Avoid Hiring Unauthorized Workers Beyond the SSN Trace
Avoid Hiring Unauthorized Workers: Beyond the SSN Trace with Absolute Validation of Personal Identifiers How to Thwart Fraudulent Job Applicants and Identity Thieves Computer Information Development LLC

Presented by: Chuck Salvia Ø VP Sales and Marketing at CID Ø National Association of Professional Background Screeners - Co-chair of Government Identity Verification Systems sub-committee - Member of Litigation Avoidance sub-committee Ø Credit Union Executives Society (CUES) member csalvia@IDValidation. net (956) 457 -4116 http: //www. IDValidation. net
Why Worry? • I-9 errors and employment of unauthorized workers can lead to massive liability • You need to be aware of ways to minimize risk © 2012 Computer Information Development, LLC
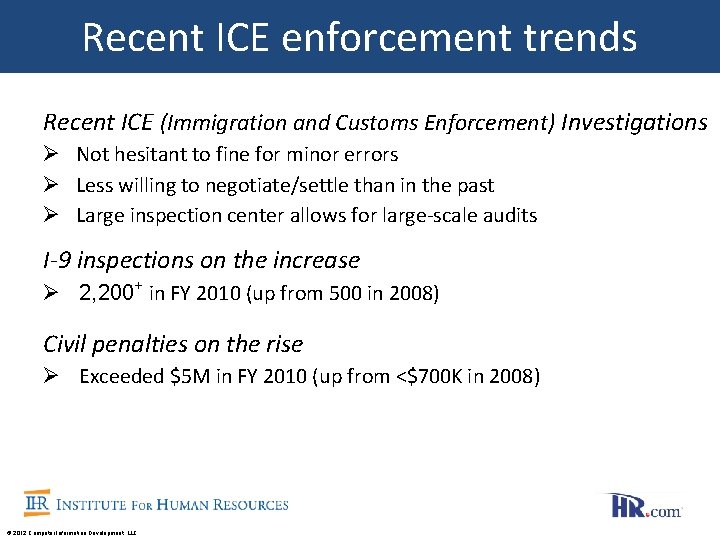
Recent ICE enforcement trends Recent ICE (Immigration and Customs Enforcement) Investigations Ø Not hesitant to fine for minor errors Ø Less willing to negotiate/settle than in the past Ø Large inspection center allows for large-scale audits I-9 inspections on the increase Ø 2, 200+ in FY 2010 (up from 500 in 2008) Civil penalties on the rise Ø Exceeded $5 M in FY 2010 (up from <$700 K in 2008) © 2012 Computer Information Development, LLC
ICE Enforcement Actions/Arrests for Employer Form I-9 Violations Recent ICE Investigations Lead to Business Owners, Managers, or Supervisors Being Arrested or Convicted for Engaging in Illegal Employment Practices or Other Crimes U. S. Immigration and Customs Enforcement (ICE) was established in 2003 as a sub-agency of the newly formed U. S. Department of Homeland Security (DHS). ICE took over responsibility for enforcing immigration law from the disbanded Immigration and Naturalization Service (INS). ICE Dramatically Expands I-9 Audits in July 2009 ICE and DHS announced an initiative to audit employers’ Form I-9 employment eligibility verification records. Department of Labor (DOL) Payroll Inspections Can Involve Form I-9 Review A DOL or State Wage and Hour Division audit clearly can lead to I-9 audits and inspections DOL has more than 1, 500 inspectors and recently announced it will spend $30 million to hire 288 additional frontline inspectors to step up enforcement against employers for wage and hour violations. Every company should consult with an immigration lawyer familiar with I-9 and Employment Eligibility Verification (EEV) to develop a written policies handbook and to train of key company executives, supervisors and plant managers, including a communication plan for what to do when ICE arrives. Employers should not wait for a phone call, letter, or knock on the door. Source: http: //www. i-9 employmenteligibility. com/recent_ice_actions. html © 2012 Computer Information Development, LLC
ICE enforcement in the news Documents sold to illegal migrants January 12, 2012 An identity fraud ring operating across the country sold personal information and identity documents to illegal immigrants since 2009, providing Social Security cards, birth certificates, and other identification documents, US Immigration and Customs Enforcement said today. The arrests reflect “unrelenting determination to identify and dismantle national smuggling rings engaged in document and identity fraud, ’’ ICE Director John Morton said in a statement. Authorities busted the alleged ring, according to an indictment unsealed in federal court in Puerto Rico. Fifty people face charges of selling the identities for $700 to $2, 500 per set. “It’s extremely serious for national security and public safety, ’’ said Bruce Foucart, and Immigration and Customs Enforcement special agent. “Just think of the damage that can be done with these things if it is in the wrong hands. ’’ Source: http: //articles. boston. com/2012 -01 -12/metro/30616844_1_identity-theft-illegal-immigrants-immigration-agency-officials © 2012 Computer Information Development, LLC
