext. (no key; may/may not know the E or D functions) n Chosen plaintext: has the ability to encrypt pieces of plaintext of his own choosing. (know the E or D function; does not know the keys used). n cs 691 9 chow
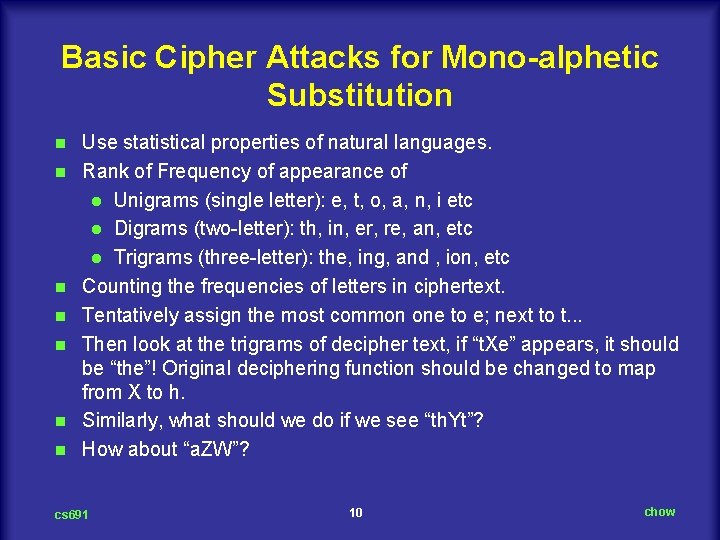
Basic Cipher Attacks for Mono-alphetic Substitution n n n Use statistical properties of natural languages. Rank of Frequency of appearance of l Unigrams (single letter): e, t, o, a, n, i etc l Digrams (two letter): th, in, er, re, an, etc l Trigrams (three letter): the, ing, and , ion, etc Counting the frequencies of letters in ciphertext. Tentatively assign the most common one to e; next to t. . . Then look at the trigrams of decipher text, if “t. Xe” appears, it should be “the”! Original deciphering function should be changed to map from X to h. Similarly, what should we do if we see “th. Yt”? How about “a. ZW”? cs 691 10 chow
Cipher Attack: Guess a Probable Word n n n Ciphertext from accounting firm CTBMN BYCTC BTJDS QXBNS GSTJC BTSWX CTQTZ CQVUJ QJSGS TJQZZ MNQJS VLNSX VSZJU JDSTS JQUUS JUBXJ DSKSU JSNTK BGAQJ ZBGYQ TLCTZ BNYBN QJSW A likely word is financial. Based on two i are separated by four letters, we look for same pattern in ciphertext. There are 12 hits, position 6, 15, 27, 31, 42, 48, 56. 66, 70, 71, 76, and 82. Only 31 and 42 has the next letter n (ana) separated by one letter. i C and J; n T and S respectively. cs 691 11 chow
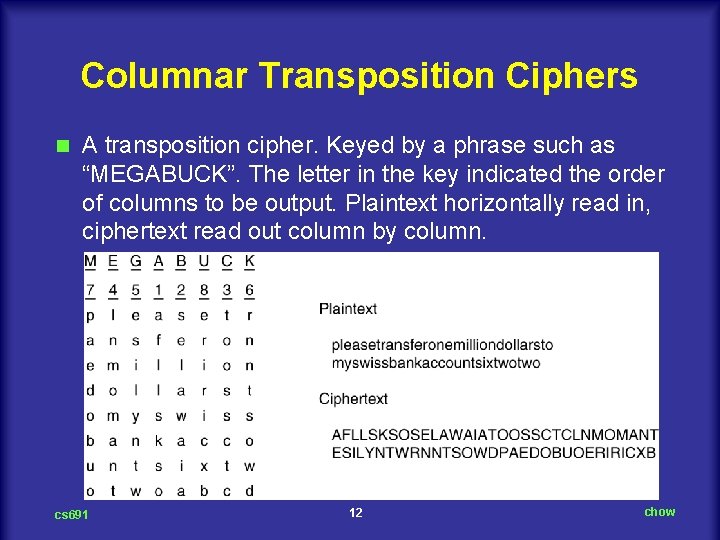
Columnar Transposition Ciphers n A transposition cipher. Keyed by a phrase such as “MEGABUCK”. The letter in the key indicated the order of columns to be output. Plaintext horizontally read in, ciphertext read out column by column. cs 691 12 chow
Breaking Transposition Cipher n n n Check if the frequency distribution of unigrams are the same in the ciphertext. If it is, then this is a transposition cipher. Guess the number of columns. Assume we suspect “milliondollars” appear in ciphertext Analyze keylength: Observe digrams MO, IL, LA, IR, and OS in ciphertext as wrapping around effect keylength = 8. Analyze order of columns. If keylength is small, column pairs (k(k 1) of them) of ciphertext can be examined and see if the patterns of digrams in the deciphered text match those of the language frequency distribution. cs 691 13 chow
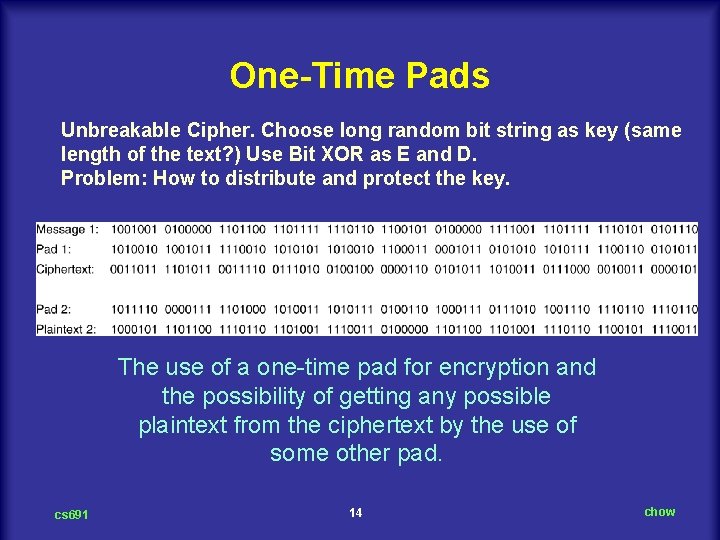
One-Time Pads Unbreakable Cipher. Choose long random bit string as key (same length of the text? ) Use Bit XOR as E and D. Problem: How to distribute and protect the key. The use of a one time pad for encryption and the possibility of getting any possible plaintext from the ciphertext by the use of some other pad. cs 691 14 chow
Quantum Cryptography n n n cs 691 Can be used to transfer one time pad over networks. Here Fiber channel is assumed. Light comes as little packets called Photons can be polarized using filter such as sunglass. The photons after the polarized filters will be polarized in the direction of the filter’s axis. If the beam goes through the 2 nd filter and 1. the two filters are perpendicular, no photons get through. 2. The light intensity after the 2 n filter is proportion to the square of the cosine of the angle between the two filter axes. 15 chow
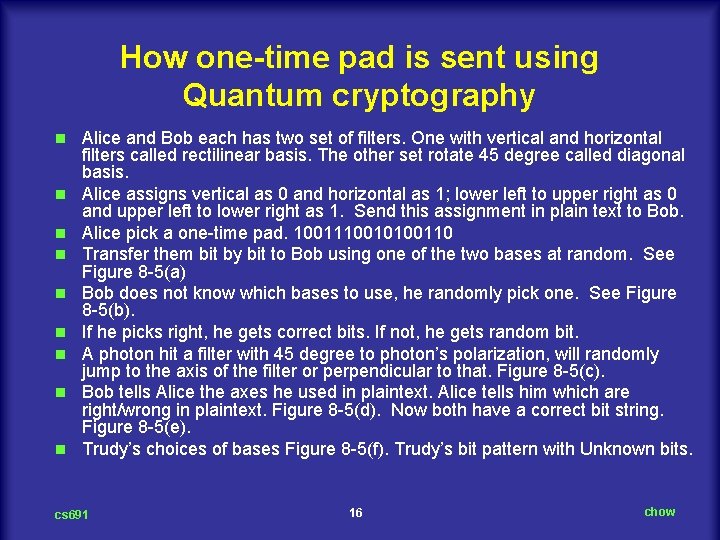
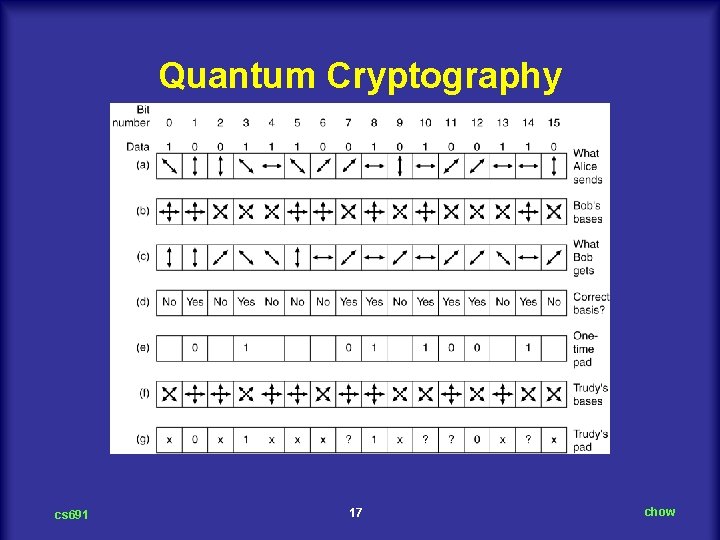
