Authentication and Open Standards Brian Kelly UKOLN University
Authentication and Open Standards Brian Kelly UKOLN University of Bath, BA 2 7 AY http: //www. ukoln. ac. uk/ 1 UKOLN is funded by the British Library Research and Innovation Centre, the Joint Information Systems Committee of the Higher Education Funding Councils, as well as by project funding from the JISC’s Electronic Libraries Programme and the European Union. UKOLN also receives support from the University of Bath where it is based.
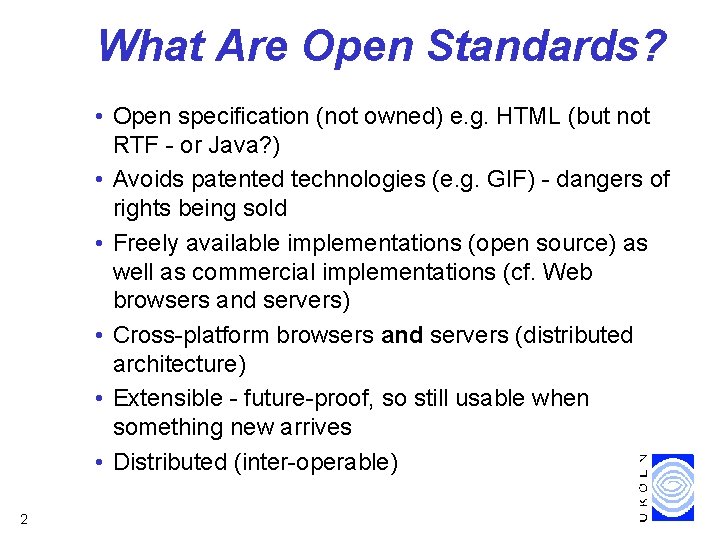
What Are Open Standards? • Open specification (not owned) e. g. HTML (but not RTF - or Java? ) • Avoids patented technologies (e. g. GIF) - dangers of rights being sold • Freely available implementations (open source) as well as commercial implementations (cf. Web browsers and servers) • Cross-platform browsers and servers (distributed architecture) • Extensible - future-proof, so still usable when something new arrives • Distributed (inter-operable) 2
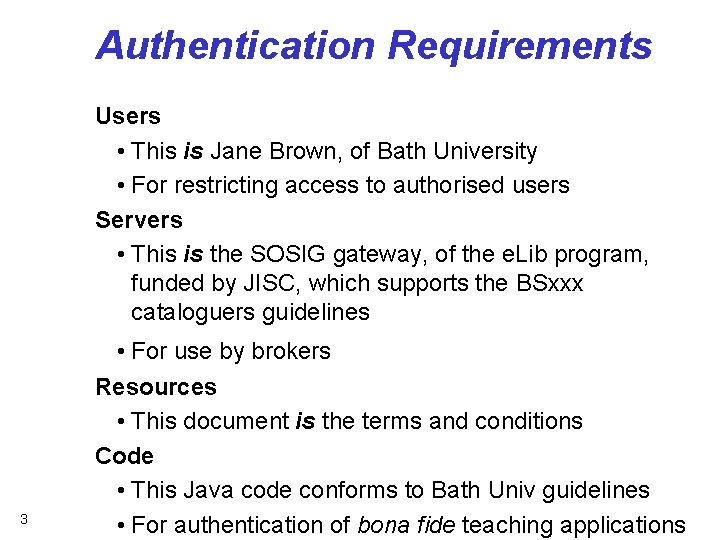
Authentication Requirements Users • This is Jane Brown, of Bath University • For restricting access to authorised users Servers • This is the SOSIG gateway, of the e. Lib program, funded by JISC, which supports the BSxxx cataloguers guidelines 3 • For use by brokers Resources • This document is the terms and conditions Code • This Java code conforms to Bath Univ guidelines • For authentication of bona fide teaching applications
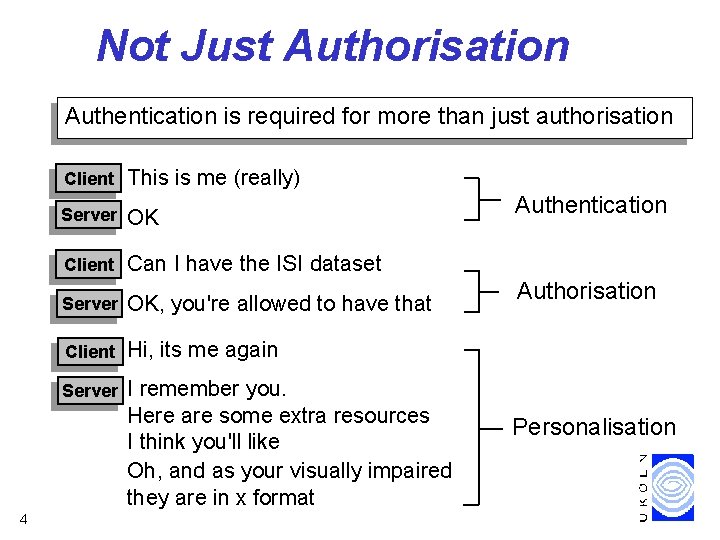
Not Just Authorisation Authentication is required for more than just authorisation 4 Client This is me (really) Server OK Client Can I have the ISI dataset Server OK, you're allowed to have that Client Hi, its me again Server I remember you. Here are some extra resources I think you'll like Oh, and as your visually impaired they are in x format Authentication Authorisation Personalisation

Digital Certificates "A digital certificate is an electronic "credit card" that establishes your credentials when doing business or other transactions on the Web. It is issued by a certification authority (CA). It contains your name, a serial number, expiration dates, a copy of the certificate holder's public key. " 5 "Internet business and many other transactions require a more stringent authentication process [than usernames]. The use of digital certificates issued and verified by a Certificate Authority (CA) as part of a Public Key Infrastructure is considered likely to become the standard way to perform authentication on the Internet. " - whatis. com
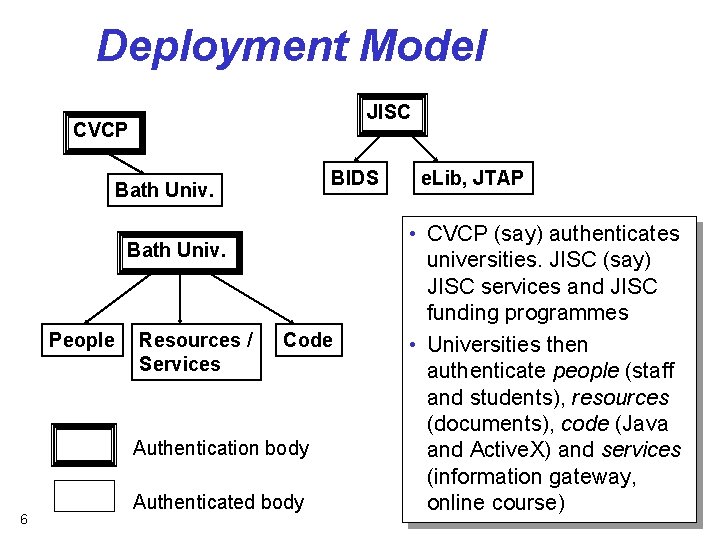
