Automation The insider threat you didnt know you






- Slides: 37
Automation: The insider threat you didn’t know you had Cyber Wars – Day 2 (Technical) 2018 John Gleason Dev. Ops Engineer

About ISE Perspective • White box Analysts • Hackers; Cryptographers; RE Exploits • i. Phone; Android; Ford; Exxon; Diebold Research • Routers; NAS; Healthcare Customers • Companies with high value assets
About Me ISE for 6 months Previously with Accenture I write lots of Power. Shell Spend lots of time designing, building, and maintaining cloud environments
Introduction Automation is everywhere I leveraged my experience scripting games to automate IT systems My experience comes from: Automated compliance audit tools Automated orchestration systems CI/CD systems leveraging industry standard toolchains
Goals Describe common automation patterns / problems Classify these issues Pose questions for use in audits
Development Automation GIT Subversion TFVC Source and Version control systems automate the Business Logic of maintaining source code
Source control through a telescope “Central” system tracks all changes or modifications Keeps full history of changes Allows for simultaneous edits, coordinates conflict resolution Source code copied to developer machines for edit
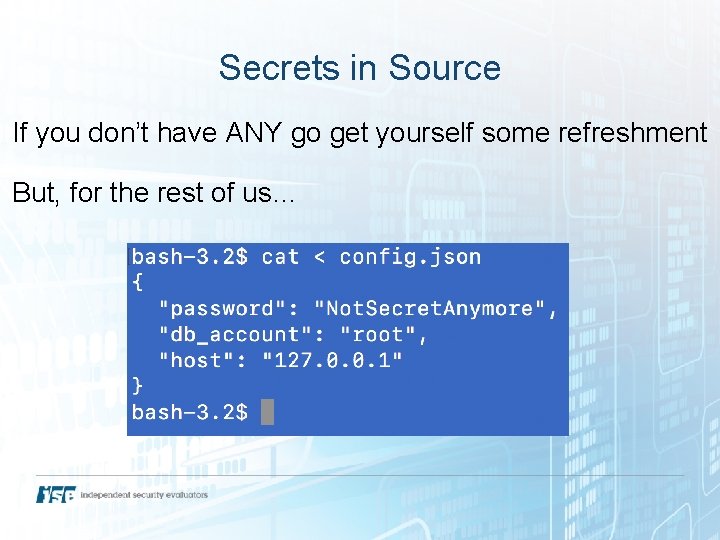
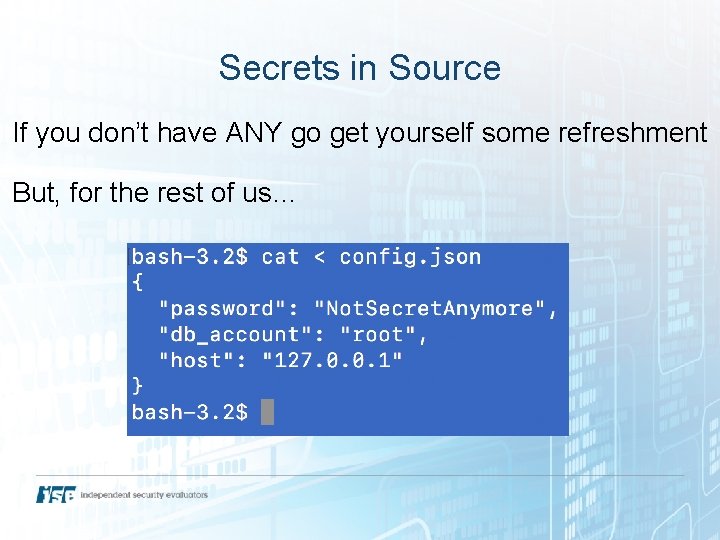
Secrets in Source If you don’t have ANY go get yourself some refreshment But, for the rest of us…
What’s the Threat? One compromised development machine = Credentials to production systems exposed Which credentials? 1. 2. 3. 4. Database Admin/Debug functionality Encryption JWT Secrets, etc