How one-time pad is sent using Quantum cryptography n n n n n Alice and Bob each has two set of filters. One with vertical and horizontal filters called rectilinear basis. The other set rotate 45 degree called diagonal basis. Alice assigns vertical as 0 and horizontal as 1; lower left to upper right as 0 and upper left to lower right as 1. Send this assignment in plain text to Bob. Alice pick a one time pad. 1001110010100110 Transfer them bit by bit to Bob using one of the two bases at random. See Figure 8 5(a) Bob does not know which bases to use, he randomly pick one. See Figure 8 5(b). If he picks right, he gets correct bits. If not, he gets random bit. A photon hit a filter with 45 degree to photon’s polarization, will randomly jump to the axis of the filter or perpendicular to that. Figure 8 5(c). Bob tells Alice the axes he used in plaintext. Alice tells him which are right/wrong in plaintext. Figure 8 5(d). Now both have a correct bit string. Figure 8 5(e). Trudy’s choices of bases Figure 8 5(f). Trudy’s bit pattern with Unknown bits. cs 691 16 chow
Quantum Cryptography cs 691 17 chow
Two Fundamental Cryptographic Principles Redundancy: Messages must contains some redundancy. l E. g. , Last three bytes of encrypted packet content are product # and quantity. l Recent fired employee can capture the packet replace the last three byte quantity field with a random number. l How redundancy can help? n Freshness Some method is needed to foil replay attacks. l How to defense reply attacks? Timestamp alone? n cs 691 18 chow
Symmetric-Key Algorithms n DES – The Data Encryption Standard n AES – The Advanced Encryption Standard n Cipher Modes n Other Ciphers n Cryptanalysis cs 691 19 chow
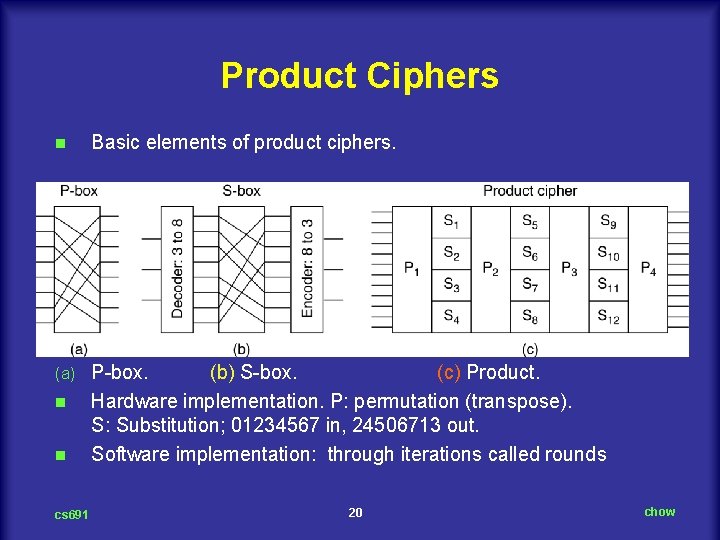
Product Ciphers n Basic elements of product ciphers. (a) P box. (b) S box. (c) Product. Hardware implementation. P: permutation (transpose). S: Substitution; 01234567 in, 24506713 out. Software implementation: through iterations called rounds n n cs 691 20 chow
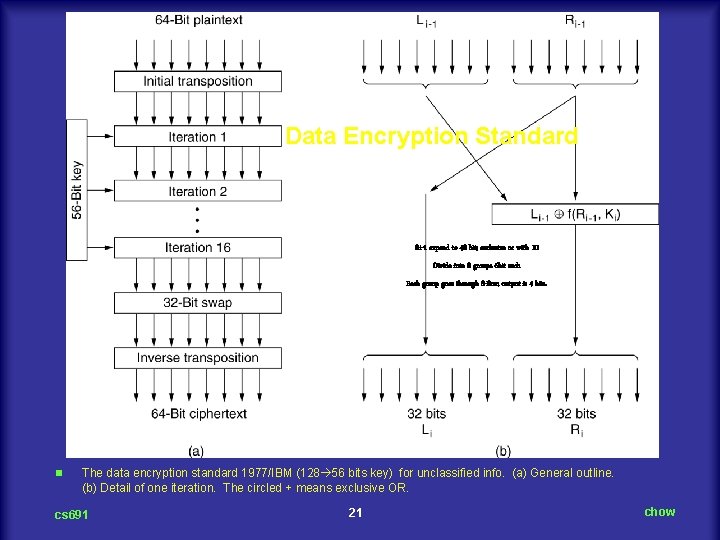
Data Encryption Standard Ri-1 expand to 48 bit; exclusive or with Ki Divide into 8 groups 6 bit each Each group goes through S-Box; output is 4 bits. n The data encryption standard 1977/IBM (128 56 bits key) for unclassified info. (a) General outline. (b) Detail of one iteration. The circled + means exclusive OR. cs 691 21 chow
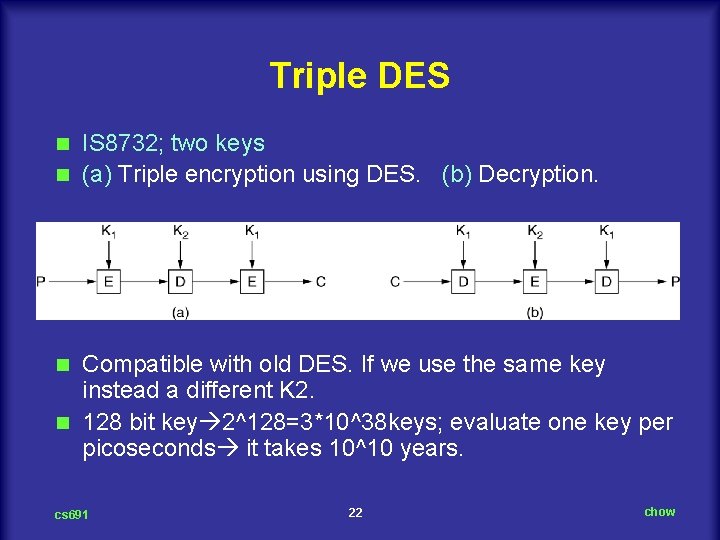
Triple DES IS 8732; two keys n (a) Triple encryption using DES. (b) Decryption. n Compatible with old DES. If we use the same key instead a different K 2. n 128 bit key 2^128=3*10^38 keys; evaluate one key per picoseconds it takes 10^10 years. n cs 691 22 chow
AES – The Advanced Encryption Standard n 1. 2. 3. 4. 5. n Rules for AES proposals The algorithm must be a symmetric block cipher. The full design must be public. Key lengths of 128, 192, and 256 bits supported. Both software and hardware implementations required The algorithm must be public or licensed on nondiscriminatory terms. http: //csrc. nist. gov/Crypto. Toolkit/aes/rijndael/ cs 691 23 chow
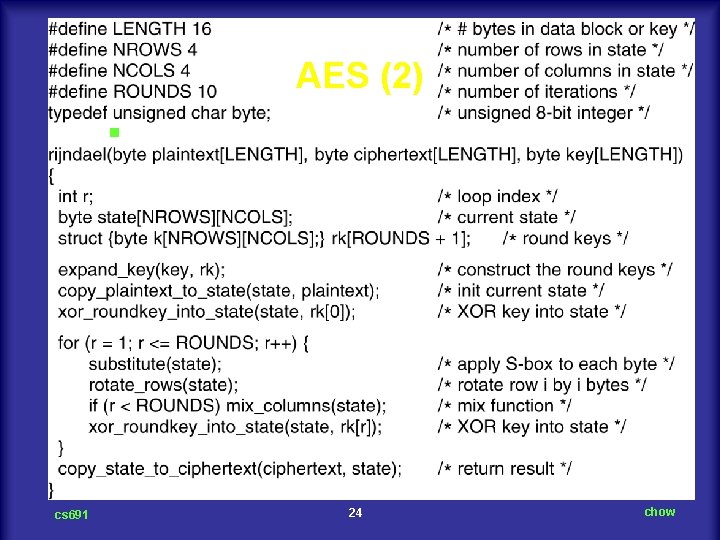
AES (2) n cs 691 An outline of Rijndael, by Joan Daemen and Vincent Rijmen 86 votes 24 chow
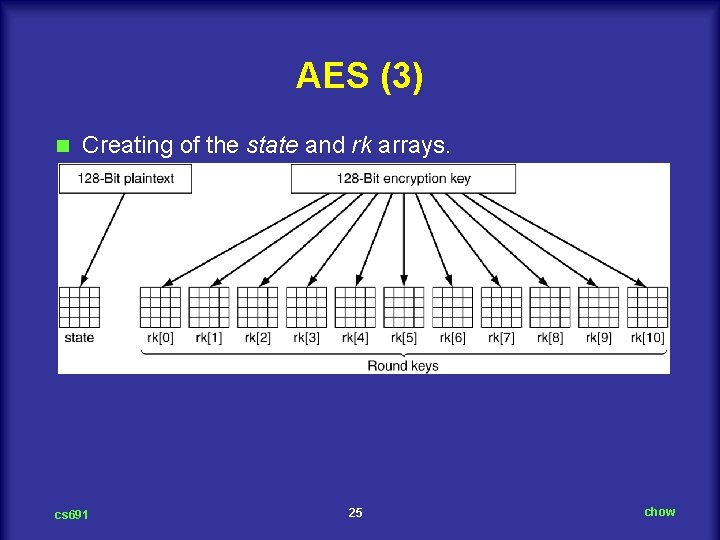
AES (3) n Creating of the state and rk arrays. cs 691 25 chow
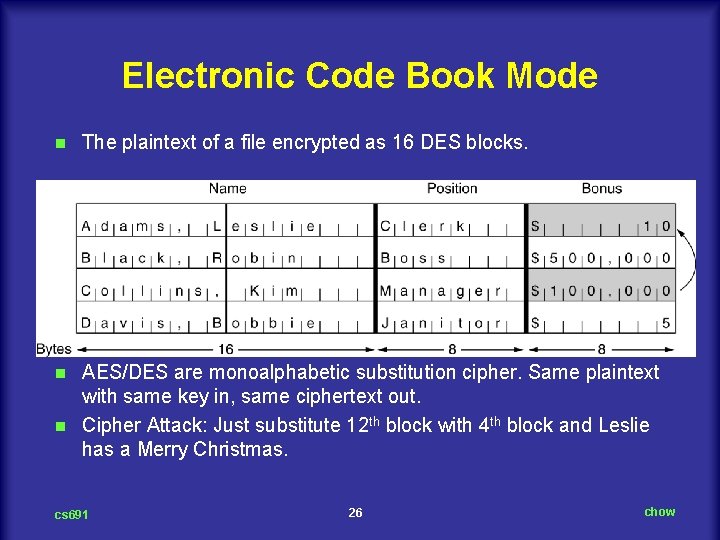
