B 061 ICT in Todays World Index 1
B 061 – ICT in Today’s World
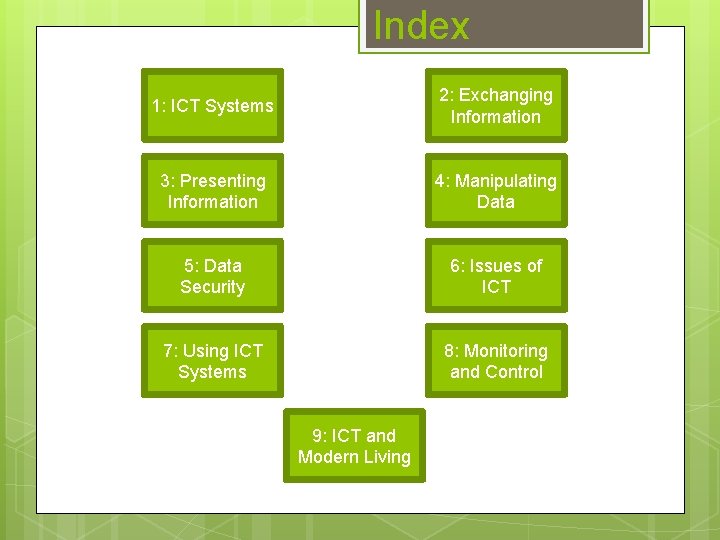
Index 1: ICT Systems 2: Exchanging Information 3: Presenting Information 4: Manipulating Data 5: Data Security 6: Issues of ICT 7: Using ICT Systems 8: Monitoring and Control 9: ICT and Modern Living
1: ICT Systems 1. 1: Computer Systems 1. 2: Hardware 1. 3: Software
Types of System 1: ICT Systems Personal Computers Standard systems for everyday personal tasks. Usually operate stand-alone with a shared web connection. Mainframes Mainly used by large businesses for bulk processing. Operate as a group of virtual machines rather than a single system. Supercomputers High-end, ultra-fast machines capable of performing complex calculations at high speeds. Use parallel processing, and so can carry out several tasks simultaneously. Often used in research establishments.

Embedded Systems 1: ICT Systems EMBEDDED SYSTEM – system with a dedicated function within a larger electrical system. The output of one system goes straight in as the input of another. Found in MP 3 players, DVD players, digital watches… Advantages: Disadvantages: Save common user settings, making appliances more convenient to use. Complex and so cannot be repaired by the user. Free up time for the user to carry out More expensive than simple systems. other tasks. Can intelligently and accurately control events, such as washing machine temperature. Tricky to fix even for qualified repairmen and so often have to be completely replaced.
Hardware 1: ICT Systems HARDWARE – the physical parts which make up a computer system. Different hardware can be categorised as follows: Input – allow users to enter data into the system Output – allow the system to transfer/display data Processing – carry out the calculations and instructions required for the system to function Storage – where data and information is stored.
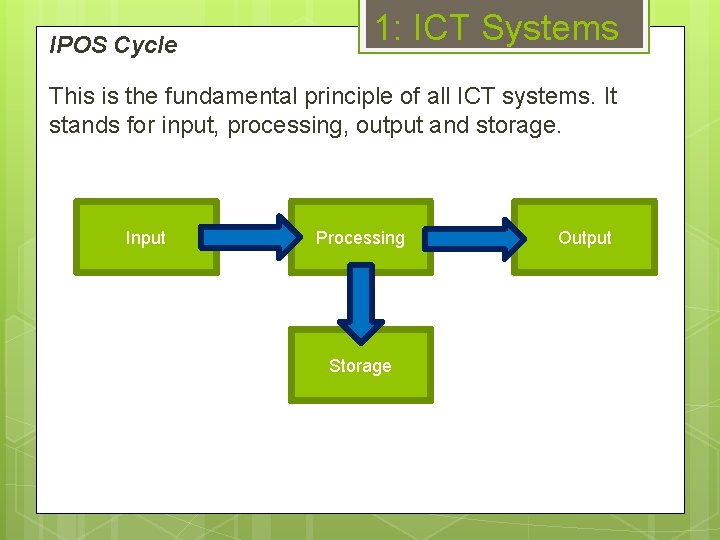
IPOS Cycle 1: ICT Systems This is the fundamental principle of all ICT systems. It stands for input, processing, output and storage. Input Processing Storage Output

Input Devices 1: ICT Systems

Output Devices 1: ICT Systems

In-Built Storage 1: ICT Systems Primary Storage – referred to as the memory of the computer. Random Access Memory – temporary storage used to hold data being used by the system at that point. The storage is what’s known as volatile - data is lost when the system is switched off. Read Only Memory – non-volatile and permanent storage which holds the instructions which the computer runs before loading the operating system (the BIOS – Basic Input/Output System). Secondary Storage – holds permanent data, stores it even when not powered. Separate from the main processor and usually some kind of hard disk. The hard disk consists of metal disks with read/write heads which move across the surface.

Removable Storage 1: ICT Systems

1: ICT Systems Digital and Analogue data is analogous – the data is not the ‘real’ data, rather the closest equivalent. It changes smoothly, unlike binary which changes in fixed steps. A computer system deals in binary, a literal system of 1 s and 0 s. All data is expressed in this way, and the table below shows the way that numbers are stored in binary. 128 64 32 16 8 4 2 1 67 0 1 0 0 1 1 121 0 1 1 0 0 1 7 0 0 0 1 1 1 Therefore if data is in analogue form, it has to first be converted to its digital equivalent so that the computer can ‘understand’ (process) it.

Software 1: ICT Systems SOFTWARE – provide the instructions which the system requires to carry out tasks given to it. Different software can be categorised as follows: Operating Systems Utility Software Drivers Applications Programming Software

GUI and CLI 1: ICT Systems What do they stand for and which is which?

GUI and CLI 1: ICT Systems What do they stand for and which is which? Graphical User Interface Windows Icons Menus Pointers Command Line Interface Text-based input Must know correct syntax Less user friendly

Operating Systems 1: ICT Systems What does an operating system do? Memory management Provide a GUI Hardware/software installation Disk management What’s so good about them? Real-time operation Interactivity Multi-tasking

Utility Software 1: ICT Systems Utility software is functional – it performs one or two tasks exceptionally well but does nothing else. For example: Anti-viral software File conversion Defragmentation manager File repair Crash dump interpreter. Many utility programs come as part of an OS, for example defragmentation managers.

Applications 1: ICT Systems

Worked Exam Questions 1: ICT Systems The image shows a computerised data logger which is designed to be worn on a person’s wrist. 1) From the diagram, identify one component for input and one for output. (2) 2) The device contains an analogue to digital converter. Explain why this is required. (2)
Worked Exam Questions 1: ICT Systems The image shows a computerised data logger which is designed to be worn on a person’s wrist. 1) From the diagram, identify one component for input and one for output. (2) Input: buttons, sensors, on/off switch (1) Output: speaker, screen (1) The device contains an analogue to digital converter. Explain why this is required. (2) Sensor logs data in analogue form (1) Computers can only read digital data (1) 1)
2: Exchanging Information 2. 1: Communication Services 2. 2: Sharing Information Securely 2. 3: Responsible Communications 2. 4: Communications Software 2. 5: The Internet 2. 6: Control and Monitoring 2. 7: New Technologies

Communication Services 2: Exchanging Information Email SMS Instant Messaging Video-conferencing Vo. IP Fax Internet Forums Chat Rooms Cloud Storage Discuss possible advantages and disadvantages of these, making a list in your notes.

