Azure Subscribe to Saa S applications Switch to

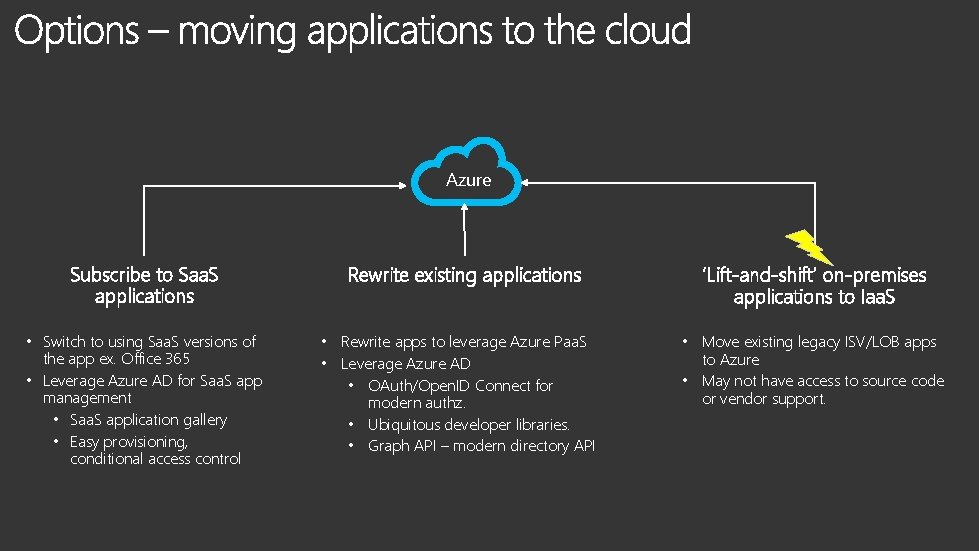
Azure Subscribe to Saa. S applications • Switch to using Saa. S versions of the app ex. Office 365 • Leverage Azure AD for Saa. S app management • Saa. S application gallery • Easy provisioning, conditional access control Rewrite existing applications • Rewrite apps to leverage Azure Paa. S • Leverage Azure AD • OAuth/Open. ID Connect for modern authz. • Ubiquitous developer libraries. • Graph API – modern directory API ‘Lift-and-shift’ on-premises applications to Iaa. S • Move existing legacy ISV/LOB apps to Azure • May not have access to source code or vendor support.
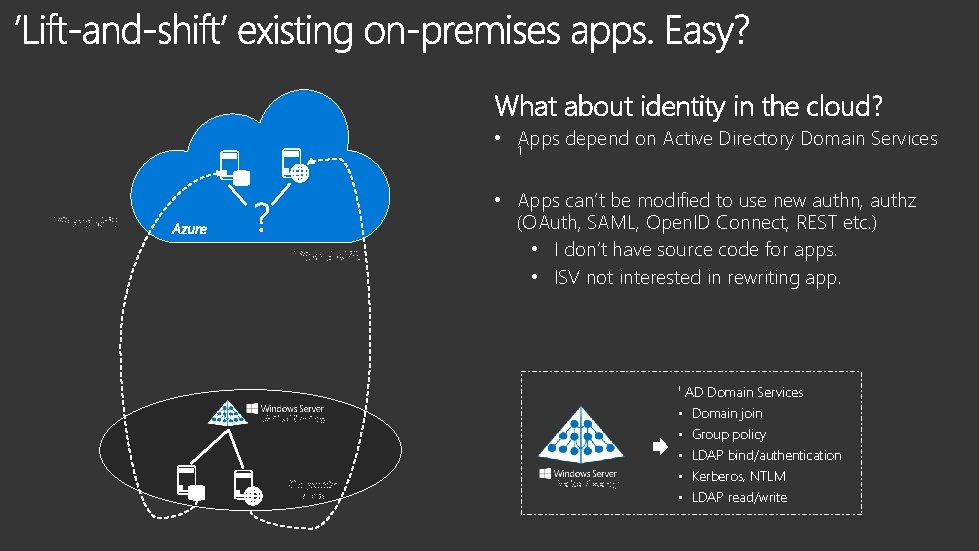
What about identity in the cloud? • Apps depend on Active Directory Domain Services 1 Lift-and-shift Azure Lift-and-shift • Apps can’t be modified to use new authn, authz (OAuth, SAML, Open. ID Connect, REST etc. ) • I don’t have source code for apps. • ISV not interested in rewriting app. 1 Active Directory On-premise apps Active Directory • • • AD Domain Services Domain join Group policy LDAP bind/authentication Kerberos, NTLM LDAP read/write