Electronic Code Book Mode n The plaintext of a file encrypted as 16 DES blocks. AES/DES are monoalphabetic substitution cipher. Same plaintext with same key in, same ciphertext out. n Cipher Attack: Just substitute 12 th block with 4 th block and Leslie has a Merry Christmas. n cs 691 26 chow
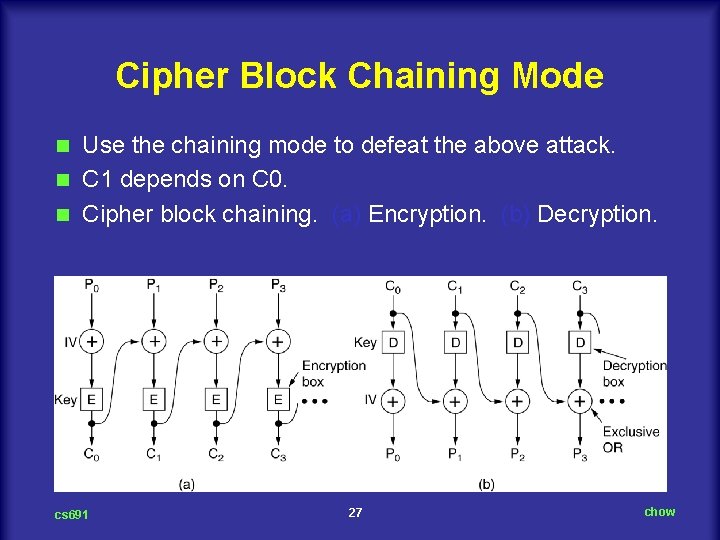
Cipher Block Chaining Mode Use the chaining mode to defeat the above attack. n C 1 depends on C 0. n Cipher block chaining. (a) Encryption. (b) Decryption. n cs 691 27 chow
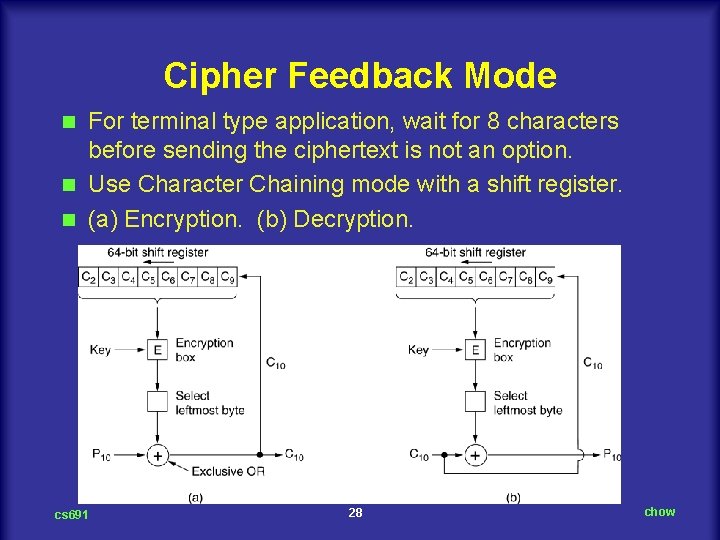
Cipher Feedback Mode For terminal type application, wait for 8 characters before sending the ciphertext is not an option. n Use Character Chaining mode with a shift register. n (a) Encryption. (b) Decryption. n cs 691 28 chow
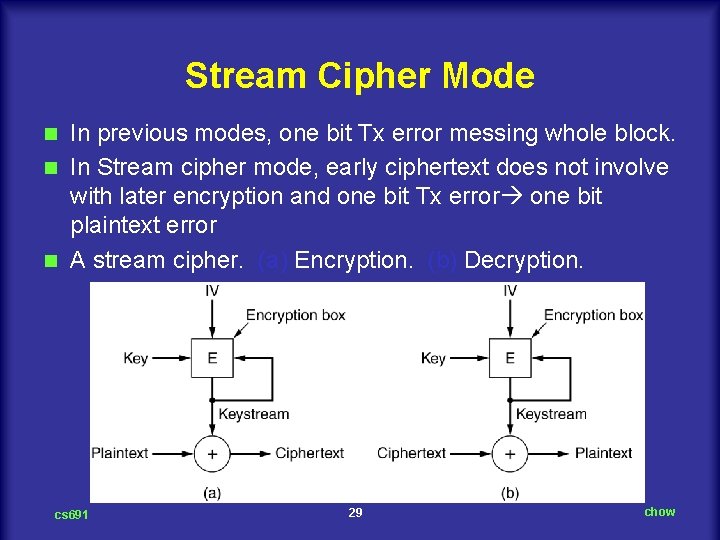
Stream Cipher Mode In previous modes, one bit Tx error messing whole block. n In Stream cipher mode, early ciphertext does not involve with later encryption and one bit Tx error one bit plaintext error n A stream cipher. (a) Encryption. (b) Decryption. n cs 691 29 chow
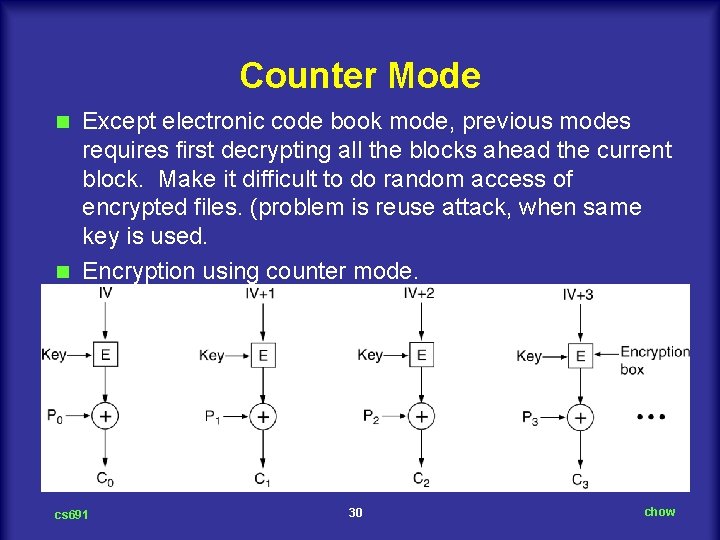
Counter Mode Except electronic code book mode, previous modes requires first decrypting all the blocks ahead the current block. Make it difficult to do random access of encrypted files. (problem is reuse attack, when same key is used. n Encryption using counter mode. n cs 691 30 chow
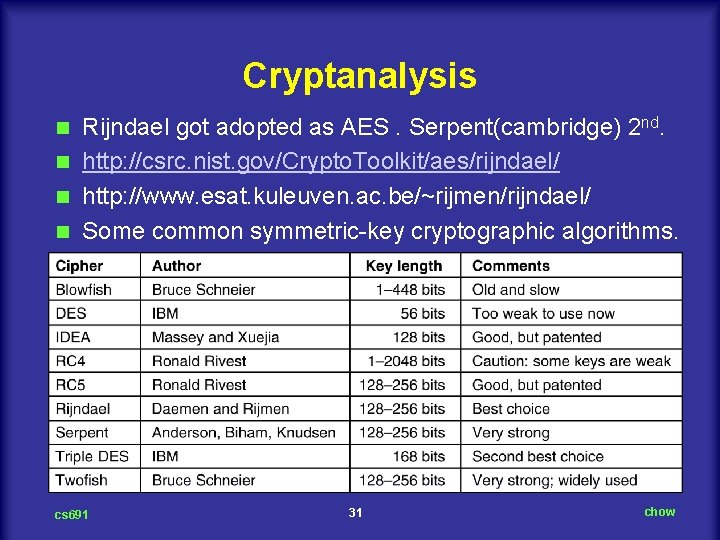
Cryptanalysis Rijndael got adopted as AES. Serpent(cambridge) 2 nd. n http: //csrc. nist. gov/Crypto. Toolkit/aes/rijndael/ n http: //www. esat. kuleuven. ac. be/~rijmen/rijndael/ n Some common symmetric key cryptographic algorithms. n cs 691 31 chow
Public-Key Algorithms 1976 Dillfie and Hellman proposed crypto scheme with two keys; public key and private key. Requirement: l Must be computationally easy to encipher/decipher msg using these keys. l Must be computationally infeasible to derive the private key from public key. l Mulst be computationally infeasible to determine the private key from a chosen plaintext attack. n Symmetric key exchange protocol n RSA n Other Public Key Algorithms n cs 691 32 chow
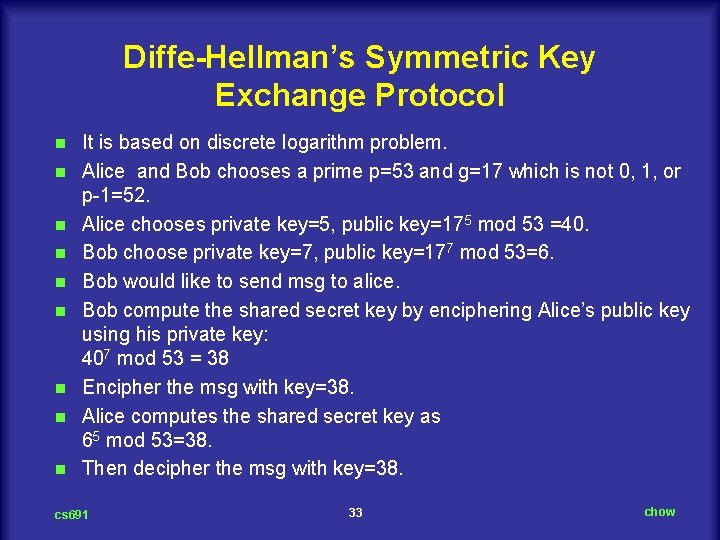
Diffe-Hellman’s Symmetric Key Exchange Protocol n n n n n It is based on discrete logarithm problem. Alice and Bob chooses a prime p=53 and g=17 which is not 0, 1, or p 1=52. Alice chooses private key=5, public key=175 mod 53 =40. Bob choose private key=7, public key=177 mod 53=6. Bob would like to send msg to alice. Bob compute the shared secret key by enciphering Alice’s public key using his private key: 407 mod 53 = 38 Encipher the msg with key=38. Alice computes the shared secret key as 65 mod 53=38. Then decipher the msg with key=38. cs 691 33 chow
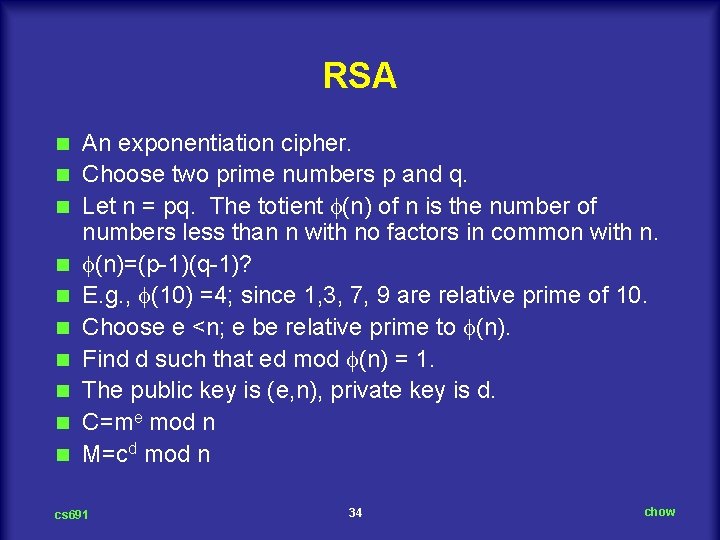
RSA n n n n n An exponentiation cipher. Choose two prime numbers p and q. Let n = pq. The totient (n) of n is the number of numbers less than n with no factors in common with n. (n)=(p 1)(q 1)? E. g. , (10) =4; since 1, 3, 7, 9 are relative prime of 10. Choose e <n; e be relative prime to (n). Find d such that ed mod (n) = 1. The public key is (e, n), private key is d. C=me mod n M=cd mod n cs 691 34 chow
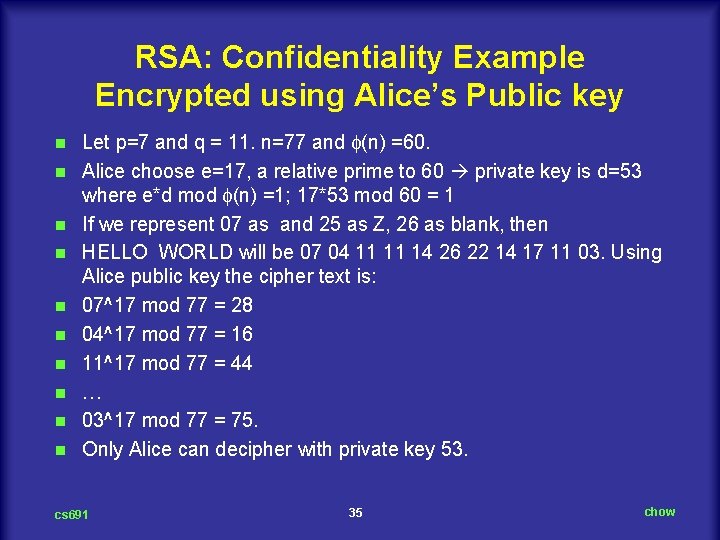
RSA: Confidentiality Example Encrypted using Alice’s Public key n n n n n Let p=7 and q = 11. n=77 and (n) =60. Alice choose e=17, a relative prime to 60 private key is d=53 where e*d mod (n) =1; 17*53 mod 60 = 1 If we represent 07 as and 25 as Z, 26 as blank, then HELLO WORLD will be 07 04 11 11 14 26 22 14 17 11 03. Using Alice public key the cipher text is: 07^17 mod 77 = 28 04^17 mod 77 = 16 11^17 mod 77 = 44 … 03^17 mod 77 = 75. Only Alice can decipher with private key 53. cs 691 35 chow