Questions Does the problem exist in your organization? Do you know how to fix it if it does occur? * *Each system has their own way of handling this, I have included links to official documentation in the references

IT Operations
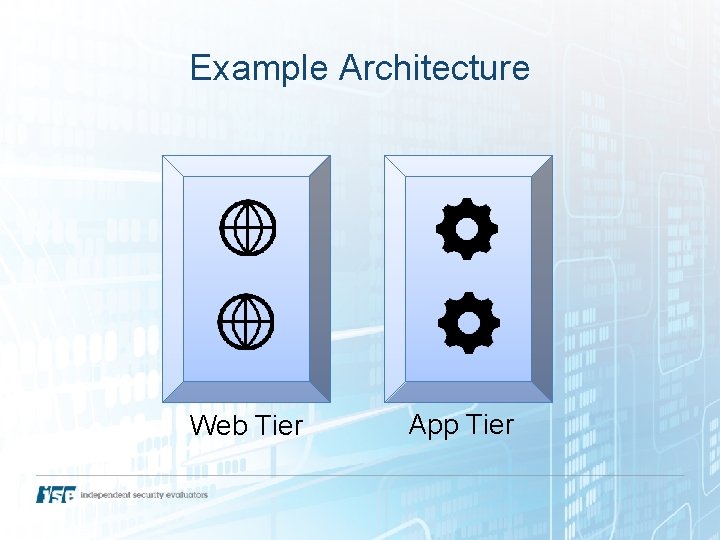
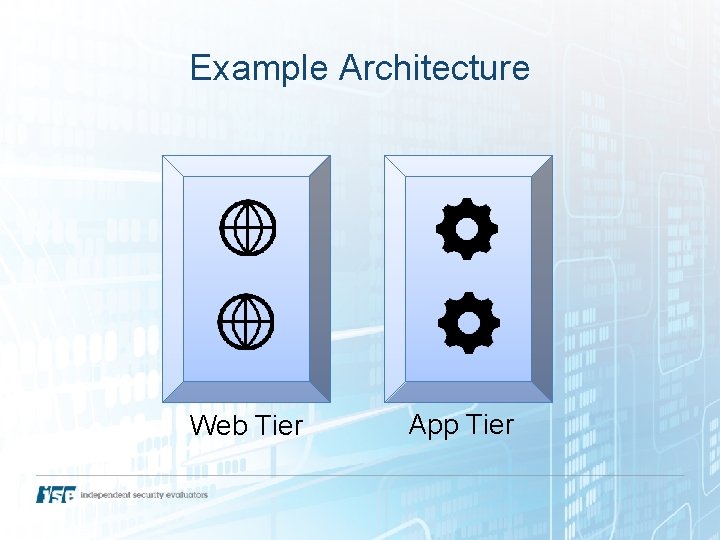
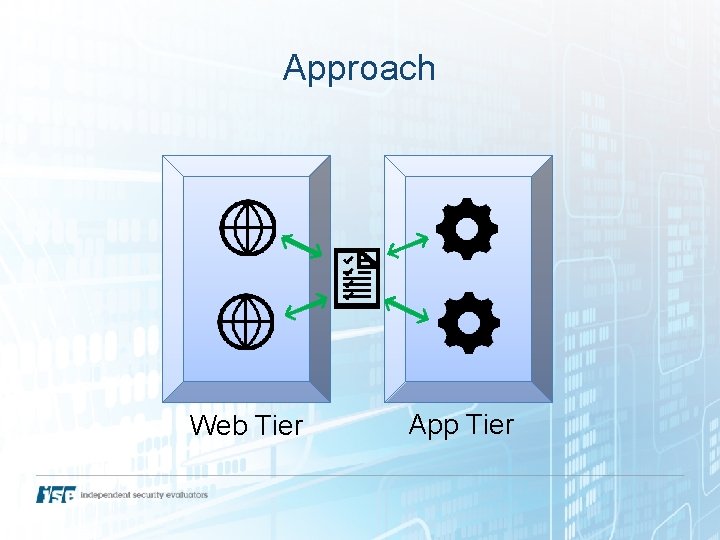
Example Architecture Web Tier App Tier
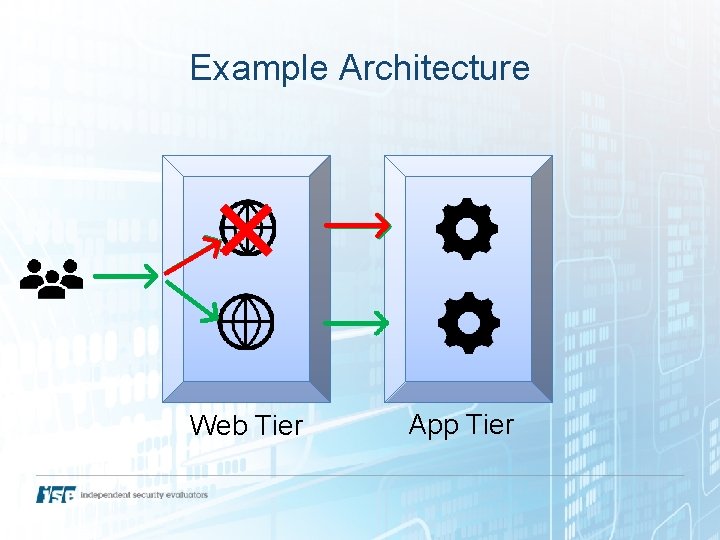
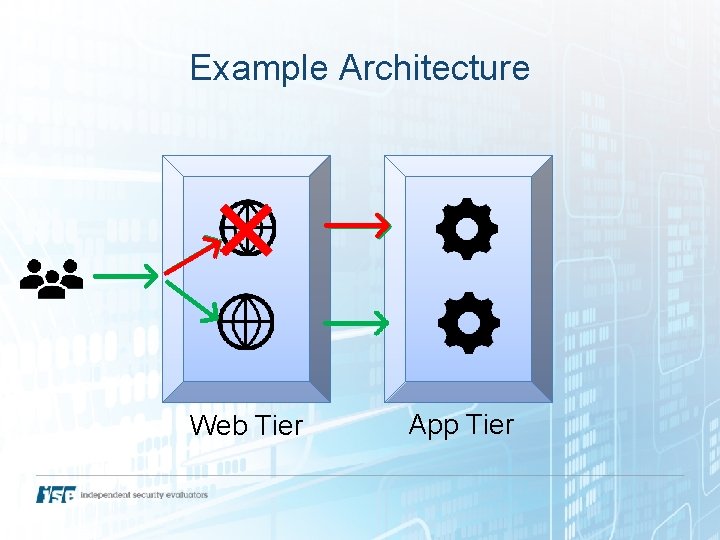
Example Architecture Web Tier App Tier
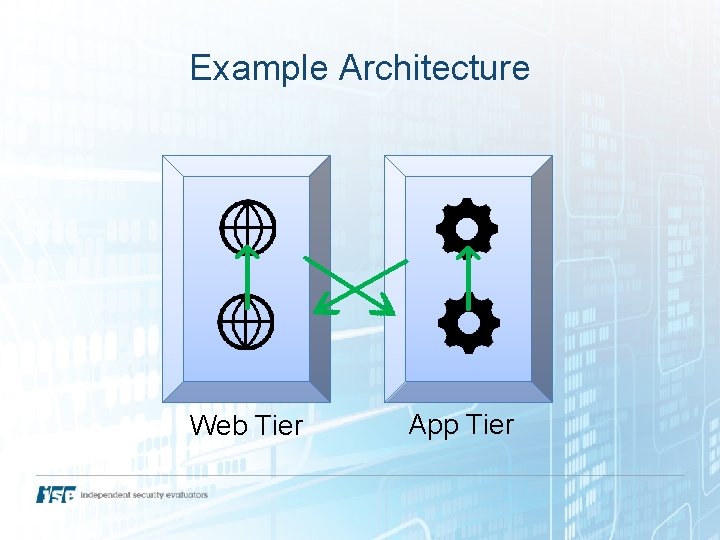
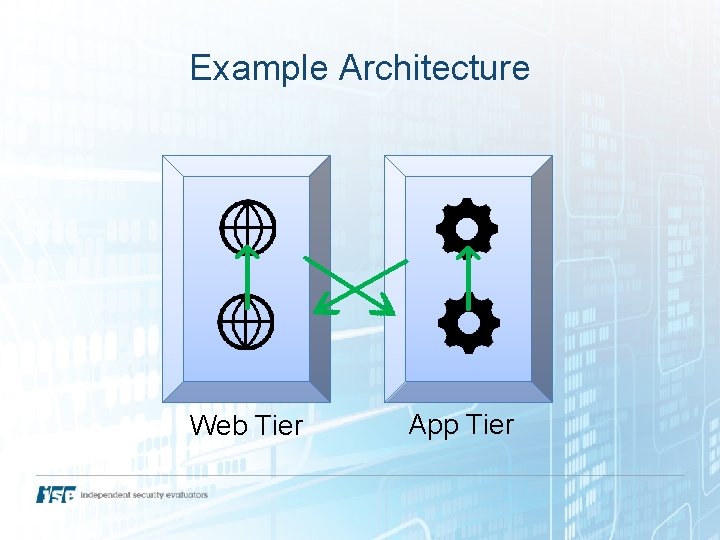