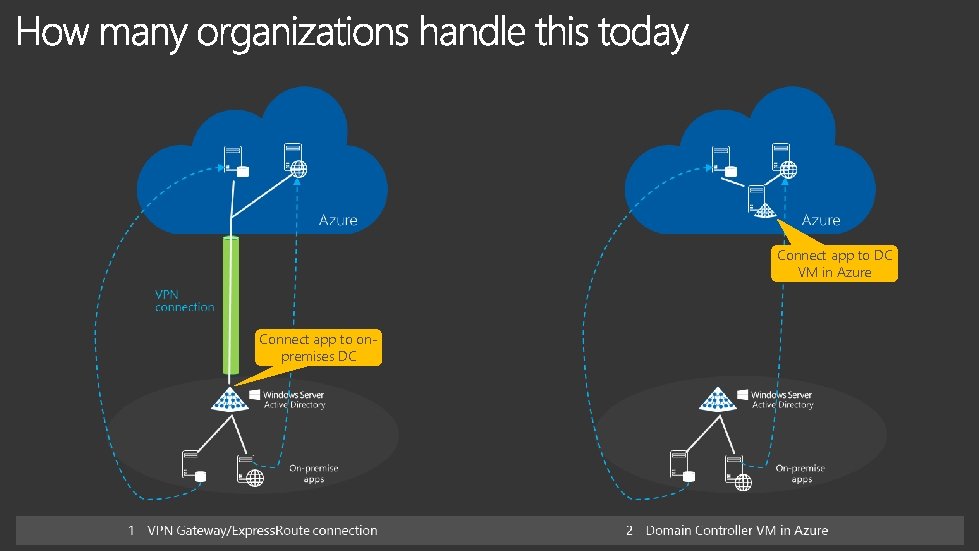
Connect app to DC VM in Azure Connect app to onpremises DC
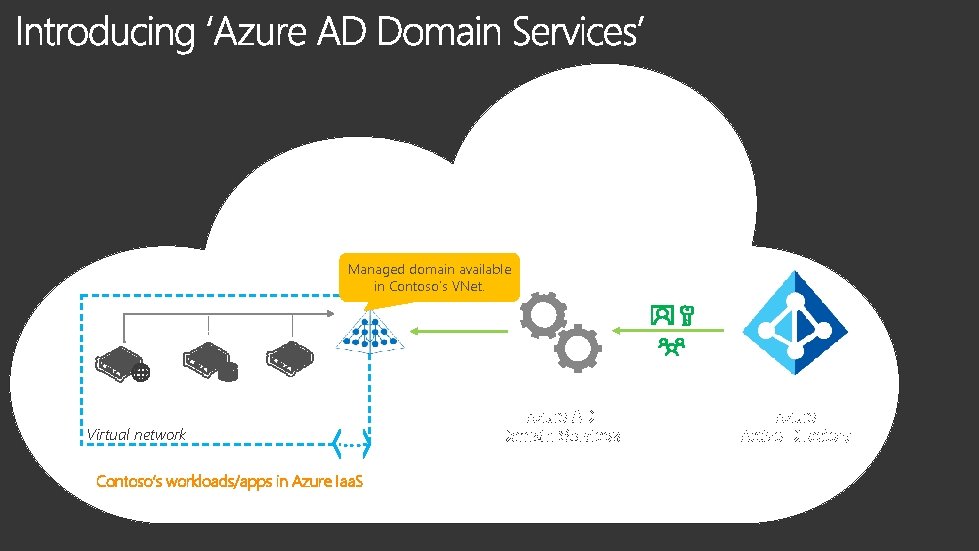
Managed domain available in Contoso’s VNet. Virtual network … Contoso’s workloads/apps in Azure Iaa. S Azure AD Domain Services Azure Active Directory
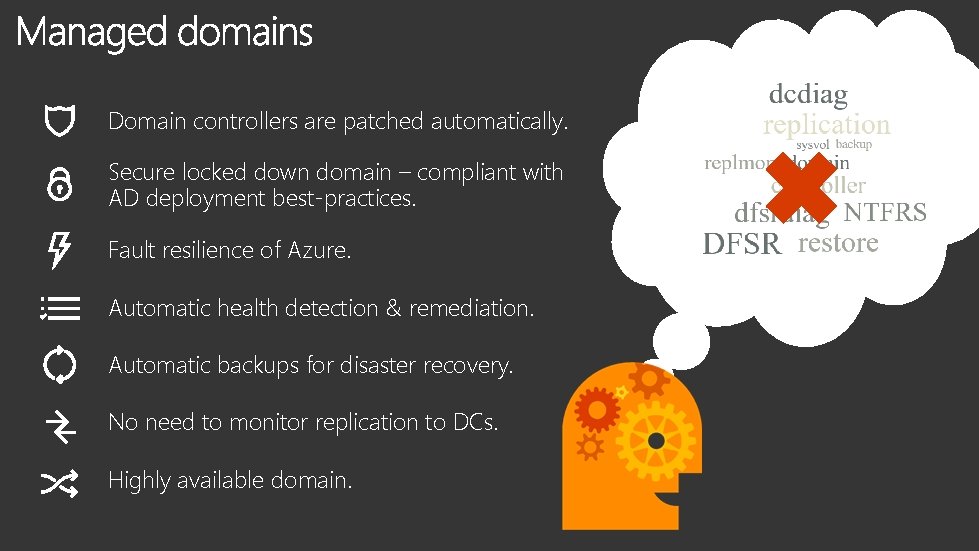
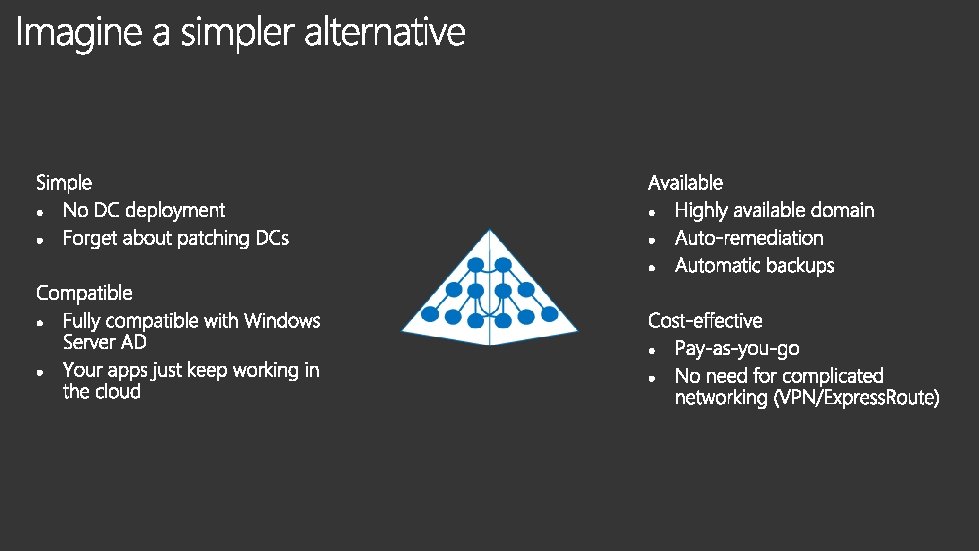
Domain controllers are patched automatically. Secure locked down domain – compliant with AD deployment best-practices. Fault resilience of Azure. Automatic health detection & remediation. Automatic backups for disaster recovery. No need to monitor replication to DCs. Highly available domain.
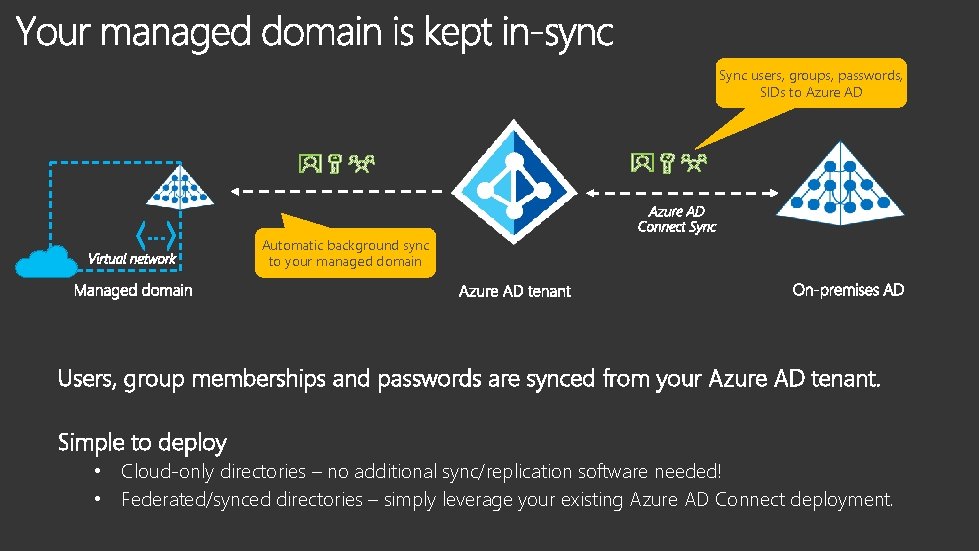
Sync users, groups, passwords, SIDs to Azure AD … Automatic background sync to your managed domain Users, group memberships and passwords are synced from your Azure AD tenant. Simple to deploy • Cloud-only directories – no additional sync/replication software needed! • Federated/synced directories – simply leverage your existing Azure AD Connect deployment.