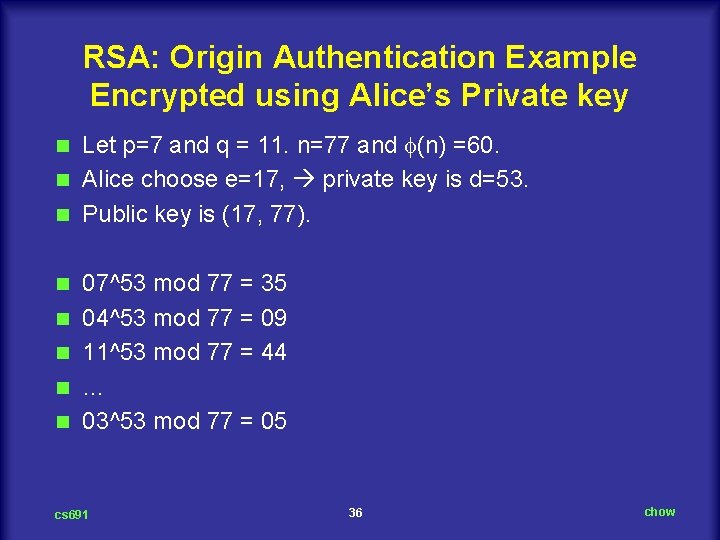
RSA: Origin Authentication Example Encrypted using Alice’s Private key Let p=7 and q = 11. n=77 and (n) =60. n Alice choose e=17, private key is d=53. n Public key is (17, 77). n n n 07^53 mod 77 = 35 04^53 mod 77 = 09 11^53 mod 77 = 44 … 03^53 mod 77 = 05 cs 691 36 chow
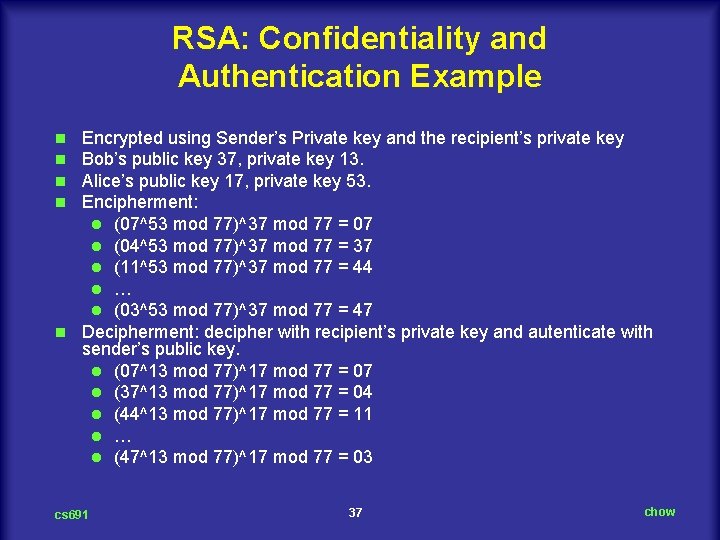
RSA: Confidentiality and Authentication Example Encrypted using Sender’s Private key and the recipient’s private key Bob’s public key 37, private key 13. Alice’s public key 17, private key 53. Encipherment: l (07^53 mod 77)^37 mod 77 = 07 l (04^53 mod 77)^37 mod 77 = 37 l (11^53 mod 77)^37 mod 77 = 44 l … l (03^53 mod 77)^37 mod 77 = 47 n Decipherment: decipher with recipient’s private key and autenticate with sender’s public key. l (07^13 mod 77)^17 mod 77 = 07 l (37^13 mod 77)^17 mod 77 = 04 l (44^13 mod 77)^17 mod 77 = 11 l … l (47^13 mod 77)^17 mod 77 = 03 n n cs 691 37 chow
RSA Cipher Attack/Defense Example Simplified example, character as block. NO can be swapped and interpreted as ON. (Attack is on or not? ) n Defense: 6 bits for block # followed by 8 bit character. The rest 1010 bits contains random data. Rearrange of blocks can be detected by checking the block # field. n This is an application of the Redundancy principle. n cs 691 38 chow
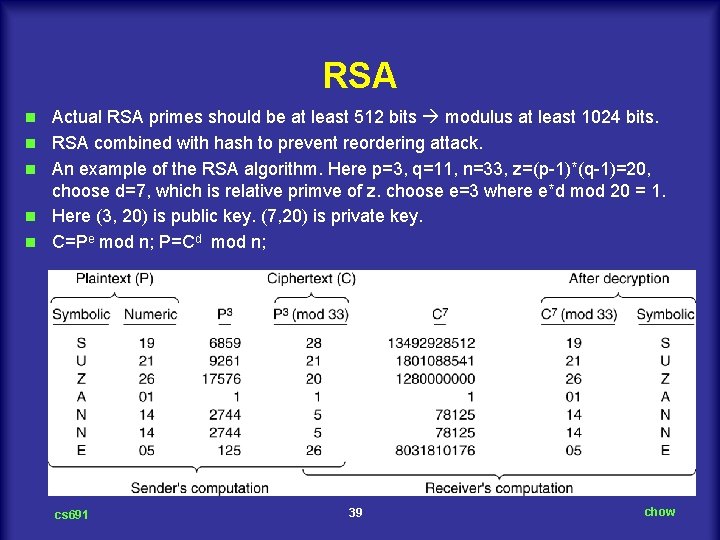
RSA n n n Actual RSA primes should be at least 512 bits modulus at least 1024 bits. RSA combined with hash to prevent reordering attack. An example of the RSA algorithm. Here p=3, q=11, n=33, z=(p 1)*(q 1)=20, choose d=7, which is relative primve of z. choose e=3 where e*d mod 20 = 1. Here (3, 20) is public key. (7, 20) is private key. C=Pe mod n; P=Cd mod n; cs 691 39 chow
Digital Signatures n Symmetric Key Signatures n Public Key Signatures n Message Digests n The Birthday Attack cs 691 40 chow
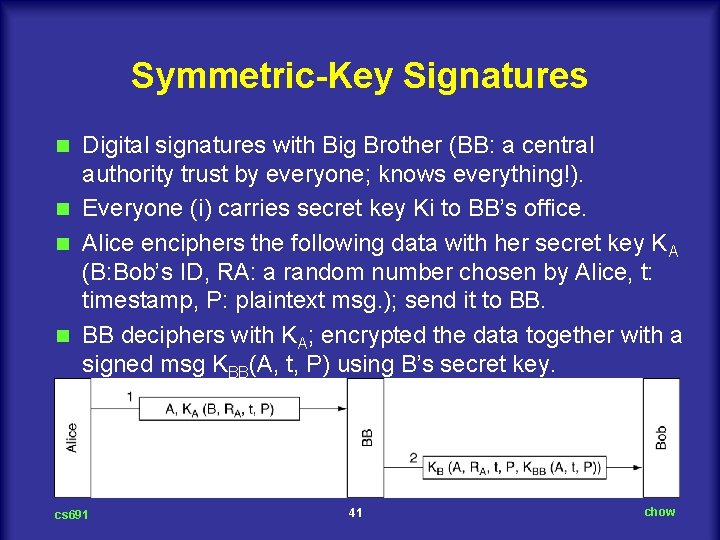
Symmetric-Key Signatures Digital signatures with Big Brother (BB: a central authority trust by everyone; knows everything!). n Everyone (i) carries secret key Ki to BB’s office. n Alice enciphers the following data with her secret key KA (B: Bob’s ID, RA: a random number chosen by Alice, t: timestamp, P: plaintext msg. ); send it to BB. n BB deciphers with KA; encrypted the data together with a signed msg KBB(A, t, P) using B’s secret key. n cs 691 41 chow
Symmetric-Key Signatures: Nonrepudiation and Against Relay Attack BB will not accept a msg from Alice unless it is encrypted with KA. n KBB(A, t, P) contains the proof that A sent P at time t. n Against replay attack: l Againstant replay: Within some time period, Bob can check if RA has been reuse; drop those packet. l Against old replay: Based on the timestamp, Bob can discard old messages. n Disadvantage: l BB needs to be trusted by everyone. l BB gets to read all signed msgs. n cs 691 42 chow
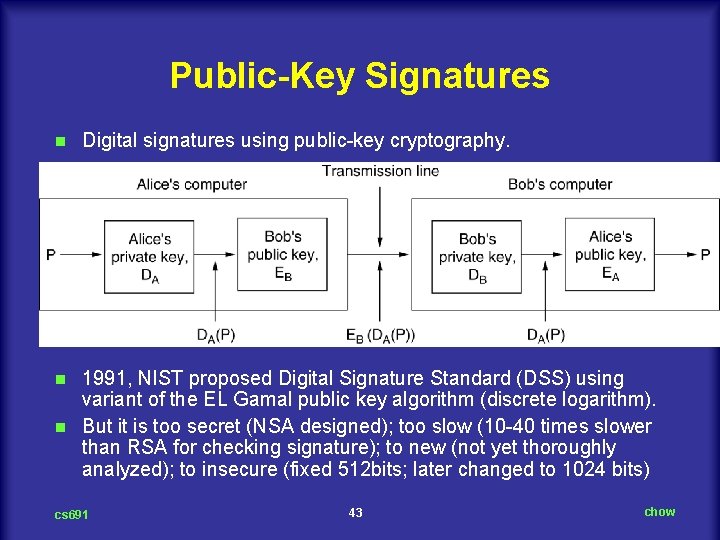
Public-Key Signatures n Digital signatures using public key cryptography. 1991, NIST proposed Digital Signature Standard (DSS) using variant of the EL Gamal public key algorithm (discrete logarithm). n But it is too secret (NSA designed); too slow (10 40 times slower than RSA for checking signature); to new (not yet thoroughly analyzed); to insecure (fixed 512 bits; later changed to 1024 bits) n cs 691 43 chow
