Backdoors Trojans and Rootkits A collection of presentation
Backdoors, Trojans and Rootkits A collection of presentation slides
Back Doors n An alternative entryway n n No fancy authentication needed Maintains access on a system n n Usually access is needed initially Still works when front door is closed
Back Doors n n n An attacker with back door access “owns” the system Attackers might make the system more secure to keep ownership The attacker does the work of the administrator
Back Doors Melded into Trojan Horses n n n Application-level Trojan Horse Backdoors Traditional Root. Kits Kernel-level Root. Kits
Application-Level Trojan Horse Backdoor Tools Adds a separate application to the system n Made up of a server and client part n n n server is installed on victims machine client is installed on attackers machine Victim must install the server portion n Once installed the attacker “owns” the victims machine n
Application-Level Trojan Horse Backdoor Tools n n n n Log Keystrokes Gather system information Get passwords from the SAM database Control the file system Edit the registry Control applications and services Redirect Packets
Application-Level Trojan Horse Backdoor Tools n Application redirection n n n Any DOS application can be spawned useful for setting up command-line backdoors Multimedia control View files in a browser Hidden mode Encryption between client and server
Application-Level Trojan Horse Backdoor Tools n Plug-ins: n n Streaming video from server machine More encryption methods n n n Blowfish, CAST-256, IDEA, Serpent, RC 6 Stronger security than a lot of commercial products! Stealthier methods for transport
Defenses against Application. Level Trojan Backdoors n n Most Anti-virus programs will notice and remove the tools mentioned Update virus definitions regularly Don’t run programs downloaded from untrusted sources Don’t auto-run Active. X controls
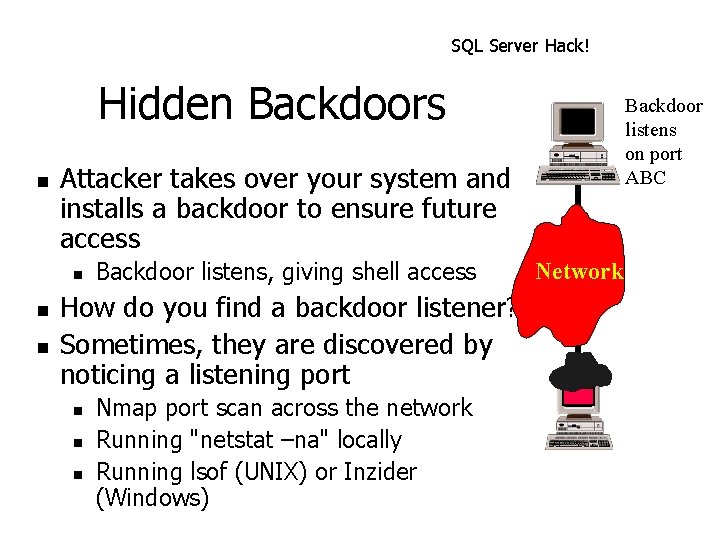
SQL Server Hack! Hidden Backdoors n Attacker takes over your system and installs a backdoor to ensure future access n n n Backdoor listens on port ABC Backdoor listens, giving shell access How do you find a backdoor listener? Sometimes, they are discovered by noticing a listening port n n n Nmap port scan across the network Running "netstat –na" locally Running lsof (UNIX) or Inzider (Windows) Network