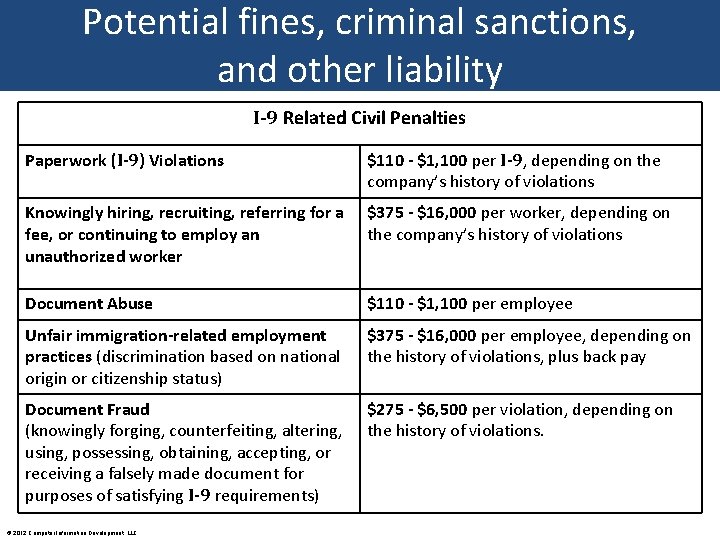
Potential fines, criminal sanctions, and other liability I-9 Related Civil Penalties Paperwork (I-9) Violations $110 - $1, 100 per I-9, depending on the company’s history of violations Knowingly hiring, recruiting, referring for a fee, or continuing to employ an unauthorized worker $375 - $16, 000 per worker, depending on the company’s history of violations Document Abuse $110 - $1, 100 per employee Unfair immigration-related employment practices (discrimination based on national origin or citizenship status) $375 - $16, 000 per employee, depending on the history of violations, plus back pay Document Fraud (knowingly forging, counterfeiting, altering, using, possessing, obtaining, accepting, or receiving a falsely made document for purposes of satisfying I-9 requirements) $275 - $6, 500 per violation, depending on the history of violations. © 2012 Computer Information Development, LLC
Criminal Penalties Pattern or practice of “knowingly” hiring or continuing to employ unauthorized workers Ø Fines of up to $3, 000 per individual Ø Up to 6 months in prison Ø This is in addition to, not instead of, civil penalties Harboring/trafficking also carry criminal penalties © 2012 Computer Information Development, LLC
Identity Verification Methods • Form I-9 Employment Eligibility Verification (EEV) • E-Verify • SSNVS (Social Security Number Verification Service) • CBSV (Consent Based Social Security Number Verification) • Non-government (e. g. , credit header information, data algorithms) © 2012 Computer Information Development, LLC
Identity Verification Methods Form I-9 Employment Eligibility Verification (EEV) • Administered by Department of Homeland Security / U. S. Citizenship and Immigration Service – “Free” – Legal requirement – Remains on file unless requested by government – Electronic I-9 s can provide additional peace of mind… and additional risks, depending on the vendor • Limit errors • Complex regulations © 2012 Computer Information Development, LLC
Identity Verification Methods E-Verify • Operated by Dept of Homeland Security in partnership with SSA – “Free” – Optional for most employers, required for some – Only to be used for new hires (some exceptions for federal government contractors/subcontractors) – Only to be used post-hire – Sends I-9 information to government – Checks for inconsistencies with government databases
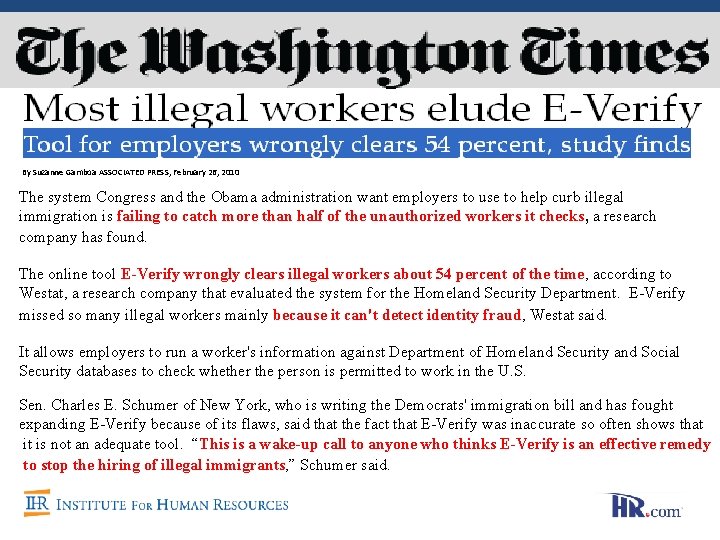
Identity Verification Methods By Suzanne Gamboa ASSOCIATED PRESS, February 26, 2010 The system Congress and the Obama administration want employers to use to help curb illegal immigration is failing to catch more than half of the unauthorized workers it checks, a research company has found. The online tool E-Verify wrongly clears illegal workers about 54 percent of the time, according to Westat, a research company that evaluated the system for the Homeland Security Department. E-Verify missed so many illegal workers mainly because it can't detect identity fraud, Westat said. It allows employers to run a worker's information against Department of Homeland Security and Social Security databases to check whether the person is permitted to work in the U. S. Sen. Charles E. Schumer of New York, who is writing the Democrats' immigration bill and has fought expanding E-Verify because of its flaws, said that the fact that E-Verify was inaccurate so often shows that it is not an adequate tool. “This is a wake-up call to anyone who thinks E-Verify is an effective remedy to stop the hiring of illegal immigrants, ” Schumer said.