Secure Sharing 2: Exchanging Information Data can be encrypted to prevent it being intercepted during transmission. An encryption cipher, such as an RSA algorithm, scrambles the data between the sender and the receiver, preventing it from being intercepted and read. Files can be encrypted in storage through the use of a service such as Bit. Locker or the in-built encryption in Microsoft Office.

Responsible Sharing 2: Exchanging Information Copyright Theft – Illegal downloading of copyrighted material including text, media and software. Email Flaming – Sending hostile or insulting messages to other users via email. Spam – Sending bulk messages to other users via email, usually used for advertising purposes. Defamatory Statements – Untrue communications which harm a person’s reputation. Other online hazards include fraudulent websites, malware and phishing scams.

Communications Software 2: Exchanging Information

Communications Software 2: Exchanging Information Find the meanings of the following key terms: POP 3 SMTP URL ISP BCC FTP Cookies

Communications Software 2: Exchanging Information Find the meanings of the following key terms: POP 3 – Post Office Protocol 3 SMTP – Simple Mail Transfer Protocol Field for adding an extra email recipient without other recipients seeing. FTP – File Transfer Protocol Supplies a connection to the internet, such as BT Broadband. BCC – Blind Carbon Copy Technical term for a web address. ISP – Internet Service Provider The standard protocol for sending emails, which are then read using POP 3. URL – Uniform Resource Locator The standard protocol for receiving emails. Protocol used to transfer files from one host to another over a network such as the internet. Cookies Small text-based files created by visiting websites and stored on a local machine.
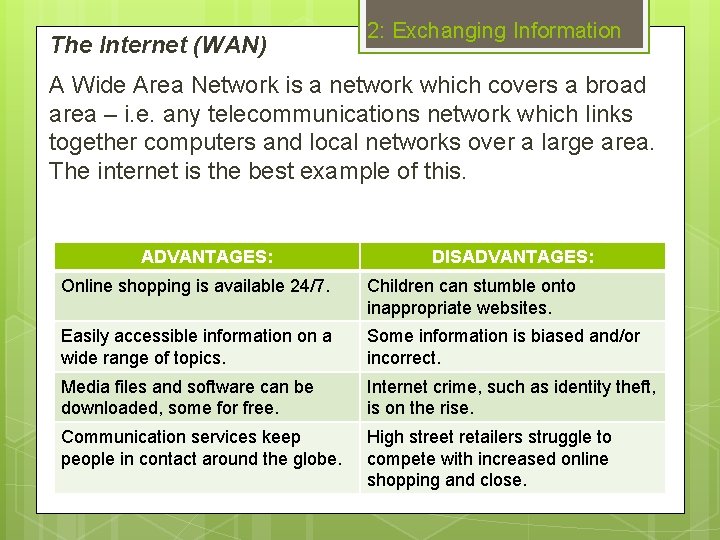
The Internet (WAN) 2: Exchanging Information A Wide Area Network is a network which covers a broad area – i. e. any telecommunications network which links together computers and local networks over a large area. The internet is the best example of this. ADVANTAGES: DISADVANTAGES: Online shopping is available 24/7. Children can stumble onto inappropriate websites. Easily accessible information on a wide range of topics. Some information is biased and/or incorrect. Media files and software can be downloaded, some for free. Internet crime, such as identity theft, is on the rise. Communication services keep people in contact around the globe. High street retailers struggle to compete with increased online shopping and close.
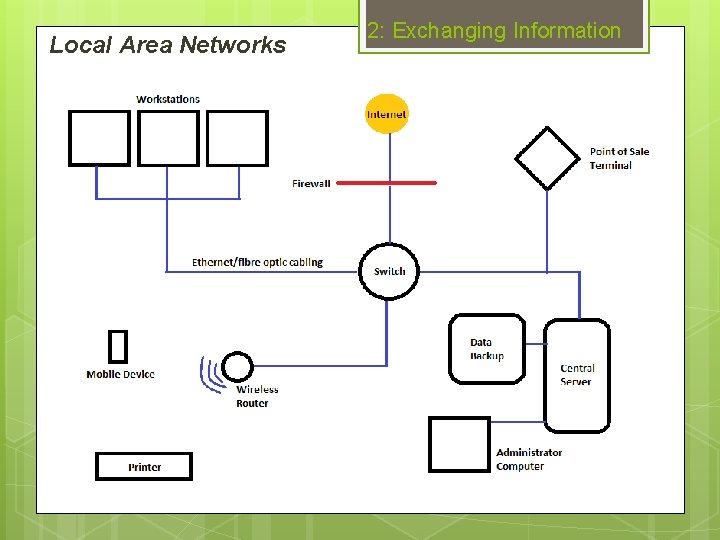
Local Area Networks 2: Exchanging Information

Control and Monitoring 2: Exchanging Information

New Technologies 2: Exchanging Information
Worked Exam Questions 1. 2. 2: Exchanging Information State 2 pieces of technology which are likely to be found in a office building’s Local Area Network. (2) Give a technical description of how emails are sent and received. (2) Question 1 Any 2 of the following for 1 mark each: Switch, workstation (computer), Wi-Fi router, backup server, printer, mobile devices. Question 2 Mention of SMTP for sending (1) Mention of POP 3 for receiving (1)
3: Presenting Information 3. 1: Word Processing and DTP 3. 2: Slideshows and Multimedia 3. 3: Web Authoring 3. 4: Image Manipulation 3. 5: Integrating Information

WP and DTP 3: Presenting Information Features common to both: Headings Borders Tables Grouping… Word Processing Desktop Publishing Letters Posters Essays Leaflets Memos Business Cards Reports Magazines
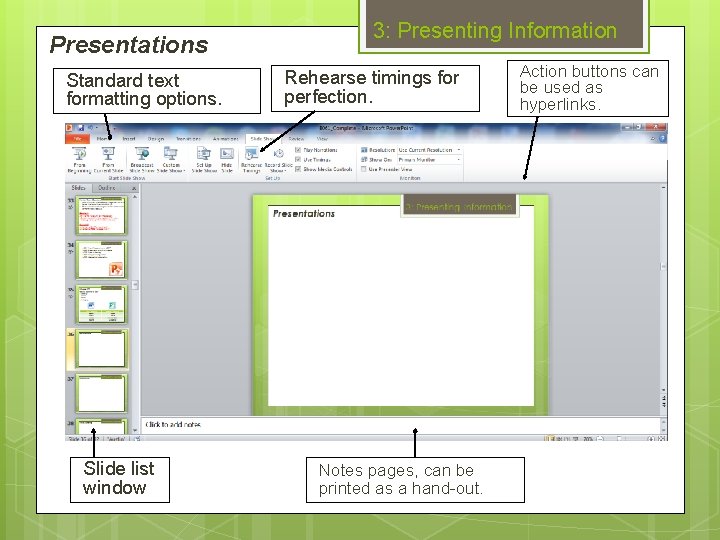
Presentations Standard text formatting options. Slide list window 3: Presenting Information Rehearse timings for perfection. Notes pages, can be printed as a hand-out. Action buttons can be used as hyperlinks.
Multimedia 3: Presenting Information What unique features of multimedia software can you identify from the screenshot?
Web Authoring 3: Presenting Information Web authoring software is a type of application which is used for creating webpages. They include features such as: Design/HTML views Flash tools Java. Script elements RSS feeds Counters Test environments FTP support. Web 2. 0 – Interactive website elements, sometimes called dynamic content, such as search boxes.