Sniffing Backdoors Who says a backdoor has to wait listening on a port? n Attackers don't want to get caught n n n They are increasingly using stealthy backdoors A sniffer can gather the traffic, rather than listening on an open port n Non-promiscuous sniffing backdoors n n Grab traffic just for one host Promiscuous sniffing backdoors n Grab all traffic on the LAN
Non-Promiscuous Backdoor – Cd 00 r n Written by FX n n Includes a non-promiscuous sniffer n n Gathers only packets destined for the single target machine Several packets directed to specific ports (where there is no listener) will trigger the backdoor n n http: //www. phenoelit. de/stuff/cd 00 r. c Sniffer grabs packets, not a listener on the ports Backdoor root shell starts to listen on TCP port 5002 only when packets arrive to the trigger ports
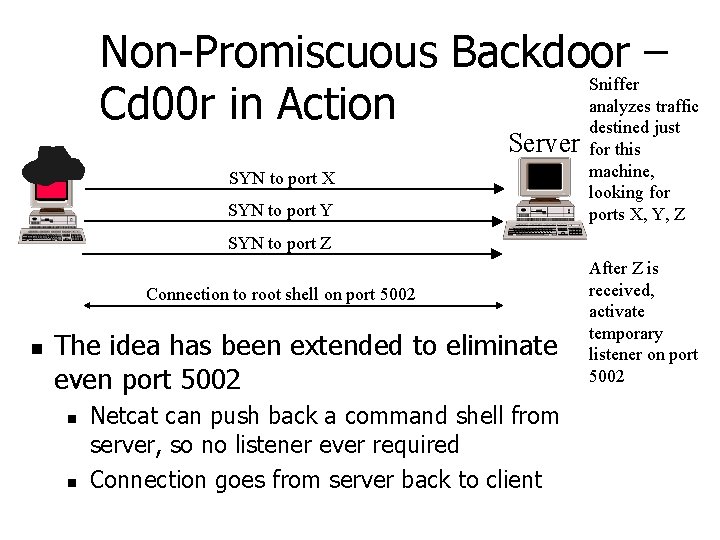
Non-Promiscuous Backdoor – Sniffer analyzes traffic Cd 00 r in Action destined just Server SYN to port X SYN to port Y for this machine, looking for ports X, Y, Z SYN to port Z Connection to root shell on port 5002 n The idea has been extended to eliminate even port 5002 n n Netcat can push back a command shell from server, so no listener ever required Connection goes from server back to client After Z is received, activate temporary listener on port 5002
Promiscuous Backdoor Can be used to help throw off an investigation n Attacker sends data for destination on same network n But the backdoor isn't located at the destination of the backdoor traffic n n Huh? How does that work?
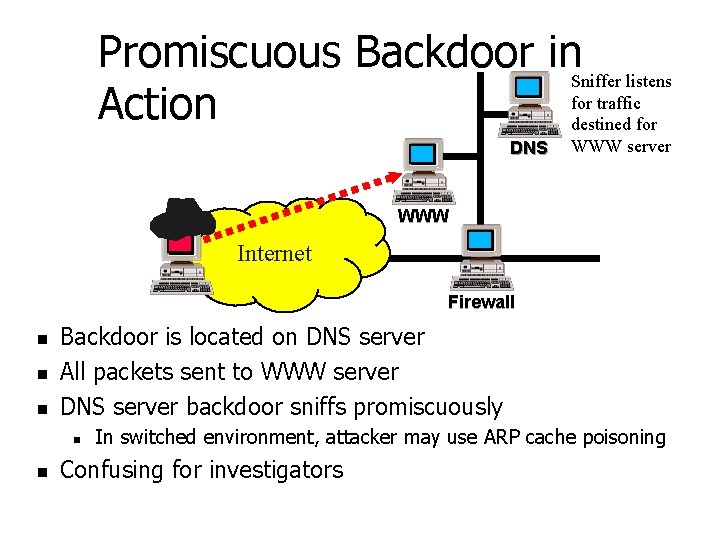
Promiscuous Backdoor in. Sniffer listens for traffic Action destined for DNS WWW server WWW Internet Firewall n n n Backdoor is located on DNS server All packets sent to WWW server DNS server backdoor sniffs promiscuously n n In switched environment, attacker may use ARP cache poisoning Confusing for investigators
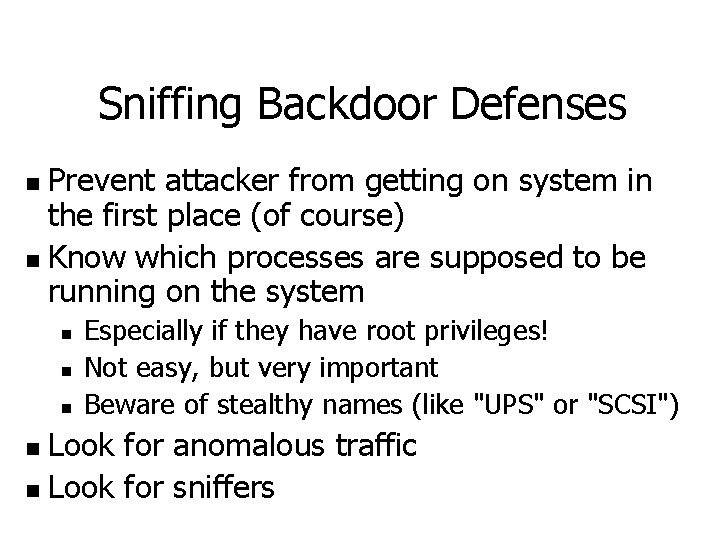
Sniffing Backdoor Defenses Prevent attacker from getting on system in the first place (of course) n Know which processes are supposed to be running on the system n n Especially if they have root privileges! Not easy, but very important Beware of stealthy names (like "UPS" or "SCSI") Look for anomalous traffic n Look for sniffers n
