Authentication for Fragments Craig Partridge BBN Technologies craigbbn
Authentication for Fragments Craig Partridge BBN Technologies craig@bbn. com
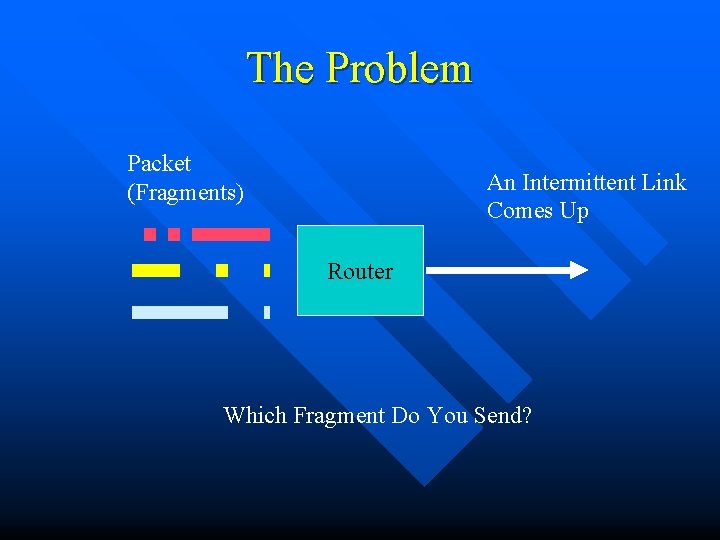
The Problem Packet (Fragments) An Intermittent Link Comes Up Router Which Fragment Do You Send?
Why An Issue? New network scenarios with intermittent (potentially) oversubscribed links n A desire to send the most valuable traffic first n Large native unit of authentication n – Mobigrams – DTN bundles
Starting Assumptions “Datagram” may be (re)fragmented at any point in the data and at any time (including during transmission) n Fragments do not all follow the same path n
“Datagram” may be (re)fragmented at any point in the data and at any time (including during transmission n Nice assumption – Can pre-empt fragments during transmission – Very general n Apparently untenable – Creates unauthenticatable fragments – Creates new style of attack on fragments n Must fragment on boundaries determined by origin (ugh!) Bytes 1. . j Auth Unit P+1 Bytes k. . n Auth Unit P
Fragments do not all follow same path n Distributed Romanow-Floyd problem – Fragment lost on path 1 means fragments on path 2 now can only do harm, yet path 2 must treat them as valuable n Shared keys problematic – Every fragmentation point has private key with each origin? – Public key signatures are BIG n Either – Each fragment is self authenticating (see PK is BIG) – Or we distribute aggregated authentication information down all possible paths (can we make it small enough? )
Can We Make Authentication Information Small Enough? n An idea: send function definition, not signature – Implies result of function is known – E. g. fragment #5 has digital hash of 5 n Such functions exist… – But either compact in representation OR strong enough to provide digital signature – NOT both (yet!) – Why this is a HOTNETS paper
While I Take Questions… n This builds on prior work – Kent/Mogul, “Fragmentation Considered Harmful” – Romanow/Floyd, “Dynamics of TCP Traffic over ATM Networks” – Matthis/Heffner/Chandler, “Fragmentation Considered Very Harmful” – Toilet paper authentication ideas in DTN list
- Slides: 8