Image Manipulation 3: Presenting Information Software for the specific task of editing picture files. Features include: Filters Layers Selection Cropping Morphing Colour balance Air brush Cloning Resizing.

Integrating Information 3: Presenting Information 2 main methods for moving and linking data between and within software packages: Copy and paste User selects data which is then saved in a temporary area known as the clipboard. Held data can then be inserted into the desired location. Object A Linking and Embedment sophisticated method for sharing data between 2 applications. The link is kept updated, so if changes made to a linked-from file, these will be reflected in the linked-to file.
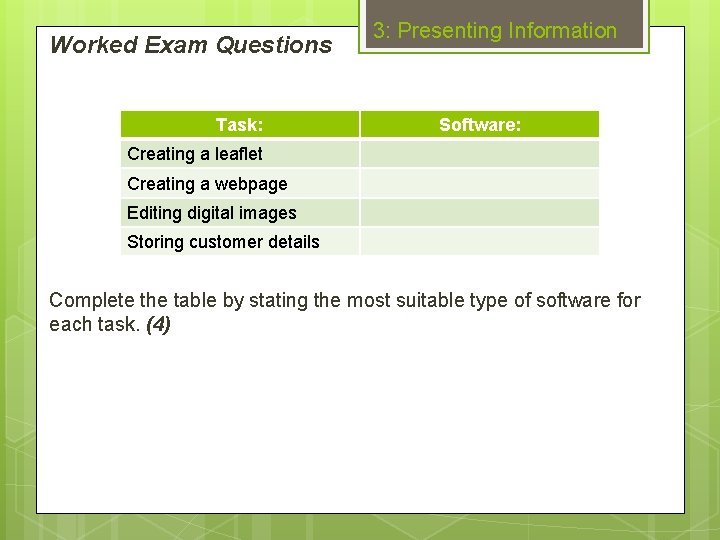
Worked Exam Questions Task: 3: Presenting Information Software: Creating a leaflet Creating a webpage Editing digital images Storing customer details Complete the table by stating the most suitable type of software for each task. (4)
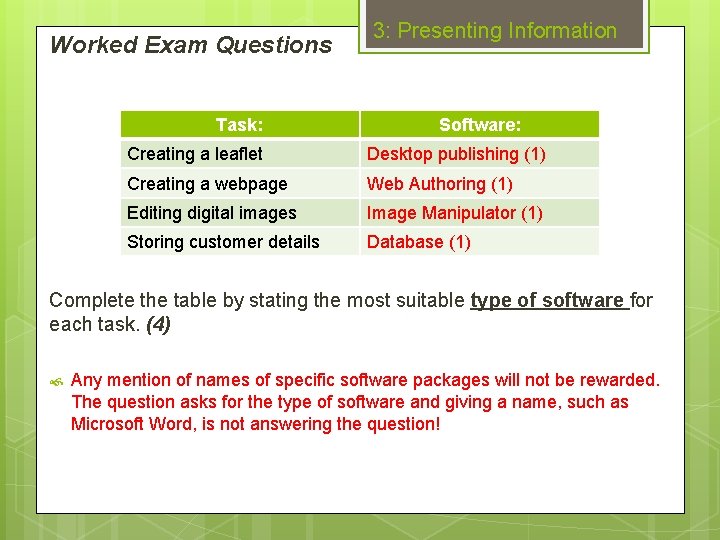
Worked Exam Questions Task: 3: Presenting Information Software: Creating a leaflet Desktop publishing (1) Creating a webpage Web Authoring (1) Editing digital images Image Manipulator (1) Storing customer details Database (1) Complete the table by stating the most suitable type of software for each task. (4) Any mention of names of specific software packages will not be rewarded. The question asks for the type of software and giving a name, such as Microsoft Word, is not answering the question!

Worked Exam Questions 3: Presenting Information Explain how multimedia features of presentation software can be used to enhance a presentation. (6) 1 mark, up to a maximum of 3, for stating multimedia features of presentation software, such as: Additional mark for each explanation, for example: Hyperlinks (1) Voice-over (1) Images (1) Animation sequences(1) Pictures and images (1) can be used in the presentation to demonstrate or convey visually what is being said, making it more understandable for the reader (1). No credit for mentioning non-multimedia features, such as text formatting.

4: Manipulating Data 4. 1: Data Types 4. 2: Data Capture 4. 3: Spreadsheets 4. 4: Databases 4. 5: Validation and Verification

4: Manipulating Data Types Alphanumeric Numerical Date/Time Image Boolean
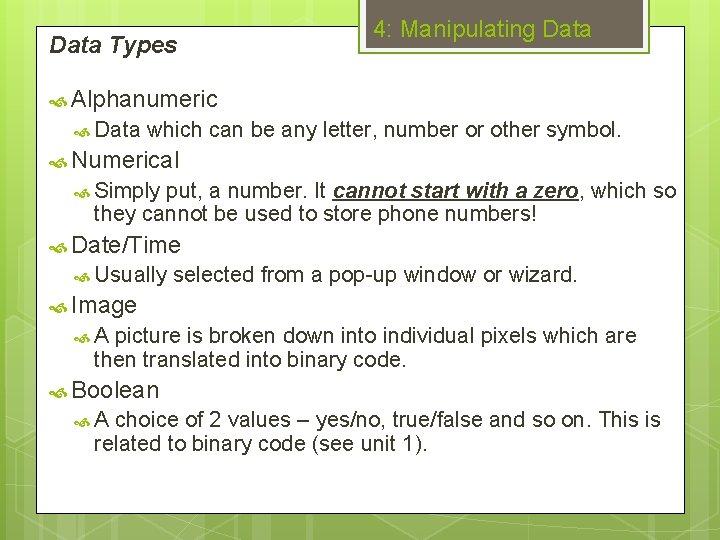
Data Types 4: Manipulating Data Alphanumeric Data which can be any letter, number or other symbol. Numerical Simply put, a number. It cannot start with a zero, which so they cannot be used to store phone numbers! Date/Time Usually selected from a pop-up window or wizard. Image A picture is broken down into individual pixels which are then translated into binary code. Boolean A choice of 2 values – yes/no, true/false and so on. This is related to binary code (see unit 1).
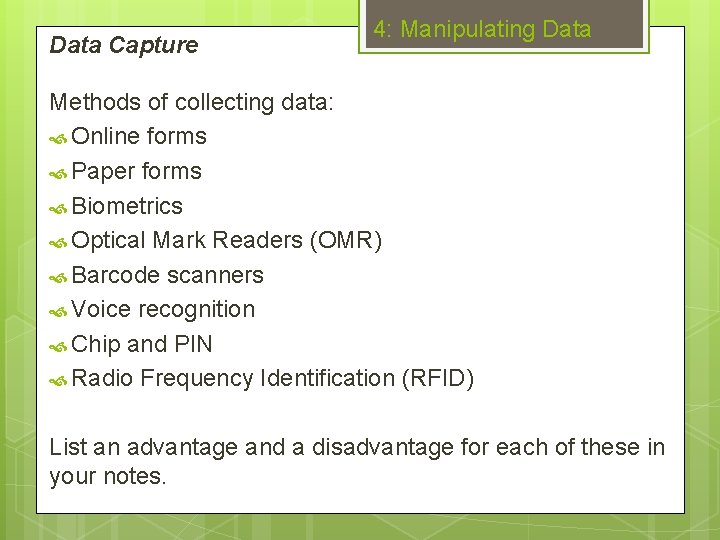
Data Capture 4: Manipulating Data Methods of collecting data: Online forms Paper forms Biometrics Optical Mark Readers (OMR) Barcode scanners Voice recognition Chip and PIN Radio Frequency Identification (RFID) List an advantage and a disadvantage for each of these in your notes.