Traditional Root. Kits n n Replaces key system components Less detectable than application-level Trojan Horse Backdoors Traditionally focus on UNIX systems Root access is required initially
Traditional Root. Kits n On Windows systems… n n Root. Kits Replace Dynamic Link Libraries or alters the system On UNIX systems… n Root. Kits replace /bin/login with a backdoor version of /bin/login
Traditional Root. Kits n n n When an attacker enters the backdoor password access is given to the system Backdoor password still works if other passwords are changed Login is not recorded in wtmp or utmp files for the backdoor user
Traditional Root. Kits n Some other programs replaced: n du - shows free disk space n n find - finds files n n Hides attacker’s files ifconfig - shows status of interfaces n n Root. Kits hides space used by attacking tools masks promiscuous mode ls - shows contents of directories n Hides attacker’s files
Traditional Root. Kits n Linux Root. Kit 5 (lrk 5) n n n written by Lord Somer one of the most full-featured Root. Kits includes Trojan versions of the following: n chfn, chsh, crontab, du, find, ifconfig, inetd, killall, login, ls, netstat, passwd, pidof, ps, rshd, syslogd, tcpd, top, sshd, and su
Defending against Traditional Root. Kits n n n Try harder to stop attackers from getting root access Remember root-level access is needed to install a Root. Kit Use “echo *” command to look for changes
Defending against Traditional Root. Kits n n n Get a program to scan /bin/login and see if it has been corrupted Use a File Integrity Checker such as Tripwire Save hashes on read-only media
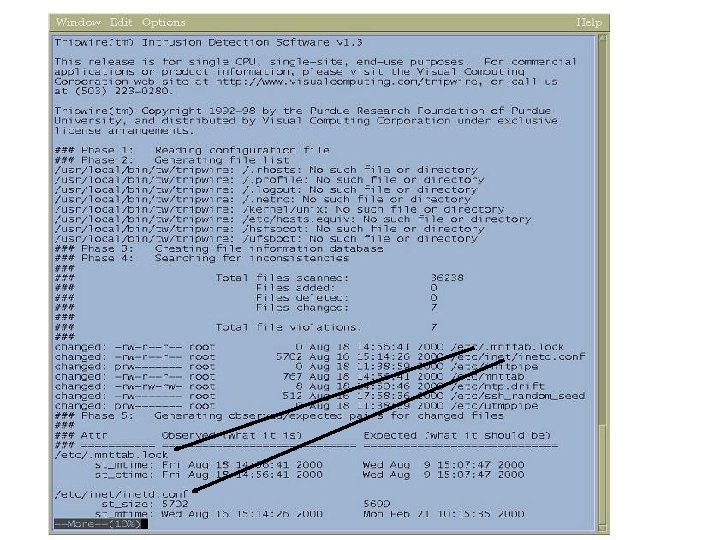
Tripwire n n n Available from www. tripwire. org First of the file integrity checkers Unix and NT versions available n n n Network capable versions available Academic version is free. Commercial versions are not. Useful in finding trojan programs
Tripwire n n Generates a “signature” for each file based on checksums and other characteristics. These signatures are stored in a database file that should be kept offline. This is the baseline. Latest threat involves dynamic exec redirection. This is part of the newer Kernel Module Rootkits.