Identity Verification Methods SSNVS (Social Security Number Verification Service) • Administered by the Social Security Administration – “Free” – Optional – Only to be used for post-hire wage reporting purposes – Not proper to use for identity or credit checks – Matches SSN and certain other information with SSA databases © 2011 Computer Information Development, LLC
Identity Verification Methods CBSV (Consent Based SSN Verification Service) • Administered by the Social Security Administration – Fee-based – Optional – May be used for any purpose, so long as the applicant/SSN holder consents to the query and the purpose therefore – Matches Name, SSN, Date of Birth, Gender and Death Indicator to SSA Master File and Death Index © 2012 Computer Information Development, LLC
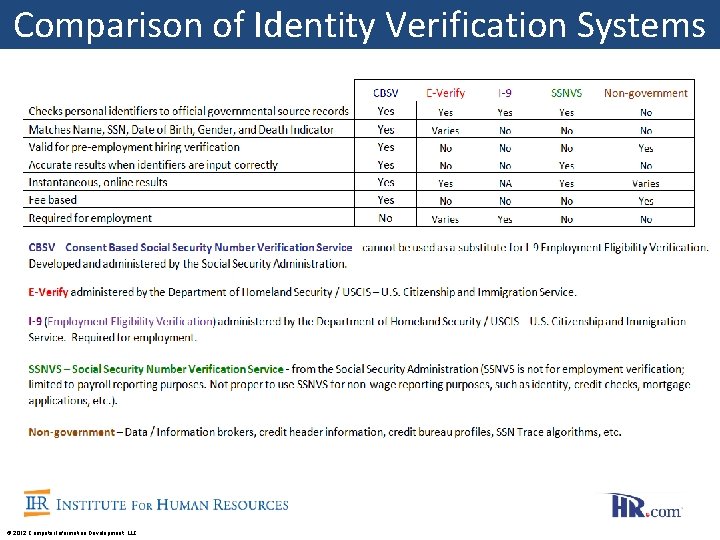
Comparison of Identity Verification Systems © 2012 Computer Information Development, LLC
Got CBSV? “Do you use CBSV? If not, you are allowing 80% of preventable fraud. ” Denis G. Kelly Certified Identity Expert
What is Absolute Validation and CBSV? • Developed and administered by the Social Security Administration • Matches Name, SSN, Date of Birth, Gender and Death Indicator to data in SSA’s Master File and Death Index • Pilot began in 2002; current version launched November 2008 • Real-time online verification and handles large volume requests • Used for all business verification purposes and compliance requirements Employment (both pre- and post-hire), Applicants of all sorts (customers, patients, students, tenants, etc. ), Loan originations (mortgage, auto, personal), Depository accounts, Fraud investigations, Collections, Special Investigative Units • Requires signed consent of applicant/SSN holder on Form SSA-89 • Used for the specific business purpose designated on the SSA-89 © 2012 Computer Information Development, LLC
Ways to Access CBSV • Use the service of a CBSV enrolled company • Avoid costs and burdens of direct enrollment • Direct enrollment through SSA • $5, 000. 00 non-refundable enrollment fee • Required annual CPA audit (SSA estimated at $8, 000. 00) • Upfront payment for the estimated number of CBSV searches for the entire year at the current SSA $1. 05 per search fee • Safeguarding and storage of the documents • Other various duties, liabilities, and responsibilities • Optional: Build interface to SSA Master File (SSA estimated $200, 000. 00) © 2012 Computer Information Development, LLC
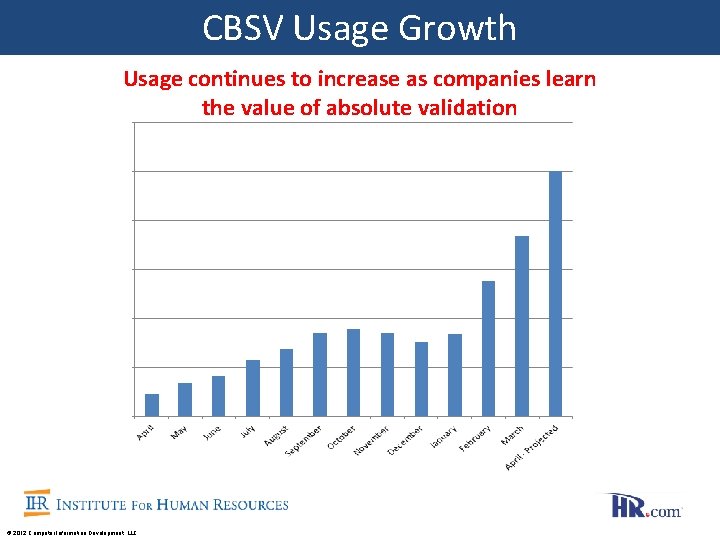
CBSV Usage Growth Usage continues to increase as companies learn the value of absolute validation © 2012 Computer Information Development, LLC
Protecting Vital Interests CBSV safeguards your company by shielding losses as it mitigates the risks of fraud and identity theft CBSV strengthens, enhances, and purifies your verification due diligence processes with direct access to official governmental source records as it validates personal identifiers © 2012 Computer Information Development, LLC
Who Uses CBSV? • HR Departments for employment (both pre and post-hire) • Creditors (Lenders, Banks, Credit Unions, Insurance companies, Retail, etc. ) • Landlords for tenant screening • Health Care providers • Higher Education for student applicants • Any and all other legitimate verification purposes © 2012 Computer Information Development, LLC