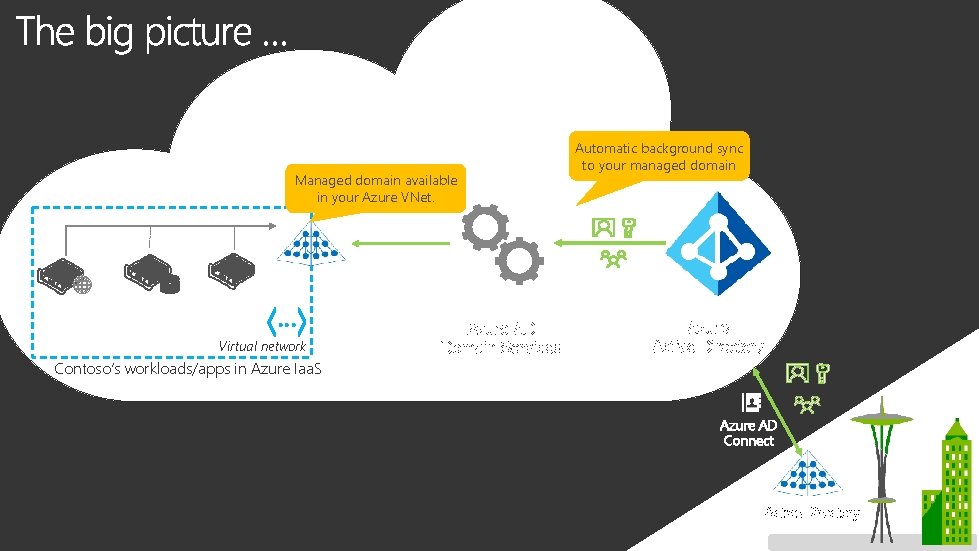
Managed domain available in your Azure VNet. … Virtual network Contoso’s workloads/apps in Azure Iaa. S Azure AD Domain Services Automatic background sync to your managed domain Azure Active Directory Azure AD Connect Active Directory
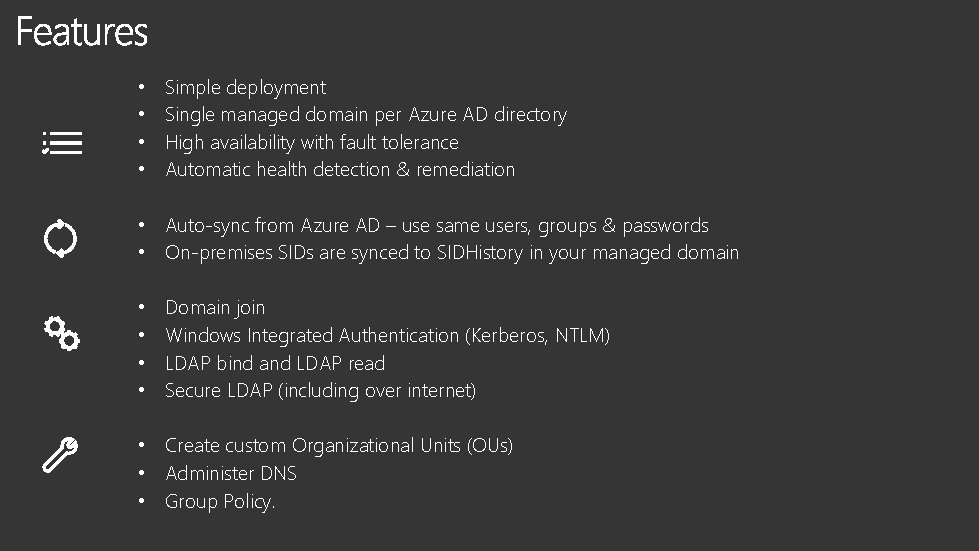
• • Simple deployment Single managed domain per Azure AD directory High availability with fault tolerance Automatic health detection & remediation • Auto-sync from Azure AD – use same users, groups & passwords • On-premises SIDs are synced to SIDHistory in your managed domain • • Domain join Windows Integrated Authentication (Kerberos, NTLM) LDAP bind and LDAP read Secure LDAP (including over internet) • Create custom Organizational Units (OUs) • Administer DNS • Group Policy.
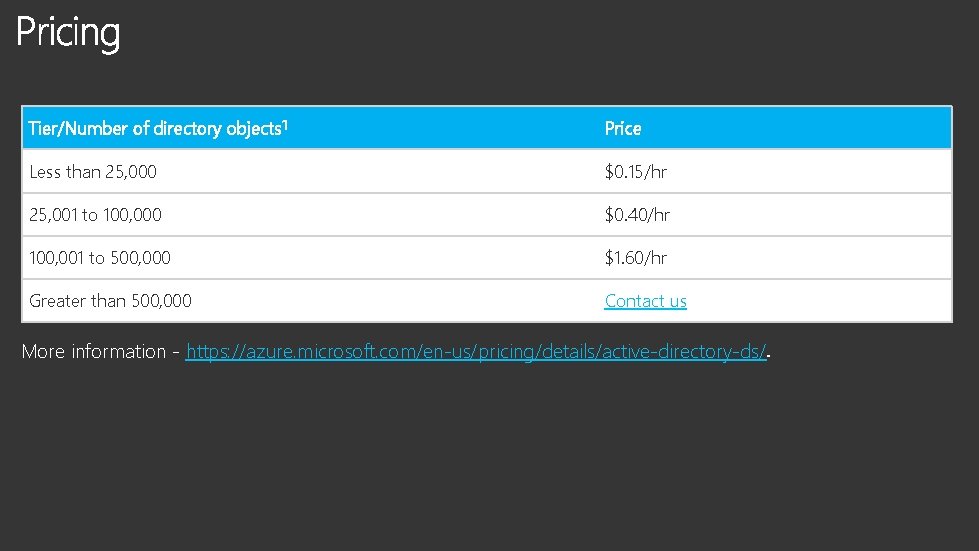
Tier/Number of directory objects 1 Price Less than 25, 000 $0. 15/hr 25, 001 to 100, 000 $0. 40/hr 100, 001 to 500, 000 $1. 60/hr Greater than 500, 000 Contact us More information - https: //azure. microsoft. com/en-us/pricing/details/active-directory-ds/
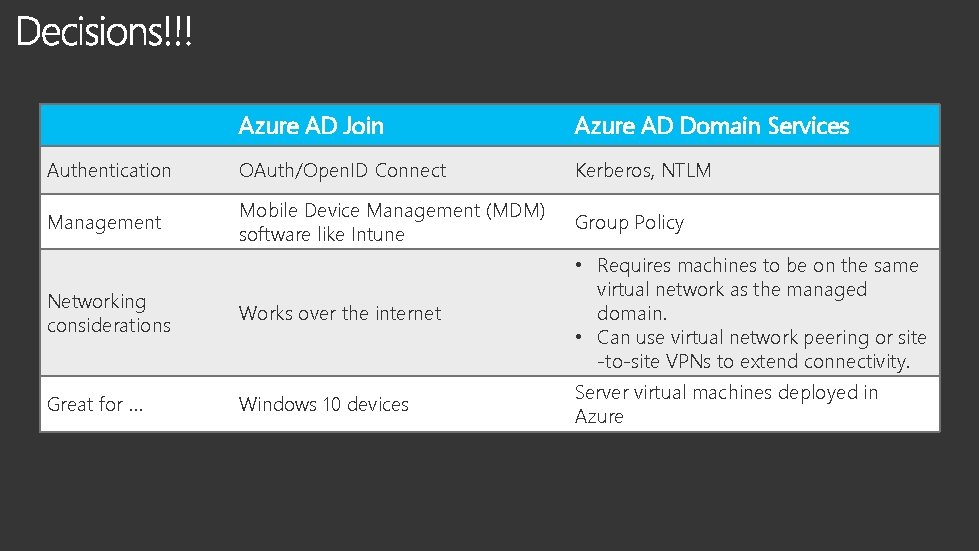
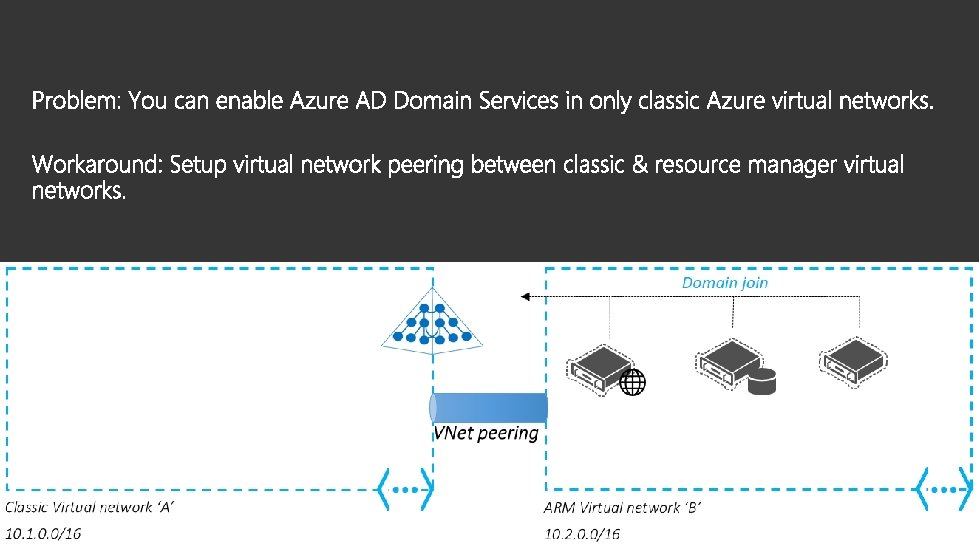