Tripwire n List of files to check: tw. config n n All files in a directory will be checked. Can prune directories from the check step. Can examine just the directory and nothing else. Can check by access time but not recommended since you’ll get a report of everything that changed. Everything!
Tripwire n Security Issues n n n Advantages n n Need to protect the DB Need to protect the vulnerable executables Simple interface, good choice of crypto hash functions, good all-around tool Disadvantages n Kernel mod attacks, initial tw. config takes some time to customize, NT version is good but costs $$$, no network security
Kernel-Level Root. Kits n n Makes the Kernel the Trojan Horse Most difficult to detect Gives the attacker complete control of the underlying system Nothing on the system can be trusted
Kernel-Level Root. Kits n n Most common feature is execution redirection Instead of changing other programs to hide files the kernel hides them Kernel may also hide processes that are running Port usage is often masked
Kernel-Level Root. Kits n Some Kernel-level Rootkits are: n n Knark (Linux) Adore (Linux) Plasmoid’s Solaris Loadable Kernel Module (Solaris) The Windows NT kernel-level Root. Kit (Windows)
Kernel-Level Root. Kits n Implemented with Loadable Kernel Modules (LKM) n n n LKM is used to extend the capabilities of the system only for some UNIX systems LKM makes it easy! To install the Knark Root. Kit type: n n “insmod knark. o, ” no reboot necessary
KNARK Background n n Written by Creed Released in 1999 Versions exist for Linux 2. 2 and 2. 4 kernels Very popular in ‘script kiddie’ community
KNARK Capabilities n n n n Hide/Unhide files or directories Hide TCP/UDP connections Execution Redirection Unauthenticated privilege escalation via the rootme program within knark Ability to change UID/GID of a running process Unauthenticated, privileged remote execution daemon Kill – 31 to hide a running process
Installing KNARK n KNARK IS installed as a Loadable Kernel Module (LKM) n n n System must have LKM enabled in order to be able to load KNARK Can be defeated if LKM is disabled, HOWEVER, updating system becomes much more complicated The KNARK rootkit has an additional LKM module to hide the presence of KNARK from the insmod (installed module) command.
What does KNARK Change? n n KNARK modifies the system call table (sys_call_table) within kernel memory by redirecting some system calls (sys_read, sys_getdents) to malicous system calls written by CREED. These new malicious system calls function as normal except in certain circumstances.
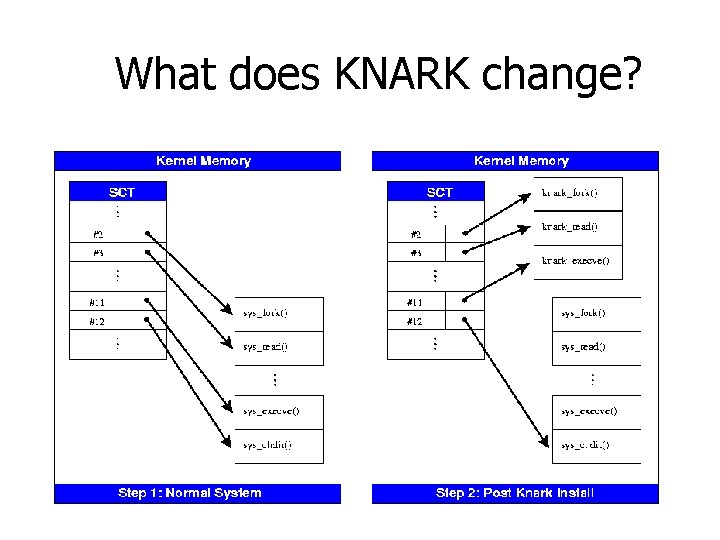
What does KNARK change?
What does KNARK Change? n n Can no longer trust the output of the system calls? Very difficult to detect rootkits such as KNARK using conventional methods n n System utility files (ls, ps) are not modified Kernel Output to system utility files IS modified.