Spreadsheets 4: Manipulating Data Spreadsheet – a table of values displayed as a grid with rows and columns. Formulae and functions Automatic recalculation Sorting data Charts and graphs Programmable macros Data modelling.
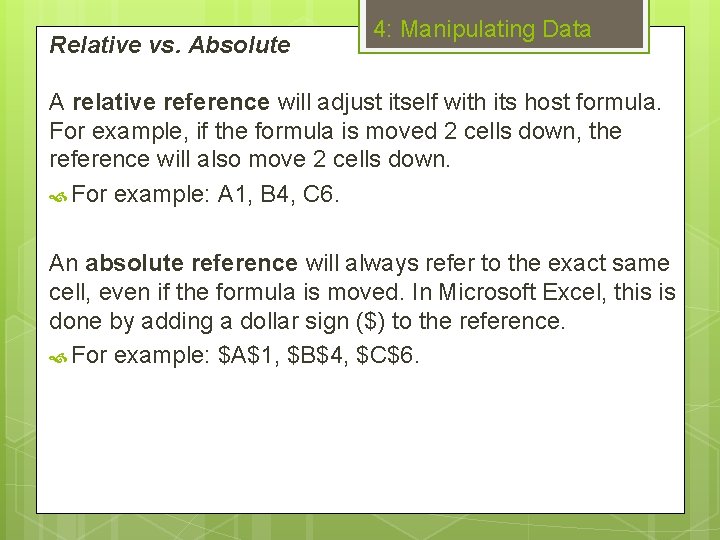
Relative vs. Absolute 4: Manipulating Data A relative reference will adjust itself with its host formula. For example, if the formula is moved 2 cells down, the reference will also move 2 cells down. For example: A 1, B 4, C 6. An absolute reference will always refer to the exact same cell, even if the formula is moved. In Microsoft Excel, this is done by adding a dollar sign ($) to the reference. For example: $A$1, $B$4, $C$6.

Analysing Data 4: Manipulating Data A spreadsheet model is where a series of equations are inserted into a spreadsheet to simulate a real situation. This can be used to make informed financial decisions. Modelling tools include: Goal seek Scenario manager Data table. This are known as scenario manager tools – they can be used to set up various situations to see how the data changes under certain conditions.

Flat-File Databases 4: Manipulating Data Define these key database terms: Field Record Report Query Form

Flat-File Databases 4: Manipulating Data Define these key terms: Field – one piece of data about a database object. Record – collection of fields about a database object. Report – method of summarising and presenting information from a database. Query – requests for information, created using set criteria. Form – interactive and more user-friendly method of database interaction. In a flat-file database, all of the data is contained in a single table. Whilst they are simple and straightforward to use, they become difficult to manage when the amount of data becomes too much or too varied.

Relational Databases 4: Manipulating Data Primary Key – A means of identifying records in a table. Usually a field with some variety of ID number. Foreign Key - A field in one relational table which is matched to the primary key of another, used to create the relationship. One-to-One Relationship – Where one record in a relational table matches to only one other in another table. Many-to-One Relationship – Where a record in a relational table matches up to multiple others in another table.

Relational Databases 4: Manipulating Data Many-to-One relationships in Microsoft Access. For example, a single customer (the ‘one’) can have many seats booked in their name (the ‘many’).

Relational Databases 4: Manipulating Data Why use a relational database? Input effort is reduced Increased reliability of data Reduced data redundancy (as data is only stored once). However they are complex – both to create and troubleshoot.
Checking Data 4: Manipulating Data VALIDATION – ensuring that data is sensible, reasonable, complete and within acceptable boundaries. An example is when you set up a condition which ensures that a person’s name only includes letters. Includes: presence, data type, length, range and format checks. VERIFICATION – checking that the data which has been inputted is identical to the original. An example is when you are forced to enter a new password twice (double keying) to ensure they are both the same.

Worked Exam Questions 4: Manipulating Data Explain the advantages of using a relational database over a flat file database. (4) Any two of the following pairs of statements for full marks: Input effort is reduced (1) Data is entered once, making them easier and more convenient to use (1). Reduced As data redundancy (1) data is stored once and then used when needed (1). Improved data reliability (1) Because data is entered once, variations and mistakes are reduced (1).

Worked Exam Questions 4: Manipulating Data The image shows a spreadsheet made in Microsoft Excel. 1. Give the reference of a cell which contains: 1. A value (1) 2. A formula (1) 2. How can the data in column B be checked to ensure it is correct? You will gain marks for using the correct specialist terms in your answer. (3)

Worked Exam Questions 1. 2. 3. 4: Manipulating Data B/C 4 -14, G/H 4 -12 (1) B 1 (1) It can be validated (1) by setting up a data type check (1) to ensure that the inputted data is a date (1).

5: Data Security 5. 1: Backups and Archiving 5. 2: Protecting Data 5. 3: Encryption 5. 4: Malware 5. 5: Hacking
Backups and Archiving 5: Data Security BACKUP – a copy of a file which is separately from the original and can be used to replace the original if it is lost or corrupted. ARCHIVE – a collection of outdated backups which make up a record of a file’s history. When creating a backup or archive, it is important to consider the following: What data needs to be backed up? How often does the backup need to be created? Where will the data be stored?

Physical Methods 5: Data Security

Virtual Methods 5: Data Security
Protecting Data Challenge 5: Data Security You are in charge of security at a large corporation. At this company, data is stored on a central server with USB drives commonly used by staff. There are no facilities for securely storing these devices. There have been a recent spate break-ins which have led to data being stolen. The data have been in a variety of formats, from USB memory sticks to the secondary storage drives themselves. Several attacks from anonymous hacking groups have also led to data being compromised.
Protecting Data Challenge 5: Data Security You are to design a system which will keep the data secure from break-ins and “hack-attacks”. Your solution should include: Physical methods Virtual methods Any relevant human factors.
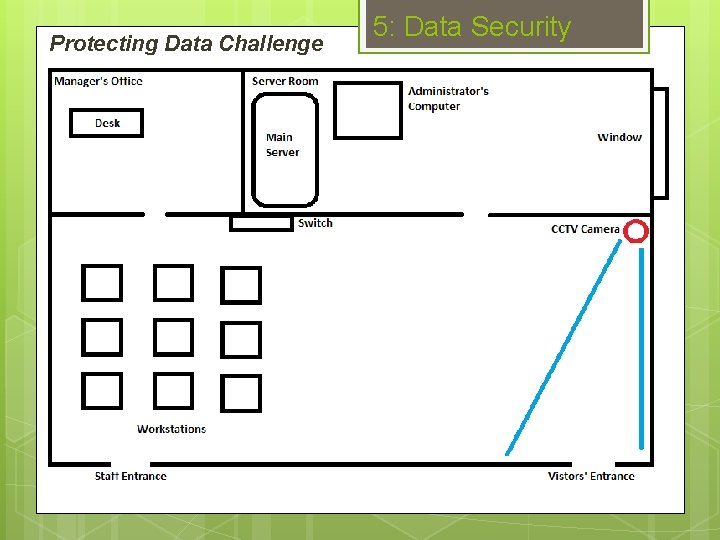
Protecting Data Challenge 5: Data Security