Example Architecture Web Tier App Tier
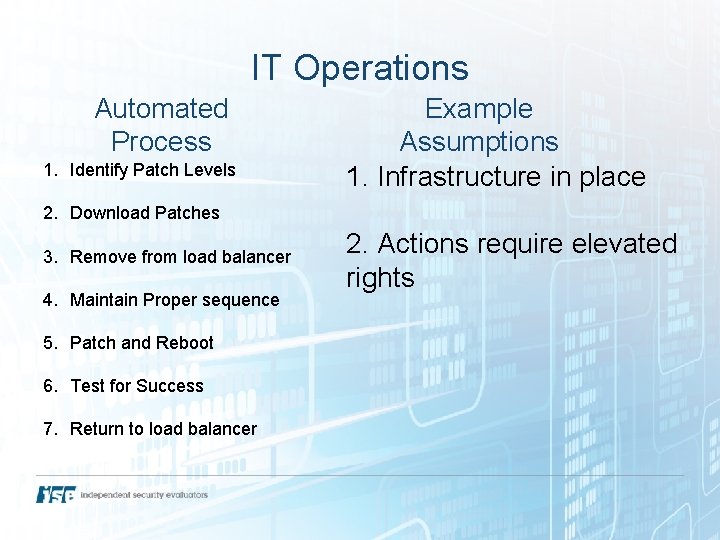
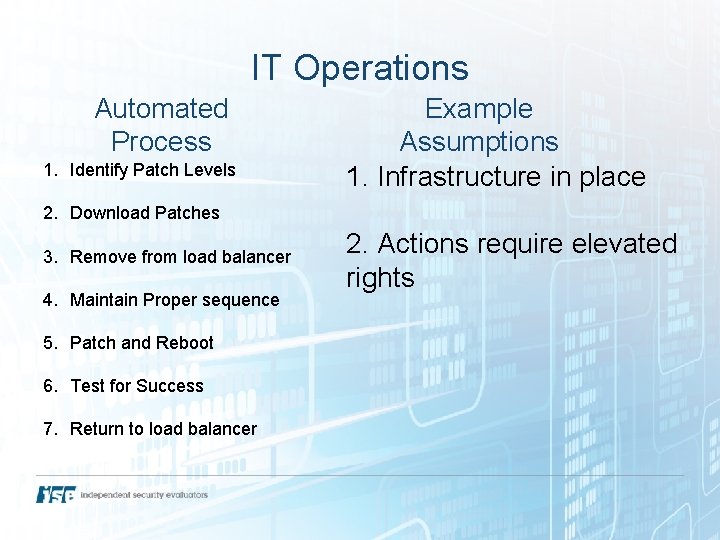
IT Operations Automated Process 1. Identify Patch Levels Example Assumptions 1. Infrastructure in place 2. Download Patches 3. Remove from load balancer 4. Maintain Proper sequence 5. Patch and Reboot 6. Test for Success 7. Return to load balancer 2. Actions require elevated rights
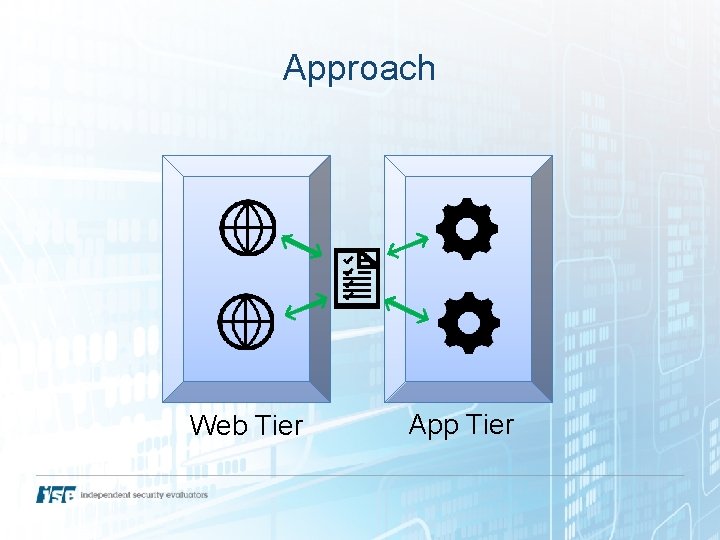
Approach Web Tier App Tier
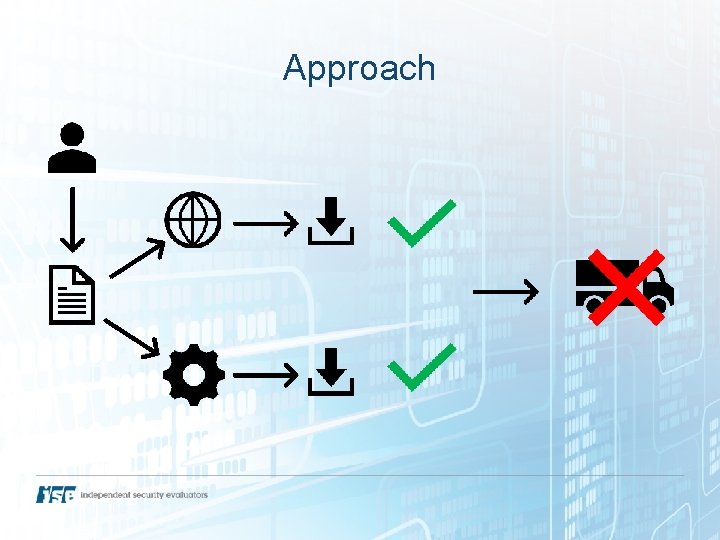
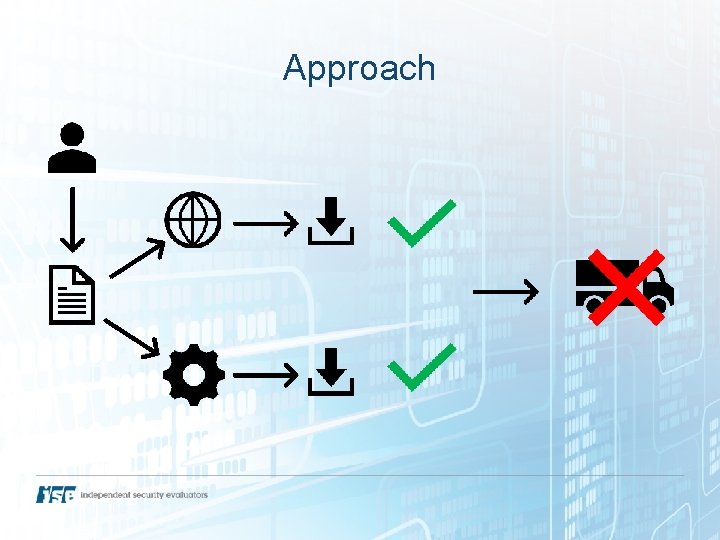
Approach

Approach ?