Message Digests Authentication without encrypting the entire msg. n 4 properties of Message Digest (MD hash function: arbitrarily long plaintext fixed length bit string. l Given P, it is easy to compute MD(P). l Given MD(P), it is effectively impossible to find P. l Given P no one can find P’ such that MD(P’)=MD(P). l A change to the input of even 1 bit produces a very different output. n For example, Instead of KBB(A, t, P) , we have KBB(A, t, MD(P)) n n Digital signatures using message digests. cs 691 44 chow
MD 5 n n n Designed by Ronald Rivest 1992. 5 th of a series of MD. Pre computation Step: l First pad the msg a length of 448 bits (mod 512). l Original msg is then appended with 64 bit integer; make it a multiple of 512 bits. l Initialize 128 bit buffer to a fixed value. Computation step: l Take 512 bit block of input, perform 4 round of mixing, thoroughly with 128 bit buffer (with sine function and table look up) l Process continues until all input consume. The content of 128 bit buffer form the message digest. You can access it on our CS Unix machines using Open. SSL pacckage “openssl md 5” For example, the following yield a pretty good random key: bash 2. 05 a# (date; ps auxg) | openssl md 5 7741348 ddf 1371 aefc 921 d 504 fa 51 e 6 a bash 2. 05 a# (date; ps auxg) | openssl md 5 7 c 56744 bb 2440 abcc 2 de 7 a 492 ae 32 d 06 cs 691 45 chow
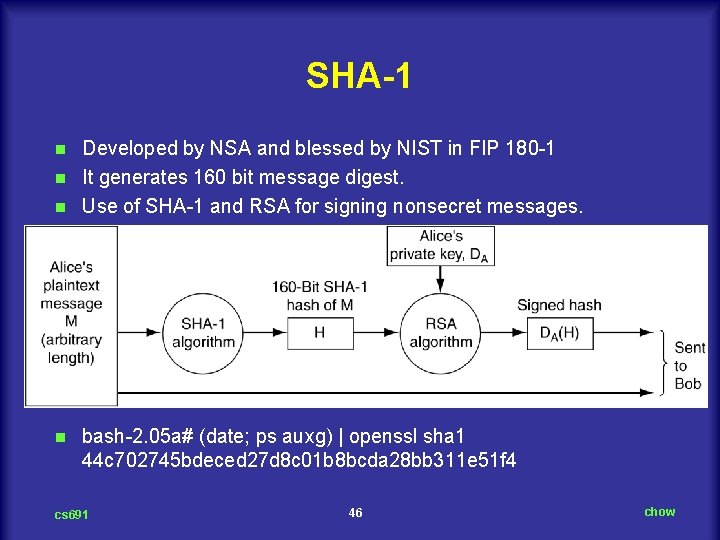
SHA-1 Developed by NSA and blessed by NIST in FIP 180 1 n It generates 160 bit message digest. n Use of SHA 1 and RSA for signing nonsecret messages. n n bash 2. 05 a# (date; ps auxg) | openssl sha 1 44 c 702745 bdeced 27 d 8 c 01 b 8 bcda 28 bb 311 e 51 f 4 cs 691 46 chow
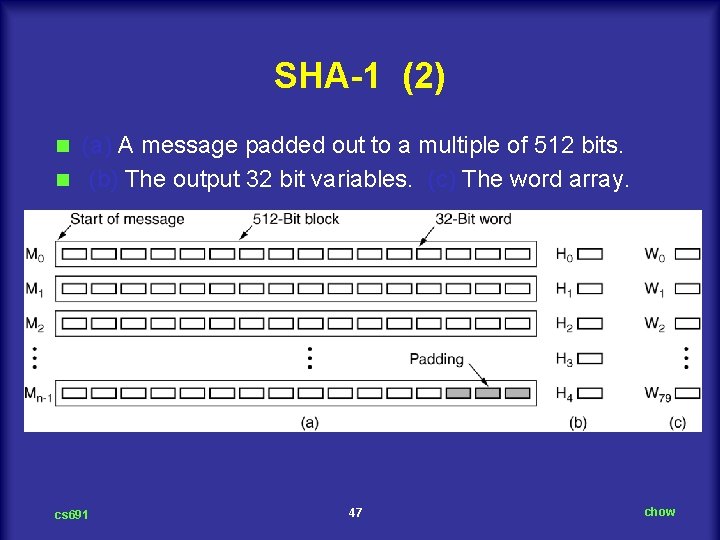
SHA-1 (2) (a) A message padded out to a multiple of 512 bits. n (b) The output 32 bit variables. (c) The word array. n cs 691 47 chow
SHA 1 n n n n Copy 16 work block input to w 0 to w 15. Scramble them to w 16 to w 79 with Wi= S 1(Wi 3 XOR Wi 8 XOR Wi 14 XOR Wi 16) (16 <=i<= 79) Sb(W) represent the left circular rotation of 32 bit word W by b bits. Actual step in pseudo C code: for (i = 0; i < 80; i++) { temp = S 5(A) + fi (B, C, D) + E + Wi + Ki; E=D; D=C; C = S 30 (B); B=A; A =temp; } f (B, C, D) = (B AND C) OR (NOT B AND D) ( 0<= i <=19) f (B, C, D) = B XOR C XOR D (20 <= i <= 39) f (B, C, D) = (B AND C) OR (B AND D) OR (C AND D) (40 <= i <= 59) f (B, C, D) = B XOR C XOR D (60<= i <= 79) At the end of 80 iterations, A E added to H 0 H 4 respectively. Continue the rest of the input blocks. Work ongoing for 256, 384, 512 bit hashes. cs 691 48 chow
The Birth Day Attack It takes 2 m operations to attack m bit MD. n But it takes 2 m/2 operations using birthday attack. Yuval 1979 paper on “how to swindle Rabin” n Example: two tenure faculty up for promotion: Tom and Dick. Tom earlier by two years. Tom asks Dept. Chair, Marilyn to write recommendation letter: n Secretary Ellen Loves Dick. She prepares two letters. n cs 691 49 chow
![Official Letter 1 Dear Dean Smith, This [letter I message] is to give my Official Letter 1 Dear Dean Smith, This [letter I message] is to give my](http://slidetodoc.com/presentation_image_h/b5399189c62e00a0f0369c5ed515347f/image-50.jpg)