Protecting Data Challenge 5: Data Security The answer? PHYSICAL METHODS VIRTUAL METHODS HUMAN FACTORS CCTV cameras Strong passwords Increased secrecy Coded doors Honeypots Must secure USB keys Safes Firewalls Receptionist Secured workstations Antivirus Log USB movements Alarm system IDS Increased guard patrols Secured switches Access rights
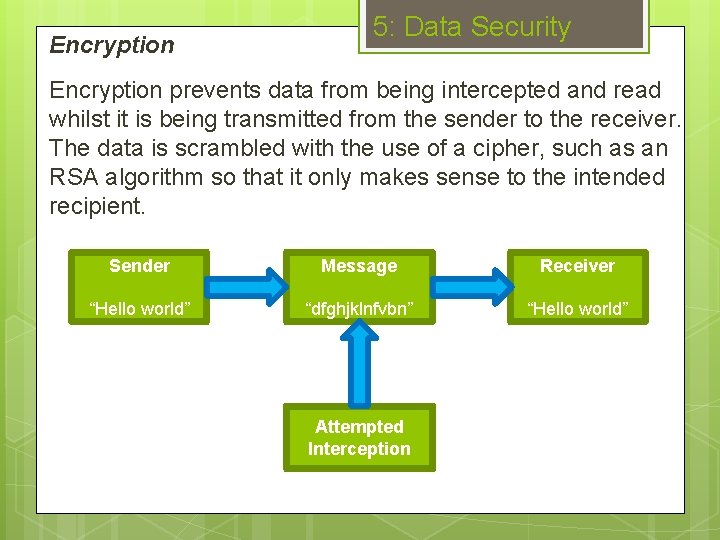
Encryption 5: Data Security Encryption prevents data from being intercepted and read whilst it is being transmitted from the sender to the receiver. The data is scrambled with the use of a cipher, such as an RSA algorithm so that it only makes sense to the intended recipient. Sender Message Receiver “Hello world” “dfghjklnfvbn” “Hello world” Attempted Interception
Malware 5: Data Security MALWARE – software which has an adverse effect on a computer system. It is usually installed without the user’s knowledge or consent, and can have a wide range of effects. Some can simply display annoying advertisements (adware), whilst others will multiply and corrupt files. Types of malware include: Viruses Worms Trojan Horses Spyware Rootkits Adware Ransom-ware

Preventing Malware 5: Data Security You can prevent malware from being installed on your system in a number of ways: Install an anti-virus Keep it regularly updated Run regular scans Treat unknown files with caution Instantly delete spam emails.

Hacking 5: Data Security HACKING – The process of accessing (or attempting to) a computer system without authorisation (see Computer Misuse Act). Hackers will often use key-logging software, which records all of the keystrokes made by the user. This is often a simple way of stealing passwords and credit card details. The best way to prevent hackers is by installing a working firewall. Intrusion Detection Systems (IDS may also be used to monitor the network/device for unauthorised users.
6: Issues of ICT 6. 1: Computer Misuse Act 1990 6. 2: Data Protection Act 1998 6. 3: P. D. G. C. 6. 4: Copyright Design and Patents Act 1988 6. 5: EC Directive 2002 6. 6: Health and Safety 6. 7: Accessibility
Computer Misuse Act 6: Issues of ICT Level 1 - unauthorised access to programs or data as a nuisance. Level 2 - unauthorised access with a further criminal intent. Level 3 - unauthorised modification of computer data. Companies such as OCER Theatre must ensure that their systems are not used for such actions. This can involve usage policies to prevent users from accessing the necessary functions and working with authorities when a contravention does occur.
Data Protection Act 6: Issues of ICT Data subjects have the right to: Compensation for an unauthorised disclosure or inaccurate data Access data about them and have it rectified. They must be told: Why the data has to be stored Who will be able to access it How it will be collected Types of data that will be stored Anyone to whom the data may be passed on to.

Data Protection Act 6: Issues of ICT Data must be: 1. Processed lawfully 2. Held for a specific purpose 3. Adequate, relevant and not excessive 4. Kept accurate 5. Not kept longer than necessary 6. Processed in accordance with the subject 7. Held securely 8. Not transferred outside of Europe. This excludes crime, research, tax and accounts data – such as police records and the census. Come up with an action that OCER Theatre must take for each principle.
P. D. G. C. Stands 6: Issues of ICT for Personal Data Guardianship Code. A social awareness guidance rather than a legal act. Covers: Accountability Visibility Consent Access Stewardship Responsibility.
Copyright Design and Patents Act 1988 6: Issues of ICT This act was introduced to protect the intellectual property of both individuals and organisations. It makes it illegal to make unauthorised downloads or to use copyrighted files without the correct permission. OCER Theatre must ensure that they have the correct permissions to use any music they play during intervals and images used in programs. They also must ensure that they possess the correct software licensing: Single-user – one machine may run the software. Multi-user – several machines may run it. Site License – everyone with network access may use the software.
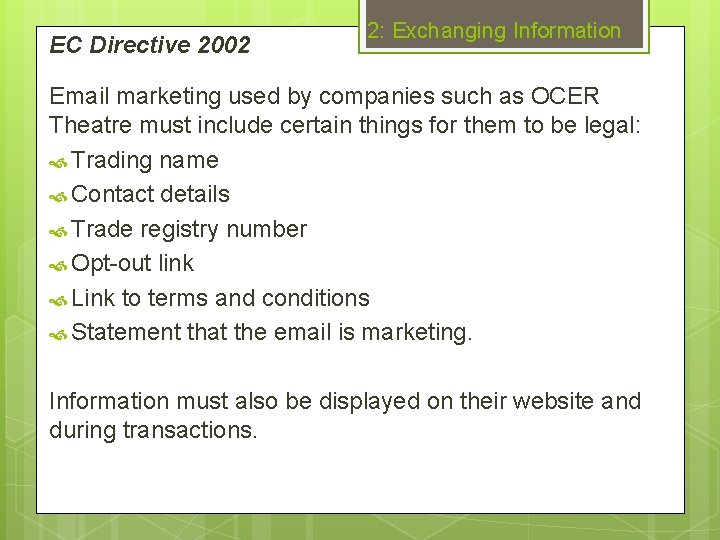
EC Directive 2002 2: Exchanging Information Email marketing used by companies such as OCER Theatre must include certain things for them to be legal: Trading name Contact details Trade registry number Opt-out link Link to terms and conditions Statement that the email is marketing. Information must also be displayed on their website and during transactions.