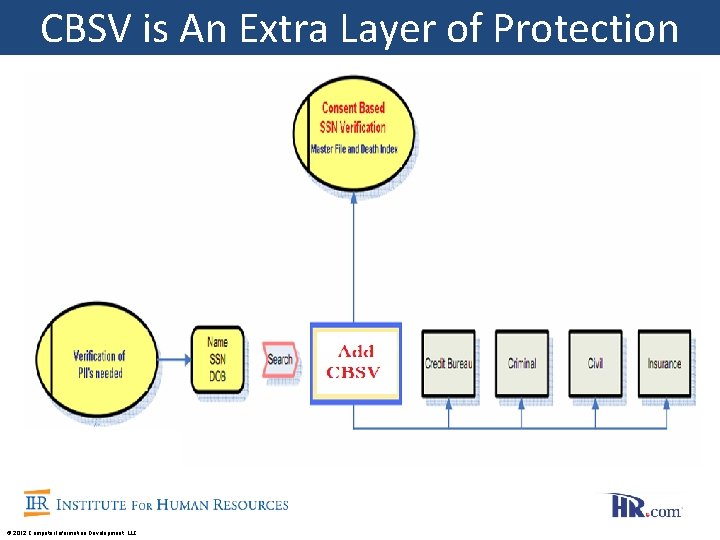
CBSV is An Extra Layer of Protection © 2012 Computer Information Development, LLC
Why is CBSV so Important? CBSV thwarts fraud and identity theft where other verification methods fail All other options include false and erroneous profiles, can be easily manipulated, and contain stale data © 2012 Computer Information Development, LLC

SSN’S ARE EVERYWHERE! Source: Lanny Britnell of Identity. Theft. America. com
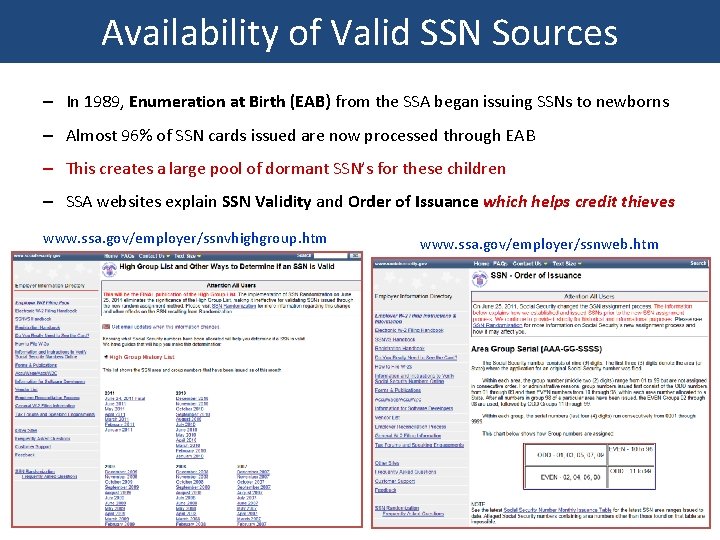
Availability of Valid SSN Sources – In 1989, Enumeration at Birth (EAB) from the SSA began issuing SSNs to newborns – Almost 96% of SSN cards issued are now processed through EAB – This creates a large pool of dormant SSN’s for these children – SSA websites explain SSN Validity and Order of Issuance which helps credit thieves www. ssa. gov/employer/ssnvhighgroup. htm www. ssa. gov/employer/ssnweb. htm
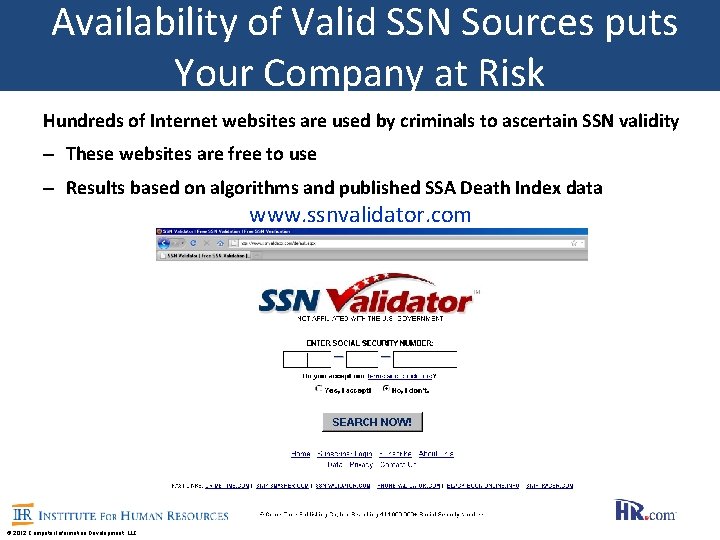
Availability of Valid SSN Sources puts Your Company at Risk Hundreds of Internet websites are used by criminals to ascertain SSN validity – These websites are free to use – Results based on algorithms and published SSA Death Index data www. ssnvalidator. com © 2012 Computer Information Development, LLC
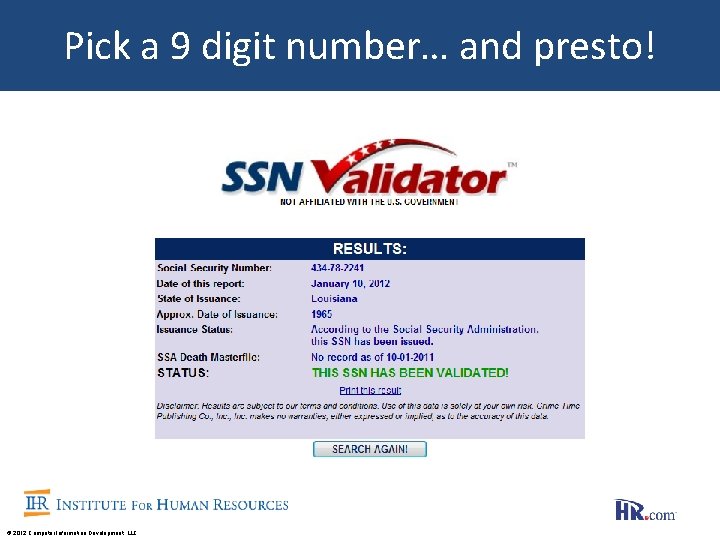
Pick a 9 digit number… and presto! © 2012 Computer Information Development, LLC
CBSV mitigates SSN abuse Availability of SSN sources puts your company at great risk © 2012 Computer Information Development, LLC
Fraud in the Workplace Massive SSN Fraud for Employment by Tom Fragala Using an SSN fraudulently to get employment is nothing new. But there’s a lot of new buzz surrounding the issue of “undocumented” workers stealing or using stolen Social Security Numbers. This is not a small matter. If someone uses an SSN to obtain employment, they are committing a federal crime and it’s a felony. And these crimes are taking place by the thousands every day. The Dallas Star-Telegram reports that the Internal Revenue Service and the Social Security Administration routinely collect evidence of potential workplace crimes, including the names and addresses of millions of people who are using bogus Social Security Numbers, their wage records and the identities of those who hire them. One internal study found that a restaurant company had submitted 4, 100 duplicate Social Security Numbers for workers. Other firms submit inaccurate names or numbers for nearly all their employees. One child's Social Security Number was used 742 times by workers in 42 states.
Case Studies 1) Synthetic Name Fraud 2) How Many Minors Have Been Hired Today? 3) Court OK’s Fraudulent SSN Use 4) Credit Profile Numbers
Synthetic Name Fraud SSN integrity has been severely compromised in credit bureau profiles and other trusted authorities. Synthetic Name Fraud is using one’s own name, date of birth and address with another persons SSN. This creates a new, fraudulent credit profile that trusted authorities share with each other as genuine. Also known as Synthetic Identity Fraud, this threat causes “piggy-backing” in credit bureau profiles. In 2007, Federal Trade Commission said there are over 10 million more credit profiles in the system than there are consumers! Why attempt to "verify” in pools of polluted profile information? © 2012 Computer Information Development, LLC
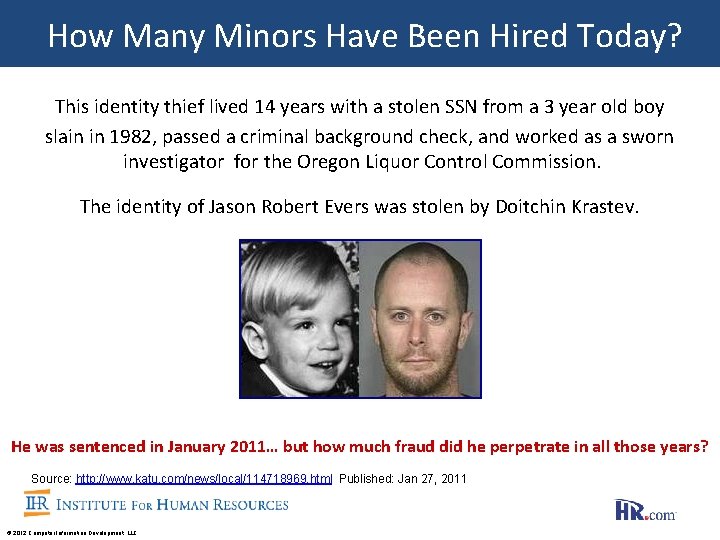