Official Letter 1 Dear Dean Smith, This [letter I message] is to give my [honest I frank] opinion of Prof. Tom Wilson, who is [a candidate I up] for tenure [now I this year]. I have [known I worked with] Prof. Wilson for [about I almost] six years. He is an [outstanding I excellent] researcher of great [talent I ability] known [worldwide I internationally] for his [brilliant I creative] insights into [many I a wide variety of] [difficult I chal lenging]problems. He is also a [highly I greatly] [respected I admired] [teacher I educator]. His students give his [classes I courses] [rave I spectacular] reviews. He is [our I the Department's] [most popular I best loved] [teacher I instructor]. [In addition I Additionally] Prof. Wilson is a [gifted I effective] fund raiser. His [grants I contracts] have brought a [large I substantial] amount of money into [the I our] Department. [This money has I These funds have] [enabled I permitted] us to [pursue I carry out] many [special I important] programs, [such as I for ex ample] your State 2000 program. Without these funds we would [be unable I not be able] to continue this program. which is so [important I essential] to both of us. I strongly urge you to grant him tenure. cs 691 50 chow
![Fake Letter Dean Smith. This [letter I message] is to give my [honest I Fake Letter Dean Smith. This [letter I message] is to give my [honest I](http://slidetodoc.com/presentation_image_h/b5399189c62e00a0f0369c5ed515347f/image-51.jpg)
Fake Letter Dean Smith. This [letter I message] is to give my [honest I frank] opinion of Prof. Tom Wilson, who is [a candidate I up] for tenure [now I this year]. I have [known I worked with] Tom for [about I almost] six years. He is a [poor I weak] researcher not well known in his [field I area]. His research [hardly ever I rarely] shows [insight in I understanding of] the [key I major] problems of [the I our] day. Furthermore, he is not a [respected I admired] [teacher I educator]. His stu dents give his [classes I courses] [poor I bad ] reviews. He is [our I the Department's] least popular [teacher I instructor], known [mostly I primarily] within [the I our] Department for his [tendency I propensity] to [ridicule I embar rass]students [foolish I imprudent] enough to ask questions in his classes. [In addition I Additionally] Tom is a [poor I marginal] fund raiser. His [grants I contracts] have brought only a [meager I insignificant] amount of money into [the I our] Department. Unless new [money is I funds are] quickly located, we may have to cancel some essential programs, such as your State 2000 program. Unfortunately, under these [conditions I circumstances] I cannot in good [consci ence I faith] recommend him to you for [tenure I a permanent position]. cs 691 51 chow
The Rest of Story n n n Now Ellen programs her computer to compute the 232 message digests of each letter overnight. Chances are. one digest of the first letter will match one digest of the second letter. If not. she can add a few more options and try again during the weekend. Suppose that she finds a match. Call the "good" letter A and the "bad" one B. Ellen now e mails letter A to Marilyn for her approval. Letter B she keeps completely secret, showing it to no one. Marilyn, of course. approves, computes her 64 bit message digest. signs the digest. and e mails the signed digest off to Dean Smith. Independently, Ellen e