Deployment Model JISC CVCP BIDS Bath Univ. People Resources / Services Code Authentication body 6 Authenticated body e. Lib, JTAP • CVCP (say) authenticates universities. JISC (say) JISC services and JISC funding programmes • Universities then authenticate people (staff and students), resources (documents), code (Java and Active. X) and services (information gateway, online course)
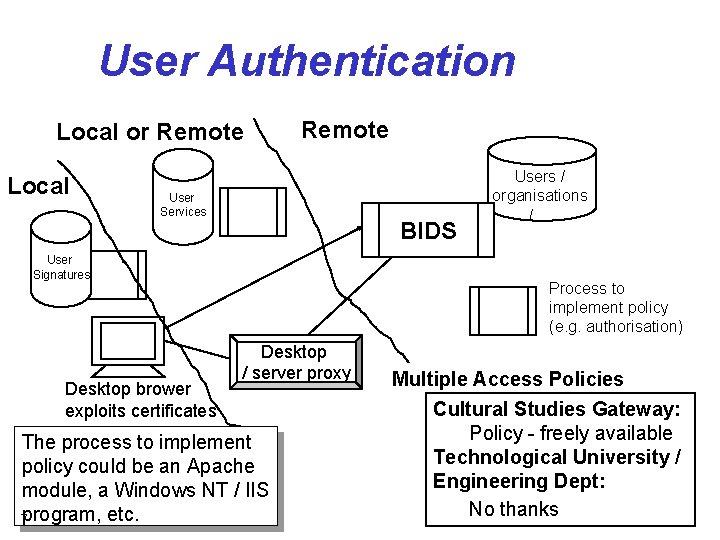
User Authentication Local or Remote Local Remote User Services BIDS User Signatures Desktop brower exploits certificates Users / organisations /. . . Process to implement policy (e. g. authorisation) Desktop / server proxy The process to implement policy could be an Apache module, a Windows NT / IIS 7 program, etc. Multiple Access Policies Cultural Studies Gateway: Policy - freely available Technological University / Engineering Dept: No thanks
Resource Authentication Available now in web browsers Can check: • Server • Resource • Mobile code Infrastructure for widespread deployment not yet in pace 8
Service Authentication In ecommerce: • Find online banks which provide loans which are members of the Banking Corporation • Search for hotels which cost < £ 100 and are members of the Good Banking organisation In HE: • Find online courses which are given by institutes recognised by the HEFCE and the US equivalent • Cross-search UK and US gateways using the new Foo. Bar distributed search protocol and which are funded by JISC or NSF and which abide by the TRUSTe privacy guidelines Note that authenticated services which provide service details in machine-readable format will be needed for deployment of intelligent agents, brokers, etc. 9
How Close to Implementation? We Want an Extranet! Thawte's white paper on Strong Extranets describes similar functionality to UK HE's requirements: • Students provided with email and access control certificate • "Relative identity" (student no. ) stored in certificate and processed by applications 10 See <URL: http: //www. thawte. com/certs/ strongextranet/contents. html >

The Market Players Many players in marketplace BT Trustwise at http: //www. trustwise. com/ Verisign at http: //www. verisign. com/ 11
What Next? Need to avoid reinventing coloured books! Gain Experience from Bottom Up • Learn from departmental / organisational experiences • Funding of pilots (see JTAP projects at <URL: http: //www. jtap. ac. uk/>) Top Down Approach • EU / UK initiatives • e-commerce developments Awareness of Alternatives • Smart cards • • Proprietary solutions 12 Pentium ID Continuation of discussions, monitoring developments, healthy scepticism, etc. Main problems are political and organisational
- Slides: 12