How Many Minors Have Been Hired Today? This identity thief lived 14 years with a stolen SSN from a 3 year old boy slain in 1982, passed a criminal background check, and worked as a sworn investigator for the Oregon Liquor Control Commission. The identity of Jason Robert Evers was stolen by Doitchin Krastev. He was sentenced in January 2011… but how much fraud did he perpetrate in all those years? Source: http: //www. katu. com/news/local/114718969. html Published: Jan 27, 2011 © 2012 Computer Information Development, LLC
Child ID Theft Volume of child ID theft cases reported annually to the Federal Trade Commission jumped 192 percent from 2003 to 2009
COURT OK’S FRAUDULENT SSN USE We’re battling an uninformed judiciary! Colorado State Supreme Court over-ruled a lower court that convicted a man of criminal impersonation when he fraudulently used the SSN of another person (a woman victim) when applying for an auto loan. The appellate court found Mr. Montes-Rodriguez defrauded a car dealership which required an SSN on its loan application. The State Supreme Court however held that since he used his own name, birth date and address, the use of another person’s SSN was not criminal impersonation. . . even though he also used her SSN for employment as well. This is classic Synthetic Name Fraud, even though Mr. Montes-Rodriguez did not know the victim. It caused a false profile to be created and shared within the credit bureaus and other trusted authorities. Use of a false SSN even without using the victim’s name is a core issue of ID theft. CBSV would have stopped the auto scam and the job scam because it verifies Name, SSN, Date of Birth, Gender, and Death Indicator Source: http: //caselaw. findlaw. com/co-court-of-appeals/1058355. html
The Elephant in the Room It’s BIG, has been ignored and gone unaddressed! Have you heard of Credit Profile Numbers? © 2012 Computer Information Development, LLC
Start a New Credit Profile with a CPN Credit thieves have re-named stolen/fabricated SSN’s by calling them Credit Profile (or Credit Privacy) Numbers As we know, the SSA’s Enumeration at Birth (EAB) creates a large pool of dormant SSN’s for credit thieves to draw from Unsuspecting children may not need to use their SSN until they apply for a job, credit, or college and find that a credit thief has stolen their identity Have you seen the headlines? © 2012 Computer Information Development, LLC
New ID theft targets kids' Social Security numbers, could threaten credit system “Thieves are targeting your kid's number long before the little one even has a bank account. Hundreds of online businesses are using computers to find dormant Social Security Numbers - usually those assigned to children who don't use them - then selling those numbers. ” By BILL DRAPER Associated Press Writer, KANSAS CITY, Mo. August 2, 2010 (AP) Source: http: //abcnews. go. com/Business/wire. Story? id=11305930 © 2012 Computer Information Development, LLC
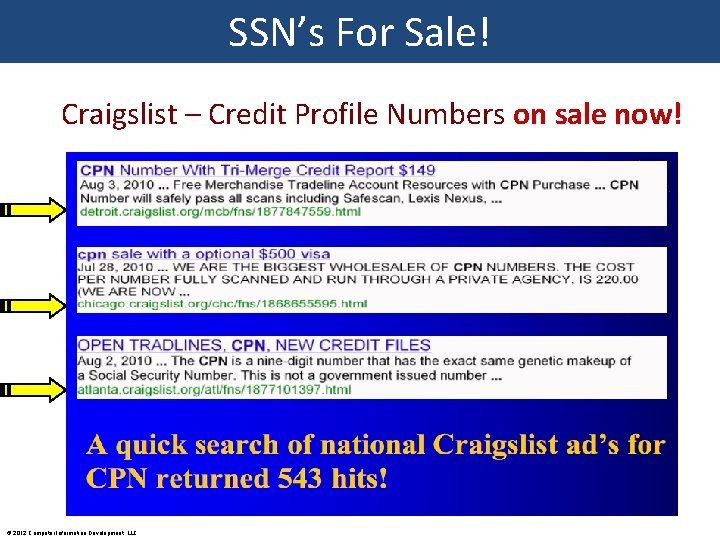
SSN’s For Sale! Craigslist – Credit Profile Numbers on sale now! © 2012 Computer Information Development, LLC
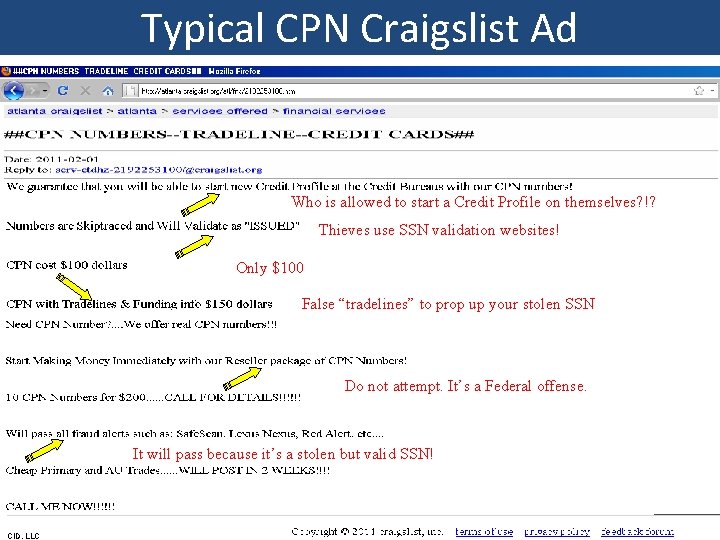
Typical CPN Craigslist Ad Who is allowed to start a Credit Profile on themselves? !? Thieves use SSN validation websites! Only $100 False “tradelines” to prop up your stolen SSN Do not attempt. It’s a Federal offense. It will pass because it’s a stolen but valid SSN! CID, LLC
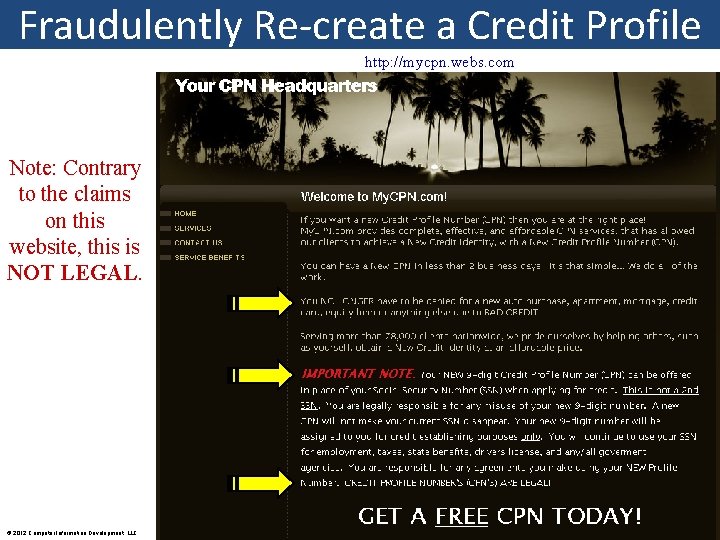
Fraudulently Re-create a Credit Profile http: //mycpn. webs. com Note: Contrary to the claims on this website, this is NOT LEGAL. © 2012 Computer Information Development, LLC

Fraudsters: Bold & Brazen Credit thieves peddle their dishonest wares on You Tube! © 2012 Computer Information Development, LLC