mails letter B to the Dean (not letter A, as she is supposed to). After getting the letter and signed message digest. the Dean runs the message digest algorithm on letter B, sees that it agrees with what Marilyn sent him, and fires Tom. The Dean does not realize that Ellen managed to generate two letters with the same message digest and sent her a different one than Marilyn saw and approved. (Optional ending: Ellen tells Dick what she did. Dick is appalled and breaks off with her. Ellen is furious and confesses to Marilyn calls the Dean. Tom gets tenure after all. ) With MD 5 the birthday attack is difficult be cause even at 1 billion digests per second, it would take over 500 years to com pute all 264 digests of two letters with 64 variants each, and even then a match is not guaranteed. Of course, with 5000 computers working in parallel, 500 years becomes 5 weeks. SHA 1 is better (because it is longer). cs 691 52 chow
Management of Public Keys n Certificates n X. 509 n Public cs 691 Key Infrastructures 53 chow
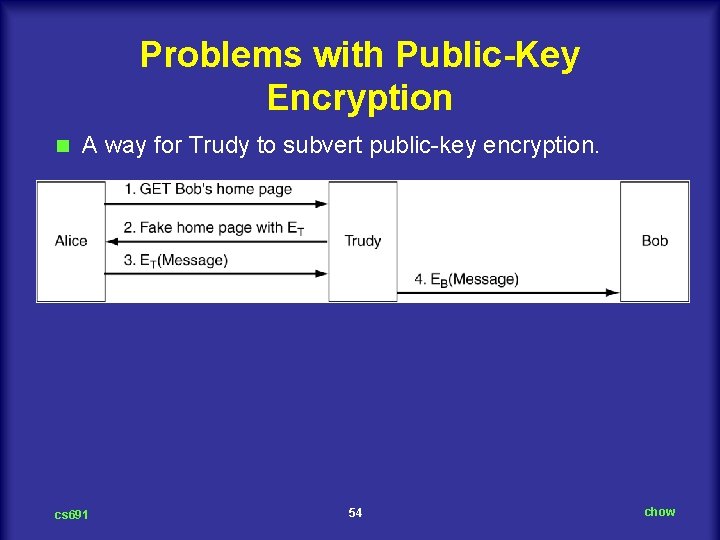
Problems with Public-Key Encryption n A way for Trudy to subvert public key encryption. cs 691 54 chow
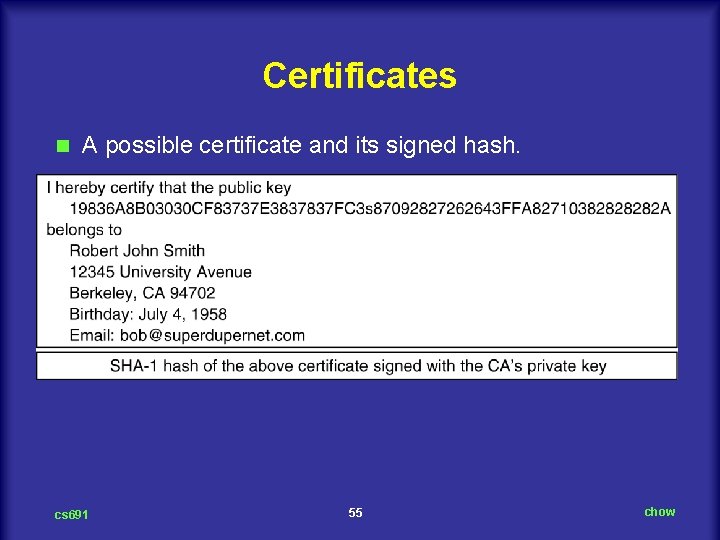
Certificates n A possible certificate and its signed hash. cs 691 55 chow
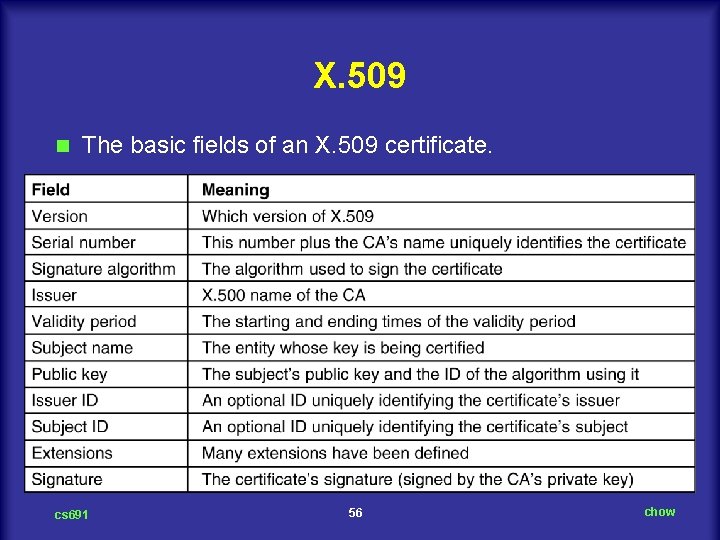
X. 509 n The basic fields of an X. 509 certificate. cs 691 56 chow
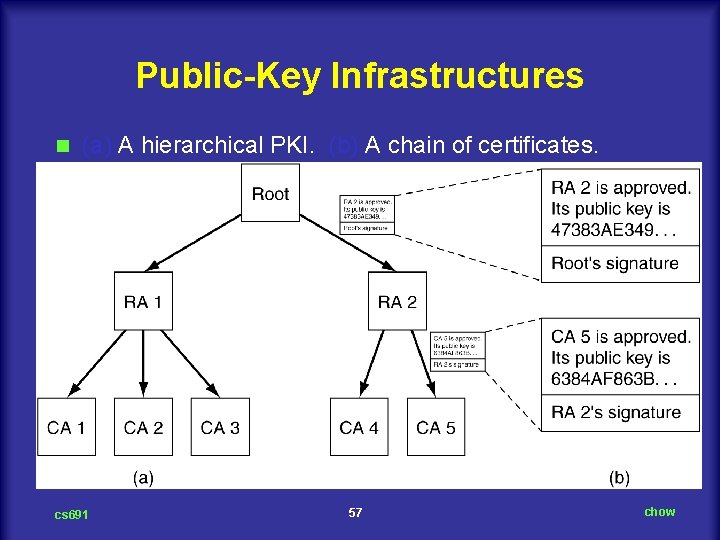
Public-Key Infrastructures n (a) A hierarchical PKI. (b) A chain of certificates. cs 691 57 chow
Communication Security n IPsec n Firewalls n Virtual Private Networks n Wireless Security cs 691 58 chow
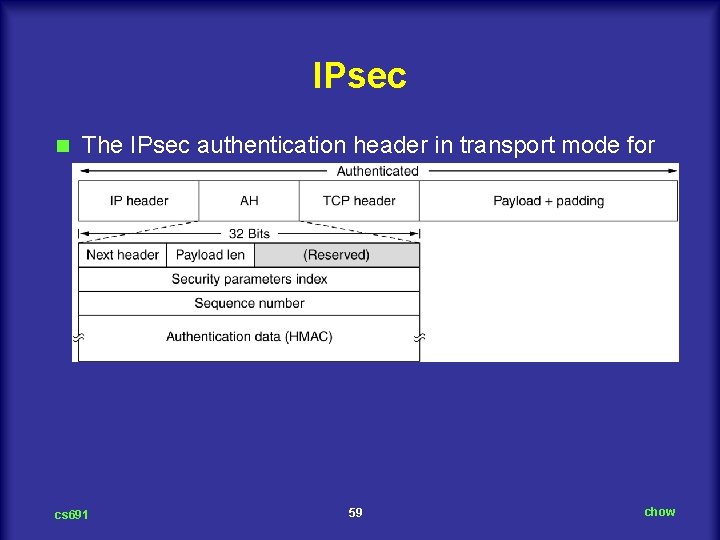
IPsec n The IPsec authentication header in transport mode for IPv 4. cs 691 59 chow
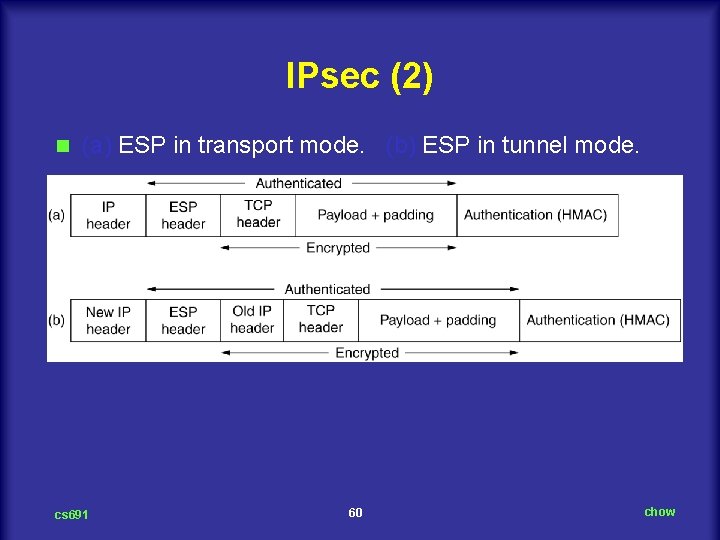
IPsec (2) n (a) ESP in transport mode. (b) ESP in tunnel mode. cs 691 60 chow
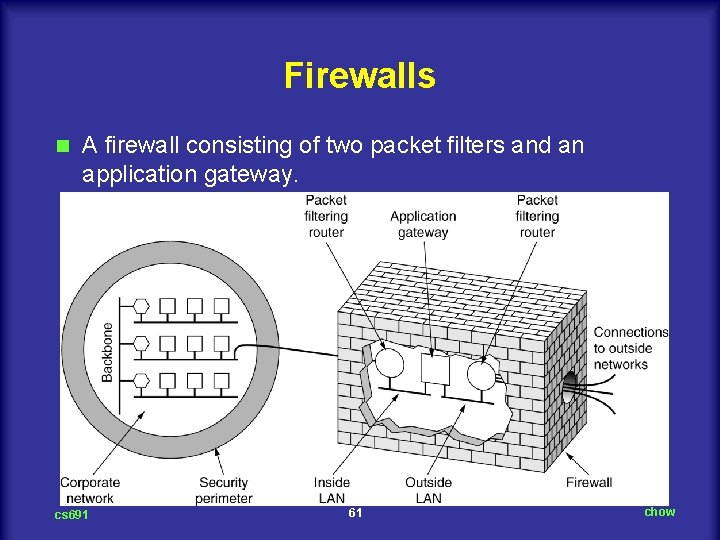
Firewalls n A firewall consisting of two packet filters and an application gateway. cs 691 61 chow
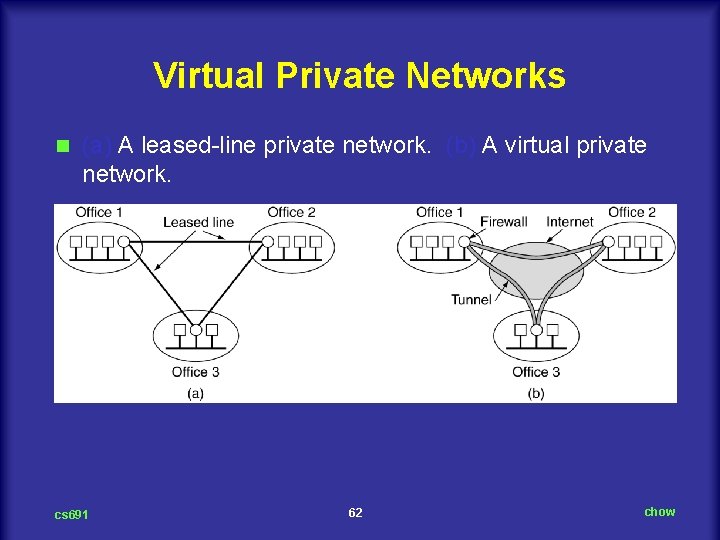
Virtual Private Networks n (a) A leased line private network. (b) A virtual private network. cs 691 62 chow
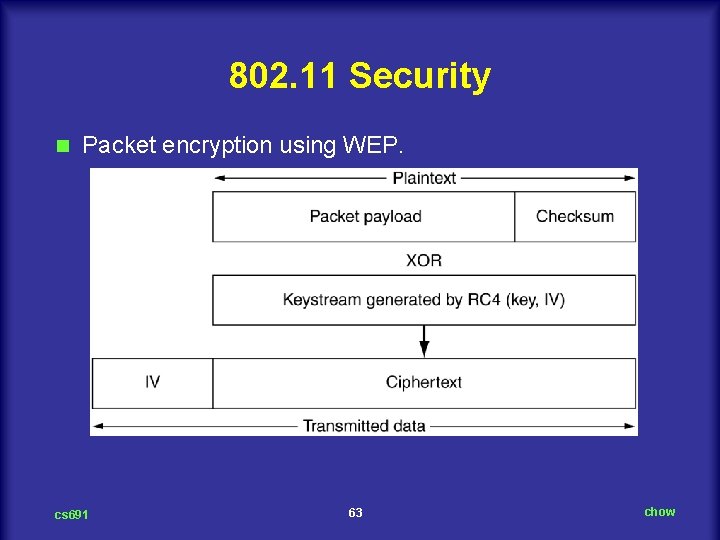
802. 11 Security n Packet encryption using WEP. cs 691 63 chow
Authentication Protocols n Authentication Based on a Shared Secret Key n Establishing a Shared Key: Diffie Hellman n Authentication Using a Key Distribution Center n Authentication Using Kerberos n Authentication Using Public Key Cryptography cs 691 64 chow
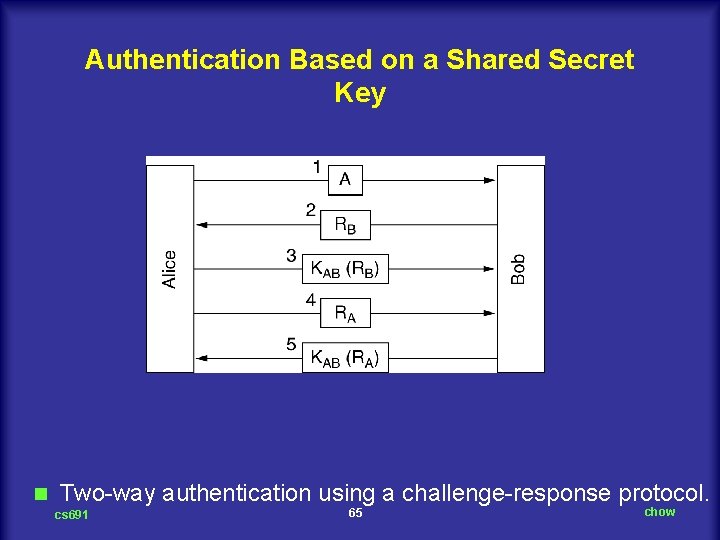
Authentication Based on a Shared Secret Key n Two way authentication using a challenge response protocol. cs 691 65 chow
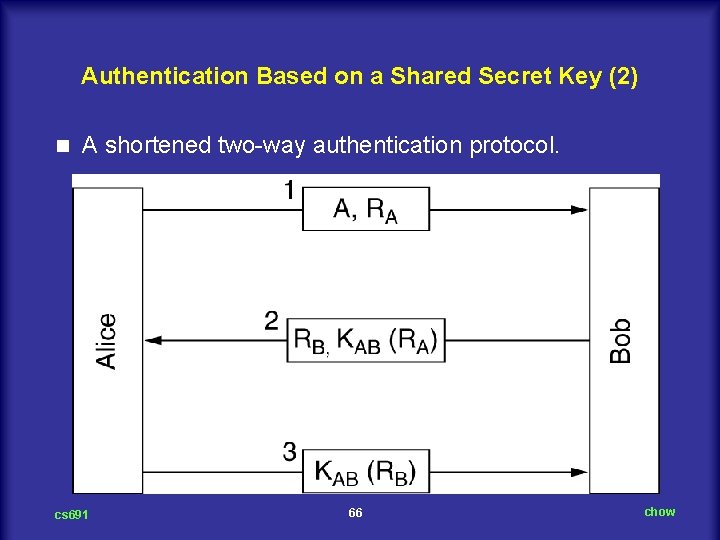
Authentication Based on a Shared Secret Key (2) n A shortened two way authentication protocol. cs 691 66 chow
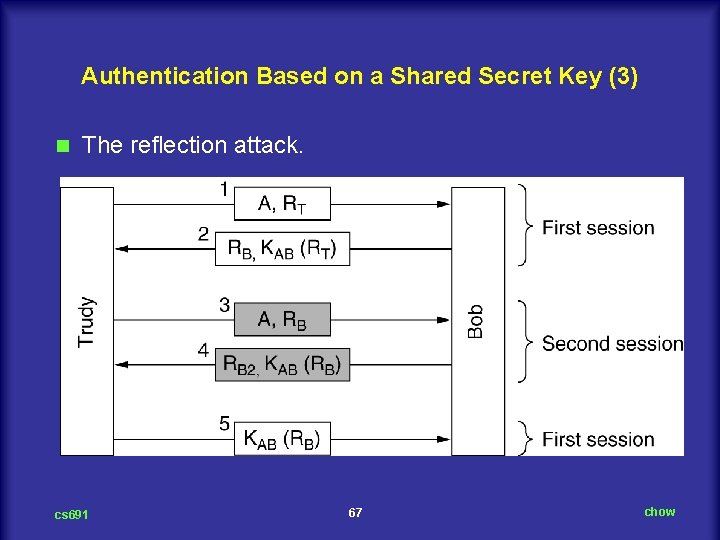
Authentication Based on a Shared Secret Key (3) n The reflection attack. cs 691 67 chow
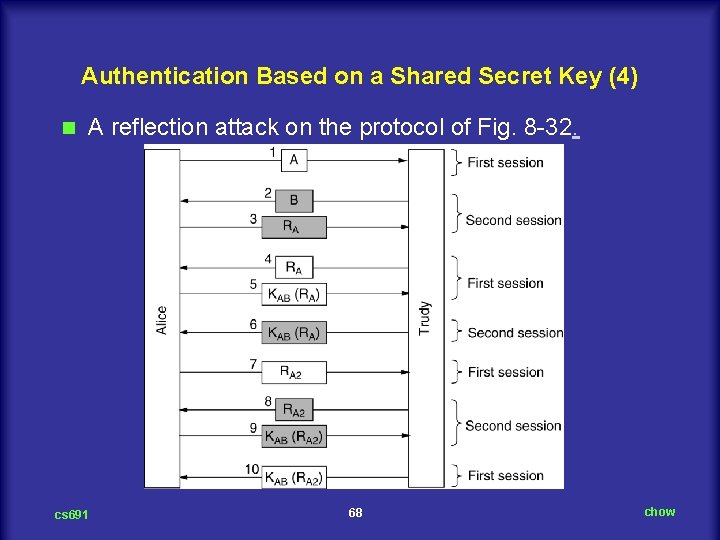
Authentication Based on a Shared Secret Key (4) n A reflection attack on the protocol of Fig. 8 32. cs 691 68 chow
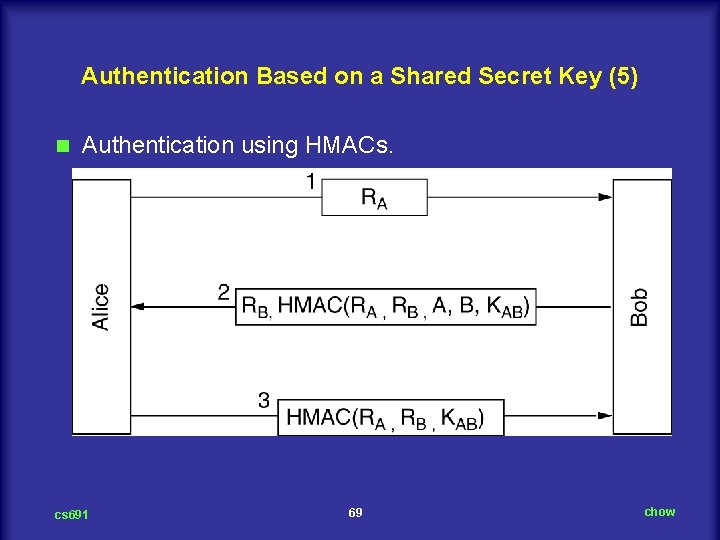
Authentication Based on a Shared Secret Key (5) n Authentication using HMACs. cs 691 69 chow
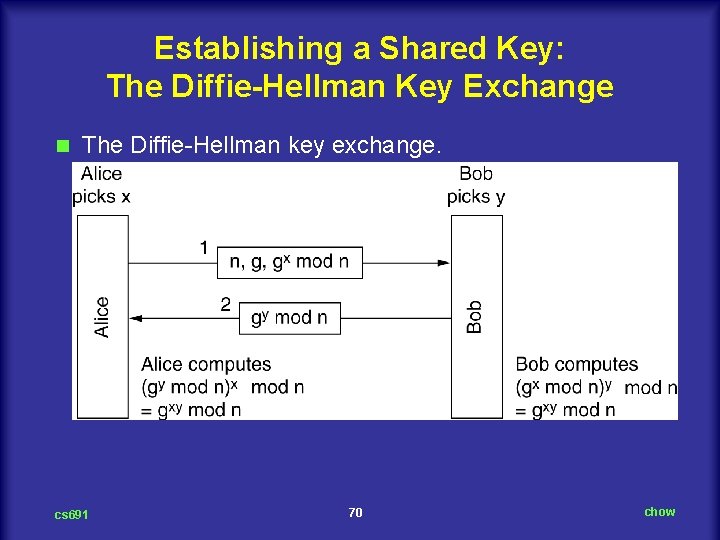
Establishing a Shared Key: The Diffie-Hellman Key Exchange n The Diffie Hellman key exchange. cs 691 70 chow