Health and Safety 6: Issues of ICT
Accessibility 6: Issues of ICT There are various features of ICT, both hardware and software, which have been designed to aid people with disabilities: Screen filters Magnifiers Braille keyboards Voice control Adjustable height desks.
Worked Exam Questions 6: Issues of ICT The following question is an example of an extended writing question. These are worth 8 marks and there will generally be two of them in the B 061 AND the B 063 exam. They are also marked differently – using descriptions of different levels of achievement. Answering a question like this fully and within the time you have requires you to pick out EXACTLY what is required from the question, as is shown on the next slide.

Worked Exam Questions 6: Issues of ICT Irrelevant! Many companies store the personal details of their customers. WHAT and HOW Explain how the Data Protection Act tries to protect the rights of customers. Your quality of written communication will be assessed as part of your answer. (8) Spelling, grammar, key terms Subject matter What are its aims? 8 marks – at least 4 different developed points
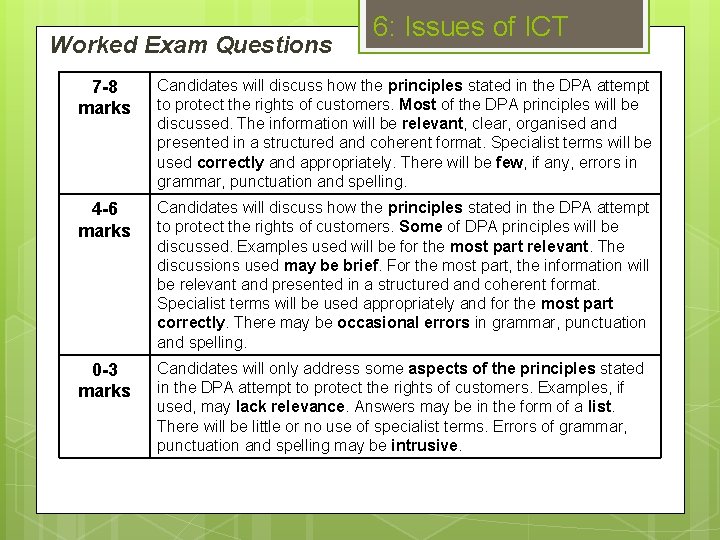
Worked Exam Questions 6: Issues of ICT 7 -8 marks Candidates will discuss how the principles stated in the DPA attempt to protect the rights of customers. Most of the DPA principles will be discussed. The information will be relevant, clear, organised and presented in a structured and coherent format. Specialist terms will be used correctly and appropriately. There will be few, if any, errors in grammar, punctuation and spelling. 4 -6 marks Candidates will discuss how the principles stated in the DPA attempt to protect the rights of customers. Some of DPA principles will be discussed. Examples used will be for the most part relevant. The discussions used may be brief. For the most part, the information will be relevant and presented in a structured and coherent format. Specialist terms will be used appropriately and for the most part correctly. There may be occasional errors in grammar, punctuation and spelling. 0 -3 marks Candidates will only address some aspects of the principles stated in the DPA attempt to protect the rights of customers. Examples, if used, may lack relevance. Answers may be in the form of a list. There will be little or no use of specialist terms. Errors of grammar, punctuation and spelling may be intrusive.
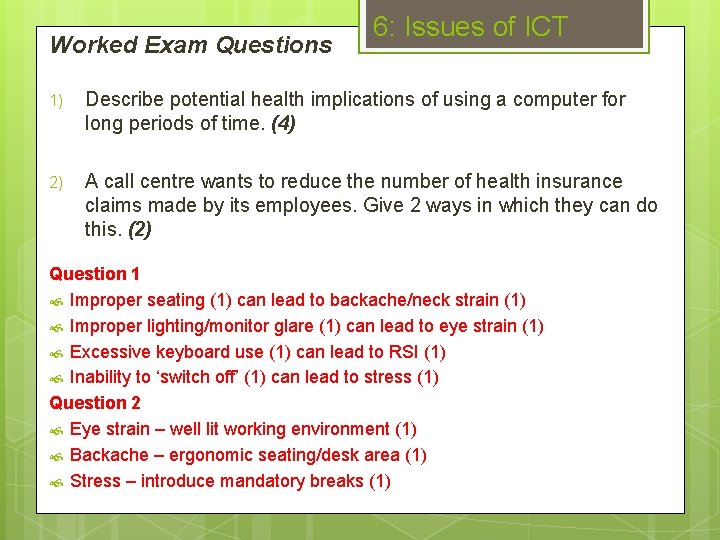
Worked Exam Questions 6: Issues of ICT 1) Describe potential health implications of using a computer for long periods of time. (4) 2) A call centre wants to reduce the number of health insurance claims made by its employees. Give 2 ways in which they can do this. (2) Question 1 Improper seating (1) can lead to backache/neck strain (1) Improper lighting/monitor glare (1) can lead to eye strain (1) Excessive keyboard use (1) can lead to RSI (1) Inability to ‘switch off’ (1) can lead to stress (1) Question 2 Eye strain – well lit working environment (1) Backache – ergonomic seating/desk area (1) Stress – introduce mandatory breaks (1)
7: Using ICT Systems 7. 1: How ICT is Used 7. 2: Troubleshooting
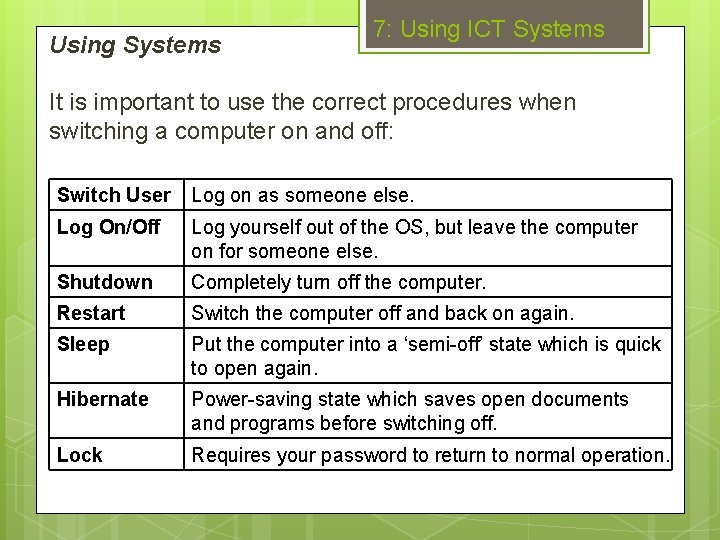
Using Systems 7: Using ICT Systems It is important to use the correct procedures when switching a computer on and off: Switch User Log on as someone else. Log On/Off Log yourself out of the OS, but leave the computer on for someone else. Shutdown Completely turn off the computer. Restart Switch the computer off and back on again. Sleep Put the computer into a ‘semi-off’ state which is quick to open again. Hibernate Power-saving state which saves open documents and programs before switching off. Lock Requires your password to return to normal operation.
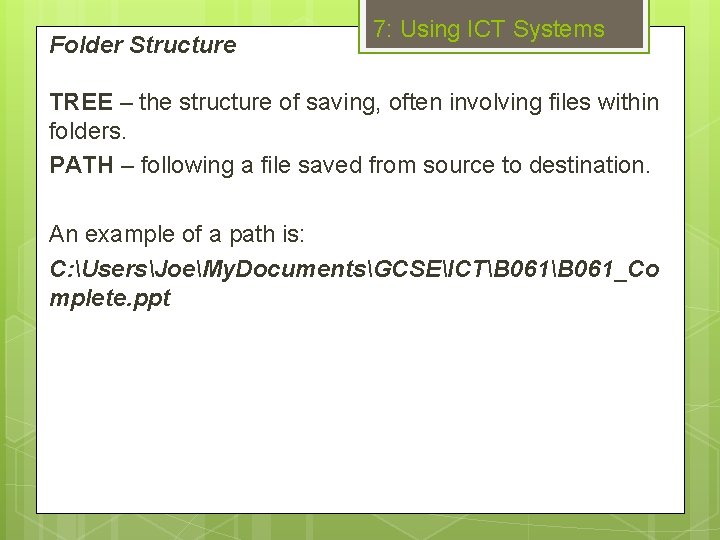
Folder Structure 7: Using ICT Systems TREE – the structure of saving, often involving files within folders. PATH – following a file saved from source to destination. An example of a path is: C: UsersJoeMy. DocumentsGCSEICTB 061_Co mplete. ppt
Filenames 7: Using ICT Systems A filename consists of the actual name and the extension, which denotes the program used to open the file. Examples of extensions include: . docx – Microsoft Word . jpeg – Paint, Adobe Photoshop… . mp 3 – Windows Media Player . css – Adobe Dreamweaver When naming a file or folder, the name should always be reflective of its contents. This allows you to easily find saved files, and prevents accidental deletion.