Azure AD Join Azure AD Domain Services Authentication OAuth/Open. ID Connect Kerberos, NTLM Management Mobile Device Management (MDM) software like Intune Group Policy Networking considerations Works over the internet • Requires machines to be on the same virtual network as the managed domain. • Can use virtual network peering or site -to-site VPNs to extend connectivity. Great for … Windows 10 devices Server virtual machines deployed in Azure


• Manage Azure Iaa. S virtual machines • • • ‘Lift-and-shift’ LDAP applications ‘Lift-and-shift’ Kerberos applications ‘Lift-and-shift’ Share. Point server Domain-joined HDInsight clusters Remote desktop deployments
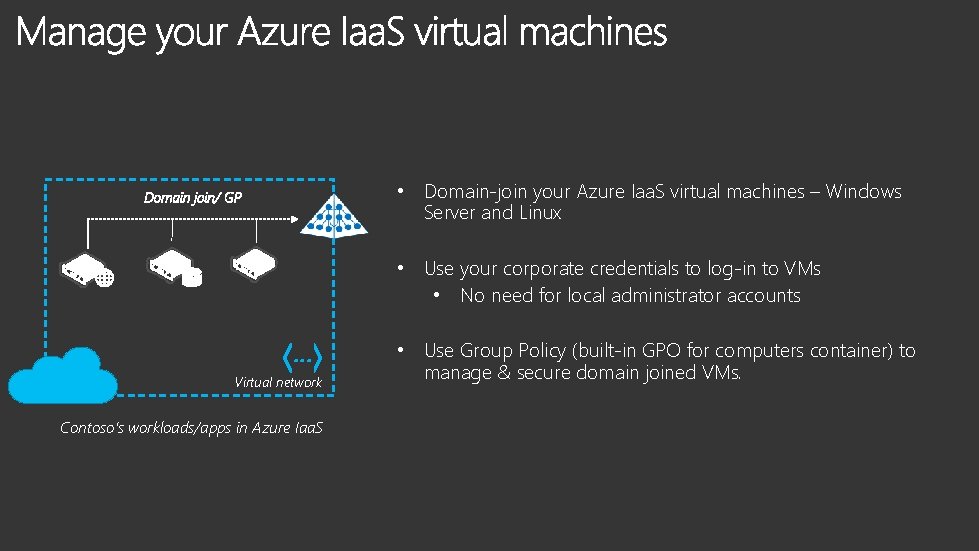
• Domain-join your Azure Iaa. S virtual machines – Windows Server and Linux • Use your corporate credentials to log-in to VMs • No need for local administrator accounts … Virtual network Contoso’s workloads/apps in Azure Iaa. S • Use Group Policy (built-in GPO for computers container) to manage & secure domain joined VMs.
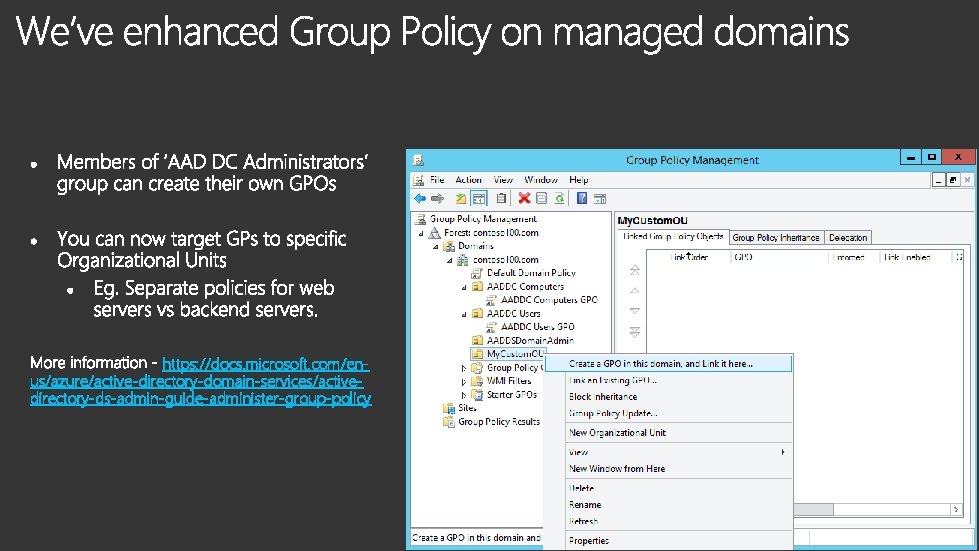
https: //docs. microsoft. com/enus/azure/active-directory-domain-services/activedirectory-ds-admin-guide-administer-group-policy
• Manage Azure Iaa. S virtual machines • ‘Lift-and-shift’ LDAP applications • • ‘Lift-and-shift’ Kerberos applications ‘Lift-and-shift’ Share. Point server Domain-joined HDInsight clusters Remote desktop deployments
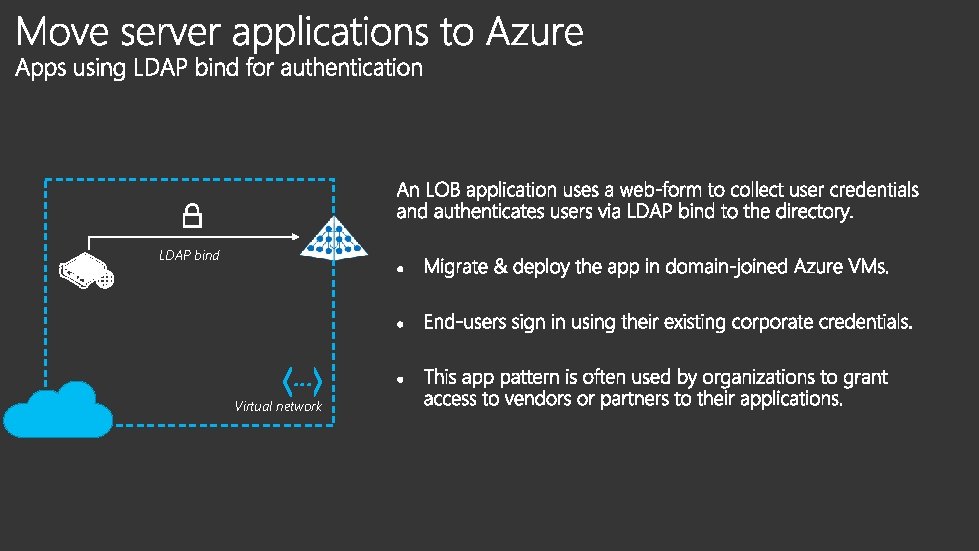
LDAP bind … Virtual network
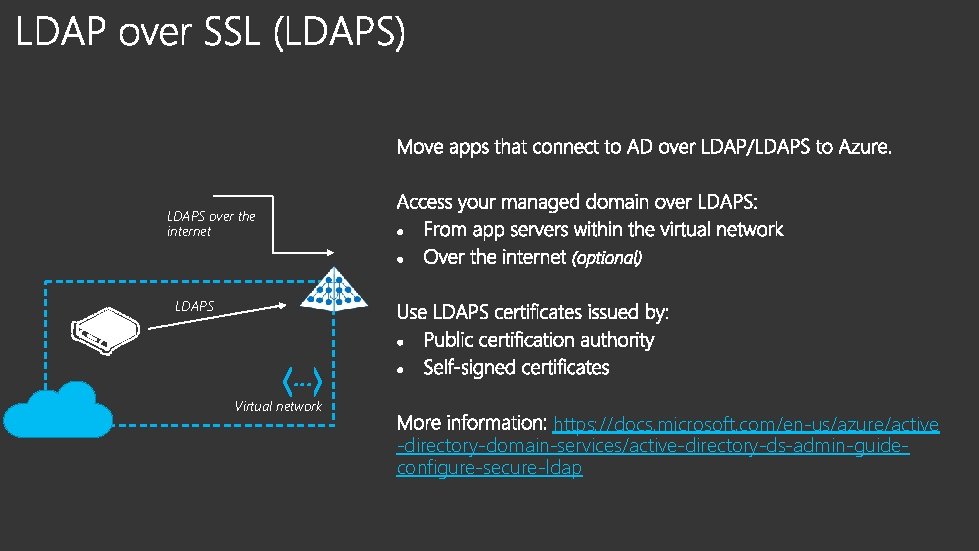