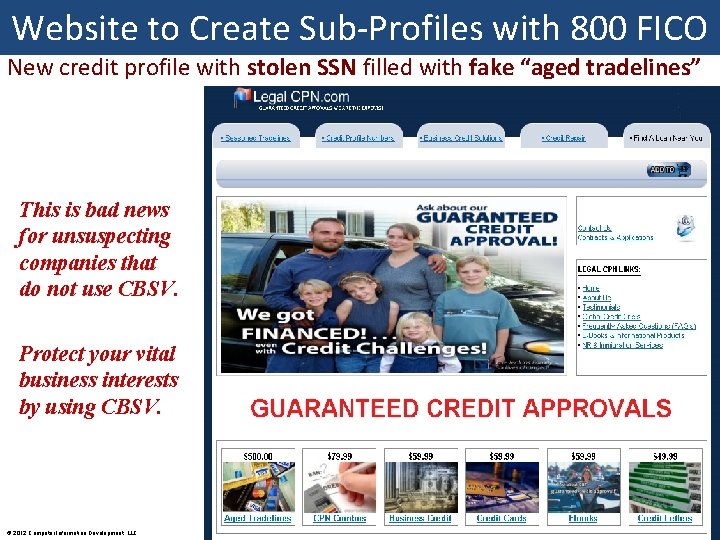
Website to Create Sub-Profiles with 800 FICO New credit profile with stolen SSN filled with fake “aged tradelines” This is bad news for unsuspecting companies that do not use CBSV. Protect your vital business interests by using CBSV. © 2012 Computer Information Development, LLC
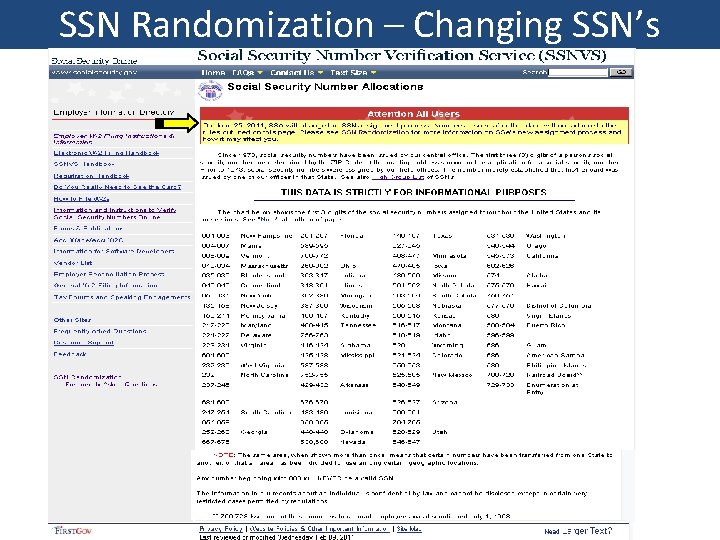
SSN Randomization – Changing SSN’s
SSN Randomization Has Changed Everything • Random SSNs began June 25, 2011 to extend the longevity in all states • SSN no longer linked to “State of Issuance” or High Group list (frozen) • Eliminates geographical significance of the first three digits of the SSN • SSN Trace algorithms no longer be useful for SSNs issued after June 25 th • Not just for Enumeration At Birth; randomized SSNs for legal immigrants, domestic violence victims, and in extremely rare cases, victims of ID theft • Previously unassigned area numbers will be introduced for assignment excluding area numbers 000, 666 and 900 -999 • Criminals will attempt to exploit this situation • SSN Randomization is having an impact on businesses http: //www. ssa. gov/employer/randomization. html © 2012 Computer Information Development, LLC

Complacency - The Real Threat • 45 Million people in the U. S. deliberately manipulate their identities - That’s 16 Percent of U. S. population engaging in improper Identity Manipulation according to ID Analytics • Carnegie Mellon University reports vulnerabilities of being able to properly “guess” an SSN • Over 20 million Americans have multiple SSN’s associated with their names. 40 Million SSN’s associated with multiple people, 6. 1% have at least 2 SSN’s associated with their name (ID Analytics) • FTC says 500, 000 people under the age of 18 are victims of ID theft every year - many more cases go unreported. 23% of all identity theft cases are caught once account is charged off and sent to collection agencies © 2012 Computer Information Development, LLC
Compliance with Internal, State and Federal Requirements • FTC’s Red Flags Rule for creditors • Patriot Act - Know Your Customer Section 326 • CIP and Identity Theft Prevention Program (ITPP) • Dodd-Frank Wall Street Reform and Consumer Protection Act • And other requirements The use of CBSV strengthens all compliance policies © 2012 Computer Information Development, LLC
FACTA Regulation 315 Some businesses are responsible for ensuring the transmittal of accurate data! © 2012 Computer Information Development, LLC
CBSV: Absolute Validation Methodology False credit profiles and “cross pollution” of personal identifier data within trusted authorities requires extreme caution in the use of these resources to validate identities Current methodologies have exposed vulnerabilities which has led to major increases in Synthetic Name Fraud Absolute Validation can only be obtained from the source with the identifiers of Name, SSN, Date of Birth, Gender, and Death Indicator The Absolute Validation Methodology is Consent Based SSN Verification © 2012 Computer Information Development, LLC
SSA-89 Consent Form The following slide is an example of an official completed SSA-89 consent form. This is the required SSA form approved by the U. S. Office of Management and Budget © 2012 Computer Information Development, LLC
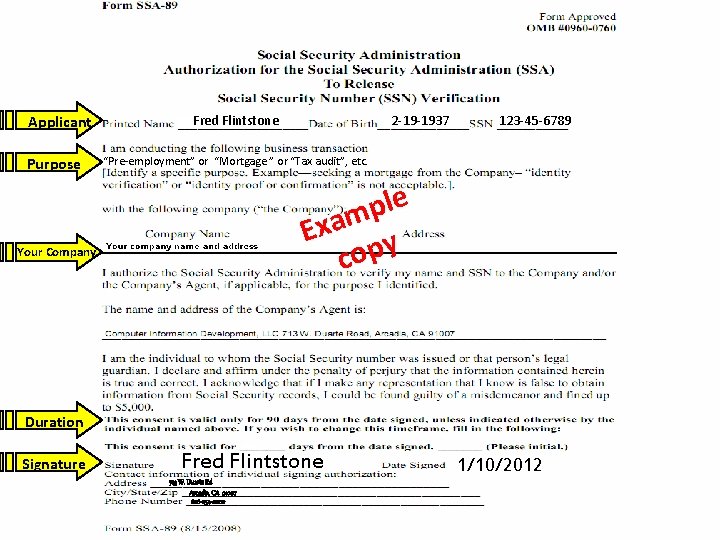
Applicant Purpose Fred Flintstone 2 -19 -1937 123 -45 -6789 “Pre-employment” or “Mortgage ” or “Tax audit”, etc. e l p m a x E y p o c Your Company Duration Signature Fred Flintstone 713 W. Duarte Rd Arcadia, CA 91007 626 -254 -0000 1/10/2012