What’s the threat? Hard to maintain Hard to teach Application account with admin creds Sustained or Recurring Outages
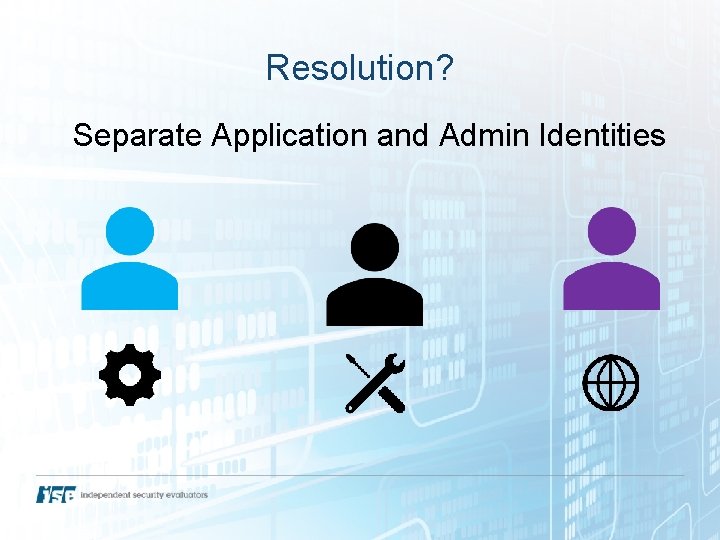
Resolution? Separate Application and Admin Identities
Questions Are independent systems within the application stack running with unique credentials, which only have the necessary rights to perform that systems tasks? Are there any accounts being used to programmatically manage or manipulate multiple layers of the application stack?
Infrastructure Automation tools can cause outages… But as systems scale, tools are necessary
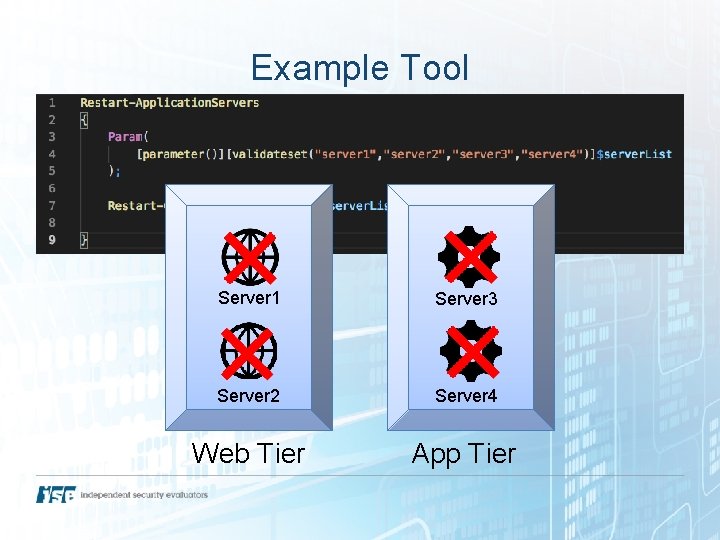
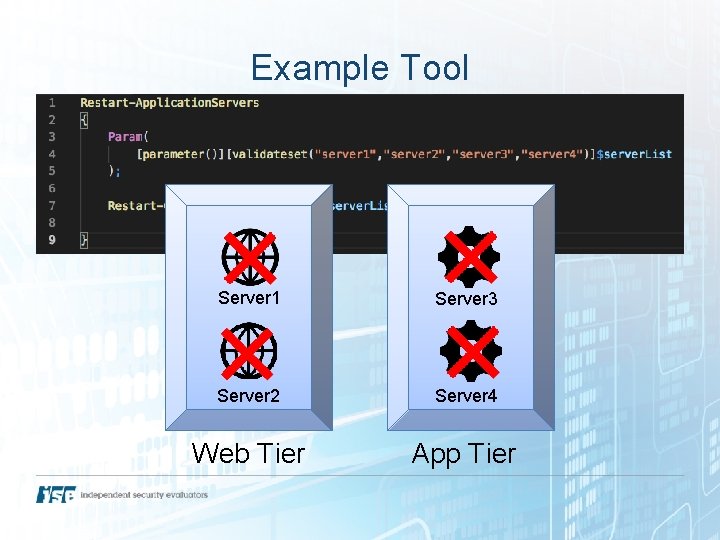
Example Tool Server 1 Server 3 Server 2 Server 4 Web Tier App Tier

Needs tools at scale!