LDAPS over the internet LDAPS … Virtual network https: //docs. microsoft. com/en-us/azure/active -directory-domain-services/active-directory-ds-admin-guideconfigure-secure-ldap
• Manage Azure Iaa. S virtual machines • ‘Lift-and-shift’ LDAP applications • ‘Lift-and-shift’ Kerberos applications • ‘Lift-and-shift’ Share. Point server • Domain-joined HDInsight clusters • Remote desktop deployments
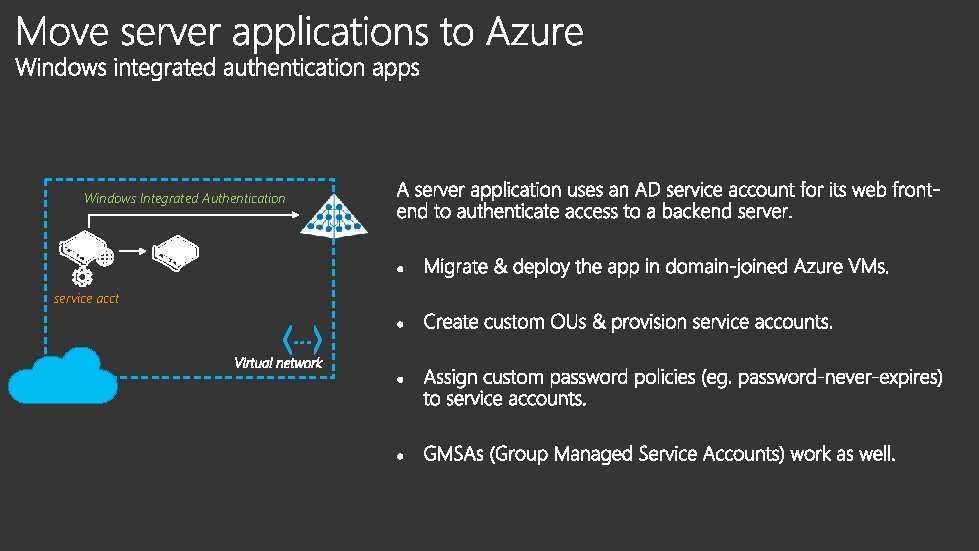
Windows Integrated Authentication service acct …
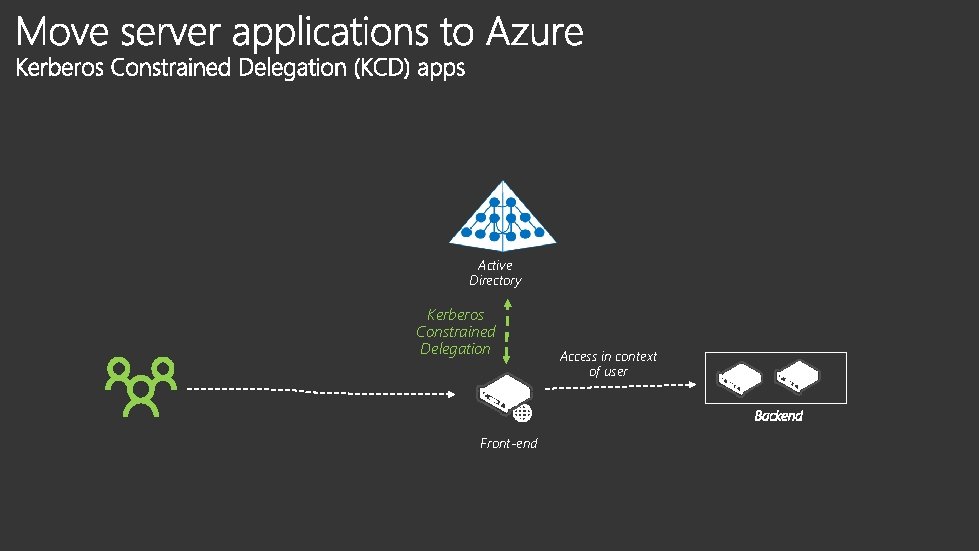
Active Directory Kerberos Constrained Delegation Front-end Access in context of user
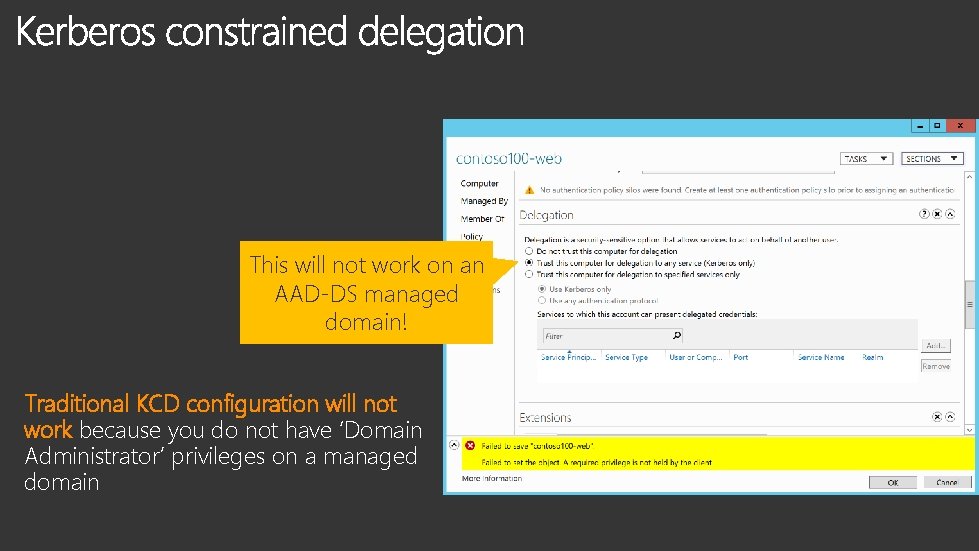
This will not work on an AAD-DS managed domain! Traditional KCD configuration will not work because you do not have ‘Domain Administrator’ privileges on a managed domain
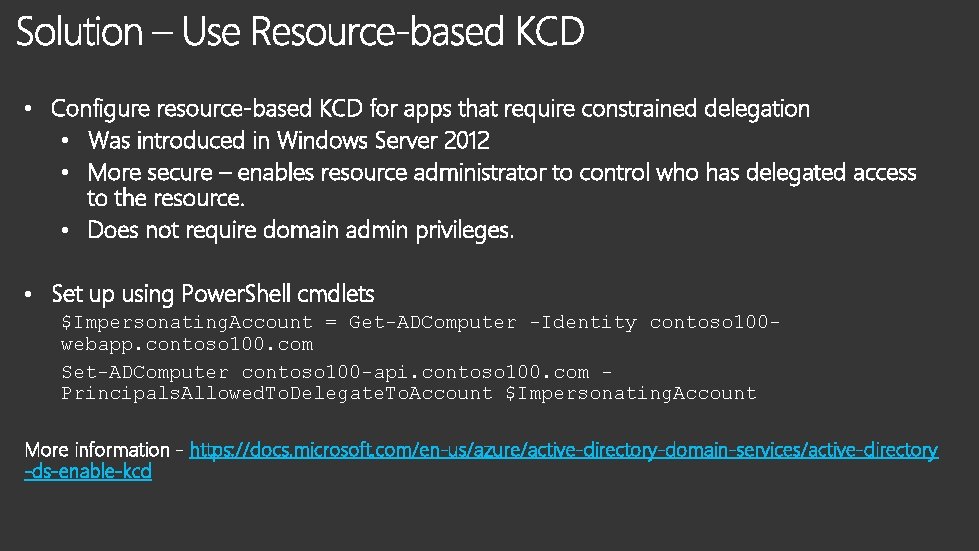
• Configure resource-based KCD for apps that require constrained delegation • Was introduced in Windows Server 2012 • More secure – enables resource administrator to control who has delegated access to the resource. • Does not require domain admin privileges. • Set up using Power. Shell cmdlets $Impersonating. Account = Get-ADComputer -Identity contoso 100 webapp. contoso 100. com Set-ADComputer contoso 100 -api. contoso 100. com Principals. Allowed. To. Delegate. To. Account $Impersonating. Account More information - https: //docs. microsoft. com/en-us/azure/active-directory-domain-services/active-directory -ds-enable-kcd