7: Using ICT Systems Troubleshooting Symptom: Problem: Solution: Blue Screen Hardware failure Reinstall or replace the faulty part. No display Loose cable Properly plug in the cable to the correct port. Software freeze Not enough CPU or RAM available. Ctrl-Alt-Del then end the process. Endless looping at system start-up. BIOS attempting to load OS from removable storage media. Unplug all removable storage devices. Files do not print. Paper jam Gently pull out the offending piece of paper.
8: Monitoring and Control 8. 1: Sensors 8. 2: Data Logging 8. 3: Controlling Devices
Sensors 8: Monitoring and Control SENSOR – a device which measures a physical quantity. Sensors almost always record data in analogue form, and so the data has to first be converted before it can be processed by a computer system. Common quantities which sensors measure include: Temperature Light Pressure.

Data Logging Computer 8: Monitoring and Control Interface Box Sensor A computer is attached to a sensor and is left to collect data over a period of time with little to no human intervention. ADVANTAGES: DISADVANTAGES: Fast and accurate readings. Interference can affect the data. Functions constantly. Equipment can be expensive. Can be used remotely and in hazardous environments. Only a single link in the chain has to be broken for it all to fail.
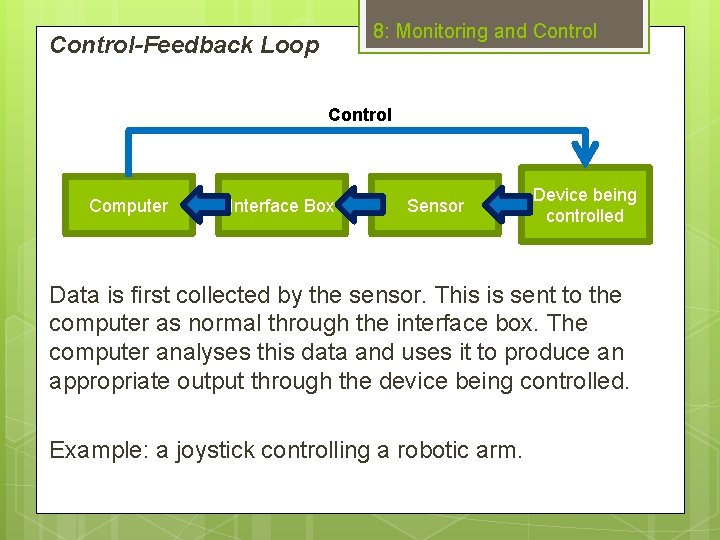
8: Monitoring and Control-Feedback Loop Control Computer Interface Box Sensor Device being controlled Data is first collected by the sensor. This is sent to the computer as normal through the interface box. The computer analyses this data and uses it to produce an appropriate output through the device being controlled. Example: a joystick controlling a robotic arm.
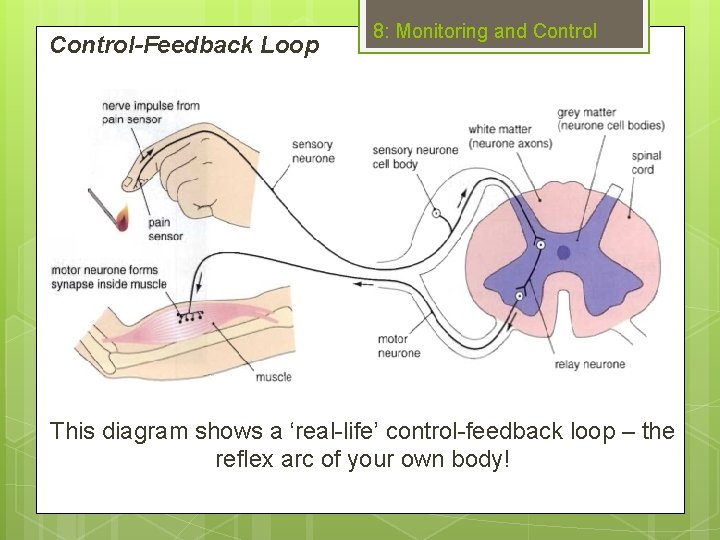
Control-Feedback Loop 8: Monitoring and Control This diagram shows a ‘real-life’ control-feedback loop – the reflex arc of your own body!

Controlled Devices 8: Monitoring and Control
Worked Exam Questions 8: Monitoring and Control 1. Explain how a control-feedback loop works. (3) 2. State 2 examples of devices which can be controlled. (2) Question 1: Data is gathered by a sensor (1), and then sent to the computer. The computer analyses the data (1) and uses it to produce an appropriate output through the controlled device (1). Question 2: Any 2 for 1 mark each: Buzzer Light Actuator Etc.
9: ICT and Modern Living 9. 1: Online Services 9. 2: Employment 9. 3: Collaboration 9. 4: The Internet 9. 5: Leisure 9. 6: The Future of ICT
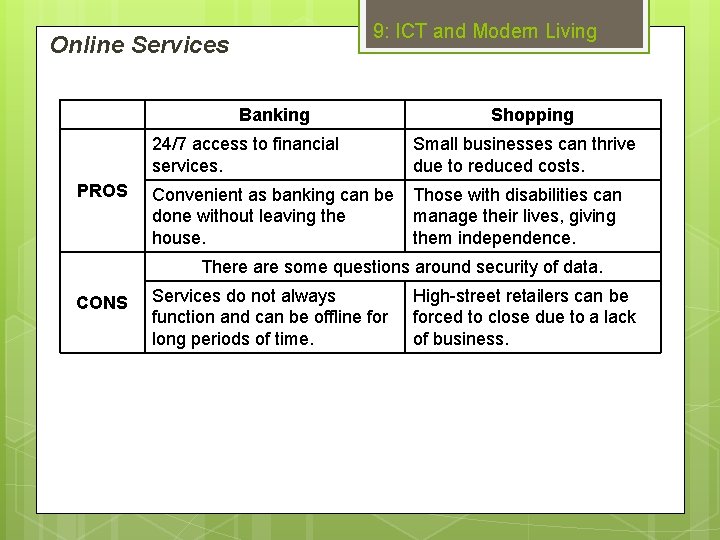
9: ICT and Modern Living Online Services Banking PROS Shopping 24/7 access to financial services. Small businesses can thrive due to reduced costs. Convenient as banking can be done without leaving the house. Those with disabilities can manage their lives, giving them independence. There are some questions around security of data. CONS Services do not always function and can be offline for long periods of time. High-street retailers can be forced to close due to a lack of business.