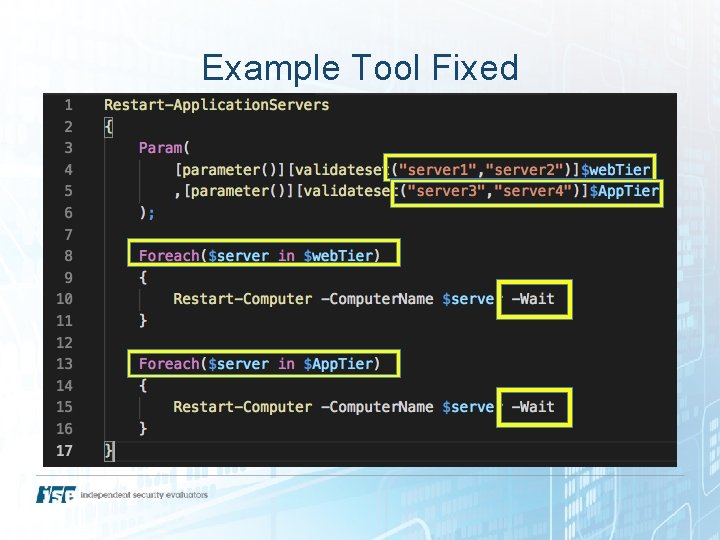
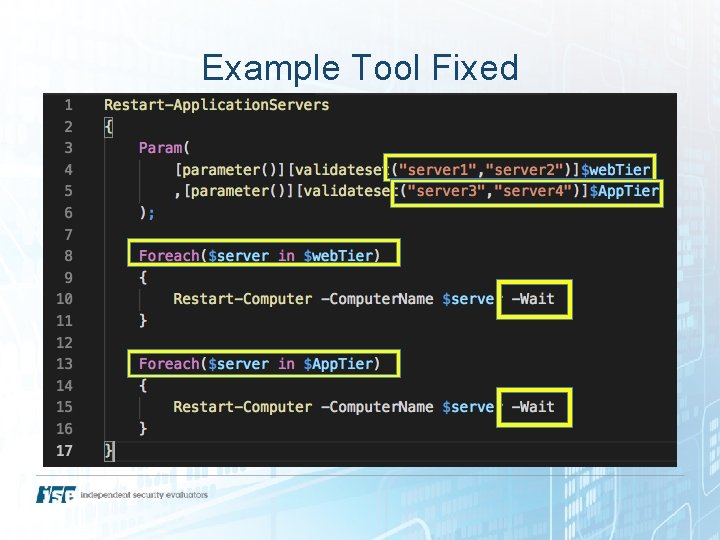
Example Tool Fixed
Tenants Always commit to source control Always peer review Always test in non-production environments
Questions Are scripts and tools, as well as the processes and procedures to leverage them, maintained in a version control system? Are scripts and tools, as well as the management processes, peer reviewed and each capability tested before it is implemented and used against production systems?
Security Auditing ?
Security Auditing Application scanning tool reported source code disclosure… … of Java. Script files. Code runs on the client
What happened? Maybe a default configuration? The report wasn’t reviewed
Auditing Tools Required component of security audits Must be interpreted by a human Otherwise, potential for disillusionment that could let vulnerabilities to go unresolved
Questions Were you involved in the process of interpreting results of an application security assessment to vet and corroborate issues discovered, and were any issues and their respective resolutions documented
Wrap Up Automation systems are software too Even small scripts count Defensive coding Teams and Tools

Our Links https: //securityevaluators. com https: //iotvillage. com https: //blog. securityevaluators. com/iselabs/home Contact Me Twitter: @johnnygtech Email: jgleason@securityevaluators. com
Resources https: //arstechnica. com/information-technology/2016/04/hacking-slack-accounts -as-easy-as-searching-github/ https: //help. github. com/articles/removing-sensitive-data-from-a-repository/ https: //subversion. apache. org/faq. html#removal Proprietary Icons https: //svn. apache. org/repos/asf/subversion/svn-logos/logo. html https: //git-scm. com/images/logos/downloads/Git-Icon-1788 C. png https: //visualstudio. microsoft. com/team-services/

THANK YOU!