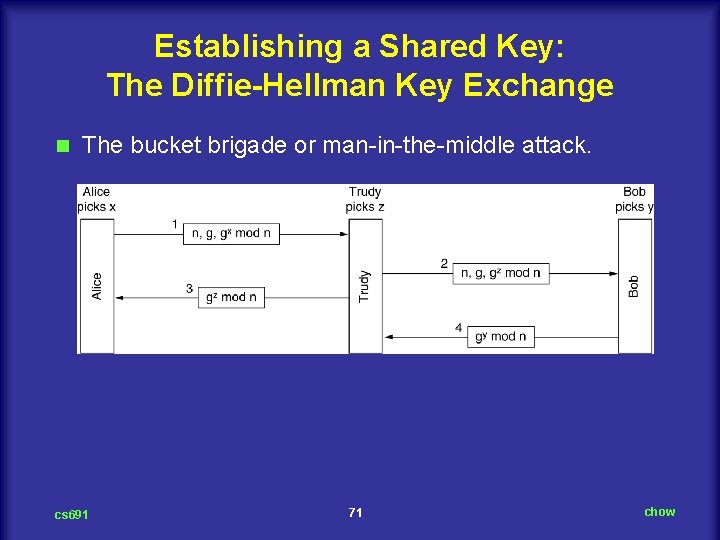
Establishing a Shared Key: The Diffie-Hellman Key Exchange n The bucket brigade or man in the middle attack. cs 691 71 chow
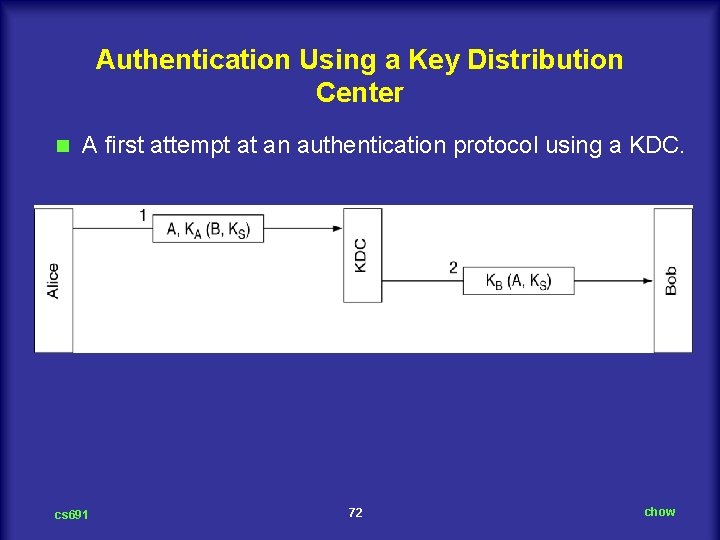
Authentication Using a Key Distribution Center n A first attempt at an authentication protocol using a KDC. cs 691 72 chow
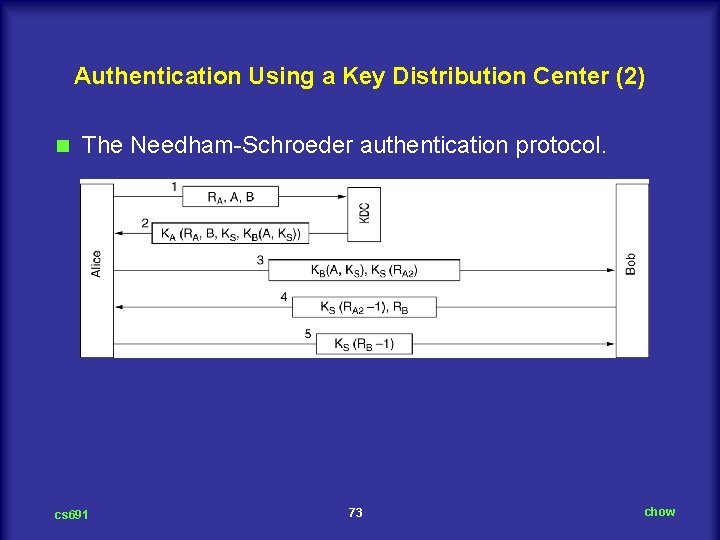
Authentication Using a Key Distribution Center (2) n The Needham Schroeder authentication protocol. cs 691 73 chow
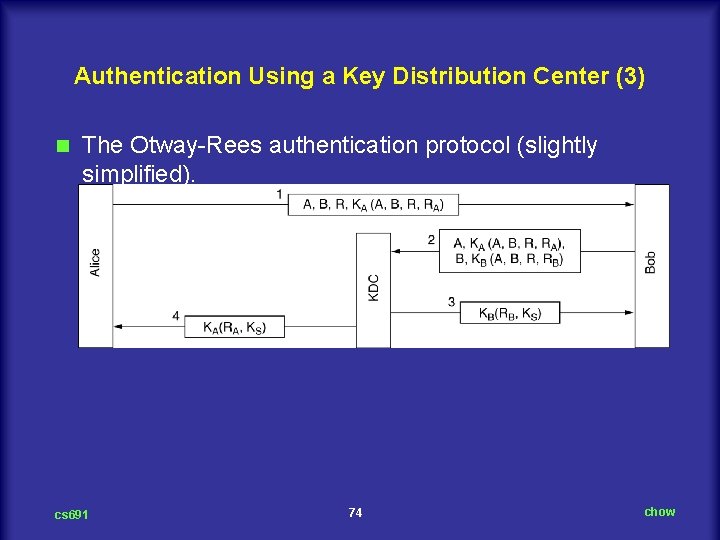
Authentication Using a Key Distribution Center (3) n The Otway Rees authentication protocol (slightly simplified). cs 691 74 chow
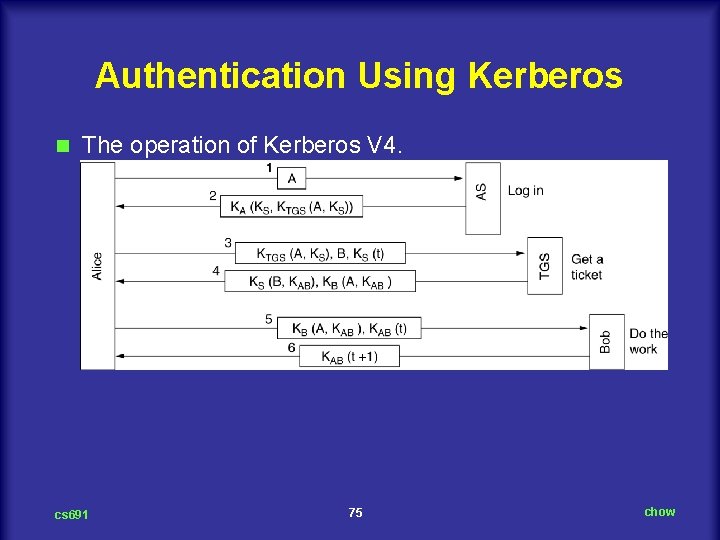
Authentication Using Kerberos n The operation of Kerberos V 4. cs 691 75 chow
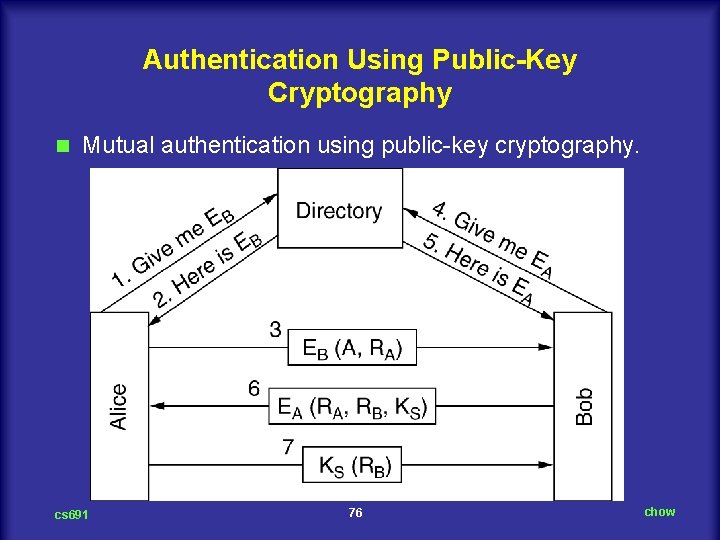
Authentication Using Public-Key Cryptography n Mutual authentication using public key cryptography. cs 691 76 chow
E-Mail Security n PGP – Pretty Good Privacy n PEM – Privacy Enhanced Mail n S/MIME cs 691 77 chow
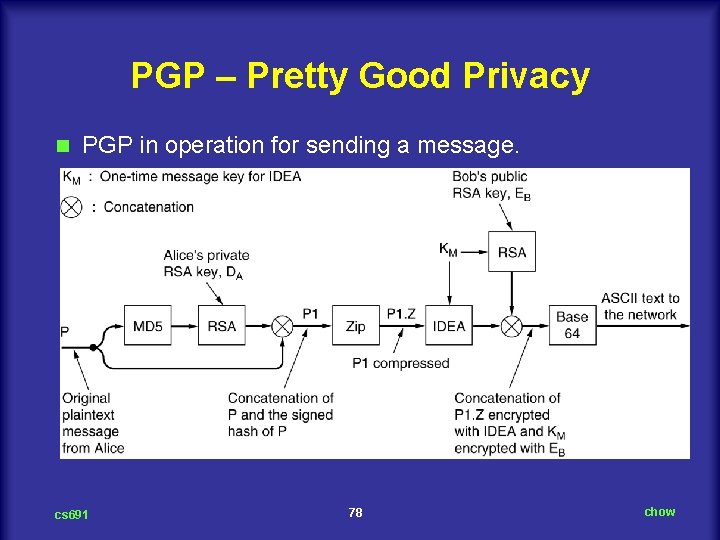
PGP – Pretty Good Privacy n PGP in operation for sending a message. cs 691 78 chow
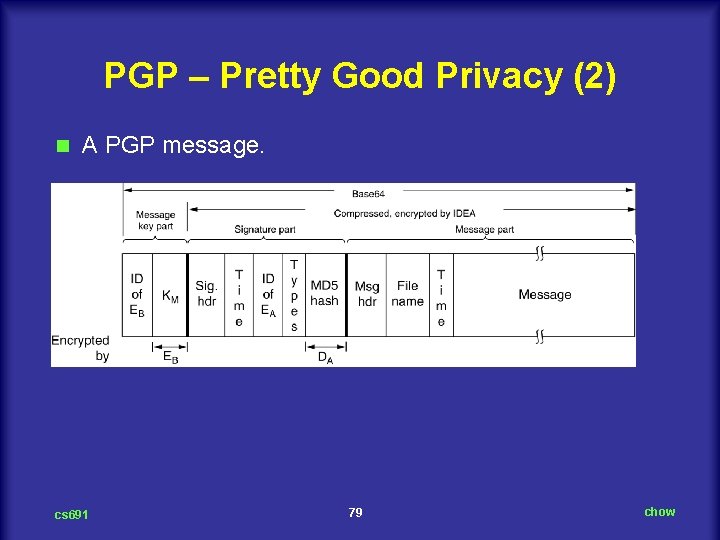
PGP – Pretty Good Privacy (2) n A PGP message. cs 691 79 chow
Web Security n Threats n Secure Naming n SSL – The Secure Sockets Layer n Mobile Code Security cs 691 80 chow
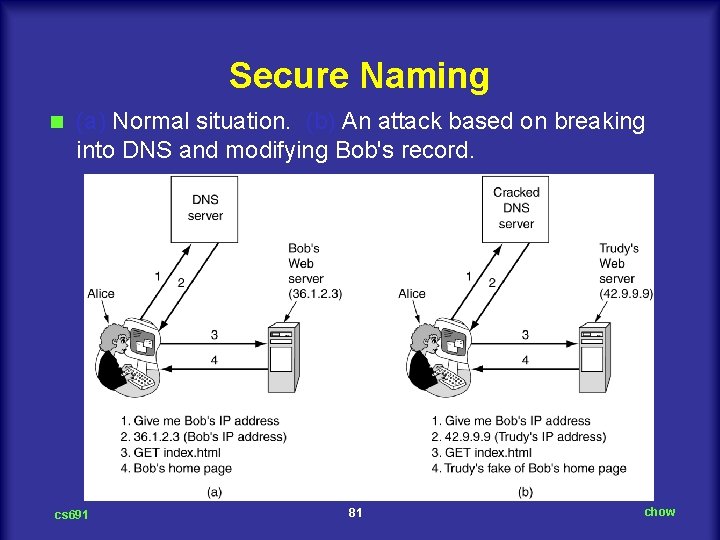
Secure Naming n (a) Normal situation. (b) An attack based on breaking into DNS and modifying Bob's record. cs 691 81 chow
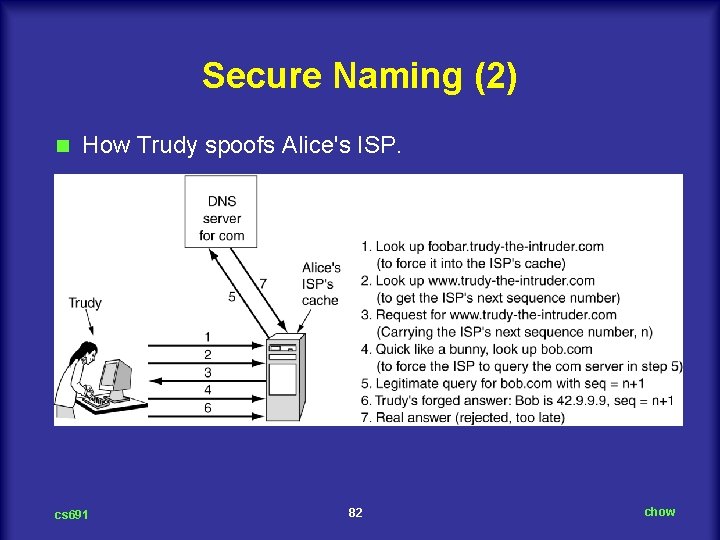
Secure Naming (2) n How Trudy spoofs Alice's ISP. cs 691 82 chow
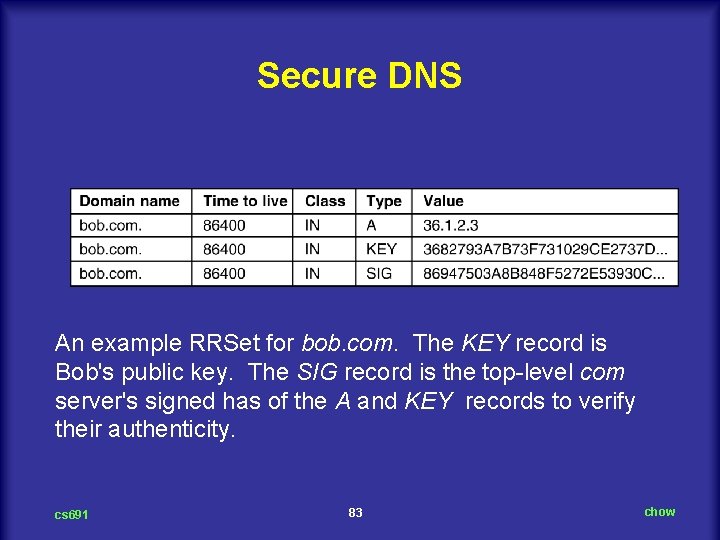
Secure DNS An example RRSet for bob. com. The KEY record is Bob's public key. The SIG record is the top level com server's signed has of the A and KEY records to verify their authenticity. cs 691 83 chow
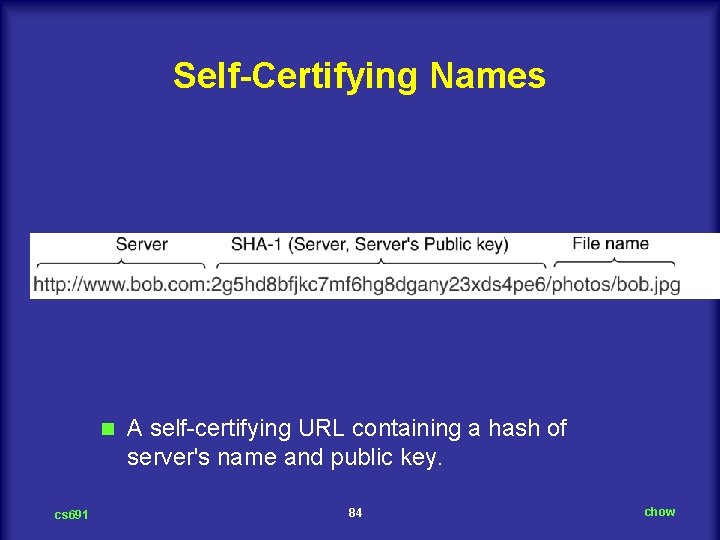
Self-Certifying Names n cs 691 A self certifying URL containing a hash of server's name and public key. 84 chow
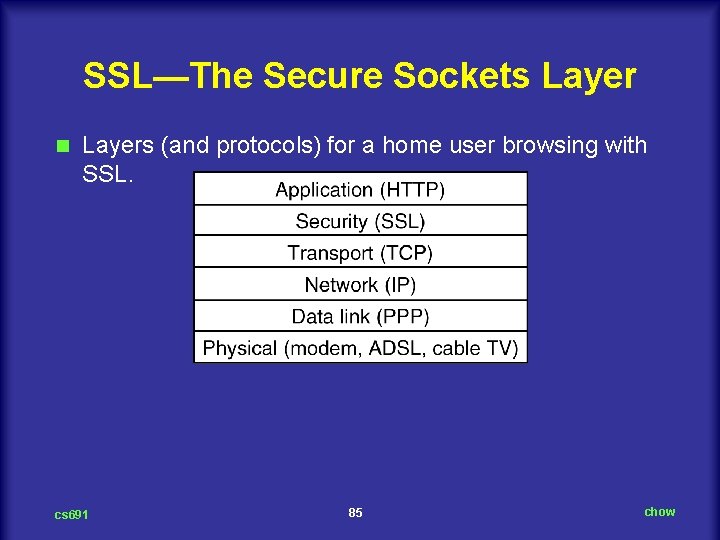
SSL—The Secure Sockets Layer n Layers (and protocols) for a home user browsing with SSL. cs 691 85 chow
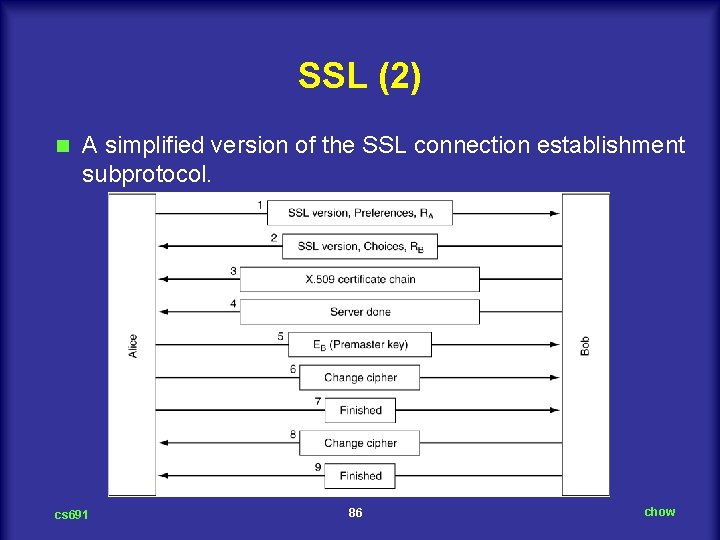
SSL (2) n A simplified version of the SSL connection establishment subprotocol. cs 691 86 chow
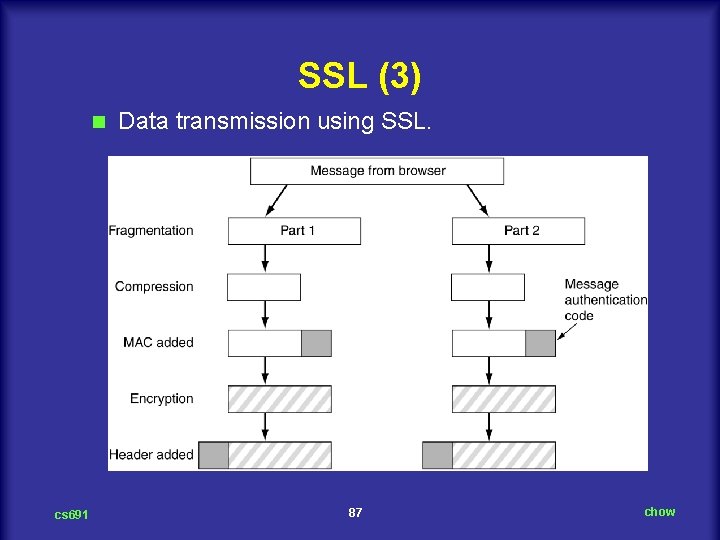
SSL (3) n cs 691 Data transmission using SSL. 87 chow
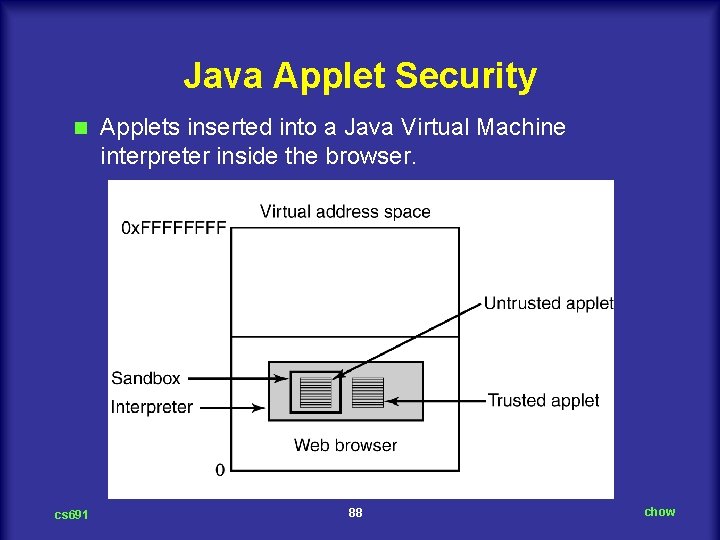
Java Applet Security n cs 691 Applets inserted into a Java Virtual Machine interpreter inside the browser. 88 chow
Social Issues Privacy n Freedom of Speech n Copyright n cs 691 89 chow
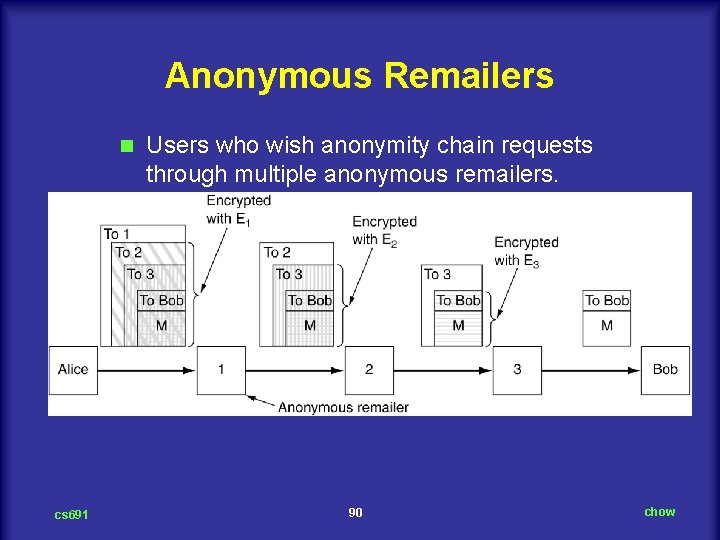
Anonymous Remailers n cs 691 Users who wish anonymity chain requests through multiple anonymous remailers. 90 chow

Freedom of Speech n 1. 2. 3. 4. 5. Possibly banned material: Material inappropriate for children or teenagers. Hate aimed at various ethnic, religious, sexual, or other groups. Information about democracy and democratic values. Accounts of historical events contradicting the government's version. Manuals for picking locks, building weapons, encrypting messages, etc. cs 691 91 chow
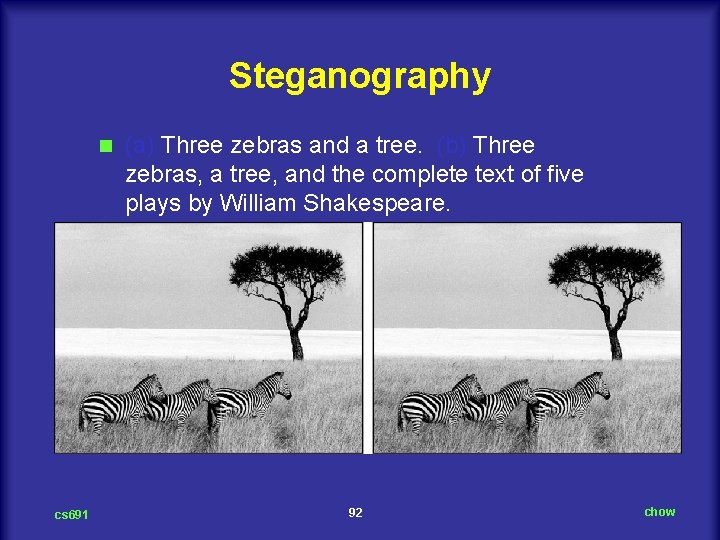
Steganography n cs 691 (a) Three zebras and a tree. (b) Three zebras, a tree, and the complete text of five plays by William Shakespeare. 92 chow
- Slides: 92