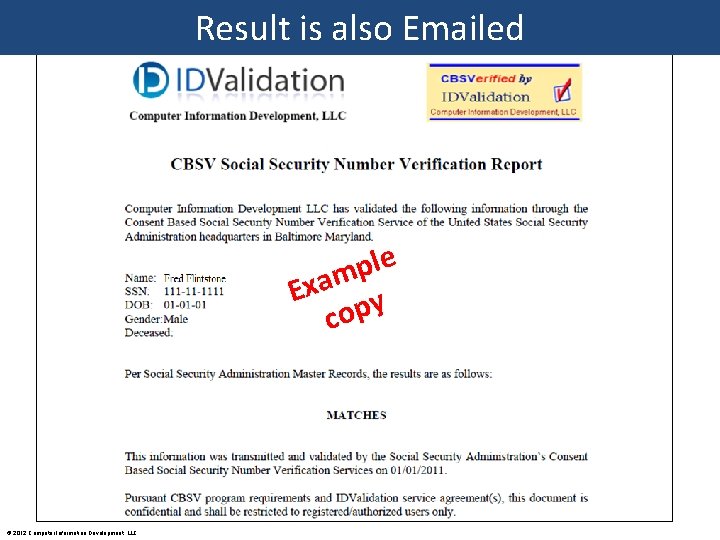
Result is also Emailed e l p m a x E y p o c © 2012 Computer Information Development, LLC
What is the Cost? How much does one incident of fraud cost? Average loan loss is over $50, 000 What is the cost of a negligent hire? 1 to 3 times their annual salary How valuable is your company’s reputation? Priceless © 2012 Computer Information Development, LLC
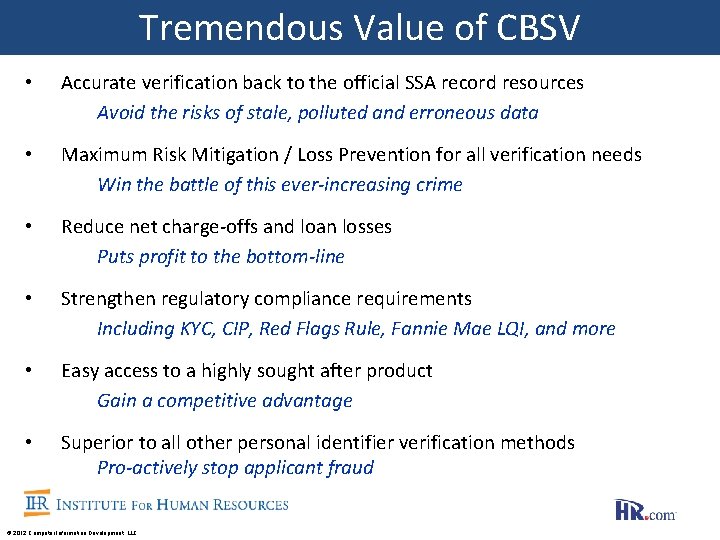
Tremendous Value of CBSV • Accurate verification back to the official SSA record resources Avoid the risks of stale, polluted and erroneous data • Maximum Risk Mitigation / Loss Prevention for all verification needs Win the battle of this ever-increasing crime • Reduce net charge-offs and loan losses Puts profit to the bottom-line • Strengthen regulatory compliance requirements Including KYC, CIP, Red Flags Rule, Fannie Mae LQI, and more • Easy access to a highly sought after product Gain a competitive advantage • Superior to all other personal identifier verification methods Pro-actively stop applicant fraud © 2012 Computer Information Development, LLC
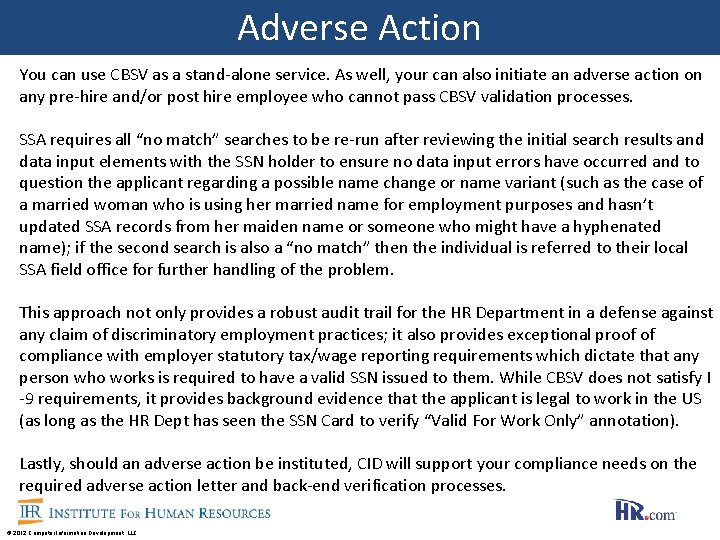
Adverse Action You can use CBSV as a stand-alone service. As well, your can also initiate an adverse action on any pre-hire and/or post hire employee who cannot pass CBSV validation processes. SSA requires all “no match” searches to be re-run after reviewing the initial search results and data input elements with the SSN holder to ensure no data input errors have occurred and to question the applicant regarding a possible name change or name variant (such as the case of a married woman who is using her married name for employment purposes and hasn’t updated SSA records from her maiden name or someone who might have a hyphenated name); if the second search is also a “no match” then the individual is referred to their local SSA field office for further handling of the problem. This approach not only provides a robust audit trail for the HR Department in a defense against any claim of discriminatory employment practices; it also provides exceptional proof of compliance with employer statutory tax/wage reporting requirements which dictate that any person who works is required to have a valid SSN issued to them. While CBSV does not satisfy I -9 requirements, it provides background evidence that the applicant is legal to work in the US (as long as the HR Dept has seen the SSN Card to verify “Valid For Work Only” annotation). Lastly, should an adverse action be instituted, CID will support your compliance needs on the required adverse action letter and back-end verification processes. © 2012 Computer Information Development, LLC
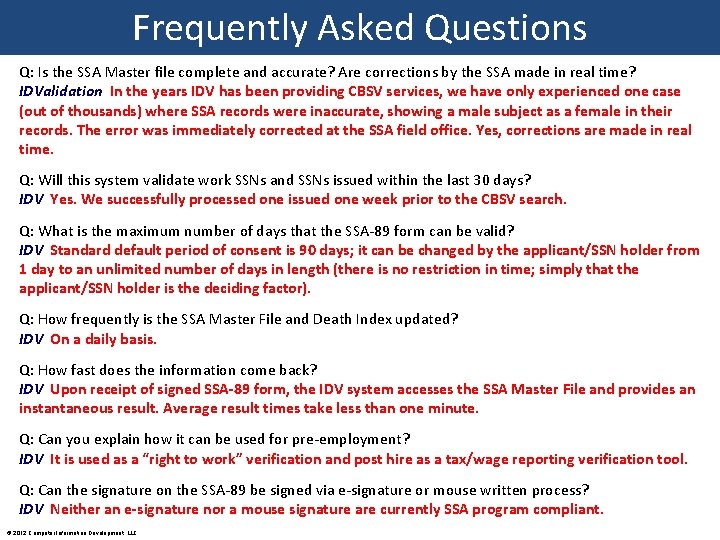
Frequently Asked Questions Q: Is the SSA Master file complete and accurate? Are corrections by the SSA made in real time? IDValidation In the years IDV has been providing CBSV services, we have only experienced one case (out of thousands) where SSA records were inaccurate, showing a male subject as a female in their records. The error was immediately corrected at the SSA field office. Yes, corrections are made in real time. Q: Will this system validate work SSNs and SSNs issued within the last 30 days? IDV Yes. We successfully processed one issued one week prior to the CBSV search. Q: What is the maximum number of days that the SSA-89 form can be valid? IDV Standard default period of consent is 90 days; it can be changed by the applicant/SSN holder from 1 day to an unlimited number of days in length (there is no restriction in time; simply that the applicant/SSN holder is the