Employment 9: ICT and Modern Living The increased use of ICT in workplaces have led to changing patterns of employment: Increased working from home. Tasks have been made faster and easier. Roles with flexible hours are ever-more common. Some sectors have seen increased unemployment.
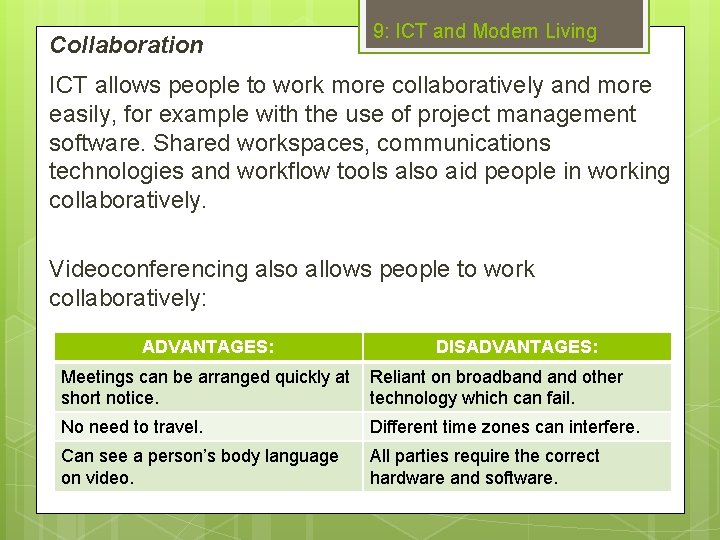
Collaboration 9: ICT and Modern Living ICT allows people to work more collaboratively and more easily, for example with the use of project management software. Shared workspaces, communications technologies and workflow tools also aid people in working collaboratively. Videoconferencing also allows people to work collaboratively: ADVANTAGES: DISADVANTAGES: Meetings can be arranged quickly at short notice. Reliant on broadband other technology which can fail. No need to travel. Different time zones can interfere. Can see a person’s body language on video. All parties require the correct hardware and software.
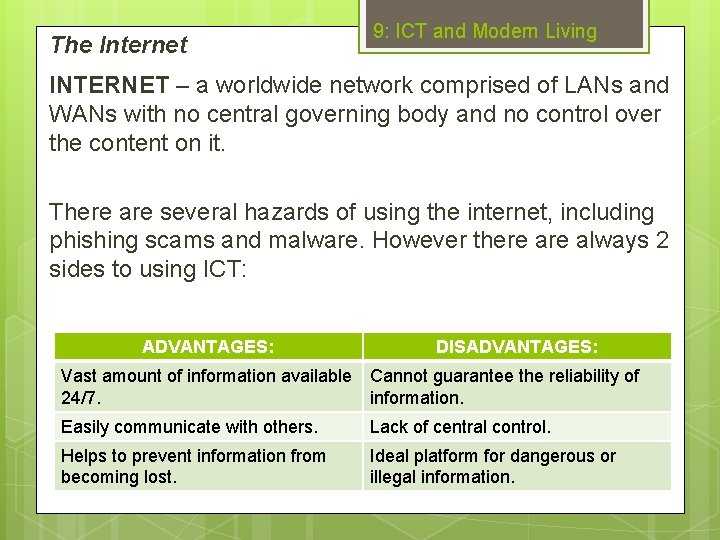
The Internet 9: ICT and Modern Living INTERNET – a worldwide network comprised of LANs and WANs with no central governing body and no control over the content on it. There are several hazards of using the internet, including phishing scams and malware. However there always 2 sides to using ICT: ADVANTAGES: DISADVANTAGES: Vast amount of information available Cannot guarantee the reliability of 24/7. information. Easily communicate with others. Lack of central control. Helps to prevent information from becoming lost. Ideal platform for dangerous or illegal information.
Leisure 9: ICT and Modern Living How has ICT changed the way that people spend their leisure time? People may interact face-to-face less. Increased use of ICT devices for chores. Use of computers for research. Health implications – back problems, eyestrain. Health related uses – training, measuring parameters. Do not have to travel for entertainment. Stay in contact with friends over long distances. Harder to ‘switch-off’ and de-stress. Sort these into positive and negatives, giving a reason for your choice.

Leisure 9: ICT and Modern Living Positives Increased use of ICT devices for chores: Use of computers for research: Help keep fit more easily. Do not have to travel for entertainment: Find a range of relevant information faster and with more convenience. Health related uses – training, measuring parameters: Which frees up time for other pursuits. Which makes it easier and more convenient. Communicate with friends over long distances: Stay in contact despite the physical divide. Negatives Harder to ‘switch-off’ and de-stress: People may interact face-to-face less: Can lead to stress-related illnesses. Leading to greater social reclusion. Health implications – back problems, eyestrain: Depends on the implication but generally can lead to great pain.
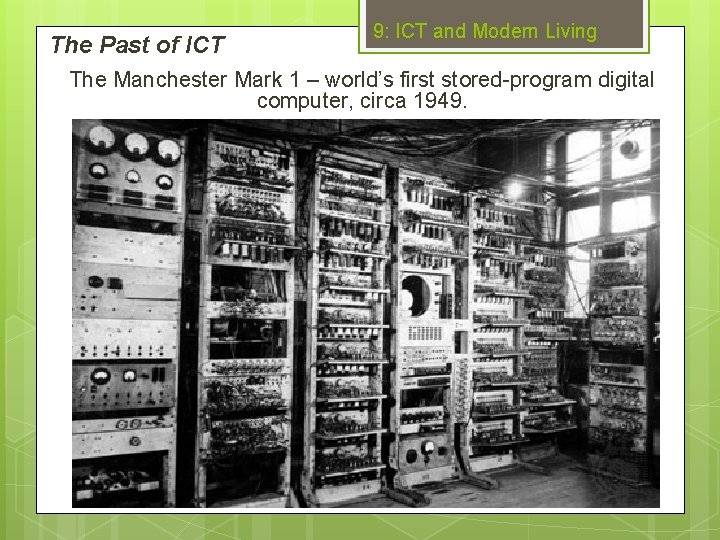
The Past of ICT 9: ICT and Modern Living The Manchester Mark 1 – world’s first stored-program digital computer, circa 1949.

The Past of ICT 9: ICT and Modern Living The Macbook Air – 2014.

9: ICT and Modern Living The Past of ICT It took just 65 years to go from a computer the size of a building to one that you can keep in your bag (!)

The Future of ICT Clip 1 1. 2. 9: ICT and Modern Living Clip 2 What outlooks on the future of ICT do the 2 clips show? How are these outlooks different?

The Future of ICT 9: ICT and Modern Living Research and make notes on the following topics: Google Glass Artificial Intelligence Oculus Rift Cyber Warfare. Make sure that your notes include: What they are Any positives of them Any negatives of them How they might affect the way we live our lives. Then also make a note of how you have conducted your online research and add these to your notes on ICT and education.
- Slides: 107