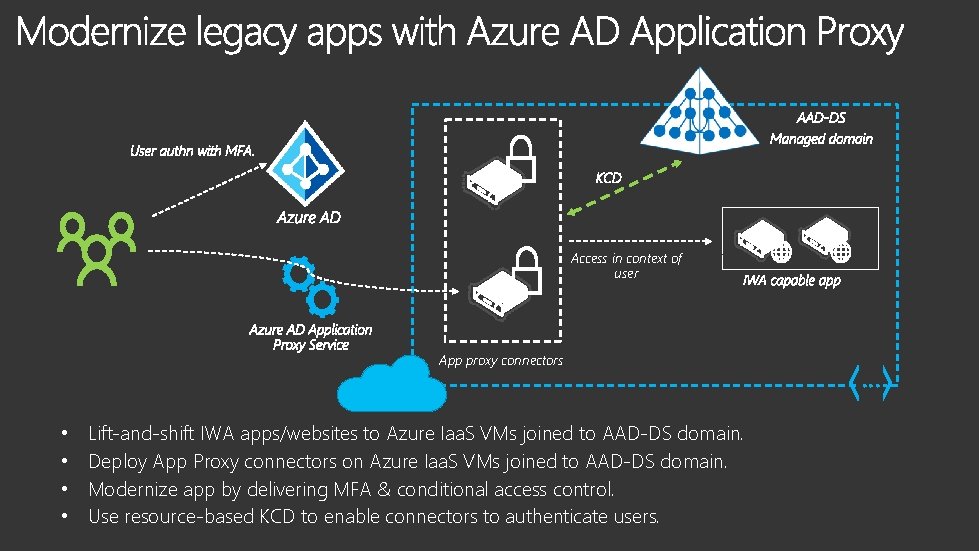
Access in context of user App proxy connectors • • Lift-and-shift IWA apps/websites to Azure Iaa. S VMs joined to AAD-DS domain. Deploy App Proxy connectors on Azure Iaa. S VMs joined to AAD-DS domain. Modernize app by delivering MFA & conditional access control. Use resource-based KCD to enable connectors to authenticate users. …
• Manage Azure Iaa. S virtual machines • ‘Lift-and-shift’ LDAP applications • ‘Lift-and-shift’ Kerberos applications • ‘Lift-and-shift’ Share. Point server • Domain-joined HDInsight clusters • Remote desktop deployments
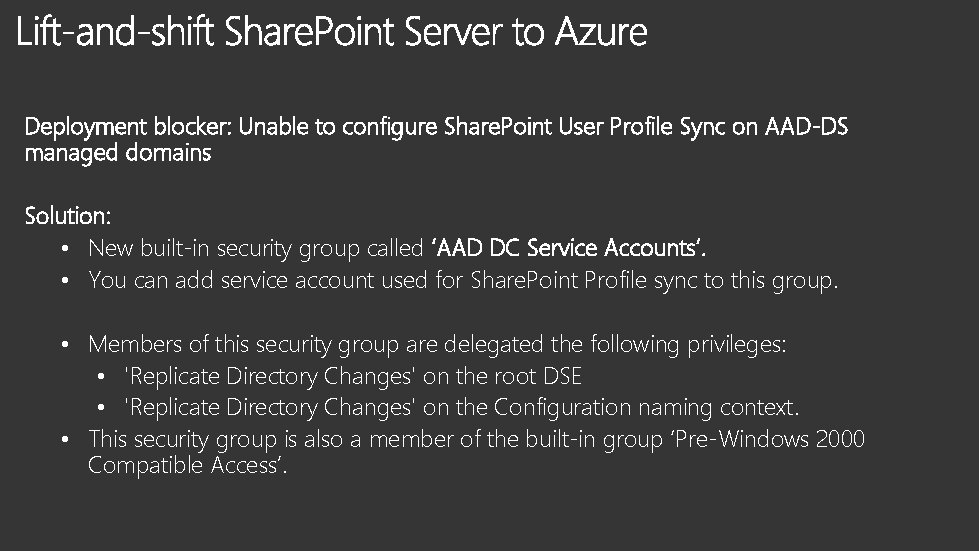
Deployment blocker: Unable to configure Share. Point User Profile Sync on AAD-DS managed domains Solution: • New built-in security group called ‘AAD DC Service Accounts’. • You can add service account used for Share. Point Profile sync to this group. • Members of this security group are delegated the following privileges: • 'Replicate Directory Changes' on the root DSE • 'Replicate Directory Changes' on the Configuration naming context. • This security group is also a member of the built-in group ‘Pre-Windows 2000 Compatible Access’.