Detecting KNARK n Cyptographic Checksums of system utilities will NOT change when KNARK is installed n n May be possible to take cryptographic checksum of selected region of kernel in order to detect rootkit modification of kernel (St. Michael) Can detect presence of KNARK type rootkits by examining sys_call_table
Detecting KNARK n The file /boot/System. map is created when system is initially compiled n n n /boot/System. map contains correct address of kernel system calls /boot/system map can be archived or retrieved from a known good system for comparison Must have Superuser (ROOT) privilege in order to read /dev/kmem (kernel memory)
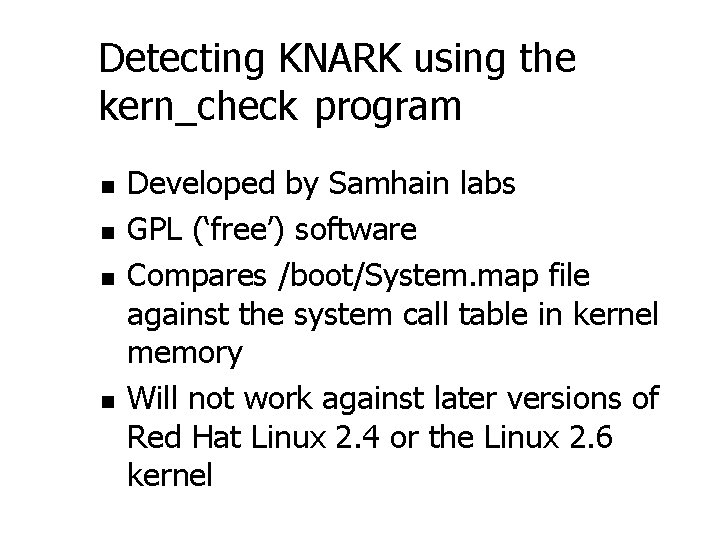
Detecting KNARK using the kern_check program n n Developed by Samhain labs GPL (‘free’) software Compares /boot/System. map file against the system call table in kernel memory Will not work against later versions of Red Hat Linux 2. 4 or the Linux 2. 6 kernel
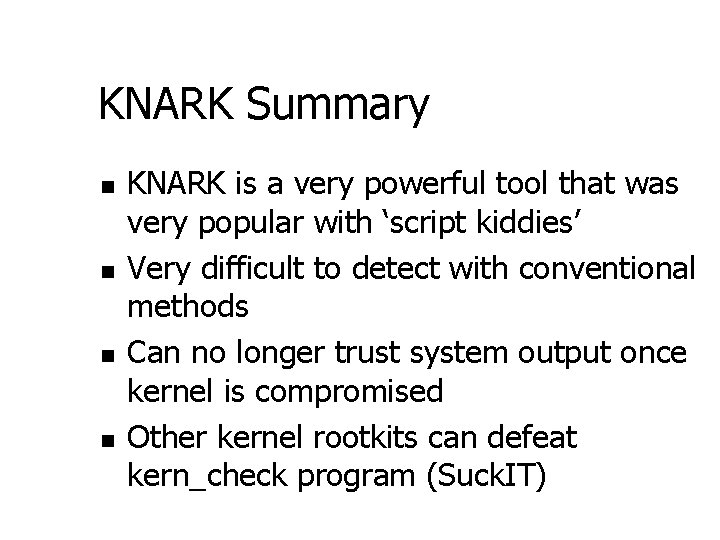
KNARK Summary n n KNARK is a very powerful tool that was very popular with ‘script kiddies’ Very difficult to detect with conventional methods Can no longer trust system output once kernel is compromised Other kernel rootkits can defeat kern_check program (Suck. IT)
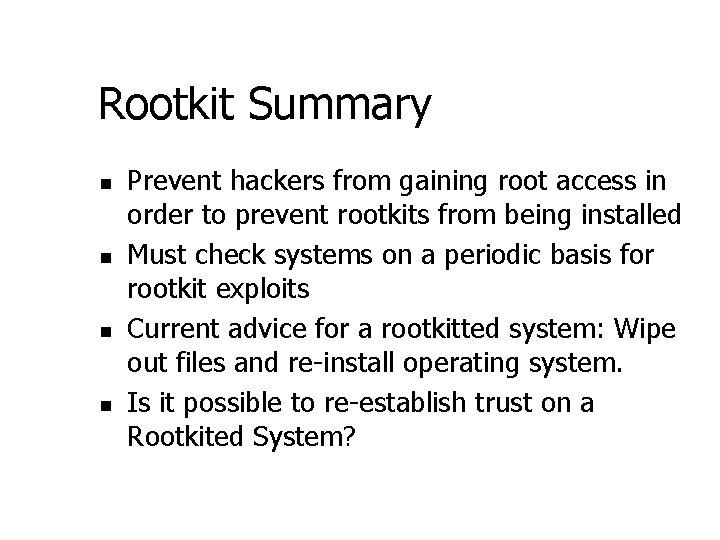
Rootkit Summary n n Prevent hackers from gaining root access in order to prevent rootkits from being installed Must check systems on a periodic basis for rootkit exploits Current advice for a rootkitted system: Wipe out files and re-install operating system. Is it possible to re-establish trust on a Rootkited System?