deciding factor). Q: How frequently is the SSA Master File and Death Index updated? IDV On a daily basis. Q: How fast does the information come back? IDV Upon receipt of signed SSA-89 form, the IDV system accesses the SSA Master File and provides an instantaneous result. Average result times take less than one minute. Q: Can you explain how it can be used for pre-employment? IDV It is used as a “right to work” verification and post hire as a tax/wage reporting verification tool. Q: Can the signature on the SSA-89 be signed via e-signature or mouse written process? IDV Neither an e-signature nor a mouse signature are currently SSA program compliant. © 2012 Computer Information Development, LLC
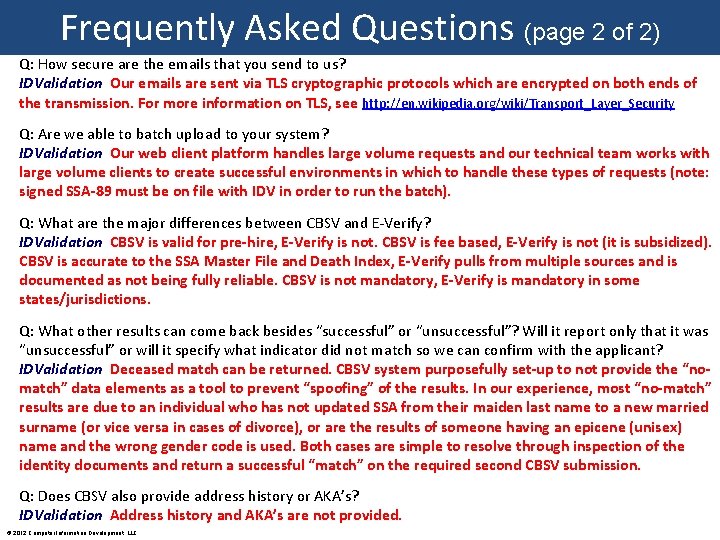
Frequently Asked Questions (page 2 of 2) Q: How secure are the emails that you send to us? IDValidation Our emails are sent via TLS cryptographic protocols which are encrypted on both ends of the transmission. For more information on TLS, see http: //en. wikipedia. org/wiki/Transport_Layer_Security Q: Are we able to batch upload to your system? IDValidation Our web client platform handles large volume requests and our technical team works with large volume clients to create successful environments in which to handle these types of requests (note: signed SSA-89 must be on file with IDV in order to run the batch). Q: What are the major differences between CBSV and E-Verify? IDValidation CBSV is valid for pre-hire, E-Verify is not. CBSV is fee based, E-Verify is not (it is subsidized). CBSV is accurate to the SSA Master File and Death Index, E-Verify pulls from multiple sources and is documented as not being fully reliable. CBSV is not mandatory, E-Verify is mandatory in some states/jurisdictions. Q: What other results can come back besides “successful” or “unsuccessful”? Will it report only that it was “unsuccessful” or will it specify what indicator did not match so we can confirm with the applicant? IDValidation Deceased match can be returned. CBSV system purposefully set-up to not provide the “nomatch” data elements as a tool to prevent “spoofing” of the results. In our experience, most “no-match” results are due to an individual who has not updated SSA from their maiden last name to a new married surname (or vice versa in cases of divorce), or are the results of someone having an epicene (unisex) name and the wrong gender code is used. Both cases are simple to resolve through inspection of the identity documents and return a successful “match” on the required second CBSV submission. Q: Does CBSV also provide address history or AKA’s? IDValidation Address history and AKA’s are not provided. © 2012 Computer Information Development, LLC
Thank you for attending! Questions? Please contact Chuck Salvia at csalvia@IDValidation. net or (956) 457 -4116 Computer Information Development LLC https: //www. IDValidation. net Founded in 2001, CID provides specialized fraud investigative services and works with government/private sector resources in the battle against fraud risk and associated losses to the business community. Provider of fraud detection, prevention and remediation services along with being one of the first SSA enrolled companies and the only provider of real-time web based Consent Based SSN Verification (CBSV) services on the IDValidation platform which launched in 2009. Please subscribe to our monthly e-newsletter containing information in the battle against fraud and identity theft Link to the February 2012 edition: http: //conta. cc/idv. Feb 2012 © 2012 Computer Information Development, LLC
- Slides: 57