• • Manage Azure Iaa. S virtual machines ‘Lift-and-shift’ LDAP applications ‘Lift-and-shift’ Kerberos applications ‘Lift-and-shift’ Share. Point server • Domain-joined HDInsight clusters • Remote desktop deployments
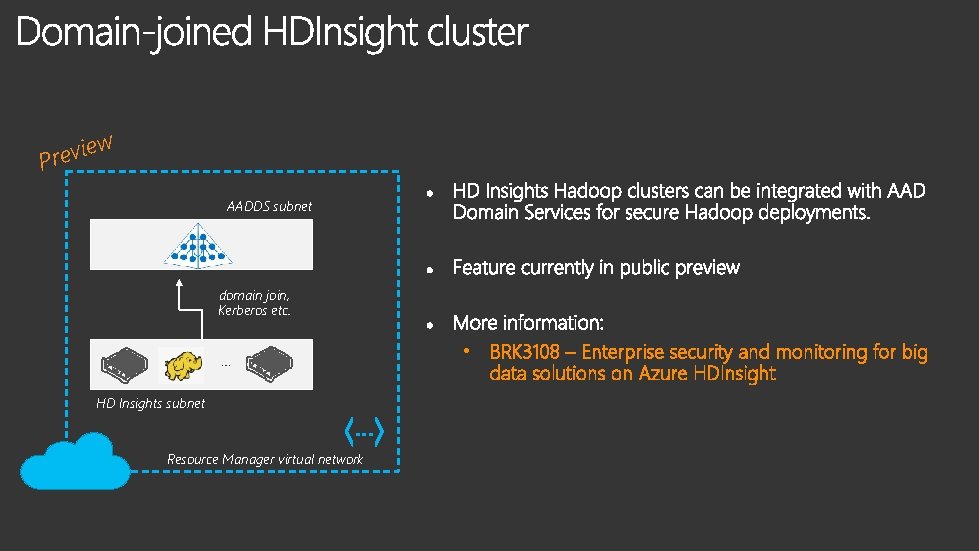
ie v e r P w AADDS subnet domain join, Kerberos etc. • BRK 3108 – Enterprise security and monitoring for big data solutions on Azure HDInsight … HD Insights subnet … Resource Manager virtual network
• • • Manage Azure Iaa. S virtual machines ‘Lift-and-shift’ LDAP applications ‘Lift-and-shift’ Kerberos applications ‘Lift-and-shift’ Share. Point server Domain-joined HDInsight clusters • Remote desktop deployments
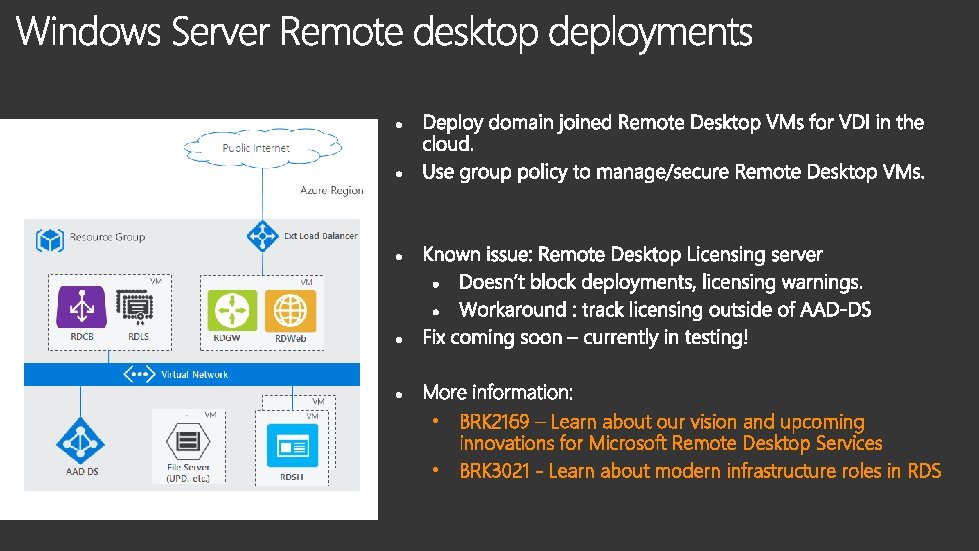
• BRK 2169 – Learn about our vision and upcoming innovations for Microsoft Remote Desktop Services • BRK 3021 - Learn about modern infrastructure roles in RDS
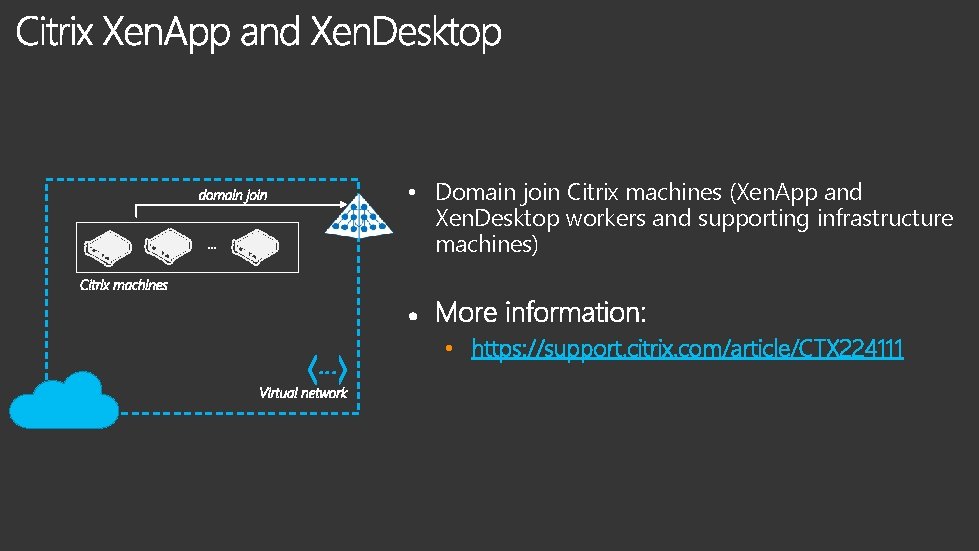
• Domain join Citrix machines (Xen. App and Xen. Desktop workers and supporting infrastructure machines) … • https: //support. citrix. com/article/CTX 224111

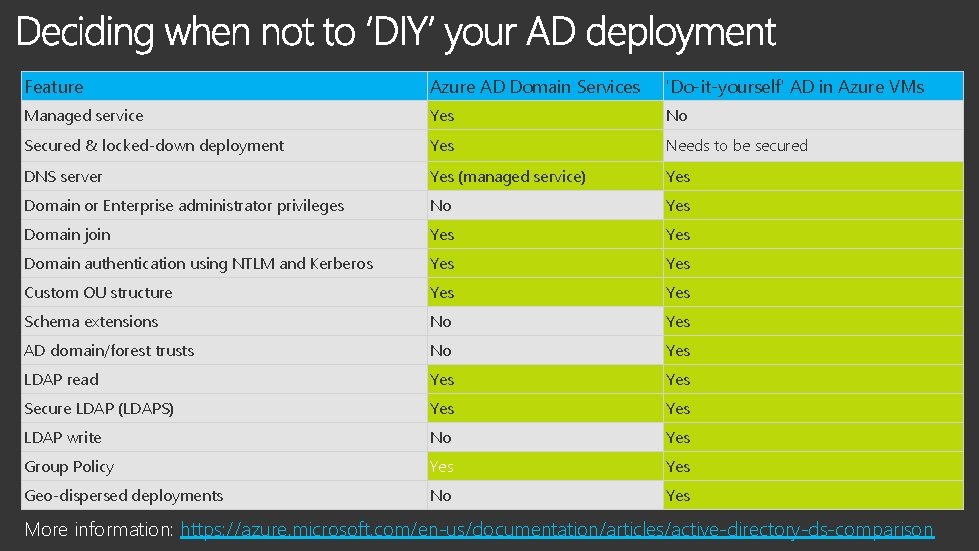
Feature Azure AD Domain Services 'Do-it-yourself' AD in Azure VMs Managed service Yes No Secured & locked-down deployment Yes Needs to be secured DNS server Yes (managed service) Yes Domain or Enterprise administrator privileges No Yes Domain join Yes Domain authentication using NTLM and Kerberos Yes Custom OU structure Yes Schema extensions No Yes AD domain/forest trusts No Yes LDAP read Yes Secure LDAP (LDAPS) Yes LDAP write No Yes Group Policy Yes Geo-dispersed deployments No Yes More information: https: //azure. microsoft. com/en-us/documentation/articles/active-directory-ds-comparison
• Cloud solution provider support • Support for a single managed domain to span multiple virtual networks. • Managed Resource forests • Schema extensions • Support for LDAP writes Questions/Feedback about the service? Contact the product team – aaddsfb@microsoft. com
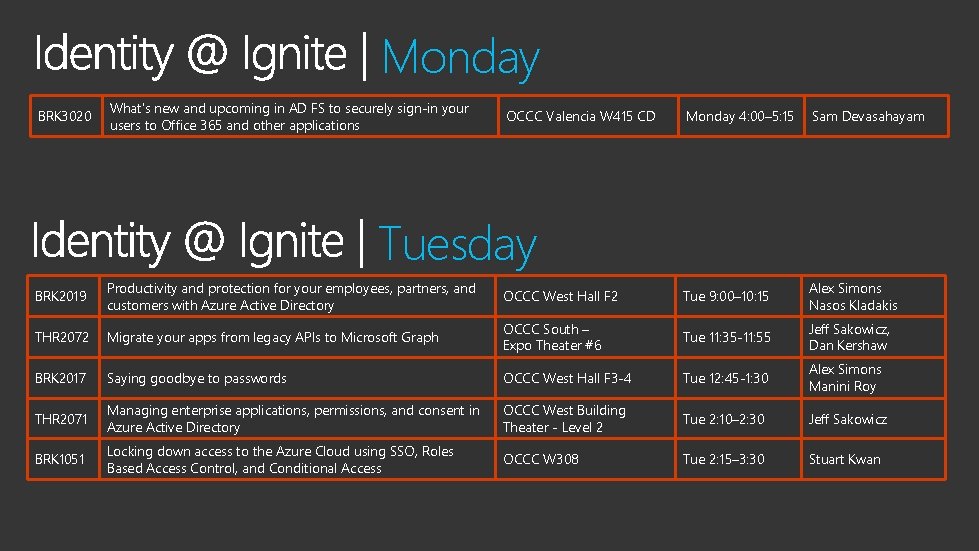
Monday BRK 3020 What's new and upcoming in AD FS to securely sign-in your users to Office 365 and other applications OCCC Valencia W 415 CD Monday 4: 00– 5: 15 Sam Devasahayam Tuesday BRK 2019 Productivity and protection for your employees, partners, and customers with Azure Active Directory OCCC West Hall F 2 Tue 9: 00– 10: 15 Alex Simons Nasos Kladakis THR 2072 Migrate your apps from legacy APIs to Microsoft Graph OCCC South – Expo Theater #6 Tue 11: 35 -11: 55 Jeff Sakowicz, Dan Kershaw BRK 2017 Saying goodbye to passwords OCCC West Hall F 3 -4 Tue 12: 45 -1: 30 Alex Simons Manini Roy THR 2071 Managing enterprise applications, permissions, and consent in Azure Active Directory OCCC West Building Theater - Level 2 Tue 2: 10– 2: 30 Jeff Sakowicz BRK 1051 Locking down access to the Azure Cloud using SSO, Roles Based Access Control, and Conditional Access OCCC W 308 Tue 2: 15– 3: 30 Stuart Kwan