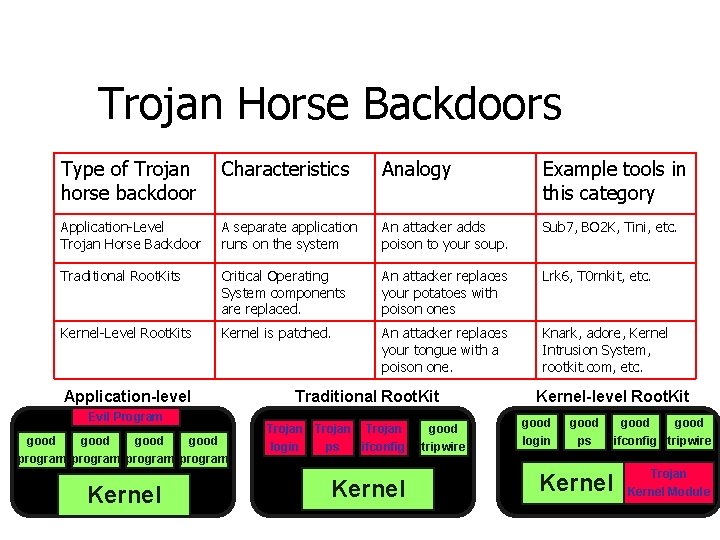
Trojan Horse Backdoors Type of Trojan horse backdoor Characteristics Analogy Example tools in this category Application-Level Trojan Horse Backdoor A separate application runs on the system An attacker adds poison to your soup. Sub 7, BO 2 K, Tini, etc. Traditional Root. Kits Critical Operating System components are replaced. An attacker replaces your potatoes with poison ones Lrk 6, T 0 rnkit, etc. Kernel-Level Root. Kits Kernel is patched. An attacker replaces your tongue with a poison one. Knark, adore, Kernel Intrusion System, rootkit. com, etc. Application-level Evil Program good program Kernel Traditional Root. Kit Trojan login ps Trojan good ifconfig tripwire Kernel-level Root. Kit good login ps Kernel good ifconfig tripwire Trojan Kernel Module
Here Come the Worms! n n n Compromising systems one-by-one can be such a chore Worms are attack tools that spread across a network, moving from host to host exploiting weaknesses Worms automate the process n n Take over systems Scan for new vulnerable systems Self-replicate by moving across the network to another vulnerable system Each instance of a worm is a “segment”
2001: Year of the Worm? n In 2001, we saw: n n n n n Ramen L 10 n Cheese Sadmind/IIS Code Red and Code Red II Nimda To date, worms haven’t been nearly as nasty as they could be Most damage is a result of worm resource consumption New generations of worms arrive every 2 to 6 months
Coming Soon - Super Worms n Be on the lookout for very nasty new worms n Multi-functional n n Multi-platform n n Many buffer overflows, etc. Zero-Day exploits n n Win, Linux, Solaris, BSD, AIX, HP-UX… Multi-exploit n n Spread, steal, erase, etc. Just discovered; no patch available Polymorphic Metamorphic We’ve seen many of these pieces, but no one has rolled them all together… yet!
Worm Defenses Buffer overflow defenses help a lot here n Rapidly deploy patches n Anti-virus solutions n n n At the desktop… …AND at the mail server …AND at the file server Incident response capabilities, linked with network management
- Slides: 48