Authenticating with Block Ciphers CS 470 Introduction to
Authenticating with Block Ciphers CS 470 Introduction to Applied Cryptography Instructor: Ali Aydin Selcuk CS 470, A. Selcuk Message Auth. Codes 1
Message Authentication Codes (MAC) • A keyed checksum of the message. • Sender of a message m computes c = MACK(M) and sends (M, c) to the receiver. • Receiver also computes c' = MACK(M). If c' = c the message is accepted. • Example applications: – protecting files on an OS against modification – authentication of routing messages CS 470, A. Selcuk Message Auth. Codes 2
MACs (cont’d) • A MACed message is not necessarily encrypted. • MAC function doesn’t need to be invertible. • MAC keys are symmetric. Hence, doesn’t provide non-repudiation. (unlike digital signatures) • Security of a MAC: An attacker shouldn’t be able to generate a valid (M', c') pair, even after seeing many valid message-MAC pairs possibly of his choice (i. e. by a chosen message attack). CS 470, A. Selcuk Message Auth. Codes 3
MAC from a Block Cipher How to obtain a MAC from a block cipher? Suggestion: – divide message into blocks – compute a checksum by adding (or xoring) them – encrypt the checksum with the block cipher Is this construction secure? – If the message is not encrypted? – If the message is encrypted? CS 470, A. Selcuk Message Auth. Codes 4
CBC-MAC • Raw CBC-MAC: – Compute the CBC over the message with IV = 0. – The last output block is the MAC – Q: Why not a random IV? Other alternatives: – ECB? – OFB/CTR? – CFB? CS 470, A. Selcuk Message Auth. Codes 5
CBC-MAC (cont. ) • Theorem: When defined over some specifiedlength input message (of n blocks) {0, 1} n x ℓ → {0, 1} ℓ raw CBC-MAC is provably secure, given that the underlying block cipher is secure. • But it is insecure if used for variable-length messages – Given the MAC of 1 -block m, c = MACK(m), attacker can compute MACK(m || m c). (How? ) – Many similar attacks are also possible. CS 470, A. Selcuk Message Auth. Codes 6
Encrypted CBC-MAC • Two keys (K, K 1). Do one additional encryption on the final block with K 1: y = CBC-MACK(M) c = EK 1(y) • Theorem: ECBC-MAC is provably secure, given that the underlying block cipher is secure. CS 470, A. Selcuk Message Auth. Codes 7
CBC-MAC Padding • How to MAC a message whose length is not a multiple of the block size ℓ ? • Padding with all 0 s? No! (why not? ) • Append a 1, and then pad with 0 s. • Do this even if the message length is already a multiple of ℓ. (why? ) • Basic Idea: Two distinct messages M and M' should remain distinct after the padding too. CS 470, A. Selcuk Message Auth. Codes 8
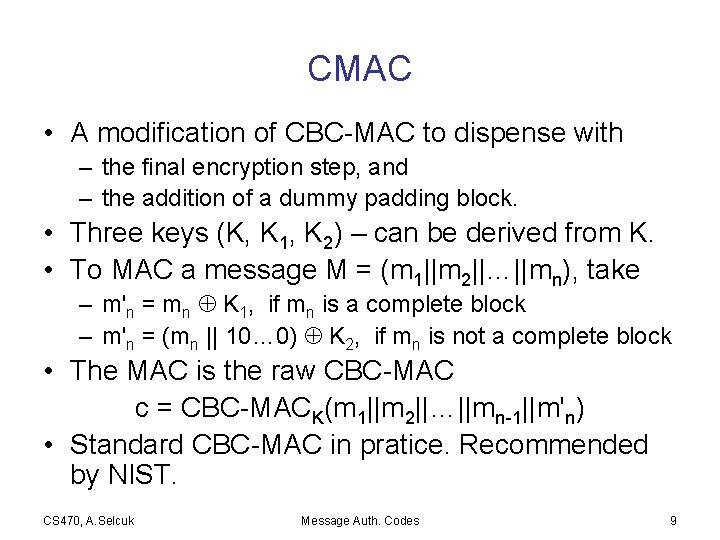
CMAC • A modification of CBC-MAC to dispense with – the final encryption step, and – the addition of a dummy padding block. • Three keys (K, K 1, K 2) – can be derived from K. • To MAC a message M = (m 1||m 2||…||mn), take – m'n = mn K 1, if mn is a complete block – m'n = (mn || 10… 0) K 2, if mn is not a complete block • The MAC is the raw CBC-MAC c = CBC-MACK(m 1||m 2||…||mn-1||m'n) • Standard CBC-MAC in pratice. Recommended by NIST. CS 470, A. Selcuk Message Auth. Codes 9
- Slides: 9