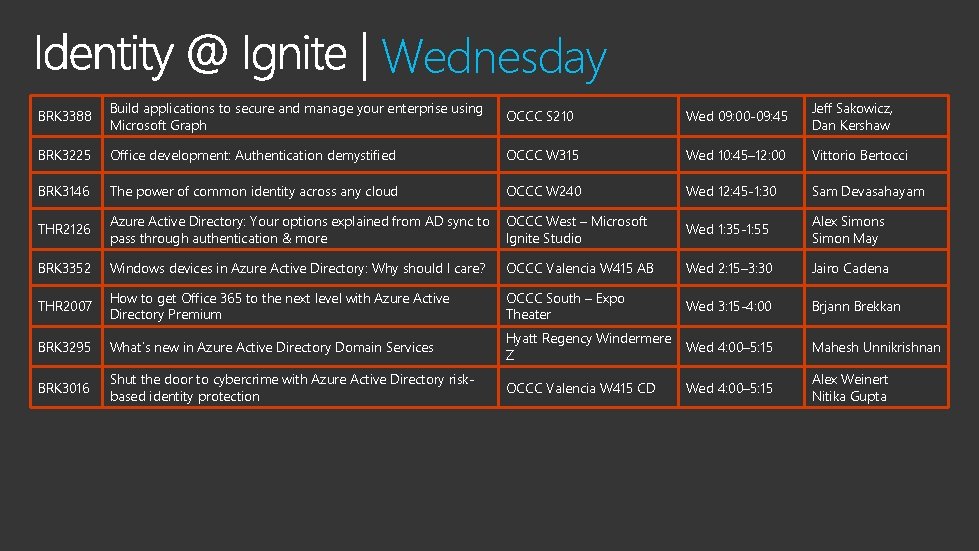
Wednesday BRK 3388 Build applications to secure and manage your enterprise using Microsoft Graph OCCC S 210 Wed 09: 00 -09: 45 Jeff Sakowicz, Dan Kershaw BRK 3225 Office development: Authentication demystified OCCC W 315 Wed 10: 45– 12: 00 Vittorio Bertocci BRK 3146 The power of common identity across any cloud OCCC W 240 Wed 12: 45 -1: 30 Sam Devasahayam THR 2126 Azure Active Directory: Your options explained from AD sync to pass through authentication & more OCCC West – Microsoft Ignite Studio Wed 1: 35 -1: 55 Alex Simons Simon May BRK 3352 Windows devices in Azure Active Directory: Why should I care? OCCC Valencia W 415 AB Wed 2: 15– 3: 30 Jairo Cadena THR 2007 How to get Office 365 to the next level with Azure Active Directory Premium OCCC South – Expo Theater Wed 3: 15 -4: 00 Brjann Brekkan BRK 3295 What’s new in Azure Active Directory Domain Services Hyatt Regency Windermere Z Wed 4: 00– 5: 15 Mahesh Unnikrishnan BRK 3016 Shut the door to cybercrime with Azure Active Directory riskbased identity protection OCCC Valencia W 415 CD Wed 4: 00– 5: 15 Alex Weinert Nitika Gupta
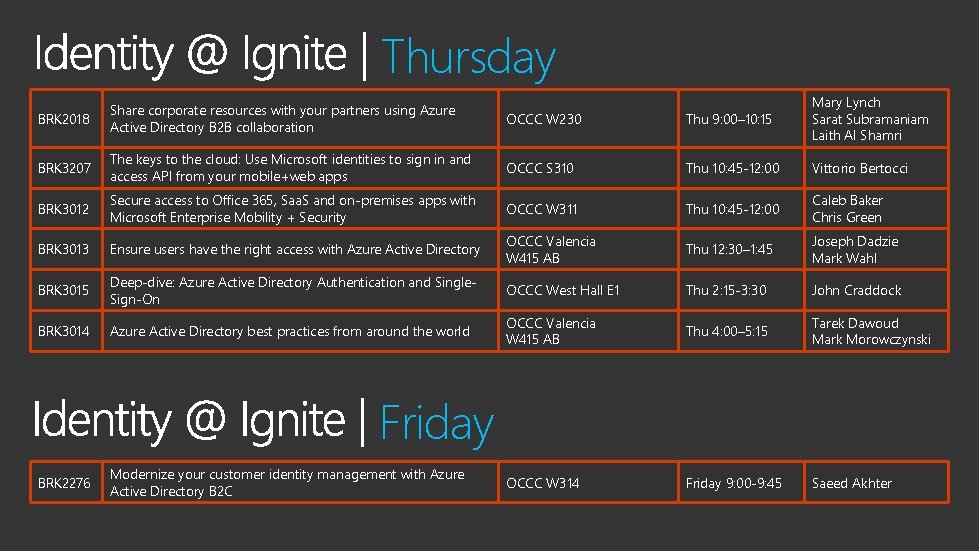
Thursday BRK 2018 Share corporate resources with your partners using Azure Active Directory B 2 B collaboration OCCC W 230 Thu 9: 00– 10: 15 Mary Lynch Sarat Subramaniam Laith Al Shamri BRK 3207 The keys to the cloud: Use Microsoft identities to sign in and access API from your mobile+web apps OCCC S 310 Thu 10: 45 -12: 00 Vittorio Bertocci BRK 3012 Secure access to Office 365, Saa. S and on-premises apps with Microsoft Enterprise Mobility + Security OCCC W 311 Thu 10: 45 -12: 00 Caleb Baker Chris Green BRK 3013 Ensure users have the right access with Azure Active Directory OCCC Valencia W 415 AB Thu 12: 30– 1: 45 Joseph Dadzie Mark Wahl BRK 3015 Deep-dive: Azure Active Directory Authentication and Single. Sign-On OCCC West Hall E 1 Thu 2: 15 -3: 30 John Craddock BRK 3014 Azure Active Directory best practices from around the world OCCC Valencia W 415 AB Thu 4: 00– 5: 15 Tarek Dawoud Mark Morowczynski OCCC W 314 Friday 9: 00 -9: 45 Saeed Akhter Friday BRK 2276 Modernize your customer identity management with Azure Active Directory B 2 C
https: //myignite. microsoft. com/evaluations https: //aka. ms/ignite. mobileapp

- Slides: 50